Ch - dennis henry
advertisement

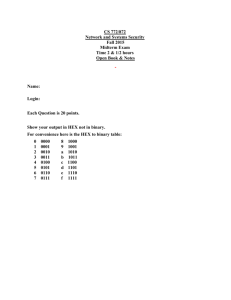
Ch. 30 shift cipher Caesar cipher Use the shift cipher with key = 15 to encrypt the message “HELLO.” Solution We encrypt one character at a time. Each character is shifted 15 characters down. Letter H is encrypted to W. Letter E is encrypted to T. The first L is encrypted to A. The second L is also encrypted to A. And O is encrypted to D. The cipher text is WTAAD. encrypt (top to bottom) decrypt (bottom to top) transposition cipher (will be given word & key) / group/block coding (add z) reorders (permutes) symbols in a block of symbols. Encrypt the message “HELLO MY DEAR,” using the key. Solution We first remove the spaces in the message. We then divide the text into blocks of four characters. We add a bogus character Z at the end of the third block. The result is HELL OMYD EARZ. We create a three-block ciphertext ELHLMDOYAZER. (hint: mapping schema… 13, 21, 42, 34…if odd number of letters in message, add bogus z so mapping is workable) Ch. 31 Confidentiality The transmitted message must make sense to only the intended receiver Integrity Means that the data must arrive at the receiver exactly as they were sent non-repudiation Means that a sender must not be able to deny sending a message that he or she, in fact, did send. The burden of proof falls on the receiver. For example, when a customer sends a message to transfer money from one account to another, the bank must have proof that the customer actually requested this transaction. digital signature (provides 2 things) Public key Private key Provides: o Message authentication o Non-repudiation??? Kerberos Kerberos is the name of a computer network authentication protocol, which allows individuals communicating over an insecure network to prove their identity to one another in a secure manner. It is also a suite of free software published by Massachusetts Institute of Technology (MIT) which implements this protocol. Its designers aimed primarily at a client-server model, and it provides mutual authentication — both the user and the server verify each other's identity. Kerberos protocol messages are protected against eavesdropping and replay attacks. Kerberos builds on symmetric key cryptography and requires a trusted third party. Extensions to Kerberos can provide for the use of public key cryptography during certain phases of the authentication protocol criterion of a hash algorithm (first and second) One-wayness o must not be able to recreate the message from the digest. o Should not be reversible Strong collision resistance o Ensures that we cannot find two messages that hash to the same digest. o This criterion is needed to ensure that Alice, the sender of the message, cannot cause problems by forging a message. o If Alice can create 2 messages that hash to the same digest, she can deny sending the first to Bob and claim that she sent only the second. o “strong” because higher probability of collision Weak collision resistance o Ensures that a message cannot easily be forged. o If Alice creates a message and a digest and sends both to Bob, this criterion ensures that Eve cannot easily create another message that hashes exactly to the same digest. ethical hacking notes (brian has these) DES/AES DES was designed by IBM and adopted by the US gvmt as the standard encryption method for nonmilitary and nonclassified use. The algorithm encrypts a 64-bit plaintext block using a 64bit key as shown on the left. DES has 2 transposition boxes (P-boxes) and 16 complex round ciphers. Each round cipher uses a different key derived from the original key. The heart of DES is the DES function. The function applies a 48-bit key to the rightmost 32 bits Ri; to produce a 32-bit output. This function is made up of 4 operations; an XOR, an expansion permutation, a group of s-boxes, and a straight permutation (as shown above). Advanced Encryption Standard (AES) was designed because DES’s key was too small. Triple DES increased the key size, but the process was too slow. AES is a very complex cipher (named after Vincent Rijmen and Joan Daeman). AES is designed with 3 key sizes: 128, 192, or 256 bits. The table above shows the relationship between the data block, number of rounds, and key size. block ciphers Operation Modes: ECB o o CBC o o CFB o o Electronic Code Book mode N N Cipher Block Chaining mode Uses previous cipher in prep for new block Cipher Feedback mode Used if “x” bits of data needs to be sent instead of the “n” bits used in the message/cipher OFB o Output Feedback mode o Same as CFB, but each bit in cipher text is independent from others. o If error occurs, no other bits are effected. # services network security provides