Quiz A(答案直接寫於題目後,不夠寫在後面) 姓名:
advertisement
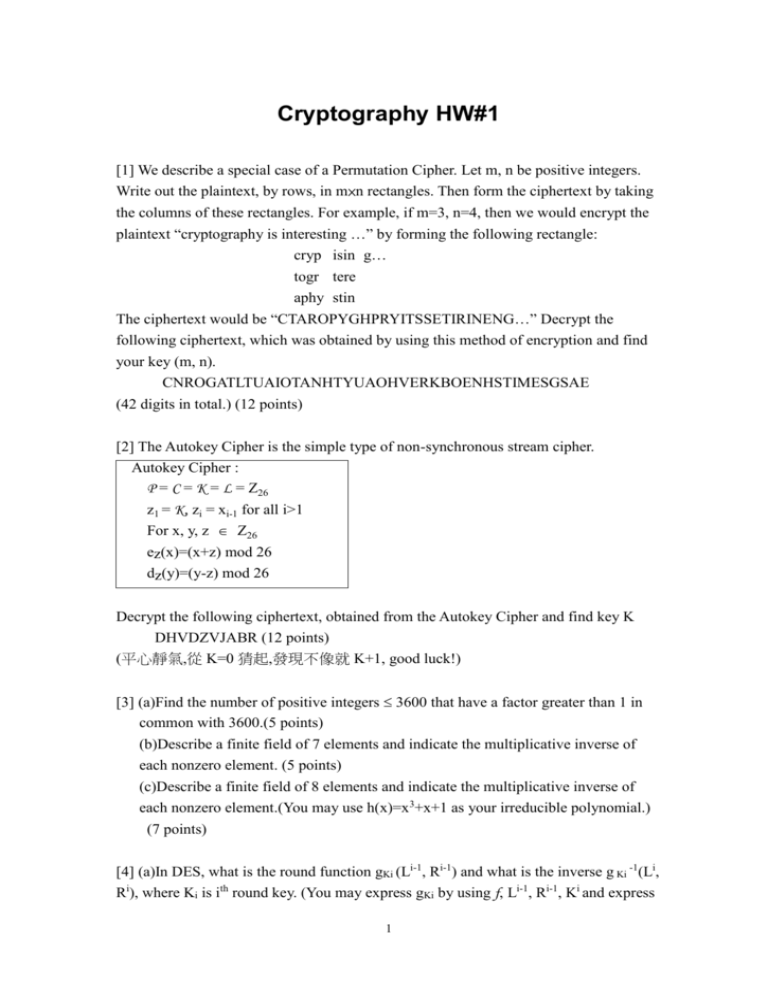
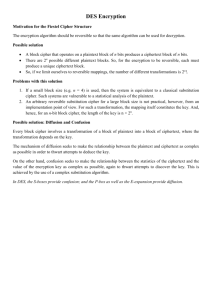
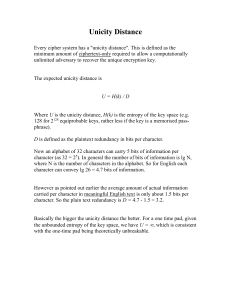
Cryptography HW#1 [1] We describe a special case of a Permutation Cipher. Let m, n be positive integers. Write out the plaintext, by rows, in m×n rectangles. Then form the ciphertext by taking the columns of these rectangles. For example, if m=3, n=4, then we would encrypt the plaintext “cryptography is interesting …” by forming the following rectangle: cryp isin g… togr tere aphy stin The ciphertext would be “CTAROPYGHPRYITSSETIRINENG…” Decrypt the following ciphertext, which was obtained by using this method of encryption and find your key (m, n). CNROGATLTUAIOTANHTYUAOHVERKBOENHSTIMESGSAE (42 digits in total.) (12 points) [2] The Autokey Cipher is the simple type of non-synchronous stream cipher. Autokey Cipher : P = C = K = L = Z26 z1 = K, zi = xi-1 for all i>1 For x, y, z Z26 ez(x)=(x+z) mod 26 dz(y)=(y-z) mod 26 Decrypt the following ciphertext, obtained from the Autokey Cipher and find key K DHVDZVJABR (12 points) (平心靜氣,從 K=0 猜起,發現不像就 K+1, good luck!) [3] (a)Find the number of positive integers 3600 that have a factor greater than 1 in common with 3600.(5 points) (b)Describe a finite field of 7 elements and indicate the multiplicative inverse of each nonzero element. (5 points) (c)Describe a finite field of 8 elements and indicate the multiplicative inverse of each nonzero element.(You may use h(x)=x3+x+1 as your irreducible polynomial.) (7 points) [4] (a)In DES, what is the round function gKi (Li-1, Ri-1) and what is the inverse g Ki -1(Li, Ri), where Ki is ith round key. (You may express gKi by using f, Li-1, Ri-1, Ki and express 1 gKi-1 by using f, Li, Ri, Ki.) (6 points) (b) S3 below is the 3rd S-box of DES S3 10 0 9 14 6 3 15 5 1 13 12 7 11 4 2 8 13 7 0 9 3 4 6 10 2 8 5 14 12 11 15 1 13 6 4 9 8 15 3 0 11 1 2 12 5 10 14 7 1 10 13 0 6 9 8 7 4 15 14 3 11 5 2 12 What is the output of S3 if the input is 101001? And what is the output of S3 if the input is 011011 (6 points) (c) In DES, you are given any pair (x, y), where x and y are of 64 bits. What is the probability that there exists a key K such that DESK(x)=y? (5 points) (d) In DES, you are given two plaintext-ciphertext pairs (x1, y1) and (x2, y2) for some unknown real key K*. And if you find some key K in the exhaustive key search with DESK(x1)=y1 and DESK(x2)=y2, what is the probability that K=K*? (6 points) [5] Give a high-level description of AES to indicate how a plaintext x in AES is transformed to a ciphertext y. (Your answer should be limited in one page.)(12 points) [6] Suppose that the S-box is replaced by the following substitution S (x) . x 0 S (x) E 1 1 2 D 3 4 4 2 5 F 6 B 7 8 8 A 9 3 A 6 B C C 9 D 5 E 0 F 7 The linear approximation table of values NL(a,b)-8 for this S-box is computed in the following table except A, B. 2 a\b 0 1 2 3 4 5 6 7 8 9 0 +8 0 0 0 0 0 0 0 0 0 1 0 +2 -2 -4 +2 0 0 +2 -2 +4 2 0 -2 -2 -4 +2 0 0 -2 0 -2 3 0 +4 0 0 0 0 0 -4 -2 -2 4 0 +2 0 -2 -2 -4 -2 0 0 -2 5 0 0 -2 -2 -4 +4 +2 +2 -2 -2 6 0 0 -2 +2 +4 0 +2 +2 0 -4 7 0 +2 0 +2 -2 0 -2 0 -2 0 8 0 0 0 0 0 0 0 0 -2 +2 9 0 -2 -2 0 -2 0 -4 +2 0 -2 A 0 +2 -2 0 -2 0 +4 -2 +2 0 B 0 +4 0 0 0 0 0 +4 +4 0 C 0 -2 +4 -2 B 0 +2 0 +2 0 D 0 0 +2 +2 0 0 +2 +2 -4 0 E 0 0 +2 -2 0 -4 +2 +2 -2 -2 F 0 -2 -4 +2 -2 -4 +2 0 0 +2 A 0 0 +2 -2 0 0 +2 B 0 +2 0 +2 +2 0 +2 A 0 +2 -2 -2 0 0 -2 0 0 +2 +4 -2 +2 0 -4 0 +2 C 0 0 +2 -2 +2 -2 0 0 +2 +2 +4 0 0 +4 -2 -2 D 0 +2 0 +2 -4 -2 0 +2 -2 +4 +2 0 +2 0 +2 0 E F 0 0 +2 0 -4 +2 -2 -2 +2 0 0 0 +2 -2 0 +2 -2 -6 0 -2 +2 0 -4 0 0 -2 -2 +2 0 0 -2 0 (a) Calculate A and B by the corresponding truth tables (you may use the following presentation of S (x) ). (6 points) X1 X2 X3 X4 Y1 Y2 Y3 Y4 0 0 0 0 1 1 1 0 0 0 0 1 0 0 0 1 0 0 1 0 1 1 0 1 0 0 1 1 0 1 0 0 0 1 0 0 0 0 1 0 0 1 0 1 1 1 1 1 0 1 1 0 1 0 1 1 0 1 1 1 1 0 0 0 1 0 0 0 1 0 1 0 1 0 0 1 0 0 1 1 1 0 1 0 0 1 1 0 1 0 1 1 1 1 0 0 1 1 0 0 1 0 0 1 1 1 0 1 0 1 0 1 1 1 1 0 0 0 0 0 1 1 1 1 0 1 1 1 (b) The trail we choose in the linear attack is shown in the following figure. What is the total bias of this trail? (Show your steps.) (10 points) 3 plaintext P1 P2 … P16 Subkey K1 mixing 1 U S11 S21 S31 S41 V1 W1 Subkey K2 mixing U2 S12 S22 S32 S42 V2 W2 Subkey K3 mixing U3 S13 S23 S33 S43 V3 W3 Subkey K4 mixing U4 S14 S24 S34 S44 4 V Subkey K5 mixing C1C2 … C16 ciphertext (c) From the above figure, list all the random variables of plaintext bits, bits of U4 and key bits, which are involved in this attack. (8 points) 4