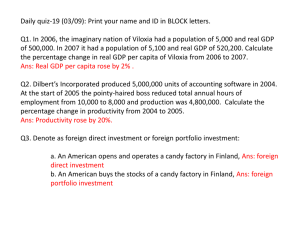
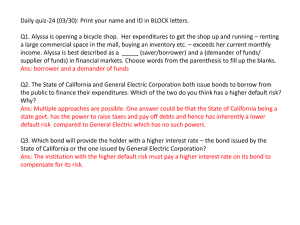
quizQ&A
advertisement

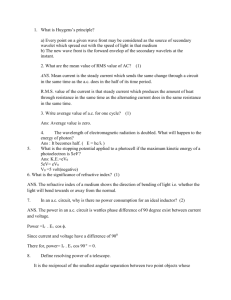
PARISUTHAM INSTITUE OF TECHNOLOGY & SCIENCE CS1355-CRYPTOGRAPHY AND NETWORK SECURITY –VI SEM (DEPARTMENT OF IT) QUIZ QUESTIONS AND ANSWERS 1) This is an encryption/decryption key known only to the party or parties that exchange secret messages. a) e-signature b) digital certificate c) private key d) security token Ans: c) private key 2) This was commonly used in cryptography during World War II. a) tunneling b) Personalization c) van Eck phreaking d) one-time pad Ans: d) one-time pad 3) Today, many Internet businesses and users take advantage of cryptography based on this approach. a) public key infrastructure b) output feedback c) Encrypting File System d) single sign on Ans: a) public key infrastructure 4) This is the name for the issuer of a PKI certificate. a) man in the middle b) certificate authority c) Resource Access Control Facility d) script kiddy Ans :b) certificate authority 5) Developed by Philip R. Zimmermann, this is the most widely used privacy-ensuring program by individuals and is also used by many corporations. a) DSS b) OCSP c) Secure HTTP d) Pretty Good Privacy Ans: d) Pretty Good Privacy 6) This is the encryption algorithm that will begin to supplant the Data Encryption Standard (DES) - and later Triple DES - over the next few years as the new standard encryption algorithm. a) Rijndael b) Kerberos c) Blowfish d) IPsec Ans: a) Rijndael 7) This is the inclusion of a secret message in otherwise unencrypted text or images. a) masquerade b) steganography c) spoof d) eye-in-hand system Ans: b) steganography 8) In AES the final round of both encryption and decryption consist of only _____ stages. Ans: 3 stages. 9) This is a mode of operation for a block cipher, with the characteristic that each possible block of plaintext has a defined corresponding cipher text value and vice versa. a) foot printing b) hash function c) watermark d) Electronic Code Book Ans: d) Electronic Code Book 10) This is a trial and error method used to decode encrypted data through exhaustive effort rather than employing intellectual strategies. a) chaffing and winnowing b) cryptanalysis c) serendipity d) brute force cracking Ans:d) brute force cracking 11) The two basic functions used in encryption algorithms are __________and __________ Ans: Substitution, Transposition 12) How many keys are required for two people to communicate via a cipher a) One Key in Symmetric cipher b) Two Keys in Asymmetric cipher c) Always Two keys in Symmetric d) More than two keys in Asymmetric Ans: a&b 13) The two approaches to attack a cipher are_______________ and _______________ Ans : Cryptanalysis , Brute-force attack 14) S-boxes in DES a) Two b) Four c) Thirty Two d) Eight Ans: d) Eight 15) In each S-Box in DES , it takes a) Two bits input and produce 4 bits as output b) Six bits input and produce 4 bits as output c) Eight bits input and produce 6 bits as output d) Six bits input and produce 6 bits as output Ans: b) Six bits input and produce 4 bits output 16) A change in one of the bit of the plaintext should produce a change in many bits of the cipher text it is called as _____________________ Ans: Avalanche Effect. 17) A ________________processes the input one block of elements at a time, producing an output block for each input block. Ans: Block Cipher 18) In Rotor Machines, each cylinder has ___ input pins and ___ output pins. Ans: 26 input pins and 26 output pins 19) The areas of cryptography and cryptanalysis are called ____________ Ans: Cryptology. 20) In each round of DES________ key bits are used. Ans: 48 bits 21) A Covert Channel is a) Secure Channel b) Secure Channel for short messages c) Insecure Channel for Long messages d) Insecure Channel Ans: d) Insecure channel 22) How many bits are used in AES a) 64 bits b) 56 bits c) 128 bits d) 192 bits 23) What type of attack “denial of service” is ? Ans: Active attack 24)_____________ matrix is used in Playfair cipher . Ans: 5*5 matrix 25) What is the typical size for number of rounds in Feistel Cipher? Ans: 16 rounds. Ans: d) 192 bits