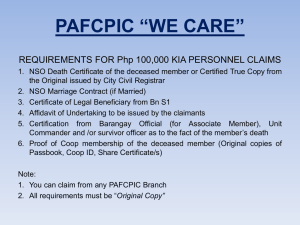
Wireless PKI - Mobile Payment Forum of India
advertisement

Wireless PKI Shakeel Ahamad Shaik (Research Fellow) Under the supervision of Dr.V.N.Sastry, Associate Professor (IDRBT) & Dr.S.K.Udgata, Reader (UOH) Monday, April 13, 2015 Wireless PKI 1 Agenda Public Key Systems PKI Functions in Mobile devices Problems faced in the adoption of PKI in Mobile Environment Validation of certificate in WPKI Environment Requirements & Configurations needed for the Implementation of WPKI in mobile payments Conclusion References Monday, April 13, 2015 Wireless PKI 2 Public-Key Systems Public Key Systems Public Key Cryptography (PKC) Monday, April 13, 2015 Personal security environment (PSE) Wireless PKI Public Key Infrastructure (PKI) 3 Public-Key Systems (Cont….) The main components of a PKI Certification Authority (CA) is responsible for issuing and revoking certificates for customers public keys. The Registration Authority (RA) provides a binding between public keys and the entities of their holders. Repositories store and make available certificate directories and a certificate revocation list (CRL). Directory service providers. CA’s in India IDRBT, Safescrypt, NIC,TCS,MTNL,GNFC,e MudhraCA Monday, April 13, 2015 Wireless PKI 4 PKI functions in Mobile Devices Generation of key-pair (public and private keys) Receiving & Storing certificate issued by CA Digital Signature generation and verification Functions for encryption and decryption Validating third party certificates Monday, April 13, 2015 Wireless PKI 5 Challenges in adopting Wired PKI for Mobile Devices Wireless network has less bandwidth, more latency, insecure connection and device problems such as less powerful CPU, less memory size, restricted battery power, small display and input device. Mobile phone lacks computing capabilities of PKI services such as key generation, digital signature generation and verification, certificate validation, and Certificate Revocation List (CRL) verification, and memory size of storing certificate and CRL. Due to less wireless communication bandwidth, processing of CMP (Certificate Management Protocol) for certificate life cycle such as certificate issue in the mobile phone, and downloading CRL required for certificate verification must be a considerable burden. Monday, April 13, 2015 Wireless PKI 6 Validation of Certificate in WPKI Environment Certificate Validation contains the following steps Verifying the integrity and authenticity of the certificate by verifying the digital signature of CA on the certificate. Verifying the validity period of the certificate. Accessing and examining certificate chain and CRL. The validation is considered successful if all the certificates in the certificate path (i.e. from leaf to the root of the tree) are checked and ensured that none of them have been revoked. This process is heavy on resources and time consuming and it is not suitable for mobile devices. Monday, April 13, 2015 Wireless PKI 7 Validation of Certificate in WPKI Environment (Cont…) Mechanisms to minimize the Certificate validation process Online Certificate Status Protocol (OCSP) Monday, April 13, 2015 Short Lived Certificate (SLC) Wireless PKI 9 Validation of Certificate in WPKI Environment (Cont….) OCSP mechanism 4. Requests for CRL 5. Sends CRL 1. Sends URL of certificat e (or) Certificat e 6. Response of Certificate Validation 3. Delegates certificate Validation of merchant’s Certificate 2. Merchant sends his X.509 Certificate Monday, April 13, 2015 Wireless PKI 10 Validation of Certificate in WPKI Environment (Cont….) Short-Lived Certificate (SLC) mechanism Certificate: Data: Version: 3 (0x2) Serial Number: 316214 (0x4d336) Signature Algorithm: ecdsa-with-SHA1 Issuer: C=IN, O=IDRBT, OU=CA, CN=CertSIGNECDSA1 Validity Not Before: Apr 17 15:00:00 2010 GMT Not After : Apr 26 14:59:59 2010 GMT Subject: C=IN, O=SBI, OU=CA, CN=test()000021420031112000653 Subject Public Key Info: Public Key Algorithm: id-ecPublicKey 04 04 df e4 6d 84 16 70 1a f3 f4 8e 80 ec ac ac f2 a3 26 b7 e0 60 03 0e 7d 6c ba b9 3e ac 9b eb 85 13 ed 6a b9 75 5c f5 c2 02 b1 Signature Algorithm: ecdsa-with-SHA1 30:2e:02:15:01:3a:07:0f:dc:e4:68:bc:c9:c1:1c:48:68:6b: 1f:99:65:0c:b5:13:55:02:15:03:65:ac:e4:82:c2:30:42:de: ce:f2:49:c5:91:30:c1:90:f3:59:72:5e Monday, April 13, 2015 Wireless PKI 11 Validation of Certificate in WPKI Environment (Cont….) Short-Lived Certificate (SLC) mechanism Improved computing & storage resources in mobile devices have made it convenient to generate key pairs & verify digital signatures on mobile devices. Using SLC mobile clients does not have to implement either CRL or OCSP for server authentication. Monday, April 13, 2015 Wireless PKI 12 Requirements & Configurations needed for the Implementation of WPKI in mobile payments Monday, April 13, 2015 Wireless PKI 13 Requirements & Configurations needed for the Implementation of WPKI in mobile payments (Cont..) Monday, April 13, 2015 Wireless PKI 14 Requirements & Configurations needed for the Implementation of WPKI in mobile payments (Cont..) Monday, April 13, 2015 Wireless PKI 15 Conclusion Compared to wired PKI Wireless PKI is suitable for low end computing devices such as mobile phones. Since Mobile payments require high level of security for its transactions which can be ensured by WPKI. We suggest the existing CA to provide digital certificate to individuals through mobile phones which can be used for mobile payment transactions. Monday, April 13, 2015 Wireless PKI 18 Abbreviations CMP WTLS WIM WAP OCSP CRL CA PKI WPKI SIM BER DER ECC SSL ECDSA ECDH URL 4/13/2015 Certificate Management Protocol Wireless Transport Layer Security Wireless Identity Module Wireless Application Protocol Online Certificate Status Protocol Certificate Revocation List Certification Authority Public Key Infrastructure Wireless Public Key Infrastructure Subscriber’s Identity Module Basic Encoding Rules Distinguished Encoding Rules Elliptic Curve Cryptography Secure Socket Layer Elliptic Curve Digital Signature Algorithm Elliptic Curve Diffie-Hellman Uniform Resource Locator Security Issues in Mobile Payments 19 REFERENCES 1) Yong Lee, Jeail Lee, JooSeokSong, “Design and implementation of wireless PKI technology suitable for Mobile phone in Mobile Commerce” in Computer Communications 30 (2007), 893-903. 2) Marko Hassinen, Konstantin Hypponen, Elena Trichina, “Utilizing national publickey infrastructure in mobile payment system”, Electronic Commerce Research and Applications 7 (2008), pp 214-231. 3) Population Register http://www.fineid.fi 4) Antonio Ruiz-Martinez, Daniel Sanchez-Martinez, Maria martinez-Montesinos and Antonio F. Gomez-Skrmeta, “A Survey of Electronic Signature Solutions in Mobile Devices” in Journal of Theoretical and Applied Electronic Commerce Research, Vol 2, Issue 3, December 2007, pp 94-109. 1) f Theoretical and Applied Electronic Commerce Research 4/13/2015 Centre. FINEID-S4-1 Security Issues in Mobile Payments Electronic ID Application. 20