Defeating SSL and

“Defeating SSL”
Impact of Hash collisions on cyber security
By vaibhav
Secure Sockets Layer
2
Objective
• Background Information of SSL , MD5 &
“Certificate”\”Public Key” Infrastructure
• Attack scenario on core assumption of SSL i.e. collision resistance of hash function
• Attack scenarios on the specification\ implementation of SSL
3
when in doubt , ask
4
5
Cryptographic Hash
• Serves an essential role within a wide range of security applications.
• Like
(a) digital signature generation and verification
(b) session key establishment
(c) management of password schemes
(d) commitment schemes in cryptographic protocols
6
Hash Functions
• Compress an arbitrary finite length m-bit input message into a fixed n-bit output value called hash.
hash
Data
Message
Digest if h = H(m) then,
• h is called the "hash" of m,
• m is called a "preimage" of h
7
Properties of (good)Hash
Function
• (practicality) computation of hash can be done efficiently
• (preimage resistance) given h, it is hard to compute a preimage of h
• (second preimage resistance) given m, it is hard to compute a second preimage of m
• (collision resistance) it is hard to compute a collision for H
8
Lets talk about SSL first
• Ensures secrecy ,authenticity, and integrity.
• Safeguarding communication from both the passive and active adversaries.
• SSL rely heavily on the x509* certificate structure.
• For SSL protocols , it is the “common name” field in the subject of an x509 certificate that is used to identify entities presenting certificates.
9
X509 ? Digital certificates ?
What ?
• ITU-T standard for the public key infrastructure.
• X.509 specifies standard formats for public key certificates
• Public key certificates are structured according to version3 of X.509 specification.
• A public key certificate uses a digital signature to bind a public key with an identity.
10
11
Certification Authorities & Hierarchy
• Browsers ship with a list of trusted CA certificate.
o Firefox 3 includes 135 trusted CA certs.
• CAs’ responsibilities: o verify the identity of the requestor o verify domain ownership for SSL certs o revoke bad certificates
12
Check
Signature
Signin CA in trust store
Check
Expiry
CN Site Name
13
Root CA
Intermediate I
CA
What if …
Hack.org is a valid certificate issued by intermediate II CA
What if hack.org issues a certificate for richest-bank.com ?
Intermediate
II CA
Chain verification algorithm as described before would validate this certificate too.
Hack.org
Richest-bank.com
14
Something must be wrong, but...
• All the signatures are valid.
• Nothing has expired.
• The chain is intact.
• The root CA is embedded in the browser and trusted.
But we just created a valid certificate for Richestbank, and we're not Richest-bank?
15
X509v3 extensions provide a extension to tackle with this.
Basic Constraints: critical CA:FALSE
But …
• Most CAs didn't explicitly set basicConstraints: CA=False
• Whether the field was there or not, most SSL implementations didn't bother to check it.
Hacker moxie marlinspike a tool, sslsniff, to attack this vulnerability.
Eventually Microsoft released a patch to address this issue.
16
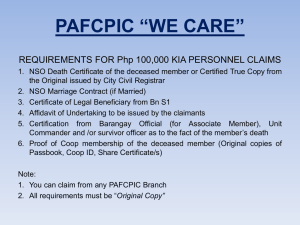
Obtaining certificates
User
User installs private key and certificate on a web server
Public Private
Key pair generation
Create and signs certificate
User Identity CSR generated
Validates user identity and domain ownership
Domain name
Public Key
CSR sent to CA
17
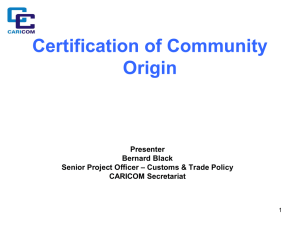
Certificate request format
18
Certificate structure
• the "to-be-signed" part, consisting of: o serial number o validity period o issuer name o subject o subject public key o "basic constraints" field, containing
• a bit indicating whether this is a CA certificate or a user certificate
• a path length field
• the "signature" part, containing a digital signature, produced by CA`s private key, over the "to-besigned“ part
19
20
Secure websites and certificates
21
Attack Scenario using Rogue
CA certificate
22
23
Revisiting MD5 and MD5
Collision
24
Overview of MD5
Hash function MD5 designed in 1991
• Iterative design using compression function.
• Collision different messages , same hash
25
MD5 Collisions in 2004
2004: First MD5 collision attack
• Only difference between messages in random looking 128 collision bytes
• Currently < 1 second on commodity PC
MD5( ) = MD5( )
26
27
MD5 Collisions in 2007
2007: Stronger collision attack
• Chosen-Prefix Collisions
• Messages can differ freely up to the random looking 716 collision bytes
• Currently approx. 1 day on PS3+PC
MD5( ) = MD5( )
28
29
Generating Colliding
Certificates
30
History of colliding certificates
Certificates with colliding to-be-signed parts
• generate a pair of certificates
• sign the legitimate certificate
• copy the signature into the rogue cert
Previous work
• Different RSA public keys in 2005 o using 2004 collision attack
• Different identities in 2006 o using chosen-prefix collisions o the theory is well known since 2007
31
Colliding certificates in 2006
32
Rogue CA certificate
CA bit
33
Action Items for generating hash colliding certificates
• Find CA which issues MD5 signed certificate
• Predict the Validity and Serial Number
• Construct structure and content rogue Certificate such that real certificate( constructed by CA) and rouge CA cert(Constructed by Hackers) are perfectly aligned.
• Compute the collision blocks
• Create RSA key pair such that it includes collision block in it.
• Construct CSR and send it to CA for signing
Detailed view
34
Why RapidSSL?
• Out of 9000 MD5 certificates collected 97% of those were issued by RapidSSL.
• RapidSSL issues exactly 6 seconds after “accept” button is clicked and expires in one year.
• RapidSSL uses sequential serial numbers and on weekend approximately 1000 certificates are issued.
35
Predicting the serial number
• Get the serial number S on Friday
• Predict the value for time T on Sunday to be S+1000
• Generate the collision bits
• Shortly before time T buy enough certs to increment the counter to S+999
• Send colliding request at time T and get serial number S+1000
36
Collision generation and
RSA keys
• Based on the 2007 chosenprefix collisions paper with new improvements
• 1-2 days on a cluster of 200
PlayStation 3’s
• Equivalent to 8000 desktop CPU cores or $20,000 on Amazon
EC2
• takes couple of minutes to calculate RSA key pair such as it contains collision blocks
37
Another Attack on SSL
38
Background
• As mentioned earlier SSL handshake uses “common name” of certificate and compares with site name.
• Before year 2000 actual people were involved while dealing with certificate request.
• Entities are validated based on proof of ownership of the domain listed in the “common name” field.
• Now a days a simple lookup in WHOIS database for the root domain listed and sending a confirmation mail would complete the verification part.
39
ASN1.0 and Certificates
• Certificates are formatted using ASN1.0 notation.
• Supports different type of strings, all represented as
PASCAL strings.
• Represented in memory by the length of the string followed by the string data.
• NULL character has no special meaning, like C strings
Example :
0x05
(length)
0x44 ( D ) 0x41 (A ) 0x00
(NULL)
0x54 ( T ) 0x41 ( A )
40
Malformed Request
• One can create a certificate request with common name as www.richest-bank.com\0www.hack.com
• CA for verification would do WHOIS
• issues the certificate with embedded NULL to the owner of hack.com.
• Spoof www.richest-bank.com
and use NULL embedded certificate
41
Defeating SSL
• This is how comparison function would be implemented for CN verification.
char *destination = getDomainWeAreConnectingTo(); char *commonName = getCommonNameFromCertificate();
Bool everythingIsOk = (strcmp(destination, commonName) == 0); char *commonName w w w .
b a n k .
c o m /0 w w w char *destination w w w .
b a n k .
string match c o m /0
42
Question ?
43
References
• http://www.win.tue.nl/hashclash/rogue-ca/
• http://conf.isi.qut.edu.au/auscert/proceedings/200
6/gauravaram06collision.pdf
• https://www.blackhat.com/presentations/bh-dc-
09/Marlinspike/BlackHat-DC-09-Marlinspike-
Defeating-SSL.pdf
44