Chapter 23 - OpenLoop.com
advertisement
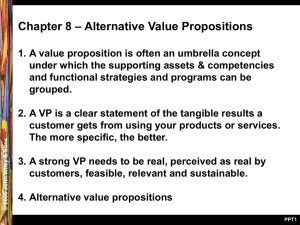
Software Engineering Modern Approaches Eric Braude and Michael Bernstein 1 Chapter 23: 23 Quality and Metrics in Implementation © 2010 John Wiley & Sons Ltd. 2 Table 1: Rough measures of quality of an implementation Planning Maintenance Testing The Software Development Requirements Lifecycle analysis Implementation Design Phase most relevant to this chapter is shown in bold © 2010 John Wiley & Sons Ltd. Learning Goals of This Chapter • How do you assess the degree of sufficiency of an implementation? • How do measure the degree of robustness? • What metrics are there for flexibility? • Reusability? Efficiency? Reliability? Scalability? • How does one assess the degree of security of an implementation? • How do code inspections improve code quality? Code reviews? • How does pair programming improve 3 code quality? Rough Measures of Quality of an Implementation Degree of Rough metric … 0 … sufficiency robustness flexibility reusability 10 (maximum score) Fails to implement the corresponding design specification Satisfies all of the design specifications for this element Will cause crash on any anomalous event Recovers from all anomalous events as well as can be expected Will have to be replaced entirely if the design or requirements change As easily adaptable to reasonable changes as can be expected Cannot be used in other applications Usable in all reasonably related applications without modification Fails to satisfy speed or data storage requirement efficiency reliability scalability security Satisfies speed or data storage requirement with reasonable margin Obviously won’t achieve required mean time between failure Obviously will achieve required mean time between failure Can’t be used as the basis of a larger version Is an outstanding basis for a version with much larger scope Security not accounted for at all No known manner of breaching security is known 4 © 2010 John Wiley & Sons Ltd. Supporting and Competing Implementation Qualities robustness security reliability scalability flexibility efficiency Key: usually competes: © 2010 John Wiley & Sons Ltd. reusability usually supports: 5 Assessing the Robustness of a Method 1. Assess input to the method a. Anomalous parameter values b. Anomalous global variables c. Anomalous event variables 2. Assess dependent methods Measure extent of compromise © 2010 John Wiley & Sons Ltd. 6 A Robustness Metric for Classes Scale: 0 TO 1 A metric for each method: No robustness = 0, some = 0.5, complete = 1. A metric for classes (degree of method’s robustness on scale of 0 to 1) all methods Number of methods © 2010 John Wiley & Sons Ltd. 7 Implementation Factors Which Increase Flexibility 1 1. Document precisely and thoroughly – Reason: cannot adapt code that you don’t understand 2. Name constants – Reason: understandability 3. Hide where possible – – Variables and methods Reason: reducing complexity increases understanding 4. Collect common code – – As helper methods and classes Reason: reduce complexity © 2010 John Wiley & Sons Ltd. 8 Implementation Factors Which Increase Flexibility 2 5. Reduce dependency on global variables -- and on any variables external to the method – Parameterize methods – Reason: allows method to be used in other contexts 6. Program at a general level – Reason: applies to more situations 7. Use understandable variable and function names © 2010 John Wiley & Sons Ltd. 9 Naming Variables and Constants Poor Better Best Dose mDD dailyDosage maxDailyDosage minDailyDosage commonDailyDosage 10 © 2010 John Wiley & Sons Ltd. Metrics for Various Attributes of An Implementation Attribute Metric 1. Degree of documentation a) Percentage of comment lines b) Percentage of commented lines 2. Extent of named constants Percentage of numerals with names (see Note 1) 3. Hide where possible a) Standard deviation of class size (see Note 2) b) Standard deviation of method size 4. Degree to which common code is collected Percentage of repeated code paragraphs (see Note 3) 5. Degree of dependency on global variables a) Percentage of public fields b) Percentage of protected fields c) Percentage of unlabeled fields 6. Degree of generic programming Percentage of generic classes 7. Use understandable variable Percentage of names clearly difficult to understand and function names © 2010 John Wiley & Sons Ltd. 11 Security Challenges for Simple Login • Store ID’s and passwords without allowing unauthorized access • Ensure that data goes only to authorized requesters • Design so that security is easily maintained as application evolves – Isolate security-affecting classes? © 2010 John Wiley & Sons Ltd. 12 Security Metrics • Confidentiality: Measure by degree of difficulty ... gaining disallowed access to information • Nonrepudiation: ... repudiating agreement • Integrity: ... altering data in transit, undetected • Authentication: ... verifying identity • Authorization: ... gaining disallowed access to a location 0=easy; 1=not easy but conceivable; 2=not conceivable © 2010 John Wiley & Sons Ltd. 13