WiMAX poster
advertisement
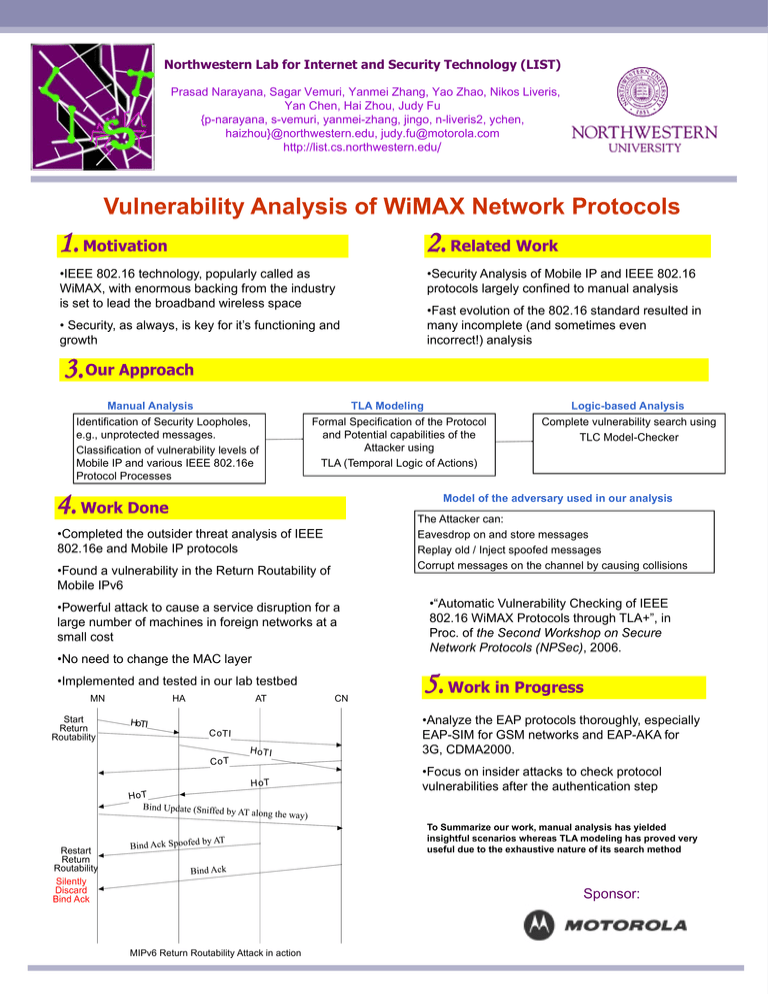
Northwestern Lab for Internet and Security Technology (LIST)
Prasad Narayana, Sagar Vemuri, Yanmei Zhang, Yao Zhao, Nikos Liveris,
Yan Chen, Hai Zhou, Judy Fu
{p-narayana, s-vemuri, yanmei-zhang, jingo, n-liveris2, ychen,
haizhou}@northwestern.edu, judy.fu@motorola.com
http://list.cs.northwestern.edu/
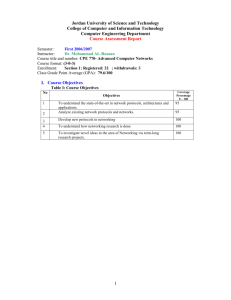
Vulnerability Analysis of WiMAX Network Protocols
1. Motivation
2. Related Work
•IEEE 802.16 technology, popularly called as
WiMAX, with enormous backing from the industry
is set to lead the broadband wireless space
•Security Analysis of Mobile IP and IEEE 802.16
protocols largely confined to manual analysis
•Fast evolution of the 802.16 standard resulted in
many incomplete (and sometimes even
incorrect!) analysis
• Security, as always, is key for it’s functioning and
growth
3. Our Approach
Manual Analysis
TLA Modeling
Identification of Security Loopholes,
e.g., unprotected messages.
Classification of vulnerability levels of
Mobile IP and various IEEE 802.16e
Protocol Processes
Formal Specification of the Protocol
and Potential capabilities of the
Attacker using
TLA (Temporal Logic of Actions)
4. Work Done
Complete vulnerability search using
TLC Model-Checker
Model of the adversary used in our analysis
The Attacker can:
Eavesdrop on and store messages
Replay old / Inject spoofed messages
Corrupt messages on the channel by causing collisions
•Completed the outsider threat analysis of IEEE
802.16e and Mobile IP protocols
•Found a vulnerability in the Return Routability of
Mobile IPv6
•Powerful attack to cause a service disruption for a
large number of machines in foreign networks at a
small cost
•No need to change the MAC layer
•Implemented and tested in our lab testbed
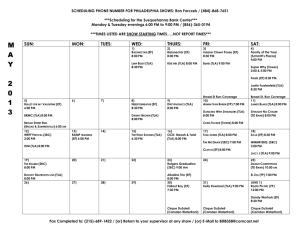
MN
Logic-based Analysis
HA
AT
CN
•“Automatic Vulnerability Checking of IEEE
802.16 WiMAX Protocols through TLA+”, in
Proc. of the Second Workshop on Secure
Network Protocols (NPSec), 2006.
5. Work in Progress
•Analyze the EAP protocols thoroughly, especially
EAP-SIM for GSM networks and EAP-AKA for
3G, CDMA2000.
Start
Return
Routability
•Focus on insider attacks to check protocol
vulnerabilities after the authentication step
To Summarize our work, manual analysis has yielded
insightful scenarios whereas TLA modeling has proved very
useful due to the exhaustive nature of its search method
Restart
Return
Routability
Silently
Discard
Bind Ack
Sponsor:
MIPv6 Return Routability Attack in action