ITAF-Approach-to-IT-Audit-Advisory-Services whpitafaas whp Eng 1020
advertisement

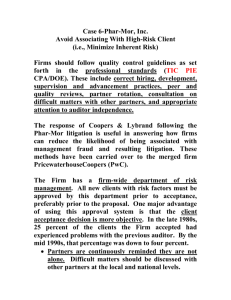
An ITAF™ Approach to IT Audit Advisory Services Audit © 2020 ISACA. All Rights Reserved. 2 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES CONTENTS 4 Introduction 4 Background 5 Auditors’ Consulting and Advisory Roles Before Sarbanes-Oxley 6 Sarbanes-Oxley’s Influence on Internal IT Auditors’ Roles as Advisors 7 Challenges to IT Auditors as Advisors and How ITAF Can Help 7 / Impaired Independence 8 / Impaired Objectivity 9 / Professional Skepticism 10 Benefits of IT Auditors in Advisory Roles 10 Current Landscape 11 Conclusion 12 Acknowledgments © 2020 ISACA. All Rights Reserved. 3 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES ABSTRACT Business scandals encompassing accounting, audit and governance date back to the 1960s and earlier. The early 2000s, however, were particularly hard hit with a number of highly publicized financial frauds at large companies. Do WorldCom, Adelphia Communications, Enron and Tyco sound familiar? In the United Kingdom, collapse of construction and facilities management giant Carillion raised similar financial fraud concerns, as did audit allegations related to the prominent Gupta family in South Africa. As a result of these and other events, the role of public auditors and their achievement and maintenance of independence rose to the forefront as a global area of concern. In the United States, the Securities and Exchange Commission (SEC) became involved. While internal IT auditors are not subject to SEC rules, the SEC’s independence guidance given to public auditing firms became (and continues to be) a source of best practices for internal IT auditors. In its Information Technology Audit Framework (ITAF™), ISACA provides additional guidance for IT auditors as they contemplate participation in advisory services. This white paper explores challenges to the principles of independence and objectivity, and how ITAF can resolve them. © 2020 ISACA. All Rights Reserved. 4 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES Introduction With the pace of digital transformation, IT auditors may are finding their roles within an enterprise shifting; they are find themselves at a crossroads. Not only do they need to being asked to provide their expertise in an advisory or keep up with new technologies, but they are being asked consultative capacity. While these shifts in roles allow IT to advise on whether those technologies should be auditors to remain relevant, they also raise potential adopted, and what controls are needed for the newly objectivity and independence concerns. How did IT audit adopted technologies. With automation, some auditors get here? Background In 1996, the residents of Clinton, a small town in Mississippi, Fast-forward to 2002. The WorldCom scandal is closely USA, were excited because a new employer was establishing associated with the Sarbanes-Oxley Act of 2002, the operations in their town. The town’s excitement would prove federal legislation that created the Public Company to be justified: the new employer in town was WorldCom, and Accounting Oversight Board (PCAOB).3 WorldCom’s in 1998 and 2002, WorldCom was the second largest demise though, through its bankruptcy filing on 19 July 1 telecommunications company in the United States. 2002, was well after the introduction of the Sarbanes- However six years after opening its office in Clinton, Oxley Act to Congress in February 2002.4 The reality is WorldCom would be at the center of a business scandal that that a pattern of concerns regarding public accounting encompassed accounting, audit and governance and independence had been forming for decades. Steven improprieties. In fact, 30,000 employees eventually would B. Harris, who served as staff director and chief counsel lose their jobs, and investors would experience losses of for the Senate Banking Committee chaired by Sen. Paul $180 billion.2 The people of Clinton could not have predicted Sarbanes and later served as a board member of the how the WorldCom saga would unfold. PCAOB, observed the following (figure 1):5 3 1 4 2 5 FIGURE 1: Timeline of Accounting and Independence Events Time Period 1970s Event Continental Vending Company (United States v. Simon)6 : Financial auditors were aware, but did not disclose, that Continental’s president had a loan with an affiliated company that was unable to repay Continental. This case was groundbreaking in that the auditors involved were charged in criminal court as well as civil court.7 6 7 1980s ESM Government Securities Inc. (ESM): An auditor of ESM-produced financial statements indicated that ESM was profitable when the auditor knew that the company was not profitable.8 1990s Cendant Corporation: Results of a forensic audit indicated that Cendant Corporation overstated its revenues and pretax income by $500 million over a three-year period.9 2000s Multiple fraud incidents: In addition to WorldCom, enterprises involved in financial fraud included Adelphia Communications, Enron and Tyco. 8 9 1 2 3 4 5 6 7 8 9 WorldCom Fraud, “Background: Introductory Information about WorldCom Fraud,” https://WorldComfraud.weebly.com/background.html Accounting Degree Review, “The 10 Worst Corporate Accounting Scandals of All Time,” www.accounting-degree.org/scandals/ Congress.gov, Public Law 107-204, 30 July 2002, www.congress.gov/107/plaws/publ204/PLAW-107publ204.pdf 4 Congress.gov, H.R. 3763 Sarbanes-Oxley Act of 2002, 30 July 2002, www.congress.gov/bill/107thcongress/house-bill/3763 5 Harris, S.; “The Future of Government Involvement in Public Accounting,” PCAOB, 20 October 2011, https://pcaobus.org/News/Speech/Pages/ 10252011_HarrisSpeech.aspx 6 United States v. Simon, US Court of Appeals, 2nd Cir., 425 F.2d 796 7 Whittington, R.; K. Pany; Principles of Auditing & Other Assurance Services, Twentieth Edition, McGraw-Hill Education, USA, 2016 8 Edwards, J.; “ESM Auditor Feared for Career,” Florida Sun Sentinel, 29 October 1986, www.sun-sentinel.com/news/fl-xpm-1986-10-29-8603060551-story.html 9 Rimkus, R.; “Cendant Corporation,” CFA Institute, 29 November 2016, www.econcrises.org/2016/11/29/cendant-corporation/ 1 2 3 © 2020 ISACA. All Rights Reserved. 5 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES Financial frauds were not limited to the United States. In the Carillion, a large construction and facilities management UK, for example, there were events that highlighted the role company. Failure of the enterprise was largely attributed to of public auditing when failures to report or missed aggressive accounting practices and warning signs around observations—whether intentional or unintentional— enabled profit that Carillion’s public accounting firm either did not fraud. One of the most notable cases was the bankruptcy of observe or observed but did not report. Auditors’ Consulting and Advisory Roles Before Sarbanes-Oxley Prior to the Sarbanes-Oxley Act of 2002 (Sarbanes-Oxley or This scenario is from 1972, well before the 2002 SOX), public accounting firms conducted audits of financial enactment of Sarbanes-Oxley. It is, however, an example statements and also provided nonaudit (i.e., consulting or of the environment at that time. Then, like now, the advisory) services. During that time, nonaudit services were performance of nonaudit services by public accounting performed under the guidance of the Securities Act of 1933 firms appeared reasonable. Through audit planning and (Act 1933) and the Securities Exchange Act of 1934 (Act conducting audits for the same clients year after year, 1934). If public auditors had questions that did not appear to auditors had become very familiar with their clients’ be addressed in Act 1933/Act 1934, generally accepted strategic objectives, internal control environments and accounting principles (GAAP), or generally accepted auditing operations. By having these auditors perform nonaudit standards (GAAS), the auditors would contact the United services, an enterprise could benefit by eliminating the States Securities and Exchange Commission (SEC) for time typically required for a consultant to become familiar feedback on the appropriateness of the nonaudit services with its operations. From the perspective of the public they wanted to provide. The SEC published responses to accounting firms, providing nonaudit services for existing those inquiries in its Accounting and Auditing Enforcement audit clients was an opportunity to strengthen client Releases to publicize its position. relationships and to generate additional revenue. While not legally binding, the SEC’s responses were based The public accounting firms were not the only ones to on federal law. An example of an SEC response relates to observe that nonaudit services generated additional a scenario where a public accounting firm, using its own revenue. The SEC also noticed that revenue stream. computer, performed data-processing activities for its Having learned of potential adverse effects to client. The work included restating accounts and making independence through questions received from firms, the corrections based on the restatement. Since the public SEC was aware of—and concerned about—an auditor’s accounting firm was maintaining client records that it ability to maintain independence when nonaudit services would likely audit in the future, the SEC opined that were provided. That concern was well-founded. In its independence had been adversely affected. review of audit fees in 2002, the year Sarbanes-Oxley was 10 10 11 10 11 10 11 11 US Securities and Exchange Commission, Accounting and Auditing Enforcement Releases, www.sec.gov/divisions/enforce/friactions.shtml US Securities and Exchange Commission, Accounting Series Release No. 126, 5 July 1972, Accounting Series Releases: Compilation of Releases to 195 As In Effect August 1976 © 2020 ISACA. All Rights Reserved. 6 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES passed, Audit Analytics published data indicating that for significant percentage of public accounting fees accelerated filers, nonaudit fees comprised 48.5% of the combined with a lack of clarity around public firm total public accounting fees paid (figure 2).12 SEC independence placed auditor independence and awareness that nonaudit service fees comprised a objectivity in the spotlight. 12 FIGURE 2: Audit and Nonaudit Fees (Including Audit-Related Fees) as a Percentage of Total Fees 72.8% 78.5% 79.9% 78.4% 78.8% 79.7% 78.0% 78.3% 78.1% 78.3% 78.2% 78.0% 79.0% 58.4% 51.5% 48.5% 41.6% 27.2% 2002 2003 2004 21.5% 20.1% 21.6% 21.2% 20.3% 22.0% 21.7% 21.9% 21.7% 21.8% 22.0% 21.0% 2005 2006 2007 2008 2009 2010 2011 2012 2013 2014 2015 2016 Source: McKeon, J.; “A Fifteen-Year Review of Audit Fees,” Audit Analytics, 4 January 2018, https://blog.auditanalytics.com/a-fifteen-year-review-of-audit-fees/ Sarbanes-Oxley’s Influence on Internal IT Auditors’ Roles as Advisors How does this backstory in the public auditing world services without jeopardizing the ability to perform future intersect with the role of the IT auditor as an advisor? engagements independently? Sarbanes-Oxley provided financial accounting guidance in response to fraud scandals like WorldCom. However, it The US Sarbanes-Oxley Act is not the only instance of government action being taken to address public also provided guidance for the potential challenges accounting concerns. In the UK, for example, the Financial associated with the performance of advisory services. As Reporting Council (FRC) was created to perform a role public accounting firms and IT auditors reviewed the SOX similar to the PCAOB that was formed through SOX. The guidance, they identified a common need. How could they FRC provides oversight of auditors, accountants and support their clients or enterprises through advisory actuaries.13 12 13 12 13 13 McKeon, J.; “A Fifteen Year Review of Audit Fees,” Audit Analytics, 4 January 2018, https://blog.auditanalytics.com/a-fifteen-year-review-of-audit-fees/ Financial Reporting Council, “About the FRC,” www.frc.org.uk/about-the-frc © 2020 ISACA. All Rights Reserved. 7 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES Challenges to IT Auditors as Advisors and How ITAF Can Help Those familiar with information security are probably aware Accepted Governance Audit Standard (GAGAS)16 states of the security principles embodied in the CIA triad: that GAGAS does not apply to what it references as 16 confidentiality, integrity and availability. The triad is a model nonaudit services. Specifically, the audit function would that is used as a basis for security policies and practices. have to clearly state to management that the work being 14 14 The performance of advisory services could easily have a performed was not an audit, and that its nonaudit services similar triad built on the principles of independence, were not performed in accordance with GAGAS.17 objectivity and professional skepticism (figure 3). 17 Assuming, however, that an enterprise is not subject to a FIGURE 3: Advisory Services Triad restriction similar to GAGAS, and that the enterprise’s services, practitioners can rely on ITAF. ITAF includes: tiv • ity Advisory Services Triad jec Ob Ind ep en de nc e audit charter authorizes IT auditors to perform advisory Perspectives on how to minimize potential impairment of independence or objectivity • Professional Skepticism Advice on how professional skepticism can assist the auditor in the performance of advisory services These principles, which are described in ISACA’s Information Technology Audit Framework—ITAF™15 can Impaired Independence form the basis of a model that addresses challenges to ITAF looks at independence from a functional- and the IT auditor’s ability to function in an advisory role. ITAF administrative-reporting relationships view that ensures is a comprehensive IT audit framework that: the IT auditor is not unduly influenced by the enterprise 15 • Establishes standards that address IT audit and assurance being audited, its managers or employees. On occasion, practitioners’ roles and responsibilities, ethics, expected the IT auditor’s expertise in a particular area may result in professional behavior, and required knowledge and skills management seeking advice. Providing this routine advice • Defines terms and concepts specific for IT audit and assurance on IT risk or controls is viewed as assisting management • Provides guidance, tools and techniques for the planning, in the performance of its duties, not assuming performance and reporting of IT audit and assurance managerial duties. Consequently, there is no impairment engagements to independence. If, however, the IT auditor is called If the IT auditor is subject to standards from an entity upon to make management decisions, the auditor other than ISACA, the IT auditor should confirm that may be influenced by senior management or the entity’s expectations regarding advisory services. For executive level of the enterprise. As a result, independence example, the Government Accountability Office’s General may be impaired. 14 15 16 17 Fruhlinger, J.; “The CIA triad: Definition, components and examples,” CSO, 10 February 2020, www.csoonline.com/article/3519908/the-cia-triad-definitioncomponents-and-examples.html 15 ISACA, IT Audit Framework (ITAF™): A Professional Practices Framework for IT Audit, 4th Edition, www.isaca.org/bookstore/audit-control-and-securityessentials/witaf4 16 GAO, Comptroller General of the United States, Government Auditing Standards, July 2018, www.gao.gov/assets/700/693136.pdf 17 Gutierrez, M.;360° Best Practices® & Methodology, “The Internal Auditor as a Consultant in the Organization,” 3 August 2017, https://360bestpracticesmethodology.wordpress.com/2017/08/03/the-internal-auditor-as-a-consultant-in-the-organization/ 14 © 2020 ISACA. All Rights Reserved. 8 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES Examples of activities that could involve management appears not to impair independence and the IT auditor decisions include: begins the engagement, the IT auditor should remain • Setting policies and strategic direction mindful of undue influence, another potential impairment • Directing and taking responsibility for the actions of the entity’s to independence. Should impairment occur after the employees engagement is initiated, the IT auditor should immediately • Authorizing transactions discuss the issue with IT management and the enterprise • Deciding which recommendations of the audit function, internal governance and oversight function. audit function, organization, firm or other third parties to Impaired Objectivity implement • Taking responsibility for designing, implementing or maintaining internal controls • Accepting responsibility for the management of an IT project or To avoid impairment to independence, the IT auditor should have a clear understanding of what any proposed advisory services entail. ITAF recommends Impairments to independence can be identified easily through exploration of the IT auditor’s involvement in managerial activities. Impaired objectivity may be more difficult to identify, however, because of its broader scope. It may involve several elements, such as: • documentation of the advisory service with IT audit Potential for self-review—Should advisory services performed by the IT auditor become the subject of an audit or an management (and/or those charged with assurance engagement also performed by that individual, the IT governance) regarding: auditor would be involved in self-review. This may happen when • The objectives of the advisory services or roles the IT auditor has expertise in a particular area and • The nature of the advisory services or roles to be performed management has a challenge in that area or wants to launch a • The audited entity’s acceptance of its responsibilities related to related project. In this example, the auditor may be asked to the advisory services or roles perform an advisory service. If the IT auditor is asked to assess Professional responsibilities related to the advisory services or that area, objectivity could be impaired for an audit conducted roles either concurrently or at a future date. ITAF recommends that • Any limitations of the advisory services or roles the IT auditor not perform advisory services in an area in • Any limitations to the scope of future audit services which the auditor is currently performing an audit. This practitioners can provide recommendation also applies to advisory services that may • • initiative 18 19 18 become the subject of an audit in the future.21 19 • On occasion, the IT auditor’s expertise in a particular area may result in management seeking advice. Providing this routine advice on IT risk or controls is viewed as assisting management in the performance of its duties, not assuming managerial duties. 21 Auditor-driven interactions that could impair the auditor’s objectivity—For auditor-driven interactions, the auditor is deemed as having some level of control over the potential impairment to objectivity. For example, it is not unheard-of for an auditor to pursue a transfer from audit to an operational IT If the advisory services can result in any impairment of role. While performing advisory services, it may become evident independence (in fact or in appearance), the IT audit that both the IT auditor and the operational IT area would function should discuss the potential impairment with benefit from the auditor changing roles within the enterprise. those charged with governance and oversight of the audit The change could possibly align with enterprise needs and function (e.g., the board of directors and/or the audit definitely meet the auditor’s career aspirations. Even with the committee).20 If the description of advisory services passage of an appropriate period of time between the 20 18 19 20 21 Ibid. Op cit ISACA Ibid. 21 Ibid. 19 18 20 © 2020 ISACA. All Rights Reserved. 9 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES performance of the advisory services and performance of an between exercising professional skepticism to avoid audit, the IT auditor may perceive that a career opportunity may independence or objectivity impairment and ‘not making be jeopardized if unfavorable findings in the audit are reported. waves’ should opt for preservation of independence This vested interest in preserving the relationship with IT and objectivity. operations management could impair objectivity. • Management-driven interactions that could impair the auditor’s objectivity—IT operations management may also drive impairment to objectivity. For example, if management develops The IT auditor should recognize that in some environments, professional skepticism is encouraged in principle, but not supported in practice. and maintains a close relationship with the IT auditor For advisory services, professional skepticism takes on performing advisory services, there is potential for the additional importance because it can help the auditor interaction to become more than a collaborative relationship. It navigate circumstances that may lead to impairment of can create familiarity at a level that precludes the IT auditor independence or objectivity. Even if participation in an from being objective when the auditor subsequently resumes advisory engagement has been vetted and approved, the audit work in the area. This impaired objectivity may range from IT auditor benefits from continuing to question the work management seeking a sympathetic ear from the auditor to that is to be performed. The description of the project enlisting the auditor as its advocate. provided prior to the start of the advisory services may To address these circumstances, if an auditor’s interest in a possible transfer to an operational IT role is known, the IT auditor should not perform audits in that particular area. Also, ITAF advises the IT audit function to rotate audit assignments periodically to mitigate familiarity appear to be free of any potential impairment. Once the work begins, however, the auditor should ensure that particular tasks (either unknown or undisclosed in the overall project description) do not impair (or appear to impair) independence and/or objectivity. between auditors and management. Further, an IT auditor To recap, prior to participating in an advisory service, the who performed direct management responsibilities in any IT audit function should determine that its intended given area should not audit that area. participation complies with the terms of its audit charter. 22 22 If there are circumstances where the IT auditor’s Professional Skepticism participation in advisory services gives the enterprise’s audit Unlike independence and objectivity, which can be committee pause, consideration should be given to the: impairments, professional skepticism is a potential • safeguard. In the audit realm, professional skepticism is Perception of the relative value added by the potentially conflicting audit and advisory services most frequently associated with the auditor making a • Level of risk attached to advisory activities to be performed critical assessment of audit evidence. ITAF requires the • Effect on how the IT audit function is perceived should the IT auditor to have a questioning mind and demonstrate professional skepticism. auditor perform the advisory services • Professional skepticism is a skill that the IT auditor uses Nature, timing and extent of the advisory services to be performed by the IT auditor in audit and assurance engagements. Similar to these If concerns surrounding the IT auditor’s participation in engagements, exercising professional skepticism during advisory services cannot be resolved, the audit function advisory services means asking the right questions. The should explore the potential of recruiting alternative IT auditor should recognize that in some environments, resources, either for the audit the IT auditor would professional skepticism is encouraged in principle, but not normally perform or for the advisory services work. ITAF’s supported in practice. An IT auditor faced with a choice general guidelines on proficiency (Section 2006) 22 22 Ibid. © 2020 ISACA. All Rights Reserved. 10 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES encourage IT auditors to gain reasonable assurance that auditor should collaborate with the alternative resources the work is outsourced only to experts possessing the to facilitate personal development of knowledge and skills required professional competence. Furthermore, the IT in the outsourced area. Benefits of IT Auditors in Advisory Roles Having identified and mitigated any challenges associated auditor to contribute directly to achievement of strategic with the IT auditor’s performance of advisory services, it is objectives, which has the potential to elevate the audit valuable to identify the benefits of this role. Involvement in function’s value within the enterprise. advisory services can be an opportunity to highlight the audit function’s contribution to the enterprise. For The audit function can also benefit as an IT auditor’s example, during an audit, a control is observed and a advisory work results in better understanding of conclusion is reached on control design and execution. operations. This insider view is useful in planning future While audits are not always binary (i.e., one of two risk assessments and audits of the subject area. As this possible outcomes), they are relatively straightforward in better understanding is shared and additional auditors terms of validation. The validation process may grant IT learn more about the area in which advisory services auditors an opportunity to identify risks or control were performed, the audit department gains more options weaknesses that may delay or hinder an enterprise’s for staff assignments to audit the area. If the subject area achievement of its strategic objectives. This is a valuable is truly specialized, the knowledge transfer can facilitate contribution. Advisory services, however, allow the IT succession planning or address key-person dependency. Current Landscape In light of the background of advisory services and best this new allowance expands the independence attribute practices for performing them, what does the current from two (impaired, unimpaired) to three (impaired, environment look like? In December 2019, the SEC unimpaired, not substantially threatened), it by no means proposed amendments to Rule 2-01 that would affect diminishes the importance of independence. public auditor independence.23 Prior to this proposed rule, For example, in September 2019, the SEC enforced its rule 23 independence either existed or it was impaired. Under the prohibiting public firms from designing and/or proposed rule, the SEC makes allowances for implementing systems that are significant to an audit relationships between public auditors and clients where independence is not “substantially threatened.” 23 24 23 24 24 24 While client’s financial statements in an action involving PricewaterhouseCoopers. The enforcement specifically US Securities and Exchange Commission, “Amendments to Rule 2-01, Qualification of Accountants,” Proposed amendments to 17 CFR Part 210, 30 December 2019, www.sec.gov/rules/proposed/2019/33-10738.pdf Tysiac, K.; “SEC proposes updating auditor independence rules,” Journal of Accountancy, vol. 2 January 2020, www.journalofaccountancy.com/news/ 2020/jan/sec-proposes-auditor-independence-rules-update-22727.html © 2020 ISACA. All Rights Reserved. 11 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES addressed IT and other advisory services performed threatened). At the same time, however, the for audit clients and resulted in a $7.9 million PricewaterhouseCoopers settlement is evidence that there settlement. are some elements of independence that are so critical for 25 25 The proposed SEC amendments to Rule 2-01 demonstrate that independence is an area of interest that continues to be evaluated. As these evaluations occur, it seems that some new philosophies on the principle of independence may be introduced (e.g., the new attribute of not substantially maintaining confidence in the audit process that they must continue to be enforced. It will be helpful for IT auditors to monitor these types of changes in the public auditing sector as they consider best practices for their involvement in advisory engagements. Conclusion In day-to-day work, public auditors and internal auditors may Prior to engaging in advisory services, the IT auditor and view their auditees as their clients. While this is true, the audit IT management can: profession’s ultimate clients are external stakeholders (i.e., • Use discussion points available in ITAF to assess whether investors in public companies and recipients of services participating in the advisory service engagement impairs the provided by nonprofits). Thus, IT auditors should consider auditor’s independence or objectivity. These discussion points advisory services through the lens of an external stakeholder. provide a foundation for IT audit management to make an Would performance of a particular advisory service give a informed decision on whether to accept the offer to provide reasonable stakeholder pause? Would the stakeholder advisory services. question the IT auditor’s independence or objectivity in • conducting audit and assurance engagements given the involvement in advisory services? Identify any potential impairment, and determine if it can be eliminated or reduced to an acceptable level. • Assess whether a tactical solution such as staff rotation addresses a potential impairment of independence or objectivity. As the SEC’s recent reinforcement action with PricewaterhouseCoopers and its proposed amendments to Rule 2-01 indicate, independence and advisory services • Ensure that the existing skill of professional skepticism is a tool that is relied upon when participating in advisory engagements. remain a relevant topic. In addition to guidance from Remembering the external stakeholder and the stakeholder’s external entities and frameworks such as the SEC and perception on whether independence or objectivity has been GAGAS, there is ITAF guidance to assist IT auditors in impaired is a valuable part of making decisions when IT making self-assessments in this area. auditors participate in advisory engagements. 25 25 Heller, M.; “PwC Fined $7M for Audit Independence Violations,” CFO, 24 September 2019, www.cfo.com/accounting-tax/2019/09/pwc-fined-7m-for-auditindependence-violations/ © 2020 ISACA. All Rights Reserved. 12 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES Acknowledgments ISACA would like to recognize: Board of Directors Tracey Dedrick, Chair Brennan P. Baybeck Former Chief Risk Officer, Hudson City Bancorp, USA CISA, CRISC, CISM, CISSP Rolf von Roessing, Vice-Chair Vice President and Chief Information Security Officer for Customer Services, Oracle Corporation, USA CISA, CISM, CGEIT, CDPSE, CISSP, FBCI Partner, FORFA Consulting AG, Switzerland Gabriela Hernandez-Cardoso Independent Board Member, Mexico Pam Nigro CISA, CRISC, CGEIT, CRMA Vice President–Information Technology, Security Officer, Home Access Health, USA Maureen O’Connell Board Chair, Acacia Research (NASDAQ), Former Chief Financial Officer and Chief Administration Officer, Scholastic, Inc., USA ISACA Board Chair, 2019-2020 Rob Clyde CISM ISACA Board Chair, 2018-2019 Independent Director, Titus, and Executive Chair, White Cloud Security, USA Chris K. Dimitriadis, Ph.D. CISA, CRISC, CISM ISACA Board Chair, 2015-2017 Group Chief Executive Officer, INTRALOT, Greece David Samuelson Chief Executive Officer, ISACA, USA Gerrard Schmid President and Chief Executive Officer, Diebold Nixdorf, USA Gregory Touhill CISM, CISSP President, AppGate Federal Group, USA Asaf Weisberg CISA, CRISC, CISM, CGEIT Chief Executive Officer, introSight Ltd., Israel Anna Yip Chief Executive Officer, SmarTone Telecommunications Limited, Hong Kong © 2020 ISACA. All Rights Reserved. 13 AN ITAF™ APPROACH TO IT AUDIT ADVISORY SERVICES About ISACA For more than 50 years, ISACA® (www.isaca.org) has advanced the best talent, expertise and learning in technology. ISACA equips individuals with knowledge, credentials, education and community to progress their careers and transform their organizations, and enables enterprises to train and build quality teams. ISACA is a global professional association and learning organization that leverages the expertise of its 145,000 members who work in information security, governance, assurance, risk and privacy to drive innovation through technology. It has a presence in 188 countries, including more than 220 chapters worldwide. 1700 E. Golf Road, Suite 400 Schaumburg, IL 60173, USA Phone: +1.847.660.5505 Fax: +1.847.253.1755 Support: support.isaca.org Website: www.isaca.org DISCLAIMER ISACA has designed and created An ITAF™ Approach to IT Audit Advisory Services (the “Work”) primarily as an educational resource for professionals. Provide Feedback: ISACA makes no claim that use of any of the Work will assure a successful https://support.isaca.org/ outcome. The Work should not be considered inclusive of all proper information, procedures and tests or exclusive of other information, Participate in the ISACA Online procedures and tests that are reasonably directed to obtaining the same Forums: https://engage.isaca.org/onlineforums results. In determining the propriety of any specific information, procedure or test, professionals should apply their own professional judgment to the specific circumstances presented by the particular systems or information Twitter: www.twitter.com/ISACANews technology environment. LinkedIn: www.linkedin.com/company/isaca RESERVATION OF RIGHTS Facebook: www.facebook.com/ISACAGlobal © 2020 ISACA. All rights reserved. Instagram: www.instagram.com/isacanews/ An ITAF™ Approach to IT Audit Advisory Services © 2020 ISACA. All Rights Reserved.