Journal of Process Control 105 (2021) 99–107
Contents lists available at ScienceDirect
Journal of Process Control
journal homepage: www.elsevier.com/locate/jprocont
Zero-dynamics attacks on networked control systems
∗
Syed Ahmed Pasha a , , Ayesha Ayub b
a
b
Department of Electrical & Computer Engineering, Air University, Islamabad, 44000, Pakistan
Electrical Engineering and Computer Science, NUST, Islamabad, 44000, Pakistan
article
info
Article history:
Received 15 May 2021
Received in revised form 27 May 2021
Accepted 20 July 2021
Available online 2 August 2021
Keywords:
Zero-dynamics attack
False data injection
Geometric control
Networked control system
Cyberphysical system
a b s t r a c t
The coupling of physical systems with information technologies infrastructure in a networked control
system (NCS) has a number of advantages such as remote control, reduced system complexity, low
maintenance cost and improved system efficiency. But these benefits come at the cost of making the
NCS vulnerable to cyberphysical attacks on the communication layer. One such class of attacks is the
zero-dynamics attack (ZDA) which targets the internal dynamics of an NCS with the potential to cause
serious damage to the physical system while remaining stealthy. A better understanding of how ZDAs
are constructed will enable more effective countermeasures. In this paper, we discuss two approaches
for constructing a ZDA and demonstrate using three industrial processes studied in this context perhaps
for the first time.
© 2021 Elsevier Ltd. All rights reserved.
1. Introduction
The rapid advancement in the field of digital control systems
has led to the use of digital controllers and communication networks in many control processes, subsequently transforming the
traditional control system into a networked control system (NCS).
An NCS is a type of a cyberphysical system where the controller
is geographically distributed and controls a physical process by
sending control signals via a communication network [1,2].
The basic architecture of an NCS includes a physical process
(or plant), sensors and actuators, a communication network and
a controller. But the coupling of the physical system with the
information technologies infrastructure makes an NCS vulnerable
to cyberphysical attacks on its communication layer [3–7]. Such
attacks disrupt the normal behaviour of a physical process and
are capable of causing catastrophic physical damage to the plant.
The first reported incident of a cyberphysical attack on an
industrial process goes back to the 1982’s Serbian pipeline explosion [8]. But the 2003 US–Canada blackout can be considered
as the turning point for security of cyberphysical systems. Cyberphysical security gained even greater attention after the 2010
StuxNet attack that targeted the centrifuge control system at an
Iranian nuclear power plant [9,10]. The severity of a cyberphysical attack can be understood by this attack whose goal was to
physically damage the plant. Further examples of staged attacks
on cyberphysical systems can be found in [5,11–13].
A cyberphysical attack can be classified based on the aim of
the attack which can vary from withholding data to physically
∗ Corresponding author.
E-mail address: s.pasha@mail.au.edu.pk (S.A. Pasha).
https://doi.org/10.1016/j.jprocont.2021.07.010
0959-1524/© 2021 Elsevier Ltd. All rights reserved.
damaging a plant. We begin a review of the literature on cyberphysical attacks on NCSs focusing on approaches for generating
stealthy attacks. An important class of attacks is the denial-ofservice (DoS) attack (also known as packet flooding attack in the
computer science literature) where an attacker tampers with the
packet delivery. Thus, preventing the plant from receiving the
control signal or the controller from receiving the sensor data.
Amin et al. [14], have considered controller design subject to
safety and power constraints in the presence of a DoS attack and
cast the optimal control problem as a semi-definite program. The
controller design approach of Yuan et al. [15], is based on value
iteration methods and linear matrix inequalities for computing
control laws under a DoS attack. Zhang et al. [16], have proposed a
scheduling policy for an attacker to degrade system performance
subject to some energy constraints. A stochastic control problem
has been considered by Befekadu et al. [17], under a Markov modulated DoS attack strategy. A scheduling policy for transmission
of packets that preserves input-to-state stability of the closedloop system in the presence of DoS attacks has been discussed by
De Persis and Tesi [18]. This work has been extended to multiple
channels by Lu and Yang [19].
Another important class of cyberphysical attacks is the replay
attack which is a closed loop attack, that is, it requires online information to construct an attack signal. A replay attack is carried
out in two simple steps: first, an attacker takes control of the
sensors and records the sensor output data for a sufficient amount
of time (without injecting additional input into the system). Then,
the attacker injects a sequence of desired input while simultaneously replaying the output data recorded earlier. The effect
of a data replay attack on a discrete-time linear time invariant
(LTI) Gaussian system equipped with an infinite horizon linear
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
quadratic Gaussian (LQG) controller has been studied by Mo
and Sinopoli [11]. The authors have provided conditions on the
feasibility of a replay attack. An extension to systems subject to
state and input constraints based on a variation of the recedinghorizon control law has been studied by Zhu and Martinez [20].
In Miao et al. [21], the authors have studied the relation between
control system performance and detection rate for replay attacks.
They have employed a finite horizon, zero-sum, nonstationary
stochastic game approach to obtain an optimal control policy in
the presence of replay attacks.
The deception attack is another important class of cyberphysical attacks that sends false data via a sensor or controller. It is
designed in a way to deceive the monitoring system to assume
that the plant is operating nominally. Scenarios where bad data
detectors fail to detect deception attacks have been investigated
by Teixeira et al. [22]. By relaxing the assumption that an attacker has perfect knowledge of the system, the authors have
studied the relation between accuracy of the model known to
an attacker and the potency of a deception attack. A false data
injection (FDI) attack is a subclass of deception attacks performed
on the sensors, requiring knowledge of the system. The seminal
work of Liu et al. [12,23] drew attention to the vulnerability of
bad data detectors and discussed, for the first time, FDI attacks
against state estimation in electric power grids. For a discretetime LTI Gaussian system equipped with an LQG controller, Mo
and Sinopoli [24], have shown how to design input to the state
estimator by providing a necessary and sufficient condition under
which an attacker can destabilize the system undetected. Li et al.
[25], have studied an FDI attack on an NCS in a Stackelberg game
(leader–follower game) framework. For a comprehensive review
of FDI attacks on power systems, the reader is referred to the wok
of Liang et al. [26].
Here, we are concerned with another subclass of deception
attacks known as the zero-dynamics attack (ZDA). A ZDA is an open
loop stealthy attack that targets the internal dynamics of an NCS.
The construction of a ZDA requires knowledge of the system. A
ZDA targets the class of non-minimum phase systems by exploiting the unstable zeros. The existence of a geometrically increasing
input with no apparent change at the output makes ZDA a serious
threat. Using a geometric control framework [27,28], stealthiness
properties of a ZDA for an LTI system have been characterized
by Teixeira [13]. Based on these results, the design of an FDI in
the control signal generated by an LQG controller that remains
stealthy has been discussed by Keller and Sauter [29].
A better understanding of how ZDAs are constructed will lead
to more effective means to protect against such attacks. With this
motivation, in this paper we make the following contributions:
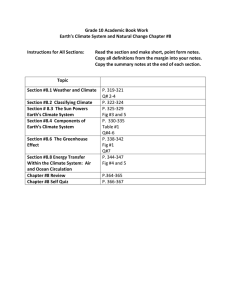
Fig. 1. Networked control system (NCS) under attack.
Notation. For an n × n matrix X , by X ≥ 0, we mean that X is
positive semidefinite. For any matrix X , Im(X ) denotes the range
space of X and null(X ) denotes the null-space of X . In is an n × n
identity matrix.
2. Networked control system model
Consider a networked control system (NCS) shown in Fig. 1
which consists of a plant, a communication network connecting
the plant to a controller and an anomaly detector that has access
to both the sensor as well as actuator data. We consider a scenario
where an attacker who does not have access to the sensor and
actuator data injects false data into the actuator channels without
detection by the anomaly detector.
A linear time-invariant state-space representation of the NCS
in discrete-time is given by
xk+1 = Axk + Bµk + wk
(1)
yk = Cxk + vk
(2)
µ k = uk + ak
(3)
n
q
where xk ∈ R is the state at time k, uk ∈ R is the feedback
control law transmitted to the plant via the actuator channels,
yk ∈ Rm is the sensor data transmitted to the controller via the
sensor channels. ak ∈ Rq is the attack vector injected into the
actuator channels. wk ∈ Rn and vk ∈ Rm are zero mean white
noise with
( ) (
wk
W
var
=
vk
0
1. we generalize the approach of Teixeira [13], to construct a
ZDA by considering the effect of the output feedback control which was ignored in [13]; this entails state estimation
via Kalman filtering;
2. we demonstrate, for the first time, the effects of a ZDA on
three industrial processes: the Tennessee Eastman process
(TEP) [30], the sextuple tank process (STP) [31] and a sugar
mill system [32]. A simplified version of the TEP has been
studied by Mo et al. [33] to detect a replay attack;
3. we compare two approaches for constructing a ZDA, emphasizing the computational aspects of the algorithms and
studying their effects on the three industrial processes,
referring the interested reader to the theoretical results in
the literature.
0
V
)
where W ≥ 0 and V ≥ 0. Matrices A, B and C are of appropriate
dimensions.
Remark 1. In general, the network communication layer is prone
to packet losses, delays as well as other network related issues.
Therefore, the sensor and actuator data will be unreliable. There
is substantial literature concerned with such issues. But to focus
on the dynamics of the NCS due to false data injection (FDI) these
issues are not considered.
We make the following assumption.
Assumption 1. In the absence of an attack, communication from
the sensors to the controller and from the controller to the plant
is reliable, i.e., in Fig. 1, νk = yk and µk = uk . During an attack,
communication from the sensors to the controller is reliable, but
from the controller to the plant is unreliable i.e., νk = yk and
µk ̸= uk .
The paper layout is as follows: Section 2 provides a model of
the NCS under attack and the assumptions needed to construct
a ZDA. In Section 3, we discuss two approaches for constructing
a ZDA. In Section 4, we demonstrate the two approaches using
three industrial processes. Finally, Section 5 concludes the paper.
100
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
In the absence of an attack, the NCS model (1)–(3) can be
written as
x̄k+1 = Ax̄k + Būk + wk
(4)
ȳk = C x̄k + vk
(5)
ūk = uk
(6)
Subtracting (4)–(6) from (1)–(3), the NCS dynamics due to an
FDI attack are given by
x̃k+1 = Ax̃k + B(ũk + ak )
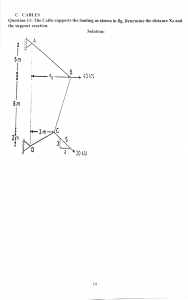
Fig. 2. (A, B)-controlled invariant subspace.
(7)
ỹk = C x̃k
(8)
ũk = uk − ūk
(9)
Consider a dynamical system given by
zk+1 = Azk + Buk
where x̃k := xk − x̄k and ỹk := yk − ȳk .
Without loss of generality, let k = 0 be the time when an
attack is initiated. Then, we have x̄o = xo ⇒ x̃o = 0.
In addition to Assumption 1, we make the following standard
assumptions [13,29].
yk = Czk
(10)
(11)
where zk ∈ Rn is the state at time k, uk ∈ Rq is the input and
yk ∈ Rm is the output.
Definition 1 ([38]). A subspace V ⊆ Rn is A-invariant if AV ⊆ V .
Assumption 2.
(4)–(6).
The attacker has knowledge of the system
A property of an A-invariant subspace is the following [38,
Property 3.2.1].
A subspace V with a basis matrix Q is A-invariant if and only
if there exists a matrix X such that
Assumption 3. m ≤ q ≤ n. Matrices B and C are full rank,
i.e., rank(B) = q and rank(C ) = m. Moreover, the system (4)–(6)
is minimal.
Assumption 4.
(A, C ) is observable and (A, B) is controllable.
Assumption 5.
The system (4)–(6) is stable.
AQ = QX
(12)
See [38, pp. 128] for a proof.
Let B = Im(B), a controlled invariant subspace can be defined
as follows [27,37,38].
Definition 2. A subspace V ⊆ Rn is (A, B)-controlled invariant if
AV ⊆ V + B.
Remark 2. Assumption 2 is required to construct a state-space
model whose output forms the attack vector. In Assumption 3,
the condition q ≤ n is required to obtain the subspace B =
Im(B) ⊆ Rn restricted to the column-space of the input matrix B.
Similarly, the condition m ≤ n is required to obtain the subspace
C = null(C ) ⊆ Rn restricted to the null-space of the output matrix
C . Finally, the condition m ≤ q is needed to ensure CB(CB)T has
full rank.
A useful property is the following [38, Property 4.1.4].
A subspace V with a basis matrix Q is controlled invariant if
and only if there exist matrices X and U such that
AQ = QX + BU
See [38, pp. 202] for a proof.
A controlled invariant can be transformed into a simple invariant via a suitable state feedback [38, Theorem 4.1.2].
The conditions for a stealthy attack can be stated as the following lemma.
Theorem 2. A subspace V is an (A, B)-controlled invariant subspace
if and only if there exists a matrix F such that (A + BF )V ⊆ V .
Lemma 1. The system (1)–(3) is attackable without being detected if and only if the system states can be excited such that
lim supk→∞ ∥x̃k ∥ = ∞, and ∥ỹk ∥ ≤ γ , ∀k ≥ 0 and γ > 0.
See [38, pp. 202] for a proof.
3. Zero-dynamics attack construction
Remark 3. From Theorem 2, there exists a nonempty subspace
V and a matrix F such that if the control law is taken as uk = Fzk ,
for all k, then the system (10)–(11) enters the (A, B)-controlled
invariant subspace V and is restricted to this subspace for all k,
i.e., (A + BF )V ⊆ V .
We discuss two approaches for constructing a zero-dynamics
attack (ZDA) on an NCS. In [13], a ZDA is constructed based on
the geometric control approach [27,28]. The attack vector ak is
the output of an autonomous dynamic system (ZDA via output
feedback). In [29], a fault detection and isolation based approach
has been used and the attack vector ak is generated from the
states of a stable system (ZDA via state feedback). We begin with
a review of some relevant results in geometric control.
This result is illustrated in Fig. 2.
If the controlled invariant subspace V is contained in C =
null(C ), we obtain an output-nulling controlled invariant subspace [39,40]. Among the set of these subspaces V ⊆ C , the
maximal element Vm is called the maximal output-nulling invariant subspace [38]. An algorithm to determine Vm can be found
in [38, Algorithm 4.1.2, pp. 204],[41]. The eigenvalues of A + BF
restricted to the eigenspace spanned by Vm are referred to as the
zeros of the system (10)–(11).
For zo ∈ Vm and uk = Fzk for all k, the system will remain in
the subspace Vm with the output in (11) identically zero for all
k ≥ 0.
3.1. Zero dynamics
A related problem in geometric control is that of zerodynamics [34–36] which requires the system output to be zero
for nonzero initial conditions and input. Zero-dynamics can be
understood using the notion of a controlled invariant subspace
[27,35,37,38].
101
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
Fa ∈ Rn×nz and da ∈ Rnz , with nz = # unstable zeros of the
system. The second term on the right in (17) is responsible for
exciting x̃k with da close to the origin. The matrices Ka and Fa are
designed such that the plant states for k ≥ 0 are contained in the
(A, B)-controlled invariant subspace. We consider three scenarios
below.
Before Attack (k < 0)
3.2. ZDA via output feedback
Taking the approach in [13], a ZDA can be constructed as,
zk+1 = (A + BF )zk ,
zo ∈ Vm
(13)
ak = Fzk
(14)
with F such that (A + BF )Vm ⊆ Vm .
The attack vector ak is then fed to the NCS (1)–(3). By taking
x̃o = zo , the output in (8) is guaranteed to satisfy the conditions
of a stealthy attack in Lemma 1.
x̃k = 0
ỹk = 0
Start of Attack (k = 0)
Remark 4. Note the apparent contradiction in the choice of
x̃o = 0 in the model (7)–(9) and x̃o = zo ∈ Rq for the outputnulling condition. To make progress, we require that zo is close
to the origin [13].
x̃1 = Fa da
ỹ1 = CFa da
To satisfy the output-nulling condition, we must have CFa = 0
since da ̸ = 0. If C⊥ is an (n − m) × n matrix of rank n − m whose
rows are orthogonal to the rows of C , then the projection theorem
gives
Remark 5. If the output-nulling condition is satisfied, i.e., ỹk for
all k ≥ 0 is at the origin, the output feedback control in (7) can
be dropped. But ỹk is not at the origin so we consider its effect
which was ignored in [13].
T
T −1
I = C T (CC T )−1 C + C⊥
(C⊥ C⊥
) C⊥
Thus, the NCS dynamics due to a ZDA including the output
feedback control are given by (7) where ũk = −K x̂k and the
controller dynamics are given by
⇒ Fa = [I − C T (CC T )−1 C ]F̄
x̂k+1 = Ax̂k + Bũk + L(ỹk − C x̂k )
x̃l = (A − BKa )l−1 Fa da ,
for any F̄ ∈ Rn×nz .
During Attack (k > 0)
l>1
where x̂k is a state estimate from the Kalman filter, K is the
feedback gain and L is the observer gain.
The dynamics of the augmented state vector ξk = (x̃Tk , x̂Tk )T are
given by
ỹl = C (A − BKa )
ξk+1 = Ãξk + B̃ak ,
ỹk = C̃ ξk
Ka = [I − BT C T (CBBT C T )−1 CB]K̄
ξo = 0
l−1
(15)
+ BT C T (CBBT C T )−1 CA
(16)
A
LC
]
[ ]
−BK
B
, B̃ =
, C̃ = C
A − BK − LC
0
[
for any K̄ ∈ R .
We use the notion of an A-invariant subspace to show how the
plant states can be excited to infinity.
Note that in (12), if X is a diagonal matrix, then the columns
of Q are the eigenvectors of A and AQ = QX is an eigenvalue
problem. Let X = diag(z1 , . . . , znz ) where zj , j = 1, . . . , nz are the
invariant zeros and Q = Fa then
0 .
]
It follows from the output-nulling condition that ξo is not
identically zero but close to the origin.
Consider the solution of (15) for k > 0,
ξk = Ãk ξo +
k−1
∑
(A − BKa )Fa = Fa diag(z1 , . . . , znz )
Ãk−1−i B̃F (A + BF )i zo .
At the start of the attack, since zo ∈ Vm is close to the origin,
the first term dominates. As the attack continues, zk increases
geometrically which results in the second term dominating and
thus lim supk→∞ ∥ξk ∥ = ∞.
Finally, if the open loop system is unstable, there is a possibility that the attack vector excites the unstable modes of A. To
avoid this, zo should be further restricted to the eigenspace of the
stable poles of A.
4. Simulations
We present simulation results to illustrate construction of
ZDAs on three industrial processes. Our aims are threefold:
3.3. ZDA via state feedback
(i) to demonstrate construction of a ZDA by exploiting unstable zeros in a system;
(ii) to highlight the consequences of such an attack;
(iii) to compare the performance of two different approaches
for constructing a ZDA.
The approach in [29] uses state feedback to construct a ZDA
offline based on an attacker’s knowledge of the system. Consider
again the NCS model (7)–(9). Substituting ak = −Ka x̃k to obtain
the autonomous system
x̃k+1 = (A − BKa )x̃k + δk,0 Fa da ,
x̃o = 0
4.1. Tennessee Eastman Process
(17)
ỹk = C x̃k
The Tennessee Eastman process (TEP) [30] is a nonlinear industrial process that consists of five process units: two-phase
reactor, stripper, compressor, separator and mixer. The TEP has
been widely used as a case study for fault diagnosis [42] and
system identification [43,44]. It is an 8-th order MIMO system
where δk,0 is the Kronecker delta
1
if i = j
0
if i ̸ = j,
(20)
All that remains is to choose F̄ in (18) such that (20) is satisfied
to restrict the plant states to the controlled invariant subspace.
Finally, if the open loop system is unstable then in addition to
Fa satisfying (20), the columns of Fa are taken orthogonal to the
eigenvectors corresponding to the unstable poles of A.
i=0
δi,j =
(19)
q×n
[
{
Fa da
To satisfy ỹl = 0, l > 1, we need to design Ka such that
C (A − BKa ) = 0. Using the projection theorem, we are led to
where
à =
(18)
102
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
with four inputs that represent valve positions for controlling
flow of reactants and four outputs that represent product flow
measurement, pressure, amount of reactant in purge and liquid
inventory.
Let the state vector xk = (x1,k , . . . , x8,k )T . Then, state variables
x1,k , . . . , x4,k represent molar holdup of reactants and x5,k , . . . ,
x8,k represent valve position of feed 1, feed 2, purge and product
at time k respectively. For a detailed description of the model the
reader is referred to [30].
We consider a discretized model after linearizing using a sampling time Ts = 0.17 s. The system matrices are:
A = bdiag(A1 , A2 , A3 )
where
A1 = .79
[
0
00
[
.02
.04
[
A2 =
.99
.06
−.09
.49
]
⎡
.30
0
0
0
0
0
.09
.01
0
0
0
0
−.18
−.09
0
0
0
A3 =
−.09
.98
⎢ 0
⎢ 0
⎢
⎢ .64
B=⎢
⎢1.58
⎢
⎢ 0
⎣
0
0
−1.160
]
−.19
0
00
.18
]
.31 ,
1.18
0
1.33
0
.37⎥
⎢−4.25
⎢ 0
.21⎥
⎢
⎥
⎢
0 ⎥
T
⎥, C = ⎢ 0
⎢ 0
⎥
0
⎢
⎥
⎢ 0
0 ⎥
⎣
⎦
0
0
0
.18
⎤
⎡
0
0
0
0
8
0
0
0
0
0
0
0
0
−.07
1.5
0
0
0⎥
0⎥
⎥
0⎥
⎥
8⎥
⎥
0⎥
⎦
0
1
⎤
The process and measurement noise covariances were taken as
W = 10−4 I8 and V = 10−2 I4 .
4.1.1. ZDA via output feedback
A basis matrix Q for Vm was constructed as outlined in [38,
Algorithm 4.1.2, pp. 204]. Q was initialized to a basis matrix
for C = null(C ) which was determined via a singular value
decomposition (SVD) of C T and choosing the last n − m columns of
the left singular vectors matrix. A−1 needed in subsequent steps
was precomputed. Note that the block diagonal structure of A
leads to A−1 = bdiag(A1 −1 , A2 −1 , A3 −1 ).
We found
[
Q =
Q1
0
⎡
.95
0
⎢.29
, Q1 = ⎣
Q
0
]
2
0
0
0
−1
0
⎤
⎡
⎤
0
0
0 ⎥
⎢−.99⎥
,Q = ⎣
0 ⎦ 2
−.04⎦
−1
0
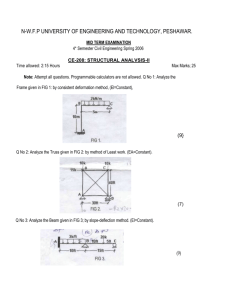
Fig. 3. TEP under ZDA via output feedback.
The state feedback matrix F such that (A + BF )Vm ⊆ Vm was
determined as outlined in [38, Algorithm 4.1.3, pp. 205] which
yielded
⎡
⎢
F =⎢
⎣
−2.97
−.93
−12.17
0
0
0
−47.98
−15.05
−196.46
0
0
0
0
0
.62
0
0
0
0
0
0
−13.08
0
0
0
−.65
0
0
The output feedback control ũk is shown in Fig. 3(c) and the
output due to the ZDA ỹk is shown in Fig. 3(d).
From Fig. 3(a), the attack signal alternates with an exponentially growing amplitude. We determine from Fig. 3(b) that the
ZDA will excite the components x6,k and x7,k of the NCS to infinity.
Recall that x6,k and x7,k represent the plant valve positions for
feed 2 of the reactant and purge respectively. As x6,k approaches
infinity much faster than x7,k , this will cause an imbalance in the
proportion of the reactant. Thus, disturbing the entire chemical
process. We can see from Fig. 3(d) that the TEP output due to
the ZDA ỹk is close to the origin so the TEP output yk will remain
close to the nominal value ȳk and the attack will remain stealthy.
Furthermore, by choosing zo sufficiently close to the origin, the
output feedback control ũk is close to the origin as shown in
Fig. 3(c).
⎤
0
0⎥
⎥
0⎦
0
We found that the system has a single unstable zero at −1.226.
The open loop system has an unstable pole at 1.185. The corresponding eigenvector is (0, 0, 0, 0, 0, 0, 0, 1)T . To construct a
ZDA we require zo orthogonal to this eigenvector. We take zo =
3.33 × 10−6 (0T , Q2T )T . It is easy to see that the attack vector
ak = (a1,k , . . . , a4,k )T has zero entries except in a2,k . The trajectory
of a2,k for 13.6 s is shown in Fig. 3(a). The ZDA excites components
x̃6,k and x̃7,k of the system. The trajectories are shown in Fig. 3(b).
103
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
4.2. Sextuple tank process
The sextuple tank process (STP) consists of three tank plants
coupled through the inputs. A typical tank module contains a
pump with a water basin and two tanks. The two tanks are
configured such that water from the upper tank can flow into
the lower tank while the water from the lower tank flows into
the reservoir.
The STP can be modelled as a 6-th order multiple-inputmultiple-output system. The objective is to regulate water levels
in the lower tanks by controlling the inlet flows to the three
way valves. The three inputs are three pump voltages and three
outputs that are water levels of the lower tanks: tank 2, tank 4
and tank 6. The six STP states are the water levels in all tanks,
i.e., tank 1, . . . , tank 6.
We consider a discrete-time STP model [31] with sampling
time Ts = 0.25 s. The system matrices are:
A = bdiag(A1 , A1 , A1 )
where
.90
A1 =
.08
[
]
0
, BT = 10−3
.90
C = bdiag(C1 , C1 , C1 ),
[
.1
[
.1
]
0
0
1.1
C1 = 0
3.8
0
0
0
.2
.2
0
0
3.7
0
0
0.2
2.7
]
1
The process and measurement noise covariance matrices are
taken as W = 10−5 I4 and V = 10−1 I2 .
4.2.1. ZDA via output feedback
A basis matrix Q for Vm was constructed as outlined in [38]
for an initial value of null(C ) which yielded
[
Q = q1
q2
q3 = bdiag(−e1 , e1 , e1 ), e1 = (1, 0)T .
]
The state feedback matrix F satisfying (A + BF )Vm ⊆ Vm was
determined as outlined in [38] which yielded
Fig. 4. TEP under ZDA via state feedback.
[
−1.093
1.298
F = 10
−0.085
0
0
0
3
4.1.2. ZDA via state feedback
The matrices Ka and Fa were computed from (18) and (19)
respectively which yielded
2.6
⎢ 0
Ka = ⎢
⎣42.2
0
2.0
0
33.2
0
12.1
0
196.4
0
[
0
0
⎡
Fa = 0
0
0
0
0
−0.6
0
0
0
−5.0
0
0
6.3
0
0
−.998
−.049
0
0
135.5
0
0
−.025
−.546
.035
.021
−.025
−.030
0
0
0
0
0
0
]
The open loop system is stable. The STP has a pair of complex
unstable zeros at 1.016 ± i.791. To generate a ZDA, a suitable
choice of zo is
zo = 10−5 (.5q1 − 3.1q2 + 19q3 )
24.9
0 ⎥
⎥
402.0⎦
6.3
⎤
[
= 10−5 −.5
0
−3.1
0
19
]T
0
The trajectories of the components of the attack vector ak =
(a1,k , a2,k , a3,k )T for 35 s are shown in Fig. 5(a). The ZDA excites the state components states x̃1,k , x̃3,k and x̃5,k as shown in
Fig. 5(b). The output feedback control ũk (not shown) was found
to be close to the origin. Fig. 5(c) shows the output due to the
ZDA.
It is clear from Fig. 5(b), that the plant states x1,k , x3,k and
x5,k will be driven to infinity. The water level in tank 5 will
drop rapidly causing the lower tank to overflow while the water
level in tank 3 will increase rapidly by pumping water from the
reservoir until it overflows. Thus, destabilizing the system. Since
ỹk remains close to the origin in Fig. 5(c), the system output yk
will be close to the nominal value ȳk and the attack will remain
stealthy.
]T
with F̄ = (0, 0, 0, 0, 0, −.998, −.049, 0)T satisfying (20) chosen
by inspection. da = 3.33 × 10−6 was taken.
It is easy to see that the attack vector ak has zero entries except
in a2,k . The trajectory is shown in Fig. 4(a). The trajectories of x̃6,k
and x̃7,k excited by the ZDA are shown in Fig. 4(b). The output of
the NCS due to the ZDA is show in Fig. 4(c).
The plots appear to be very similar to the case where a ZDA is
constructed via output feedback with one difference. For the same
initial conditions, the energy of the attack signal a2,k constructed
via output feedback is higher which destabilizes the system more
rapidly.
The computation time for constructing a ZDA using both approaches was obtained by averaging over 1000 runs on a 2.53 GHz
processor utilizing 2 cores. The computation time for the output
feedback approach was 0.55 ms compared to the state feedback
approach which took 0.85 ms to construct the attack trajectory.
4.2.2. ZDA via state feedback
The matrices Ka and Fa were computed from (18) and (19)
which yielded
1094
Ka= −1298
85
[
104
11105
−13180
863.3
25.2
546.9
−35.8
255.5
5552.6
−363.7
−21.6
25.7
30.8
−219.7
260.8
312.8
]
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
Fig. 6. STP under ZDA via state feedback.
Fig. 5. The STS under ZDA via output feedback.
Fa = bdiag(E1 , E1 , E1 )F̄ ,
[
E1 =
1
0
0
0
]
Ts = 0.5 s gives
⎡
−.0595 −.1656
.6736
⎢ .2667
A=⎣
.1304
.4252
.0003
.0008
⎡
⎤
−.003 .266
⎢−.010 .522 ⎥
B=⎣
−.009 .118 ⎦
.247 .031
with
[
−.024 − i.042
F̄ =
−.024 + i.429
0
0
−.154 + i.268
−.154 − i.268
0
0
.949
.949
]T
0
0
.
da = 10−5 was taken.
The resulting ZDA is shown in Fig. 6(a). The effect of the attack
on the system states is shown in Fig. 6(b). Fig. 6(c) shows the
contribution to output by the ZDA.
The attack trajectories shown in Fig. 6(a) are very similar to
those in Fig. 5(a) for the same initial conditions. Naturally, we
expect the attack to destabilize the plant in a similar fashion. A
comparison of the computation time to generate a ZDA showed
that the output feedback approach took 0.886 ms compared to
1.371 ms for the state feedback approach.
2.505
−.001
[
C =
.012
−.005
.0009
.0004
.9992
.0008
.011
−.004
⎤
−.0233
−.0090 ⎥
,
.0211 ⎦
.9803
−.360
.079
]
The process and measurement noise covariance matrices are
taken as W = 10−4 I4 and V = 4 × 10−4 I2 .
4.3.1. ZDA via output feedback
A basis matrix Q for Vm was constructed as outlined above for
an initial value of null(C ). Q was found as
4.3. Sugar mill system
A sugar crushing mill system can be modelled as a 4-th order
system with two inputs: turbine speed and chute flap and two
outputs: turbine torque and chute height. A discretized model of
the continuous-time sugar mill system [32] for a sampling time
[
Q = q1
105
⎡
.005
] ⎢.718
q2 = ⎣
.690
.085
⎤
0
.692 ⎥
−.721⎦
.001
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
Fig. 7. The sugar mill under ZDA via output feedback.
Fig. 8. Sugar mill system under ZDA via state feedback.
The state feedback matrix F satisfying (A + BF )Vm ⊆ Vm was
determined as outlined above and found as
[
.0002
F =
.0027
.0405
.6485
.0022
.0151
The resulting ZDA is shown in Fig. 8(a). The effect of the
attack on the plant states can be determined from Fig. 8(b) which
suggests that the plant will rapidly destabilize. Fig. 8(c) shows the
contribution to output by the ZDA.
A comparison of Fig. 7(b) and Fig. 8(b) shows that both approaches generate identical attack vectors for the same initial
conditions. The computation time for generating a ZDA via output
feedback was 1.2 ms compared to 1.53 ms via state feedback.
.0027
.0416
]
The open loop system is unstable with the largest eigenvalue of A at unity. The corresponding eigenvector is (.0001,
−.0001, −.9992, −.0404)T . To generate a ZDA a suitable choice
of zo that is orthogonal to the above eigenvector is z0 = 10−3 q1 .
The trajectories of the components of the attack vector ak =
(a1,k , a2,k )T for 70 s are shown in Fig. 7(a). The attack vector
excites all four system states as shown in Fig. 7(b). The output
feedback control ũk (not shown) was found to be close to the
origin. Fig. 7(c) shows the output due to the ZDA.
From Fig. 7(b), we can determine that all plant states will be
driven to infinity with x3,k growing the most rapidly. Since ỹk
remains close to the origin, the system output yk will be close
to the nominal value ȳk and the attack will remain stealthy.
5. Conclusions
A zero-dynamics attack (ZDA) targets the internal dynamics
of a system and remains stealthy to detectors that monitor a
system’s inputs and outputs. In this paper, we have reviewed two
approaches for constructing a ZDA based on geometric control
and fault detection and isolation techniques. A comparison of
the two approaches is presented by demonstrating the attacks
on three industrial processes. We have found that the two approaches generate very similar attack trajectories that rapidly
destabilize the systems.
In this paper, a constraint on the energy of the attack vector
was not considered which grows unbounded. Future work will
consider construction of a ZDA under energy constraints on the
attack vector. We will also investigate conditions under which a
ZDA can be constructed under imperfect knowledge of an NCS.
4.3.2. ZDA via state feedback
The matrices Ka and Fa were computed from (18) and (19)
which yielded
[
]
−.104 −.288 −.230 3.943
−.233 −.648 −.014 −.031
[
]T
Fa = .0056 .7271 .6812 .0847
Ka =
with F̄ = (.0056, .7271, .6812, .0847)T . da = 10−3 was taken.
106
S.A. Pasha and A. Ayub
Journal of Process Control 105 (2021) 99–107
CRediT authorship contribution statement
[19] A.-Y. Lu, G.-H. Yang, Input-to-state stabilizing control for cyber-physical
systems with multiple transmission channels under denial of service, IEEE
Trans. Automat. Control 63 (6) (2017) 1813–1820.
[20] M. Zhu, S. Martinez, On the performance analysis of resilient networked
control systems under replay attacks, IEEE Trans. Automat. Control 59 (3)
(2014) 804–808.
[21] F. Miao, M. Pajic, G.J. Pappas, Stochastic game approach for replay attack
detection, in: 52nd IEEE Conf. Decision and Control, 2013, pp. 1854–1859.
[22] A. Teixeira, S. Amin, H. Sandberg, K.H. Johansson, S.S. Sastry, Cyber security
analysis of state estimators in electric power systems, in: 49th IEEE Conf.
Decision and Control, CDC, 2010, pp. 5991–5998.
[23] Y. Liu, P. Ning, M.K. Reiter, False data injection attacks against state
estimation in electric power grids, in: Proc. 16th ACM Conf. Computer
and Communications Security, 2009, pp. 21–32.
[24] Y. Mo, B. Sinopoli, False data injection attacks in control systems, in: 1st
Workshop on Secure Control Systems, 2010.
[25] Y. Li, D. Shi, T. Chen, False data injection attacks on networked control
systems: A stackelberg game analysis, IEEE Trans. Automat. Control 63
(10) (2018) 3503–3509.
[26] G. Liang, J. Zhao, F. Luo, S.R. Weller, Z.Y. Dong, A review of false data
injection attacks against modern power systems, IEEE Trans. Smart Grid 8
(4) (2016) 1630–1638.
[27] G. Basile, G. Marro, Controlled and conditioned invariant subspaces in
linear system theory, J. Optim. Theory Appl. 3 (5) (1969) 306–315.
[28] W.W. Murray, Linear Multivariable Control: A Geometric Approach,
Springer-Verlag, 1979.
[29] J. Keller, D. Sauter, Monitoring of stealthy attack in networked control
systems, in: Conf. Control and Fault-Tolerant Systems, SysTol, 2013, pp.
462–467.
[30] J.J. Downs, E.F. Vogel, A plant-wide industrial process control problem,
Comput. Chem. Eng. 17 (3) (1993) 245–255.
[31] D. Copot, A. Maxim, R. De Keyser, C.-M. Ionescu, Multivariable control of
sextuple tank system with non-minimum phase dynamics, in: Proc. 2016
IEEE Intl. Conf. Automation, Quality and Testing, Robotics, AQTR, 2016, pp.
399–404.
[32] G. Goodwin, S. Graebe, M. Salgado, Control System Design, Prentice Hall,
2001.
[33] Y. Mo, R. Chabukswar, B. Sinopoli, Detecting integrity attacks on SCADA
systems, IEEE Trans. Control Syst. Technol. 22 (4) (2013) 1396–1407.
[34] S. Monaco, D. Normand-Cyrot, Zero dynamics of sampled nonlinear
systems, Systems Control Lett. 11 (3) (1988) 229–234.
[35] J. Tokarzewski, Finite Zeros in Discrete Time Control Systems, vol. 338,
Springer, 2006.
[36] A. Isidori, The zero dynamics of a nonlinear system: from the origin to the
latest progresses of a long successful story, Eur. J. Control 19 (5) (2013)
369–378.
[37] W.M. Wonham, A.S. Morse, Decoupling and pole assignment in linear
multivariable systems: a geometric approach, SIAM J. Control 8 (1) (1970)
1–18.
[38] G. Basile, G. Marro, Controlled and Conditioned Invariants in Linear System
Theory, Prentice Hall, Englewood Cliffs, NJ, 1992.
[39] B.D. Anderson, Output-nulling invariant and controllability subspaces, IFAC
Proc. Vol. 8 (1) (1975) 337–345.
[40] B. Anderson, A note on transmission zeros of a transfer function matrix,
IEEE Trans. Automat. Control 21 (4) (1976) 589–591.
[41] E.D. Sontag, Mathematical Control Theory: Deterministic Finite Dimensional Systems, Springer, 1990.
[42] H. Chen, P. Tiňo, X. Yao, Cognitive fault diagnosis in Tennessee Eastman
Process using learning in the model space, Comput. Chem. Eng. 67 (2014)
33–42.
[43] B.C. Juricek, D.E. Seborg, W.E. Larimore, Identification of the Tennessee
Eastman challenge process with subspace methods, Control Eng. Pract. 9
(12) (2001) 1337–1351.
[44] H. Faris, A. Sheta, Identification of the Tennessee Eastman chemical process
reactor using genetic programming, Intl. J. Adv. Sci. Technol. 50 (2013)
121–140.
Syed Ahmed Pasha: Conceptualization, Methodology, Writing – review & editing, Supervision. Ayesha Ayub: Software,
Validation, Investigation, Writing – original draft, Visualization.
Declaration of competing interest
The authors declare that they have no known competing financial interests or personal relationships that could have appeared
to influence the work reported in this paper.
References
[1] R. Alur, K.-E. Arzen, J. Baillieul, T. Henzinger, Handbook of Networked and
Embedded Control Systems, Springer Science & Business Media, 2007.
[2] J.P. Hespanha, P. Naghshtabrizi, Y. Xu, A survey of recent results in
networked control systems, Proc. IEEE 95 (1) (2007) 138–162.
[3] A. Cardenas, S. Amin, B. Sinopoli, A. Giani, A. Perrig, S. Sastry, Challenges
for securing cyber physical systems, in: Workshop on Future Directions in
Cyber-Physical Systems Security, vol. 5, 2009.
[4] F. Pasqualetti, F. Dörfler, F. Bullo, Cyber-physical attacks in power networks: Models, fundamental limitations and monitor design, in: 50th
IEEE Conf. Decision and Control and European Control Conf., 2011, pp.
2195–2201.
[5] A. Teixeira, D. Pérez, H. Sandberg, K.H. Johansson, Attack models and
scenarios for networked control systems, in: Proc. 1st Intl. Conf. High
Confidence Networked Systems, 2012, pp. 55–64.
[6] H. Fawzi, P. Tabuada, S. Diggavi, Secure estimation and control for cyberphysical systems under adversarial attacks, IEEE Trans. Automat. Control
59 (6) (2014) 1454–1467.
[7] R. Taormina, S. Galelli, N.O. Tippenhauer, E. Salomons, A. Ostfeld, Characterizing cyber-physical attacks on water distribution systems, J. Water
Resour. Plan. Manag. 143 (5) (2017).
[8] V.L. Do, L. Fillatre, I. Nikiforov, P. Willett, Security of SCADA systems against
cyber–physical attacks, IEEE Aerosp. Electron. Syst. Mag. 32 (5) (2017)
28–45.
[9] R. Langner, Stuxnet: Dissecting a cyberwarfare weapon, IEEE Secur. Priv. 9
(3) (2011) 49–51.
[10] J.P. Farwell, R. Rohozinski, Stuxnet and the future of cyber war, Survival
53 (1) (2011) 23–40.
[11] Y. Mo, B. Sinopoli, Secure control against replay attacks, in: 47th Annual
Allerton Conf. Communication, Control, and Computing, 2009, pp. 911–918.
[12] Y. Liu, P. Ning, M.K. Reiter, False data injection attacks against state
estimation in electric power grids, ACM Trans. Inf. Syst. Secur. 14 (1)
(2011) 1–33.
[13] A. Teixeira, I. Shames, H. Sandberg, K.H. Johansson, Revealing stealthy
attacks in control systems, in: 50th Annual Allerton Conf. Communication,
Control, and Computing, 2012, pp. 1806–1813.
[14] S. Amin, A.A. Cárdenas, S.S. Sastry, Safe and secure networked control
systems under denial-of-service attacks, in: Proc. 12th Intl. Conf. Hybrid
Systems: Computation and Control, 2009, pp. 31–45.
[15] Y. Yuan, Q. Zhu, F. Sun, Q. Wang, T. Başar, Resilient control of cyberphysical systems against denial-of-service attacks, in: 6th Intl. Symp.
Resilient Control Systems, 2013, pp. 54–59.
[16] H. Zhang, P. Cheng, L. Shi, J. Chen, Optimal denial-of-service attack
scheduling with energy constraint, IEEE Trans. Automat. Control 60 (11)
(2015) 3023–3028.
[17] G.K. Befekadu, V. Gupta, P.J. Antsaklis, Risk-sensitive control under Markov
modulated denial-of-service (DoS) attack strategies, IEEE Trans. Automat.
Control 60 (12) (2015) 3299–3304.
[18] C. De Persis, P. Tesi, Input-to-state stabilizing control under denial-ofservice, IEEE Trans. Automat. Control 60 (11) (2015) 2930–2944.
107