A Voice-Activated Undergraduate
Computer Science Advising System
Submitted to:
Professor. Hubert A. Johnson
Software Engineering & Reliability
CSIT 515_01 FALL22
Submitted by: Geek Squad
NAME /CWID
EMAIL-ID/PHONE
SANDEEP RAO REDDIMALLA (50062206)
REDDIMALLAS1@MONTCLAIR.EDU
ESWAR SAI KORRAPATI (50066572)
KORRIPATIE1@MONTCLAIR.EDU
ADITYA KATKOJU (50059105)
KATKOJUA1@MONTCLAIR.EDU
HARI PRIYA RETNENI (50065577)
RETNENIH1@MONTCLAIR.EDU
SRUJAN GAMBIRRAO (50069072)
GAMBIRRAOS1@MONTCLAIR.EDU
1
ACKNOWLEDGEMENT
We are pleased to present “A Voice-Activated Undergraduate Computer Science Advising System”
project and take this opportunity to express our profound gratitude to all those people who
helped us in completion of this project.
We express our deepest gratitude towards our Prof. Hubert Johnson who gave a
valuable and timely advice during the various phases in our project. We would also like
to thank him for providing us with all proper facilities and support. We would like to
thank her for support, patience, and faith in our capabilities and for giving us flexibility in
terms of working and reporting schedules.
1
ABSTRACT
Voice recognition system: speech-to-text is a software that lets the user control computer
functions and dedicates text by voice. The system consists of two components, first
component is for processing acoustic signal which is captured by a microphone and second
component is to interpret the processed signal, then mapping of the signal to words. model
for each letter will be built using Hidden Markov Model (HMM). feature extraction will
be done using Mel Frequency Cepstral Co-efficient (MFCC). Feature training of the data
set will be done using vector quantization and feature testing of the data set will be done
using Viterbi algorithm. Home automation will be completely based on voice recognition
system.
Keywords: Voice recognition, MFCC, HMM, Vector quantization, Viterbi algorithm,
PHP, SQL.
2
LIST OF FIGURES
Figure 3.1.1: overview of voice recognization system
15
Figure 4.1.1: voice activated advising system Flowchart
21
Figure 4.1.2: Sequence Diagram of voice activated advising system
22
Figure 4.1.3: Class Diagram
23
Figure 4.1.4: Use case diagram
24
Figure 5.1: Phase of Software Development
29
3
LIST OF TABLES
Table 3.4.1: Client-side Hardware requirement
19
Table 3.4.2: Client-side Software requirement
20
Table 5.4.4: Module Test Cases
31
4
LIST OF ABBREVIATIONS
CSS
Cascading Style Sheets
GUI
Graphical User Interface
HDD
Hard Disk Drive
HTML
Hypertext Markup Language
HTTP
Hyper Text Transfer Protocol
HTTPs
Hyper Text Transfer Protocol Secured
SDLC
System Development Life Cycle
UML
Unified Modeling Language
GPIS
Graphical Password through Image Segmentation
PHP
Hypertext Preprocessor
SQL
Structured Query Language
5
Table of Contents
ACKNOWLEDGEMENT ............................................................................................... 1
ABSTRACT .................................................................................................................... 2
LIST OF FIGURES ......................................................................................................... 3
LIST OF ABBREVIATIONS .......................................................................................... 5
CHAPTER 1: INTRODUCTION .................................................................................... 9
1.1 Introduction of the Project ......................................................................................9
1.2 Objective ............................................................................................................. 11
1.3 Problem Statement ............................................................................................... 11
1.4 Purpose ................................................................................................................ 11
1.5 Intended Audience ............................................................................................... 11
CHAPTER 2: LITERATURE REVIEW ........................................................................ 12
2.1 Existing System Review ...................................................................................... 12
CHAPTER 3: SYSTEM ANALYSIS ............................................................................ 15
3.1 Requirement Analysis .......................................................................................... 15
3.1.1 Functional Requirements ............................................................................... 15
3.1.2 Non- Functional Requirements ...................................................................... 16
3.2 Feasibility Study .................................................................................................. 17
3.2.1 Technical Feasibility ..................................................................................... 18
3.2.2 Economical Feasibility .................................................................................. 18
3.2.3 Operational Feasibility .................................................................................. 18
3.2.4 Schedule Feasibility ...................................................................................... 18
3.4 Technical Requirement ........................................................................................ 19
6
3.4.1 System Hardware Architecture ...................................................................... 19
3.4.2 System software architecture ......................................................................... 19
CHAPTER 4: SYSTEM DESIGN ................................................................................. 21
4.1 System Design ..................................................................................................... 21
4.1.1 System Flow Diagram ................................................................................... 21
4.1.2 Sequence Diagram ........................................................................................ 22
4.1.3 Class Diagram ............................................................................................... 23
4.1.4 Use Case Diagram ......................................................................................... 24
CHAPTER 5: IMPLEMENTATION AND TESTING ................................................... 25
5.1 Implementation .................................................................................................... 25
5.2 Tools Used ........................................................................................................... 25
5.2.1 Front End Tools ............................................................................................ 25
5.2.2 Back-End Tools ............................................................................................ 26
5.2.3 Documentation Tools .................................................................................... 27
5.2.4 Coding tools .................................................................................................. 27
5.3 Development Methodology .................................................................................. 27
5.4 Testing ................................................................................................................. 29
5.4.1 Unit Testing .................................................................................................. 29
5.4.2 Integration Testing ........................................................................................ 29
5.4.3 System Testing .............................................................................................. 30
5.4.4 Module Test Cases ........................................................................................ 30
7
CHAPTER 6: CONCLUSION ....................................................................................... 32
6.1 Conclusion: .......................................................................................................... 32
APPENDICES ............................................................................................................... 35
8
CHAPTER 1: INTRODUCTION
1.1 Introduction of the Project
Voice is the basic, common, and efficient form of communication method for people to interact
with each other. Today speech technologies are commonly available for a limited but interesting
range of task. These technologies enable machines to respond correctly and reliably to human
voices and provide useful and valuable services. As communicating with computer is faster using
voice rather than using keyboard, so people will prefer such system. Communication among the
human being is dominated by spoken language, therefore it is natural for people to expect voice
interfaces with computer. This can be accomplished by developing voice recognition system:
speech-to-text which allows computer to translate voice request and dictation into text. Voice
recognition system: speech-to-text is the process of converting an acoustic signal which is captured
using a microphone to a set of words. The recorded data can be used for document preparation. 2.
Classification of speech recognition system: Speech recognition system can be classified in several
different types by describing the type of speech utterance, type of speaker model and type of
viability that they have ability to recognize. The challenges are briefly explained below:
A. Types of speech utterance Speech recognition are classified according to what type of utterance
they have ability to recognize. They are classified as: 1) Isolated word: Isolated word recognizer
usually requires each spoken word to have quiet (lack of an audio signal) on bot h side of the
sample window. It accepts single word at a time. 2) Connected word: It is like isolated word, but
it allows separate utterances to „run-together‟ which contains a minimum pause in between them.
3) Continuous Speech: it allows the users to speak naturally and in parallel the computer will
determine the content. 4) Spontaneous Speech: It is the type of speech which is natural sounding
and is not rehearsed.
B. Types of speaker model Speech recognition system is broadly into two main categories based
on speaker models namely speaker dependent and speaker independent.
9
1) Speaker dependent models: These systems are designed for a specific speaker. They are easier
to develop and more accurate, but they are not so flexible. 2) Speaker independent models: These
systems are designed for variety of speaker. These systems are difficult to develop and less
accurate, but they are very much flexible.
C. Types of vocabulary the vocabulary size of speech recognition system affects the processing
requirements, accuracy, and complexity of the system. In voice recognition system: speech-to-text
the types of vocabularies can be classified as follows: 1) Small vocabulary: single letter. 2)
Medium vocabulary: two or three letter words. 3) Large vocabulary: more letter words
3. Survey of research papers:
Academic advising is an important and time-consuming task and different tools, and techniques
can be used to make it an effective and efficient process. Most of the process, however, relies on
personal interactions between students and advisors, which leads to problems such as
inconsistencies among different advisors and poor utilization of resources, since very often a good
portion of the advisors’ time is spent answering recurrent questions and solving trivial class
scheduling problems. In response to these problems, the Department of Computer Science and
Engineering (CSE) at Florida Atlantic University (FAU) has been working since 1999 on a project
that supplements the conventional advising process with a voice activated advising system. The
CSE department at FAU currently has approximately 700 undergraduate Computer Science (CS)
and 300 undergraduate Computer Engineering (CE) students. Advising undergraduate CS and CE
students is an important and time-consuming task in the department. To accomplish it effectively
and efficiently several different
10
1.2 Objective
The objective of this project is:
It allows a student who’s major or minor is Computer Science or IT to obtain automatic
advising from the system pertaining to appropriate course.
It also tells that which courses need to be taken by the student at a particular semester to
complete his degree.
1.3 Problem Statement
The overall motive of the project is that “It allows a student who’s major or minor is
Computer Science or IT to obtain automatic advising from the system pertaining to
appropriate course which needs to be taken and which courses the students permitted to
take at a particular juncture during their pursuit of the degree.
1.4 Purpose
This software requirement specification (SRS) article defines the " A Voice-Activated
Undergraduate Computer Science Advising System " in both functional and non-functional
terms. The system's scope, vision, use case, features, and other associated requirement concerns
are detailly described after the working and objectives are briefly outlined. This document should
be referred to as the functional model of the system in later phases of the project, such as system
design, database design, implementation, and testing.
1.5 Intended Audience
The document is intended for a variety of readers, including developers, administrators, and
authorized users. The rest of this SRS includes an overall description, needs for external
interfaces, system features, and other non-functional requirements.
11
CHAPTER 2: LITERATURE REVIEW
The project aims to provide a feature and content-rich web application that allows computer
science or IT students to register for courses
2.1 Existing System Review
Kuldip K. Paliwal and et al in the year 2004 had discussed that without being affected by their
popularity for front end parameter in speech recognition, the cepstral coefficients which had been
obtained from linear prediction analysis is sensitive to noise. Here, the use of spectral sub band
centroids had been discussed by them for robust speech recognition. They discussed that
performance of recognition can be achieved if the centroids are selected properly as in comparison
with MFCC. to construct a dynamic centroid feature vector a procedure had been proposed which
essentially includes the information of transitional spectral information. Esfandier Zavarehei and
et al in the year 2005, studied that a time-frequency estimator for enhancement of noisy speech
signal in DFT domain is introduced. It is based on low order auto regressive process which is used
for modelling. The time-varying trajectory of DFT component in speech which has been formed
in Kalman filter state equation. For restarting Kalman filter, a method has been formed to make
alteration on the onsets of speech. The performance of this method was compared with parametric
spectral subtraction and MMSE estimator for the increment of noisy speech. The resultant of the
proposed method is that residual noise is reduced and quality of speech in improved using Kalman
filters [2]. Ibrahim Patel and et al in the year 2010, had discussed that frequency spectral
information with Mel frequency is used to present as an approach in the recognition of speech for
improvement of speech, based on recognition approach which is represented in HMM. A
combination of frequency spectral information in the conventional Mel spectrum which is based
on the approach of speech recognition. The approach of Mel frequency utilizes the frequency
observation in speech within a given resolution resulting in the overlapping of resolution feature
which results in the limit of recognition. In speech recognition system, which is based on HMM,
resolution decomposition is used with a mapping approach in a separating frequency. The result
of the study is that there is an improvement in quality metrics of speech recognition with respect
to the computational time and learning accuracy in speech recognition system. Kavita Sharma and
Prateek Hakar in the year 2012 has represented recognition of speech in a broader solution. It refers
12
to the technology that will recognize the speech without being targeted at single speaker.
Variability in speech pattern, in speech recognition is the main problem. Speaker characteristics
which include accent, noise and co-articulation are the most challenging sources in the variation
of speech. In speech recognition system, the function of basilar membrane is copied in the frontend of the filter bank. To obtain better recognition results it is believed that the band subdivision
is closer to the human perception. In speech recognition system the filter which is constructed for
speech recognition is estimated of noise and clean speech. Puneet Kaur, Bhupender Singh, and
Neha Kapur in the year 2012 had discussed how to use Hidden Markov Model in the process of
recognition of speech. To develop an ASR (Automatic Speech Recognition) system the essential
three steps necessary are pre-processing, feature Extraction and recognition and finally hidden
markov model is used to get the desired result. Research persons are continuously trying to develop
a perfect ASR system as there are already huge advancements in the field of digital signal
processing but at the same time performance of the computer are not so high in this field in terms
of speed of response and matching accuracy. The three different techniques used by research
fellows are acoustic phonetic approach, pattern recognition approach and knowledge-based
approach.
Chadawan Ittichaichareon and Patiyuth Pramkeaw in the year 2012 had discussed that signal
processing toolbox has been used to implement the low pass filter with finite impulse response.
Computational implementation and analytical design of finite impulse response filter has been
successfully accomplished by performing the performance evaluation at signal to noise ratio level.
The results are improved in terms of recognition when low pass filters are used as compared to
those process which involves speech signal without filtering. Geeta Nijhawan, Poonam Pandit and
Shivanker Dev Dhingra in the year 2013 had discussed the techniques of dynamic time warping
and Mel scale frequency cepstral coefficient in the isolated speech recognition. Different features
of the spoken word had been extracted from the input speech. A sample of 5 speakers has been
collected and each had spoken 10 digits. A database is made on this basis. Then feature has been
extracted using MFCC.DTW is used for effectively dealing with various speaking speed. It is used
for similarity measurement between two sequence which varies in speed and time.
13
2.2 Table Comparison:
Table 1: Table of comparison.
14
CHAPTER 3: SYSTEM ANALYSIS
3.1 Requirement Analysis
Requirement analysis for this study has been done by first identifying key factors that will affect
the project and key people who will be affected by the project. Every system needs some
requirements for development process. Without requirements the system cannot be developed. It
includes:
3.1.1 Functional Requirements
The functional requirement for a system should describe what the system do or perform. These
requirements depend on the type of software being developed, the expected user of the software
and the general approach taken by the organization when writing requirements. Functional
requirements describe system function in detail with its input, output, and so on. The proposed
system allows user to register for classes and edit or drop them. The next time, the user logs on to
the system the courses he registered should be visible. Then the project is said to be done.
Overview of Voice Recognition System:
Figure 3.1.1: Overview of Voice Recognition System: Speech-to-text.
15
Input signal- Voice input by the user. Feature Extraction- it should retain useful information of the
signal, deduct redundant and unwanted information, show less variation from one speaking
environment to another, occur normally and naturally in speech. Acoustic model- it contains
statistical representations of each distinct sounds that makes up a word. Decoder- it will decode
the input signal after feature extraction and will show the desired output. Language model- it
assigns a probability to a sequence of words by means of a probability distribution. Outputinterpreted text is given by the computer. The main of the project is to recognize speech using
MFCC and VQ techniques. The feature extraction will be done using Mel Frequency Cepstral
Coefficients (MFCC). The steps of MFCC are as follows: 1) Framing and Blocking
2) Windowing
3) FFT (Fast Fourier Transform)
4) Mel-Scale
5) Discrete Cosine Transform (DCT) Feature matching will be done using Vector Quantization
technique.
The steps are as follows: 1) By choosing any two dimensions, inspection on vectors is done and data points are plotted.
2) To check whether data region for two different speakers are overlapping each other and in same
cluster, observation is needed.
3) Using LGB algorithm Function Vqlbg will train the VQ codebook. The extracted features will
be stored in .mat file using MFCC algorithm. Models will be created using Hidden Markov Model
(HMM). The desired output will be shown in MATLAB interface.
3.1.2 Non- Functional Requirements
There are constraints on the services or functions offered by “ A Voice-Activated Undergraduate
Computer Science Advising System” such as timing constraints, constraints on the development process,
standards, etc. After conducting requirement analysis some of the non-functional requirements
were find out. Some of them are listed that are useful to restate the problem definition are given
below:
● User Interface:
16
o The system maintains an easy-to-use interface across all functionalities and for all
users.
o The client’s user interface is compatible with all commonly used browsers.
● Scalability:
o Some systems can’t provide the high-level security when the data to be embedded
is large. In that case, scalability plays major role.
● Portability:
o The system is run on a variety of web browsers including chrome, Mozilla Firefox
etc.
● Maintainability:
o There is a clear separation of back end and front end.
o There is a clear separation between the data access objects that map the database
and the business logic code.
● Availability:
o The program should provide the security from unauthorized modifications.
o The program should be flexible and should be available within a mean time and
should work in any operating system
3.2 Feasibility Study
Voice activated advising system uses simple development tools and uses no physical hardware
devices. Beside this, it contains single database which is feasible and easy to develop and maintain.
Voice system for administration use only computers and internet.
In a concise way, a feasibility study evaluates the project’s potential for success. There are some
feasibility studies which will be performed on the project working.
Some of the feasibility studies are:
Technical Feasibility
Operational Feasibility
Economic Feasibility
Schedule Feasibility
17
3.2.1 Technical Feasibility
The system uses simple development tools and use no physical hardware devices. Beside this, it is
feasible and easy to develop and maintain. voice system for administration uses only computers,
and internet. On the other hand, web app uses personal data or existing Wi-Fi technology which is
technically feasible.
3.2.2 Economical Feasibility
Voice activated advising system is economically feasible since it can be used through a single
computer device having internet access. This application is economically feasible because this
application is made using open-source software and the time spend in the development of this
application is 3 months.
3.2.3 Operational Feasibility
The system can easily be developed under less operational effort and can be implemented under
current technology. User with low technical knowledge may get deprive from the benefits that the
system provides but rapid increase in use of smart device which made this system easily accessible
to all level users.
3.2.4 Schedule Feasibility
Schedule Feasibility is the probability of a project to be completed within its scheduled time limits,
by a planned due date. If a project has a high probability to be completed on-time, then its schedule
feasibility is appraised as high. Schedule feasibility study includes use of Project Estimation and
Gantt charts.
To make sure the project is completed before it loses it utility, one had to give proper attention to
controlling the schedule feasibility: to calculate and continually reexamine whether it is possible
to complete all amount of work lying ahead within specified time in the Gantt chart.
18
3.4 Technical Requirement
3.4.1 System Hardware Architecture
Hardware architecture refers to the identification of a system’s physical components and their
interrelationships. This allows to understand how the components fit into a system architecture
and provides information needed for the software development and integration. If these following
hardware configurations are met, the system will run smoothly.
Client-side Hardware Requirements
Requirements
Minimum Specification
Processor
I3 Processor Based Computer
RAM
2 GB
HDD
5 GB
Display
Monitor
Table 3.4.1: Client-Side Hardware Requirement
3.4.2 System software architecture
The system software architecture refers to the high level of structures of a software system and the
discipline of creating such structures, and system. Each structure comprises software elements,
relations among them. The architecture has been designed with various semi structures of the parts
of the software phases.
19
Client-side Software Requirements
Requirements
Minimum Specification
Host Operating System
Windows 7 or higher
Browser
Edge, Firefox 3.5+, Chrome, Opera 9+
Protocols
TCP/IP, HTTP, SMTP, HTTPS
Table 3.4.2: Client-Side Software Requirement
20
CHAPTER 4: SYSTEM DESIGN
4.1 System Design
System design is the process of defining the elements of a system such as the architecture, modules
and components, the different interfaces of those components and the data that goes through that
system. It is meant to satisfy specific needs and requirements of a business or organization through
the engineering of a coherent and well-running system.
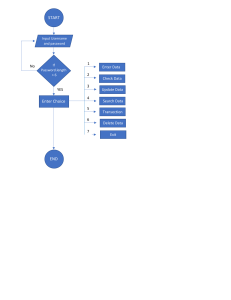
4.1.1 System Flow Diagram
The flow chart given below shows the flow of the system briefly which simplifies the prominent
working of the system.
Fig 4.1.1: Voice Activated Advising System Flowchart
21
4.1.2 Sequence Diagram
Sequence Diagrams are interaction diagrams that detail how operations are carried out. They
capture the interaction between objects in the context of a collaboration. Sequence Diagrams are
time focus, and they show the order of the interaction visually by using the vertical axis of the
diagram to represent time what messages are sent and when. The sequence diagram for the system
is shown below:
Fig 4.1.2: Sequence Diagram of voice activated advising system
22
4.1.3 Class Diagram
Class diagrams are the blueprints of your system or subsystem. You can use class diagrams to
model the objects that make up the system, to display the relationships between the objects, and
to describe what those objects do and the services that they provide. Class diagrams are useful in
many stages of system design. Operations are descriptions of behavioral or dynamic features of a
class The below is a class diagram of the system that shows the flow of system through different
phases.
Fig 4.1.3: Class Diagram
23
4.1.4 Use Case Diagram
A use-case model is a model of how different types of users interact with the system to solve a
problem. As such, it describes the goals of the users, the interactions between the users and the
system, and the required behavior of the system in satisfying these goals.
A use-case model consists of several model elements. The most important model elements are
use cases, actors and the relationships between them.
Fig 4.1.4: Use case diagram: voice activated advising system
24
CHAPTER 5: IMPLEMENTATION AND TESTING
5.1 Implementation
There are five major tasks in this phase: coding, testing, installation, documentation, and training.
The purpose of this phase is to convert the physical system specifications into working and reliable
software and hardware, document the work that have been done and provide help for current and
future users. The application is developed in keeping the user’s perspective. The application is
targeted to the end use so it must fulfill the requirement of the users. Various tools and coding
languages are used, which are very essential for the development of the application.
5.2 Tools Used
We have used various tools throughout the project. For Front end design, for diagrammatic
representation, flow diagrams, Activity diagrams, for documentation purposes etc.
5.2.1 Front End Tools
Javascript, HTML, CSS:
HTML is used for the design of the webpage.
CSS is used for styling of the webpage.
Javascript is used for interaction with backend tools like PHP and SQL.
Data Source Controls
For binding data to controls on Web pages, you can now use data source controls, which
encapsulate connections, query commands, and parameters into a single control. It includes
data source controls that work with a variety of back-end data sources, including Microsoft
SQL Server, Microsoft Access, XML files, Web services, FrontPage site maps, and business
objects that return data sets. All data source controls support the same basic object model,
giving you a consistent way to work with data regardless of its source.
25
Data source controls can automatically fetch data and manage it when the page runs. You
no longer need to write code to execute commands and manage datasets for common data
scenarios.
To pass parameters to data source controls, you can configure the controls to draw
parameters values from other controls, Session state, query strings, or cookies; in addition, you
can set parameter values programmatically.
5.2.2 Back-End Tools
PHP
It is used to interact with databases by creating dynamic content. It is a server-side
scripting language.
Microsoft SQL Server 2005
Microsoft® SQL Server™ 2005is a set of components that work together to meet the data
storage and analysis needs of the largest Web sites and enterprise data processing systems.
The topics in SQL Server Architecture describe how the various components work together
to manage data effectively.
Microsoft® SQL Server™ 2005data is stored in databases. The data in a database is
organized into the logical components visible to users. A database is also physically
implemented as two or more files on disk.
Each instance of SQL Server has four system databases (master, model, temp db
and msdb) and one or more user databases (hmd db, Address Book, payroll, sales,
employees). Some organizations have only one user database, containing all the data for
their organization. Some organizations have different databases for each group in their
organization, and sometimes a database used by a single application. For example, an
organization could have one database for sales, one for payroll, one for a document
management application, and so on. Sometimes an application uses only one database;
other applications may access several databases.
26
It is not necessary to run multiple copies of the SQL Server database engine to allow
multiple users to access the databases on a server. An instance of the SQL Server Standard
or Enterprise Edition is capable of handling thousands of users working in multiple
databases at the same time. Each instance of SQL Server makes all databases in the instance
available to all users that connect to the instance, subject to the defined security
permissions.
When connecting to an instance of SQL Server, your connection is associated with a
particular database on the server. This database is called the current database.
5.2.3 Documentation Tools
● Microsoft Word: It is a graphical word processing program that users can type with. It is
made by the computer company Microsoft. In our project Microsoft word is used for
documentation process.
● Draw.io: Draw.io, a web application, is a production-grade, open-source technology stack for
building diagramming applications, and the world’s most widely used browser-based end user
diagramming application. In our project it is used to create diagrams in a simple and
convenient way this tool is used.
5.2.4 Coding tools
● XAMPP: Sublime Text editor is the text editor used for coding purpose. Sublime Text is a
sophisticated text editor used for coding purpose. It has the slick user interface, extraordinary
features, and amazing performance. Some of its major features for selection of this code editor
are code preview, fast performance, div highlighting, plugin community, configurability,
lightning-fast loading, and better stability.
5.3 Development Methodology
After some research, I discovered that the processing of the data should be highly structured and
very well understood in the many different stages. Therefore, we chose waterfall model as the
software development model. The waterfall model is executed in sequential phases. For each
phase, we would need to identify the different tasks that are being needed to perform and this
27
would allow tracking of the progress easily before proceeding to the next phase. As such, these
datelines will act as milestones to know whether the project is on schedule, behind schedule or in
front of schedule. All these makes monitoring of the progress of the whole schedule easier.
So, it can be concluded that with the use of the waterfall model, the developer can execute a high
level of control on the progress of the whole project and a higher quality of the design and
implementation of the different phases of the projects can be expected with this tighter control on
the project as each phase is to be complete with satisfaction before proceeding to the next phase.
As the Waterfall Model illustrates the software development process in a linear sequential flow;
hence it is also referred to as a Linear-Sequential Life Cycle Model (Brien, 2011). It is very simple
to understand and use. In a waterfall model, each phase must be completed before the next phase
can begin and there is no overlapping in the phases. The Waterfall model is the earliest SDLC
approach that was used for software development. The waterfall Model illustrates the software
development process in a linear sequential flow. This means that any phase in the development
process begins only if the previous phase is complete. In this waterfall model, the phases do not
overlap.
Fig 5.1: Phases of Software development
28
5.4 Testing
After the code was developed in the coding phase, the codes were tested to check whether it
complied with the requirements and that the code solved the needs that were addressed in the
requirements phase. Testing has been done for the individual activities of the project. Errors that
occurred were corrected and further debugging was performed. In testing phase, various units,
modules, interfaces were tested. Different types of testing methods like unit testing, system testing
was conducted.
5.4.1 Unit Testing
Unit Testing is done to verify that each unit function properly. After the coding of modules, they
were tested, made error free and debugged. In this way we carried out the unit test. Some of them
are listed on the table. In this testing phase, each function/ module like login and send message
feature were tested before integrating. The errors were corrected, and modifications were done
according to the requirement.
5.4.2 Integration Testing
Integration testing (I&T) is a software development process in which program modules are
merged and tested as a group in a variety of methods. A unit is the smallest tested portion of an
application in this context. Integration testing can reveal issues with software component
interfaces before they become difficulties in real-world program operation. Integration testing is
a part of Extreme Programming, a pragmatic software development strategy that takes a
thorough approach to producing a product through continuous testing and revision.
The bottom-up approach and the top-down method are the two main methods for performing an
integration test. Unit testing is the first step of bottom-up integration testing, which is followed
by tests of increasingly higher-level combinations of units termed modules or builds. The
highest-level modules are checked first in top-down integration testing, followed by increasingly
lower-level modules. Bottom-up testing is frequently done first in a thorough software
development environment, followed by top-down testing.
29
5.4.3 System Testing
System testing is a level of software testing where a complete and integrated software is tested.
The purpose of this test is to evaluate the system’s compliance with the specified requirements.
This testing is done to check whether the system works accurately and efficiently before live
operation commences. In this testing, the whole web application is tested including its
responsiveness, log-in, sign-up, send message feature.
5.4.4 Module Test Cases
Login Registration
Cas
e#
Tester
Permissi
on Level
Page
1
0
Login
Page
Test Case
Tester fills out
all entry
information
and clicks
login.
Expected Actual Result
Result
Login
Succ
essfu
l
Login
Successful.
Result
Pass
30
database, the
system will
display
registration
successful, and
the user will be
able to Login
into the
homepage
using the
created
credentials.
2
0
Click on start
Should ask
microphone
access.
Displays the
microphone
access
Pass
3
1
Say semesters
It should
display three
semesters
Spring 2023,
Fall 2023,
Spring 2024.
Displays the
three
semesters
Pass
4
1
Say semester name
It should get
into particular
semester.
It goes into
particular
semester
Pass
5
2
Say course names
It should
display all the
courses listed
It displays all
courses
Pass
6
2
Select Course
It should add
the course
It adds the
described
course
Pass
7
3
Add/Drop
It should add
new courses or
drop the older
ones.
It adds or
drops courses
Pass
8
4
Logout
It should
logout from
the website
It logs out
Pass
31
CHAPTER 6: CONCLUSION
6.1 Conclusion:
In this work the fundamentals are discussed, and its recent progress is investigated. The various
approaches available for developing a Voice Recognition System based on adapted feature
extraction technique and the speech recognition approach for the language are compared in
this paper. The main aim of our project is to develop a system that will allow the computer
science or it to register for courses through voice detection and help them get the degree
certificate.
32
REFERENCES
[1] Jindong Chen, Member, Yutong (Arden) Huang, Qi Li, Kuldip K. Pallial, “Recognition of
Noisy Speech using Dynamic Spectral Subban Centroids” IEEE SSIGNAL PROCESSING
LETTERS, Vol. 11, Number 2, February 2004.
[2] Hakam Erdogan, Ruchi Sari kaya, Yuqin Gao, “Using semantic analysis to improve speech
recognition performance” Computer Speech and Language, ELSEVIER 2005.
[3] Carawan Ittichaichareon, Patiyuth Pramkeaw, “Improving MFCC-based Speech
Classification with FIR Filter” International Conference on Computer Graphics, Simulation
and Modelling (ICGSM‟2012) July 28-29, 2012, Pattaya (Thailand).
[4] Bhupinder Singh, Neha Kapur, Puneet Kaur “Speech Recognition with Hidden Markov
Model: A Review” International Journal of Advanced Research in Computer and Software
Engineering, Vol. 2, Issue 3, March 2012. [5] Shivanker Dev Dhingra, Geeta Nijhawan,
Poonam Pandit, “Isolated Speech Recognition using MFCC and DTW” International Journal
of Advance Research in Electrical, Electronics and Instrumentation Engineering, Vol.2, Issue
8, August 2013.
[6] Ibrahim Patel, Dr. Y. Srinivas Rao, “Speech Recognition using HMM with MFCC-an
analysis using Frequency Spectral Decomposition Technique” Signal and Image Processing:
An International Journal (SIPIJ), Vol.1, Number.2, December 2010.
[7] Om Prakash Prabhakar, Navneet Kumar Sahoo” A Survey on Voice Command Recognition
Technique” International Journal of Advanced Research in Computer and Software
Engineering, Vol 3, Issue 5, May 2013. [8] M A Abusua, “Speech recognition by Machine”,
International Journal of Computer Science and Information security, Vol. 6, number 3,2009.
[9] Sikha Gupta, Jafreezal Jaafar, Wan Fatimah wan Ahmad, Arpit Bansal, “Feature
Extraction Using MFCC” Signal & Image Processing: An International Journal, Vol 4, No. 4,
August 2013.
33
[10] Kavita Sharma, Prateek Hakar “Speech Denoising Using Different Types of Filters”
International journal of Engineering Research and Applications Vol. 2, Issue 1, Jan-Feb 2012
34
APPENDICES
A voice-based unlock system for our computer will be the application that will take our voice
as input and process that voice converts it into a text-based instruction for our computer and
then perform an action based on that instruction. This process uses The State-of-the-art
process in a speech to text, Natural Language Understanding, and Deep Learning in the text
to speech.
The first step to build a voice-based application in our application is to listen to the user’s
voice command.
Codes:
getdata.php
<?php
include 'config.php';
$searchText = $_POST['speechText'];
// search query
$query = 'SELECT * FROM posts WHERE title like "%'.$searchText.'%" or content
like "%'.$searchText.'%" ';
$result = mysqli_query($con,$query);
$html = '';
if(mysqli_num_rows($result) > 0){
while($row = mysqli_fetch_array($result)){
$id = $row['id'];
$title = $row['title'];
35
$content = $row['content'];
$shortcontent = substr($content, 0, 160)."...";
// $link = $row['link'];
// Creating HTML structure
$html .= '<div id="post_'.$id.'" class="post"> <a href="adding.php">Add </a>';
$html .= '<h1>'.$title.'</h1>';
$html .= '<p>'.$shortcontent.'</p>';
// $html .= '<a href="'.$link.'" class="more" target="_blank">More</a>';
$html .= '</div>';
}
}else{
$html .= '<div >';
$html .= '<p>No Record Found.</p>';
$html .= '</div>';
}
echo $html;
exit;
edit.php
<?php
// including the database connection file
include_once("config.php");
if(isset($_POST['update']))
{
$id = mysqli_real_escape_string($con, $_POST['id']);
$name = mysqli_real_escape_string($con, $_POST['name']);
36
// $age = mysqli_real_escape_string($mysqli, $_POST['age']);
// $email = mysqli_real_escape_string($mysqli, $_POST['email']);
// checking empty fields
if(empty($name) ) {
// if(empty($name)) {
//
echo "<font color='red'>Name field is empty.</font><br/>";
// }
// if(empty($age)) {
//
echo "<font color='red'>Age field is empty.</font><br/>";
// }
// if(empty($email)) {
//
echo "<font color='red'>Email field is empty.</font><br/>";
// }
} else {
//updating the table
$result = mysqli_query($con, "UPDATE courses SET name='$name'
WHERE id=$id");
//redirecting to the display page. In our case, it is index.php
header("Location: index.php");
}
}
?>
<?php
//getting id from url
$id = $_GET['id'];
//selecting data associated with this particular id
$result = mysqli_query($con, "SELECT * FROM courses WHERE id=$id");
while($res = mysqli_fetch_array($result))
{
$name = $res['name'];
}
?>
<html>
<head>
<title>Edit Data</title>
</head>
<body>
37
<a href="index.php">Home</a>
<br/><br/>
<form name="form1" method="post" action="edit.php">
<table border="0">
<tr>
<td>Name</td>
<td><input type="text" name="name" value="<?php echo
$name;?>"></td>
</tr>
<tr>
<td><input type="hidden" name="id" value=<?php echo
$_GET['id'];?>></td>
<td><input type="submit" name="update"
value="Update"></td>
</tr>
</table>
</form>
</body>
</html>
delete.php
<?php
//including the database connection file
include("config.php");
//getting id of the data from url
$id = $_GET['id'];
//deleting the row from table
$result = mysqli_query($con, "DELETE FROM courses WHERE id=$id");
//redirecting to the display page (index.php in our case)
header("Location:index.php");
?>
adding.php
38
<?php
//including the database connection file
include_once("config.php");
//fetching data in descending order (latest entry first)
//$result = mysql_query("SELECT * FROM users ORDER BY id DESC"); //
mysql_query is deprecated
$result = mysqli_query($con, "SELECT * FROM courses ORDER BY id DESC"); //
using mysqli_query instead
?>
<html>
<head>
<title>Homepage</title>
</head>
<body>
<a href="adding.php">Add New Data</a><br/><br/>
<table width='80%' border=0>
<tr bgcolor='#CCCCCC'>
<td>Name</td>
<td>Update</td>
</tr>
<?php
//while($res = mysql_fetch_array($result)) { // mysql_fetch_array is
deprecated, we need to use mysqli_fetch_array
while($res = mysqli_fetch_array($result)) {
39
echo "<tr>";
echo "<td>".$res['name']."</td>";
echo "<td><a href=\"edit.php?id=$res[id]\">Edit</a> | <a
href=\"delete.php?id=$res[id]\" onClick=\"return confirm('Are you sure you want to
delete?')\">Delete</a></td>";
}
?>
</table>
</body>
</html>
login.php
<?php
// Initialize the session
session_start();
// Check if the user is already logged in, if yes then redirect him to welcome page
if(isset($_SESSION["loggedin"]) && $_SESSION["loggedin"] === true){
header("location: index.php");
exit;
}
// Include config file
require_once "config.php";
// Define variables and initialize with empty values
$username = $password = "";
$username_err = $password_err = $login_err = "";
40
// Processing form data when form is submitted
if($_SERVER["REQUEST_METHOD"] == "POST"){
// Check if username is empty
if(empty(trim($_POST["username"]))){
$username_err = "Please enter username.";
} else{
$username = trim($_POST["username"]);
}
// Check if password is empty
if(empty(trim($_POST["password"]))){
$password_err = "Please enter your password.";
} else{
$password = trim($_POST["password"]);
}
// Validate credentials
if(empty($username_err) && empty($password_err)){
// Prepare a select statement
$sql = "SELECT id, username, password FROM users WHERE username = ?";
if($stmt = mysqli_prepare($con , $sql)){
// Bind variables to the prepared statement as parameters
mysqli_stmt_bind_param($stmt, "s", $param_username);
// Set parameters
$param_username = $username;
// Attempt to execute the prepared statement
41
if(mysqli_stmt_execute($stmt)){
// Store result
mysqli_stmt_store_result($stmt);
// Check if username exists, if yes then verify password
if(mysqli_stmt_num_rows($stmt) == 1){
// Bind result variables
mysqli_stmt_bind_result($stmt, $id, $username, $hashed_password);
if(mysqli_stmt_fetch($stmt)){
if(password_verify($password, $hashed_password)){
// Password is correct, so start a new session
session_start();
// Store data in session variables
$_SESSION["loggedin"] = true;
$_SESSION["id"] = $id;
$_SESSION["username"] = $username;
// Redirect user to welcome page
header("location: index.php");
} else{
// Password is not valid, display a generic error message
$login_err = "Invalid username or password.";
}
}
} else{
// Username doesn't exist, display a generic error message
$login_err = "Invalid username or password.";
}
} else{
echo "Oops! Something went wrong. Please try again later.";
42
}
// Close statement
mysqli_stmt_close($stmt);
}
}
// Close connection
mysqli_close($con);
}
?>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Login</title>
<link rel="stylesheet"
href="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css">
<style>
body{ font: 14px sans-serif; }
.wrapper{ width: 360px; padding: 20px; }
</style>
</head>
<body>
<div class="wrapper">
<h2>Login</h2>
<p>Please fill in your credentials to login.</p>
<?php
if(!empty($login_err)){
43
echo '<div class="alert alert-danger">' . $login_err . '</div>';
}
?>
<form action="<?php echo htmlspecialchars($_SERVER["PHP_SELF"]); ?>"
method="post">
<div class="form-group">
<label>Username</label>
<input type="text" name="username" class="form-control <?php echo
(!empty($username_err)) ? 'is-invalid' : ''; ?>" value="<?php echo $username; ?>">
<span class="invalid-feedback"><?php echo $username_err; ?></span>
</div>
<div class="form-group">
<label>Password</label>
<input type="password" name="password" class="form-control <?php
echo (!empty($password_err)) ? 'is-invalid' : ''; ?>">
<span class="invalid-feedback"><?php echo $password_err; ?></span>
</div>
<div class="form-group">
<input type="submit" class="btn btn-primary" value="Login">
</div>
<!-- <p>Don't have an account? <a href="register.php">Sign up
now</a>.</p> -->
</form>
</div>
</body>
</html>
Index.php
44
<?php
// Initialize the session
session_start();
// Check if the user is logged in, if not then redirect him to login page
if(!isset($_SESSION["loggedin"]) || $_SESSION["loggedin"] !== true){
header("location: login.php");
exit;
}
?>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Welcome</title>
<link rel="stylesheet"
href="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css">
<style>
body{ font: 14px sans-serif; text-align: center; }
</style>
<link href='style.css' rel='stylesheet' type='text/css'>
<script src="jquery-3.2.1.js"></script>
<script type='text/javascript'>
var recognition = new webkitSpeechRecognition();
recognition.onresult = function(event) {
console.log('result');
var saidText = "";
for (var i = event.resultIndex; i < event.results.length; i++) {
if (event.results[i].isFinal) {
45
saidText = event.results[i][0].transcript;
} else {
saidText += event.results[i][0].transcript;
}
}
document.getElementById('speechText').value = saidText;
// Search Posts
searchPosts(saidText);
}
function startRecording(){
recognition.start();
}
// Search Posts
function searchPosts(saidText){
$.ajax({
url: 'getData.php',
type: 'post',
data: {speechText: saidText},
success: function(response){
$('.container').empty();
$('.container').append(response);
}
});
}
</script>
46
</head>
<body>
<h1 class="my-5">Hi, <b><?php echo
htmlspecialchars($_SESSION["username"]); ?></b>. Welcome to our site.</h1>
<div class='search_container'>
<!-- Search box-->
<input type='text' id='speechText' > &nbsp; <input type='button'
id='start' value='Start' onclick='startRecording();'>
</div>
<!-- Search Result -->
<div class="container"></div>
<p>
<!-- <a href="reset-password.php" class="btn btn-warning">Reset Your
Password</a> -->
<a href="logout.php" class="btn btn-danger ml-3">Sign Out of Your
Account</a>
</p>
</body>
</html>
Register.php
<?php
// Include config file
require_once "config.php";
// Define variables and initialize with empty values
$username = $password = $confirm_password = "";
$username_err = $password_err = $confirm_password_err = "";
// Processing form data when form is submitted
47
if($_SERVER["REQUEST_METHOD"] == "POST"){
// Validate username
if(empty(trim($_POST["username"]))){
$username_err = "Please enter a username.";
} elseif(!preg_match('/^[a-zA-Z0-9_]+$/', trim($_POST["username"]))){
$username_err = "Username can only contain letters, numbers, and
underscores.";
} else{
// Prepare a select statement
$sql = "SELECT id FROM users WHERE username = ?";
if($stmt = mysqli_prepare($con, $sql)){
// Bind variables to the prepared statement as parameters
mysqli_stmt_bind_param($stmt, "s", $param_username);
// Set parameters
$param_username = trim($_POST["username"]);
// Attempt to execute the prepared statement
if(mysqli_stmt_execute($stmt)){
/* store result */
mysqli_stmt_store_result($stmt);
if(mysqli_stmt_num_rows($stmt) == 1){
$username_err = "This username is already taken.";
} else{
$username = trim($_POST["username"]);
}
} else{
echo "Oops! Something went wrong. Please try again later.";
48
}
// Close statement
mysqli_stmt_close($stmt);
}
}
// Validate password
if(empty(trim($_POST["password"]))){
$password_err = "Please enter a password.";
} elseif(strlen(trim($_POST["password"])) < 6){
$password_err = "Password must have atleast 6 characters.";
} else{
$password = trim($_POST["password"]);
}
// Validate confirm password
if(empty(trim($_POST["confirm_password"]))){
$confirm_password_err = "Please confirm password.";
} else{
$confirm_password = trim($_POST["confirm_password"]);
if(empty($password_err) && ($password != $confirm_password)){
$confirm_password_err = "Password did not match.";
}
}
// Check input errors before inserting in database
if(empty($username_err) && empty($password_err) &&
empty($confirm_password_err)){
// Prepare an insert statement
49
$sql = "INSERT INTO users (username, password) VALUES (?, ?)";
if($stmt = mysqli_prepare($con, $sql)){
// Bind variables to the prepared statement as parameters
mysqli_stmt_bind_param($stmt, "ss", $param_username,
$param_password);
// Set parameters
$param_username = $username;
$param_password = password_hash($password, PASSWORD_DEFAULT);
// Creates a password hash
// Attempt to execute the prepared statement
if(mysqli_stmt_execute($stmt)){
// Redirect to login page
header("location: login.php");
} else{
echo "Oops! Something went wrong. Please try again later.";
}
// Close statement
mysqli_stmt_close($stmt);
}
}
// Close connection
mysqli_close($con);
}
?>
<!DOCTYPE html>
50
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Sign Up</title>
<link rel="stylesheet"
href="https://stackpath.bootstrapcdn.com/bootstrap/4.5.2/css/bootstrap.min.css">
<style>
body{ font: 14px sans-serif; }
.wrapper{ width: 360px; padding: 20px; }
</style>
</head>
<body>
<div class="wrapper">
<h2>Sign Up</h2>
<p>Please fill this form to create an account.</p>
<form action="<?php echo htmlspecialchars($_SERVER["PHP_SELF"]); ?>"
method="post">
<div class="form-group">
<label>Username</label>
<input type="text" name="username" class="form-control <?php echo
(!empty($username_err)) ? 'is-invalid' : ''; ?>" value="<?php echo $username; ?>">
<span class="invalid-feedback"><?php echo $username_err; ?></span>
</div>
<div class="form-group">
<label>Password</label>
<input type="password" name="password" class="form-control <?php
echo (!empty($password_err)) ? 'is-invalid' : ''; ?>" value="<?php echo $password;
?>">
<span class="invalid-feedback"><?php echo $password_err; ?></span>
</div>
<div class="form-group">
51
<label>Confirm Password</label>
<input type="password" name="confirm_password" class="form-control
<?php echo (!empty($confirm_password_err)) ? 'is-invalid' : ''; ?>" value="<?php
echo $confirm_password; ?>">
<span class="invalid-feedback"><?php echo $confirm_password_err;
?></span>
</div>
<div class="form-group">
<input type="submit" class="btn btn-primary" value="Submit">
<input type="reset" class="btn btn-secondary ml-2" value="Reset">
</div>
<p>Already have an account? <a href="login.php">Login here</a>.</p>
</form>
</div>
</body>
</html>
Logout.php
<?php
// Initialize the session
session_start();
// Unset all of the session variables
$_SESSION = array();
// Destroy the session.
session_destroy();
// Redirect to login page
header("location: login.php");
exit;
52
?>
Config.php
<?php
$host = "localhost"; /* Host name */
$user = "root"; /* User */
$password = ""; /* Password */
$dbname = "voice"; /* Database name */
$con = mysqli_connect($host, $user, $password,$dbname);
// Check connection
if (!$con) {
die("Connection failed: " . mysqli_connect_error());
}
53
User manual Implementation:
Voice recognition website to detect the voice and provide the output. This is a useful website
for students to get their voice and courses will be list out. Student can add their courses.
Students can update and delete the courses.
Login screen:
The student will login using the username and password:
Username: eswar
Password: 12345678
Dashboard
54
Voice detects:
Click on start and say something like courses:
Add courses
Student can add courses using the add link. Edit and delete options are here and user can edit
the course and can delete.
55
Edit course:
Logout
Student can logout from the website.
56
Database:
57