Uploaded by
Baojia LI (optimus FFFx)
DFDI Attacks Against State Omniscience: Security Analysis
advertisement

4634
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
Decentralized False-Data Injection Attacks
Against State Omniscience: Existence and
Security Analysis
Tian-Yu Zhang , Member, IEEE, Dan Ye , Senior Member, IEEE, and Yang Shi , Fellow, IEEE
Abstract—This article focuses on how false-data injection (FDI) attacks compromise state omniscience, which
needs each node in a jointly detectable sensor network
to estimate the entire plant state through distributed observers. To reveal the global vulnerability of state omniscience, we investigate decentralized FDI (DFDI) attacks
that destabilize the estimation error dynamics but eliminate their influences on the residual in each sensor node.
First, the sufficiency and necessity for the existence of
such attacks are studied from system eigenvalues and attackable sensors. Second, the self-generated DFDI attack
sequences independent of system real-time data are designed to achieve the attack objective with elaborate parameters. Especially, the DFDI attack sequences are improved
to maintain real values even if the system matrix only has
unstable imaginary eigenvalues. Finally, we analyze the secure range for observer interaction weights and the sensor
protection scheme to guarantee the security of state omniscience under DFDI attacks. The theoretical results for DFDI
attacks are demonstrated with the linearized discrete-time
model of an aircraft system.
Index Terms—Complete stealthiness, cyber-physical
system security, decentralized false-data injection (DFDI)
attacks, distributed observers, state omniscience.
Manuscript received 15 February 2022; revised 8 May 2022; accepted
9 September 2022. Date of publication 26 September 2022; date of
current version 28 July 2023. This work was supported in part by the
National Natural Science Foundation of China under Grant 62173071,
Grant U1813214, and Grant 61621004, in part by the China Postdoctoral Science Foundation (BX20220061), in part by the LiaoNing
Revitalization Talents Program under Grant XLYC1907035, in part by
the Liaoning BaiQianWan Talents Program (202062), and in part by the
Fundamental Research Funds for the Central Universities (N2204008).
Recommended by Associate Editor F. Zhang. (Corresponding author:
Dan Ye.)
Tian-Yu Zhang is with the College of Information Science and Engineering, Northeastern University, Shenyang, Liaoning 110819, China
(e-mail: zhangtianyu1994@qq.com).
Dan Ye is with the College of Information Science and Engineering,
and State Key Laboratory of Synthetical Automation for Process Industries, Northeastern University, Shenyang, Liaoning 110819, China
(e-mail: yedan@ise.neu.edu.cn).
Yang Shi is with the Department of Mechanical Engineering, University of Victoria, Victoria, BC V8W2Y2, Canada (e-mail: yshi@uvic.ca).
Color versions of one or more figures in this article are available at
https://doi.org/10.1109/TAC.2022.3209396.
Digital Object Identifier 10.1109/TAC.2022.3209396
I. INTRODUCTION
ISTRIBUTED estimation recently attracts increasing attention owing to its wide applications in the monitoring
for transportation systems [1], ecological environments [2],
power grids [3], and so on. When a sensor network is only
jointly detectable for physical plants, distributed estimation is
extremely challenging since plant states may not be observed by
a single sensor node [4]. A key challenge is the creditability of
inadequate local measurements in face of cyber-attacks. This
promotes security to be a significant concern of distributed
estimation and furnishes the motivation of this article.
As a typical objective of distributed estimation, state omniscience is to observe the entire state of a plant in each
sensor node even if local measurements are not adequate. In
this scenario, information exchanges among sensor nodes are
of importance to ensure the estimation objective. Distributed
estimation for state omniscience has been researched with two
main techniques: Kalman filters [5] and state observers [6].
Distributed Kalman filters iterate feedback gains to obtain optimal noise attenuation, but require more information interactions
of covariance matrices [7], [8]. Benefited by only exchanging
estimation signals, state-observer-based techniques are widely
studied in [9] and [10] for discrete-time cases and [11], [12],
[13] for continuous-time cases. In [9], the necessary and sufficient condition for state omniscience is proved to be the joint
detectability of each source component in a sensor network.
Moreover, the Kalman observable canonical decomposition is
brought to design the distributed observers for state omniscience
in [10]. For continuous-time cases, the distributed observers with
and without the augmented states are developed based on jointly
detectable sensor networks in [11] and [12], respectively. Then,
a complete decentralization method is proposed to design the
distributed observers without the knowledge for the structure
and number of sensor networks [13]. However, when sensor
networks are compromised by malicious attacks, the precision
of state omniscience will suffer major crises in each distributed
observer.
Among various malicious attacks, false-data injection (FDI)
attacks attract increasing attention due to their serious disruptions on plant operations and deep stealthiness against monitors [14], [15]. Compared with such attacks, other typical attacks
(e.g., denial-of-service attacks and replay attacks) are either
less destructive or less stealthy [16], [17], [18], [19]. From the
D
0018-9286 © 2022 IEEE. Personal use is permitted, but republication/redistribution requires IEEE permission.
See https://www.ieee.org/publications/rights/index.html for more information.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
boundedness of attack effectiveness, FDI attacks are further
divided into imperfect FDI attacks [20], [21], [22], [23] and
perfect FDI attacks [25], [26].
Imperfect FDI attacks only cause bounded influences on
system performances under stealthiness constraints. Thus, their
attack effectiveness is yoked to stealthiness, which implies that
the price of stronger attack effectiveness is sacrificing stealthiness. Nevertheless, the implementation of such attacks has
no particular requirements for system structures. The trade-off
between the attack effectiveness and stealthiness of imperfect
FDI attacks is studied in [20], [21], [22], [23], [24]. To guarantee
cyber-security under imperfect FDI attacks, centralized secure
estimation that reconstructs the real state of physical plants is
widely studied in [27], [28]. Furthermore, the distributed secure
estimators under attacked sensor measurements and attacked
communication links are investigated in [29] and [30], respectively. In [31], [32], the attack detection methods are proposed to
counter imperfect FDI attacks based on distributed estimation.
Although plenty of results have been obtained for imperfect
attacks, none of them focuses on how FDI attacks affect system
stability.
Perfect FDI attacks destabilize systems under stealthiness
constraints, which implies that unbounded attack influences are
stealthily brought into system performances. The perfection
feature ensures that attack effectiveness is not constrained by
stealthiness [33], [34]. In static state estimation for different
systems, the existence of perfect FDI attacks that only modify
sensor outputs is studied in [35], [36]. However, perfect sensor
FDI attacks in dynamic state estimation have more complex
requirements for system structures. The existence of perfect
sensor FDI attacks is studied from the eigenvalues of system
matrices in [25], [37], [38]. By compromising multiple channels,
e.g., actuator and sensor channels, perfect FDI attacks can be
achieved with weaker requirements for system structures [39],
[40], [41]. Compared with actuators, sensors are more vulnerable
in distributed dynamic estimation due to the wide applications
of wireless sensor networks [24], [30]. In [42], perfect sensor
FDI attacks are developed to destabilize the estimation error
dynamics of at least one node in the distributed observers.
However, it is still an open problem whether the estimation error
dynamics of all observers will be destabilized by FDI attacks.
This ignites our interest in what pivotal role the perfect sensor
FDI attacks play in distributed estimation for state omniscience.
In this article, FDI attacks which destabilize the estimation
error dynamics of all distributed observers are called as perfect
decentralized false-data injection (DFDI) attacks. Since sensor
nodes can share the detection results with each other, the deeper
stealthiness is an important concern of DFDI attacks. In our
previous work [43], complete stealthiness is proposed to asymptotically remove the influences of FDI attacks on detectors.
Compared with the stealthiness that maintains bounded influences against detectors [25], [37], [38], [42], complete stealthiness is more appropriate with the stealthy purpose of DFDI
attacks. Hence, a class of perfect DFDI attacks with complete
stealthiness, which dispersively compromises the measurement
outputs of sensor networks, is researched to reveal the global
4635
vulnerability of state omniscience. The main contributions of
this article are summarized as follows.
1) Different from existing perfect FDI attacks that only
destabilize at least one distributed observer [26], [42],
perfect DFDI attacks are developed to destabilize all
observers and hold complete stealthiness.
2) From the viewpoints of system matrix eigenvalues and
attackable sensors, the sufficiency and necessity are developed for the existence of perfect DFDI attacks with
complete stealthiness.
3) The attack sequences are designed to achieve the proposed attack objective without the real-time data of attacked systems, and their steady-state stealthy performances are evaluated. In addition, the designed attack
sequences maintain real values by involving multiple
system eigenvalues whereas the one in [43] is imaginary
value.
4) Based on the necessary conditions of attack existence,
we propose the secure range for observer interaction
weights and a sensor protection scheme that exposes the
considered attacks to detectors.
Notation: R and N denote the sets of real numbers and
natural numbers, respectively. For a matrix X, X T represents
its transpose, span(X) stands for its column spanning space
and cs(X) is the vector set constituted by all the columns
of X. For a square matrix X, ρ(X) denotes its spectral
radius, Λ(X) represents the set of its all eigenvalues and
Ω(X) is the set of its all eigenvectors. Define ΛP (X) = {λ ∈
Λ(X)||λ| > 1} and ΛQ (X) = {λ ∈ Λ(X)||λ| ≥ 1} as the
subsets of Λ(X). Denote ΩP (X) = {v|(X − λI)v = 0, λ ∈
ΛP (X)} and ΩQ (X) = {v|(X − λI)v = 0, λ ∈ ΛQ (X)} as
the subsets of Ω(X). For a vector υ, υ, and υ∞ stand for its
Euclidean norm and infinite norm, respectively. X and X∞
are the matrix norms induced by the Euclidean norm and infinite
norm of vectors, respectively. X ⊗ Y denotes the Kronecker
product of the matrices X and Y . For a complex number c, c∗ ,
Re{c}, and |c| represent its conjugate complex number, real part,
and modulus, respectively. The identity matrix with n dimensions is represented as In . 1 is an appropriate-dimensional vector
with all elements being 1. 0 is a zero vector with appropriate
dimensions. N (μ, σ 2 ) stands for the Gaussian distribution with
mean μ and variance σ 2 . Prob(Z) is the probability of a random
event Z.
II. PROBLEM FORMULATION AND PRELIMINARIES
A. Graph Theory
Let a directed graph G = (V, E) describe the interaction relations of the sensor network. V = {1, 2, . . . , N } and E ⊆ V × V
represent the sets of sensor nodes and interaction links, respectively. A digraph is strongly connected if any two distinct
nodes are connected by a directed path. Denote ai,j = 1 if there
exists a directed edge from the jth node to the ith node. Then,
the Laplacian matrix of the graph G is L = [li,j ]N ×N , where
li,i = N
j=1,j =i ai,j and li,j = −ai,j for i = j.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4636
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
B. System Model
The physical layer including the observed plant and
sensors is described by the following discrete-time linear
system:
xk+1 = Axk + ωk
yi,k = Ci xk + υi,k , i = 1, . . . , N
(1)
where xk ∈ Rn is the physical plant state and yi,k ∈ Rmi is
the measurement output of the ith sensor node. Then, yk T
T
, . . . , yN,k
]T ∈ Rm represents the global measurement of
[y1,k
the sensor network. The process noise and measurement noise
obey ωk ∼ N (0, Q) and υi,k ∼ N (0, Ri ), respectively.
Assumption 1: The plant is jointly detectable for the sensor
T T
] , A) is detectable.
network, that is, the matrix pair ([C1T · · · CN
Assumption 2: The interaction network G among the sensor
nodes is strongly connected.
The following definition introduces the objective of state
omniscience.
Definition 1 (see [9], [10]): A group of distributed observers
achieve state omniscience if each sensor node’s observer asymptotically estimates the entire state of the physical plant under
noise-free cases, i.e., limk→∞ x̂i,k − xk = 0, ∀i ∈ V.
In the cyber layer, the distributed observers for state omniscience are designed as follows:
wi,j Ax̂j,k +Li (yi,k −Ci x̂i,k ), i = 1, . . . , N (2)
x̂i,k+1 =
j∈Ni
where Ni {j ∈ V|li,j = 0} and wi,j is the interaction weight
satisfying
j∈Ni wi,j = 1. In light of [9], to achieve state
omniscience, the weight matrix W [wi,j ]N ×N should satisfy
that (i) every eigenvalue of W is simple; (ii) every eigenvector
of W has no zero entries. Let W be the set of all the matrices W
that match the abovementioned two properties. Represent the
estimation error and residual of the ith sensor node as ei,k xk − x̂i,k and zi,k yi,k − Ci x̂i,k , respectively. Furthermore,
the dynamics of the global estimation error and residual are
ek+1 = (W ⊗ A − L̄C̄)ek + 1 ⊗ ωk − L̄υk
zk = C̄ek + υk
(3)
T
T
where ek [eT1,k , . . . , eTN,k ]T , zk [z1,k
, . . . , zN,k
]T , and
T
T
T
υk [υ1,k , . . . , υN,k ] . C̄ diag(C1 , . . . , CN ) and L̄ diag(L1 , . . . , LN ) are block diagonal matrices. To achieve state
omniscience, the weight matrix W and observer gain L̄ are
supposed to satisfy W ∈ W and ρ(W ⊗ A − L̄C̄) < 1, respectively.
Remark 1: In [9], it is proved that almost all the choices
of the weight matrix satisfy W ∈ W under Assumption 2. In
addition, a particular choice of W ∈ W is W = IN − L, where
0 < < (maxi∈V li,i )−1 .
To reveal potential anomalies, the residual-based detector
T
Πi zi,k and residual-energy-based detector ḡi,k =
gi,k = zi,k
k
1/k( p=0 zi,p )T Π̄i kp=0 zi,p are applied in each sensor
node [25], [37], [44], where Πi and Π̄i are positive-definite
matrices. Whenever gi,k (ḡi,k ) is larger than the threshold
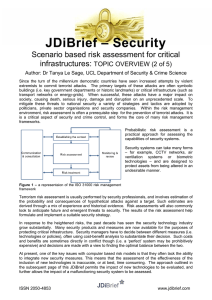
Fig. 1.
Distributed observers under DFDI attacks.
value gi,th (ḡi,th ), the corresponding detector gives an alarm.
Furthermore, the false alarm rates of the residual-based and
residual-energy-based detectors are pF
i,k Prob(gi,k > gi,th )
Prob(ḡ
>
ḡ
),
respectively.
By transmitting a
and p̄F
i,k
i,th
i,k
flag bit, the alarms of arbitrary sensor node can be reported to
the whole sensor network with low bandwidth.
C. DFDI Attack Model
DFDI attacks dispersedly tamper with sensor measurements
to damage distributed observers (see Fig. 1). The attacked outputs of the sensor nodes are described as
a
= Ci xk + Γi ai,k + υi,k , i = 1, . . . , N
yi,k
(4)
where ai,k and Γi = diag(γi,1 , . . . , γi,mi ) are the attack sequence and attack target matrix against the ith sensor node,
respectively. If the jth measurement of the ith sensor node is
attacked, then γi,j = 1, and γi,j = 0 otherwise.
Remark 2: In many practical applications, sensor data is
transmitted to observers through wireless communications. Vulnerable wireless communications give attackers the opportunity
to compromise transmitted sensor data with FDI attacks modeled
in (4). The attack model in (4) describes a class of attack
behaviors which compromise sensor output data with elaborate
malicious signals. Not only perfect sensor FDI attacks in [25],
[35], [36], [37], [42], and [43] but also imperfect sensor FDI
attacks in [21], [22], [24], [27], [28], and [32] can be represented
by (4).
Furthermore, the distributed observers under DFDI attacks
are written as follows:
a
wi,j Ax̂aj,k +Li (yi,k
−Ci x̂ai,k ), i = 1, . . . , N (5)
x̂ai,k+1 =
j∈Ni
where x̂ai,k is the attacked state estimation in the ith sensor
a
a
yi,k
− Ci x̂ai,k be the
node. Let eai,k xi,k − x̂ai,k and zi,k
estimation error and residual of the ith sensor node under attacks. According to [25], [37], [43], we focus on the attacked
components of the estimation errors and residuals, i.e., ẽi,k a
− zi,k . Then, ẽk [ẽT1,k , . . . , ẽTN,k ]T
eai,k − ei,k and z̃i,k zi,k
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
T
T
and z̃k [z̃1,k
, . . . , z̃N,k
]T have the following dynamics:
ẽk+1 = (W ⊗ A − L̄C̄)ẽk − L̄Γ̄ak
z̃k = C̄ ẽk + Γ̄ak
(6)
(7)
where Γ̄ diag(Γ1 , . . . , ΓN ) and ak [aT1,k , . . . , aTN,k ]T .
Since the attacks do not occur at k = −1, the initial values of the
error systems (6) and (7) are ẽ0 = 0 and z̃0 = Γ̄a0 , respectively.
To explore more dangerous attack behaviors in distributed
observers, we analyze perfect DFDI attacks that destabilize the
estimation error dynamics and hold deeper stealthiness in each
node. Therefore, perfect DFDI attacks with strict stealthiness,
which cause no influences on detectors, are introduced as follows.
Definition 2: Perfect DFDI attacks with strict stealthiness are
achieved in the distributed observers (5) if for any k ∈ N[0, ∞),
the estimation error and residual of each sensor node satisfy (i)
limk→∞ ẽi,k = ∞ and (ii) z̃i,k = 0.
Proposition 1: There exists no perfect DFDI attacks with
strict stealthiness in the distributed observers (5).
Proof: According to (6), the dynamics of ẽk are rewritten as
follows:
ẽk = −
k−1
(W ⊗ A)k−p−1 L̄z̃p .
(8)
p=0
It is easy to obtain ẽk = 0 when z̃k = 0 is established at any
time. Thus, limk→∞ ẽi,k = ∞ and z̃i,k = 0, ∀k ∈ N[0, ∞)
cannot hold simultaneously, which implies that perfect DFDI
attacks with strict stealthiness are inexistent in the distributed
observers (5).
Although there exist no perfect DFDI attacks with strict
stealthiness, how to asymptotically remove the attack influences
on detectors is still our concern. In view of this purpose, we
introduce the following definition for perfect DFDI attacks with
complete stealthiness.
Definition 3: Perfect DFDI attacks with complete stealthiness
are achieved in the distributed observers (5) if there exist positive
constants α and β such that for any k ∈ N[0, ∞), the estimation
error and residual of each sensor node satisfy the following:
i) limk→∞ ẽi,k = ∞;
ii) z̃i,k ≤ α;
iii) limk→∞ z̃i,k = 0;
iv) kp=0 z̃i,p ≤ β.
Proposition 2: When the distributed observers (5) are
compromised by DFDI attacks, the residual-based detector
a
a T
a
a
= (zi,k
) Πi zi,k
and residual-energy-based detector ḡi,k
=
gi,k
k
k
a T
a
1/k( p=0 zi,p ) Π̄i p=0 zi,p satisfy
F
(i) limk→∞ (pD
i,k − pi,k ) = 0 if limk→∞ z̃i,k = 0;
k
D
(ii) limk→∞ (p̄i,k − p̄F
i,k ) = 0 if p=0 z̃i,p ≤ β, ∀k ∈
N[0, ∞),
a
D
a
where pD
i,k Prob(gi,k > gi,th ) and p̄i,k Prob(ḡi,k >
ḡi,th ) are the detection rates of the residual-based and residualenergy-based detectors, respectively.
Proof: The proof is similar to [43, Props. 1 and 2] and omitted
here.
4637
Remark 3: Different from the deterministic stealthiness in
Definition 3, some works consider the statistical stealthiness
a
[20],
described by the probability distributions of zi,k and zi,k
[21], [39]. Obviously, the probability distributions of zi,k and
a
a
are the same when zi,k
is equal to zi,k , but not vice versa.
zi,k
Therefore, when DFDI attacks guarantee limk→∞ z̃i,k = 0,
∀i ∈ V, the deterministic stealthiness in Definition 3 is stronger
than the statistical stealthiness in the steady state.
III. EXISTENCE OF PERFECT DFDI ATTACKS
In this section, the sufficiency and necessity for the existence
of perfect DFDI attacks with complete stealthiness are investigated, respectively.
Suppose |ΛP (W ⊗ A)| = s and |ΛQ (W ⊗ A)| = s̄. Obviously, the eigenvalue λq ∈ Λ(W ⊗ A) and eigenvector vq ∈
A
W
Ω(W ⊗ A) can be decomposed as λq = λW
q λq and vq = vq ⊗
W
A
A
W
A
vq , where (λq IN − W )vq = 0 and (λq In − A)vq = 0.
The Jordan canonical form of W ⊗ A is defined as
J = V (W ⊗ A)U , where U = V −1 = [u1 , . . . , uN n ] is an invertible matrix. Let DW and JA be the diagonal canonical
form of W and the Jordan canonical form of A, respectively.
Thus, there is an invertible matrix UA = VA−1 such that JA =
VA AUA . Furthermore, the Jordan canonical form J of W ⊗ A
is described as J = DW ⊗ JA and any column of U can be
W
A
rewritten as uq = vqW ⊗ uA
q for vq ∈ Λ(W ) and uq ∈ cs(UA ).
Evidently, J can be partitioned as
Ja 0
Va
(9)
W ⊗ A = U J V = [Ua Ub ]
0 Jb Vb
where Ja ∈ Rs̄×s̄ is the Jordan block corresponding to the
eigenvalues λq ∈ ΛQ (W ⊗ A). It is easy to observe Va Ua = Is̄ ,
Vb Ub = IN n−s̄ , and Va Ub = Vb Ua = 0. Several useful lemmas
are introduced as follows.
Lemma 1 (see [43]): Let X ∈ RN n×N n be an arbitrary matrix
that satisfies ρ(X) < 1. The matrix
norm and vector
norm in the linear space RN n×N n are defined as X Gε VX XUX G−1
ε ∞ and ν Gε VX ν∞ respectively,
where Gε = diag(1, ε, ε2 , . . . , εN n−1 ) and ε < 1 − ρ(X). Let
UX = VX−1 be an invertible matrix such that JX = VX XUX is
the Jordan canonical form of the matrix X. Then, the norm
has the following properties.
i) For the matrix X satisfying ρ(X) < 1, one has X <
1;
ii) The vector
norm is compatible with the matrix
norm, i.e., Xν ≤ X ν ;
iii) The
vector
norm
satisfies
ν ≤
√
N nUX G−1
ε ν .
Nn
Lemma 2: For any given constant vector νp ∈ R
, if there
exist the constant vectors φ = 0 and φ̄ such that ∞
p=0 (W ⊗
A)p νp = ∞ · φ + φ̄ holds, then φ ∈ span(Ua ).
Proof: Please see Appendix A.
The existence of perfect DFDI attacks with complete stealthiness is analyzed in the following theorems.
Theorem 1 (Sufficiency): There exist DFDI attacks satisfying
Definition 3 in the distributed observers (5) if
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4638
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
(i) the system matrix satisfies ρ(W ⊗ A) > 1;
(ii) there exists at least one eigenvector vq ∈ ΩP (W ⊗ A)
such that the attack target matrix satisfies C̄vq ∈ span(Γ̄).
Proof: This theorem is true when there exist the particular
attack sequences satisfying Definition 3 under conditions (i) and
(ii). The design of the particular attack sequences is given in
Section IV and omitted here.
Based on the global condition of the attack targets, we further
analyze whether a sensor node is the required attack target for
DFDI attacks satisfying Definition 3.
Corollary 1: The global attack target matrix satisfies C̄vq ∈
span(Γ̄) if and only if Ci vqA ∈ span(Γi ) for any sensor node
i ∈ V.
Proof: Please see Appendix B.
Theorem 2 (Necessity): There exist DFDI attacks satisfying
Definition 3 in the distributed observers (5) only if
(i) the system matrix satisfies ρ(W ⊗ A) ≥ 1;
(ii) there exists at least one vector uq ∈ cs(Ua ) such that the
attack target matrix satisfies C̄uq ∈ span(Γ̄).
Proof: Please see Appendix C.
Corollary 2: The global attack target matrix satisfies C̄uq ∈
span(Γ̄) if and only if Ci uA
q ∈ span(Γi ) for any sensor node
i ∈ V.
Proof: Combined with uq = vqW ⊗ uA
q , the proof is similar
to Corollary 1.
Remark 4: If a sensor node satisfies Ci vqA = 0 for vqA ∈
ΩP (A), then perfect DFDI attacks with complete stealthiness
can be achieved without compromising this sensor node. This
implies that DFDI attacks may destabilize all observers by
compromising a part of sensor nodes.
Remark 5: With two particular cases, we introduce the existence of perfect DFDI attacks with complete stealthiness under
ρ(W ⊗ A) = 1 with two particular cases. Firstly, choose W ⊗
A = 1. Then, for any k ∈ N[0,
a constant β̄
∞), there exists
∞
z̃
≤
β̄
if
such that limk→∞ ẽk = L̄ ∞
p=0 p
p=0 z̃i,p ≤
β holds for any i ∈ V. This implies that such attacks are inexistent in this particular case. Secondly, choose W ⊗ A = −1.
Then, there exist L̄1 = 0 and z̃p = ((−1)p 1)/(p + 1), which
satisfy the constraints in Definition 3, such that limk→∞ ẽk =
∞
p=0 1/(p + 1)|L̄1| = ∞ is established. Thus, such attacks are
existent in this particular case. These cases can be extended to
the high-dimensional situations when W ⊗ A is diagonalizable.
As a result, the existence of such attacks is undetermined for
ρ(W ⊗ A) = 1.
IV. DESIGN OF PERFECT DFDI ATTACKS
Consider ρ(W ⊗ A) > 1 and choose vq1 , . . . , vqs∗ ∈
ΩP (W ⊗ A) to satisfy that their corresponding vqA1 , . . . , vqAs∗ ∈
Ω(A) are linearly independent. Due to vq = vqW ⊗ vqA , the
vectors vq1 , . . . , vqs∗ are also linearly independent. The DFDI
attack sequences against the sensor outputs are designed as
W
ai,k+1 = ai,k −
θq,k+1 λk+1
vi,q
δi,q , i = 1, . . . , N (10)
q
q∈S
W
where S {q1 , . . . , qs∗ }, vi,q
is the ith element of vqW and δi,q
A
is a solution of Ci vq = Γi δi,q . The coefficient θq,k is chosen
as κq for k ∈ N[0, τq ) and μq κq for k ∈ N[τq , ∞), where κq
and μq are constants. τq ∈ N[1, ∞) is the switching instant
values of the attack sequences (10) are
of θq,k . The
initial W
δi,q , i = 1, . . . , N . Obviously, the attack
ai,0 = − q∈S θq,0 vi,q
sequences (10) are independent of the real-time data in the sensor
network, which reflects the “self-generated” feature.
Let the attack target Γi satisfy Theorem 1. Under the attack
sequences (10), ẽk and z̃k satisfy:
Ek+1 ẽk+1 − ẽk = (W ⊗ A − L̄C̄)Ek + L̄Γ̄
θq,k λkq δq
Zk z̃k − z̃k−1 = C̄Ek − Γ̄
q∈S
θq,k λkq δq
(11)
q∈S
W T
W T
where δq [v1,q
δ1,q , . . . , vN,q
δN,q ]T . Without loss of generality, we suppose τq1 ≤ τq2 ≤ · · · ≤ τqs∗ .
Proposition 3: The solutions of the error dynamics (6) and
residual dynamics (7) under the attack sequences (10) are
ẽk = −
k
∗
q∈Sk−1
q∈S p=0
τq
+
κq λpq vq +
q∈Sk−1 p=0
−
k
κq (W ⊗ A − L̄C̄)p vq +
k
κq λpq vq
p=0
μq κq λpq vq
q∈Sk−1 p=τq +1
k
(μq − 1)κq λτqq (W ⊗ A − L̄C̄)p−τq vq
q∈Sk−1 p=τq +1
(12)
and
z̃k = −
k
κq C̄(W ⊗ A − L̄C̄)p vq
q∈S p=0
−
k
q∈Sk p=τq
(μq − 1)κq λτqq C̄(W ⊗ A − L̄C̄)p−τq vq
(13)
where Sk {q ∈ S|τq ≤ k} and Sk∗ S \ Sk .
Proof: Please see Appendix D.
Furthermore, the necessary and sufficient condition that the
DFDI attack sequences (10) satisfy Definition 3 is analyzed as
follows.
Theorem 3: The DFDI attack sequences (10) satisfy Definition 3 in arbitrary distributed observers that conform to (5) with
W ∈ W, ρ(W ⊗ A) > 1 and ρ(W ⊗ A − L̄C̄) < 1 if and only
if
κq = 0,
(1 −
μq )λτqq
∃q ∈ S
− 1 = 0, ∀q ∈ Sκ
(14)
where Sκ {q ⊆ S|κq = 0}. Moreover, for any k ∈ N[0, ∞),
z̃k and kp=0 z̃p have the following upper bounds:
√
N n|κq |Û G−1
∗ C̄vq z̃k ≤
(15)
1
−
W
⊗
A
− L̄C̄
q∈S
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
k
√
z̃p ≤
N n|κq |Û G−1
∗ C̄(Hq,τq −1 + Lq,∞ )
p=0
q∈S
(16)
where Hk,q kp=0 pl=0 W ⊗ A − L̄C̄l vq , Lq,∞ τ q
(1 − W ⊗ A − L̄C̄ )−1 p=1
W ⊗ A − L̄C̄ p vq ,
∗
< 1 − ρ(W ⊗ A − L̄C̄), and Û = V̂ −1 is an invertible matrix that leads to the Jordan canonical form Jˆ = V̂ (W ⊗ A −
L̄C̄)Û .
Proof: Please see Appendix E.
Although it has been proved that kp=0 z̃i,p is bounded
for any k ∈ N[0, ∞)
in Theorem 3, we desire to investigate the
accurate value of ∞
p=0 z̃i,p to further evaluate the attack
stealth capability.
Corollary 3: Suppose that the distributed observers (5) are
compromised
by the DFDI attack sequences (10) under (14),
z̃
then ∞
p=0 i,p is given by the following equality:
∞
p=0
z̃i,p = κq Ci Δq,i , i = 1, . . . , N
(17)
q∈S
where Δq = [ΔTq,1 , . . . , ΔTq,N ]T Ξq,τq −1 + Θq,∞ , Ξq,k k p
l
p=0 l=0 (W ⊗ A − L̄C̄) vq and Θq,∞ (I − W ⊗ A +
τ
q
L̄C̄)−1 p=1 (W ⊗ A − L̄C̄)p vq .
Proof: Please see Appendix F.
Evidently, the attack sequences (10) may be imaginary number when W ⊗ A has imaginary eigenvalues. Hence, we further
investigate how the attack sequences (10) maintain real values
even if W ⊗ A only has unstable imaginary eigenvalues.
Theorem 4: Let q and q̄ refer to the conjugate eigenvalues, i.e.,
λq = λ∗q̄ . When W ⊗ A only has unstable imaginary eigenvalues, the DFDI attack sequences (10) are real values under κq =
q
κq̄ ∈ R, τq = τq̄ ∈ N[1, ∞) and μq = μ∗q̄ = 1 − λ−τ
q , ∀q ∈ S.
Proof: Please see Appendix G.
Remark 6: When the system matrix only has unstable imaginary eigenvalues, the attack sequences in [43] with a single
eigenvalue must be imaginary. By involving multiple eigenvalues of the system matrix, the attack sequences (10) can maintain
real values since the imaginary eigenvalues of a real system
matrix are in pairs and conjugate.
Remark 7: Note that 1 is a eigenvector of the weight matrix
W . When the attack sequences (10) are designed to satisfy vqW =
1, ∀q ∈ S, one has that ẽi,k of all observer nodes reach the same
values according to (12). Therefore, the attacker can also hold
stealthiness against the neighbor error x̂ai,k − x̂aj,k , ∀i, j ∈ V,
under condition (14).
V. SECURE ANALYSIS UNDER PERFECT DFDI ATTACKS
As stated in Theorems 1 and 2, the spectral radius ρ(W ⊗ A)
and attack targets Γ̄ are pivotal to perfect DFDI attacks with complete stealthiness. First, for the security of state omniscience,
we investigate how to decrease ρ(W ⊗ A) by choosing wi,j .
The relationship between ρ(W ⊗ A) and ρ(A) is introduced as
follows.
4639
Lemma 3: For the distributed observers (5) that satisfy
j∈Ni wi,j = 1, one
has ρ(W ⊗ A) ≥ ρ(A).
Proof: Due to j∈Ni wi,j = 1, it is inferred that W 1 = 1,
which implies that 1 is an eigenvalue of W . Hence, there exist
W A
A
λW
q ≥ 1 and λq = λq λq ≥ λq , which implies ρ(W ⊗ A) ≥
ρ(A).
Based on Lemma 3, choosing wi,j to guarantee ρ(W ⊗ A) =
ρ(A) is an important principle for the security of state omniscience. Thus, the secure range for the interaction weights of
the distributed observers (5) is summarized as follows.
Theorem 5: For the distributed observers (5) with
j∈Ni wi,j = 1, if the interaction weights satisfy wi,j > 0 for
any i, j ∈ V, then ρ(W ⊗ A) = ρ(A) holds. Proof: Based on Gerschgorin theorem and j∈Ni wi,j = 1,
W
one obtains |λW
q − wi,i | ≤ 1 − wi,i for any λq ∈ Λ(W ) and
i ∈ V when wi,j ≥ 0 holds for any i, j ∈ V. Then, we have
−1 < 2wi,i − 1 ≤ λW
q ≤ 1 due to wi,i > 0, ∀i ∈ V. FurtherA
A
more, any λq ∈ Λ(W ⊗ A) satisfies |λq | ≤ |λW
q ||λq | ≤ |λq |
since |λW
q | ≤ 1 is established. Finally, combining with ρ(W ⊗
A) ≥ ρ(A) in Lemma 3 results in ρ(W ⊗ A) = ρ(A).
Secondly, the sensor protection scheme is studied to defend
perfect DFDI attacks with complete stealthiness. Let ΓP
i =
P
P
, . . . , γi,N
) be the sensor protection matrix, where
diag(γi,1
P
= 1 if the jth measurement of the ith sensor node is proγi,j
P
= 0 otherwise. A sensor cannot be chosen as the
tected, and γi,j
attack target when it is protected, that is, ΓP
i Γi = 0.
Theorem 6: Perfect DFDI attacks with complete stealthiness
cannot be achieved in the distributed observers (5) if there exists
a sensor node i ∈ V such that the protected sensors satisfy
A
A
W
A
ΓP
i Ci uq = 0 for any uq corresponding to uq = vq ⊗ uq ∈
cs(Ua ).
Proof: Supposing Ci uA
q ∈ span(Γi ), there is a constant vecA
tor ϑi,q such that Ci uA
=
Γi ϑi,q . Then, we obtain ΓP
q
i Ci uq =
P
A
ΓP
i Γi ϑi,q = 0, which violates Γi Ci uq = 0. Thus, if there exists
P
A
i ∈ V such that Γi Ci uq = 0 for any uA
q corresponding to
/ span(Γ̄) holds for any uq ∈ cs(Ua ).
uq ∈ cs(Ua ), then C̄uq ∈
As a result, there exist no perfect DFDI attacks with complete
stealthiness in the distributed observers (5) according to Theorem 2.
satCorollary 4: Consider the sensor protection matrix ΓP
i
isfying Theorem 6. If the distributed observers (5) are compromised by DFDI attacks, which lead to limk→∞ ek = ∞,
then there exists a sensor node i ∈ V such that its residual-based
and residual-energy-based detectors expose such attacks with
D
limk→∞ pD
i,k = limk→∞ p̄i,k = 1.
Proof: If the protection matrix ΓP
i of a sensor node satisfies
/ span(Γ̄) for any uq ∈ cs(Ua ).
Theorem 6, then we have C̄uq ∈
Hence, according to the proof of Theorem 2, it is obtained
that limk→∞ zk = ∞ holds if limk→∞ ek = ∞. When
limk→∞ zk = ∞ is established, we have limk→∞ pD
i,k =
D
limk→∞ p̄i,k = 1, ∃i ∈ V, by following the similar proofs of
[43, Props. 1 and 2].
Remark 8: For a continue-time plant, the discrete-time observers (2) will lose more information with the sampling interval
T > 0 increasing. For the continue-time system matrix G, we
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4640
Fig. 2.
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
Longitudinal attitude of aircrafts.
have A = eGT [45]. If a eigenvalue of G has the positive real
part (or all the eigenvalues of G have the negative real parts),
then ρ(A) > 1 (or ρ(A) < 1) holds under any T . Hence, the
existence of perfect DFDI attacks with complete stealthiness
is not influenced by T when the attack targets are selected
arbitrarily. However, the attack sequences (10) need to be redesigned for different T since they depend on the eigenvalues
of W ⊗ A. Moreover, the secure range of the observer weights
in Theorem 5 remains the same for ρ(W ⊗ A) = ρ(A) under
different T . To establish a robust protection scheme for different
T , one can protect all the output data of a sensor node i ∈ V
satisfying Theorem 6.
Remark 9: The proposed results in this article can be extended
to linearizable nonlinear systems. For a nonlinear system satisfying [46, Th. 1], it is linearized as (1) with the coordinate
transformation xk = T (x∗k ), where x∗k is the state of original
nonlinear systems. Then, the state estimation of original nonlinear systems is obtained by x̂∗i,k+1 = T −1 (x̂i,k+1 ), where T −1 (·)
is the inverse function of T (·). Even in nonlinear systems, we can
still consider the attack objective in Definition 3, which depends
on the indexes ẽi,k and z̃i,k of linearized systems. Therefore, the
corresponding results of perfect DFDI attacks with complete
stealthiness can be extended into such linearizable nonlinear
systems.
VI. SIMULATION RESULTS
In this section,we demonstrate perfect DFDI attacks with
complete stealthiness based on the longitudinal motion model of
an aircraft system in [47], which is discretized with a sampling
period 0.1s. The considered aircraft states x1,k , . . . , x6,k are the
forward velocity, attack angle, pitch rate, pitch angle, elevon
deflection, and canard deflection, respectively. Fig. 2 illustrates
the longitudinal attitude of the aircraft, whose system matrix A,
shown at the bottom of this page.
Notice that the system matrix A has the real eigenvalues 0.5668, 0.9742, 0.0498, 0.0498 and imaginary eigenvalues
1.0711 + 0.0319i, 1.0711 − 0.0319i.
⎡
0.9961
⎢
⎢0.0001
⎢
⎢0.0011
A=⎢
⎢0.0001
⎢
⎢
⎣ 0
0
−4.4069
0.8738
0.9503
0.0509
0
0
−1.9937
0.0799
0.8133
0.0895
0
0
Fig. 3. Information interaction graph of sensor network under DFDI
attacks.
Suppose that the aircraft system (Plant) is measured by three
sensor nodes: S1 , S2 , and S3 . The sensor node S1 measures the
deflections of the elevon and canard. Consider that S1 sends
the integrated data x5,k + x6,k to the observer O1 for saving
communication resources. Moreover, S2 acquires the forward
velocity and attack angle, and S3 acquires the pitch rate and
pitch angle. These two sensor nodes also send the integrated
data to the observers O2 and O3 , respectively. Thus, the measurement matrices are C1 = [0 0 0 0 1 1], C2 = [1 1 0 0 0 0],
and C3 = [0 0 1 1 0 0]. The interaction network G among
these sensors is strongly connected and illustrated in Fig. 3.
Let the covariance matrices of the process and measurement
noises be Q = diag(0.022 I4 , 0.12 I2 ), R1 = 0.12 , R2 = 0.052 ,
and R3 = 0.052 . The initial state x0 is a zero-mean Gaussian
random variable with covariance 0.082 I6 . By checking the
detectability of each sensor node, we know that (C2 , A) and
(C3 , A) are detectable but (C1 , A) is not detectable. Consider
that the interaction weight matrix is chosen as
⎡
⎤
0.5 0.25 0.25
⎢
⎥
W = ⎣0.25 0.5 0.25⎦
0.25
0
0.75
which satisfies wi,j > 0 for any i, j ∈ V in Theorem 5. Hence,
ρ(W ⊗ A) = ρ(A) = 1.0715 holds. Then, the observer gains
are designed as, shown at the bottom of the next page.
Next, the estimation errors in these sensor nodes under no
attacks are shown in Fig. 4, where ei,j,k is the jth element of
ei,k . Although the system state is not detectable for the node S3 ,
the estimation error dynamics of S3 are still stable through the
data interactions with other two nodes. Since the dynamics of
all the estimation errors are stable, the distributed observers in
S1 , S2 , and S3 achieve state omniscience for the aircraft system.
Based on Theorem 1, perfect DFDI attacks with complete
stealthiness can be achieved with appropriate attack targets due
−3.2034
−0.0001
−0.0018
0.9999
0
0
1.5378
−0.0647
−0.8605
−0.0659
0.0498
0
⎤
−1.0289
⎥
0.0423 ⎥
⎥
0.6070 ⎥
⎥.
0.0466 ⎥
⎥
⎥
⎦
0
0.0498
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
Fig. 5.
a3,k .
4641
Trajectories of attack sequences a2,k and a3,k . (a) a2,k ; (b)
Fig. 4. Trajectories of estimation error ei,j,k under no attacks. (a)
e1,j,k ; (b) e2,j,k ; (c) e3,j,k .
to ρ(W ⊗ A) = 1.0715 > 1. Then, set λ1 = 1.0711 + 0.0319i
and λ2 = 1.0711 − 0.0319i. According to Theorem 1 and
Corollary 1, the attacker only needs to attack the sensor nodes
S2 and S3 , i.e., Γ1 = 0 and Γ2 = Γ3 = 1, since the sensor node
S1 satisfies C1 v1A = C1 v2A = 0. Furthermore, the decentralized
attack sequences, namely Attacks I, are designed as
(0.9965 − 0.002i)
a2,k+1 = a2,k + 0.5774θ1,k+1 λk+1
1
(0.9965 + 0.002i)
+ 0.5774θ2,k+1 λk+1
2
(−0.0221 − 0.0096i)
a3,k+1 = a3,k + 0.5774θ1,k+1 λk+1
1
(−0.0221 + 0.0096i)
+ 0.5774θ2,k+1 λk+1
2
(18)
∗
∗
where θ1,k = θ2,k
= 0.1144 for k ∈ N[0, 10) and θ1,k = θ2,k
=
0.0596 + 0.0168i for k ∈ N[10, ∞). The attack parameters
κ1 = κ2 = 0.1144, μ1 = μ∗2 = 0.5209 + 0.1469i and τ1 =
τ2 = 10 satisfy Theorem 3, which implies that Attacks I achieve
the attack objective in Definition 3. Under
these attack paz̃1,p = 0, ∞
rameters, one has ∞
p=0
p=0 z̃2,p = 1.9987,
∞
z̃
=
0.0727
and
z̃
=
2 based on Corol ∞
3,p
p
p=0
p=0
lary 3. Since the attack parameters satisfy Theorem 4, a2,k and
a3,k are real values all the time in Fig. 5.
In Figs. 6 and 7, the performance indexes of Attacks I are
shown, where ẽi,j,k is the jth element of ẽi,k . Fig. 6 illustrates
that Attacks I lead to the divergence of ẽi,k in each node. In
Fig. 7, z̃i,k converges to zero and kp=0 z̃i,p is bounded in
each node, which depicts the stealthy
Attacks I. In
capacities of addition, it is shown in Fig. 7 that kp=0 z̃1,p , kp=0 z̃2,p ,
Fig. 6. Trajectories of ẽi,j,k under Attacks I. (a) ẽ1,j,k ; (b) ẽ2,j,k ;
(c) ẽ3,j,k .
kp=0 z̃3,p , and kp=0 z̃p converge to 0, 1.9987, 0.0727,
and 2, respectively. This supports the theoretical results in Corollary 3. Therefore, by only compromising the sensor nodes S2
and S3 , Attacks I achieve perfect DFDI attacks with complete
stealthiness.
Consider that any sensor node is monitored by the residualbased detector gi,k and residual-energy-based detector ḡi,k with
T
L1 = 0.0358
−0.0126
−0.0906
−0.0052
0.0127
0.0122
L2 = 1.3388
−0.0343
−0.0848
−0.0390
0.0006
−0.0005
L3 = −9.6888
0.3796
1.0258
0.2863
−0.0017
0.0014
T
T
.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4642
Fig. 7.
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
Trajectories of z̃i,k and z̃i,k ; (b) k
k
z̃ p=0 i,p
under Attacks I. (a)
z̃ .
p=0 i,p
Fig. 9. Trajectories of ẽi,j,k under Attacks II. (a) ẽ1,j,k ; (b)
ẽ2,j,k ; (c) ẽ3,j,k .
Fig. 8. Detection rates and false alarm rates of each node’s detectors
under Attacks I.
Πi = Π̄i = 1. The threshold values are g1,th = 0.25, ḡ1,th = 0.3,
g2,th = 3, ḡ2,th = 11.5, g3,th = 0.2, and ḡ3,th = 0.18. Based on
10000 Monte Carlo simulations, the alarm rates of the residualbased and residual-energy-based detectors are depicted in Fig. 8.
Obviously, all the detection rates against Attacks I converge to
the false alarm rates in these sensor nodes. Hence, perfect DFDI
attacks with complete stealthiness can deceive such two classes
of detectors.
Furthermore, two comparative examples are given to demonstrate the danger of complete stealthiness and the effectiveness
of the sensor protection scheme.
1) Perfect DFDI Attacks without Complete Stealthiness: In
this example, we implement the DFDI attack sequences, namely
Attacks II, which have the same parameters as the attack sequences (18) except for μ1 = μ2 = 5. Obviously, such DFDI
attack sequences have no complete stealthiness since the attack
parameters violate Theorem 3. In Fig. 9, Attacks II still make
ẽi,k diverge in each node. However, compared with Fig. 7,
Fig. 10 illustrates that z̃i,k cannot converge to zero and
kp=0 z̃i,p is unbounded in a part of nodes. Therefore, the
Fig. 10.
Trajectories of z̃i,k and z̃i,k ; (b) k
k
z̃ p=0 i,p
under Attacks II. (a)
z̃ .
p=0 i,p
Fig. 11. Detection rates and false alarm rates of each node’s detectors
under Attacks II.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
4643
Fig. 14. Detection rates and false alarm rates of each node’s detectors
when S2 is protected from Attacks I.
Fig. 12. Trajectories of ẽi,j,k when S2 is protected from Attacks I.
(a) ẽ1,j,k ; (b) ẽ2,j,k ; (c) ẽ3,j,k .
the sensor node S2 . In Fig. 14, the DFDI attack sequences can be
detected in the sensor nodes S2 and S3 since the detection rates
increase to one hundred percent. Although Attacks I deceive S1
within the simulation time, the alarms of S2 or S3 can be reported
to S1 with just a flag bit. As a result, the sensor protection scheme
ensures Attacks I to be exposed in each node.
VII. CONCLUSION
Fig. 13.
Trajectories of z̃i,k and from Attacks I. (a) z̃i,k ; (b) k
k
z̃ p=0 i,p
when S2 is protected
z̃ .
p=0 i,p
From system eigenvalues and attack targets, we investigate
how DFDI attacks destabilize all observers and hold complete
stealthiness against state omniscience. The results show that
DFDI attacks can even cause such global destruction by only
compromising a part of sensor nodes. Moreover, the attack
sequences are designed to achieve the abovementioned objective
with the elaborate match of the attack parameters. In addition,
these attack sequences are improved to maintain real values
by involving multiple system eigenvalues. Finally, the security
of state omniscience under DFDI attacks is analyzed from the
interaction weights of distributed observers and the protection
scheme of sensors. In future works, we will focus on the security
of multiagent systems and complex dynamic networks under
perfect FDI attacks.
APPENDIX A
detection rates of the detectors increase in these nodes, which is
shown in Fig. 11. Especially, the detection rates of the residualenergy-based detectors in S2 and S3 increase to one hundred
percent. As a result, although DFDI attacks without complete
stealthiness can destabilize the estimation error dynamics in each
node, their stealthy capacities against the residual-based and
residual-energy-based detectors are much weaker than DFDI
attacks with complete stealthiness.
2) Sensor Protection Scheme: According to Theorem 6, Attacks I cannot achieve the attack objective in Definition 3 when
the measurement output of S2 or S3 is protected. Consider that
I, then Figs. 12 and 13 depict that
S2 is protected from Attacks
ei,k , z̃i,k , and kp=0 z̃i,p diverge in each sensor node.
Therefore, the stealthiness of Attacks I is broken by protecting
A. Proof of Lemma 2
Based on (9), one has
⎡
∞
p
(W ⊗ A) = [Ua
p=0
∞
Jap
⎢p=0
Ub ] ⎢
⎣
0
⎤
⎥ Va
⎥
∞
⎦ V
b
Jp
0
p=0
b
which leads to
⎡
∞
p=0
∞
⎢p=0
V (W ⊗ A)p U V νp = ⎢
∞
⎣
p=0
Jap Va νp
Jbp Vb νp
⎤
⎥
⎥
⎦
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4644
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
Va
=∞·
φ + V φ̄.
Vb
(19)
Since ρ(Jb ) < 1 and νp is a constant vector, there exists a
constant ν̄ ≥ νp such that
∞
∞
Vb ν̄
p
Jb Vb ν p ≤
Jb p Vb ν̄ ≤
< ∞.
1
− Jb p=0
p=0
for any sensor node. As a result, ρ(W ⊗ A) ≥ 1 is established if
perfect DFDI attacks with complete stealthiness can be achieved
in the distributed observers (5).
Next, we prove that there exist no perfect DFDI attacks with
complete stealthiness if condition (ii) is violated. According
to Lemma 2, when limk→∞ ẽi,k = ∞ is established for any
node, one has
p
This implies that ∞
constant vector. Therefore,
p=0 Jb Vb νp is a
∞
p
p
p=0 Ja Va νp = ∞ holds if ∞
p=0 (W ⊗ A) νp = ∞.
Then, it is obtained from (19) that Va φ = 0 and Vb φ = 0. Define
u1 , . . . , us̄ as the columns of Ua and us̄+1 , . . . , uN n as the
columns of Ub . Since U is a full-rank matrix, the vector φ = 0 is
represented as φ = l1 u1 + · · · + lN n uN n , where the constants
l1 , . . . , lN n are not all zero. However, if ls̄+1 , . . . , lN n are not
all zero, then we have Vb φ = 0 that violates Vb φ = 0. As a
result, φ is rewritten as φ = l1 u1 + · · · + ls̄ us̄ . Due to Va φ = 0,
there exists at least one constant li = 0 for i ∈ {1, . . . , s̄}, which
implies φ ∈ span(Ua ).
B. Proof of Lemma 2
(If) If Ci vqA ∈ span(Γi ) is established for any sensor node,
then there exist the constant vectors δ1,q , . . . , δN,q such that
W T
W T
δ1,q , . . . , vN,q
δN,q ]T
Ci vqA = Γi δi,q , ∀i ∈ V. Denote δq [v1,q
W
W
W
with vi,q being the ith entry of vq . Since vq has no zero
entries, the equation C̄(vqW ⊗ vqA ) = Γ̄δq holds, which means
C̄vq ∈ span(Γ̄).
(Only if) When C̄vq ∈ span(Γ̄) is satisfied, there exists a
constant vector δq such that C̄vq = Γ̄δq . Hence, it is obtained
that Ci vqA = Γi δi,q , ∀i ∈ V. As a result, Ci vqA ∈ span(Γi ) holds
for any sensor node.
lim ẽk = ∞ ·
k→∞
s̄
lq uq + φ̄
(22)
q=1
where l1 · · · , ls̄ are constants and at least one of them is nonzero.
/ span(Γ̄) holds for any q ∈ {1, . . . , s̄}, it
Furthermore, if C̄uq ∈
can be deduced that
s̄
(23)
lim z̃k = ∞ ·
lq C̄uq + Γ̄ak + φ̄ = ∞
k→∞
q=1
which violates Definition 3. In conclusion, at least one vector uq ∈ cs(Ua ) satisfies C̄uq ∈ span(Γ̄) if there exist perfect DFDI attacks with complete stealthiness in the distributed
observers (5).
D. Proof of Proposition 3
First, we deduce the solution of the error dynamics (6)
under the DFDI attack sequences (10). It is easy to see the
initial value of Ek is zero, i.e., E0 = 0. Due to Γ̄δq = C̄vq , for
k ∈ N[1, τq1 + 1), Ek is described by
Ek = (W ⊗ A − L̄C̄)Ek−1 + L̄C̄
κq λk−1
vq
(24)
q
q∈S
which follows that
Ek −
⎛
κq λkq vq = (W ⊗ A − L̄C̄) ⎝Ek−1 −
q∈S
C. Proof of Theorem 2
⎞
κq λk−1
vq ⎠ .
q
q∈S
(25)
Here, we analyze if condition (i) is violated, then there exist
no perfect DFDI attacks with complete stealthiness in the distributed observers (5). When ρ(W ⊗ A) < 1 holds, one obtains
W ⊗ A < 1 according to Lemma 1. From (8), the Euclidean
norm of ẽk satisfies
k−1
√
ẽk ≤ N nU G−1
L̄ z̃p W ⊗ Ak−p−1
p=0
(20)
where < 1 − ρ(W ⊗ A). For any k ∈ N[0, ∞), z̃i,k ≤ α
and kp=0 z̃i,p ≤ β both mean that z̃k ≤ ᾱ holds for a
constant ᾱ. Based on norm equivalence, there exists a constant
α̃
that z̃k ≤ α̃, ∀k ∈ N[0, ∞). Furthermore, we have
such
∞
p
−1
and
p=0 W ⊗ A = (1 − W ⊗ A )
√
N nU G−1
L̄ α̃
<∞
(21)
lim ẽk ≤
k→∞
1 − W ⊗ A
which violates limk→∞ ẽi,k = ∞, ∀i ∈ V. Therefore, if
ρ(W ⊗ A) < 1, then limk→∞ ẽi,k = ∞ and z̃i,k ≤ α (or
kp=0 z̃i,p ≤ β), ∀k ∈ N[0, ∞), cannot hold simultaneously
Then, (25) is iterated as
⎛
Ek = (W ⊗ A − L̄C̄)k ⎝E0 −
⎞
κq v q ⎠ +
q∈S
κq λkq vq .
q∈S
(26)
Combing (26) with E0 = 0 results in
Ek = −
κq (W ⊗ A − L̄C̄)k vq +
κq λkq vq
q∈S
(27)
q∈S
for k ∈ N[0, τq1 + 1). To obtain the solution of Ek for k ∈
N[τq1 + 1, τqs∗ + 1), the dynamics of Eτq1 +1 are first studied
as a guide. Supposing τq1 < τq2 , one obtains
τ
Eτq1 +1 = (W ⊗ A − L̄C̄)Eτq1 + L̄C̄μq1 κq1 λq1q1 vq1
+ L̄C̄
κq λτqq vq
(28)
q∈S\q1
which is equivalent to
τ
Eτq1 +1 − μq1 κq1 λq1q1
+1
v q1 −
κq λqτq +1 vq
q∈S\q1
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
⎛
= (W ⊗ A − L̄C̄) ⎝Eτq1 −
− (μq1 −
⎞
and for k ∈ N[τqs∗ + 1, ∞)
κq λτqq vq ⎠
q∈S
ẽk = −
τ
1)κq1 λq1q1 (W
k
+
τq
τ
− (μq1 − 1)κq1 λq1q1 (W ⊗ A − L̄C̄)vq1 .
(29)
Therefore, we have the following dynamics of Ek for k ∈
N[τqr + 1, τqr+1 + 1).
μq κq λk−1
vq
Ek = (W ⊗ A − L̄C̄)Ek−1 + L̄C̄
q
q∈Sk−1
∗
q∈Sk−1
κq λk−1
vq .
q
(30)
Here, Sk−1 = {q1 , . . . , qr } for k ∈ N[τqr + 1, τqr+1 + 1).
Then, it can be deduced from (30) that
κq (W ⊗ A − L̄C̄)k vq
Ek = −
q∈S
+
μq κq λkq vq +
q∈Sk−1
−
∗
q∈Sk−1
κq λkq vq
(μq − 1)κq λτqq (W ⊗ A − L̄C̄)k−τq vq .
(31)
−
−
(35)
As a result, (33)–(35) constitute solution (12) of the error dynamics (6) under the attack sequences (10).
Second, the solution of the residual dynamics (7) is analyzed.
For k ∈ N[0, τq1 ), we have
κq λkq vq
Zk = C̄Ek − C̄
= −
ẽk = −
κq (W ⊗ A − L̄C̄) vq +
q∈S p=0
k
(32)
κq λpq vq
q∈S p=0
(33)
ẽk = −
τq
κq λpq vq +
q∈Sk−1 p=0
−
∗
q∈Sk−1
p=0
κq (W ⊗ A − L̄C̄)p vq +
q∈S p=0
+
k
k
k
κq C̄(W ⊗ A − L̄C̄)k vq .
(36)
Next, it is obtained that for k ∈ N[τqr , τqr+1 )
μq κq λkq vq − C̄
κq λkq vq
Zk = C̄Ek − C̄
= −
q∈Sk∗
q∈Sk
κq C̄(W ⊗ A − L̄C̄)k vq
(μq − 1)κq λτqq C̄(W ⊗ A − L̄C̄)k−τq vq . (37)
Based on (32), for k ∈ N[τqs∗ , ∞)
μq κq λkq vq
Zk = C̄Ek − C̄
= −
q∈S
κq C̄(W ⊗ A − L̄C̄)k vq
q∈S
−
(μq − 1)κq λτqq C̄(W ⊗ A − L̄C̄)k−τq vq .
In light of (36)–(38), the solutions for the dynamics of z̃k obey
that for k ∈ N[0, τq1 )
z̃k = −
κq λpq vq
μq κq λpq vq
(38)
q∈S
for k ∈ N[τqr + 1, τqr+1 + 1)
k
q∈S
q∈Sk
Based on (27), (31), and (32), the solutions for the dynamics of
ẽk satisfy that for k ∈ N[0, τq1 + 1)
p
q∈S
q∈S
k
(μq − 1)κq λτqq (W ⊗ A − L̄C̄)p−τq vq .
q∈S p=τq +1
−
q∈S
(μq − 1)κq λτqq (W ⊗ A − L̄C̄)k−τq vq .
μq κq λpq vq
q∈S
Similarly, for k ∈ N[τqs∗ + 1, ∞), one has
Ek = −
κq (W ⊗ A − L̄C̄)k vq +
μq κq λkq vq
q∈S
k
q∈S p=τq +1
k
q∈Sk−1
κq λpq vq +
q∈S p=0
q∈S
+ L̄C̄
κq (W ⊗ A − L̄C̄)p vq
q∈S p=0
⊗ A − L̄C̄)vq1
⎛
⎞
= (W ⊗ A − L̄C̄)τq1 +1 ⎝E0 −
κq v q ⎠
4645
k
κq C̄(W ⊗ A − L̄C̄)p vq
(39)
q∈S p=0
for k ∈ N[τqr τqr+1 )
z̃k = −
q∈Sk−1 p=τq +1
k
κq C̄(W ⊗ A − L̄C̄)p vq
q∈S p=0
(μq − 1)κq λτqq (W ⊗ A − L̄C̄)p−τq vq
q∈Sk−1 p=τq +1
−
k
q∈Sk p=τq
(34)
(μq − 1)κq λτqq C̄(W ⊗ A − L̄C̄)p−τq vq
(40)
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4646
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
and for k ∈ N[τqs∗ , ∞)
z̃k = − κq
k
where πk = k − τq + 1 for k ∈ N[τq , ∞), and πk = 0 otherwise. Then, we obtain that
k
p (47)
z̃k ≤
|κq |C̄ (W ⊗ A − L̄C̄) vq .
C̄(W ⊗ A − L̄C̄)p vq
q∈S p=0
−
k
q∈S p=τq
p=πk
q∈S
(μq − 1)κq λτqq C̄(W ⊗ A − L̄C̄)p−τq vq .
(41)
With ρ(W ⊗ A − L̄C̄) < 1, one has
k
(W ⊗ A − L̄C̄)p vq p=0
As a result, solution (13) of the residual dynamics (7) is inferred
from (39) to (41).
k
≤
√
p
N nÛ G−1
∗ W ⊗ A − L̄C̄ vq p=0
E. Proof of Theorem 3
and
k
p (W
⊗
A
−
L̄
C̄)
v
q
p=k−τq +1
(If) According to (12) in Proposition 3, it can be obtained that
lim ẽk = −
κq Ψq,∞ −
(μq − 1)κq λτqq Ψ̄q,∞
k→∞
q∈S
+
τq
q∈S
κq λpq vq
q∈S p=0
where
k−τq
Ψq,k +
∞
μq κq λpq vq
(42)
q∈S p=τq +1
k
p=0 (W
L̄C̄)p vq .
p
⊗ A − L̄C̄) vq
Ψ̄q,k and
Due to ρ(W ⊗ A − L̄C̄) < 1,
p=1 (W ⊗ A −
Ψq,∞ and Ψ̄q,∞ can be solved by
(I − W ⊗ A + L̄C̄)Ψq,∞ = vq
(43)
(I − W ⊗ A + L̄C̄)Ψ̄q,∞ = (W ⊗ A − L̄C̄)vq .
(44)
Note that the first three items in the right-hand side of (42) are
all constant vectors. For any q ∈ S, one has λq > 1, which
q
> 0. Thus, if there is κq = 0, q ∈ S,
means μq = 1 − λ−τ
∞ q
W A
then q∈S p=τq +1 μq κq λpq vi,q
vq = ∞ is established for
W
any i ∈ V since vq has no zero entries and vqA1 , . . . , vqAs∗ are
linearly independent. As a result, limk→∞ ei,k = ∞, ∀i ∈ V,
is obtained.
Based on (13), z̃k is described as
(κq + (μq − 1)κq λτqq )C̄Ψq,∞ .
(45)
lim z̃k = −
k→∞
q∈S
If (1 − μq )λτqq − 1 = 0, ∀q ∈ Sκ , then (1 + (μq − 1)λτqq )κq =
0 holds for any q ∈ S, which implies limk→∞ z̃k = 0.
Moreover, the upper bound of z̃k under condition (14) is
investigated. According to (14), we can rewrite (13) as follows:
z̃k = −
k
k
≤
Fq,k kp=0 W ⊗
Due
to
W ⊗ A − L̄C̄ < 1,
and
Gq,k kp=k−τq +1 W ⊗ A −
A − L̄C̄p vq L̄C̄p vq are monotonically increasing for k ∈ N[0, τq )
and decreasing for k ∈ N[τq , ∞), respectively. Hence, it is
obtained that for k ∈ N[0, τq )
k
√
(W ⊗ A − L̄C̄)p vq ≤ N nÛ G−1
∗ Fq,τq −1
p=π
k
and for k ∈ N[τq , ∞)
k
√
(W ⊗ A − L̄C̄)p vq ≤ N nÛ G−1
∗ Gq,τq .
p=πk
∞
p
Further considering
p=0 W ⊗ A − L̄C̄ vq = (1 −
W ⊗ A − L̄C̄ )−1 vq > Fq,τqr −1 > Gq,τqr , the upper
bound of z̃k satisfies (15) at any time. As a result, there exists
a constant α such that z̃i,k ≤ α, ∀k ∈ N[0, ∞) when z̃k is
bounded at any time.
By (13), kp=0 z̃p is described as
k
z̃p = −
p=0
−
−
= −
+
p
q∈S p=πk
k p−τ
q
k p−τ
q
q∈Sk p=τq l=0
κq C̄(W ⊗ A − L̄C̄) vq
κq C̄(W ⊗ A − L̄C̄)p vq
κq C̄(W ⊗ A − L̄C̄)l vq
q∈Sk p=τq l=0
κq C̄(W ⊗ A − L̄C̄) vq
μq κq λτqq C̄(W ⊗ A − L̄C̄)l vq
κq λτqq C̄(W ⊗ A − L̄C̄)l vq (48)
which follows from (1 − μq )λτqq − 1 = 0, ∀q ∈ Sκ that
q∈Sk p=k−τq +1
k
p
k q∈S p=0 l=0
p
k
p
N nÛ G−1
∗ W ⊗ A − L̄C̄ vq .
p=k−τq +1
q∈Sk∗ p=0
√
(46)
k
p=0
z̃p = −
p
k κq C̄(W ⊗ A − L̄C̄)l vq
q∈Sk∗ p=0 l=0
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
k
−
p
κq C̄(W ⊗ A − L̄C̄)l vq
q∈Sk p=τq l=p−τq +1
q −1 p
τ
−
κq C̄(W ⊗ A − L̄C̄)l vq
q∈Sk p=0 l=0
k
= −
p
κq C̄(W ⊗ A − L̄C̄)l vq
q∈Sk p=τq l=p−τq +1
−
p
k−π
k κq C̄(W ⊗ A − L̄C̄)l vq .
(49)
q∈S p=0 l=0
Then, we have
k
k
≤
z̃
|κ
|
C̄
p
q
(W ⊗ A − L̄C̄)l vq p=τq l=p−τq +1
q∈Sk
k−π p
k +
|κq |C̄ (W ⊗ A − L̄C̄)l vq .
p=0
p
p=0 l=0
q∈S
(50)
Based on Lemma 1, the last term of (50) satisfies
k−π p
k l (W ⊗ A − L̄C̄) vq p=0 l=0
≤
k−π
k
p
√
l
N nÛ G−1
∗ W ⊗ A − L̄C̄ vq .
by contradiction, if Ψq1 ,∞ , . . . , Ψqs∗ ,∞ are linearly dependent,
then there exist the constants lq1 , . . . , lqs∗ such that lq1 Ψq1 ,∞ +
· · · + lqs∗ Ψqs∗ ,∞ = 0. Combining with Ψq,∞ = (I − W ⊗
A + L̄C̄)−1 vq , one has (I − W ⊗ A + L̄C̄)−1 (lq1 vq1 + · · · +
lqs∗ vqs∗ ) = 0. Then, lq1 vq1 + · · · + lqs∗ vqs∗ = 0 holds since
I − W ⊗ A + L̄C̄ is full rank, which violates the linear independence of vq1 , . . . , vqs∗ . As a result, Ψq1 ,∞ , . . . , Ψqs∗ ,∞ are
linearly independent.
Then, we prove that the attack sequences (10) violate Definition 3 if (14) is not established. When κq = 0, ∀q ∈ S, holds, it is
easy to see limk→∞ ẽk = 0 according to (42), which violates
Definition 3.
If (1 − μq )λτqq − 1 = 0, ∃q ∈ Sκ , then there exists q ∈ S
such that (1 + (μq − 1)λτqq )κq = 0. Since Ψ
q1 ,∞ , . . . , Ψqs∗ ,∞
are linearly independent, one obtains
q∈S (κq + (μq −
1)κq λτqq )Ψq,∞ = 0. Thus, when (1 − μq )λτqq − 1 = 0, ∃q ∈
Sκ , is established,
there are system parameters (e.g. C̄ is row full
rank) such that q∈S (κq + (μq − 1)κq λτqq )C̄Ψq,∞ = 0, which
implies limk→∞ z̃i,k = 0, ∃i ∈ V according to (45).
Furthermore, we intend to prove that the index (iv) is also
violated if (1 − μq )λτqq − 1 = 0, ∃q ∈ Sκ . Let us rewrite (48)
as
k
z̃p = −
p=0
p=0 l=0
Furthermore, it can be deduced from (50) that
p
k
l (W ⊗ A − L̄C̄) vq p=τq l=p−τq +1
≤
k
p
p=τq l=p−τq +1
k
√
l
N nÛ G−1
∗ W ⊗ A − L̄C̄ vq .
p
κq C̄Ξq,k −
q∈S
q∈Sk
where Ξq,k satisfies
p=0
p
l=0 (W
⊗ A − L̄C̄)l vq . Notice that Ξq,k
(I − W ⊗ A + L̄C̄)Ξq,k
= −
k
(W ⊗ A − L̄C̄)p+1 vq + kvq
p=0
which
implies
(I − W ⊗ A + L̄C̄)Ξq,∞ =−Ψ̄q,∞ +
∞
limk→∞ kvq . Based on (51), it is obtained that
p=0 z̃p =
τq
− q∈S ηq C̄Ξq,∞ , where ηq (1 + (μq − 1)λq )κq . If
(1 − μq )λτqq − 1 = 0, ∃q ∈ Sκ , i.e., ηq = 0, ∃q ∈ S, is satisfied,
then there exist system parameters (e.g., C̄ is row full rank)
such that ∞
p=0 z̃p = ∞.
In conclusion, (14) holds if the attack sequences (10) satisfy
Definition 3 in arbitrary distributed observers that conform to
(5) with W ∈ W, ρ(W ⊗ A) > 1 and ρ(W ⊗ A − L̄C̄) < 1. F. Proof of Corollary 3
L̄C̄l vq where Lq,k p=τq l=p−τq +1 W ⊗ A −
is
also monotonically increasing for k ∈ N[0,
Combinτ∞).
q
W ⊗ A −
ing with Lq,∞ = (1 − W ⊗ A − L̄C̄ )−1 p=1
L̄C̄p vq , the upper bound of kp=0 z̃p satisfies (16)
at
any time. As a result, there exists a constant β such that
kp=0 z̃i,p ≤ β, ∀k ∈ N[0, ∞), since kp=0 z̃p is bounded
for any time.
In conclusion, the attack indexes in Definition 3 are achieved
by the attack sequences (10) if (14) is established.
(Only if) To analyze the necessity, we first prove that
Ψq1 ,∞ , . . . , Ψqs∗ ,∞ are linearly independent. Based on the proof
(μq − 1)κq λτqq C̄Ξq,k−τq
(51)
k
p=0 l=0
Obviously, Hk,q = kp=0 pl=0 W ⊗ A − L̄C̄l vq is
monotonically increasing for k ∈ N[0, ∞), which results in
k−π p
√
k l (W ⊗ A − L̄C̄) vq ≤ N nÛ G−1
∗ Hq,τq −1 .
4647
Combined with (13) and (14),
lows:
∞
z̃p = −
p=0
q −1 p
τ
∞
p=0 z̃p
is described as fol-
κq C̄(W ⊗ A − L̄C̄)l vq
q∈S p=0 l=0
−
∞
p
κq C̄(W ⊗ A − L̄C̄)l vq . (52)
q∈S p=τq l=p−τq +1
Define Θq,k kp=τq pl=p−τq +1 (W ⊗ A − L̄C̄)l vq , then it is
τq
obtained that Θq,∞ = (I − W ⊗ A + L̄C̄)−1 p=1
(W ⊗ A −
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
4648
IEEE TRANSACTIONS ON AUTOMATIC CONTROL, VOL. 68, NO. 8, AUGUST 2023
L̄C̄)p vq . Substituting Ξq,k and Θq,∞ into (52) results in
∞
p=0
z̃p = −
κq C̄Δq = −
q∈S
κq C̄(Ξq,τq −1 + Θq,∞ ).
q∈S
(53)
As a result, ∞
q∈S κq Ci Δq,i holds since C̄
p=0 z̃i,p = is block diagonal.
G. Proof of Theorem 4
The global model of the DFDI attack sequences (10) is given
as
ak+1 = ak −
θq,k+1 λk+1
δq .
q
(54)
q∈S
Consider an imaginary eigenvalue λq ∈ ΛP (W ⊗ A), which
corresponds to an imaginary eigenvector vq ∈ ΩP (W ⊗ A).
Due to ((λq IN n − W ⊗ A)vq )∗ = (λ∗q IN n − W ⊗ A)vq∗ , there
is an imaginary eigenvalue and an imaginary eigenvector of W ⊗
A that satisfy λq̄ = λ∗q and vq̄ = vq∗ , respectively. According to
C̄vq = Γ̄δq , δq and δq̄ are also conjugate. Hence, by choosing
κq = κq̄ ∈ R, we obtain θq,k λkq δq + θq̄,k λkq̄ δq̄ = 2κq Re{λkq δq }
for any k ∈ N[0, τq ). Then, for k ∈ N[τq , ∞), one has θq,k λkq =
q
κq (λkq − λk−τ
) based on (14), which implies θq,k λkq δq +
q
k
q
θq̄,k λq̄ δq̄ = 2κq Re{(λkq − λk−τ
)δq } with τq = τq̄ ∈ N[1, ∞)
q
∗
and μq = μq̄ . As a result, ak is real number for any time unq
der κq = κq̄ ∈ R, τq = τq̄ ∈ N[1, ∞) and μq = μ∗q̄ = 1 − λ−τ
q ,
∀q ∈ S.
REFERENCES
[1] E. Hashemi, M. Pirani, B. Fidan, A. Khajepour, S. Chen, and B. Litkouhi,
“Distributed robust vehicle state estimation,” in Proc. IEEE Intell. Veh.
Symp., 2017, pp. 693–698.
[2] J. Zeng, J. Liu, T. Zou, and D. Yuan, “State estimation of wastewater
treatment processes using distributed extended Kalman filters,” in Proc.
IEEE Conf. Decis. Control, 2016, pp. 6721–6726.
[3] M. H. Cintuglu and D. Ishchenko, “Secure distributed state estimation for networked microgrids,” IEEE Internet Things J., vol. 6, no. 5,
pp. 8046–8055, Oct. 2019.
[4] U. A. Khan and A. Jadbabaie, “On the stability and optimality of distributed
Kalman filters with finite-time data fusion,” in Proc. Amer. Control Conf.,
2011, pp. 3405–3410.
[5] R. Olfati-Saber, “Distributed Kalman filtering for sensor networks,” in
Proc. IEEE Conf. Decis. Control, 2007, pp. 5492–5498.
[6] S. Battilotti and M. Mekhail, “Distributed estimation for nonlinear systems,” Automatica, vol. 107, pp. 562–573, Sep. 2019.
[7] I. Matei and J. S. Baras, “Consensus-based linear distributed filtering,”
Automatica, vol. 48, no. 8, pp. 1776–1782, Aug. 2012.
[8] G. Battistelli, L. Chisci, G. Mugnai, A. Farina, and A. Graziano,
“Consensus-based linear and nonlinear filtering,” IEEE Trans. Autom.
Control, vol. 60, no. 5, pp. 1410–1415, May 2015.
[9] S. Park and N. C. Martins, “Design of distributed LTI observers for state
omniscience,” IEEE Trans. Autom. Control, vol. 62, no. 2, pp. 561–576,
Feb. 2017.
[10] A. Mitra and S. Sundaram, “Distributed observers for LTI systems,” IEEE
Trans. Autom. Control, vol. 63, no. 11, pp. 3689–3704, Nov. 2018.
[11] L. Wang and A. S. Morse, “A distributed observer for a time-invariant
linear system,” IEEE Trans. Autom. Control, vol. 63, no. 7, pp. 2123–2130,
Jul. 2018.
[12] W. Han, H. L. Trentelman, Z. Wang, and Y. Shen, “A simple approach
to distributed observer design for linear systems,” IEEE Trans. Autom.
Control, vol. 64, no. 1, pp. 329–336, Jan. 2019.
[13] T. Kim, C. Lee, and H. Shim, “Completely decentralized design of distributed observer for linear systems,” IEEE Trans. Autom. Control, vol. 65,
no. 11, pp. 4664–4678, Nov. 2020.
[14] A. Teixeira, I. Shames, H. Sandberg, and K. H. Johansson, “A secure
control framework for resource-limited adversaries,” Automatica, vol. 51,
pp. 135–148, Jan. 2015.
[15] C. Zhou, B. Hu, Y. Shi, Y. Tian, X. Li, and Y. Zhao, “A unified architectural
approach for cyberattack-resilient industrial control systems,” Proc. IEEE,
vol. 109, no. 4, pp. 517–541, Apr. 2021.
[16] Y. Li, L. Shi, P. Cheng, J. Chen, and D. E. Quevedo, “Jamming attacks
on remote state estimation in cyber-physical systems: A game-theoretic
approach,” IEEE Trans. Autom. Control, vol. 60, no. 10, pp. 2831–2836,
Oct. 2015.
[17] Q. Sun, J. Chen, and Y. Shi, “Event-triggered robust MPC of nonlinear
cyber-physical systems against DoS attacks,” Sci. China Inf. Sci., vol. 65,
Jan. 2022, Art. no. 110202.
[18] C. Deng, D. Zhang, and G. Feng, “Resilient practical cooperative output
regulation for MASs with unknown switching exosystem dynamics under
DoS attacks,” Automatica, vol. 139, May. 2022, Art. no. 110172.
[19] Y. Mo, R. Chabukswar, and B. Sinopoli, “Detecting integrity attacks on
SCADA systemss,” IEEE Trans. Control Syst. Technol., vol. 22, no. 4,
pp. 1396–1407, Jul. 2014.
[20] C.-Z. Bai, V. Gupta, and F. Pasqualetti, “On Kalman filtering with compromised sensors: Attack stealthiness and performance bounds,” IEEE Trans.
Autom. Control, vol. 62, no. 12, pp. 6641–6648, Dec. 2017.
[21] Z. Guo, D. Shi, K. H. Johansson, and L. Shi, “Worst-case stealthy
innovation-based linear attack on remote state estimation,” Automatica,
vol. 89, pp. 117–124, Mar. 2018.
[22] J. Shang, H. Yu, and T. Chen, “Worst-case stealthy attacks on stochastic
event-based state estimation,” IEEE Trans. Autom. Control, vol. 67, no. 4,
pp. 2052–2059, Apr. 2021.
[23] P. Cheng, Z. Yang, J. Chen, Y. Qi, and L. Shi, “An event-based stealthy
attack on remote state estimation,” IEEE Trans. Autom. Control, vol. 65,
no. 10, pp. 4348–4355, Oct. 2020.
[24] H. Song, P. Shi, C.-C. Lim, W.-A. Zhang, and L. Yu, “Attack and estimator
design for multi-sensor systems with undetectable adversary,” Automatica,
vol. 109, Nov. 2019, Art. no. 108545.
[25] Y. Mo and B. Sinopoli, “False data injection attacks in control systems,”
in Proc. 1st Workshop Secure Control Syst., Stockholm, Sweden, 2010,
paper 7.
[26] A.-Y. Lu and G.-H. Yang, “Malicious attacks on state estimation against
distributed control systems,” IEEE Trans. Autom. Control, vol. 65, no. 9,
pp. 3911–3918, Sep. 2020.
[27] J. Huang, D. W. C. Ho, F. Li, W. Yang, and Y. Tang, “Secure remote state
estimation against linear man-in-the-middle attacks using watermarking,”
Automatica, vol. 121, Nov. 2020, Art. no. 109182.
[28] M. Showkatbakhsh, Y. Shoukry, S. N. Diggavi, and P. Tabuada, “Securing
state reconstruction under sensor and actuator attacks: Theory and design,”
Automatica, vol. 116, Jun. 2020, Art. no. 108920.
[29] L. An and G.-H. Yang, “Distributed secure state estimation for cyberphysical systems under sensor attacks,” Automatica, vol. 107, pp. 526–538,
Sep. 2019.
[30] W. Yang, Y. Zhang, G. Chen, C. Yang, and L. Shi, “Distributed filtering under false data injection attacks,” Automatica, vol. 102, pp. 34–44,
Apr. 2019.
[31] M. Deghat, V. Ugrinovskii, I. Shames, and C. Langbort, “Detection and
mitigation of biasing attacks on distributed estimation networks,” Automatica, vol. 99, pp. 369–381, Jan. 2019.
[32] J. Yang, W.-A. Zhang, and F. Guo, “Adaptive distributed Kalman-like filter
for power system with cyber attacks,” Automatica, vol. 137, Mar. 2022,
Art. no. 110091.
[33] F. Pasqualetti, F. Dörfler, and F. Bullo, “Attack detection and identification
in cyber-physical systems,” IEEE Trans. Autom. Control, vol. 58, no. 11,
pp. 2715–2729, Nov. 2013.
[34] Y. Chen, S. Kar, and J. M. F. Moura, “Dynamic attack detection in cyberphysical systems with side initial state information,” IEEE Trans. Autom.
Control, vol. 62, no. 9, pp. 4618–4624, Sep. 2017.
[35] R. Deng, G. Xiao, R. Lu, H. Liang, and A. V. Vasilakos, “False data
injection on state estimation in power systems—Attacks, impacts, and defense: A. survey,” IEEE Trans. Ind. Informat., vol. 13, no. 2, pp. 411–423,
Apr. 2017.
[36] Z. Zhao, Y. Huang, Z. Zhen, and Y. Li, “Data-driven false data-injection
attack design and detection in cyber-physical systems,” IEEE Trans. Cybern., vol. 51, no. 12, pp. 6179–6187, Dec. 2021.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.
ZHANG et al.: DFDI ATTACKS AGAINST STATE OMNISCIENCE: EXISTENCE AND SECURITY ANALYSIS
[37] L. Hu, Z. Wang, Q.-L. Han, and X. Liu, “State estimation under false data
injection attacks: Security analysis and system protection,” Automatica,
vol. 87, pp. 176–183, Jan. 2018.
[38] A.-Y. Lu and G.-H. Yang, “Malicious adversaries against secure state
estimation: Sparse sensor attack design,” Automatica, vol. 136, Feb. 2022,
Art. no. 110037.
[39] Z.-H. Pang, G.-P. Liu, D. Zhou, F. Hou, and D. Sun, “Two-channel
false data injection attacks against output tracking control of networked
systems,” IEEE Trans. Ind. Electron., vol. 63, no. 5, pp. 3242–3251,
May 2016.
[40] Q. Zhang, K. Liu, Y. Xia, and A. Ma, “Optimal stealthy deception attack
against cyber-physical systems,” IEEE Trans. Cybern., vol. 50, no. 9,
pp. 3963–3972, Sep. 2020.
[41] W. Xu, Z. Wang, L. Hu, and J. Kurths, “State estimation under joint
false data injection attacks: Dealing with constraints and insecurity,” IEEE
Trans. Autom. Control, to be published, doi: 10.1109/TAC.2021.3131145.
[42] T. Sui and X. M. Sun, “The vulnerability of distributed state estimator
under stealthy attacks,” Automatica, vol. 133, Nov. 2021, Art. no. 109869.
[43] T.-Y. Zhang and D. Ye, “False data injection attacks with complete stealthiness in cyber-physical systems: A self-generated approach,” Automatica,
vol. 120, Oct. 2020, Art. no. 109117.
[44] D. Ye and T.-Y. Zhang, “Summation detector for false data-injection
attack in cyber-physical systems,” IEEE Trans. Cybern., vol. 50, no. 6,
pp. 2338–2345, Jun. 2020.
[45] K. Ogata, Discrete-Time Control Systems. Englewood Cliffs, NJ, USA:
Prentice-Hall, 1987.
[46] W. Lin and C. I. Byrnes, “Remarks on linearization of discrete-time
autonomous systems and nonlinear observer design,” Syst. Control Lett.,
vol. 25, no. 1, pp. 31–40, May 1995.
[47] L. An and G.-H. Yang, “Secure state estimation against sparse sensor
attacks with adaptive switching mechanism,” IEEE Trans. Autom. Control,
vol. 63, no. 8, pp. 2596–2603, Aug. 2018.
Tian-Yu Zhang (Member, IEEE) received the
B.S. degree in electrical engineering and automation from the North China University of
Science and Technology, Tangshan, China, in
2016 and the M.S. and Ph.D. degrees in control science and engineering from Northeastern
University, Shenyang, China, in 2018 and 2022,
respectively.
He is currently a Postdoctoral Research
Fellow with the College of Information Science and Engineering, Northeastern University,
Shenyang, China. His research interests include security of cyberphysical systems, distributed estimation, and multiagent systems.
Dr. Zhang was the recipient of the fellowship of China National Postdoctoral Program for Innovative Talents in 2022.
4649
Dan Ye (Senior Member, IEEE) received the
B.S. and M.S. degrees in mathematics and applied mathematics from Northeast Normal University, Changchun, China, in 2001 and 2004,
respectively, and the Ph.D. degree in control
theory and engineering from Northeastern University, Shenyang, China, in 2008.
She was a Lecturer with the Northeastern
University from 2008 to 2010. She is currently a
Professor of the College of Information Science
and Engineering, Northeastern University. Her
research interest includes fault-tolerant control, robust control, adaptive
control, and security of cyber-physical systems.
Yang Shi (Fellow, IEEE) received the Ph.D.
degree in electrical and computer engineering
from the University of Alberta, Edmonton, AB,
Canada, in 2005.
From 2005 to 2009, he was an Assistant Professor and Associate Professor with the Department of Mechanical Engineering, University
of Saskatchewan, Saskatoon, SK, Canada. In
2009, he joined the University of Victoria, Victoria, BC, Canada, and he is currently a Professor
with the Department of Mechanical Engineering, University of Victoria, Victoria, BC, Canada. His current research
interests include networked and distributed systems, model predictive
control (MPC), cyber-physical systems (CPS), robotics and mechatronics, control of autonomous systems (AUV and UAV), and energy system
applications.
Dr. Shi was the recipient of the University of Saskatchewan Student Union Teaching Excellence Award in 2007, and the Faculty of
Engineering Teaching Excellence Award in 2012 at the University of
Victoria (UVic). He is the recipient of the JSPS Invitation Fellowship
(short-term) in 2013, the UVic Craigdarroch Silver Medal for Excellence
in Research in 2015, the 2017 IEEE TRANSACTIONS ON FUZZY SYSTEMS Outstanding Paper Award, the Humboldt Research Fellowship for
Experienced Researchers in 2018. He is currently the Chair of IEEE
IES Technical Committee on Industrial Cyber-Physical Systems, and
Co-Editor-in-Chief for IEEE TRANSACTIONS ON INDUSTRIAL ELECTRONICS.
He is currently an Associate Editor for Automatica, IEEE TRANSACTIONS
ON CONTROL SYSTEMS TECHNOLOGY, etc. He is currently a General Chair
of the 2019 International Symposium on Industrial Electronics (ISIE)
and the 2021 International Conference on Industrial Cyber-Physical
Systems (ICPS). He is a Fellow of ASME, CSME, and Engineering
Institute of Canada (EIC), and a registered Professional Engineer in
British Columbia, Canada.
Authorized licensed use limited to: BEIJING INSTITUTE OF TECHNOLOGY. Downloaded on September 08,2023 at 08:55:17 UTC from IEEE Xplore. Restrictions apply.