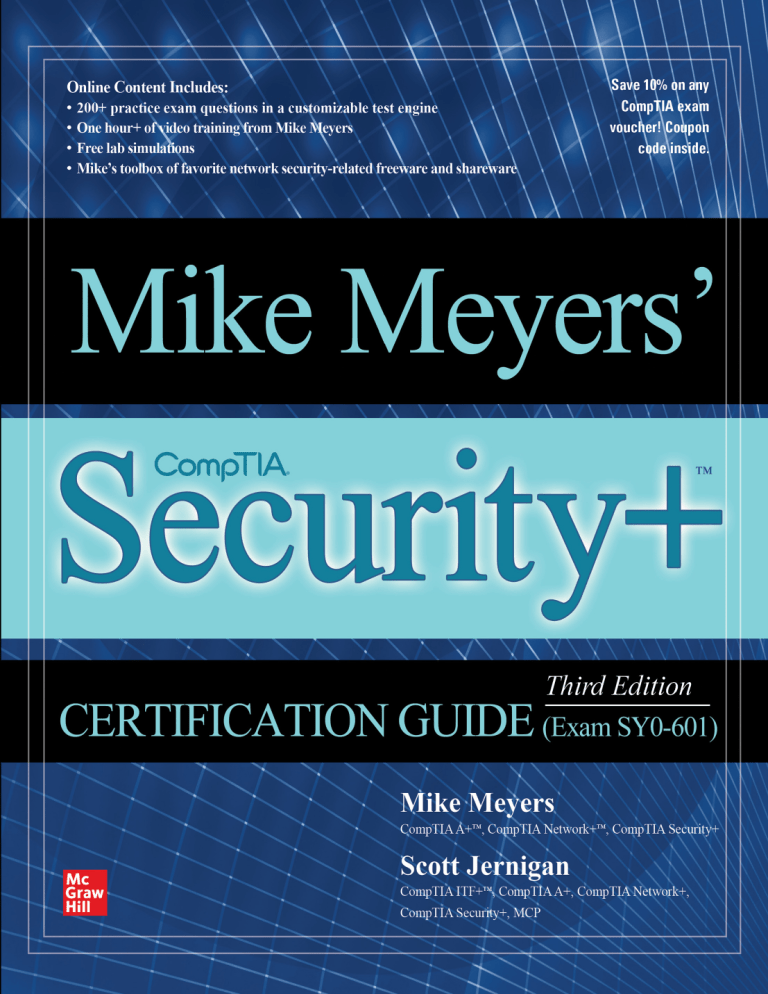
All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio i Mike Meyers’ ™ CompTIA Security+ Certification Guide 00-FM.indd 1 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio ii ABOUT THE AUTHORS Mike Meyers, CompTIA A+, CompTIA Network+, CompTIA Security+, is the industry’s leading authority on CompTIA certifications and the best-selling author of ten editions of CompTIA A+ Certification All-in-One Exam Guide (McGraw Hill). He is the president and founder of Total Seminars, LLC, a major provider of PC and network repair seminars for thousands of organizations throughout the world, and a member of CompTIA. Scott Jernigan, CompTIA ITF+, CompTIA A+, CompTIA Network+, CompTIA Security+, MCP, is the author or co-author (with Mike Meyers) of over two dozen IT certification books, including CompTIA IT Fundamentals (ITF+) Certification All-inOne Exam Guide (McGraw Hill). He has taught seminars on building, fixing, and securing computers and networks all over the United States, including stints at the FBI Academy in Quantico, Virginia, and the UN Headquarters in New York City, New York. About the Technical Editor Matt Walker is currently a member of the Cyber Security Infrastructure team at Kennedy Space Center with DB Consulting. An IT security and education professional for more than 20 years, he has served in multiple positions ranging from director of the Network Training Center and a curriculum lead/senior instructor for Cisco Networking Academy on Ramstein AB, Germany, to instructor supervisor and senior instructor at Dynetics, Inc., in Huntsville, Alabama, providing onsite certification-awarding classes for (ISC)2, Cisco, and CompTIA. Matt has written and contributed to numerous technical training books for NASA, Air Education and Training Command, and the US Air Force, as well as commercially (CEH Certified Ethical Hacker All-in-One Exam Guide, now in its fourth edition), and continues to train and write certification and college-level IT and IA security courses. 00-FM.indd 2 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio iii Mike Meyers’ ™ CompTIA Security+ Certification Guide Third Edition (Exam SY0-601) Mike Meyers Scott Jernigan New York Chicago San Francisco Athens London Madrid Mexico City Milan New Delhi Singapore Sydney Toronto McGraw Hill is an independent entity from CompTIA® and is not affiliated with CompTIA in any manner. This publication and accompanying media may be used in assisting students to prepare for the CompTIA Security+ exam. Neither CompTIA nor McGraw Hill warrants that use of this publication and accompanying media will ensure passing any exam. CompTIA and CompTIA Security+ are trademarks or registered trademarks of CompTIA in the United States and/or other countries. All other trademarks are trademarks of their respective owners. The CompTIA Marks are the proprietary trademarks and/or service marks of CompTIA and its affiliates used under license from CompTIA. 00-FM.indd 3 20/03/21 7:04 PM Copyright © 2021 by McGraw Hill. All rights reserved. Except as permitted under the United States Copyright Act of 1976, no part of this publication may be reproduced or distributed in any form or by any means, or stored in a database or retrieval system, without the prior written permission of the publisher, with the exception that the program listings may be entered, stored, and executed in a computer system, but they may not be reproduced for publication. ISBN: 978-1-26-047370-4 MHID: 1-26-047370-8 The material in this eBook also appears in the print version of this title: ISBN: 978-1-26-047369-8, MHID: 1-26-047369-4. eBook conversion by codeMantra Version 1.0 All trademarks are trademarks of their respective owners. Rather than put a trademark symbol after every occurrence of a trademarked name, we use names in an editorial fashion only, and to the benefit of the trademark owner, with no intention of infringement of the trademark. Where such designations appear in this book, they have been printed with initial caps. McGraw-Hill Education eBooks are available at special quantity discounts to use as premiums and sales promotions or for use in corporate training programs. To contact a representative, please visit the Contact Us page at www.mhprofessional.com. Information has been obtained by McGraw Hill from sources believed to be reliable. However, because of the possibility of human or mechanical error by our sources, McGraw Hill, or others, McGraw Hill does not guarantee the accuracy, adequacy, or completeness of any information and is not responsible for any errors or omissions or the results obtained from the use of such information. TERMS OF USE This is a copyrighted work and McGraw-Hill Education and its licensors reserve all rights in and to the work. Use of this work is subject to these terms. Except as permitted under the Copyright Act of 1976 and the right to store and retrieve one copy of the work, you may not decompile, disassemble, reverse engineer, reproduce, modify, create derivative works based upon, transmit, distribute, disseminate, sell, publish or sublicense the work or any part of it without McGraw-Hill Education’s prior consent. You may use the work for your own noncommercial and personal use; any other use of the work is strictly prohibited. Your right to use the work may be terminated if you fail to comply with these terms. THE WORK IS PROVIDED “AS IS.” McGRAW-HILL EDUCATION AND ITS LICENSORS MAKE NO GUARANTEES OR WARRANTIES AS TO THE ACCURACY, ADEQUACY OR COMPLETENESS OF OR RESULTS TO BE OBTAINED FROM USING THE WORK, INCLUDING ANY INFORMATION THAT CAN BE ACCESSED THROUGH THE WORK VIA HYPERLINK OR OTHERWISE, AND EXPRESSLY DISCLAIM ANY WARRANTY, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. McGraw-Hill Education and its licensors do not warrant or guarantee that the functions contained in the work will meet your requirements or that its operation will be uninterrupted or error free. Neither McGraw-Hill Education nor its licensors shall be liable to you or anyone else for any inaccuracy, error or omission, regardless of cause, in the work or for any damages resulting therefrom. McGraw-Hill Education has no responsibility for the content of any information accessed through the work. Under no circumstances shall McGraw-Hill Education and/or its licensors be liable for any indirect, incidental, special, punitive, consequential or similar damages that result from the use of or inability to use the work, even if any of them has been advised of the possibility of such damages. This limitation of liability shall apply to any claim or cause whatsoever whether such claim or cause arises in contract, tort or otherwise. All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio v For the great friends from around the world who shared this crazy lockdown with us: Andre de Gooyert, Tullowit, Alice Pozzi, Zak Morrill, Patricia Grace, Jose Braden, and so many others. Cheers! —Mike and Scott 00-FM.indd 5 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio vi This page intentionally left blank 00-FM.indd 6 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM CONTENTS AT A GLANCE Chapter 1 Risk Management .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 Chapter 2 Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77 Chapter 3 Identity and Account Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 153 Chapter 4 Tools of the Trade . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 217 Chapter 5 Securing Individual Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 267 Chapter 6 The Basic LAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327 Chapter 7 Securing Wireless LANs .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 371 Chapter 8 Securing Public Servers .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 401 Chapter 9 Securing Dedicated Systems .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 435 Chapter 10 Physical Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479 Chapter 11 Protocols and Applications .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 503 Chapter 12 Testing Infrastructure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 557 Chapter 13 Dealing with Incidents .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 601 Appendix A Exam Objective Map .. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 661 Appendix B About the Online Content . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 699 Glossary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 703 Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 769 vii 00-FM.indd 7 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio viii This page intentionally left blank 00-FM.indd 8 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM CONTENTS Chapter 1 Acknowledgments . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xix xxi Risk Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-1: Defining Risk . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Asset . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Likelihood . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Threat Actor . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Vulnerability and Threat . . . . . . . . . . . . . . . . . . . . . . . . . . . . Circling Back to the Risk Definition . . . . . . . . . . . . . . . . . . . Vectors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Threat Intelligence . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-2: Risk Management Concepts . . . . . . . . . . . . . . . . . . . . Infrastructure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Security Controls . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Risk Management Frameworks . . . . . . . . . . . . . . . . . . . . . . . Module 1-3: Security Controls . . . . . . . . . . . . . . . . . . . . . . . . . . . . Control Categories . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Control Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-4: Risk Assessment . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Risk Assessment Processes and Concepts . . . . . . . . . . . . . . . . Quantitative Risk Assessment . . . . . . . . . . . . . . . . . . . . . . . . Qualitative Risk Assessment . . . . . . . . . . . . . . . . . . . . . . . . . Putting It All Together: Risk Analysis . . . . . . . . . . . . . . . . . . Risk Response . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-5: Business Impact Analysis . . . . . . . . . . . . . . . . . . . . . . BIA Basics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Types of Impact . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Locating Critical Resources . . . . . . . . . . . . . . . . . . . . . . . . . . Calculating Impact . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Calculating Downtime . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-6: Data Security and Data Protection . . . . . . . . . . . . . . . Organizing Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Legal and Compliance . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Data Destruction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Privacy Breaches . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 1 2 2 3 3 5 6 6 7 16 16 18 18 25 25 25 27 28 33 36 37 38 40 41 43 45 45 46 47 48 51 56 58 ix 00-FM.indd 9 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide x Module 1-7: Personnel Risk and Policies . . . . . . . . . . . . . . . . . . . . . Hiring . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Onboarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Personnel Management Policies . . . . . . . . . . . . . . . . . . . . . . . Training . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . User Habits . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Offboarding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 1-8: Third-Party Risk and Policies . . . . . . . . . . . . . . . . . . . Third-Party Risk Management . . . . . . . . . . . . . . . . . . . . . . . Agreement Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Chapter 2 00-FM.indd 10 60 60 60 61 63 65 65 67 68 68 71 74 76 Cryptography. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 77 Module 2-1: Cryptography Basics . . . . . . . . . . . . . . . . . . . . . . . . . . 78 Essential Building Blocks . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78 Early Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 81 Cryptography Components . . . . . . . . . . . . . . . . . . . . . . . . . . 85 Module 2-2: Cryptographic Methods . . . . . . . . . . . . . . . . . . . . . . . 90 Symmetric Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . . 90 Asymmetric Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . 93 Hashing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 94 Limitations in Symmetric vs. Asymmetric Cryptography . . . . 96 Hybrid Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 97 The Perfect Cryptosystem . . . . . . . . . . . . . . . . . . . . . . . . . . . 97 Module 2-3: Symmetric Cryptosystems . . . . . . . . . . . . . . . . . . . . . 98 DES . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 98 3DES . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 101 AES . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 101 Blowfish . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 102 Twofish . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 102 RC4 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 102 Summary of Symmetric Algorithm Characteristics . . . . . . . . 102 Module 2-4: Asymmetric Cryptosystems . . . . . . . . . . . . . . . . . . . . . 103 RSA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 103 Diffie-Hellman . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 105 PGP/GPG . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106 ECC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106 ElGamal . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 106 Module 2-5: Hashing Algorithms . . . . . . . . . . . . . . . . . . . . . . . . . . 107 Hashing Process . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 107 MD5 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 109 SHA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 109 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Contents xi Chapter 3 00-FM.indd 11 RIPEMD . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . HMAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 2-6: Digital Signatures and Certificates . . . . . . . . . . . . . . . Digital Signatures . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Digital Certificates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 2-7: Public Key Infrastructure . . . . . . . . . . . . . . . . . . . . . . Keys, Algorithms, and Standards . . . . . . . . . . . . . . . . . . . . . . PKI Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Digital Certificates and PKI Structure . . . . . . . . . . . . . . . . . . Key Safety . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Trust Models . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 2-8: Cryptographic Attacks . . . . . . . . . . . . . . . . . . . . . . . . Attack Strategies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Attackable Data . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Attack Scenarios . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Defending Password Storage . . . . . . . . . . . . . . . . . . . . . . . . . Other Attack Options . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 2-9: Other Cryptosystems . . . . . . . . . . . . . . . . . . . . . . . . . Homomorphic Encryption . . . . . . . . . . . . . . . . . . . . . . . . . . Blockchain . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Quantum Cryptography . . . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 110 110 110 111 113 120 121 123 124 131 132 133 133 135 137 145 146 148 149 149 150 150 152 Identity and Account Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 3-1: Understanding Authentication . . . . . . . . . . . . . . . . . . Identification and AAA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Identification and Authentication . . . . . . . . . . . . . . . . . . . . . Authorization . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Accounting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Trust . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 3-2: Authentication Methods and Access Controls . . . . . . . Authentication Methods . . . . . . . . . . . . . . . . . . . . . . . . . . . . Biometrics . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Authorization and Access Control Schemes/Models . . . . . . . Module 3-3: Account Management . . . . . . . . . . . . . . . . . . . . . . . . . User Accounts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Account Policies . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Account Administration . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 3-4: Point-to-Point Authentication . . . . . . . . . . . . . . . . . . PAP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . CHAP/MS-CHAP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Remote Access Connection and Authentication Services . . . . 153 155 155 156 162 164 165 167 168 175 179 182 183 190 199 201 202 202 203 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xii 00-FM.indd 12 Module 3-5: Network Authentication . . . . . . . . . . . . . . . . . . . . . . . The Challenge of LAN Access Management . . . . . . . . . . . . . Microsoft Networking . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . LDAP and Secure LDAP . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 3-6: Identity Management Systems . . . . . . . . . . . . . . . . . . Trust . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Shared Authentication Schemes . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 205 205 207 210 211 212 213 214 216 Chapter 4 Tools of the Trade . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 4-1: Operating System Utilities . . . . . . . . . . . . . . . . . . . . . Network Reconnaissance and Discovery . . . . . . . . . . . . . . . . File Manipulation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Shell and Script Environments . . . . . . . . . . . . . . . . . . . . . . . Module 4-2: Network Scanners . . . . . . . . . . . . . . . . . . . . . . . . . . . . Scanning Methods . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Scanning Targets . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Scanner Types . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 4-3: Protocol Analyzers . . . . . . . . . . . . . . . . . . . . . . . . . . . Why Protocol Analyze? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Wireshark . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . tcpdump . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 4-4: Monitoring Networks . . . . . . . . . . . . . . . . . . . . . . . . . Exploring Log Files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Centralizing Log Files . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Security Information and Event Management . . . . . . . . . . . . Log File Management . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 217 217 218 231 235 237 239 239 239 246 247 248 251 252 253 257 259 262 263 264 Chapter 5 Securing Individual Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 5-1: Types of System Attacks . . . . . . . . . . . . . . . . . . . . . . . Attacking Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Driver Manipulation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Malicious Code or Script Execution . . . . . . . . . . . . . . . . . . . Module 5-2: Malware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Virus . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Cryptomalware/Ransomware . . . . . . . . . . . . . . . . . . . . . . . . . Worm . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Trojan Horse . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Potentially Unwanted Programs . . . . . . . . . . . . . . . . . . . . . . . Bots/Botnets . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Logic Bomb . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 267 269 270 276 277 279 280 281 282 283 283 285 286 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Contents xiii Chapter 6 00-FM.indd 13 Keylogger . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . RAT . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Rootkit . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Backdoor . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 5-3: Cybersecurity Resilience . . . . . . . . . . . . . . . . . . . . . . . Non-persistence . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Redundancy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Diversity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 5-4: Securing Hardware . . . . . . . . . . . . . . . . . . . . . . . . . . . Physical Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Securing the Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Securing Boot Integrity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 5-5: Securing Endpoints . . . . . . . . . . . . . . . . . . . . . . . . . . Hardening Operating Systems . . . . . . . . . . . . . . . . . . . . . . . . Anti-malware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Data Execution Prevention . . . . . . . . . . . . . . . . . . . . . . . . . . File Integrity Monitors . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Data Loss Prevention . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 5-6: System Recycling . . . . . . . . . . . . . . . . . . . . . . . . . . . . Clear . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Purge . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Destroy . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 286 287 288 288 288 289 295 300 300 301 303 305 310 310 317 319 319 320 321 321 323 324 324 326 The Basic LAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 6-1: Layer 2 LAN Attacks . . . . . . . . . . . . . . . . . . . . . . . . . ARP Poisoning . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Man-in-the-Middle Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . MAC Flooding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . MAC Cloning . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 6-2: Organizing LANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . Configuration Management . . . . . . . . . . . . . . . . . . . . . . . . . Network Segmentation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Load Balancing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 6-3: Implementing Secure Network Designs . . . . . . . . . . . Securing the LAN . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Internet Connection Firewalls . . . . . . . . . . . . . . . . . . . . . . . . Securing Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 6-4: Virtual Private Networks . . . . . . . . . . . . . . . . . . . . . . . How VPNs Work . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Early VPNs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . IPsec VPNs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . TLS VPNs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 327 327 328 330 332 333 334 335 338 342 343 343 347 354 357 358 360 360 361 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xiv 00-FM.indd 14 Module 6-5: Network-Based Intrusion Detection/Prevention . . . . . Detection vs. Prevention . . . . . . . . . . . . . . . . . . . . . . . . . . . . Detecting Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Configuring Network-Based IDS/IPS . . . . . . . . . . . . . . . . . . Monitoring NIDS/NIPS . . . . . . . . . . . . . . . . . . . . . . . . . . . . Endpoint Detection and Response . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 362 362 362 364 366 367 367 369 Chapter 7 Securing Wireless LANs . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 7-1: Networking with 802.11 . . . . . . . . . . . . . . . . . . . . . . Wireless Cryptographic Protocols . . . . . . . . . . . . . . . . . . . . . Wireless Authentication Protocols . . . . . . . . . . . . . . . . . . . . . Module 7-2: Attacking 802.11 . . . . . . . . . . . . . . . . . . . . . . . . . . . . Wireless Survey/Stumbler . . . . . . . . . . . . . . . . . . . . . . . . . . . Packet Capture . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Attack Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Rogue Access Point . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Jamming . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Packet Sniffing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Deauthentication Attack . . . . . . . . . . . . . . . . . . . . . . . . . . . . Near-Field Communication . . . . . . . . . . . . . . . . . . . . . . . . . . Replay Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . WEP/WPA Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . WPS Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Wireless Peripherals . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 7-3: Securing 802.11 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Installation Considerations . . . . . . . . . . . . . . . . . . . . . . . . . . Wireless Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Security Posture Assessment . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 371 371 372 377 380 380 381 381 382 383 385 385 386 387 387 388 388 389 389 393 397 398 400 Chapter 8 Securing Public Servers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 8-1: Attacking and Defending Public Servers . . . . . . . . . . . Distributed Denial-of-Service . . . . . . . . . . . . . . . . . . . . . . . . Route Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Quality of Service . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Monitoring Services . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 8-2: Virtualization Security . . . . . . . . . . . . . . . . . . . . . . . . Virtualization Architecture . . . . . . . . . . . . . . . . . . . . . . . . . . Containers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Virtualization Risks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Using Virtualization for Security . . . . . . . . . . . . . . . . . . . . . . 401 401 402 404 404 404 406 407 410 411 412 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Contents xv Module 8-3: Cloud Deployment . . . . . . . . . . . . . . . . . . . . . . . . . . . Let’s Talk Amazon . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Cloud Deployment Models . . . . . . . . . . . . . . . . . . . . . . . . . . Cloud Architecture Models . . . . . . . . . . . . . . . . . . . . . . . . . . Cloud Growing Pains . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 8-4: Securing the Cloud . . . . . . . . . . . . . . . . . . . . . . . . . . . Cloud Security Controls . . . . . . . . . . . . . . . . . . . . . . . . . . . . Unique Cloud Security Solutions . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 414 416 419 422 424 426 426 432 432 434 Securing Dedicated Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 9-1: Embedded, Specialized, and Mobile Systems . . . . . . . Embedded Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . SCADA/ICS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Internet of Things . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Specialized Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Mobile Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 9-2: Connecting to Dedicated Systems . . . . . . . . . . . . . . . Common Communication Technologies . . . . . . . . . . . . . . . . IoT-Specific Communication Technologies . . . . . . . . . . . . . . Module 9-3: Security Constraints for Dedicated Systems . . . . . . . . Hardware . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Programming . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Connectivity . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 9-4: Implementing Secure Mobile Solutions . . . . . . . . . . . Mobile Device Management . . . . . . . . . . . . . . . . . . . . . . . . . Deployment Models . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Inventory Control and Asset Tracking . . . . . . . . . . . . . . . . . . Application Management and Security . . . . . . . . . . . . . . . . . Encryption and Authentication . . . . . . . . . . . . . . . . . . . . . . . Enforcement and Monitoring for Device Security . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 435 436 436 439 440 441 447 448 448 451 453 453 453 455 456 458 459 462 466 467 468 475 477 Chapter 10 Physical Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 10-1: Physical Security Controls . . . . . . . . . . . . . . . . . . . . Passive Defensive Systems and Perimeter Controls . . . . . . . . . Active Alert Systems . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Manned Defensive Systems . . . . . . . . . . . . . . . . . . . . . . . . . . Module 10-2: Environmental Controls . . . . . . . . . . . . . . . . . . . . . . EMI and RFI Shielding . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Fire Suppression . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . HVAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 479 479 480 488 489 494 494 495 498 Chapter 9 00-FM.indd 15 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xvi 00-FM.indd 16 Temperature and Humidity Controls . . . . . . . . . . . . . . . . . . Hot and Cold Aisles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Environmental Monitoring . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 498 499 500 500 502 Chapter 11 Secure Protocols and Applications . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 11-1: Secure Internet Protocols . . . . . . . . . . . . . . . . . . . . . DNS Security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . SNMP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . SSH . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . FTP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . SRTP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 11-2: Secure Web and E-mail . . . . . . . . . . . . . . . . . . . . . . . HTTP . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . HTTPS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . E-mail . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 11-3: Web Application Attacks . . . . . . . . . . . . . . . . . . . . . Injection Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Hijacking and Related Attacks . . . . . . . . . . . . . . . . . . . . . . . . Other Web Application Attacks . . . . . . . . . . . . . . . . . . . . . . . Module 11-4: Application Security . . . . . . . . . . . . . . . . . . . . . . . . . Development . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Code Quality and Testing . . . . . . . . . . . . . . . . . . . . . . . . . . . Staging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Production . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Quality Assurance . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Getting Organized . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 11-5: Certificates in Security . . . . . . . . . . . . . . . . . . . . . . . Certificate Concepts and Components . . . . . . . . . . . . . . . . . PKI Concepts . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Online vs. Offline CA . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . PKI TLS Scenario . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Types of Certificates . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Certificate Formats . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Key Escrow . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 503 504 505 506 507 508 509 509 509 510 513 517 517 520 523 526 527 535 537 537 538 538 542 542 542 545 547 548 552 554 554 556 Chapter12 557 557 558 559 562 Testing Infrastructure . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 12-1: Vulnerability Impact . . . . . . . . . . . . . . . . . . . . . . . . . Device/Hardware Vulnerabilities . . . . . . . . . . . . . . . . . . . . . . Configuration Vulnerabilities . . . . . . . . . . . . . . . . . . . . . . . . . Management/Design Vulnerabilities . . . . . . . . . . . . . . . . . . . 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Contents xvii 00-FM.indd 17 Module 12-2: Social Engineering . . . . . . . . . . . . . . . . . . . . . . . . . . Social Engineering Goals . . . . . . . . . . . . . . . . . . . . . . . . . . . . Principles . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Types of Attacks . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 12-3: Artificial Intelligence . . . . . . . . . . . . . . . . . . . . . . . . . Understanding Artificial Intelligence . . . . . . . . . . . . . . . . . . . Machine Learning Essentials . . . . . . . . . . . . . . . . . . . . . . . . . OSINT . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Adversarial Artificial Intelligence . . . . . . . . . . . . . . . . . . . . . . Module 12-4: Security Assessment . . . . . . . . . . . . . . . . . . . . . . . . . Threat Hunting . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Vulnerability Scans . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Penetration Testing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 12-5: Assessment Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . Protocol Analyzer . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Network Scanner . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Vulnerability Scanner . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Configuration Compliance Scanner . . . . . . . . . . . . . . . . . . . . Penetration Testing with Metasploit . . . . . . . . . . . . . . . . . . . . Specific Tools Mentioned by CompTIA . . . . . . . . . . . . . . . . Interpreting Security Assessment Tool Results . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 563 564 567 570 577 577 577 578 579 579 580 581 584 590 591 591 593 594 594 595 596 597 599 Chapter 13 Dealing with Incidents . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 13-1: Incident Response . . . . . . . . . . . . . . . . . . . . . . . . . . . Incident Response Concepts . . . . . . . . . . . . . . . . . . . . . . . . . Incident Response Procedures . . . . . . . . . . . . . . . . . . . . . . . . Scenarios: Mitigation During and After an Incident . . . . . . . Module 13-2: Digital Forensics . . . . . . . . . . . . . . . . . . . . . . . . . . . . Digital Forensics Concepts . . . . . . . . . . . . . . . . . . . . . . . . . . Data Volatility . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Critical Forensics Practices . . . . . . . . . . . . . . . . . . . . . . . . . . . Data Acquisition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Analyzing Evidence . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Module 13-3: Continuity of Operations and Disaster Recovery . . . Risk Management Best Practices . . . . . . . . . . . . . . . . . . . . . . Contingency Planning and Resilience . . . . . . . . . . . . . . . . . . Functional Recovery Plans . . . . . . . . . . . . . . . . . . . . . . . . . . . Backup and Restore Plans and Policies . . . . . . . . . . . . . . . . . . Questions . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Answers . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 601 601 602 604 617 620 620 623 627 632 635 637 637 641 643 645 657 659 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xviii Appendix A Exam Objective Map . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 661 Exam SY0-601 . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 661 Appendix B About the Online Content . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . System Requirements . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Your Total Seminars Training Hub Account . . . . . . . . . . . . . . . . . . Privacy Notice . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Single User License Terms and Conditions . . . . . . . . . . . . . . . . . . . TotalTester Online . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Other Book Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Video Training from Mike Meyers . . . . . . . . . . . . . . . . . . . . . TotalSim Simulations . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Mike’s Cool Tools . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . Technical Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 699 699 699 699 699 701 701 701 702 702 702 Glossary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 703 Index. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 769 00-FM.indd 18 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM ACKNOWLEDGMENTS In general, we’d like to thank our amazing teams at McGraw Hill and KnowledgeWorks Global Ltd. for such excellent support and brilliant work editing, laying out, and publishing this edition. Special shout out to our co-workers at Total Seminars—Michael Smyer, Dave Rush, and Travis Everett—for listening to us rant and providing excellent feedback. We’d like to acknowledge the many people who contributed their talents to make this book possible: To Tim Green, our acquisitions editor at McGraw Hill: Thank you for the steady encouragement during this crazy year. You’re the best! To Matt Walker, technical editor: Excellent working with you! Thanks for laughing at our geeky jokes and sharing great stories. To Bill McManus, copy editor: What an absolute delight to do this project with you! Your efforts made this a much better book. To Emily Walters, acquisitions coordinator at McGraw Hill: Thanks for the Friday meetings and slightly menacing cat-on-lap petting. Way to keep us on track! To Neelu Sahu, project manager at KnowledgeWorks Global Ltd.: Enjoyed working with you, Neelu. Hope the somewhat chaotic pacing wasn’t too stressful! To Lisa McCoy, proofreader: Fabulous job, thanks! To Ted Laux, indexer extraordinaire: Well done! To KnowledgeWorks Global Ltd. compositors: The layout was excellent, thanks! To Janet Walden, editorial supervisor at McGraw Hill: Great to work with you on this project! Next time we’ll make a few extra changes in page proofs just for you! To Tom Somers, production supervisor at McGraw Hill: Thanks for waving that magic wand of yours and making so much happen as smoothly as possible. xix 00-FM.indd 19 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio xx This page intentionally left blank 00-FM.indd 20 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM INTRODUCTION Most societies teem with a host of networked devices, from servers to smartphones, that provide the backbone for much of modern life. People and companies use these devices to produce and sell products and services, communicate around the globe, educate at every level, and manage the mechanisms of governments everywhere. Networked devices and the complex networks that interconnect them offer advances for humanity on par with, or perhaps beyond, the Agricultural and Industrial Revolutions. That’s the good news. The bad news is the fact that reliance on these devices creates a security risk to the resources placed on them. Networks can lose critical data and connections, both of which equate to loss of energy, confidence, time, and money. To paraphrase a few words from the American statesman, James Madison, if humans were angels, there’d be no need for security professionals. But humans are at best negligent and at worst petty, vindictive, and astoundingly creative in pursuit of your money and secrets. Networked devices and the networks that interconnect them need security professionals to stand guard. The need for security professionals in information technology (IT) far outstrips demand, and we assume that’s why you picked up this book. You see the trend and want to take the first step to becoming an IT security professional by attaining the acknowledged first security certification to get CompTIA Security+. This introduction starts with an overview of the goals of security, to put a framework around everything you’re going to learn. Second, we’ll discuss the CompTIA Security+ certification and look at exam details. Finally, this introduction details the overall structure of the book, providing a roadmap for studying for the exam. Goals of Security Traditional computer security theory balances among three critical elements: functionality, security, and the resources available to ensure both. From a functionality standpoint, systems must function as people need them to function to process the data needed. Users and other systems need to interface with systems and data seamlessly to get work done. Don’t confuse functionality with free rein. Allowing users to do whatever they wish with systems and data may result in loss, theft, or destruction of systems and data. Therefore, functionality must balance with security. From the security standpoint, however, increasing the levels of protection for systems and data usually reduces functionality. Introducing security mechanisms and procedures into the mix doesn’t always allow users to see or interact with data and systems the way they would like. This usually means a reduction in functionality to some degree. xxi 00-FM.indd 21 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xxii Figure 1 Balancing functionality, security, and resources More Functionality Resources Security Less To add another wrinkle, the resources expended toward functionality and security, and the balance between them, are finite. No one has all the money or resources they need or as much functionality or security as they want. Keep in mind, therefore, that the relationship between functionality and security is inversely proportional; that is to say, the more security in place, the less functionality, and vice versa. Also, the fewer resources a person or organization has, the less of either functionality or security they can afford. Figure 1 illustrates this careful balancing act among the three elements of functionality, security, and resources. Security theory follows three goals, widely considered the foundations of the IT security trade: confidentiality, integrity, and availability. Security professionals work to achieve these goals in every security program and technology. These three goals inform all the data and the systems that process it. The three goals of security are called the CIA triad. Figure 2 illustrates the three goals of confidentiality, integrity, and availability. NOTE The CIA triad is put into practice through various security mechanisms and controls. Every security technique, practice, and mechanism put into place to protect systems and data relates in some fashion to ensuring confidentiality, integrity, and availability. Confidentiality Confidentiality tries to keep unauthorized people from accessing, seeing, reading, or interacting with systems and data. Confidentiality is a characteristic met by keeping data secret from people who aren’t allowed to have it or interact with it in any way, while making sure that only those people who do have the right to access it can do so. Systems achieve confidentiality through various means, including the use of permissions to data, encryption, and so on. 00-FM.indd 22 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Introduction xxiii Figure 2 The CIA triad Confidentiality Systems and Data Integrity Availability Integrity Meeting the goal of integrity requires maintaining data and systems in a pristine, unaltered state when they are stored, transmitted, processed, and received, unless the alteration is intended due to normal processing. In other words, there should be no unauthorized modification, alteration, creation, or deletion of data. Any changes to data must be done only as part of authorized transformations in normal use and processing. Integrity can be maintained by the use of a variety of checks and other mechanisms, including data checksums and comparison with known or computed data values. Availability Maintaining availability means ensuring that systems and data are available for authorized users to perform authorized tasks, whenever they need them. Availability bridges security and functionality, because it ensures that users have a secure, functional system at their immediate disposal. An extremely secure system that’s not functional is not available in practice. Availability is ensured in various ways, including system redundancy, data backups, business continuity, and other means. During the course of your study, keep in mind the overall goals in IT security. First, balance three critical elements: functionality, security, and the resources available to ensure both. Second, focus on the goals of the CIA triad—confidentiality, integrity, and availability—when implementing, reviewing, managing, or troubleshooting network and system security. The book returns to these themes many times, tying new pieces of knowledge to this framework. 00-FM.indd 23 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xxiv CompTIA Security+ Certification The CompTIA Security+ certification has earned the reputation as the first step for anyone pursuing a career in the highly complex, highly convoluted, and still very much evolving world of IT security. Let’s start with a description of CompTIA, then look at the specifics of the certification. CompTIA The Computing Technology Industry Association (CompTIA) is a nonprofit, industrywide organization of just about everyone in the IT industry. The different aspects of CompTIA’s mission include certification, education, and public policy. As of this writing, CompTIA offers 13 vendor-neutral certifications covering a wide range of information technology areas. Examples of some of these areas and certifications include CompTIA Linux+ (focusing on the Linux operating system), CompTIA A+ (which focuses on computer technology support fundamentals), CompTIA Network+ (covering different network technologies), and, of course, CompTIA Security+. CompTIA certifications are considered the de facto standard in the industry in some areas. Because they are vendor neutral, almost all CompTIA certifications cover basic knowledge of fundamental concepts of a particular aspect of IT. CompTIA works hard to develop exams that accurately validate knowledge that professionals must have in that area. This enables employers and others to be confident that the individual’s knowledge meets a minimum level of skill, standardized across the industry. The CompTIA Security+ Exam Let’s state up front that CompTIA does not have any requirements for individuals who want to take the CompTIA Security+ exam. There are no prerequisites for certification or definitive requirements for years of experience. CompTIA does have several recommendations, on the other hand, including knowledge that might be validated by other CompTIA certifications such as the CompTIA Network+ certification. In other words, the level of networking knowledge you are expected to have before you take the CompTIA Security+ exam is the level that you would have after successfully completing the CompTIA Network+ certification. Here are CompTIA’s recommendations: •• Network+ certification •• Two years of experience in IT systems administration, with a focus on security You should have experience in several areas, such as networking knowledge, basic information security concepts, hardware, software (both operating systems and applications), cryptography, physical security, and so on. The next few sections cover specific exam objectives that you need to know. 00-FM.indd 24 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Introduction xxv The following table shows the five domains in the CompTIA Security+ Certification Exam Objectives document for exam SY0-601. Each of these domains has very detailed exam objectives. Domain Name Percent of Exam 1.0 Threats, Attacks, and Vulnerabilities 24 2.0 Architecture and Design 21 3.0 Implementation 25 4.0 Operations and Incident Response 16 5.0 Governance, Risk, and Compliance 14 Threats, Attacks, and Vulnerabilities Domain 1.0 is all about the attacks, from malware to application attacks. It’s critical you know your keyloggers from your RATs and your buffer overflows from your cross-site scripting. In addition, you should recognize the threat actors, from script kiddies to evil governments to incompetent users. Along with the threats and attacks, you should understand different types of vulnerabilities that enable these attacks to thrive and the two main tools you use to minimize those vulnerabilities, security assessments, and penetration testing. Architecture and Design Domain 2.0 explores a lot of topics under its benign-sounding title. You’re expected to explain important security concepts, such as data protection, hashing, and site resiliency. The domain covers cloud models, such as infrastructure as a service (IaaS); you’ll need to summarize containers, infrastructure as code, and virtualization. In addition, this domain covers the design of secure applications and security for embedded systems. Domain 2.0 requires you to know how to use security devices, protocols, and tools. This domain covers the frameworks that enable secure IT, the design concepts such as defensein-depth, and benchmarks used to measure security. This domain covers technologies to defend networks, such as VLANs, screened subnets, and wireless designs. In addition, this domain covers the design of secure applications and security for embedded systems. Domain 2.0 also covers physical security controls, such as fencing and fire prevention. Finally, domain 2.0 expects knowledge of cryptographic concepts. You’ll get questions on symmetric versus asymmetric cryptography, for example. The objectives explore public key encryption, keys, salting, hashing, and more. Implementation The key with domain 3.0 is in the name, “Implementation.” Concepts discussed in other domains get scenario-level in this domain. Domain 3.0 goes into great detail about authentication, authorization, and accounting. It expects you to know and implement authentication and the many identity and access services such as LDAP and Kerberos. 00-FM.indd 25 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Mike Meyers’ CompTIA Security+ Certification Guide xxvi The domain addresses authorization via user groups and accounts and the tools and methods used to control them. You’ll need to know how to implement secure wireless and mobile solutions, plus apply cybersecurity solutions to cloud computing. Finally, the domain expects you to understand how to implement public key infrastructure. Operations and Incident Response Domain 4.0 explores organizational security, such as incident response policies and procedures. You’ll need to know mitigation techniques and controls, plus practical forensic practices, such as how to acquire and handle evidence. Governance, Risk, and Compliance Domain 5.0 defines critical concepts in risk management, such as events, exposures, incidents, and vulnerability. You’re expected to know risk-related tools, such as business impact analysis, assessments, incident response, and disaster recovery/business continuity. You’ll need to understand the regulations, standards, and frameworks that impact operational security and explain policies that organizations use to implement security. Finally, the domain expects you to know how privacy and sensitive data use impacts security. Getting Certified This book covers everything you’ll need to know for CompTIA’s Security+ certification exam. The book is written in a modular fashion, with short, concise modules within each chapter devoted to specific topics and areas you’ll need to master for the exam. Each module covers specific objectives and details for the exam, as defined by CompTIA. We’ve arranged these objectives in a manner that makes fairly logical sense from a learning perspective, and we think you’ll find that arrangement will help you in learning the material. NOTE Throughout the book, you’ll see helpful Notes and Exam Tips. These elements offer insight on how the concepts you’ll study apply in the real world. Often, they may give you a bit more information on a topic than what is covered in the text or expected on the exam. And they may also be helpful in pointing out an area you need to focus on or important topics that you may see on the test. End of Chapter Questions At the end of each chapter you’ll find questions that will test your knowledge and understanding of the concepts discussed in the modules. The questions also include an answer key, with explanations of the correct answers. 00-FM.indd 26 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM Introduction xxvii Using the Exam Objective Map The Exam Objective map included in Appendix A has been constructed to help you cross-reference the official exam objectives from CompTIA with the relevant coverage in the book. References have been provided for the exam objectives exactly as CompTIA has presented them—the module that covers that objective, the chapter, and a page reference are included. Online Resources The online resources that accompany this book feature the TotalTester exam software that enables you to generate a complete practice exam or quizzes by chapter or by exam domain. See Appendix B for more information. Study Well and Live Better We enjoyed writing this book and hope you will enjoy reading it as well. Good luck in your studies and good luck on the CompTIA Security+ exam. If you have comments, questions, or suggestions, tag us: Mike: desweds@protonmail.com Scott: jernigan.scott@gmail.com 00-FM.indd 27 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / FM / Blind Folio xxviii This page intentionally left blank 00-FM.indd 28 20/03/21 7:04 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 1 CHAPTER Risk Management “It seems to me that if there were any logic to our language, trust would be a four-letter word.” —Joel Goodson, Risky Business IT security professionals walk a tight line between keeping systems safe from inside and outside threats and making resources available to people who need them. Perfectly secure systems would allow no access, right? If attackers can’t access the systems, they can’t break or steal anything. But such “perfect” security clearly blocks legitimate users from using resources to produce anything of value. Conversely, a wide-open system provides great access for creativity and production, but also provides access to malicious people. Security professionals provide a space in between, with enough security to stop attackers, yet enough access to enable good people to create and produce. With risk management, security folks identify and categorize risks and then systematically put controls in place to manage those risks and thus minimize their impact on the organization. As a science, risk management uses statistics, facts, scans, and numbers to align a vision, a design for the organization. As an art, security professionals craft a plan for risk management that people will buy into and actually follow. This chapter tours IT risk management in eight modules: • • • • • • • • Defining Risk Risk Management Concepts Security Controls Risk Assessment Business Impact Analysis Data Security and Data Protection Personnel Risk and Policies Third-Party Risk and Policies 1 01-ch01.indd 1 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 2 Module 1-1: Defining Risk This module covers the following CompTIA Security+ objectives: • 1.2 Given a scenario, analyze potential indicators to determine the type of attack • 1.5 Explain different threat actors, vectors, and intelligence sources In IT security, risk implies a lot more than the term means in standard English. Let’s start with a jargon-filled definition, then examine each term in the definition. We’ll review the definition with some examples at the end of the module. Risk is the likelihood of a threat actor taking advantage of a vulnerability by using a threat against an IT system asset. This definition of risk includes five jargon terms that require further explanation: • • • • • Asset Likelihood Threat actor Vulnerability Threat Defining each jargon word or phrase relies at least a little on understanding one or more of the other jargon phrases. We’ll cover these next, and then explore two related topics, vectors and threat intelligence, to round out the concept of risk. Let’s do this. Asset An asset is a part of an IT infrastructure that has value. You can measure value either tangibly or intangibly. A gateway router to the Internet is an example of an asset with tangible value. If it fails, you can easily calculate the cost to replace the router. What if that same router is the gateway to an in-house Web server? If that Web server is no longer accessible to your customers, they’re not going to be happy and might go somewhere else due to lack of good faith or goodwill. Good faith doesn’t have a measurable value; it’s an intangible asset. Here are a few more examples of assets: • • • • • 01-ch01.indd 2 Servers The computers that offer shared resources Workstations The computers that users need to do their job Applications Task-specific programs an organization needs to operate Data The stored, proprietary information an organization uses Personnel The people who work in an organization 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 3 • Wireless access Access to the network that doesn’t require plugging into an Ethernet port • Internet services The public- or private-facing resources an organization provides to customers, vendors, or personnel via the Web or other Internet applications We will cover assets in much greater detail later in this chapter. Likelihood Likelihood means the probability—over a defined period of time—of someone or something damaging assets. Likelihood is generally discussed in a comparative nature. Here are a couple of examples: • The company expects many attacks on its Web server daily, but few on its internal servers. The potential for a successful attack on the Web server is much more likely than on internal servers, and thus the controls—the things put in place to protect the systems—would vary a lot. • Hard drives will likely fail after three years, with the probability of failure rising over time. The drive could fail right out of the box, but the likelihood of failure of a drive under three years old is much lower than a drive of three or more years old. NOTE You will also hear the term probability as a synonym for likelihood. Threat Actor A threat actor is anyone or anything that has the motive and resources to attack another enterprise’s IT infrastructure. Threat actors manifest in many forms. Many folks think of a threat actor as a malicious person, such as a classic hacker bent on accessing corporate secrets. But a threat actor can take different guises as well, such as programs automated to attack at a specific date or time. A threat actor could be a respected member of an organization who has just enough access to the IT infrastructure but lacks the knowledge of what not to do. The word actor here simply means someone or something that can initiate a negative event. The CompTIA Security+ exam covers nine specific types of threat actor: • • • • • • 01-ch01.indd 3 Hackers Hacktivists Script kiddies Insiders Competitors Shadow IT 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 4 • Criminal syndicates • State actors • Advanced persistent threat Hackers—and more specifically security hackers—have the technical skills to gain access to computer systems. White hat hackers use their skills for good, checking for vulnerabilities and working with the full consent of the target. The malicious black hat hackers, in contrast, do not have the consent of the target. Gray hat hackers fall somewhere in the middle. They’re rarely malicious, but usually do not have the target’s consent. EXAM TIP The CompTIA Security+ objectives use bland and nonstandard descriptive terms for hacker types. Be prepared for either term to describe/ label a hacker. —White hat = Authorized —Black hat = Unauthorized —Gray hat = Semi-authorized A hacktivist is a hacker and an activist. These threat actors have some form of agenda, often political or fueled by a sense of injustice. Hacktivism is often associated with sophisticated yet loosely associated organizations, such as Anonymous. Free Willy! Save the whales! Script kiddies are poorly skilled threat actors who take advantage of relatively easyto-use open-source attacking tools. They get the derogatory moniker because they don’t have skills that accomplished hackers possess. Their lack of sophistication makes them notoriously easy to stop, most of the time. Insiders (or insider threats) are people within an organization. As part of the targeted organization, these threat actors have substantial physical access and usually have user accounts that give them access to assets. In fact, the absolute best way to attack an organization is to be hired by them. You get hired; they hand you the keys to the kingdom; you’re in. Insiders are often motivated by revenge or greed, but that’s not universal. Some folks just do stupid things that cause all sorts of havoc. 01-ch01.indd 4 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 5 Shadow IT describes information technology systems installed without the knowledge or consent of the main IT department. Almost never based on malicious intent, shadow IT springs up when users need to work around limitations imposed by IT departments for purposes of security, limitations that hamper their jobs. Isn’t it interesting that one attribute of the two previous threat actors is that they are inside the organization? The rest of the threat actors are external to the organization. EXAM TIP Take the time to recognize the attributes of threat actors: internal/external, intent/motivation, resources/funding, level of sophistication/capability. Competitors are outside organizations that try to gain access to the same customers as the targeted company. Competitors, by definition in the same business, know precisely the type of secure information they want. Organizations practice competitive intelligence gathering to get information about competitors, their customers, their business practices, and so on. The information gathered can help shape business practices. Criminal syndicates use extra-legal methods to gain access to resources. Also known as organized crime, criminal syndicates are a huge problem today. These groups are sophisticated, are well funded, and cause tremendous damage to vulnerable systems worldwide to make money. State actors—or nation states—refers to government-directed attacks, such as the United States sending spies into Russia. Whereas criminal syndicates commonly use threats specifically to make money, state actors take advantage of vulnerabilities to acquire intelligence. Nation states have the resources—people and money—to collect open-source intelligence (OSINT) successfully—information from media (newspapers, television), public government reports, professional and academic publications, and so forth. State actors are easily the best funded and most sophisticated of all threat actors. State actors often use advanced persistent threats (APTs), where a threat actor gets long-term control of a compromised system, continually looking for new data to steal. NOTE Many state actors use criminal syndicates to conduct cyberattacks against other nation states. Vulnerability and Threat The terms vulnerability and threat go hand-in-hand, so it makes sense to talk about both at the same time. A vulnerability is a weakness inherent in an asset that leaves it open to a threat. A threat is an action a threat actor can use against a vulnerability to create a negative effect. Vulnerabilities and their associated threats exist at every level of an organization. Not changing the default password on a router is a vulnerability; someone taking control of your router by using the default password is the threat. Giving a user full control to a 01-ch01.indd 5 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 6 shared folder (when that user does not need nor should have full control) is a vulnerability. That same user having the capability to delete every file in that folder is a threat. Hmm . . . I wonder what would happen if I pressed [Delete]? Oh no! Threats do not have to originate only from people or organizations. Forces of nature like earthquakes and hurricanes (a big deal here in Houston, Texas) can also be threats. As you might imagine, dealing with threats by minimizing vulnerabilities is a core component of risk management. This chapter will develop this concept in detail. NOTE You will see two other terms associated with the jargon phrases covered in this section, attack and incident. An attack is when a threat actor actively attempts to take advantage of a vulnerability. When the target recognizes an attack, it is called an incident. Both attacks and incidents go beyond the concept of risk and are covered in Chapter 13. Circling Back to the Risk Definition Now that we have explored each jargon term in some detail, let’s look at the definition of risk again and follow it with an example. Risk is the likelihood of a threat actor taking advantage of a vulnerability by using a threat against an IT system asset. Here’s an example of a risk: There’s a 15 percent chance in the next month that Sally the hacktivist will guess correctly John’s password on the important company server to gain access to secret documents. The likelihood is 15 percent over the next month. The threat actor is Sally the hacktivist. John’s lame password is a vulnerability; the threat is that Sally will get that password and use it to access the server. The assets are both the server and the secret documents. Got it? Let’s move on. Vectors Threat actors use a variety of attack vectors—pathways to gain access to infrastructure— to carry out attacks. In the olden days, threat actors used floppy disks or optical media 01-ch01.indd 6 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 7 as vectors to install malware or tools. Today, the only commonly used removable media are USB thumb drives, the vector of choice for a threat actor who has physical access to a target system. Other attack vectors include the classic “hacker gets into your network through your router” (a.k.a. direct access), the ubiquitous vector of wireless networks (802.11, Bluetooth, cellular), and the relatively new cloud vector. Don’t limit yourself to thinking networking when you consider vectors. Almost any application that transfers information between systems might be a vector. Threat actors can use e-mail, social media, conferencing, and even shared document applications as vectors for an attack. Smartphones and other mobile devices and the Internet of Things (IoT) offer serious and growing attack vectors for modern organizations. Just about everyone has a smartphone with sophisticated recording—video and sound—devices built in, plus always-on connectivity to the cellular network and the Internet. Any rogue or buggy app can create a pathway into a network. IoT devices controllable from outside the network also provide a point of entry to the network. It’s a brave new world that attackers will try very hard to exploit. The infamous Stuxnet worm that disrupted the Iranian nuclear program back in 2010 used a supply-chain vector. Threat actors (almost certainly the United States and Israel) infected printers with this worm that were then purchased by the Iranian government. This is a brutal example of a supply-chain attack. Threat Intelligence Cybersecurity professionals in organizations maintain and update information about past, current, and potential threats to the organization. This collection of information, called threat intelligence, helps those security professionals prepare for—and hopefully prevent—attacks on the organization. Moreover, most security folks share information about vulnerabilities and associated threats with other professionals in the field. It’s like one big, highly paranoid family out there! Sources for threat intelligence come from many places. Dedicated threat intelligence sources—such as vulnerability databases available on the Internet—provide a wealth of information, of course. But so do what CompTIA calls research sources—things like academic journals and social media. Security professionals dive into all of these sources to build their threat intelligence. This section explores the types of sources available for threat intelligence gathering and provides examples. This is not an exhaustive list of specific sources—impossible and instantly outdated—but a guide to the types of sources. We’ll look at dedicated threat intelligence sources, then follow with research sources. Threat Intelligence Sources Dedicated threat intelligence sources enable security professionals to research potential threats to their organizations and share threats they discover with their peers. These sources reveal the past and current threats, explore potential threats by defining characteristics or signature types, and much more. 01-ch01.indd 7 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 8 This section explores nine dedicated threat intelligence sources: • • • • • • • • • OSINT Public/private information-sharing centers Dark Web Indicators of compromise Adversary tactics, techniques, and procedures Predictive analysis Threat maps File/code repositories Vulnerability databases OSINT We discussed open-source intelligence (OSINT) sources earlier in this module. This category includes information gathered from media (newspapers, television), public government reports, professional and academic publications, and so forth. Security professionals rely heavily on OSINT for the big picture or the framework for the picture that can then get more specific in terms of nonpublic information layers. Public/Private Information-Sharing Centers Motivated by the lack of coordinated information sharing between different federal organization after 9/11, the US government began a series of legislation establishing information-sharing centers, more commonly called Information Sharing and Analysis Centers (ISACs). Originally designed as governmentbased public entities just in the United States, most countries now have public ISACs as well as many private ISACs. ISACs communicate via Automated Indicator Sharing (AIS) tools to update each other’s databases automatically. The US Department of Homeland Security (DHS) sponsors several specifications for facilitating cybersecurity information sharing. Trusted Automated eXchange of Intelligence Information (TAXII) enables information sharing through services and message exchanges. TAXII provides transport for threat information exchange. Structured Threat Information eXpression (STIX) enables communication among organizations by providing a common language to represent information. Cyber Observable eXpression (CybOX) provides standardized specifications for communicating about cybersecurity phenomenon and elements, from malware types to event logging. DHS has made these specifications available globally for free. EXAM TIP You might see a question on the CompTIA Security+ exam about DHS-sponsored specifications for cybersecurity information sharing. Only TAXII and STIX are in the objectives, though. CybOX is not mentioned. Dark Web The Dark Web refers to Internet sites that are inaccessible without using specific applications such as the Tor network. Dark Web sites run the gamut from illegal drug sales to terrorist groups to interesting puzzles, with just about everything 01-ch01.indd 8 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 9 Figure 1-1 A sketchy site on the Dark Web in between (Figure 1-1). Dark Web sites are “dark” because search engines, like Google, don’t index them. You can’t find these sites with a typical Internet search, in other words, but they function just like any other Web site. The Dark Web can provide a lot of important information, especially about criminal activity through sting operations conducted by law enforcement agents posing as Dark Web site visitors interested in engaging in illegal transactions. Plus, a lot of Dark Web sites offer highly entertaining, completely legal content. It’s the Wild West, so take care if (when) you venture in. Indicators of Compromise It’s almost impossible for a threat actor to attack a system and not leave behind clues of the actor’s presence. An IT security person must recognize the artifact of an intrusion, known as an indicator of compromise (IoC). IoCs take on many forms. A sudden increase in outgoing network traffic, malware signatures, strange changes in file permissions—all of these are examples of IoCs. IoCs feature as key evidence collected in forensic investigations. Recognizing IoCs enables cybersecurity professionals to monitor networks and provide threat monitoring tools as threat feeds—real-time data streams to recognize threats. Threat feeds work with internal networks as well as outside networks. Adversary Tactics, Techniques, and Procedures The term adversary tactics, techniques, and procedures (TTP) describes the actions of threat actors to gain access to 01-ch01.indd 9 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 10 your infrastructure. A tactic is the goal of the attacker, such as to gain initial access to a network or system. A technique is how the attacker implements that tactic, such as using a valid account or finding a weakness in your supply chain to gain initial access. A procedure is precisely how the attacker performs the technique; for example, watching a user’s keyboard as the user enters an account password. The MITRE ATT&CK framework incorporates TTP, breaking tactics into a dozen or so categories and providing common techniques associated with those tactics. Check it out here: https://attack.mitre.org. EXAM TIP CompTIA places threat feeds and TTP as types of research sources, but many researchers consider them part of dedicated threat intelligence sources. Either way, the key for the exam is that both sources enable you to enhance threat intelligence. Predictive Analysis Every IT security professional could use a crystal ball enabling him or her to know an incident is about to take place. That’s the world of predictive analysis: using software, often artificial intelligence, to look for trends to anticipate any upcoming problems. Predictive analysis isn’t perfect for every aspect of IT security, but for issues like hardware failure prediction and network loads, predictive analysis is a powerful tool. NOTE Check out the Predictive Analytics portal at CIO for the latest news on the subject: https://www.cio.com/category/predictive-analytics/. Threat Maps Threat maps are graphical representations of the geographical source and target of attacks (Figure 1-2). Threat maps are certainly pretty, but they aren’t real time and they lack any form of deep detail about the attacks. They work well for presentations, especially to show broader trends. File/Code Repositories A repository is a storage area for data files or code. Unlike archive data, repository data/code is stored in such a way that the data/code is sorted or indexed based on certain information pertinent to that data or code. Log files for an entire network over a certain number of years is one example of a file repository. Code repositories are a different matter. These are used by developers to produce and control code development. It’s rare to find anything written these days that doesn’t use a code repository like GitLab (Figure 1-3). EXAM TIP CompTIA lumps file and code repositories into a single term, file/code repositories. Vulnerability Databases The IT industry aggressively looks for vulnerabilities and their associated threats. Many governments and organizations host vulnerability databases, 01-ch01.indd 10 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 11 Figure 1-2 Cyber Threat Map from FireEye Figure 1-3 GitLab 01-ch01.indd 11 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 12 Figure 1-4 NIST National Vulnerability Database collections of all the known problem areas or weaknesses in deployed software. One of the most important vulnerability databases in the United States is the National Institute of Standards and Technology’s National Vulnerability Database (Figure 1-4). Another great source for vulnerabilities is the Common Vulnerabilities and Exposures (CVE) list provided by MITRE Corporation: https://cve.mitre.org. Also, check out the open-source, community-driven vulnerability database, VULDB: https://vuldb.com. There are a lot more vulnerability databases out there, but these three should get you started. NOTE CompTIA’s division between research sources and threat intelligence sources is somewhat arbitrary. In practice, these two areas overlap. 01-ch01.indd 12 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 13 Research Sources Research sources aren’t devoted exclusively to the idea of threat intelligence, but they’re always good places to look for problems in a more generic way. Whether you’re just checking a vendor forum or chatting at a conference, if security issues are out there, they’re always a hot topic. This section looks at seven common research sources: • • • • • • • Vendor Web sites Vulnerability feeds Conferences Academic journals Requests for comments Local industry groups Social media If you want to know anything about a product, go directly to the vendor Web site to do some good research (Figure 1-5). Who else knows more about a product (hopefully) than the vendor who makes or sells it? Find a support forum and dig in! If you want to stay on the bleeding edge of vulnerabilities and you want them basically delivered to you, vulnerability feeds make your research easy (easier) by delivering RSS feeds, tweets, social media posts, or other methods to let you see what’s out there. There are hundreds of these types of feeds. The NVD, mentioned earlier, has a great feed. Get out there and hit some conferences! There are plenty of great conferences at the regional, national, and international level. Every IT security person should make a trip to the famous Black Hat conference, held annually in Las Vegas and in other locations internationally (such as Black Hat Europe and Black Hat Asia). Reading academic journals is the ultimate egghead research path, but many vulnerabilities are first brought to public attention using journals. The only challenge to reading about vulnerabilities in academic journals is that the articles often only discuss a theoretical vulnerability without showing how to do it (in many cases, someone usually does create a practical attack after an article is published). Requests for comments (RFCs) started as the original ARPANET documents that literally defined the Internet. While this is still true, RFCs evolved to cover every aspect of TCP/IP communication and are issued by Internet Engineering Task Force (IETF), the Internet Research Task Force (IRTF), and the Internet Architecture Board (IAB). If you want the gritty details on any technology that is part of TCP/IP communications, RFCs are the place to go (Figure 1-6). All RFCs are public and can be accessed via www .rfc-editor.org. Many security issues are industry specific, so joining local industry groups is almost always the best way to connect with the folks who deal with similar issues in your industry. These are often the only reliable source for industry-specific or closed/proprietary information. Search in your area for a local Information Systems Security Association International (ISSA) chapter. They’re super good: https://issa.org. 01-ch01.indd 13 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 14 Figure 1-5 Advanced networking device manufacturer Juniper’s support forums Virtually every company or organization that provides hardware, software, services, or applications has some form of bug bounty program. These programs reward people who report vulnerabilities with money, swag, and acclaim (Figure 1-7). Before you get too excited and start hacking your favorite (fill in the blank), know that all of these programs have very specific scopes and parameters. Going beyond the scope could get you in serious legal trouble. Look before you leap! And get permission before you start. Social media, such as Twitter and Reddit, provide a wealth of threat intelligence sources. Numerous Twitter feeds are dedicated to cybersecurity. Check out @Dejan_Kosutic— for hourly updates. The r/threatintel subreddit, while not quite as hyperactive as the Twitter feeds, has some great information as well. IT security professionals use a lot of tools to combat risk. These tools get lumped together under the term “risk management.” Primarily, the tools reduce the impact of—mitigate—threats posed to an organization. Module 1-2 explores risk management concepts; later modules expand on the toolsets available. Let’s leave Module 1-1 with a definition of the job of an IT security professional: IT security professionals implement risk management techniques and practices to mitigate threats to their organizations. 01-ch01.indd 14 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-1: Defining Risk 15 Figure 1-6 RFC for HTTPS Figure 1-7 Facebook vulnerability reporting 01-ch01.indd 15 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 16 Module 1-2: Risk Management Concepts This module covers the following CompTIA Security+ objectives: • 5.2 Explain the importance of applicable regulations, standards, or frameworks that impact organizational security posture • 5.3 Explain the importance of policies to organizational security Module 1-1 ended with a pithy job description: IT security professionals implement risk management techniques and practices to mitigate threats to their organizations. To get to the “implement” stage requires knowledge, naturally, and the term “risk management” is loaded with meaning. This module explores four aspects of risk management: infrastructure, security controls, risk management frameworks, and industry-standard frameworks and reference architectures. Later modules build on this information to get you to the “implement” step. The term security posture (or cybersecurity posture) refers to the security status of every aspect of an organization. That includes the security of networks, systems, physical property, and intellectual property, plus all the systems, policies, and controls that implement that security. Security posture includes external entities that affect the organization, such as partners, vendors, and the supply chain. This module takes some of the theory and concepts from Module 1-1 and begins the journey to understanding the security posture. Infrastructure In IT risk management, the term infrastructure applies to just about every aspect of an organization, from the organization itself to its computers, networks, employees, physical security, and sometimes third-party access. Organization At its most basic, an organization is who you work for: your company, your corporation, your nonprofit, your governmental department. These are good potential examples of an organization, but in some cases, you might need more details. A single organization, for example, might look like a collection of smaller organizations in terms of risk management (Figure 1-8). The big difference here is how autonomous your IT management is in relation to the overall organization. The more decisions the main organization lets a smaller group handle, the more the smaller group should look at itself as an organization. A smaller organization might be a single physical location in a different city or perhaps a different country. It might be a division of a corporation, or a regional governmental agency. NOTE A quick way to determine the scope of any IT infrastructure is to identify the bigwigs. A single IT infrastructure should never have more than one chief security officer, for example. 01-ch01.indd 16 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-2: Risk Management Concepts 17 Figure 1-8 What’s your organization? Big Organization Physically Separate Subdivisions Functionally Separate Subdivisions Separate Security Subdivisions Separate Legal Subdivisions Systems Computers and network equipment are part of an IT infrastructure, but there are many more components. People matter, such as IT managers, IT techs, human resources, chief security officer, chief information officer, and legal staff; even individual users are part of the IT infrastructure. See Figure 1-9. Physical Security Physical security is also an important part of an IT infrastructure. Fences, cameras, and guards protect your infrastructure just as well as they protect the rest of your organization. We’ll cover physical security in Chapter 7, Module 7-8. Third-Party Access Third parties that your organization contracts with are part of your IT infrastructure. Does your organization have an intranet that enables suppliers to access your equipment? Then those suppliers are part of your IT infrastructure. Have a maintenance contract on all your laser printers? There’s another part of your infrastructure. The company that hosts all your Web servers? Yes, they are part of your IT infrastructure as well. We’ll cover third-party access in Module 1-8. Dating Habits Arrest Records Lab Results People Data Equipment Figure 1-9 We are your infrastructure. 01-ch01.indd 17 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 18 Security Controls The action of strengthening a vulnerability to reduce or eliminate the threat is called a security control. A security control is a directed action you place on some part of your infrastructure. Security controls don’t say how to perform the steps needed to mitigate a threat, only that they must be performed. Here is an example of a security control in the NIST Special Publication 800-53 (Rev. 4). IA-5 Authenticator Management Control Description The organization manages information system authenticators by: a. Verifying, as part of the initial authenticator distribution, the identity of the individual, group, role, or device receiving the authenticator; b. Establishing initial authenticator content for authenticators defined by the organization; c. Ensuring that authenticators have sufficient strength of mechanism for their intended use; Plus about seven other points that collectively make up the security control. You don’t have to know what all of that means yet, but do note that the controls are guidelines, not specific implementation steps. Steps required to implement the controls will vary among operating systems and network systems. The bottom line for your job as a security professional is to locate vulnerabilities and apply security controls. It’s what we do. NOTE The security control listed here comes from the NIST NVD in case you want to look it up: https://nvd.nist.gov/800-53/Rev4/control/IA-5. As you might imagine, the typical infrastructure probably has thousands, if not tens of thousands, of security controls that need to be applied. How does a lone IT security pro create this list of controls? The answer is, you don’t. You use a bit of magic called a risk management framework. Risk Management Frameworks A framework is a description of a complex process, concentrating on major steps and the flows between the steps. A risk management framework (RMF) describes the major steps and flows of the complex process of applying security controls in an organized and controlled fashion. 01-ch01.indd 18 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-2: Risk Management Concepts 19 EXAM TIP The CompTIA Security+ 601 objectives use the term key frameworks as an umbrella term for the various risk management frameworks discussed in this module. That’s an objectives organizational term rather than an industry term. One popular RMF is the National Institute of Standards and Technology (NIST) Risk Management Framework (RMF). See Figure 1-10. This RMF is described in NIST Special Publication (SP) 800-37, Revision 2, Risk Management Framework for Information Systems and Organizations: A System Life Cycle Approach for Security and Privacy. Originally designed as an RMF expressly for US federal organizations, the NIST RMF has been adopted as the de facto RMF by many in the IT security industry. The NIST RMF isn’t the only well-known framework. NIST RMF was originally designed only for government agencies (although the latest version of RMF changed its name from “Federal Information Systems” to “Information Systems and Organizations”). Not too many years after developing the NIST RMF, NIST introduced the NIST Cybersecurity Framework (CSF), geared more towards private industry. The NIST CSF is a similar, less comprehensive framework than the NIST RMF. International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) 27001 is the international standard for best-practice information security management systems (ISMS), roughly like the NIST RMF. ISO/IEC 27002 is the international standard to help organizations enumerate—list, define—their security controls. ISO/IEC 27002 lists categories of security controls, not actual individual controls. ISO/IEC 27701 extends the ISO/IEC 27001 standard to address personal information and privacy issues. Figure 1-10 NIST RMF from NIST.SP.800-37r2 .pdf CATEGORIZE MONITOR SELECT PREPARE Process Initiation AUTHORIZE IMPLEMENT ASSESS 01-ch01.indd 19 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 20 NOTE ISO 27001 and 27002 are certainly frameworks, but think of them more as frameworks with teeth! The EU can selectively choose to require organizations to use these frameworks as a compliance check, making them more of a standard than a simple recommendation like the NIST’s publications. ISO 31000 provides a broad, higher-level, and less technical overview of risk management concepts and tools to implement risk management frameworks from the executive standpoint. The Center for Internet Security (CIS) publishes CIS Benchmarks, an interesting and respected framework. The fact that CIS is a nonprofit, nongovernmental organization makes its framework attractive to many security professionals. Additionally, the CIS Benchmarks framework explicitly works with small, medium, and large organizations— the only framework that addresses the “little guy.” ISACA—a professional association devoted to risk management, auditing, and security controls management—produces the COBIT framework designed for enterprise-wide management and governance of information processing and technology. Currently at COBIT 2019, the framework has wide adoption in the industry. Although it might at first seem odd to throw accounting frameworks into the security mix, the auditing aspect of accounting certainly applies. The American Institute of Certified Public Accountants (AICPA) publishes the Statement on Standards for Attestation Engagements (SSAE) as a guide to financial reporting. In 2017, AICPA updated the standard from SSAE 16 to SSAE 18 to include a cybersecurity risk management reporting framework. It includes System and Organization Controls (SOC) to guide organizations in their reporting. This framework has been updated since. SOC 2 reports come in two forms, called Type I and Type II. These refer to evaluations of controls in place (Type I) and the efficiency of those controls over time (Type II). EXAM TIP The CompTIA Security+ exam objectives use the term “SSAE SOC 2 Type I/II” for the SSAE 18 framework as it applies to cybersecurity. The Cloud Security Alliance (CSA) created the Cloud Controls Matrix (CCM), a framework for security controls designed exclusively for cloud computing. Additionally, CSA produces reference architectures—templates, really—for both broad and veryspecific cloud security. Plus, the CSA CCM works well with—and was designed to complement—other industry frameworks, such as the NIST and CIS frameworks. The two biggest players in cloud computing today, Microsoft Azure and Amazon Web Services (AWS), have frameworks for security in networks that use their services. Amazon has extensive documentation for its AWS Well-Architected Framework, for example, providing guidelines for every aspect of security. Curious? Check out AWS’s Five Pillars of the Framework: https://wa.aws.amazon.com/wat.pillars.wa-pillars.en.html. Organizations use one or more of the frameworks discussed above to apply various security controls. That begs the question: Where do security controls originate? Let’s 01-ch01.indd 20 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-2: Risk Management Concepts 21 dive into the sources of some controls, such as legislation and regulations, standards, best practices, and security policies. Legislation/Regulations Many laws affect how and what types of security controls your organization may use. Governments from states/territories and nations affect those whose businesses work or operate in the respective locations. The United States has many laws that IT security professionals should know, such as the Patriot Act (2001), the Electronic Communications Privacy Act of 1986 (ECPA), the Computer Security Act of 1987, the Health Insurance Portability and Accountability Act of 1996 (HIPAA), and the Sarbanes-Oxley Act of 2002 (SOX). There are many more, but a couple of descriptions should do for this introduction. HIPAA provides data privacy and security provisions for safeguarding medical information. These include provisions for who may have access to patient records and how to properly store records. SOX has many provisions, but the one that is most important to many companies is the requirement for private businesses to retain critical records for specific time periods. Both HIPAA and SOX are discussed in more detail in Module 1-6. NOTE The CompTIA Security+ exam barely scratches the surface of what security professionals need to know about laws that affect our field. You cannot skip over legal guidelines, though, because they will bite you . . . and make your security career short and unpleasant. In response to demands by the public to protect the privacy of users visiting Web sites, the European Union (EU) created the General Data Protection Regulation (GDPR). Since GDPR became effective in 2018, odds are good you’ve seen a GDPR notification on Web sites such as shown in Figure 1-11. GDPR is an interesting law, as in theory it applies globally to any organization or country that processes or stores personal information of any EU citizen. As of this writing, the EU hasn’t attempted to sanction or fine any non-EU organization, but it’s just a matter of time. GDPR is unique to the EU, but many national, state, and territorial governments have adopted similar legislation. The state of California, for example, adopted the California Consumer Privacy Act (CCPA). Standards A standard is a ruleset voluntarily adopted by an industry to provide more uniform products and services. It might be more accurate to replace the word voluntarily with the word voluntold, because many standards are often required for participation in certain industries. Easily the most far-reaching standard from the standpoint of IT security is the Payment Card Industry Data Security Standard (PCI DSS). This industry-specific framework, adopted by everyone who processes credit card, debit card, prepaid card, or gift card transactions, provides for several highly detailed security controls to mitigate credit card fraud. Vendors who accept credit cards but fail to abide by PCI DSS rules quickly find themselves cut off from their ability to accept cards. 01-ch01.indd 21 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 22 Figure 1-11 GDPR notification Benchmarks/Secure Configuration Guides Benchmarks and secure configuration guides are knowledgeable recommendations that lack the enforceability of legislation and standards, but are an important consideration of any IT security framework. Benchmarks and guides come from governments (if you want to be accurate, even the NIST RMF is just a guide), industry groups, and vendors. In most cases benchmarks and guides tend to be very specific, directed toward a platform such as Microsoft Windows, Apache Web servers, application servers, network infrastructure devices, and so on. NOTE Add the term “best practices” to benchmarks and guides, as they are basically the same thing. 01-ch01.indd 22 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-2: Risk Management Concepts 23 Figure 1-12 Excerpt from CIS Benchmark for Apache HTTP Server One excellent example of benchmarks is the collection of CIS Controls from the Center for Internet Security, the same folks who made the CIS Benchmarks mentioned earlier. These platform-specific benchmarks are wonderfully detailed and are an excellent tool for those of us who need a more step-by-step guide for securing a broad cross-section of platforms. Figure 1-12 shows a few lines from CIS’s excellent guide to securing the popular Apache Web server. Sometimes it’s down to the users of equipment to tell others about their security experiences. Any organization can create or use a Security Technical Implementation Guide (STIG) to standardize security protocols throughout their networks. A typical STIG provides details on how to optimize desktop computer security, for example, and best practices for patching and security updates. STIGs also cover configuration and security details for every common networking device, from routers to firewalls. EXAM TIP The CompTIA Security+ exam will test your knowledge of the European legislation GDPS, US laws (HIPAA and SOX), and standards such as PCI DSS. The entire IT industry is filled with vendor-specific guides, providing best practices that vendors recommend you follow. From configuring access control lists for a Cisco router to hardening Remote Desktop on Windows Server 2019, there’s a benchmark (or best practice) for you. Microsoft provides incredibly detailed best practices for all its products (Figure 1-13). 01-ch01.indd 23 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 24 Figure 1-13 Best practices for a Microsoft product Security Policies A security policy is a document that organizations generate to declare what actions and attitudes they will take for certain critical aspects of their infrastructure. An organization may have hundreds of policies, but, generally, policies most commonly define security controls for the trickiest assets in every organization—the people. Later modules will delve deeply into policies; for now, let’s look at one of the most common, an acceptable use policy. An acceptable use policy (AUP) defines exactly what users may or may not do on systems in the organization. Here are a few lines from an example AUP pulled from one of many free boilerplates available on the Web: • Users must not attempt to access any data, documents, e-mail correspondence, and programs contained on systems for which they do not have authorization. • Users must not share their account(s), passwords, personal identification numbers (PIN), security tokens (i.e., smart card), or similar information or devices used for identification and authorization purposes. • Users must not use non-standard shareware or freeware software without the appropriate management approval. • Users must not engage in activity that may degrade the performance of Information Resources; deprive an authorized user access to resources; obtain extra resources beyond those allocated; or circumvent computer security measures. • Users must not download, install, or run security programs or utilities such as password cracking programs, packet sniffers, or port scanners that reveal or exploit weaknesses in the security of a computer resource unless approved by the CISO (chief information security officer). 01-ch01.indd 24 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-3: Security Controls 25 Module 1-3: Security Controls This module covers the following CompTIA Security+ objective: • 5.1 Compare and contrast various types of controls The previous module covered the concept of security controls and even showed you a few examples. This module delves deeply into the organization of security controls. This organization makes it easier to consider the types of controls available and to classify them into specific groups based on what they do to mitigate threats. The CompTIA Security+ objectives group controls into two broad areas: categories and types. Let’s look at both to see how they work. Control Categories Control categories define who or what aspect of the enterprise deals with them or who or what aspect of the infrastructure they affect. In this case, we break security controls into managerial, operational, and technical. Managerial Controls You can categorize controls by defining the people responsible for those controls. A managerial control (or management control), for example, is a broad control that covers the entire organization. All employees, no matter their location, must use a 12-character password updated every 30 days—that’s a managerial control. These require some form of management overview. Management controls are reviewed periodically, such as yearly or monthly. Operational Controls Operational controls apply to a single unit in an organization and deal with how things get done. An example of an operational control would be a requirement that a certain PC controller must be reset daily. Operational controls rarely need management overview and are reviewed far more frequently than management controls. Technical Controls Technical controls are security controls applied to technology. If you specify a security control that states, “All edge routers must be able to communicate on SNMPv3,” then you’ve made a technical control. Control Types Thus far, the book has defined a security control as an action performed on a vulnerability to mitigate the impact of a risk. But what form of action can a control take? At first glance you might be tempted to look at a security control as an action to block an attack. It’s tempting, for example, to think of placing 20-character, complex WPA2 passwords on all the wireless access points (WAPs) in an organization as a security control that will stop anyone from hacking the 802.11 network. This is a strong security control 01-ch01.indd 25 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 26 Figure 1-14 Mitigation isn’t perfection. My complex, 20-character password makes this SSID unhackable! WPA2 Not unhackable, just a lot harder to hack. no doubt, but it can’t absolutely stop a determined attacker. Even long passwords can be hacked, although the probability of a successful attack is greatly reduced (Figure 1-14). Mitigation doesn’t mean stopping an attack. Attacks happen. Therefore, it’s helpful to define security controls based on when they work relative to the phase of an attack. A security control might work before, during, or after an attack. These are generally known as control types. You need to know five control types for both essential skills and the CompTIA Security+ exam: deterrent, preventive, detective, corrective, and compensating. EXAM TIP The CompTIA Security+ objectives include physical as a control type. The physical control category includes options for securing physical areas from unauthorized access, such as fences, bollards, and so on. See Chapter 10, Module 10-1 for physical controls in depth. Deterrent Control A deterrent control is designed to deter a potential attacker from even attempting an attack. Good lighting or signage around your building might deter an intruder from entering. Not building a server building near a fault line is another example. Figure 1-15 shows the welcome banner from a Secure Shell (SSH) server. Surely that will deter any potential hacker! Figure 1-15 Mike’s SSH warning 01-ch01.indd 26 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 27 Preventive Control A preventive control attempts to keep an active attack from succeeding. The earlier example of using a 20-character password on WPA2 is a great example of a preventive control. Putting a lock on the server room door is another example of a preventive control. Doing thorough background checks on potential new employees would be a third example. NOTE Most security controls are preventive controls. Detective Control A detective control works during an attack. As the name implies, these controls actively look for an attack and alert security professionals to the presence of an active, ongoing attack. An intrusion detection system, for example, watches a network for activity that indicates an intrusion attack. A security camera detects someone trying to go into a place he or she does not belong. EXAM TIP Some security controls cross phases. A security guard can be classified as a deterrent control, preventive control, or detective control, for example, depending on the role that the security guard is playing at any given moment. Corrective A corrective control applies after an attack has taken place and fixes/mitigates the result of the incident. Restoring data from backups is probably the most common example of a corrective control. Compensating Sometimes you need to provide a temporary solution to a vulnerability that’s less than optimal. Perhaps someone tried to drive through a fence and you need to hire an extra guard for a short time. Maybe all users have to log into a system as root until a completely new system comes online, so you add extra logs to track usage more closely. These are compensating controls. You use compensating controls to keep going until a better control is available or possible. Module 1-4: Risk Assessment This module covers the following CompTIA Security+ objective: • 5.4 Summarize risk management processes and concepts Previous modules discussed risk and the security controls used to mitigate risk. So, you might think that risk management is nothing more than an ongoing process 01-ch01.indd 27 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 28 Figure 1-16 Probably not worth it We can just skip payroll! No. Ion Cannon of identifying each vulnerability and then applying some form of security control to mitigate the risks that vulnerability exposes. Applying security controls is important, but the actual step of applying a security control is the end of a complex process. Risk management is much more nuanced. This nuance comes from the fact that every risk has a different vulnerability and impact. A risk with very low impact might not be worth the cost of mitigation. Equally, a risk with very low impact might motivate you to ignore the risk. Also, consider the fact that IT security teams have a limited amount of money, time, and resources to apply to addressing all the risks. Consider the risk of a meteor hitting your facility (Figure 1-16). If you could get a Star Wars ion cannon for the low, low price of $47 trillion, how would you feel about sending that bill to your accounting department? These variables require a good IT security professional to develop a risk assessment, which is a carefully organized plan, more nuanced than simply trying to mitigate everything. A good risk assessment uses several tools and methods to enable the IT security professional to react to all threats in a realistic and practical way. This module starts by defining some of the main concepts and tools of risk assessment. The module describes existing frameworks you can use to help you perform a comprehensive risk assessment. Risk Assessment Processes and Concepts Risk assessment brings a lot of jargon into play to describe specific aspects or nuances in security. This section explores risk assessment terms that define common processes and concepts: risk awareness, risk and controls, risk assessment methods, threat sources and events, vulnerabilities, likelihood and impact, and risk register. Risk Awareness Risk awareness is the process by which people recognize risk. It’s one of those terms that sounds obvious but really isn’t. Sure, we want to be aware of risk, but how does that awareness manifest? Knowing how we are aware of a risk often helps us mitigate that risk. First of all, maybe it doesn’t manifest at all. Perhaps the awareness comes from careful analysis, or perhaps the person identifying the risk has some form of bias about that risk. 01-ch01.indd 28 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 29 Risk and Controls There’s more to risk than simply mitigating through controls. You can’t just recognize a risk and slap on a control to mitigate that risk. You need to consider the ramifications of the control before applying it to a risk. Does the control mitigate the risk? What happens without the control? How much mitigation does the control provide? Is it worth it? Does the application of the control create other risks that also have to be mitigated? That creates three states: the risk with no control applied; the risk after a control; new risks developed because of the control. Inherent risk represents the amount of risk that exists in the absence of controls. Residual risk is the amount of risk that remains after accounting for controls. Control risk is the probability of loss resulting from the malfunction of internal control measures implemented to mitigate risks. Once a control is applied, it’s important to make a control assessment. These assessments manifest in many ways, but you should know the two ways to perform that assessment: a risk control assessment is when you use an outside source to inspect and judge the quality of your controls. This might be important especially to comply with laws or regulations that affect control risk or risk posture—the overall scope of risk for an organization. Otherwise, an organization can simply perform a risk control selfassessment—as in you use in-house resources to do the assessment. Risk Assessment Methods In addition to hiring knowledgeable and experienced risk management personnel, organizations can implement and follow a formalized process or methodology in assessing risk. Developing this process can be quite an undertaking, but, fortunately, organizations can use existing methods created by experts in the risk management profession. One such common method of conducting risk assessments is NIST SP 800-30, Rev. 1, Guide for Conducting Risk Assessments. Another assessment methodology comes from ISACA, a professional association devoted to risk management, auditing, and security controls management. This methodology is The Risk IT Framework. Both methodologies describe detailed processes for conducting risk assessments, and both can be adapted for any organization to use. NIST SP 800-30, Rev. 1, prescribes a four-step risk assessment process: 1. Prepare for assessment. 2. Conduct assessment: A. Identify threat sources and events. B. Identify vulnerabilities and predisposing conditions. C. Determine likelihood of occurrence. D. Determine magnitude of impact. E. Determine risk. 3. Communicate results. 4. Maintain assessment. 01-ch01.indd 29 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 30 After initial preparation, the IT security professional begins the assessment. First, identify threat actors (sources) and threat events, and then identify vulnerabilities associated with assets and other risk factors. You then calculate likelihood and impact values, which define the risk. Communicating the risk assessment results means reporting the assessment to management, so that risk response options can be carefully considered. Maintaining the assessment means implementing the response options and closely monitoring the risk, periodically reassessing it to ensure the effectiveness of the response options and to determine whether the risk has changed. NOTE Although you likely will not be tested on either the NIST or ISACA methodologies, they’re good to know for use on the job, especially if you are assigned any type of risk assessment duties for your organization. Identifying Threat Sources and Events The first step in threat assessment is to identify the threat sources and to categorize them into groups. The process of categorizing threats may seem daunting, but NIST and ISACA provide some good basic categories to begin the process. Referencing NIST SP 800-30, Rev. 1, Table D-2, one possible categorization might look something like Figure 1-17. You’re not required to use this categorization. Some organizations simply break all threat sources into no more than the following four categories. Compare these to similar categories listed in Figure 1-17 to get an idea as to how different organizations can use totally different categories to cover the same types of threats. • Environmental Natural disasters outside the control of humans • Person-made Any threat that is not environmental; includes disasters caused by people • Internal Threat generated by internal sources, usually an insider to the organization • External Threat generated from outside your infrastructure Vulnerabilities As a refresher from Module 1-1, a vulnerability is a weakness inherent in an asset that leaves it open to a threat. Vulnerabilities in an organization vary according to the unique components of that organization, so it’s hard to provide anything concrete here that applies universally. Broadly speaking, though, just as with threat sources, organizations can have internal and external vulnerabilities. Internal vulnerabilities include legacy systems and software compliance/licensing issues. As a business grows over time, that “old Windows 7 computer in the corner that has one job” might not have any security support anymore. Assessing all the systems in use throughout an organization is essential to finding vulnerabilities. Likewise, software that is out of compliance or license creates a financial vulnerability—get caught in an audit and pay stiff penalties. 01-ch01.indd 30 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 31 Figure 1-17 Example taxonomy of threat sources (from NIST SP 800-30, Rev. 1) Multiparty affiliations can expose external vulnerabilities, such as the communications among the entities, or a shared database in the cloud with users from each entity. Having valuable intellectual property presents a prototypical vulnerability, IP theft by external hackers. 01-ch01.indd 31 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 32 Combine these vulnerabilities with willing and able threat actors, then define the likelihood of occurrence (described next). These are classic risks for which you need to implement security measures to protect the organization. NOTE CompTIA uses the term “risk types” to describe vulnerabilities like those outlined in this section. The vulnerabilities become risks when you add threats and likelihood. Likelihood and Impact Once you have collected all the different data on threats, vulnerabilities, and assets, you can assess likelihood of occurrence and impact. Likelihood of occurrence is the probability that a threat actor will initiate a threat or the probability that a threat could successfully exploit a given vulnerability. Impact is the degree of harm or damage caused to an asset or the organization. Both can be viewed in either objective or subjective terms. Objectively, likelihood or impact could be expressed in terms of numerical values. In a subjective expression, both elements may be termed qualitatively, or using a range of descriptions on a scale. These two ways of expressing likelihood and impact are the two risk assessment types discussed in the upcoming sections: quantitative (objective or numerical) and qualitative (subjective) assessment types. Risk Register High A risk register is a scatter-plot graph that compares probability to impact. Risk registers are handy tools for detecting otherwise easily missed risks. Meteor Impact Fire Impact Lose Critical Programmer Patching Error Low Router Failure Malware Low Probability High Taxonomy of Threat Sources 01-ch01.indd 32 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 33 Quantitative Risk Assessment An organization uses a quantitative risk assessment when it requires exact figures on risk equated to likelihood and impact. Exact dollar values, for instance, can be used to describe impact or loss of an asset. A quantitative risk assessment requires that the organization measure and obtain certain pieces of data, because the assessment depends upon the accuracy and completeness of the data fed into it. A quantitative risk assessment is based on objective data—typically, numerical data. A quantitative assessment is objective in that the data fed into it is measurable and independently verifiable. For example, cost expressed as a dollar value is a measurable and concrete piece of data often used to perform quantitative analysis. Other types of numerical data may include statistical analysis of different aspects of likelihood, for instance. In the next few sections, we’ll look at five data elements required to perform a quantitative assessment: asset value, exposure factor, single-loss expectancy, annualized rate of occurrence, and annualized loss expectancy. Note that these are very simplistic data elements; in more complex assessments, other data elements might be required as well. Asset Value and Exposure Factor A quantitative risk assessment starts with determining asset value, a monetary figure that reflects various factors, such as replacement or repair cost, cost over time, and more. First, determine an asset’s replacement cost. Some organizations may need to consider depreciation values over time, however, which would reduce the amount of money they may have available to replace an asset. Another consideration is repair cost versus replacement cost. If an asset simply needs repair to return to an operational condition, then the organization should consider different costs for different components required to repair the asset. (See Module 1-5 for more on component failure measurements.) Beyond cost to replace or repair the asset, you must also look at the revenue the asset generates. To replace a failed server, for example, costs $5000; the amount of revenue that the server brings in every day, due to the data that’s processed on it, is $3000. So even if you pay the $5000 to order a new server, if the vendor can’t get it to you and installed within four days, you’ve lost $12,000 in revenue in addition to the cost of the server. Those considerations may require you to reevaluate the value of the asset. It’s not only about the cost of replacement for the asset, but also how much value it gives to the organization. NOTE When valuing an asset, consider not only the replacement cost but also the revenue the asset generates, as this will be lost as well if the asset is not available. Along with asset valuation, organizations should consider the exposure factor, the percentage of an asset’s value that could be lost during a negative event. Realistically, you will not always lose 100 percent of the value; you may lose only 30 percent or 50 percent, 01-ch01.indd 33 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 34 for example. Exposure factor considers the percentage of the asset’s value (or the revenue derived from the asset) lost in the event of an incident. You can use exposure factors when performing risk assessments to determine realistically how much of a loss your organization may suffer during an incident. This in turn affects how much money or other resources you should devote to budgeting for risk response. Exposure factors are normally expressed mathematically as a decimal number. An exposure factor of 0.4, for example, is a 40 percent loss, and an exposure factor of 1 is a 100 percent loss. Single-Loss Expectancy The single-loss expectancy (SLE) is a value that’s computed simply by multiplying the asset’s value (in dollars) by the exposure factor (percentage of loss). Use this simple formula as the initial step in describing risk from a quantitative point of view. The SLE indicates what the loss would be in a single circumstance of a negative incident affecting the asset. The formula can also be described as follows: SLE (single-loss expectancy) = AV (asset value) × EF (exposure factor) Given this formula, suppose you had an asset worth $5000, and during a single-loss event such as a fire, you’d expect to lose 50 percent of that asset’s value. This would be expressed as: SLE = $5000 (AV) × 0.50 (EF) = $2500 Obviously, this is a very simple scenario. When calculating SLE, you must look at other aspects of the loss, such as the event that might cause the loss, its likelihood, revenue generated from the asset, and so on. Additionally, exposure factor can be a difficult value to nail down. You might use statistical analysis, or even the “best guess” by a committee of experts, to determine exposure factor for different assets. EXAM TIP Know the formula for single-loss expectancy: SLE = AV (asset value) × EF (exposure factor) Annualized Rate of Occurrence The annualized rate of occurrence (ARO) is how many times per year you would expect a negative event to occur, resulting in a loss of the asset. This value relates more to likelihood than impact and serves to establish a baseline of how likely a specific threat is to occur, affecting the asset. This value can result from several different sources. First, you could look at historical trends. For example, let’s say that your business is in an area prone to tornadoes. You can gather information from the National Weather Service on how many tornadoes normally occur in your region every year. This would be the ARO for that threat. Obviously, other events would have other rates of occurrence. Some of these would be difficult to quantify without more in-depth information. For instance, obtaining the ARO for 01-ch01.indd 34 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 35 attacks from hackers would be problematic, since that would not necessarily be limited to a geographical area. You might have to gather data and perform statistical analysis to determine how often serious attacks occur, given specific circumstances, attack methods, level of attack, and so on, with regard to your type of industry or business. Some of this data might come from published industry trends, and some information may come from law enforcement or threat intelligence sources (introduced in Module 1-1) that provide aggregate analysis of this particular type of data. In the end, this might simply be an educated guess, based upon the best data you have available to you. In any case, what you’re after is an end number that you can use as a factor in determining how often a particular threat might occur on an annual basis. You’ll use this number during the next calculation, the ALE. Annualized Loss Expectancy The annualized loss expectancy (ALE) essentially looks at the amount of loss from the SLE and determines how much loss the organization could realistically expect in a one-year period. Viewing potential loss on an annual basis makes it easier to craft budgets and allocate resources toward risk management, since most organizations function on a fiscalyear basis. Additionally, this allows the organization to project how many times in a given year a particular event may occur. The formula for ALE is also quite simple: ALE (annualized loss expectancy) = SLE × ARO Let’s use an example to make this formula clear. The Bayland Widgets Corporation has a data center in Totoville, Kansas. Totoville averages about seven major tornados a year. The ARO of a tornado is therefore 7. A serious tornado hit to the $2,000,000 facility would likely cause about 20 percent damage. Put those numbers together to create the SLE: SLE = AV ($2,000,000) × EF (20% or 0.2) SLE = $400,000 If all seven major tornadoes that occurred during the year actually hit and caused this level of damage to the facility, then the ALE would be $400,000 (SLE) × 7 (ARO) = a potential loss of $2,800,000 (ALE). This would be the worst-case scenario. Realistically, since all seven are not likely to hit the facility, you can lower the ARO to a lesser number. Obviously, this is a very simplistic (and most likely remote) scenario; the object here is to show you the different data elements and demonstrate how the formulas work. These simple formulas don’t take into account realistic values or other risk factors that may affect likelihood and impact. However, they do demonstrate the basics of how you might calculate these two risk elements. You’ll find that these particular formulas are prevalent throughout the Security+ exam as well as other higher-level information security exams, such as the CISSP. EXAM TIP Understand the formula for computing the annualized loss expectancy: ALE = SLE (single-loss expectancy) × ARO (annualized rate of occurrence) 01-ch01.indd 35 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 36 Qualitative Risk Assessment Quantitative risk assessments seem to be, on the surface, the way to go if an organization wants a very accurate, data-driven view of risk. Quantitative analysis, however, has a couple of weak points. First, a lack of data can force organizations to use incomplete or subjective numerical values. Second, even exact numbers can be misleading, simply because of the different methods people and organizations use to arrive at numerical values. Yet another issue is the fact that even when you’re talking about exact numbers, they can still be subjective. People, because of their own opinions or limitations of their data collection and analysis processes, sometimes have to make educated guesses about numerical values. These issues can cause data to be incomplete, inexact, or simply incorrect. Another big shortfall with quantitative analysis is that many other types of data cannot be easily quantified or measured. Some of these pieces of data are also subjective. In other words, they are dependent upon the point of view of the person collecting and analyzing the data. This is why a qualitative analysis is often preferred. A qualitative risk assessment doesn’t necessarily use numerical values; it relies on a risk appetite. Risk appetite is a relative term of how much risk is perceived by the organization. Organizations usually assign a descriptive value, such as low, medium, or high when defining a risk appetite for a particular risk. They take into consideration less tangible ideas such as experience, opinion, trend analysis, or best estimates. For example, what would the impact be to an organization if it suffered a loss of reputation in the marketplace? Reputation cannot be easily quantified numerically. Those are typically the values (or some similar range of descriptive values) that qualitative analysis uses. In the case of loss of reputation, the impact might be designated as high, for instance. Even risk elements that could normally be assigned a numerical value can be expressed qualitatively. The likelihood of a threat exploiting a vulnerability could be expressed in a range of descriptive values, such as very low, low, moderate, high, and extreme. The same could be said for impact. Of course, these values are subjective; what one person believes to be a high likelihood, another may believe to be an extreme likelihood. In qualitative analysis, the organization must come to a consensus over what qualitative values mean and the relationships among values. We can use tools such as a risk matrix to help organize risk assessment. A risk matrix is a table that plots the likelihood of occurrence of a risk against the severity of the impact. Imagine a scenario where a server room becomes inoperable. Plotting severity of impact against likelihood, we could see something like the risk matrix shown in Table 1-1. Impact Marginal Likelihood Minor Important Critical Certain Moderate High Extreme Extreme Likely Moderate High High Extreme Possible Low Moderate High High Unlikely Low Low Moderate Moderate Rare Very Low Very Low Low Moderate Table 1-1 Risk Matrix 01-ch01.indd 36 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 37 Figure 1-18 Qualitative and semi-qualitative values (from NIST SP 800-30, Rev. 1) This sample risk matrix is fairly easy to read, but as a matrix gets larger it’s often handy to add color to the matrix to represent the risk by color: red the highest and green the lowest. This is called a heat map. Despite the subjective nature of qualitative analysis, this type of assessment can be very meaningful and accurate. The organization can develop a method of calculating risk based upon the relative values of impact and likelihood, even given descriptive values. In Figure 1-18, taken from NIST SP 800-30, Rev. 1, risk can be calculated from a qualitative perspective using descriptive likelihood and impact values. It’s also worth mentioning here that another type of scale could be used, one that does use numeric values. You could have a scale that uses values from 1 to 10, for example. In this case, the scale will be referred to as semi-quantitative, because these numbers could be averaged together to get aggregate values. Since it is still a subjective measurement, however, it is really a qualitative type of analysis. Putting It All Together: Risk Analysis Although qualitative risk analysis is probably most often used because it can accept a wide variety of data, including elements that are not easily quantifiable, most organizations use a combination of qualitative and quantitative analyses. To calculate the impact, for example, the organization might use quantitative assessments. To calculate likelihood, the organization may go with a qualitative approach. For some risk scenarios, either one or both may be more appropriate. Which method an organization uses depends upon what type of data it has and what type of data it wants to obtain from the analysis. Also, although risk scenarios typically revolve around a single threat, vulnerability, and asset at a time taken together in context, these risks are usually calculated and then rolled up into a larger level of risk that applies to the entire organization. Figure 1-19, also taken from NIST SP 800-30, Rev. 1, illustrates how the use of qualitative values can be used to describe overall risk. At first glance, Figure 1-19 seems almost identical to Figure 1-18, but read the descriptions. Figure 1-18’s description is concerned with 01-ch01.indd 37 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 38 Figure 1-19 Qualitative assessment of risk (from NIST SP 800-30, Rev. 1) the attacker, whereas the description in Figure 1-19 describes the risk in terms of how it might affect infrastructure. NOTE Remember the difference between qualitative and quantitative assessment methods. Qualitative methods use descriptive terms, while quantitative methods primarily use numerical values. Risk Response After you’ve identified and analyzed risk for assets and the organization, you must then decide how to respond to the risks produced as a result of the analysis. Responding to risk means to attempt to minimize its effects on the organization. Risk management strategies fall into four categories: • • • • Mitigation Transference Acceptance Avoidance An organization chooses risk mitigation, risk transference, risk acceptance, or risk avoidance depending on several factors, including cost, effectiveness, and what value it places on the asset in question. Often, risk responses could include implementing 01-ch01.indd 38 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-4: Risk Assessment 39 technologies or controls that cost more than the asset is worth, and the organization has to decide whether it is worth it to deal with the risk. Risk mitigation is an attempt to reduce risk, or at least minimize its effects on an asset. This may mean reducing the likelihood of occurrence, reducing or eliminating the exposure of the vulnerability, or reducing the impact if a negative event does occur. Mitigation usually involves adding security controls to protect an asset against a threat, reducing likelihood, exposure, or impact in some way. Be aware that most risk management theory states that risk can never be completely eliminated; it can only be reduced or mitigated to an acceptable level. The acceptable level may be an extremely low likelihood of occurrence or an extremely low impact if the risk were to be realized. Risk transference (also sometimes called risk sharing) deals with risk by sharing the burden of the risk, especially the impact element. In risk transference, an organization contracts with another party to share some of the risk, such as the cost to the organization if the threat were realized. The standard example of risk transference you will often hear about in the security community is the use of cybersecurity insurance. Buying insurance to protect a business in the event of a natural disaster, for example, alleviates the burden to the business by reducing the impact of cost if a natural disaster occurs. The insurance pays the business if equipment or facilities are damaged, reducing the impact. Note that this doesn’t lessen the likelihood of the threat occurring; it only lessens the financial impact to the business. Another example of risk sharing is through the use of third-party service providers, such as those that provide infrastructure or data storage services. In this example, the business contracts with a third party to store and protect the business’s data in a different location. Such an arrangement could be beneficial to the business because it might reduce the likelihood of a threat occurring that would destroy data (by providing additional security controls and data redundancy, for example) as well as the impact. NOTE Transferring risk does not also mean transferring legal responsibility or liability from the organization. Ultimately, the responsibility for protecting data and following legal governance still belongs to the organization. Risk acceptance means the organization has implemented controls and some risk remains. It does not mean simply accepting an identified risk without taking any action to reduce its effects on the organization. Risk acceptance isn’t the act of ignoring risk. Risk acceptance occurs when an organization has done everything it can do to mitigate or reduce risk inherent to an asset, yet finds that some small level of risk remains even after these efforts (called residual risk). Remember that risk can never be completely eliminated; it may simply be reduced to a very unlikely level or to a very insignificant impact. As an example, suppose that an organization believes there is significant risk to one of its most valuable information technology assets, a critical server that processes realtime financial transactions. If this server costs $20,000 to replace, the organization may spend $3000 in security controls to protect the server. After it has spent this money, 01-ch01.indd 39 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 40 the organization may find that the risk is reduced to a very small level. The residual risk is very unlikely, and even if it were to occur, it would have only a very slight impact. The organization could reduce the risk even more by spending an additional $2000 on more controls, but if the risk is very small, would spending the additional money be worth it? At this point, the organization has to decide whether to spend the additional money or simply accept the residual risk. Risk avoidance means that the organization could choose not to participate in activities that cause unnecessary or excessive risk. Note that this doesn’t mean that the risk is ignored and that the organization does not take steps to reduce it. In some cases, a business pursuit or activity may be too risky to undertake, for example. The organization may perform a risk analysis on a proposed activity and simply decide that the risk is not worth the potential negative effects to the asset or organization. Often, an organization will use a combination of these responses to address the many and varied risks it encounters; there is no one perfect response solution that fits all organizations, assets, and activities. The decision of how to respond to a particular risk scenario involves many complex factors, which include cost, effectiveness of the response, value of the asset, and the ability of the organization to implement a particular response successfully. Additionally, as risk factors and conditions change over time, the organization must continually monitor and revisit risk responses from time to time to ensure that they are still effective. EXAM TIP Remember the four possible risk responses: risk mitigation, risk transference, risk acceptance, and risk avoidance, as well as their definitions. Module 1-5: Business Impact Analysis This module covers the following CompTIA Security+ objectives: • 1.6 Explain the security concerns associated with various types of vulnerabilities • 5.4 Summarize risk management processes and concepts • 5.5 Explain privacy and sensitive data concepts in relation to security A good risk assessment requires analysis of the impact of incidents against the IT infrastructure. You should consider the impact of an incident in terms of how it affects the work of an organization. To do this, security professionals perform a business impact analysis (BIA) that predicts both the consequences of incidents and the time and resources needed to recover from incidents. This module starts with an overview of the steps involved with performing a BIA, using my company, Total Seminars, as an example. The rest of the module focuses on three important BIA functions: types of impact, location of critical resources, and calculating impact. 01-ch01.indd 40 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-5: Business Impact Analysis 41 NOTE A business impact analysis is designed to mitigate the effects of an incident, not to prevent an incident. BIA Basics NIST SP 800-34, Rev. 1, Contingency Planning Guide for Federal Information Systems, offers a detailed, three-stage BIA (Figure 1-20): 1. Determine mission/business processes and recovery criticality. Mission/Business processes supported by the system are identified and the impact of a system disruption to those processes is determined along with outage impacts and estimated downtime. My interpretation: Make sure you know which workflows and processes your organization depends on to operate, in other words, the mission-essential functions. Determine the types of impact and consider the impact of the failure of each of these workflows and processes. Estimate how long it takes to bring those workflows and processes up to speed. 2. Identify resource requirements. Realistic recovery efforts require a thorough evaluation of the resources required to resume mission/business processes and related interdependencies as quickly as possible. My interpretation: What are the critical tools your organization uses to do these workflows and processes? Where are they? How do they work? In other words, a BIA provides identification of critical systems. Figure 1-20 NIST SP 800-34, Rev. 1 01-ch01.indd 41 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 42 3. Identify recovery priorities for system resources. Based upon the results from the previous activities, system resources can be linked more clearly to critical mission/ business processes and functions. Priority levels can be established for sequencing recovery activities and resources. My interpretation: Once you understand all the resources that make a workflow/ process work, determine the priority of bringing them back up to speed if they fail. Make sure you know the mission-essential functions of the organization; this helps you prioritize recovery. NOTE A BIA is part of a broader field of study in IT security called contingency planning (CP). CP covers almost everything an IT security person needs to consider to keep an infrastructure humming in the face of an incident. CP goes way beyond the scope of the CompTIA Security+ exam, but note for future studies that the two go together. A typical small business provides an excellent example for a BIA in action. Total Seminars (or TotalSem, for short) writes books, generates online content, builds test banks, and makes lots of videos (shameless plug: check out hub.totalsem.com). Determine Mission/Business Processes and Recovery Criticality TotalSem has three critical workflows: • The online store (www.totalsem.com) for selling products • Internet access for R&D and customer communication • Video production facility consisting of workstations and a few critical local servers The three workflows differ in what the company can do to protect them. Amazon Web Services hosts the Web site and store, so there is little to do to mitigate the impact of AWS going down, other than wait. Internet access has two components. The cable company provides the pipe—not much to do there, just like with AWS—and TotalSem techs control access to the Internet for each workstation. Video production, while important, can go down for a day or two without too much impact (unless you’re waiting for my next video!). Now, let’s sort these workflows by priority. 1. Internet access 2. Video production 3. Web store The Web store generates company profits and, from a business sense, should have top priority. Because TotalSem has no direct control over the store, however, it drops to the bottom of this list. Once you’ve determined priorities, move to the next BIA stage. 01-ch01.indd 42 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-5: Business Impact Analysis 43 Identify Resource Requirements At the second stage, you should analyze all the resources required for each mission/process outlined in the first stage. Total Seminars’ Internet access provides a good example. Total Seminars’ Internet access isn’t very complex. A single Internet service provider (ISP) provides a cable modem that’s owned by the ISP. Locally, TotalSem has a midrange edge router (Cisco ASA) that supports a public-facing DNS server. The TotalSem internal network moves through a second NAT router (with a built-in switch) to individual systems. The resources for Internet access therefore consist of a cable modem, a server, and a couple of routers/switches. After outlining all resource needs for each mission/process, move to the next stage. Identify Recovery Priorities for System Resources At the final stage, prioritize recovery steps. If TotalSem completely lost Internet access, for example, the priority would be (other people may have a different opinion as to this order): 1. Repair/restore/replace cable modem (must have for Internet). 2. Repair/restore/replace edge router (need the protection for DNS server). 3. Repair/restore/replace DNS server (critical to access certain systems). 4. Repair/restore/replace NAT router (for workstations). At this stage, you should identify recovery priorities for system resources that support every mission/process outlined in stage one. Types of Impact To analyze the impact of an incident, focus first on the consequences in terms of business processes supported by the affected resources. A typical BIA looks at (at least) five types of impact: • • • • • Financial Reputation Availability loss Privacy Data Financial Financial impact manifests in several ways. It might mean lost or delayed sales. It might also lead to increased expenses, such as overtime, outsourcing, and fines. The one good aspect of financial impact is that it has a quantitative dollar value. Reputation How does a potential customer feel if he or she heads to www.totalsem.com only to find the Web site down (Figure 1-21)? Reputation is an important impact to consider, but it’s 01-ch01.indd 43 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 44 Figure 1-21 Reputation is critical. Noooooo! Site Down also difficult to quantify. There are studies that can give a financial estimate of loss of reputation, but even these are very specific (such as sales loss due to lost customers due to a data breach). Availability Loss Every organization relies on critical data. If that data becomes unavailable, it can have a massive negative impact on the organization. Here are some examples: customer lists deleted; file storage disconnected and unavailable; an expired certificate that makes access to a company Web site fail; all these describe availability loss. Privacy Any organization that keeps individuals’ personal information takes on several risks with serious legal and financial impacts, both to itself and to the individuals whose data is being stored. The next module, Module 1-6, goes into great detail on the concept of privacy. I’ll save the details until then but address the concept of privacy impact here. An organization performs a privacy impact assessment (PIA) to determine the impact on the privacy of the individuals whose data is being stored and to ensure that the organization has sufficient security controls applied to be within compliance with applicable laws or standards. To create a PIA, an organization performs a privacy threshold assessment (PTA) on its infrastructure to locate personal information, determine what personal information is stored, and from whom the personal information is collected. Once the PTA is complete, the PIA can then be applied. Data Bad things can happen to good data, from outright loss to unauthorized access by untrusted sources. Problems with data can have impacts in many categories. Data loss reduces productivity, because the data needs to be re-created. Worse, it has a financial impact—the time to re-create the data costs money. Finally, data loss can hurt reputationally; for example, a deliverable not getting to a client on time because of data loss besmirches the organization. Data breaches occur when confidential information has been exposed, whether by accident or by malicious intent. Data exfiltration is a type of data breach, specifically 01-ch01.indd 44 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-5: Business Impact Analysis 45 involving bad actors/malware performing an unauthorized transfer of data. The impact of such data breaches and exfiltration will undermine customer confidence, impacting the organization’s reputation. The financial impact can come from getting sued over the breach and paying legal fees as well. Locating Critical Resources Analyzing critical resources as part of a BIA can reveal unexpected vulnerabilities. Resources needed for TotalSem’s Internet access provides a good example. Total Seminars’ Internet access relies on four basic resources: • • • • Cable modem Edge router DNS server NAT router The BIA clearly shows several single points of failure: if any one of these resources fails, TotalSem loses its business process of Internet access. The impact of losing this process could cause negative financial consequences for the company: pretty much every employee stops working. You should mitigate single points of failure if possible. In the case of resources needed for Internet access, for example, several actions could mitigate the problems: • Cable modem Add a second ISP into the mix. This could act as a failover if the primary ISP fails. • Edge router Cisco produces very reliable routers, but a quick check of the Cisco Web site shows the router model used by TotalSem accepts dual power supplies. This will help increase the MTBF (see the next section) significantly. • DNS server A single DNS server is never a good idea. TotalSem could add a second DNS server or create a secondary lookup zone on a cloud server. • NAT router TotalSem uses a low-quality router, but has spares ready to go. There will be a time impact to install the replacement, but having the spare onsite is far better than running to the store. Calculating Impact The process of calculating impact has the same problem that calculating risk in earlier modules had: is it qualitative or quantitative? The CompTIA Security+ exam touches only on qualitative business impact analysis, and only on a few well-known factors: MTBF, MTTF, and MTTR. The mean time between failures (MTBF) factor, which typically applies to hardware components, represents the manufacturer’s best guess (based on historical data) regarding 01-ch01.indd 45 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 46 Figure 1-22 Router datasheet showing MTBF how much time will pass between major failures of that component (Figure 1-22). This is, of course, assuming that more than one failure will occur, which means that the component will be repaired rather than replaced. Organizations should take this risk factor into account because it may affect likelihood and impact of the risks associated with critical systems. The mean time to failure (MTTF) factor indicates the length of time a device is expected to last in operation. In MTTF, only a single, definitive failure will occur and will require that the device be replaced rather than repaired. Lastly, the mean time to repair (MTTR) is the average time it takes to repair (or replace) a hardware component. Mean time to recovery (MTTR) is the time it takes for a hardware component to recover from failure. (The two MTTR definitions are frequently used interchangeably.) EXAM TIP You should understand the difference between mean time between failures (MTBF), mean time to failure (MTTF), and mean time to repair (MTTR) measurements for hardware failure. Calculating Downtime When systems go down, they affect other systems as well. The recovery time objective (RTO) is the maximum amount of time that a resource should remain unavailable before an unacceptable impact on other system resources occurs. The recovery point objective (RPO) defines the amount of time that will pass between an incident and recovery from backup. If a company backed up yesterday, for example, the RPO is 24 hours. If data changes so rapidly (an accounts receivable database, for example) that any backup more than an hour old requires calling customers or other extraordinary actions, then the RPO is one hour. The RTO and RPO help IT professionals calculate how much an organization can or will lose if a system goes down before backup systems can be brought online. 01-ch01.indd 46 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 47 Module 1-6: Data Security and Data Protection This module covers the following CompTIA Security+ objectives: • 1.6 Explain the security concerns associated with various types of vulnerabilities • 2.1 Explain the importance of security concepts in an enterprise environment • 2.7 Explain the importance of physical security controls • 5.3 Explain the importance of policies to organizational security • 5.5 Explain privacy and sensitive data concepts in relation to security IT security professionals protect data. Proprietary data is the lifeblood of many companies. Those companies put a premium on securing that data (Figure 1-23). The complexity of data security presents a challenge to IT security professionals. Data manifests throughout an infrastructure in many ways: from a single user’s personal folders containing a few Word documents to massive multiterabyte databases, accessed by hundreds or even thousands of users. The complexity of access and control of data adds another challenge to IT security professionals. Every database program, every operating system, and many Internet services offer settings that give administrators impressively fine control when configuring which users and groups may access specific classes of data and what they are permitted to do with that data. But how do we control that access? How do we look at the data and determine the amount of access any given entity receives? We’ll answer these questions in Chapter 3. Handling certain types of data involves serious legal and privacy issues. Organizations need to protect data aggressively. If your databases contain individuals’ private medical information, customers’ personal credit card numbers, or even a young offender’s rap sheet, you are under tremendous pressure to maintain that privacy (Figure 1-24). This module covers the basics of data security and privacy. The module starts by covering common methods of data organization, then delves into legal compliance and privacy. We’ll look at tried and true methods for data destruction. The module closes by covering privacy breaches. Figure 1-23 Data is precious. I’ll keep you safe! Our Data 01-ch01.indd 47 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 48 Figure 1-24 Storing personal data brings heavy responsibilities. Dating Habits Personal data MUST stay private! Arrest Records Lab Results Organizing Data Attaining data security starts with organization. Analyze individual chunks of data, such as databases, spreadsheets, access control lists, and so on. Then determine the importance—the sensitivity—of that data. After accomplishing both tasks, sort the data into different classifications based on sensitivity. These classifications help security professionals to determine the amount of security control to apply to each data set. The dynamic nature of data requires more than just classification of the data. Every data set needs to be administered by one or more people. The roles of the people who manage the data and the users who access that data need classification as well. NOTE The NIST Federal Information Processing Standards (FIPS) Publication 199, Standards for Security Categorization of Federal Information and Information Systems, is considered by many sources as the de facto framework for IT data classification. Data Sensitivity IT security professionals need to apply appropriate security controls to data, making decisions based on the sensitivity of that data. Organizations can apply a dizzyingly large number of security controls to data. Some data sets need stringent security controls. Other data sets need less complex security controls. Not all data in an organization has the same sensitivity. The more sensitive the data, the more controls we apply to ensure its security. Organizations spend a lot of time thinking about their data and coming up with classifications to enable them to identify the sensitivity to in turn address their handling. One way to consider sensitivity is by the impact of an incident that exposes the data. NIST FIPS 199 provides one way to consider the impact by looking at the confidentiality, integrity, and availability (CIA) of the data and breaking the impact into three levels: low, moderate, and high (Figure 1-25). It’s also very common to differentiate between commercial and government/military to classify data. 01-ch01.indd 48 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 49 Figure 1-25 Impact table for data (FIPS 199) Commercial Classifications Classifying data using commercial labels works well for most private-sector organizations. Most security pros in the nongovernmental sector start with some variation of the following list: • Public Information that is not sensitive. The prices of all the products on eBay is one example. Private Information that specifically applies to an individual, such as a Social Security number. • Sensitive A generic label that is often tied to both commercial and government/ military label types. • Confidential Information that one party offers to a second party. Usually secured via a non-disclosure agreement (NDA). A common example is internal company information used by its employees. 01-ch01.indd 49 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 50 • Critical Data without which an organization could not function or fulfil its essential mission. • Proprietary Information owned by a company that gives the company certain competitive advantages. The secret formula to Coca-Cola is an example. • Customer data Information about the customer, such as personally identifiable information and personal health information (covered later in this module). NOTE Public information may not have confidentiality, but it still needs integrity and availability. Government/Military Labels If you enjoy spy novels, most government/military labels should sound familiar. In fact, these types of labels predate computers to a time when paper documents literally had physical labels (or stamps) signifying their sensitivity. Experts disagree on exactly what these labels mean, although not as much as with commercial labels. Here in the United States, security professionals refer to Executive Order 13526 of December 29, 2009, “Classified National Security Information,” which defines the labels for government data—property of the government—as follows: • “Top Secret” shall be applied to information, the unauthorized disclosure of which reasonably could be expected to cause exceptionally grave damage to the national security that the original classification authority is able to identify or describe. • “Secret” shall be applied to information, the unauthorized disclosure of which reasonably could be expected to cause serious damage to national security that the original classification authority is able to identify or describe. • “Confidential” shall be applied to information, the unauthorized disclosure of which reasonably could be expected to cause damage to the national security that the original classification authority is able to identify or describe. Data Roles Every data set needs some number of people with clearly defined roles who manage that data at various levels. Data roles help define both the various responsibilities and the responsible parties for the different jobs. Let’s go through the data roles listed by the CompTIA Security+ exam objectives. Data Owner The data owner is the entity who holds the legal ownership of a data set. This includes any copyrights, trademarks, or other legal possession items that tie the data set to the entity. The data owner can rent, sell, or give away the data set as the owner sees fit. Data owners are almost always the organization itself and not an actual person. This entity has complete control over the data and will delegate responsibility for the management of that data set to persons or groups to handle the real work on that data. 01-ch01.indd 50 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 51 Data Controller The General Data Protection Regulation (GDPR) in the European Union outlines in great detail how organizations should deal with private information. GDPR went into force in 2018 and includes a few roles added to the traditional ones, notably the data controller and data processor. Many countries have subsequently adopted similar regulations, so, naturally, many multinational corporations comply with those regulations throughout their organizations. A data controller controls the data, which sounds silly, but means the person must ensure that data complies with the protections of personally identifiable information (PII) thoroughly, according to the regulations in the GDPR. The data controller must create systems about data processing and report on them as well. Data Processor A data processor in GDPR parlance doesn’t have as much control over the data as a data controller. The data processor essentially works under the guidance of the data controller, handling data according to the controller’s guidelines. Data Custodian A data custodian ensures that the technical aspects of the data set are in good order. Data custodians are the folks who make sure the data is secure, available, and accurate. They audit the data and ensure they have both the appropriate storage capacity and proper backups. Data Steward A data steward makes sure that the data set does what the data is supposed to do for the organization. Data stewards interface with the users of the organization to ensure data governance: to cover data requirements, to ensure legal compliance, and to make sure the data ties to company or industry standards. Data stewards update the data as needed to conform to needs. Data stewards also define how users access the data. NOTE Data stewards and data custodians always closely interact. Data Protection Officer The GDPR requires organizations to staff the role of data protection officer (DPO), a leadership role responsible for making sure the enterprise complies with GDPR rules. Specifically, the DPO oversees an organization’s policies and procedures for protection of data. Legal and Compliance Most countries have laws, regulations, and standards designed to protect different forms of data. As introduced in Module 1-2, in the United States, the Health Insurance Portability and Accountability Act (HIPAA) and Sarbanes-Oxley Act (SOX) provide strict federal guidelines for the handling, storage, and transmission of data. In addition, the Payment Card Industry Data Security Standard (PCI DSS), while not a law, has equally stringent guidelines for the handling, storage, and transmission of credit card data. In all these cases, the job of IT security changes from securing the IT infrastructure to making sure the organization doesn’t get fined (and no one gets arrested!) for lack of compliance. 01-ch01.indd 51 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 52 Many companies use digital rights management (DRM) technologies to protect their intellectual property, methods to stop easy copying (and redistributing) of music, movies, and so on. Many governments, in turn, supplement these efforts with laws criminalizing tampering with or circumventing the DRM technologies, such as the Digital Millennium Copyright Act (DMCA) in the United States. NOTE The US government has levied millions in fines and has imprisoned individuals for violations of both HIPAA and SOX. Credit card companies have revoked credit card processing from a huge number of businesses for failure to comply with PCI DSS standards. Rather than break down these individual laws/standards, it’s often better to concentrate on some of the more important aspects. Focus on personally identifiable information, protected health information, data retention, and data sovereignty. Personally Identifiable Information Personally identifiable information (PII) is any information referencing an individual that either by itself or with other information could identify that individual, allowing persons to contact or locate that individual without their permission. The idea of PII has been around since the early 1970s, but came into stronger prominence with HIPAA in the mid-1990s. PII is also very important for PCI DSS. While there is no single definition of PII, NIST SP 800-122, Guide to Protecting the Confidentiality of Personally Identifiable Information (PII), (Figure 1-26) provides many examples: • Name, such as full name, maiden name, mother’s maiden name, or alias • Personal identification numbers, such as Social Security number (SSN), passport number, driver’s license number, taxpayer identification number, or financial account or credit card number • Address information, such as street address or e-mail address • Personal characteristics, including photographic image (especially of face or other identifying characteristic), fingerprints, handwriting, or other biometric data (e.g., retina scan, voice signature, facial geometry) • Information about an individual that is linked or linkable to one of the above (e.g., date of birth, place of birth, race, religion, weight, activities, geographical indicators, employment information, medical information, education information, financial information) Different laws and standards vary the definition of what entails PII. For example, here are a few examples of PII by PCI DSS standards: • Account number • Cardholder name 01-ch01.indd 52 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 53 Figure 1-26 NIST SP 800-122 • • • • Expiration date Magnetic strip or chip data PIN CVC2/CVV2/CID Protected Health Information Protected health information (PHI) is any form of personal health information (treatment, diagnosis, prescriptions, etc.) electronically stored or transmitted by any health provider, insurer, or employer. This health information must be tied to the individual’s PII to be considered PHI. In other words, a blood pressure reading combined with age and race is alone not PHI. A blood pressure reading combined with a name, address, or SSN is PHI. Financial Information Personal financial information is any information that provides insight into an individual’s finances. This includes bank account numbers, credit scores, or user name and login information for electronic payment applications. Privacy Enhancing Technologies Consider the types of PII and PHI just described and ask yourself, “What types of organization might store this type of data?” The answer is that PII/PHI exists everywhere! 01-ch01.indd 53 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 54 Hospitals, doctors’ offices, and governments all store health information. Banks and financial institutions store financial information. Every store and e-commerce site stores customer data, and only the government knows how much PII it keeps on you. There are plenty of privacy enhancing tools out there to help organizations protect PII/PHI. Let’s look at some of the more common ways used to secure this type of data from potential exposure. Terms of Agreement/Privacy Notice If you’re going to use someone’s PII/PHI, you should tell them what you’re doing with it and how you’re going to keep their data private. Terms of agreement inform parties that your organization will be asking for and storing personal information. A privacy notice informs the person about how you will (or in some cases will not) keep their data private. Anyone who’s ever clicked through one of those screens on a Web page that has “I agree” on the bottom has dealt with a privacy notice (Figure 1-27). Data Minimization Why keep something you don’t need? Data minimization is just like it sounds—only keeping the minimum PII/PHI for you to get the job done. This reduces both the data contents and the amount of time the data is kept. Data Masking Data masking is the process of hiding original data with modified content, such as using asterisks to hide all but the last four digits of a credit card number. Tokenization Why send around sensitive data like a credit card number when you can replace it with a random value, or token, that’s only known by a single source to tie Figure 1-27 Terms of Agreement 01-ch01.indd 54 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 55 back to the actual number? Data tokenization is extremely common. For example, once a patient’s record is stored in a database, just assign a patient number to that record so things like name and address don’t have to be associated with that patient number. Anonymization There’s a lot of useful information that comes from PII/PHI that doesn’t require actually identifying the people whose information is part of the data set. How many people in Houston, Texas, are morbidly obese? What’s the average age for women in the United States to have their first child? How many complaints came in last month about our new smartphone app? These types of statistics are very helpful, but it’s up to the data set provider to ensure that no PII/PHI is retrieved by implementing anonymization of the data. TIP Anonymization removes all PII/PHI. Pseudoanonymization tokenizes the PII/PHI. Sometimes the process of extracting anonymous data from a PII data set creates problems—or worse yet might accidently allow exposure of PII. One way to avoid this issue is to create a second data set and replace all PII with token data that looks random. This is called pseudoanonymization. Data Retention A number of laws and regulations have strict requirements regarding how long types of organizations must retain different types of data. Data retention is part of the information life cycle. The Sarbanes-Oxley Act is easily the most far-reaching law affecting the types of data public companies must retain and the length of time they must retain that data. In particular, IT departments must react to two parts of the law covered in Section 802(a): Whoever knowingly alters, destroys, mutilates, conceals, covers up, falsifies, or makes a false entry in any record, document, or tangible object with the intent to impede, obstruct, or influence the investigation … shall be fined under this title, imprisoned not more than 20 years, or both. Yipe! But at least it also gives some idea as to the length of time companies need to retain records: Any accountant who conducts an audit of an issuer of securities … shall maintain all audit or review workpapers for a period of 5 years from the end of the fiscal period in which the audit or review was concluded. It’s not that hard to keep contracts, accounts, audits, and such for five years, but this also includes e-mail. Managing and storing e-mail for an entire company can be a challenge, especially because e-mail is usually under the control of individual users (ever deleted an e-mail?). SOX alone changed everything, requiring publicly traded companies to adopt standard practices outlined in the law and making lots of storage providers very happy indeed! 01-ch01.indd 55 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 56 EXAM TIP The information life cycle is generally understood to have five phases, from creation to storage, usage, archival, and then destruction. Data retention falls into cycles two and four. We’ll see cycle five a little later in this module. Data Sovereignty Governments have laws in place to give them access to data. That data could help solve crimes, protect people, and so on; and the desire for access is clear. The question that begs in a world of multinational corporations and cloud computing as the normal way to store data is, which laws apply to data stored in which countries? Let’s explore this through a scenario. Microsoft has servers based in Ireland. Some e-mail accounts hosted on those servers belong to people who might have committed crimes in the United States. Microsoft Corporation is a US-based company. If the US government decides that it needs access to those e-mail account records, which US law or laws permit such access, and what can or should Microsoft do in response? The concept of data sovereignty determines that the laws of the country of origin of data apply to that data. The e-mail accounts hosted by a server in Ireland (an EU member nation), therefore, must abide by—and are protected by—EU laws, not US laws. This isn’t just a hypothetical scenario, by the way. Microsoft argued and won against the US government that US laws did not apply to its Ireland-based holdings. Data Destruction When it’s time to get rid of storage media, you should also destroy the data stored on that media. But how do you destroy media in such a way to ensure the data is gone? Let’s take a moment to talk about secure data destruction/media sanitization. NIST SP 800-88, Rev. 1, Guidelines for Media Sanitization, provides some great guidelines (Figure 1-28). Figure 1-28 NIST SP 800-88, Rev. 1 01-ch01.indd 56 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 57 The CompTIA Security+ exam covers a number of different data destruction methods that apply to specific types of data. Stored data fits into one of two categories: legacy media (paper, film, tape, etc.) or electronic media (hard drives, SD cards, optical media, etc.). Each category has different methods for data destruction. NOTE The terms data destruction, data sanitization, and data purging are interchangeable. Legacy Media Given that most legacy media isn’t completely erasable, the best way to eliminate the data is to destroy the media. Paper, film, and tape are all extremely flammable, so burning is an excellent method to destroy the data. For “greener” organizations, pulping water-soluble media (paper) enables them to recycle the media and not pollute the environment. Electronic Media Almost all electronic media is erasable, so in many cases you can nondestructively remove the data. Simple erasing, however, even reformatting, isn’t enough. A good forensic examiner can recover the original data from a hard disk that’s been erased as many as nine times. You need to go through a specific wiping process that removes any residual data. NIST SP 800-88, Rev. 1, describes the ATA Secure Erase command built into PATA and SATA drives. Third-party solutions can help here. Several programs can perform a secure erase. Figure 1-29 shows DBAN 2.3.0 (Darik’s Boot and Nuke), a popular secure erase utility (and it’s free!). Figure 1-29 DBAN 2.3.0 (Darik’s Boot and Nuke) 01-ch01.indd 57 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 58 To ensure complete data destruction, destroy the media. A common method is degaussing the media through a degaussing machine. A degausser uses a powerful electromagnet both to wipe the data and make the media useless. Pulverizing or shredding are great methods for destroying media as well. Pulverizing means to smash completely. Shredding works for both legacy media and electronic media. A classic shredder can shred paper, optical media, and many types of flash media. There are several types of shredding cuts (Figure 1-30). Shredding doesn’t stop with paper! There are machines available that shred (or pulverize, or crush) just about any media, reducing them to bits of metal for you to recycle. You’ll see those machines, and much more about data sanitizing, in Chapter 5, Module 5-7. Privacy Breaches We talked about data breaches back in Module 1-5 and the reputational and financial impact to an organization. Organizational consequences of privacy and data breaches involving PII or PHI have a whole order of magnitude more impact. You’ve likely heard of data breaches of health insurance companies, dating Web sites, and other hosts of PII and PHI. These breaches have led to horrific reputational damage, identity theft of customers, intellectual property stolen (IP theft), civil court cases with massive fines . . . and in a few cases, people going to jail. The serious consequences of privacy breaches like these require organizations to address any incidents quickly and aggressively. First, organizations that are subject to industry or governmental regulations, such as PCI, HIPAA, and so on, are required to escalate these incidents by reporting to the proper government agencies. These regulations are important. Before they came into force, organizations would try to hide privacy breaches or even deny they happened at all. Last, organizations, through moral or legal reasons, should provide public notification and disclosure of the type of data exposed to lessen reputational damage and avoid legal actions based on failure to disclose. An organization should not only make a public notification of the breach, they also should make a best attempt to inform those affected. Web sites such as https://haveibeenpwned.com, for example, provide the public with easy access to determine if an e-mail address has been breached. EXAM TIP Expect a question on the CompTIA Security+ exam that asks about proper company response to breaches and private or sensitive data loss. The organization must provide notification of breaches to customers, escalation of response to government agencies, and public notifications. 01-ch01.indd 58 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-6: Data Security and Data Protection 59 Figure 1-30 Shredded drive 01-ch01.indd 59 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 60 Module 1-7: Personnel Risk and Policies This module covers the following CompTIA Security+ objective: • 5.3 Explain the importance of policies to organizational security An organization’s users—the human beings who perform their jobs every day by using the resources of the organization’s IT infrastructure—are also one of the biggest IT risk issues faced by security professionals. Human actions, from accidental to innocent, from incompetent to downright criminal, keep security pros awake at night in fear and loathing. But it doesn’t have to be that way. A well-organized risk management plan includes detailed policies that define security controls to mitigate risk brought on by personnel. This module explores the lifespan of an employee’s relationship with an organization, from hiring day to exit day, and examines the risk concepts and security controls used to keep users from trashing the place. Specifically, the module starts with hiring and onboarding, then goes into detail on personnel management policies. The module wraps up with discussions about user training and policies that apply to user habits. NOTE Policies in and of themselves do not provide security. Well-designed policies implemented and followed diligently by users can provide security. What people do matters a whole lot. Hiring Personnel risk management starts before the new employee ever steps into the infrastructure. In today’s security-conscious environment, a potential new hire is screened heavily. At the very least, it’s common for someone in an organization to do a social media analysis—checking Facebook or Instagram (or the current flavor of the day) for behavior that doesn’t fit the company’s values—and a general Web search. Many organizations perform background checks to look for potential issues, such as felony convictions, and to verify résumé statements. Any company with substantial intellectual property will require new employees—and occasionally even potential candidates—to sign a non-disclosure agreement (NDA), a legal document that prohibits the signer from disclosing any company secrets learned as a part of his or her job. Onboarding Onboarding is the process of giving a new hire the knowledge and skills he or she needs to do the job, while at the same time defining the behaviors expected of the new hire within the corporate culture. A lot of onboarding has nothing to do with IT security, but some part of the process usually is dedicated to helping new hires understand the expectations 01-ch01.indd 60 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-7: Personnel Risk and Policies 61 and attitudes toward IT security that are important to the organization. One of the biggest issues is their understanding of the organization’s personnel management policies. You can’t be on Facebook all day. Just sayin. . . New kid! Onboa rd talk That Onboarding Moment Personnel Management Policies A personnel management policy defines the way a user works within the organization. An organization will invest in one or more personnel management policies to help mitigate a number of different types of personnel risks. Let’s go through all of these personnel management policies to see how they work to make an infrastructure less vulnerable to risks. Standard Operating Procedures An important part of the onboarding process is making sure new hires understand the standard operating procedures (SOPs)—that is, how they do things according to the organization’s best practices—for their job functions. Some SOPs that are particularly important for IT security include login procedures, usable data storage locations, use of security credentials, and procedures for lost or damaged equipment. No, seriously. Social media is out. Right out. New kid! S.O.P. Necessary Knowledge Mandatory Vacations Many industries (for example, the US banking industry) require all employees to take off work for a minimum of two weeks every year, a mandatory vacation. Mandatory vacations are an important security control mainly to make it harder to perpetuate embezzlement. 01-ch01.indd 61 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 62 Any embezzlement scheme usually requires the embezzler to monitor orders constantly, manipulate records, or deal with issues that might arise to keep themselves from being detected. NOTE Mandatory vacations have benefits beyond IT security, but for the exam think “embezzlement.” Job Rotation Job rotation involves periodically switching people around to work in different positions. This practice enables different people to become proficient in a variety of job roles so that the organization doesn’t have to depend solely on one person to perform certain critical functions or tasks. If something were to happen to an individual occupying a critical position, for example, another person could step in to do the job. When people become too comfortable with a job, they might believe that they can get away with performing actions they are not authorized to perform. Rotating people into different positions increases the potential to detect fraud or misuse in that position and can discourage or prevent nefarious activities. Job rotation is difficult for many organizations, for the same reasons that organizations don’t always implement mandatory vacations. A shortage of trained personnel as well as positions that require substantial training and commitment are two reasons why job rotation isn’t always performed. Separation of Duties In the separation of duties concept, a single individual should not perform all critical or privileged-level duties. These types of important duties must be separated or divided among several individuals. Separation of duties ensures that no single individual can perform sufficiently critical or privileged actions that could seriously damage a system, operation, or the organization. These critical or privileged actions can be split among two or more people, requiring some level of checks and balances. Security auditors responsible for reviewing security logs, for example, should not necessarily have administrative rights over systems. Likewise, a security administrator should not have the capability to review or alter logs, because he or she could perform unauthorized actions and then delete any trace of them from the logs. Two separate individuals are required to perform such activities to ensure verifiability and traceability. Separation of duties is considered an administrative control, because it’s related to policy. Closely related to the concept of separation of duties is the technique of using multiperson control to perform some tasks or functions. NOTE A related concept to separation of duties is the principle of least privilege—don’t give people access to anything beyond what they need to accomplish their jobs. CompTIA adds least privilege as a personnel policy, but it’s more of a principle. You’ll find more discussion in Chapter 3. 01-ch01.indd 62 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-7: Personnel Risk and Policies 63 Multiperson Control Multiperson control means that more than one person is required to accomplish a specific task or function. An organization might implement multiperson controls, for example, to ensure that one person, by herself, could not initiate an action that would cause detrimental consequences for the organization, resulting in loss of data, destruction of systems, or theft. Organizations implement multiperson control by dividing up critical tasks to require more than one person to accomplish those tasks. In a banking environment, for example, one person may be authorized to sign negotiable instruments, such as checks, for up to $10,000. Beyond the limit of $10,000, however, requires two signatures to process the transaction. This would help prevent one malicious person from stealing more than $10,000. Although it’s conceivable that two people could conspire to use their assigned abilities to commit an unauthorized act, fraud in this case, separation of duties and multiperson control make this more difficult. In this case, counter-signing a check is a multiperson control. In an information security environment, multiperson control could be used to access sensitive documents, recover passwords or encryption keys, and so on. Training User training should take place at two very distinct points in the user’s relationship with an organization: during the onboarding process to get the new hire to understand and subscribe to critical policies and good user habits and, possibly even more importantly, as an ongoing continuing-education process. Let’s look at role-based training and various training techniques. NOTE Just as policies do not achieve security if they are not implemented, training does not achieve security if its lessons aren’t implemented. Users need ongoing, memorable training, because people forget details over time or, worse, choose not to follow best practices because they’re too hard. Training requires enforcement to make it stick. Role-Based Training User training differs according to the role an individual plays in an organization. Rolebased training targets five broad categories: user, privileged user, executive user, system administrator, and data owner/system owner. Let’s look at all five. User A user must understand how his or her system functions and have proper security training to recognize common issues (malware, unauthorized user at his or her system, etc.). Privileged User A privileged user has increased access and control over a system, including access to tools unavailable to regular users. Like a regular user, the privileged user needs a basic understanding of his or her system’s functions; the privileged user must also have security awareness that ties to access level. A regular user may run anti-malware software, for example, but a privileged user may update the anti-malware program as well as run it. 01-ch01.indd 63 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 64 Executive User An executive user concentrates on strategic decisions including policy review, incident response, and disaster recovery. System Administrator The system administrator has complete, direct control over a system. His or her training would include best practices for adding and removing users, applying permissions, and doing system maintenance and debugging. Data Owner/System Owner From a role-based training aspect, these two otherwise slightly different functions are very similar in that in almost all cases the data owner is the organization. In these cases, the main security role here is to know how to delegate security awareness to the proper authority. For data, this is usually the data custodian; for systems, it is usually the system administrator. Training Techniques Ongoing user training is critical to keep users aware of potential attacks on the organization’s infrastructure. The downside of ongoing training is that it can get very, very boring, and users will tune out or ignore the training. Thus, keeping users’ attention requires incorporating a diversity of training techniques. Change those PowerPoint presentations into videos. Change those videos into games. Change those instructional memos into classroom training. With computer-based training (CBT) these days, it’s easy to provide diversity in training. Gamification Gamification turns learning about security into games. The term encompasses a wide variety of activities, from tablet-based mini games to full-on competitions among users that feature points, badges, a leaderboard, and more. Capture the Flag Capture the flag means to direct someone to accomplish something on a remote system. For training purposes, we can challenge entry-level security personnel to apply what they’ve learned in a controlled environment. It’s fun to talk about SQL injections or cross-site scripting, but it really lights people up the first time you let them do these attacks. (And it’s best if the attacks don’t actually destroy your network or someone else’s network.) See Modules 7-1, 11-3, and 12-2 in later chapters for discussion of specific cyberattacks. Phishing Campaigns Phishing attacks represent the greatest threat to company security that involves users specifically. Phishing is an attempt to get personal information from people through e-mail, social media, instant messaging, and other forms of electronic communications. The most classic form of phishing is sending e-mail messages with links to fraudulent Web sites that purport to be legitimate Web sites. It might look like a message from your bank, but that “link” goes to the fraudulent Web site to grab your information. The best way to create user awareness about phishing is through an in-house phishing campaign. Send out e-mail messages to your users and see just how many of them go to the fraudulent Web site you’ve created. Phishing campaigns are a way to see who needs training. Not comfortable making a phishing campaign from scratch? Plenty of vendors sell software packages or Web sites for phishing simulations. 01-ch01.indd 64 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-7: Personnel Risk and Policies 65 Policies If people are going to use your organization’s equipment, they need to read, understand, and, in most cases, sign policies that directly affect the user’s experience. Two policy types handle this job: acceptable use policies and security policies. Acceptable Use Policy/Rules of Behavior Policy An acceptable use policy (AUP), also called a rules of behavior policy, defines what a user may or may not do on the organization’s equipment. These policies tend to be very detailed documents, carefully listing what users may and may not do. Some examples of issues covered in an AUP include • • • • Company data can only be used for company business uses. Users will not access illegal or unacceptable Internet sites. Users will not introduce malware into a system. Users will work aggressively to protect company systems and data. General Security Policies People use social media networks and personal e-mail to exchange information and photographs and keep in touch with family members and friends. Unfortunately, some people post way too much information on social media networks and through social media applications—hello, Snapchat—decreasing their (and others’) level of privacy. Although organizations may have very little control over what individual employees post to social media sites and send in their e-mail, it’s a good idea to create a relevant policy and train users on what they should and should not post on social media or e-mail to others. For example, users should be briefed that they should not post any sensitive or proprietary information on their social media sites that would compromise the organization or result in any type of unauthorized access or breach of information. User Habits In addition to policy-related topics, topics that concern the actions and habits of users must be addressed in training programs. Many such items will also be set forth in policy, but that doesn’t mean that users don’t need training and reinforcement to break bad habits where they exist. We’ll look at some of these bad habits in the next few sections and, where appropriate, discuss how they also may be established in policy and why they should be included in any organizational information security training program. Password Behaviors By now, you should be aware that password issues can pose serious problems in an organization. Users forget passwords, write them down where they can be easily discovered by others, share passwords, use simple passwords, and so on. These are the causes of most password security issues, and the reasons why users need training regarding how 01-ch01.indd 65 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 66 to create and use passwords properly in the organization. Following are some key points that should be emphasized: • • • • • Users should create long passwords. Users should create complex passwords. Users must try to create passwords that don’t use dictionary words. Users should never share their passwords or write them down. Users should change their passwords often to thwart password attacks. Of course, you should also use technical measures to reinforce some of these rules, including configuring systems to allow only complex passwords of a certain length, as well as password expiration rules. Periodically check around the users’ work areas to make sure they haven’t written down passwords, and ensure that multiple people aren’t using the same accounts and passwords to log into systems. In addition, check to see if your password policies are being complied with by occasionally engaging in password cracking yourself—with the appropriate approval from management, of course. The problems associated with password behaviors, as well as the speed and ease with which passwords can be cracked by sophisticated attackers and systems, are the main reasons why organizations should consider multifactor authentication methods. (Check out Chapter 3, Module 3-2 for more details on multifactor authentication.) Clean Desk Policies A clean desk space policy isn’t about asking employees not to leave old soda cans and candy wrappers on their desks! Instead, it creates a process for employees to clear sensitive data out of work areas so that it is stored securely at the end of the workday. Sensitive data must not be exposed to unauthorized people such as janitors, maintenance personnel, guards, and even other employees when an authorized employee is away from his or her desk. A clean desk policy can apply to any time employees are using sensitive data at their desks and they need to leave the area. The goal is to make sure that sensitive data is not unattended and available. This policy should be developed and implemented as a formal written policy, and all employees should be trained on it. Preventing Social Engineering Attacks Users should be briefed on the general concepts of social engineering and how it works, and they should also be briefed on the specific types of attacks they may encounter, such as shoulder surfing, tailgating, dumpster diving, and so on. By being aware of these attacks, they can do their part in helping to prevent them. Tailgating, in particular, exposes the organization and others to serious harm or danger if an unauthorized person is allowed to enter the facility. Users should be trained on how to spot potential social engineering attacks, including tailgaters, and how to respond to them by following organizational policies and procedures. 01-ch01.indd 66 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-7: Personnel Risk and Policies 67 Personally Owned Devices Users should get training on risks posed by bringing personally owned devices to work and how they might help prevent these risks. Using such devices in the organization can lead to a loss of privacy by the individual, as well as loss of both personal and organizational data if the device is lost or stolen. If the organization allows individuals to manage their own devices, while allowing their use in the organization to process the organization’s data, then the organization incurs a huge risk. Users must be trained on those risks and how serious their responsibilities are. If the organization centrally manages mobile devices with mobile device management (MDM) software, the risk is significantly lowered because the organization can use remote capabilities to lock, encrypt, or wipe data on the device. Users should be briefed on these capabilities if they are used within the organization to manage devices, because users must accept organizational control of their devices and the policies that may be enforced on them. Many companies around the globe have clear policies on bring your own device (BYOD), the catchy phrase for incorporating employee-owned technology (such as laptops, tablets, and smartphones) in the corporate network. As the trend intensifies, just about every organization should have such policies. Offboarding When employees leave an organization, the organization must perform a number of important steps to ensure a tidy and professional separation. This process, called offboarding, varies among organizations, but includes several common steps: • Termination letter • Equipment return • Knowledge transfer Termination Letter/Exit Interview An employee should provide a written termination letter, defining the final day of employment. In many organizations, this is also the time to perform an exit interview. Exit interviews give the soon-to-be-separated employee an opportunity to provide insight to the employer about ways to improve the organization. Some example questions include • What are your main reasons for leaving? • What procedures can we improve upon? Return of Equipment All organizations should use a checklist to ensure that all equipment owned by the organization is returned by the departing employee. This includes computers, phones, and tablets, as well as any other issued equipment. Also, this is the time to return keys, ID cards, and other access tools. 01-ch01.indd 67 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 68 Knowledge Transfer Knowledge transfer is the process that makes sure a separating employee provides any and all knowledge needed by the organization. In some cases knowledge transfer may last weeks. In other cases it’s no more than part of the exit interview. Module 1-8: Third-Party Risk and Policies This module covers the following CompTIA Security+ objectives: • 1.6 Explain the security concerns associated with various types of vulnerabilities • 5.3 Explain the importance of policies to organizational security Every organization interacts with third parties. Every infrastructure has vendors, contractors, business-to-business (B2B) intranets, partnerships, service providers—the list of third parties touching an infrastructure in one way or another is endless. The challenge with all these third parties is risk. For example, in 2019, two Facebook apps— developed by third parties that interact with Facebook—gashed out over 500 million personal records in hacks. Those records included usernames, groups, passwords, likes, movies, photos, music, and much more. Home Depot in 2014 had over 50 million customer credit card numbers stolen by a hack of its third-party payment systems. This list can go on for a very long time. What can IT security professionals do to mitigate risks potentially created by those outside the infrastructure? General security practices hold third parties to certain levels of security through several types of agreements (Figure 1-31). This module considers the concept of third-party risk and risk management and then looks at some of the more common types of agreements used between parties. Third-Party Risk Management If your organization works with vendors, then it must use vendor management, the process of handling everything from selecting vendors and negotiating contracts or agreements with them to eventually terminating those vendor relationships. Vendor management is critically important when it comes to IT security. Figure 1-31 It’s all in the agreement. 01-ch01.indd 68 Agreement 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-8: Third-Party Risk and Policies 69 It’s said that the devil is in the details; this is definitely true when it comes to security considerations that involve multiple parties. When you negotiate a contract with a third-party provider or business partner, you must ensure that several considerations are specified in your business agreements. You should have representatives from your security, privacy, and legal departments review any business agreements with third parties to ensure that certain security-related stipulations are included in the agreements and the day-to-day business transactions with outside entities. Let’s look at a few of these security considerations next. Data Storage Whether it’s a supplier accessing your inventory databases or a group of programmers creating your next great Web app, vendors will need to access data stored on your organization’s systems directly or store your organization’s data on their own systems. Controls over data storage must match the same level regardless of whether your organization or the third party maintains that data. Just as your organization has its own security policies, procedures, and processes, thirdparty organizations have their own as well. Before your organization conducts business with another organization, the two parties need to negotiate how to handle any conflicts between their respective policies, procedures, and processes regarding data storage that might affect the business relationship. In some cases, contract agreements may specify security policies and procedures that both parties must follow regarding shared data or contracted services. This applies to all third parties: software developers, service providers, business associates, subcontractors, and so on. Security policies and procedures agreed upon in advance ensure that external entities protect your organization’s data to the level your organization would protect the data internally. Data Privacy Considerations Your organization must ensure privacy when exchanging data with any third party. If you contract services with a third party, make sure to agree on data privacy safeguards prior to entering into any business agreements. Privacy considerations include employee data privacy; privacy related to the type of data itself, such as financial data, personally identifiable information (PII), and protected health information (PHI); and how the third party will treat this data. Legal or regulatory governance may provide you some protection, in that the third party has to obey laws with regard to data privacy, but you may find that your organization has additional requirements that need to be met by the third party. It’s also possible that the agreement could be too restrictive in favor of the service provider, and your organization requires more flexible terms to ensure data privacy to your standards. In any case, ensure to specify in any agreements made between your organization and a third-party provider or business associate how to handle private data, including how it is stored, processed, accessed, and especially transmitted to other third parties. For example, the HIPAA security regulations require that any third-party providers (referred to as “business associates” in HIPAA parlance) that could possibly have access to PHI be subjected to strict access control and handling requirements for that type of data. 01-ch01.indd 69 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 70 Unauthorized Data Sharing Security policies set forth in third-party agreements should cover unauthorized data sharing and access control. In addition to setting forth minimum requirements for access control, which include administrative, technical, and operational controls, the agreement should set forth mechanisms that an organization must use in order to share data with other authorized parties, as well as conditions under which the third party must comply with the law in sharing data with government and law enforcement agencies. The agreement should also cover how the organizations will respond in the event of a data breach or unauthorized access. Last, the agreement specifies who is liable for any fines or damages stemming from unauthorized data sharing. Data Ownership Organizations must define the types of data to which they claim ownership initially and how they would classify that data in terms of its sensitivity and protection requirements. The organizations must also determine how they will decide on ownership of data that is created during the contract term and who will control it. Some third parties that process data for an organization specifically agree that any data created during the contract term still belongs to the originating organization, but other third-party providers may maintain that they have legal ownership over any data that is created on their systems, based upon their unique processes or proprietary methods. This issue must be resolved prior to engaging in business with a third party. Issues with data ownership can lead to disputes over copyrights and patents, as well as unauthorized disclosure issues between two parties that both claim to own the data produced. Supply Chain Concerns Ensuring the security of supply chains—equipment, software, online services that collectively make products happen—requires proactive measures. IT security folks conduct supply chain assessments to ensure the availability of those critical components, to secure alternative processes, and to verify the security of data. Two important aspects of supply chain assessment are end of life (EOL) and end of service life (EOSL). These two terms are similar but have important, if subtle, differences. All products have a life cycle. Software versions are abandoned after a new version comes out. When a software or hardware vendor releases a new version of its product, it abandons any effort to update, market, or sell the prior version. Vendors must let us know when a product reaches the end of its life. A lack of vendor support clearly marks a risk in dealing with third parties. A vendor releases an EOL to inform its customers that it will no longer sell a particular product, although the vendor may provide upgrades, patches, or maintenance. End of service life marks the moment that an organization stops supporting a product. Microsoft might continue to provide updates and security patches for Windows 8.1, for example, but Highland Gadgets Corporation no longer provides support for operating systems older than Windows 10. The latter enterprise therefore announces the EOSL for Windows 8.1. 01-ch01.indd 70 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-8: Third-Party Risk and Policies 71 System Integration There are many situations where two organizations might find it beneficial to perform many types of system integration, linking or matching networks, software, security, services, and so forth. To share data securely, for example, a third-party vendor might integrate its domain to your Active Directory forest and then create trust relationships. System integration comes with all the risks of any single system. Users from the third party must be created with proper passwords. Both parties must use careful trust relationships to make sure no one has access to the other’s data and resources unless needed. Third-party systems need acceptable anti-malware … this list goes on and on! Measurement Systems Analysis Having systems in place to test or check production and services provides necessary data about third-party contributions to the organization. Measurement systems analysis (MSA) tests the accuracy of those systems and data collection using math. As an example of how MSA is helpful in managing third-party risk, a supply-chain supervisor gets complaints that some part coming from Source Alpha seems to be causing all sorts of problems with the end product. The supervisor checks production and finds that Source Alpha follows every guideline for production to the letter. What could cause the problem? If the calibration or measurements used for production were off by just a little, the end product could be off by a lot. MSA checks the accuracy of the measurements to discover errors. Agreement Types When your organization enters into any type of business partnership or agreement with a third-party business partner or service provider, the agreements and contract documents created serve to protect both organizations from a legal perspective as well as establish the terms of the business relationship. You’ll need to be familiar with several types of documents for the exam, covering various aspects of data protection, interoperability, interconnection, and so on. They basically define the interoperability relationship between the two (and sometimes more) parties. Obviously, these types of agreements will be negotiated by the business contracting and legal personnel in each organization, but advice and input should also come from other affected functions within the businesses, such as security, privacy, IT support, and so on. Let’s take a look at a few of these types of business agreements. Sales and Purchase Agreement A sales and purchase agreement (SPA) is a legal document obligating a buyer to buy and a seller to sell a product or service. SPAs are critical and common for large, complex purchases. An SPA not only defines prices but payment amounts and time frames for deposits. On the seller’s side, an SPA defines how and when the property is to be transferred to the seller, acceptable condition of the goods or services, and any details that might impede the transfer. 01-ch01.indd 71 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 72 You’ll often see SPAs used in the cabling industry. Pulling cable, especially in an existing building, is complex. A good SPA for cabling covers all of the issues, such as when the installation will take place, when it will be complete, what types of cabling will be used, where the cable runs will go, how the runs will be labeled, how technicians will enter your facility, and whether the vendor is paid at once or at certain completion points. Service Level Agreement A service level agreement (SLA) is a legal document that defines the level of service that a third-party provider guarantees it will provide to the organization. The provider guarantees the service that it provides to be up and running and usable by the organization either for a certain percentage of time or to a certain level of standards. If the provider is storing or processing data for the organization, the SLA may state that the data will be available in a particular format, through a particular application or system, in a specified format, and to authorized users within the organization. If the provider is offering a service such as outsourced network or Web-based transactional services, for example, the SLA states that the services will be available for authorized users whenever they need them. The SLA may describe technologies and redundant systems used to ensure availability for the customer’s data and services, as well as specify what actions the provider will take in the event of incidents that may affect availability of services, and how long the provider has to restore full access for the organization. Finally, most SLAs specify penalties for failure to provide the specified service. NOTE Time is an important element for an SLA—length of time of the agreement, uptime guarantees, and response time for problems. Business Partnership Agreement The business partnership agreement (BPA) specifies what type of relationships the different parties will have, usually from a legal perspective. An entirely separate company may be established for the business venture, combining elements of both individual businesses; this is usually for long-term or large-scale ventures. Usually, however, legal agreements dictate the type of partnerships or customer–provider relationships. These partnerships are usually distinguished by scope, term length, and level of product, service, data access, and so forth provided to each party in the agreement. NOTE A BPA rarely has a time frame but it will have clear methods for ending the partnership. Memorandum of Understanding A memorandum of understanding (MOU), sometimes called a memorandum of agreement (MOA), is a document often used within a large business or government agency that 01-ch01.indd 72 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Module 1-8: Third-Party Risk and Policies 73 establishes an agreement between two independently managed parties that may be working together on a project or business venture. In this type of agreement, a contract isn’t necessarily in place (nor required), simply because both parties work for the same overall organization. An MOU is established so that each party will agree to provide certain services or functions to the other party. Since both parties may work for the same higherlevel organization, money doesn’t necessarily change hands, but it could in a fee-forservice model where funds are transferred from one party’s account to another’s within the same company, for example. An example of this type of MOU would be if a division of the company provides data center services to other divisions of the same company; this MOU would outline the division’s responsibilities and guaranteed levels of services to another division that uses it for data storage and protection. You’ll also see an MOU type of agreement between different government agencies; a military base, for example, may agree to provide network infrastructure services for another nonmilitary government agency that resides on the base (think of NASA, for example, which may have divisions housed on various US Army and US Air Force bases throughout the world). You could also see an MOU between two businesses, of course, as part of a larger contract agreement; this may simply serve to define functions and interactions between two lower-level functions or departments located in each organization that weren’t specified in the overall contract. The MOU may be agreed to and signed off by the middle-level managers of each department. Non-Disclosure Agreement There are plenty of situations where your organization needs to provide a vendor private/ proprietary information. A non-disclosure agreement (NDA) is a legally binding agreement by your vendor that it will not release or expose the information your organization provides to it to any person not specifically listed in the NDA. Interconnection Security Agreement Telecommunication companies will use an interconnection security agreement (ISA) when connecting to each other’s network to handle essential details about technology and personnel. An ISA is not a legal document used to cover technical issues between two parties. An ISA may detail how two independently owned and managed network infrastructures are connected to each other. The businesses that own each network may require interconnections to share and access each other’s data, and may use this type of agreement to specify the technical details needed for the connections. The ISA may specify security requirements, such as firewall and VPN use, encryption levels and methods, authentication types, allowed protocols, and so forth. The ISA may be an attachment or amendment to the overall contract between parties. Verifying Compliance and Performance Any agreement between business parties and providers should specify how each party can verify compliance and performance standards. The parties may specify certain common 01-ch01.indd 73 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 74 standards and performance levels that each party has to meet, as well as legal or governance compliance. Audits or periodic inspections may be used by either party to verify the other party’s compliance and performance. Access control checks, data integrity checks, and review of availability mechanisms (such as backup and restore devices and processes) may be addressed in this part of the agreement. Performance and security metrics such as throughput, availability times, backup frequency, limits on data permissions, and so forth may be specified and used to measure whether or not each organization is adhering to compliance and performance standards. Details regarding noncompliance and failure to perform up to standards should also be addressed in such agreements to give each party an avenue of redress against the other. Questions 1. A script kiddie is a classic example of a(n) __________. A. attacker B. criminal C. threat D. threat actor 2. Risk is often considered formulaically as A. Risk = Probability × Threat B. Risk = Threat × Impact C. Risk = Vulnerability × Threat D. Risk = Probability × Impact 3. A company makes a document called “Acceptable Use” that defines what the company allows users to do and not do on their work systems. The company requires new employees to read and sign this. What is this type of document called? A. Standard B. Policy C. Procedure D. Control 4. A __________ is a description of a complex process, concentrating on major steps and the flows between the steps. A. law B. procedure C. framework D. control 01-ch01.indd 74 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Questions 75 5. A No Trespassing sign is an example of a __________ control. A. deterrent B. preventive C. detective D. corrective 6. A lock on the door of a building is an example of a __________ control. A. deterrent B. preventive C. detective D. corrective 7. An asset’s exposure factor is measured in __________. A. dollars B. percentages C. units D. reputation 8. Which of the following equations is correct? A. Single-Loss Expectancy = Asset Value × Exposure Factor B. Annualized Rate of Occurrence = Asset Value × Exposure Factor C. Annualized Loss Expectancy = Asset Value × Exposure Factor D. Single Rate of Occurrence = Asset Value × Exposure Factor 9. Financial is one type of business impact. Which of the following names another? A. Pride B. Technical C. Device D. Reputation 10. Which of the following represents the component manufacturer’s best guess (based on historical data) regarding how much time will pass between major failures of that component? A. MTTR B. MTBF C. MTMB D. MOAB 01-ch01.indd 75 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 1 Chapter 1: Risk Management 76 Answers 1. D. A script kiddie is a classic example of a threat actor. 2. D. Risk is often considered formulaically as Risk = Probability × Impact. 3. B. Policies are normally written documents that define an organization’s goals and actions. Acceptable use policies are very common. 4. C. A framework is a description of a complex process, concentrating on major steps and the flows between the steps. 5. A. A deterrent control deters a threat actor from performing a threat. A No Trespassing sign is a good example. 6. B. A preventive control stops threat actors from performing a threat. Locks are a notable example. 7. B. Exposure factor is measured in terms of a percentage of loss to the value of that asset. 8. A. The only correct equation is Single-Loss Expectancy = Asset Value × Exposure Factor. 9. D. Of the choices listed, only reputation is a common business impact. 10. B. Mean time between failures (MTBF) represents the component manufacturer’s best guess (based on historical data) regarding how much time will pass between major failures of that component. 01-ch01.indd 76 25/03/21 2:11 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 CHAPTER Cryptography 2 Now he had learned that a machine, simple in its design, could produce results of infinite complexity. —Neal Stephenson, Cryptonomicon Every organization has private data, data accessible by authorized users and not accessible to outsiders. This data includes customer databases; e-mails with critical business strategies; file servers with proprietary recipes and manufacturing processes; cameras sending images of security gates; and Web sites where people type in their names, addresses, and credit card information. Organizations need to keep this data secure. Encryption gives organizations the tools to accomplish this goal. Encryption is a reversible process of converting data such that to a third party the data is nothing more than a random binary string. Note the phrase reversible process. This means a good encryption method must make it easy for someone who knows something secret to encrypt the data and to reverse the process to return the data from an encrypted state to an unencrypted state. Decrypting makes encrypted data readable. This chapter explores cryptography, the science of encrypting and decrypting data, in nine modules: • • • • • • • • • Cryptography Basics Cryptographic Methods Symmetric Cryptosystems Asymmetric Cryptosystems Hashing Algorithms Digital Signatures and Certificates Public Key Infrastructure Cryptographic Attacks Other Cryptosystems 77 02-ch02.indd 77 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 78 Module 2-1: Cryptography Basics This module covers the following CompTIA Security+ objectives: • 2.1 Explain the importance of security concepts in an enterprise environment • 2.8 Summarize the basics of cryptographic concepts Cryptography provides methods and technologies to enable people and systems to exchange information securely, from local connections to enterprise environments that span the globe. Cryptography ensures confidentiality—the encrypted data can be unencrypted and read only by the intended recipient. Cryptography also affords integrity, so the recipient can know that the data received matches the data sent—that the data hasn’t been altered in some way. To accomplish these tasks, developers and programmers have created immensely complicated and awesome systems…and those systems come with a ton of epic jargon and details. This module begins the exploration into the systems that make up modern cryptographic methods. It starts with basic building block concepts, such as plaintext and ciphertext. You’ll look at early cryptography to understand the methods with simple examples. The module finishes with an overview of the essential components of every cryptographic system. Essential Building Blocks Cryptography has terms that describe the state of data, tools used to affect that data, and the movement of data from one state to another. This section discusses these terms: • Plaintext and ciphertext • Code and cipher • Data at rest, data in use, data in transit Plaintext and Ciphertext IT professionals use the terms plaintext and ciphertext to describe the current readability of data. Humans and machines can easily read plaintext. Ciphertext, on the other hand, is unreadable. The process of converting plaintext information into ciphertext information is called encryption. The goal of encryption is to obfuscate the plaintext—to make it unreadable, to look as though it were simply a random jumble of data. Essentially, encryption is about data protection. The reverse of encryption, converting ciphertext back into plaintext, is called decryption. Figure 2-1 shows the icons used here when discussing plaintext and ciphertext. NOTE Don’t mistake the “text” portion of the words plaintext and ciphertext to mean only letters of the alphabet. Any form of easily readable binary data is plaintext. Any form of encrypted binary data is ciphertext. 02-ch02.indd 78 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 79 Figure 2-1 Plaintext and ciphertext Plaintext Ciphertext Lorem ipsum dolor sit amet, conse ctetur adipiscing elit, sed do eius mod 12 46 5e 4e f0 5a fd c4 9f db 50 10 2b ff 26 08 c2 2a 9b ab a5 78 65 95 d1 14 9c 67 a9 47 39 db f8 d2 90 83 a6 Code and Cipher IT professionals use the terms code and cipher to describe generically the ways tools encrypt and decrypt. A code is a representation of an entire phrase or sentence, whereas a cipher tends to represent text on a character-by-character basis. For example, a coded version of the phrase “We attack at dawn” might be “Mother bought some brown eggs at the store.” Codes are not typically transformative; that is, there is usually no formal process to convert the true meanings of messages into their coded equivalents or back. Codes usually require a codebook, a predefined dictionary that translates codes to their plaintext messages and back. The need for a codebook limits the range of messages that can be sent and received via codes. Codes were common before computers, but are not at all common today in modern cryptography. Ciphers, on the other hand, use some form of formal, usually mathematical process to work instead of a fixed codebook. This makes the range of potential messages that can be sent using ciphers essentially unlimited, because these processes are usually done on the fly. Modern cryptographic methods with computers tend to use ciphers. You may sometimes hear the terms encode and decode (as well as encipher and decipher) thrown around. In encoding, data transforms, changes from one form to another. For example, you can encode a sound file from uncompressed WAV format into an MP3 file format. This saves space, but has nothing to do with security. In cryptography, encipher and encrypt mean the same thing, although the former is not in common use. Since IT security focuses on ciphers, this book sticks to the terms that apply to ciphers: encrypt and decrypt. NOTE Codes are entire words and phrases; ciphers are individual characters. The cryptography methods discussed in this book focus on ciphers. Data at Rest, Data in Use, and Data in Transit Dealing with cryptography for computer data depends on the location of the data and the actions of that data at any given moment. The process of encrypting and decrypting data sitting on a hard drive, for example, differs from the process of encrypting and 02-ch02.indd 79 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 80 decrypting data moving wirelessly between a wireless access point and a wireless client. Three terms define the current state of data: • Data at rest • Data in use • Data in transit Data at Rest Data at rest describes data that resides in storage. This data is not currently accessed, transmitted, or received, nor used by the computer. Data at rest is normally represented by data stored in static files on a hard drive or other storage media, when the device that holds that media is powered down. In other words, data on a laptop computer, powered down and sitting in Steve’s bag, is data at rest. NOTE Once Steve has logged into his computer at the airport lounge, the data on the laptop’s SSD could change at any time. So is it truly data at rest? Cybersecurity professionals argue this point a lot, and some call the data subject to change data at rest (inconstant). You won’t see that phrase on the CompTIA Security+ exam. Data in Use Data in use describes data currently in use by a computing device and not at rest or in transit. Data in a computer’s RAM and accessed by the computer’s CPU, operating system, and applications is data in use. Operating systems and applications take data at rest and put it into use on a constant basis, transforming it, using it as input to processes, and so on. A Microsoft Word document Susan is currently editing is an obvious example. Lots of techniques target data in use. Shoulder surfing—a social engineering technique where someone literally or figuratively looks over a user’s shoulder to view/record the contents on the screen—can grab data in use. A fairly simple USB keycatcher—easy to install when a user isn’t looking—can record or transmit via wireless everything the user types. Data in use is very much data in danger! EXAM TIP The CompTIA Security+ objectives use the term data in processing as an alternative label for data in use. Don’t be thrown off by the odd term. Data in Transit Data in transit describes data currently in transport. This data is being transmitted or received from one person or host to another. Examples of data in transit include information moving over a network, over an Internet connection, from computer to computer over an Ethernet connection, or even over wireless networks. The data is not in storage; it has been transformed and formatted to be transmitted and received. Data in transit has high requirements for confidentiality. It’s relatively easy for malicious actors to intercept transmitting data, so we need good encryption. Data in 02-ch02.indd 80 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 81 transit also has very high requirements for integrity. The recipient must have assurance that the data received is the same as the data sent. EXAM TIP The CompTIA Security+ objectives describe a key facet of data protection as dealing with data in transit/motion. The industry term used here, data in transit, means the same thing. Don’t get tripped up by the wording. Outstanding! The module has covered enough terms to enable a brief survey of the history of cryptography. Pay attention here, as almost everything done hundreds of years ago is still used today on modern computers. Early Cryptography People throughout the past few thousand years have used cryptography to protect personal secrets, military troop movements, diplomatic messages, and so on. Historians have discovered several examples of the uses of crude, but effective, cryptographic methods, such as the Spartan scytale, which was a baton or stick with a strip of parchment wound around it several times, from one end of the stick to the other (Figure 2-2). After the parchment was wrapped on the baton, a person wrote a message in plaintext. Once the parchment was removed from the stick, the words on the strip of parchment made no sense, since they were effectively encrypted. To “decrypt” the message, the receiver had to know the exact dimensions of the baton and have an identical one so that he could rewrap the parchment the same way around the baton and read the message. Figure 2-2 Author’s homemade scytale (Attack at dawn) 02-ch02.indd 81 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 82 Other historical uses of cryptography involved using different techniques to scramble letters of the alphabet so that only the sender and recipient would know how to unscramble and read them. The next sections of the chapter discuss those methods. Still other, more modern ways of using cryptography involved the use of specially built machines to encrypt and decrypt messages. The classic example is the Enigma machine used by the Germans during World War II. This machine used encryption techniques that were considered unbreakable, until Dr. Alan Turing, a British mathematician, figured out how the machine worked and the methods it used to encrypt its information. Turing, now considered the father of modern cryptography and, to a large degree, computers, decrypted intercepted German messages. The capability of the British government to decrypt German military communications gave the Allies incredible insight into enemy troop movements, invasion plans, and so forth, effectively turning the tide of the war. Alan Turing didn’t invent cryptography, but many of the concepts used today were quantified by him in the huge number of academic papers Turing wrote. Turing clarified the ideas of substitution and transposition, the two pillars of cryptography. Substitution A substitution cipher swaps letters of the alphabet for other letters. To make a substitution cipher work, rotate the letters of the alphabet by some number of characters, then swap the letters that will substitute for them. A typical rotation shifts the alphabet 13 characters, called ROT13. Here’s the standard alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ And here’s the same alphabet with ROT13 applied: NOPQRSTUVWXYZABCDEFGHIJKLM Note that the letter N replaces letter A. Letter G replaces letter T. Line the two up so you can see the full replacement scheme: ABCDEFGHIJKLMNOPQRSTUVWXYZ NOPQRSTUVWXYZABCDEFGHIJKLM Now apply an example. The plaintext phrase, WE ATTACK AT DAWN, would change to JRNGGNPXNGQNJA in ROT13 encryption. NOTE ROT13 is not the only ROT cipher. You can do ROT2, ROT10, ROT25, and so on. This type of cipher is also called a shift cipher because it essentially shifts the entire alphabet down 13 spaces and then starts over with the first letter. Still other methods of using substitution ciphers might use different words to begin the substitution alphabet and then follow those words with the rest of the alphabet in normal order. 02-ch02.indd 82 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 83 NOTE Julius Caesar used a substitution cipher in his military campaigns for sensitive communications. Thus, a substitution cipher is commonly referred to as a Caesar cipher. A Vigenère cipher takes the Caesar cipher to its extreme. Figure 2-3 shows a tabula recta, a table of all 26 possible ROT ciphers that creates a grid. The Vigenère cipher uses a repeating key word to determine which row to use for encryption. Here’s how to use the tabula recta and key word to encrypt the plaintext. Find the plaintext letter at the top (column), then use the key word letter along the side (row). The matching column and row intersection provides the encrypted letter. An example will make this clear. Again our plaintext is WE ATTACK AT DAWN. And we’ll use a key word of MIKE (repeated here to match the text): WEATTACKATDAWN MIKEMIKEMIKEMI Figure 2-3 Vigenère cipher table, or tabula recta 02-ch02.indd 83 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 84 Use the tabula recta to create the encrypted phrase. Here are the first five letters: W E A T T → → → → → M I K E M = = = = = I M K X F And so on . . . Note that the second “T” encrypts to a different letter than the first “T” because of the difference in the key word letter. Sweet! Here’s the fully encrypted phrase: IMKXFIMOMBNEIV If the recipient knows the key word, he or she can quickly decipher the code. Without the key word, deciphering becomes more difficult (and relies on repetition analysis and so forth). Vigenère ciphers were popular for centuries. Examples of substitution ciphers can be found in the standard word puzzle books you see on magazine racks in supermarkets and bookstores. In cryptography, confusion means that every character in a key is used to make the ciphertext more random looking. Adding a key to change the ROT value of every character adds confusion, making a Vigenère cipher much harder to crack than a ROT. Vigenère ciphers have a weakness. Encrypt the plaintext WE ATTACK AT NOON with the MIKE key, but each letter in the key only affects the plaintext character directly underneath it. A better encryption should act in such a way that even the smallest change in the key makes for very different ciphertext. This is called diffusion. The Vigenère cipher lacks diffusion. Modern codes do not! Transposition A transposition cipher transposes or changes the order of characters in a message using some predetermined method that both the sender and recipient know. The sender transposes the message and sends it. The recipient applies the same transposition method in reverse, decrypting the message. There are a variety of different transposition methods, including columnar, rail fence, and route ciphers. Current computer-based cryptography uses both substitution and transposition together in wildly complex ways. Cryptanalysis For as long as people have encrypted and decrypted data (or messages or whatever), others have tried to crack those messages. Cryptanalysis is the study of breaking encryption, the opposite of cryptography. You perform cryptanalysis on ciphertext data to reverse it to a plaintext state when you do not have access to the methods used to encrypt the data in the first place. Both security professionals and malicious actors perform cryptanalysis when attempting to decrypt ciphertext. There are hundreds, if not thousands, of methods for performing cryptanalysis, but many of them depend upon having a piece of plaintext that can be compared to its corresponding ciphertext, and vice versa, when you have some knowledge of the methods used to encrypt and decrypt the text. The next few modules discuss various methods of cryptanalysis. 02-ch02.indd 84 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 85 Cryptography Components Cryptography has several basic components that make the process work. These include algorithms, keys, XOR functions, shifts, rounds, and cryptosystems. While this module covers only the basics of these components, the remaining modules on cryptography discuss in depth how these different components work together. Algorithms and Keys Algorithms and keys work together to create cryptographic methods used to encrypt and decrypt messages. (They also can create cryptographic hash functions, used for digital signatures and more, a subject covered in depth in Module 2-5.) Algorithms are mathematical constructs that define how to transform plaintext into ciphertext, as well as how to reverse that process during decryption. An individual algorithm might be very simple or very complex. A very simple algorithm used in a substitution cipher, for example, only requires shifting a letter several spaces to the right. Almost all the real-world algorithms used in IT encryption/decryption are extraordinarily complex. A single algorithm will contain a dizzying number of mathematical manipulations. A key applies a variable used by the algorithm for the final cryptosystem (see the upcoming section “Cryptosystems”). In a ROT13 cryptosystem, ROT is the algorithm— to implement the encryption/decryption, shift letters of the alphabet. The 13 is the key or cryptovariable that defines how many letters to shift. Algorithms often don’t change. Keys change to keep bad actors guessing. Keys are kept secret. Keys are typically not simplistic numbers. They are often complex, lengthy strings of numbers or characters. A key might also be a password, passphrase, personal identification number (PIN), code word, and so on. Algorithms and keys are used to encrypt or decrypt text, as illustrated in Figure 2-4. Figure 2-4 Algorithms and keys Key Plaintext Ciphertext Algorithm 02-ch02.indd 85 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 86 Algorithms are generally well known and tested, giving cryptographers and security professionals a level of confidence in their strength and ability to protect data. Kerckhoffs’ principle states that the algorithm should not be the secret part of the cryptographic process or method used; the key should be kept secret, not the algorithm. Most security professionals follow this principle. NOTE Dutch cryptographer Auguste Kerckhoffs developed Kerckhoffs’ principle in the late 19th century. This stuff has been around for a while! Key escrow grants knowledge or copies of keys to a third party. Businesses and other organizations use key escrow to store keys securely in the event that they are lost, they become corrupt, or an individual in the company with the only knowledge of the keys is terminated or quits. Key escrow provides an exception to Kerckhoffs’ principle. EXAM TIP An algorithm is a mathematical construct or rule that dictates how data will be encrypted and decrypted. Algorithms are generally well known and not kept secret. Secret algorithms are not needed. Keys are the variables that algorithms use to ensure secrecy and randomness in the cryptographic process. Keys should be kept secret. Key length or key size refers to the number of bits in a key; this number implies security—a hacker can readily break a short key, for example. With the unbelievable growth in computing power today, on the other hand, a long key doesn’t necessarily equate to better security. You’ll see various key lengths used in practical cryptography in Modules 2-3 and 2-4. The most secure keys would come from truly randomly generated numbers, numbers that no one could predict. Such a number would have an entropy value of 1, meaning full entropy or complete unpredictability. The reverse of this, with a completely deterministic system, would have an entropy value of 0. The ROT13 system discussed earlier, for example, with its predictable, fixed system, is such a deterministic system. Computers are not random, though, but very much predictable. Many will use software to generate pseudorandom numbers based on some mathematical system. Not surprisingly, the type of software used in cryptography is called a cryptographically secure pseudorandom number generator (CSPRNG), or simply cryptographic random number generator (CRNG). The factor to keep in mind here is that the keys come from some system and thus provide a place for threat actors to attack. We’ll see more of this in Module 2-8, “Cryptographic Attacks.” Block and Streaming Algorithms Algorithms have a wide variety of characteristics that include mathematical foundation, strength, and how they operate on plaintext. Modules 2-3 and 2-4 go into detail about specific algorithms used in cipher suites (groups of algorithms used to secure network connections), but for now, let’s discuss an important distinction within algorithms: block and streaming. 02-ch02.indd 86 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 87 Remember the distinction between codes and ciphers and how they work with entire phrases (codes) or on individual characters (ciphers)? The algorithms discussed in this book work on binary digits (bits) of plaintext, either individually or in specified groups. A block algorithm operates on a predefined size of a group of bits, known as a block. Different block algorithms use different block sizes, but typical sizes are 16-, 64-, and 128-bit blocks. Most of the algorithms discussed in this book are block algorithms. Streaming algorithms operate on individual bits, one bit at a time. Streaming algorithms don’t work on blocks of text; instead, they look at each individual bit and perform a mathematical operation on that bit and then move on to the next bit. Streaming algorithms tend to work much faster than block algorithms and are used in cryptographic methods that support fast communications requirements, such as wireless technologies. EXAM TIP Block algorithms work on predefined sizes of plaintext blocks, while streaming algorithms work on single bits of plaintext. CompTIA refers to streaming algorithms as stream algorithms. Streaming algorithms have a problem. Since they only encrypt one bit at a time, they need a piece of arbitrary value or string to get the encryption process started. This code, called an initialization vector (IV), provides the necessary randomness for the algorithms. There are also some interesting situations where IVs work in a block protocol as well. See “DES” in Module 2-3 for more. XOR Functions Computing devices use binary data. Hard drives store Word documents in binary format. YouTube videos stream to a browser in binary format. Caesar ciphers use alphabets, not bits, so they don’t readily apply to binary data. Computers need mathematical tools to encrypt, to transpose and substitute ones and zeros. The most commonly used binary math function used in cryptography is called eXclusive OR (XOR). XOR compares two bits to determine difference. With XOR, any bits that compare and are the same (two binary 0’s, for example) yield a resultant bit of false (and produce a 0-bit as the output). Any bits that compare and are different (a binary 1 and a binary 0) produce a true value, and an output bit of 1 is generated. Figure 2-5 illustrates this process. (If you’ve taken the CompTIA Network+ exam, then you know about XOR comparison from subnetting. The 1’s in the subnet mask compare to the IP address to differentiate the network ID from the host ID.) NOTE XOR results might seem a little weird at first. Keep in mind that XOR determines differences in compared data. A true result means that the compared data is not the same. A false result means the data is the same. Here’s an example of XOR in action, encrypting the randomly selected name, Mike, as the data: MIKE 02-ch02.indd 87 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 88 Keystream Ciphertext XOR Plaintext Input Plaintext Keystream Value Text Value XOR’d Value 1 1 0 0 0 0 1 0 1 0 1 1 Figure 2-5 The XOR function in action As a first step, convert these four letters into binary. For this example, we’ll use ASCII code. ASCII converts every letter of the English alphabet in 8-bit binary values: M I K E = = = = 01001101 01001001 01001011 01000101 So, MIKE in binary is 01001101010010010100101101000101. This string of bits is the plaintext. The XOR function compares two binary values, right? To encrypt with XOR requires another value to compare with the plaintext. To XOR encrypt this binary data, therefore, we need a binary key. Let’s arbitrarily choose the ridiculously easy key of 0110. To encrypt, repeatedly place the key under the plaintext, as follows: 01001101010010010100101101000101 (plaintext) 01100110011001100110011001100110 (key repeated) Now go one bit at a time, using XOR to encrypt: 01001101010010010100101101000101 01100110011001100110011001100110 00101011001011110010110100100011 (ciphertext) 02-ch02.indd 88 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-1: Cryptography Basics 89 Congrats! You’ve just done binary encryption, in this example using XOR. Want to decrypt the ciphertext? Just XOR it against the repeated key, as follows: 00101011001011110010110100100011 (ciphertext) 01100110011001100110011001100110 (key repeated) 01001101010010010100101101000101 (plaintext) Using XOR solely, especially with such a short key, creates an easily cracked ciphertext. Let’s make it harder by adding a shift. Shifts As the name implies, a shift in binary means moving the ciphertext left or right. Let’s shift the ciphertext four digits to the left. Here’s the initial ciphertext: 00101011001011110010110100100011 Now, take the first four binary values on the far left and move them to the end on the far right, as follows: 10110010111100101101001000110010 Adding a shift increases the complexity involved in decrypting. You need the key, plus knowledge of the shift. A simple shift makes better encryption, but a powerful computer can figure out this shifty trick in milliseconds! Let’s enhance the encryption by doing the whole XOR/leftshift multiple times. Rounds Repeating the XOR/left-shift iteration more than once—such as five times—makes the encryption harder to crack. It also means it will take longer to encrypt and decrypt, because every encryption and decryption must repeat the iteration five times. (That’s the price required for security.) Each of these XOR/left-shift iterations is called a round. Most modern algorithms use multiple rounds, repeating the process several times to ensure that the process is effective. Cryptosystems A cryptosystem includes everything in a cryptographic process, such as the algorithms, keys, functions, methods, and techniques. The example used here—the Mike Meyers Excellent Cryptosystem—includes four components: • • • • 02-ch02.indd 89 A four-bit key An XOR A four-digit left shift of the ciphertext The XOR/left-shift iteration repeated in five rounds 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 90 Cryptosystems use algorithms and keys as basic components to stir up the binary data and also implement them in ways that enable the encryption/decryption to be faster, more efficient, or stronger. Module 2-2: Cryptographic Methods This module covers the following CompTIA Security+ objectives: • 2.1 Explain the importance of security concepts in an enterprise environment • 2.8 Summarize the basics of cryptographic concepts You can differentiate cryptographic methods by the encryption method used, either symmetric or asymmetric. These two types of cryptography focus more on the aspect of the keys used than the algorithms, although each type has its own algorithms, as discussed in later modules. This module explores symmetric cryptography first, followed by asymmetric cryptography. The third section in the module describes a unique type of cryptography called hashing. The fourth section explores the relative limitations between symmetric and asymmetric cryptographic systems. The fifth section puts symmetric cryptographic systems, asymmetric cryptographic systems, and hashing together in hybrid cryptography. The final section discusses what makes a perfect cryptosystem. Symmetric Cryptography Symmetric cryptography uses a single key that both encrypts and decrypts data. All parties that require access to a piece of encrypted data know that key. If someone encrypts a file or sends a secure message to another person, both persons must have the key used to encrypt the data to decrypt it. NOTE The industry uses the terms “symmetric cryptography” and “symmetric-key cryptography” interchangeably. You’ll see that here and in a similar form with “asymmetric cryptography” used interchangeably with “asymmetric-key cryptography.” Symmetric keys are sometimes called secret keys or session keys. Session keys, more specifically, are created and used for a single communications session. They are not reused after the communications session ends. If the parties want to communicate again using symmetric cryptography, new session keys are generated by either party or by the cryptosystem in use. Figure 2-6 shows how two parties use symmetric keys to exchange sensitive data. EXAM TIP Symmetric key cryptography uses a single key that both encrypts and decrypts data. 02-ch02.indd 90 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-2: Cryptographic Methods 91 Figure 2-6 Symmetric keys in use Symmetric Key Symmetric Key Plaintext Ciphertext Symmetric Algorithm Symmetric Algorithm Plaintext Symmetric key cryptography is both low latency (quick to respond) and good at handling large amounts of data, such as storage or transmission of large files. Symmetric keys require minimal computational overhead. Since only one key is involved, in communications limited to only two parties, symmetric key cryptography works great. Symmetric key cryptography has a couple of weaknesses in scaling and key exchange. First, when multiple parties require access to the same encrypted data (such as a group of friends or business associates), the exchange uses the same key. The more people who have the key, the greater the chances that it will get inadvertently disclosed to an unauthorized person. Second, getting the key into the hands of only the desired users presents challenges. Let’s look at an example of the scaling problem. User Meghan wants to communicate with user Amy. Both need only one secret key. Adding more users, such as Tim, Bobby, and Dawn, means each must have the same key to access the encrypted data. What if, however, Meghan wants only Amy to view a piece of data, and she doesn’t want Tim, Bobby, or Dawn to see it? Meghan must maintain separate symmetric keys for each party with whom she wants to communicate. Among a few people this scenario might be manageable. But imagine what happens if Meghan needs to maintain separate keys for 100 people? Meghan has a lot of keys! Worse yet, what if each of the 100 people required secure, unique communication with every other user? How many total keys must be generated? 02-ch02.indd 91 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 92 Math comes to the rescue here. The total number of keys required is equal to the number of people in the group, multiplied by that same number less 1, and then divided by 2. Here’s the formula: K = N × (N – 1)/2 • K is the total number of keys required. • N is the number of people in the group. So: K = 100 × (100 – 1)/2 = 4950. As you can see, with 100 users, a lot of keys must be generated, issued, and exchanged among each pair of users in the group who must securely communicate. Symmetric key cryptography does not scale very well in larger groups or entities that must securely communicate with one another. Key exchange refers to the process used to exchange keys between users who send a message and those who receive it. Without the key, an authorized user or message recipient can’t decrypt the message; the message will simply remain as ciphertext. Since only one key is used in a symmetric communication, there must be a way to deliver the key securely to the right users, with an assurance that it won’t be intercepted and compromised. E-mail is usually not the most secure way, although sometimes people send their secret keys via an e-mail message. Manual methods offer a little more security, such as giving someone a key stored on a USB memory stick. Most of the time, especially in large organizations or when communicating with someone over greater distances, manual exchange isn’t practical. The problem with key exchange, therefore, is getting the key to someone using a means that is considered secure—so that the key will not be intercepted and used by an unauthorized person, rendering the entire process useless. Symmetric key cryptography has problems with secure key exchange. Key exchange has two terms to describe the exchange methods: • In-band • Out-of-band In-band key exchange involves using the same communications channel you are using to send the message to send the key. This may not be the most secure way, since that channel may be monitored by a malicious person. Out-of-band key exchange involves the use of a separate, independent channel, such as snail mail, USB stick, or even a different network connection, to send the key to the authorized users. In smaller groups of users that reside near each other, key exchange may not be much of a problem. In large organizations, however, in which users may be geographically separated, key exchange can be an issue, especially when using only symmetric key cryptography. EXAM TIP Symmetric key cryptography excels in speed, efficiency, and the ability to handle large amounts of data easily. The disadvantages primarily involve scalability and key exchange. 02-ch02.indd 92 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-2: Cryptographic Methods 93 Asymmetric Cryptography Asymmetric cryptography uses two separate keys—a key pair—for secure communication. Data encrypted with one key requires the other key in the key pair for decryption. In public key cryptography—the primary asymmetric implementation—these keys are called a public key and a private key. Each user is issued or generates a key pair for his or her own use. The user gives the public key to anyone, even posting it on the Internet. The user keeps the private key, on the other hand, secret. With public key cryptography, what one key encrypts, only the other key can decrypt, and vice versa. If the key in the pair is used to encrypt a message, it cannot decrypt the same message. This makes the cryptography process, particularly sending and receiving confidential messages, different from the process used in symmetric key cryptography. EXAM TIP Public key cryptography uses two mathematically related keys in a pair, a public key and a private key. What one key encrypts, only the other key in the pair may decrypt, and vice versa. In current systems, the public key encrypts and the private key decrypts. (See Module 2-6 for the only use for reversing this process, validating a certificate by viewing the digital signature.) Jack and Jill want to communicate using public key cryptography. They need to follow specific steps. First, each must generate a unique key pair. Second, each user makes his or her public key readily available, such as posting it to the Internet. Jack acquires Jill’s public key, encrypts a message using that key, and sends it to Jill. Jill receives the message and decrypts it with her private key. Her private key is the only way to decrypt a message encrypted with her public key. For Jill to send a message to Jack securely, she reverses the process. She gets his public key and uses it to encrypt the message. Upon receipt, Jack decrypts the message using his private key. It’s an elegant system. Figures 2-7 and 2-8 demonstrate this process. Asymmetric key cryptography has several advantages over symmetric key cryptography, the major one being key exchange. The process eliminates key exchange issues, since no Private Keys Kept Secret Figure 2-7 Distribution of public and private keys Jill’s Private Key Jack’s Private Key Jack’s Public Key 02-ch02.indd 93 Public Keys Exchanged Jill’s Public Key 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 94 Figure 2-8 Using asymmetric key cryptography Jill’s Public Key Jack’s Public Key Jack’s Private Key Jill’s Private Key Jack Jill one really has to exchange a key. Anyone can acquire the public key. The sending party encrypts the message with the receiving person’s public key, and only the recipient who possesses the private key can decrypt it. Asymmetric key cryptography has a couple of disadvantages as well. First, it’s slower than symmetric key cryptography and more computationally intensive to generate keys. Second, it works well only with small amounts of data; it’s not suited for bulk data encryption or transmission. Module 2-7 will discuss the primary uses of asymmetric key cryptography, which involve public key infrastructure, or PKI, and uses of digital certificates and signatures. EXAM TIP Asymmetric key cryptography does great key exchange, but features slower speed compared to symmetric key cryptography and doesn’t handle large amounts of data very efficiently. Expect a question or two on the CompTIA Security+ exam that asks you to contrast symmetric vs. asymmetric encryption concepts and methods. Hashing Hashing provides integrity in the confidentiality, integrity, availability (CIA) triad of security by creating unique numbers for data and originators of information. Hashing helps verify that data came from a specific source and that the data did not change from what was sent. In the hashing process, variable-length text, such as a document or spreadsheet, or even a password, is exposed to a cryptographic algorithm that produces a cryptographic sum, or hash (also sometimes called a message digest), of the document. This hash is only a representation of the text; it is not the same thing as the text itself. Think of a hash as a unique fingerprint that identifies a very specific piece of plaintext. The piece of plaintext can be any length, and it generally does not matter how large the input plaintext is. The resulting hash will always be a fixed-length piece of ciphertext, usually expressed in a hexadecimal format. An example of a typical hash is shown in Figure 2-9. 02-ch02.indd 94 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-2: Cryptographic Methods 95 Figure 2-9 A hash value computed for a file Unlike the encryption and decryption process, hashing was not designed to be reversible. In other words, you don’t simply encrypt text with a hashing function with the expectation of decrypting it later. Hashing is a one-way mathematical function whose sole purpose is to produce the cryptographic sum of the input plaintext. Think of the hashing process as sort of a measuring process for the data, with the resultant hash being the actual measurement itself. Although its purpose is not to decrypt text, the cryptographic sum produced by hashing has some uses. First, hashing is used to provide for integrity of data. A hash is unique to a particular piece of text. If one letter or word of the text is altered in any way, if even one binary digit changes, the resulting hash will differ from the original hash. Hashing assures the integrity of a piece of plaintext, since any changes would produce an easily detected different sum. Figure 2-10 shows the hashing process. Data transmitted over a network can be hashed before transmission and after reception, and the two resulting hashes can be compared. If the hashes match, you have unaltered data. If they differ, you can assume that the data has changed in some way during transmission. We’ll discuss hashing in more depth in Module 2-5, with specific examples of hashing methods. NOTE The term “message” generically refers to any piece of variable-length text, be it a password, text document, spreadsheet, picture file, or any other type of data. Figure 2-10 The hashing process Variable-Length Text 02-ch02.indd 95 Hashing Algorithm Fixed-Length Hash or Message Digest 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 96 Limitations in Symmetric vs. Asymmetric Cryptography You need to have clarity on the relative strengths and weaknesses of symmetric and asymmetric cryptography in concept before you delve into the next two modules, which layer on all the specific implementations of those systems. Limitations of systems include • • • • • • • • • • Speed Size Weak keys Time Longevity Predictability Reuse Entropy Computational overheads Resource vs. security constraints The module has discussed several of these limitations already, notably speed, size, weak keys, and computational overheads, noting that symmetric encryption is faster and has lower computational overhead than asymmetric encryption and that small-sized keys are weak keys. Size also relates to symmetric encryption handling larger files more efficiently than asymmetric encryption. The other limitations require a little more discussion. No encryption scheme is unbreakable. Developers instead strive to create an encryption scheme that provides strong enough security to make it too difficult—in terms of time and computational power needed—to crack. Because technology advances rapidly increase the computing power available to hackers, on the other hand, the relative security of any cryptosystem is a moving target. Folks at the National Institute of Standards and Technology (NIST) keep track of these things, rating the longevity of each active cryptosystem, as in how many years a cryptosystem remains secure in the current computing environment. We’ll save the details for the next couple of modules, but current cryptosystems are pretty awesome, and increasing the size of keys by just a single bit makes a cryptosystem twice as hard to crack. Modern cryptographic systems generate some kind of key to encrypt and decrypt messages, but those keys usher in limitations and vulnerabilities. We discussed the entropy level of pseudorandom numbers in the previous module, a measure of how predictable those numbers can be. The four characters in the Mike Meyers Excellent Cryptosystem, for example, have a very low entropy level, meaning a hacker could predict or guess them pretty quickly. Other cryptosystems might seem to have much tougher keys, such as 64-bit keys, but if 32 bits of the key have high predictability, the overall key is vulnerable to attack. There’s also the reuse factor for keys. An 8-bit key, for example, would generate numbers between 0 and 255, which means the numbers would quickly be reused, making the 8-bit key weak. In contrast, a one-time password that’s never reused? Almost uncrackable. 02-ch02.indd 96 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-2: Cryptographic Methods 97 Finally, resource vs. security constraints boils down to the relationship between how much computing power goes into the system and the security of the system. Higher key lengths offer more security but require more computing power to deal with. A millioncharacter one-use key would be utterly secure, but to generate that every time a message gets encrypted/decrypted would kill modern systems. Every cryptosystem works on this balancing principle, defining an inherent limitation. Hybrid Cryptography Many modern implementations of cryptography combine symmetric key and asymmetric key functions with hashing to create a highly secure mashup generically called hybrid cryptography. Symmetric key cryptography handles large data well, but is weak at key exchange. Asymmetric does key exchange well, but encrypts/decrypts more slowly than symmetric. Both pretty much define confidentiality, but lack integrity. Hashing provides the missing integrity aspect. Here’s an example of hybrid key cryptography in action. A common method of key exchange involves the creation of a “secret” between the two parties. This secret is then run through a hash to create the one-and-only unique, cannot-be-reversed (supposedly) key to be used on the symmetric side. Encrypt and send this hash via your asymmetric system and voilà! You’ve securely exchanged a viable key for your symmetric side. Nothing is perfect, of course, and there are many variables—using certificates to identify each party, encryption streams within the exchange, and so on. But for the purposes of this discussion, just remember hybrid encryption means to use combinations of symmetric, asymmetric, and hashing to ensure better confidentiality and integrity. EXAM TIP Hybrid cryptography leverages the advantages of both symmetric and asymmetric key cryptography and eliminates their disadvantages. The Perfect Cryptosystem Cryptosystems should render unclear or unintelligible—obfuscate—any plaintext into what anyone who can’t decrypt would see as nothing more than random data. This obfuscation makes data secure. Security through obfuscation is what cryptography is all about! EXAM TIP Look for questions on the CompTIA Security+ exam that ask you to recognize common use cases of cryptography supporting obfuscation. You’ll see more use cases when we tackle specific cryptosystems in Modules 2-3 and 2-4. Proponents of security through obscurity argue that hiding how cryptosystems work hardens those systems. If you invent a great cryptosystem, full of interesting math using all kinds of substitutions, transpositions, and shifts over lots of rounds, and, in the implementation, count on the fact that no one else knows the algorithm, you have the perfect, uncrackable cryptosystem. 02-ch02.indd 97 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 98 NOTE Many IT security professionals argue that making a target appear uninteresting adds a level of protection. This differently nuanced definition of security through obscurity applies to situations such as a bank versus a would-be robber. The robber might spend all of his time on the vault door, so storing vital stuff in a simple locked janitor closet would work. Security through obscurity misses one essential fact: every cryptosystem is crackable over time. What seems impossible today becomes child’s play with tomorrow’s technologies. Rather than hiding how cryptosystems work, modern cryptography makes algorithms public. Making the systems available for everyone to attack exposes vulnerabilities and weaknesses that can be addressed. Make the underlying algorithm unassailable, as Kerckhoffs suggested, but keep the specific key used secret. Because of this attitude, new, more resilient cryptosystems come out every few years. The creators of these cryptosystems happily send them out for academic rigor, making sure the code has high resiliency, that it holds up against cracking. Finally, that elusive perfect cryptosystem should hold up over time. In some cases, keys might be used for weeks, months, or even years perhaps. Forward secrecy means to protect a cryptosystem from one key giving away some secret that makes it easier to crack. If an algorithm achieves this, we call it perfect forward secrecy. There is no such thing as perfect forward secrecy other than using a key only once and throwing it away—a one-time pad. Module 2-3: Symmetric Cryptosystems This module covers the following CompTIA Security+ objective: • 2.8 Summarize the basics of cryptographic concepts Developers have created and deployed numerous symmetric key cryptosystems over the years to provide fast and secure data communications. This module explores the six most common symmetric cryptosystems. Some of the data here is historical, but all of it informs modern cryptosystems. Let’s look at these cryptosystems: • • • • • • DES 3DES AES Blowfish Twofish RC4 DES The Data Encryption Standard (DES) is an older, now obsolete standard for commercialgrade encryption within the United States. DES uses an algorithm called Lucifer, developed by IBM. In the DES implementation, Lucifer has a 64-bit key size. Eight of those 02-ch02.indd 98 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-3: Symmetric Cryptosystems 99 bits are used for computational overhead, so the true key size is only 56 bits. DES is a symmetric block algorithm and uses 64-bit block sizes. Blocks that are less than 64 bits in size are padded. EXAM TIP The CompTIA Security+ exam will quiz you on block sizes, so make notes throughout this module! DES works in modes of operation, defined methods that determine how a plaintext block is input and changed to produce ciphertext. Each of these modes processes input blocks of text in different ways to encrypt the data. Modes also use certain mathematical functions to transform the data for stronger encryption. DES uses 16 rounds for each mode. So, for whichever mode is used, that process is repeated 16 times on a block of plaintext to produce the output ciphertext. DES uses five different block cipher modes of operation: • • • • • ECB CBC CFB OFB CTR In the electronic code book (ECB) mode, plaintext blocks of 64 bits are manipulated to produce ciphertext. With ECB mode, a given piece of plaintext will always produce the same corresponding piece of ciphertext. Unfortunately, this makes ECB mode very predictable, and it can easily be broken if an attacker has specific pieces of plaintext and ciphertext to compare. The cipher block chaining (CBC) mode produces much stronger encryption by XORing the previous block to the block being encrypted. The very first block introduces an initialization vector (IV) into the process. This ensures that every block of plaintext input into the process produces a uniquely different piece of ciphertext. So even when the same block of plaintext is input repeatedly, the resultant ciphertext will not be identical to any previous outputs. Cipher feedback (CFB) mode is like CBC except the plaintext is XORed into the IV after each round. Output feedback (OFB) mode is very similar to CFB mode, but instead of the previous block’s ciphertext being the next block’s IV, it takes the result of the previous encryption of the IV and key before the plaintext is XORed. In DES, counter (CTR) mode uses a random 64-bit block as the first IV, then increments a specified number or counter for every subsequent block of plaintext. CTR mode offers the best performance. Figure 2-11 illustrates how complex even the simple ECB mode is in DES; this screenshot was taken from the freely available open-source CrypTool cryptography learning program (www.cryptool.org). 02-ch02.indd 99 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 100 Permuted input R2 … … 2×32-bit K[3] … L2 K[5] L15 Overview 64-bit Key K IP PC1 Permuted input PC2(K) 16 DES rounds 16 subkeys round 3–15 R15 f Input block X Pre-output K[16] IP–1 L16 R16 R16 L16 Pre-output Output block Y 2×32-bit 64-bit – The permuted input is split in two halves called L0 and R0, each 32-bit wide. – For i =1, ..., 16 (16 DES rounds) let Li = Ri–1 and Ri = Li–1 f (Ri–1, Ki) – Ki is the subkey index and means bitwise addition modulo 2 (also called) (XOR) – In this schematic round 3 to 15 are abbreviated, but they run just the same. Figure 2-11 Illustration of how DES ECB mode works (screenshot from the CrypTool cryptography learning program) EXAM TIP You need to know the different characteristics of DES for the exam—16 rounds of encryption, 64-bit blocks, 56-bit keys, and five cipher modes of operation. Authenticated Encryption The modes of operation used in symmetric cryptosystems can run in a couple of different ways, as unauthenticated or authenticated. The strength of the encryption doesn’t change either way, but unauthenticated modes offer a flaw when used in online applications. An attacker can use an attack called a chosen ciphertext attack to intercept, modify, and, eventually, decrypt messages. You can implement cryptosystems that fix this flaw in a couple of ways, but such implementations have traditionally been optional, presumably because the encryption standards were good enough and faster without the added layers of protections. The most common way today to secure modes of operation is to use authenticated encryption (AE) modes that both encrypt and authenticate messages. (See the description of GCM in the upcoming discussion of AES for a very commonly used AE mode.) Alternatively, you could use the more complicated message authentication code to add more protection. (See “HMAC” in Module 2-5 for more details.) 02-ch02.indd 100 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-3: Symmetric Cryptosystems 101 EXAM TIP Look for questions on the Security+ exam that ask about unauthenticated vs. authenticated encryption modes of operation. Bottom line? Unauthenticated = bad. Authenticated = good. 3DES Triple DES (3DES or TDES) is a later iteration of DES designed to fix some of the problems found in DES. It basically puts plaintext blocks through the same type of DES encryption process, but it does so in three distinct iterations. Where DES uses single 56-bit keys, 3DES uses three 56-bit keys. Many IT folks—and the CompTIA Security+ exam—combine the three keys, so describe 3DES as having a 168-bit key. 3DES uses the same modes that DES uses; it just repeats them three times using three different keys. Other than the number of iterations, there are no differences between the two algorithms. This similarity causes 3DES to suffer from some of the same weaknesses as DES. These weaknesses motivated the industry to replace 3DES with more modern algorithms, particularly AES, discussed next. EXAM TIP 3DES made up for some of DES’s weaknesses, but it did not significantly change the algorithm. It puts plaintext through more iterations than DES, but it still suffers from some of the same weaknesses. AES The Advanced Encryption Standard (AES) is a symmetric block cipher that can use block sizes of 128 bits, with key sizes of 128, 192, and 256 bits. It uses 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys. Like DES, AES can use different modes to encrypt and decrypt data. Most attacks on AES are theoretical in nature—referred to as side-channel attacks, which take advantage of ineffective implementations of the AES algorithm in the cryptosystem, versus the algorithm itself. EXAM TIP AES is the de jure encryption standard for the US government and the de facto standard for private and commercial organizations. It is a block cipher that uses 128-bit block sizes, with 128-bit, 192-bit, and 256-bit keys. It uses 10, 12, and 14 rounds, respectively, for these keys. AES supports all the modes listed under DES, but tends to use the much lowerlatency mode called Galois/Counter Mode (GCM). GCM starts with CTR mode, but adds a special data type known as a Galois field to add integrity. GCM is an authenticated encryption mode of operation. NOTE You’ll sometimes hear AES called by its original name, Rijndael, derived from the last names of its two Belgian developers, Vincent Rijmen and Joan Daemen. 02-ch02.indd 101 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 102 Blowfish Blowfish is a block cipher that accepts 64-bit blocks and has a wide range of variable key links, from 32 bits all the way up to 448 bits. It uses 16 rounds of encryption, just as DES does. It is widely implemented in different software encryption solutions and is considered a good choice for a strong encryption algorithm, since there have been no more effective complete cryptanalysis solutions published to date. The designer, Bruce Schneier, placed Blowfish in the public domain, free for all to use. Twofish Twofish is a symmetric block algorithm that uses a 128-bit block size. It can use 128-bit, 192-bit, or 256-bit keys. Like DES, it uses 16 rounds of encryption. It is viewed as a successor to Blowfish. Although there have been some published partial theoretical attacks against Twofish, there are currently no publicly known attacks against it. Like Blowfish, Twofish has been placed in the public domain, making it freely available for anyone to use. EXAM TIP Although AES is the official US standard, both Blowfish and Twofish are exceptionally good encryption algorithms. Both use 64-bit blocks, and both perform 16 rounds of encryption. Blowfish can use key sizes from 32 to 448 bits, and Twofish uses key sizes of 128 bits, 192 bits, and 256 bits. Longer keys provide better key strength. RC4 Rivest Cipher 4 (RC4) is a streaming symmetric algorithm (unlike the block algorithms discussed previously in the module). Because it is a streaming cipher, it uses only one round of encryption. RC4 can use key sizes from 40 to 2048 bits in length. It’s a very fast protocol, as all streaming ciphers are. RC4 uses a key stream (stream of pseudorandom bits injected into the encryption process), which is then combined with plaintext using the XOR function to encrypt them into ciphertext. RC4 is most popularly used in wireless encryption with the older, now obsolete and cryptographically broken Wired Equivalent Privacy (WEP) protocol. It can also be found in versions of the Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols. RC4 has some documented weaknesses, which makes it unsuitable for future implementations. Current software vendors advise against its use, and the Internet Engineering Task Force’s (IETF) RFC 7465 eliminated its use in TLS. EXAM TIP RC4 is likely the only example of a streaming cipher you will see on the exam. All the other symmetric algorithms discussed throughout this book are block ciphers. Summary of Symmetric Algorithm Characteristics Table 2-1 summarizes the characteristics of the different symmetric algorithms. 02-ch02.indd 102 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-4: Asymmetric Cryptosystems 103 Symmetric Algorithm Block or Streaming Block Size Rounds Key Size Notes DES Block 64-bit 16 56 bits (64 bits total, with 8 bits for parity overhead) Uses five modes of operation: ECB, CBC, CFB, OFB, and CTR. 3DES Block 64-bit 16 168 bits (three 56-bit keys) Repeats DES process three times. AES Block 128-bit 10, 12, and 14 (based on key size) 128, 192, and 256 bits Encryption standard for the US government; GCM mode is popular. Blowfish Block 64-bit 16 32–448 bits Public domain algorithm. Twofish Block 128-bit 16 128, 192, and 256 bits Public domain algorithm. RC4 Streaming N/A 1 40–2048 bits Used in WEP, SSL, and TLS; largely deprecated in current technologies. Table 2-1 Summary of Symmetric Algorithms Module 2-4: Asymmetric Cryptosystems This module covers the following CompTIA Security+ objective: • 2.8 Summarize the basics of cryptographic concepts Developers have created and deployed numerous asymmetric key cryptosystems over the years to provide robust key exchange and secure data communications. This module explores the five most common asymmetric cryptosystems. Some of the data here is historical, but all of it informs modern cryptosystems. Let’s look, in order, at these cryptosystems: • • • • • RSA Diffie-Hellman PGP/GPG ECC ElGamal RSA The RSA cryptosystem enables you to create and use a public-private key pair. It generates keys based on the mathematical problem of the difficulty of factoring two very large prime numbers (each generally up to several hundred digits in length). RSA uses one round of encryption, and its typical key sizes range from 1024 to 4096 bits. 02-ch02.indd 103 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 104 Although RSA is considered very secure, keys of smaller sizes have been broken in various published attacks. Still, these attacks are largely based upon faulty implementations of the protocol, rather than the protocol itself. RSA is pretty much the de facto asymmetric algorithm used in most public key cryptography implementations today. Figure 2-12 demonstrates how RSA works, using simple prime numbers and the CrypTool learning program. NOTE RSA is the de facto asymmetric protocol used for generating publicprivate key pairs. The name RSA reflects the first letters of its creators, Ron Rivest, Adi Shamir, and Leonard Adleman. Figure 2-12 Simple demonstration of the RSA algorithm (screenshot from the CrypTool cryptography learning program) 02-ch02.indd 104 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-4: Asymmetric Cryptosystems 105 Diffie-Hellman The Diffie-Hellman (DH) protocols enable you to use asymmetric key exchange to give both sides of a conversation a single symmetric key. This means that two parties can use a nonsecure channel to establish a secure communications session. This secure key exchange works even when the parties have no previous relationship. DH offers a much faster connection compared to RSA. RSA provides great security, but requires a lot of computation and complex key exchange procedures. If you prefer speed over security, DH is the asymmetric algorithm for you! DH uses discrete logarithms, modulo arithmetic, and prime numbers to generate key pairs randomly that derive a symmetric key without ever sending any private information. Part of the DH key exchange process requires each side to create a temporary key, called an ephemeral key, which is used in only one exchange and then discarded. This ephemeral key usage is called Diffie-Hellman Ephemeral (DHE). DH relies on pseudorandom number generation to create the ephemeral keys. In most cases, this relies on pseudorandom number code that uses aspects of the underlying system like dates, MAC address of the network interface card (NIC), and other seemingly random information to make these values. Unfortunately, dates and MAC addresses really aren’t random; in theory, a malicious actor can use this against you. To fight against this, several alternatives exist. One alternative is to use a larger modulus: an important value that helps DH derive keys. A preset modulus of a specific size is called a DH group. As long as both sides agree to a group size, we can improve DH while still providing backward support for systems that only can derive smaller keys. Here are a few examples of DH groups: • • • • Group 1 Group 2 Group 5 Group 14 768-bit modulus 1024-bit modulus 1536-bit modulus 2048-bit modulus Another alternative is to skip ephemeral keys with DH and use something more resilient, such as Elliptic-Curve Diffie-Hellman Ephemeral (ECDHE). ECDHE skips pseudorandom number generation and instead uses ephemeral keys calculated using elliptic-curve cryptography, discussed later in this module. ECDHE is negotiated by groups as well: • Group 19 25-bit elliptic curve • Group 20 384-bit elliptic curve • Group 21 521-bit elliptic curve NOTE Many applications (such as secure Web sites) use RSA for authentication and DH for key exchange. 02-ch02.indd 105 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 106 PGP/GPG Pretty Good Privacy (PGP) is a cryptography application and protocol suite used in asymmetric cryptography. PGP can use both asymmetric and symmetric keys for a wide variety of operations, including bulk encryption, data at rest encryption (including both file and full disk encryption), key-pair generation, and key exchange. Unlike other public key cryptography schemes, PGP uses a web-of-trust rather than a public key infrastructure. (See Module 2-7 for details.) Although PGP is considered a commercialized, proprietary version, it has an open-source equivalent, Gnu Privacy Guard (GPG). The various versions of PGP and GPG comply with the OpenPGP standard, an IETF standard published as RFC 4880. EXAM TIP With PGP/GPG, think e-mail here. That’s where you’ll see these standards in play. ECC Elliptic-curve cryptography (ECC) is an asymmetric method of cryptography based on problems involving the algebraic structure of elliptic curves over finite fields. (Say that three times fast!) ECC has many uses, including variations that apply both to encryption and digital signatures. ECC has special uses involving mobile devices. It requires low computational power and memory usage, so ECC has been widely implemented in smartphones and other low-power mobile devices. EXAM TIP Expect a question on common use cases involving low-power devices, such as smartphones, on the exam. ECC provides the answer. ECC typically uses much smaller key sizes than other asymmetric algorithms, but these smaller-sized ECC keys are also harder to break. The largest known ECC key broken to date is only a 112-bit key, for example, compared to a 768-bit key size that has been broken with RSA. ElGamal ElGamal is an asymmetric algorithm that can be used for both digital signatures and general encryption. (See Module 2-6 for the details on digital signatures.) Taher Elgamal based his eponymous algorithm partially on Diffie-Hellman key exchange algorithms. ElGamal uses mathematical problems related to computing discrete logarithms. You’ll see ElGamal used in hybrid cryptosystems, where ElGamal encrypts the comparatively tiny symmetric key and some other (faster) scheme encrypts the message. It’s also widely used in open standards and cryptosystems, including PGP and GPG. 02-ch02.indd 106 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-5: Hashing Algorithms 107 The US government’s Digital Signature Algorithm (DSA) is based upon the ElGamal signature scheme. Module 2-5: Hashing Algorithms This module covers the following CompTIA Security+ objectives: • 2.1 Explain the importance of security concepts in an enterprise environment • 2.8 Summarize the basics of cryptographic concepts IT professionals use several hashing algorithms to ensure the integrity of data and source. This module starts with a brief discussion of how hashing works—a rehash of the introduction in Module 2-2, so to speak. [Insert groan here at bad pun.] Then we’ll explore the four most common hashing algorithms: • • • • MD5 SHA RIPEMD HMAC Hashing Process Encryption necessarily implies decryption. Plaintext transformed through encryption into an unreadable state can be decrypted and returned to a plaintext state. Hashing does not encrypt text; it generates a representation of that text, which is the hash or message digest. A hash is not the plaintext itself, but rather a unique identifier for the text, like a fingerprint. Note that hashing does not use keys at all, only algorithms, also making it less like encryption and decryption. Theoretically, an identical piece of plaintext will always produce the same hash value, assuming that you use the same hashing algorithm. Likewise, no two different pieces of plaintext should ever produce the same hash, given the same algorithm, although it happens. These accidentally matching hashes, called collisions, can enable a miscreant in theory to generate a piece of data with the right hash to fool others as to its integrity. Figure 2-13 illustrates the collision process a bit more clearly, where two differing texts run through the hashing algorithm, but result in identical hashes. Several older hashing algorithms can produce collisions. As this module addresses the different hashing algorithms, we’ll point out the older, collision-prone algorithms. NOTE Hashing is not the same thing as encryption and decryption. Hashes cannot be reversed or decrypted; they can only be compared to see if they match. 02-ch02.indd 107 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 108 AC 68 53 0B E5 FF 26 34 E9 F2 7C E8 1F 62 4D 5A 9F C1 E7 89 14 05 F0 7A AC 0D 69 A9 7A A2 6C 0F Variable-Length Text #1 Hashing Algorithm Fixed-Length Hash or Message Digest #1 AC 68 53 0B E5 FF 26 34 E9 F2 7C E8 1F 62 4D 5A 9F C1 E7 89 14 05 F0 7A AC 0D 69 A9 7A A2 6C 0F Variable-Length Text #2 Hashing Algorithm Fixed-Length Hash or Message Digest #2 Figure 2-13 The hashing process and collisions Hashing supports confidentiality (in the case of hashing passwords, for instance) and integrity. For confidentiality, you can hash a password (run it through the hashing algorithm) and send the resulting hash over an untrusted network for authentication. You would not need to transmit the actual password (Figure 2-14). When the authenticating server receives the hash, it takes the password hash it has stored in the credentials database and compares it to the hash it received. If they match, the server knows that the user also knew the correct password, and it allows authentication. If the hashes don’t match, the server refuses authentication, because the user obviously did not know the correct password, which in turn did not generate the correct hash. Hashing thus supports authentication as well as confidentiality and integrity. EXAM TIP Expect questions on common use cases for supporting authentication, confidentiality, or integrity. Hashing provides all three. Some systems encrypt password hashes during transmission using symmetric key cryptography and then decrypt them on the receiving end to protect the hash during transmission. This action blocks an obvious attack option. Figure 2-14 Sending a password’s hash instead of the password itself 02-ch02.indd 108 I can’t read the password if it’s sent as a hash! 1ad487ce2354b5ff69211be87e 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-5: Hashing Algorithms 109 An attacker can intercept a password hash as it travels over a network. The attacker won’t have the actual password at that point, of course, and can’t reverse the hash to get it, but she can use various methods to perform the same type of hash comparisons against a list of potential passwords and generate an identical hash, letting her discover the original password. An encrypted hash blunts that capability. Because identical pieces of plaintext always produce the same hash value, using the same hashing algorithm on both enables you to tell if a piece of text has changed, even by one binary digit (bit). If even a single 1 or 0 bit changes in the text, the hash produced will differ from the hash of the original piece of text. In this way, comparing hashes of two supposedly identical pieces of plaintext can verify the integrity of the original. If the hashes match when compared, the samples of text are identical and have not been altered. If the hashes differ when compared, however, then a change has occurred between the original text and what was received, violating integrity. EXAM TIP Hashing can be used to assure both confidentiality and integrity. MD5 The Message Digest 5 (MD5) algorithm generates a 128-bit hash, 32 hexadecimal characters long, and it replaced an earlier version of the MD series, MD4. MD5 has weaknesses, however, and researchers have demonstrated collisions (and thus vulnerability to collision attacks) many times, even using off-the-shelf consumer laptops. Despite deprecation by security experts—as in, “don’t use this broken thing!”—many low-security situations still use it, even in 2020. MD5 is also used as part of other cryptographic methods, including the Extensible Authentication Protocol (EAP), as part of its EAP-MD5 implementation. EXAM TIP MD5 produces a 128-bit message digest, consisting of 32 hexadecimal characters, regardless of the length of the input text. SHA The US National Security Agency (NSA) developed the Secure Hash Algorithm (SHA) standards to provide cryptographic hash functions, starting in 1993. Since the initial release—SHA-0, SHA has seen several iterations, including SHA-1, SHA-2, and SHA-3. The 160-bit SHA-1 algorithm, originally designed as the standardized Digital Signature Algorithm for the United States, produces 40-character hashes. SHA-1 was a contemporary of MD5 and had similar cryptographic flaws. SHA-2 is made up of two separate algorithms, SHA-256 and SHA-512, but each has minor versions that include SHA-224 and SHA-384. SHA-3 uses a hash function called Keccak that makes it different internally than SHA-1 and SHA-2. It has the same hash lengths as the SHA-2 versions. 02-ch02.indd 109 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 110 EXAM TIP SHA-1 and SHA-2 have been replaced by the latest iteration of SHA, known as SHA-3, which is an implementation of the Keccak hashing function. Also, you might see SHA on the exam as Secure Hashing Algorithm, so don’t get confused. The exam means SHA. RIPEMD RACE Integrity Primitives Evaluation Message Digest (RIPEMD) is a hashing algorithm not often seen in practical implementation. It was developed in an open-standard type of environment, as opposed to SHA. RIPEMD comes in 128-, 160-, 256-, and 320-bit versions. Again, it is not in widespread use, despite the relatively stable and secure implementation of the RIPEMD-160 iteration, which is the most common. HMAC Hash-based Message Authentication Code (HMAC) is used in conjunction with a symmetric key both to authenticate and verify the integrity of the message. HMAC can use either MD5 or SHA series of hashing algorithms (and noted as HMAC-MD5 or HMAC-SHA1/2/3, respectively). The HMAC process produces a hash value, the message authentication code (MAC), whose length and strength correspond to whichever hashing algorithm was used to create it. Here’s how it works. You already know that a given piece of plaintext or message produces the same hash every time, as long as you use the same hashing algorithm. This can be used to verify integrity; however, anyone can send a message that can be verified in terms of integrity, if the hashes match. But you cannot verify the authenticity of the message—that is, who sent it—and you cannot verify who will be able to receive it. HMAC uses a secret (symmetric) key with the hashing process, so that a given message produces a unique hash using that symmetric key. If someone does not have the key, she cannot reproduce the hash of the message, so that neither integrity nor authenticity can be verified. Only someone who has the secret key can successfully produce the same hash. This verifies not only integrity but also authenticity, since only the person having the secret key could have produced that unique hash and sent the message. EXAM TIP HMAC can use hashing functions and symmetric keys to produce a message authentication code (MAC), used to ensure both integrity and authenticity of a message. Module 2-6: Digital Signatures and Certificates This module covers the following CompTIA Security+ objectives: • 2.8 Summarize the basics of cryptographic concepts • 3.9 Given a scenario, implement public key infrastructure 02-ch02.indd 110 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-6: Digital Signatures and Certificates 111 Figure 2-15 Secure Web site, Hello! Hello, www.totalsem.com! Hello! I want this to be Secure HTTP. OK! Here’s my public key: 1ab4e88d923cc13d4aa…. Asymmetric encryption relies heavily on trust. When you access a secure Web site to make a purchase, for example, you need to trust in the security of the connection between the Web server and your client before putting in a credit card number. Two related cryptographic functions create this security, digital signatures and digital certificates. Digital Signatures Secure Web sites use RSA keys for asymmetric encryption. Every connection to a secure Web site requires a key exchange. At the very least, the Web server provides its public key to the client so the client can encrypt messages securely. In some cases, the client will share its public key (Figure 2-15). The challenge to key exchange isn’t handing out the keys. The Web server and client can automatically share their public keys the moment they connect. The problem comes with the key itself. Imagine a scenario where a third party intercepts the data and tries to send a bogus public key to the client (Figure 2-16). Digital signatures address this scenario. To send a message in a typical asymmetric encryption cryptosystem, the sender encrypts using the recipient’s public key; the recipient decrypts using her private key. The reverse, however, can also work. The sender can encrypt with his private key; the only key that would enable decryption is his public key. This concept makes digital signatures possible. Here’s the full process of creating a digital signature. Figure 2-16 Third parties can be evil! OK! Here’s my (evil) public key: 9c5bba277d1aa2003d4a8c…. www.totalscam.com 02-ch02.indd 111 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 112 To prove that the public key your client receives came from the proper server, the Web server adds a digital signature. The Web server takes the current Web page and does the following: 1. Encrypts the page with the client’s public key. 2. Hashes the page. 3. Encrypts the hash with the server’s private key. 4. Sends the page, the public key, and the hash to the client. Now it’s the client’s turn: 1. The client decrypts the hash using the server’s public key to verify it really came from the server. (Only the server’s public key can decrypt something encrypted with the server’s private key.) 2. The client decrypts the message with the client’s private key. Figure 2-17 helps describe this process. The hash value encrypted with the private key and that accompanies the public key is a digital signature. NOTE Digital signatures are one of the very few places where private keys are used to encrypt. Normally, public keys encrypt and private keys decrypt. Digital signatures alone work great to verify the identity of a source. Successfully decrypting the message using the source’s public key means the message could only have come from that source. Figure 2-17 Proof that the message came from the owner of the private key I’ll take the current page you’re looking at… Encrypt it with my PRIVATE key and HASH the result… Encrypt the HASH with my private key Then send you the page as well as my public key and the HASH If you can decrypt it with the public key and generate the same HASH You’ll know that only I, the holder of the private key, sent it. 02-ch02.indd 112 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-6: Digital Signatures and Certificates 113 Who do I trust? NO! NO! HERE is the totalsem.com public key, digitally signed. Here’s the totalsem.com public key, digitally signed. Figure 2-18 Who can you trust? Digital Certificates A digital signature is only good for verifying that the entity who sent you a public key is legitimately the one who possesses the corresponding private key. But how do you know that public key really came from the Web site, or the owner of that e-mail address, or the VPN service, or whatever other thing you want to connect to that you need to know you can trust? You need something more than a digital signature (Figure 2-18). You might at this point say, “I know I’m on the right Web site because it says so in the address bar” or, “I know this e-mail came from mike@totalsem.com, because that’s who the e-mail said it came from.” This is not acceptable. First, it’s easy to make another Web site look just like one you know (Figure 2-19). Equally, it’s easy to make another service—e-mail is a great example—look like it came from a known source. This process But the Web site said www.totalsem.com! Oh, really? Figure 2-19 It’s easy to deceive. 02-ch02.indd 113 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 114 Figure 2-20 A certificate should have a third-party signature. And I, Trusted Third Party, add my digital signature as well, signifying this is www.totalsem.com! Here’s the totalsem.com public key, digitally signed. Digital Certificate is called spoofing. Simply relying on the fact that something looks like it’s a legitimate source isn’t good enough. (And how closely do most people look at URLs anyway?) Worse, a fiend can use Unicode to whack out URLs to the point where you could swear you know where you are, but you are at a completely different URL. To create trust in this scenario requires a digital certificate, an electronic file specifically formatted using industry standards that contains identifying information. That’s a mouthful! Think of a digital certificate like a Word document with a bunch of spaces to fill in with specific information. There are different digital certificate “forms” for different jobs (e-mail, Web servers, code signing, and many more). Any digital certificate will store a public key with a digital signature, personal information about the resource (URL, e-mail address, phone numbers, whatever), and a second digital signature from a third party you both trust (Figure 2-20). The rest of this module concentrates on the types of digital certificates and their formats and tours a typical certificate on a PC. NOTE Module 2-7 goes into depth on maintaining digital certificates. Touring a Certificate Let’s look at a digital certificate. In Windows, you can see your certificates by opening any Web browser’s Settings and locating a certificates option. In Microsoft Edge, for example, click the icon with three horizontal dots in the upper-right corner and choose Settings. Select Privacy and Services, then click the Manage Certificates button to open the Certificates dialog box (Figure 2-21). 02-ch02.indd 114 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-6: Digital Signatures and Certificates 115 Figure 2-21 Getting to the Certificates dialog box in Microsoft Edge NOTE All Web browsers have a certificate location. Take your time, you’ll find it. The Certificates dialog box features several tabs. For this module, pick any tab, select any certificate on that tab, and then click View (or whatever your system says) to see the certificate in detail. You should see something like Figure 2-22. Now click the Details tab at the top. On the Show pull-down menu, select Version 1 Fields Only to see something like Figure 2-23. Click each field as you read through the following descriptions to see what each value stores. • Version The common certificate format is X.509. It started with version 1. Modern certificates are version 3. This field shows the X.509 version of this certificate. • Serial number A unique number given to this certificate by the issuing body. • Signature algorithm The type of encryption and hash used by this certificate. • Signature hash algorithm Same as signature algorithm. (It’s a Microsoft thing.) • Issuer X.509 formatted name of issuer of this certificate. (See “Certificate Attributes” next.) • Valid from Time the certificate was granted. • Valid to Time the certificate expires. • Subject To what this certificate is issued in X.509 format. • Public key The public key for the certificate. 02-ch02.indd 115 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 116 Figure 2-22 Certificate view in Windows There’s a lot more to see if you change Show: to <ALL>, but there are two fields that warrant note here: • Thumbprint The certificate’s digital signature. • Authority Key Identifier The third party’s digital signature. 02-ch02.indd 116 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-6: Digital Signatures and Certificates 117 Figure 2-23 Typical certificate details in Windows Certificate Attributes Digging deeper into certificates reveals a lot more information, specifically certificate attributes that vary according to the purpose of the certificate. Figure 2-24 shows a local Trusted Root Certification Authority certificate from COMODO ECC Certification Authority. 02-ch02.indd 117 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 118 Figure 2-24 Local Trusted Root CA certificate Note the Issuer details in the bottom pane: • • • • • CN The canonical name, the full name of the issuing body O The organization, COMODO CA Limited L The locality, Salford S The state or province, Greater Manchester C The country or origin, Great Britain Contrast the certificate shown in Figure 2-24 with the certificate shown in Figure 2-25, which comes from the Chrome Web browser connected to https://www.amazon.com. The Details tab is selected again, but the Subject is chosen in the top pane rather than Issuer. As you might expect, it reveals the details about Amazon, including the CN, O, L, S, and C; Amazon’s headquarters are in Seattle, Washington, United States of America. 02-ch02.indd 118 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-6: Digital Signatures and Certificates 119 Figure 2-25 Web certificate attribute details Getting a Certificate Virtually all cryptosystems that use asymmetric cryptography require a certificate. Probably the best example is a secure Web site. Let’s say you want to set up a secure (HTTPS) Web server. You can spin up your own server and load some Web server software on your own, but if you want to use HTTPS, you’ll need a certificate. To get a certificate, submit information to a certificate issuing organization, called a certificate authority (CA). There are a handful of these organizations, though three dominate the market: IdenTrust, DigiCert, and Sectigo (formerly Comodo). Before you give a certificate issuing organization your credit card details, you need to generate a certificate signing request (CSR) on your Web server, as described in the “Certificate Life Cycle” section of Module 2-7. Figure 2-26 shows part of this process in Microsoft Internet Information Services (IIS). Once you create the CSR, cut and paste the information into an online form. Depending on the certificate, you’ll get your certificate sent via e-mail or through a Web interface. In most cases, the certificate installs itself. You can import if necessary. 02-ch02.indd 119 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 120 Figure 2-26 Creating a CSR in IIS NOTE You don’t have to pay for third parties to sign certificates (e.g., Let’s Encrypt, https://letsencrypt.org, is a popular free certificate issuer, backed by IdenTrust). Self-signed certificates work just fine within your network for services that require certificates—applications and such on the corporate intranet, for example. There’s no reason to pay for certificates for internal use. Make certain those self-signed or untrusted-signed certificates never see the rest of the world. Module 2-7: Public Key Infrastructure This module covers the following CompTIA Security+ objectives: • 2.8 Summarize the basics of cryptographic concepts • 3.9 Given a scenario, implement public key infrastructure Public key infrastructure (PKI) implementations combine symmetric and asymmetric key cryptographic methods with hashing to create robust and secure systems. This module puts together all the information in Modules 2-1 through 2-6 of this chapter to describe these systems. The module starts with keys, algorithms, and standards. The second section explores PKI services. The third section discusses digital certificates and PKI structure. We’ll look at key safety next and then finish with trust models. 02-ch02.indd 120 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 121 PKI puts cryptography into practical application. IT professionals use PKI to implement strong authentication and encryption schemes to protect data confidentiality and integrity and to ensure non-repudiation. Let’s get started. Keys, Algorithms, and Standards Hybrid cryptographic systems incorporate the advantages of asymmetric and symmetric algorithms, while at the same time making up for the disadvantages each has. Symmetric algorithms are fast, and they can encrypt large amounts of data efficiently. Symmetric cryptography suffers from key exchange and scalability problems. Asymmetric cryptography, on the other hand, has no issues with key exchange. It’s also very scalable, since it only requires that each individual have a public and private key pair. Unfortunately, asymmetric cryptography doesn’t do very well with speed or encrypting large amounts of data. PKI takes advantage of these different positive aspects of both asymmetric and symmetric key cryptography and uses each, along with hashing algorithms, for different aspects of identification, authentication, encryption, and non-repudiation. Let’s look now at keys and algorithms that relate to PKI. EXAM TIP PKI is composed of several components and technologies, as well as the infrastructure and processes used to manage certificates. Keys Asymmetric cryptographic systems use a public and private key pair. Both keys are mathematically related, but you cannot use one to derive the other. The keys are generated using various mathematical algorithms. What one key in a pair encrypts, only the other key in the same pair can decrypt. Public keys are given to anyone who wants them, and private keys are kept confidential, protected by the individuals who own them. To exchange messages between two parties, each must have a public and private key pair. Each party must also possess the public key of the other party. When one person wants to send an encrypted message to the other, the sender encrypts the message using the receiver’s public key. Then, the receiver decrypts it using the receiver’s private key, since that’s the only key in the pair that can decrypt what the public key encrypts. This is demonstrated in Figure 2-27. Figure 2-27 Communicating using public and private keys 02-ch02.indd 121 Meghan’s Public Key Amy’s Public Key Amy’s Private Key Meghan’s Private Key Amy Meghan 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 122 Symmetric cryptography, on the other hand, uses only one key. Both parties must possess that same key to encrypt and decrypt data. Getting the same key to each party securely poses the major obstacle in symmetric cryptography. In a hybrid cryptographic system, party A generates a symmetric key—often called a session key—and encrypts that key using party B’s public key, and then sends the encrypted key to party B. Party B, the receiving party, decrypts the encrypted session key with party B’s private key. After that, faster communications can take place using the symmetric session key. Using this hybrid approach with asymmetric and symmetric keys ensures confidentiality, since both data and the session keys are encrypted. It doesn’t, however, ensure authenticity or integrity of the message, nor does it provide for non-repudiation. Adding hashing algorithms into the process provides those services; we’ll discuss those momentarily. EXAM TIP The CompTIA Security+ SY0-601 objectives use specific wording on this topic. So a common use case for cryptography is supporting confidentiality. The hybrid cryptographic system clearly accomplishes this goal. Algorithms Previous modules discussed the algorithms, both symmetric and asymmetric, employed in PKI. These include symmetric algorithms such as AES and asymmetric algorithms such as RSA for key generation and Diffie-Hellman for key exchange. PKI also uses hashing algorithms, such as MD5, RIPEMD, and the SHA family of algorithms. Let’s look at specific PKI standards to see how they put the algorithms together. PKI Standards PKI implementations use one of several standards. The primary standard is X.509; other standards apply to specific industries. The ITU Telecommunication Standardization Sector (ITU-T) X.509 standard describes how digital certificates are constructed, including what information they will contain, their uses, and their formatting. The X.509 standard also describes processes involved with issuing certificates, as well as other processes in the certificate life cycle. NOTE The initialism “ITU” has changed meaning over the years, from International Telegraph Union, formed in 1865, to the International Telecommunication Union, created in 1932. ITU-T morphed from the Comité consultatif international téléphonique et télégraphique (CCITT), formed in 1956, to the current initialism, created in 1993. (And none of this brief history lesson shows up on any CompTIA exam.) Other somewhat proprietary standards that you’ll encounter in PKI come from different industry segments, but usually comply with open standards. One set of these standards is the Public Key Cryptography Standards (PKCS), developed by RSA Security. 02-ch02.indd 122 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 123 The PKCS describe certificate construction and use. Cryptosystems use a PKCS #7 file digital certificate, for example, to sign or encrypt messages, such as e-mail. A PKCS #12 file contains public and private keys and is encrypted for secure key storage. Other vendors, such as Microsoft and Apple, for example, also have proprietary ways of issuing and managing certificates throughout the certificates’ life cycle, although these standards usually comply with the X.509 standards. EXAM TIP The primary standard used in PKI is the X.509 standard, which describes the certificate format and how it is used. PKI Services In addition to confidentiality, PKI provides for secure key exchange, message authentication and integrity, and non-repudiation. The next few sections discuss how PKI provides these different services. We’ll also revisit digital signatures. Key Generation and Exchange PKI has technologies and methods built in for several different processes. Among those are key generation and key exchange. Key generation is the process of creating a public and private key pair, which is then issued to an individual, based upon his or her confirmed identity. RSA is the most popular key generation algorithm, although there are others. Key exchange is a process, typically using Diffie-Hellman algorithms, that assists in the creation and secure exchange of symmetric keys, typically session keys used for one communications session only. After keys are generated, public and private keys are used to encrypt and decrypt session keys once they are transmitted and received, respectively, by both parties. Non-repudiation Non-repudiation means that a person cannot deny that he or she took a specific action. The person’s identity has been positively verified, and any actions that person takes are traced back to that identity. PKI assures non-repudiation by using public and private keys. The certificate authority must positively identify and authenticate an individual before the CA issues a key pair. After issuing that key pair, the CA digitally signs the individual’s certificate using the CA’s private key. This signing confirms the CA has validated the user’s identity. Finally, because only the issuing organization can sign with its private key, this verifies that the certificate came from a valid issuing organization. Once Jack gets his key pair from the certificate authority, any message he signs using his private key verifies he sent the message. This assumes that Jack did the right thing and protected his private key, of course. If a message is signed using a key pair owned by Jack, in other words, he cannot deny that he sent the message. This assures non-repudiation. EXAM TIP The CompTIA Security+ SY0-601 objectives use specific wording on this topic. So a common use case for cryptography is supporting nonrepudiation. PKI clearly accomplishes this goal. 02-ch02.indd 123 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 124 Message Integrity PKI can provide message integrity through hashing algorithms. Using hashing algorithms such as SHA-512, for instance, you can hash messages to generate unique fingerprints, or hashes, that can be checked both before transmission and after the message is received. If the hashes compare and match, you can be assured of data integrity. If they compare and do not match, you know that something (or someone) has changed the integrity of the message. Message integrity can be altered accidentally through simple “bit-flipping” during bad transmission conditions or intentionally by some malicious actor. Message integrity is assured by also incorporating hashing algorithms into the PKI process. Although there are several possible ways to do this, the simplest way is to hash the message and encrypt both the message and the hash and send them on to the recipient, so that when the recipient gets the message, he can simply decrypt the message with his private key and then rehash the message to generate a hash that he can compare to the hash he received. The recipient doesn’t do this manually; the automatic PKI processes take care of these steps at the application level. EXAM TIP The CompTIA Security+ SY0-601 objectives use specific wording on this topic. So a common use case for cryptography is supporting integrity. PKI clearly accomplishes this goal. Digital Signatures PKI systems incorporate digital signatures to authenticate the source of a message. Encrypting a message with a private key assures the recipient of the source when the corresponding public key decrypts that message. Add in the hashing component of digital signatures and you’ve got a winning combination, as discussed back in Module 2-6. Digital Certificates and PKI Structure This section explores how a basic public key infrastructure organization works, describing some of the elements in a PKI, such as the certificate and registration authorities, as well as the certificate revocation list. First, however, we’ll take another look at digital certificates and describe them in more detail. Digital Certificates As mentioned earlier, digital certificates are simple electronic files. The X.509 and PKCS standards determine the specific formats for digital certificates, as well as the file types and formats. Digital certificates come in a variety of file formats, including those with .cer and .pem file extensions. (We’ll cover all of these in detail in Module 11-5.) Additionally, there is a variety of types of certificate files, and each of these may fulfill a unique function in a PKI, such as a certificate request file. Digital certificates can be stored on several types of media, such as USB sticks, mobile devices, internal computer storage, and even centralized repositories on a network or the Internet. 02-ch02.indd 124 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 125 Certificates come in a variety of types, each type serving one or more purposes such as the following: • • • • Signing and encrypting e-mails Identifying and authenticating networks Identifying servers Digitally signing software, verifying its authenticity from a publisher Certificates typically contain a variety of information, known as certificate attributes, including the public key of the individual and information that identifies that person, the issuing organization, and valid dates and functions for the certificate to be used (Figure 2-28). Cryptographic systems can use certificate attribute filters to allow or deny specific access. A filter might examine the organization (O) attribute and allow only traffic that comes from Total Seminars, for example. EXAM TIP The CompTIA Security+ SY0-601 objectives use specific wording on this topic. So a common use case for cryptography is supporting authentication. Certificates clearly accomplish this goal. Figure 2-28 A digital certificate 02-ch02.indd 125 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 126 Certificate Life Cycle Managing a digital certificate from issuance, through use, and finally disposal refers to the process of managing the certificate over its life cycle. That life cycle follows four main stages: 1. Registration by an entity 2. Issuance of certificate from certificate authority 3. Maintenance by the certificate authority 4. End of life through expiration, suspension, or revocation The sections below explore both the life cycle stages and the entities involved. We’ll look at certificate registration, certificate authorities, certificate servers, and certificate end of life features. Certificate Registration A certificate’s life cycle begins when a user registers to receive a certificate. The person requesting the certificate must provide valid identification to the certificate authority (CA), the entity that issues and controls the digital certificates. Registration usually means the user must present identification that the issuing organization authenticates, thus verifying the person’s identity. Valid forms of identification that a requester may submit include her driver’s license, birth certificate, passport, photographs, and any other identification that the issuing organization requires. Once a user has submitted the required identification, the CA decides whether to issue the certificate and under what circumstances. NOTE Before issuing a certificate to an individual, the certificate authority must verify the individual’s identity. Certificate Authority As just mentioned, the certificate authority issues and controls digital certificates. The CA might be a commercial organization, such as GoDaddy, or it could be the user’s organization. Often, private organizations have internal CAs that issue digital certificates used specifically within the logical bounds of the organization. The CA also manages the certificate server (sometimes called the CA server), the host computer that generates keys and produces digital certificate files. The CA normally handles all user registration, identification, and validation processes, and it issues digital certificates to the user. In larger organizations, to help balance the workload for the CA, registration functions may be delegated to a separate registration authority (RA), which verifies user identities and then passes the information on to the CA for certificate generation. The CA makes decisions on whether to issue the certificate, under what circumstances, and with what caveats. When an entity requests a certificate, it submits a certificate signing request (CSR). The CA reviews the CSR, which contains the information that will be embedded in the digital certificate, including the public key, organization name, common 02-ch02.indd 126 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 127 Root CA Root CA Intermediate CA Subordinate CA Subordinate CA Subordinate CA End entity certificate End entity certificate End entity certificate Subordinate CA End entity certificate End entity certificate End entity certificate Figure 2-29 Simple CA hierarchy name, and so on. The CA then generates a certificate for the requesting entity. That certificate is called an end entity certificate. After generating certificates, the CA must also perform actions on them, such as renewing, suspending, or revoking them, as needed. EXAM TIP A certificate authority (CA) is the primary element in PKI. Depending on a host of factors, such as geographical considerations, supply chains, and so forth, a “single” CA—the root CA—creates a hierarchy of trust to subordinate CAs. The subordinate CAs have a chain of trust with the root CA; they in turn grant the end entity certificates. Additionally, a subordinate CA might also need its own subordinate CAs. The CA in the middle of the chain is called an intermediate CA (Figure 2-29). Certificate Servers Smaller organizations may use only one or two servers that manage all their certificate needs. Larger organizations, however, may have an entire hierarchy of servers. At the top of this hierarchy is the single master server, called the root CA server. The root issues its own self-signed certificate, unless the organization purchases and receives one from an external certificate authority. Whether self-signed or received from an external CA, the root CA server has the root certificate for the organization. All other certificates in the hierarchy derive from this trust point. NOTE Module 11-5 goes into much more detail on the various types of certificates. This module is an overview to help make PKI concepts make sense. The root CA server can also issue certificates for any other use, but it typically issues trusted certificates only to intermediate or subordinate servers. These intermediate 02-ch02.indd 127 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 128 Figure 2-30 A hierarchy of certificate servers Root CA Intermediate CA User Authentication Certificate CA E-mail Certificate CA Intermediate CA Code Signing Certificate CA servers may perform all the different certificate authority functions, or they may perform only very specific functions, depending upon the needs of the organization. Normally, once an organization has set up intermediate or subordinate servers, they take the root CA server offline to protect it against possible compromise. The root CA server may be brought back up online only occasionally for maintenance or to update certificate information. Figure 2-30 shows a typical arrangement of a hierarchy of certificate servers in an organization. NOTE An organization normally takes the root CA server offline after setting up intermediate and subordinate CA servers, to prevent compromise of the server and the root certificate. If the root certificate is compromised, all subordinate certificates that have been issued or signed by the root are also considered compromised and should be treated as no longer valid or trustworthy. Certificate Expiration, Suspension, and Revocation Certificates do not last forever. Certificates remain valid only for a specific period of time, and after that time they expire. This is because, like passwords, certificates could be compromised. Certificate expiration enables a user and the CA to monitor certificate compromise and periodically reissue certificates to ensure that a compromised certificate isn’t used over long periods of time. CA rules determine certificate lifetimes. An average time might be three years, but it may be a longer or lesser period, depending upon the circumstances under which the certificate was issued. For example, a temporary employee might receive a digital certificate that’s good for only a year. Before a certificate expires, the user and the issuing organization must take steps to revalidate the user, as well as their need for the certificate, and reissue it. A user cannot use an expired and thus invalid certificate. Most browsers and applications will display errors when trying to use or accept an expired certificate. Figure 2-31 gives an example of an expired certificate. 02-ch02.indd 128 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 129 Figure 2-31 An expired certificate Certificates can lose their validity even before their expiration dates. This usually requires some intervention from the CA and is usually because of adverse circumstances. A certificate may be suspended, which renders it invalid for a temporary, indefinite time period. Normally a certificate would be suspended if the user is on extended leave, or during an investigation, for instance. Suspending a certificate means that it could be reinstated, allowing a user to continue using the certificate, but only if and when the CA makes a conscious decision to do so. Revoking a certificate, on the other hand, means that the certificate is permanently rendered invalid. Once a digital certificate has been revoked, it can’t be reissued or reused. The CA might revoke a certificate if a user no longer needs it, if the user has been terminated or retires, or if the certificate has been misused or compromised in any way. If a certificate has been revoked, the CA must reissue a totally different certificate to the user if the CA determines that the user requires it. The CA publishes a certificate revocation list (CRL) that contains the certificates the entity has issued and subsequently revoked. Users can access this list to determine the validity of a certificate. If a certificate has been revoked, it is considered no longer valid 02-ch02.indd 129 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 130 Figure 2-32 A small sample of a CRL entry from Verisign and cannot be used. Certificate revocation lists can be published online, or they can be part of an automated process that application software checks from a centralized repository. Similarly, the Online Certificate Status Protocol (OCSP) is used to automate certificate validation, making checking the status of certificates seamless and transparent to the user. Most modern browsers and other applications that use digital certificates can use OCSP to check CRLs automatically for certificate validity. A sample from a CRL, downloaded to a user’s browser, is shown in Figure 2-32. OCSP permits users (through Internet browsers and other certificate-aware applications) to check for certificate expiration, suspension, and revocation before the certificate is accepted. In Figure 2-33, you can see an example of a revoked certificate, which in this case is a famous example of a certificate erroneously issued to a fraudulent party claiming to be Microsoft. The certificate was quickly revoked after the error was discovered. 02-ch02.indd 130 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-7: Public Key Infrastructure 131 Figure 2-33 A revoked certificate EXAM TIP Suspended certificates can be reused after the organization determines it is safe to reactivate them. Revoked certificates are never reused and are considered invalid forever. Key Safety Keys in PKI encrypt and decrypt data; losing a key means losing access to any data encrypted by the other key in the pair. That would be a bad thing! Two key management options protect organizations from such a loss, recovery agents and key escrow. Recovery Agent A recovery agent is a designated person or entity who has the authority to recover lost keys or data in the event the person holding the keys is not available. Recovery agents can work in a few different ways. One way requires the individual to store his private key in a secure area that a recovery agent can access in the event the individual is terminated or unavailable to decrypt data, for example, that had been encrypted with his private key. This would be the least desirable way, however, since non-repudiation would suffer 02-ch02.indd 131 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 132 because private keys are supposed to be kept private and confidential and accessible only by the user. Another, more common way would be to have the recovery agent maintain a different key that can decrypt any data encrypted by an individual. Key Escrow As you’ll recall from Module 2-1, key escrow is the practice of maintaining private keys, sometimes by an independent third party, so that they can be accessed in the event individuals are not able or unavailable to use them to recover data that has been encrypted. Organizations should approach this practice with caution, however, because, as mentioned previously, this can create issues with non-repudiation. Before an organization puts key escrow into practice, it should identify a secure, carefully executed, and transparent method of key escrow. An organization may want to implement key escrow to guard against the possibility that an individual will encrypt sensitive data and then leave the company suddenly, without a way for the organization to recover the data. Trust Models Most commercial certificate authorities are generally trusted by most browsers and applications, since their root certificate is usually contained in the root certificate store of most devices. Private CAs, however, such as an internal CA that issues certificates only to its own employees, may not generally be trusted by outside organizations. This would render the certificates they have issued as untrusted by anyone outside their own organization. Because of this, some trust models have evolved over the years to enable organizations to take advantage of each other’s digital certificates, permitting some level of trust between them. Let’s look at three trust modules: • Hierarchical trust • Cross-trust • Web-of-trust Hierarchical Trust A hierarchical trust is normally found within an organization, particularly a larger organization, and involves trust in digital certificates within organizational boundaries. Often, there are intermediate or subordinate CAs within a large organization that must trust each other. One subordinate CA may issue e-mail certificates, for example, and another may issue code-signing certificates. All the certificates, however, can be traced back and trusted through the originating root CA. This is possible with a hierarchical trust model, such that all subordinate and intermediate CAs trust each other because they trust the original root CA. Look again at Figure 2-29, shown earlier, as an example of a hierarchical trust model. Cross-Trust A cross-trust model is often used between two different organizations. In this trust model, organizations typically have their own certificate authorities and issuing servers. However, 02-ch02.indd 132 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 133 because of business partner arrangements, they must trust each other’s certificates so that their personnel can authenticate to access resources in each other’s security domains. A cross-trust model enables organizations to have their root CAs trust each other (and the certificates they generate) or even have specific subordinate CAs trust each other. This type of trust can be open to any certificate or limited only to very specific certificates issued under particular circumstances. Web-of-Trust A web-of-trust model is not typically used in a PKI. You’ll most often see this type of model used in smaller groups or organizations, typically in those that allow individual users to generate their own public and private key pairs. The use of Pretty Good Privacy (PGP) and Gnu Privacy Guard (GPG) between small groups of users is a prime example of a web-of-trust. In this model, there is no central issuing authority that validates user identities. It is left up to each individual user to trust another user’s certificates. While this works well in small groups, where each user has some level of assurance of the identity of another user, it’s typically not scalable to large groups of people or organizations. Module 2-8: Cryptographic Attacks This module covers the following CompTIA Security+ objectives: • 1.2 Given a scenario, analyze potential indicators to determine the type of attack • 1.3 Given a scenario, analyze potential indicators associated with application attacks • 2.8 Summarize the basics of cryptographic concepts • 4.1 Given a scenario, use the appropriate tool to assess organizational security Cryptanalysis, the science of breaking encryption, is as old as encryption itself. From Louis XVI at his palace in Versailles to the latest state-sponsored attacks, encryption has been successfully attacked many times. This module looks at some of the more common cryptographic attacks and the tools used to perform them. Understanding these attacks and their tools provides a better understanding on how to keep data secure. (Plus, it’s really fun to crack stuff!) The module starts with a general discussion of attack strategies and then examines attackable data. The third section explores password-oriented attacks and the tools commonly used in the attacks. The fourth section describes how to defend password storage. The module finishes with a look at a few attacks unrelated to passwords. Attack Strategies Every cryptosystem has an underlying algorithm, a key (or in the case of hashes, a digest), or some implementation of the cryptosystem itself, all of which the attacker understands. 02-ch02.indd 133 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 134 All cryptographic algorithms are known and rarely change, in accordance with Kerckhoffs’ principle (introduced in Module 2-1). Every cryptographic attack starts by careful inspection of the cryptosystem and aggressively probing and experimenting to find some form of weakness in one of those three aspects. NOTE Every cryptosystem currently in use has countries, universities, private organizations, and individuals who constantly experiment with them, looking for weaknesses. We need this research so that a weakness may be discovered and shared with others in IT security and adjustments may be made. Attack the Algorithm Every cryptographic algorithm is crackable given enough time to research. This is why organizations and agencies such as the National Security Agency (NSA) update encryption standards every few years. As of this writing, the only symmetric encryption algorithm that has not shown any substantial weakness is AES. (Although that happy state of affairs could have already changed between my typing and your reading of the printed work!) The danger here is that many modern cryptosystems can use pre-AES encryptions such as RC4 or DES. In this case, skilled cryptographers can crack a “secure” cryptosystem by attacking the underlying algorithm. NOTE No secure Web server package will easily allow you to use non-AES encryptions. Attack the Key Given that virtually every cryptosystem uses some form of key, it’s obvious that cryptanalysis will look at the key for weaknesses or, more importantly, attempt to determine the key simply by attacking at the ciphertext. One of the great weaknesses is key length. Modern increases in computing power make it easier to crack keys that were once considered too long to crack. Consider a bike lock with only four wheels versus a bike lock with many more than four (Figure 2-34). Which of these is faster to crack? The same concept applies to keys. Taking a piece of ciphertext and trying every possible key until something that looks like plaintext appears is a brute-force attack. (More on that type of attack shortly.) DES has an effective key length of only 56 bits. That means it has a key space (the total number of possible keys) of 256 or 72,057,594,037,927,936 different combinations. This number seems like an impossibly large number of combinations, but specialized computing systems like the Electronic Freedom Federation’s Deep Crack cracked a DES key in 22 hours … back in 1998. Today, a high-end desktop computer’s processing power isn’t too far from that same power. 02-ch02.indd 134 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 135 Figure 2-34 Two bike locks— which is easier to crack? Attack the Implementation Some implementations of new cryptosystems have some inherent flaw that causes an unanticipated weakness that is no fault of the underlying algorithm. Wired Equivalent Privacy (WEP) was marketed as a complete 802.11 encryption cryptosystem, introduced with the first generation of 802.11 wireless access points (WAPs) in 1999. Widely adopted, within a year cryptographers discovered that WEP poorly implemented the way it used the underlying RC4 encryption. That flaw enabled a simple cryptanalysis to derive the key simply by collecting enough encrypted data. NOTE WEP was not a true encryption mechanism, but instead provided the expectation of privacy the users would get from a wired network connection. In practice, as noted, it quickly failed to protect much of anything. Attackable Data No cipher attack is going to work if you don’t have access to something crackable. This crackable data can be divided into two different types: ciphertext or hashes. Before we go about attacking anything, let’s first create two example scenarios: one with ciphertext and another with hashes. Then we’ll attack. Ciphertext Scenario Let’s use a simple example of an 802.11 network encrypted with Wi-Fi Protected Access Pre-Shared Key (WPA-PSK). When a client connects to a WAP, the client goes through a simple handshake procedure that determines that each side stores the same PSK. This process does not transmit the key, but contains enough information to provide the key to a skilled hacker. Programmers have developed applications that can capture WPA handshakes. Figure 2-35 shows the popular Aircrack-ng program grabbing a handshake. 02-ch02.indd 135 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 136 Figure 2-35 Aircrack-ng grabbing a WPA handshake NOTE An online attack is executed against data in transit. An offline attack is done against data at rest. Once this handshake is captured, the attacker has a value upon which to apply a 128-bit key. If the attacker places the correct 128-bit key, she can determine the PSK. Hash Scenario Many cryptographic attacks target cracking passwords. Let’s start this scenario with a review of the where, how, and why of passwords. A computer system or application that requires password authentication must contain a database or table of passwords. Because these password tables are potentially vulnerable to anyone with the technical knowledge to locate them and try to crack them, storing a plaintext password is dangerous. It is extremely common, therefore, not to store the password itself, but instead store a cryptographic hash of the password in the database. The following is a sample of a hypothetical password list, consisting of four user names with their associated passwords stored as MD5 hashes. How can you tell they are MD5? Simply by counting the number of characters! This sample could be used for many applications. This example uses a text file; a password list could be a text file, a binary file, a cookie, or registry settings, depending on the application or the operating system that uses the passwords. Mike, bd4c4ea1b44a8ff2afa18dfd261ec2c8 Steve, 4015e9ce43edfb0668ddaa973ebc7e87 Janet, 8cbad96aced40b3838dd9f07f6ef5772 Penny, 48cccca3bab2ad18832233ee8dff1b0b Once you have the hashes, you can hash every possible conceptual password to see if you can match the hash. 02-ch02.indd 136 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 137 Attack Scenarios The ciphertext and hash scenarios previously presented have common features. Both rely on a single data point: either ciphertext or a hash. Both have a clearly understood algorithm: WPA and MD5. Finally, you can use an attack to apply a key to obtain plaintext. But how do bad actors perform this attack? What tools do they use to read that ciphertext or hash and try to extract the plaintext key or password? They use programs called password crackers or password recovery tools to perform these password attacks. Password crackers have legitimate use in assessing organizational security and recovering forgotten passwords. Such tools belong in every network security professional’s toolbox. In the wrong hands, though, tools to help can readily turn into tools to harm. Password crackers come in a broad assortment of functions and interfaces. A Linuxbased attacker, for example, uses Jack the Ripper or Hashcat (Figure 2-36). A Windowsbased attacker might employ the venerable Cain & Abel (Figure 2-37). Figure 2-36 Hashcat 02-ch02.indd 137 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 138 Figure 2-37 Cain & Abel In general, all these tools follow similar patterns. First, they grab the ciphertext or hashes you want to attack. Second, they analyze the data to determine the type of encryption (or they know the encryption by the source). Finally, they give you the option to attack in most, if not all, of the ways listed in this module. Let’s look at five common attack types that apply to these password-based scenarios: • • • • • Brute-force attack Dictionary attack Rainbow-table attack Password spraying attack Plaintext/unencrypted attack NOTE There is no such thing as a do-it-all single password cracker. There are hundreds of different password crackers, each with a different niche depending on your needs. Brute-Force Attack A brute-force attack is the simplest and least-efficient type of attack against known ciphertext/hashes. A brute-force attack attempts to derive a password or key by inspecting either ciphertext or a hash and then trying every possible combination of key or hash until it can decrypt the plaintext or generate a match. The challenge to brute force is the total number of iterations necessary to try every possible key combination. Consider a captured WPA handshake. The key is 128-bit, so it can go from 128 zeros to 128 ones, plus all the combinations in between. 02-ch02.indd 138 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 139 So, how long does it take to try 2128 combinations? Longer means more combinations and therefore harder, so 2128 is equal to 3.40282366920938463463374607431768211456 × 1038 That’s a huge number, but computers are powerful. A single, very high-end Intel Core i7 can process at half a trillion floating point operations per second (FLOPS), and you can readily source a computer with a lot of these CPUs. Additionally, password crackers are carefully optimized to take advantage of all those FLOPS. In fact, the better crackers can even take advantage of powerful graphics processing units (GPUs) on video cards as well as special-purpose application-specific integrated circuit (ASIC) devices that work hundreds or even thousands of times faster than a CPU (Figure 2-38). So, without spending outrageous text on the intricacies of CPUs, FLOPS, GPUs, and such, we can arguably say that a very high-end cracking system could process 1 trillion cracking attempts per second. It would take something like 10,790,283,070,806,014,188 years to try every possible key. If that seems like an impossibly long time to you, it is. Keep in mind that the key might be all zeros, which means you will get the WPA key on the very first try. Alternatively, the key might be all ones, which means you would have to try all 2128 combinations. This might make you think that brute force is useless, and it is for relatively large keys. Shorter keys, however, can easily be cracked. For example, a 56-bit DES key can be cracked (using the preceding assumptions) in about 20 hours. As computing power increases, what was once a long key or hash becomes short. That’s why keys and hashes get longer and longer over the years. Figure 2-38 Typical ASIC 02-ch02.indd 139 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 140 But even if we can run a brute-force attack in hours, why not come up with attacks that speed up the process? How can we narrow down the possible number of keys to try? Dictionary Attack Easily the weakest aspect to passwords is the fact that human beings create them. People produce passwords like this one: Password123 This is a great password, right? It mixes upper- and lowercase letters and numbers. Hmm … not so much when it comes to modern cryptographic attacks. People rarely create a password that looks like this: 1x3^^7vEssde6) That’s a far more awesome password, but it’s just not what typical people create. With this thought in mind, we can tell our cracking program to read a text file filled with all the common words in the (in this case) English language—a dictionary file. The cracking software will then use this dictionary file instead of brute force in a dictionary attack. Here is a tiny, tiny piece of a dictionary file downloaded from the Internet: A AA AAA AAAA a aa aaa aaaa As you can see, most dictionary files include lots of non-words as well. That’s because non-words like “AAAA” or “QWERTY” or “NASA” are commonly used for passwords. A small dictionary file might only store a few million passwords. The largest dictionary files contain many millions of passwords. NOTE If you recall the discussion of password policies from Chapter 1, you might see a nice attack opportunity here. A perpetrator who obtains a copy of an organization’s security policies could readily see specific password policies. If the policy sets password length to 16+ characters, for example, the perp won’t waste time or computational power on shorter passwords, but rather cut straight to the chase. Good dictionary attack tools don’t try only passwords in the dictionary list. Check out the dictionary attack settings for Cain & Abel in Figure 2-39. Note the options that allow you to modify the dictionary. If your dictionary file has the word cheese, for example, Cain & Abel will let you • Reverse the word: eseehc • Double pass: cheesecheese 02-ch02.indd 140 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 141 Figure 2-39 Cain & Abel dictionary options • • • • • Uppercase to lowercase: not applicable, as cheese is all lowercase Lowercase to uppercase: CHEESE Number substitution: ch33s3 Case permutations: Cheese, cHeese, etc. Add one or two numbers to the end: cheese1, cheese44 You can argue that these options add a brute-force aspect to a dictionary attack. A dictionary attack combined with brute-force options such as these is called a hybrid attack. NOTE As a quick mental exercise, ask yourself this question: Would the Cain & Abel tool be able to derive any of the passwords you use? 02-ch02.indd 141 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 142 Figure 2-40 Hydra in action Keep in mind there’s a huge difference in the quality of dictionary files. I keep a set of dictionary files, accumulated over the years from many sources, sorted by length of password, lowercase/uppercase, special characters, numbers in front, and so forth. With good dictionary files, good understanding of the tools, and belief in the laziness of people to use poor passwords, I can crack most any offline password in a few hours, a classic offline attack scenario. What if you don’t have any ciphertext to attack? What if you just want to try a few million passwords to try to log into a Web site? That’s a classic online attack situation and it’s no problem! There are plenty of online dictionary attack password crackers such as the popular Hydra (Figure 2-40). Online attacks are slow, but it’s easy to start an attack and let it run for days or weeks. Rainbow-Table Attack The challenge to dictionary attacks, particularly when you are trying to crack hashed passwords, is the fact that you have to take a word in the dictionary, hash it, then compare the hash to the hash in the password file. You could include hash values for all the entries in a dictionary file using common hashing algorithms to increase the effectiveness of a dictionary attack. The SHA-256 hash for “password” will always be 5e884898da28047151d0e56f8dc6292773603d0d6aabbdd62a11ef721d1542d8 So, what if we edited our dictionary files to include the hash? Sure, it might take weeks to generate the billions of hashes and save them in our dictionary file, but once it’s done, 02-ch02.indd 142 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 143 Figure 2-41 Simple dictionary files with hashes are too massive for practical use. Whoa! Way too big! we have a file that includes the dictionary word as well as the hash. Such a dictionary file would start like this: a, ca978112ca1bbdcafac231b39a23dc4da786eff8147c4e72b9807785afee48bb aa, 961b6dd3ede3cb8ecbaacbd68de040cd78eb2ed5889130cceb4c49268ea4d506 aaa, 9834876dcfb05cb167a5c24953eba58c4ac89b1adf57f28f2f9d09af107ee8f0 aaaa, 61be55a8e2f6b4e172338bddf184d6dbee29c98853e0a0485ecee7f27b9af0b4 Using such an inclusive dictionary file could make a dictionary attack brutally effective. Except there’s a huge problem. Files like these are massive, potentially in the hundreds of petabytes range for dictionary files that include really long passwords. They are simply too big for practical use (Figure 2-41). Math comes to the rescue! Using complicated math well outside the scope of the CompTIA Security+ exam, a password cracker can create a rainbow table, a dramatically reduced-sized dictionary file that includes hashed entries. NOTE Online vs. offline, which is better? You can run brute-force, dictionary, and rainbow table attacks either way, but offline is faster if you have a key. Rainbow tables are binary files, not text files. Figure 2-42 shows the contents of one set of rainbow tables, designed to help crack the old Windows XP–style List Manager passwords files. Rainbow tables for more advanced operating systems can be much larger, although always much smaller than a traditional dictionary file with hashes. 02-ch02.indd 143 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 144 Figure 2-42 Rainbow tables for Windows XP passwords Rainbow tables were long the first choice for cracking passwords; such attacks are fast and generally very successful. Rainbow tables were so popular that you can find online services that let you load hashes to crack, and powerful systems will crack a password for just a few dollars (Figure 2-43). (Or, you can use GPU brute force, which is how modern hackers do it.) Password Spraying Attack In a password spraying attack, an actor applies a few common passwords to many accounts in an organization. By applying “123456” or “password1” to 100 different accounts, for example, the attacker tries to find an entry into the network while avoiding lockouts and remaining undetected. Single sign-on (like in a Windows domain) and cloud accounts provide the most tempting targets of password spraying. Plaintext/Unencrypted Attack Attackers can use packet sniffing software to monitor and capture traffic on a network. If passwords are sent in plaintext or unencrypted, it’s game over instantly. Depending on the encryption strength, attackers can decrypt a lot of encrypted traffic given 02-ch02.indd 144 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 145 Figure 2-43 One of many online cracking services enough time. CompTIA uses the term plaintext/unencrypted as a type of password attack, but it’s more commonly referred to as a generic packet sniffing attack. EXAM TIP The simplest and most effective password attack is to ask the user for his password. It works (allegedly, not that I’ve done anything like this!). Defending Password Storage Between brute-force, dictionary, and rainbow attacks, traditional hash password storage has been under prolonged attack, making it important for cryptographers to come up with methods to make password storage more robust against these attacks. Salts and key stretching offer protections. Salts A salt is an arbitrary value, usually created by the application or operating system storing passwords, added to the end of a password before it is hashed. If a user’s password is 1234567, for example, a system might add an eight-character preset value, a salt, to the end of the password as such: 1234567akxcf3sf When hashed (in this example SHA256), it looks like this: a75f22d3cd5aea740f2a17b0275bfacd0c822aca 02-ch02.indd 145 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 146 Salts defeat rainbow tables simply because (hopefully) there are no rainbow tables that include dictionary terms plus the string akxcf3sf. Salts are common in just about everything that stores passwords. The downside is that a salt must be stored. If someone had access to your hashes, they also have access to the salt. They can run dictionary attacks, but now they must add the salt every time and recalculate the hash, slowing cracking down immensely. Also, it is possible to grab a salt and re-create a rainbow table, although this is also a slow process. EXAM TIP All modern operating systems use salts in password storage. You’ll see the term “salting” on the CompTIA Security+ exam to mean “using a salt.” Cryptosystems often use a nonce instead of, or along with, a salt to enhance security. A nonce is a number used once that helps in the transmission of shared keys, among many other uses. Because it’s used once and not repeated, a nonce prevents common attacks— called replay attacks—from cracking encryption. Key Stretching Another trick used to make cracking harder is key stretching. Keys are almost always generated from some plain English password. If we just hash the password, it doesn’t take a lot of time for an attacker to pick a potential password, hash it, then compare the results to a password hash file. But what if we were to make the process by which a key is derived from a password more complex? We can do so with a key derivation function. What if, for example, we hashed an initial password five times to then derive the key? This would require the attacker to run not just one hash, but five hashes for every iteration. Using key derivation functions that intentionally slow this derivation of keys is key stretching. There are several key stretching key derivation functions; two stand out: PBKDF2 and bcrypt. Password-Based Key Derivation Function 2 (PBKDF2) combines adding a very long salt and a huge number of hashing iterations to make a key. PBKDF2 doesn’t set the number of hash iterations. Some operating systems that employ PBKDF2 use 10,000 iterations! bcrypt generates hashes based on the Blowfish cipher. In many ways similar to PBKDF2, it also has flexible hash iterations. bcrypt has a very long key derivation process and is considered stronger than PBKDF2. Other Attack Options Several types of cryptographic attacks deviate from the crack-the-password variety. This section explores three such attack types: • Collision attacks • Known-plaintext attacks • Implementation attacks 02-ch02.indd 146 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-8: Cryptographic Attacks 147 Collision Attack A collision attack exploits the fact that hashes have a finite size, and there will be times when two different values create the same hash, a hash collision (as described in Module 2-5). Given that hashes provide integrity, an attacker may take advantage of collisions to do harmful things. For example, if an attacker can create a collision with a digital signature; she doesn’t need to know the actual private key, just a value to make an identical signature. There’s no magic to creating a collision. You use brute force on millions of hashes until you get one that collides. This is a big job, but there are some interesting aspects of hashes that make it a bit easier. The most well-known is the birthday attack. It seems that every undergraduate statistics class begins with the teacher looking out at his or her class and saying, “There are 30 students in this classroom. What are the odds that two people share the same birthday?” They are surprisingly high; for 30 students, about 70 percent. The same situation happens with hash collisions. A 64-bit hash has approximately 1.8 × 1019 different outputs. While this number is huge, the goal here is to find another identical hash. That’s where the birthday statistic applies. It only takes roughly half (5.38 × 109) to generate a collision using brute force. Known-Plaintext Attack A known-plaintext attack isn’t a true attack as much as it is an attack strategy. If you have both a known plaintext and the ciphertext, you can sometimes derive the key itself. Known-plaintext attacks have worked many times in the past. It’s how the British cracked the Nazi Enigma code in World War II. Military messages followed rigid forms, for example, so some words would always be in the same relative place. Messages would end with Heil Hitler, in other words, and wetter (weather) was consistently placed. Implementation Attack Any cryptosystem has weaknesses or aspects that attackers may use to help them. Attacking the WEP weakness described earlier is a classic example of a weak implementation attack. Download and replay attacks exploit weaknesses in implementation. Downgrade Attack Almost all of today’s cryptosystems give a client multiple ways to access a system. One of the best examples is TLS. A Web server using TLS supports several authentication and encryption methods to give flexibility for different Web browsers. In TLS, a client and a server traditionally request the most robust encryption. In a downgrade attack, the attack makes a legitimate request to the Web server to use a weak, deprecated algorithm that’s easier to crack (Figure 2-44) in hopes of then successfully getting keys, passwords, and so forth. NOTE A deprecated algorithm is an algorithm deemed obsolete or too flawed for use by the IT community. Deprecated means no one should use it in the future. 02-ch02.indd 147 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 148 Figure 2-44 Downgrade attack against TLS I offer 256-bit AES encryption! Can I just use DES? Web Server Replay Attack In many situations, an attacker can sniff or capture traffic on a network, monitoring the different communications taking place. A replay attack is an attack where the attacker captures some type of legitimate traffic and resends it as needed to do something malicious. Here’s an example: Bob: “Hey Joe, I need you to send the encryption keys for this session to me.” Joe: “Okay, Bob, here you go.” Bad Guy Mike: “Hey Joe, I need you to send the encryption keys for this session to me.” Joe: “Okay, Bob. I thought I just did, but whatever. Here you go.” Bad Guy Mike: “Mwuhuhahahahaha….” NOTE True replay attacks tend to be more complicated than the Bad Guy Mike scenario. A hacker might steal all the back and forth in a certificate exchange, for example, and then boot the originator off just before completion. Then the hacker would resend the same stream. But you get the idea. Module 2-9: Other Cryptosystems This module covers the following CompTIA Security+ objective: • 2.8 Summarize the basics of cryptographic concepts Several cryptosystems—current and speculative—fall outside the classic paradigms of symmetric and asymmetric cryptosystems. Depending on the field you wind up in as an IT security professional, you might encounter and need to work with one or more of these non-classical cryptosystems. This module explores four cryptosystem fields: • • • • 02-ch02.indd 148 Homomorphic encryption Blockchain Quantum cryptography Post-quantum cryptography 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Module 2-9: Other Cryptosystems 149 Homomorphic Encryption A clear challenge to storing data in the cloud is ensuring that personal data remains private. An organization cannot risk the possibility that an individual’s medical data, for example, could be shared or mined or even known without the explicit permission of the individual. Cryptographers have kicked around the problem and sought solutions since the late 1970s, but the beginnings of practical answers finally came in 2009 with the publication of Craig Gentry’s Stanford University PhD thesis, “Fully Homomorphic Encryption Using Ideal Lattices.” We’ll spare you the details on how Gentry’s initial scheme worked and how subsequent developments (with input from other awesome cryptographers) made current cryptosystems work. Homomorphic encryption enables manipulation of encrypted data—without decrypting—that then applies to that data when it’s decrypted. Wrap your head around that for a moment. Private, encrypted data can be outsourced to the cloud without compromising the privacy of that data. It means researchers can run analytical scans on encrypted data, get amazing amounts of information, and never compromise the private records of individuals. Cryptographers see the current state of homomorphic encryption as the third generation. Gentry and his collaborators continue to innovate in the field. The world awaits the future. Blockchain E-commerce on the Internet relies on hierarchical cryptosystems. Certificate authorities (CAs) provide certificates to organizations; that creates trust. We can buy from https:// amazon.com or https://linengarb.com with trust that our financial information (credit card numbers and such) won’t be compromised. Encryption, hashing, and other aspects of cryptography provide the secure connection between our computers and the e-commerce servers. Moreover, traditional institutions such as banks and credit card companies facilitate the flow of our money to vendors. Users of e-commerce, therefore, rely heavily on institutions that are not the seller. Blockchain radically disrupts this model, creating a decentralized, peer-to-peer system for secure interaction between buyer and seller. Here are the details. The shadowy figure Satoshi Nakamoto—real identity unknown—invented blockchain in 2008 to support the bitcoin cryptocurrency. Bitcoin is a topic for a whole other book, but in a nutshell, it’s money, called cryptocurrency, that’s not tied to any bank or nation state. Blockchain provides the peer-to-peer record—public ledger, in bitcoin speak—of all the transactions among people using bitcoin. You buy a pizza and pay for it using bitcoins, for example; that transaction goes into all the computers connected into the blockchain. The pizza joint now has bitcoins to spend on something else available in the market. Bitcoin and blockchain rely on public key infrastructure (PKI) cryptosystems to ensure safe storage of the currency and the transactions as well. You know about PKI from previous modules. Everything you learned applies here. Private keys must stay private (or else your bitcoins will get stolen); public keys are just that, public. Encryption/decryption works the same. 02-ch02.indd 149 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 150 The fundamental difference between traditional e-commerce and commerce conducted with bitcoin and blockchain is the decentralized structure of the latter. Quantum Cryptography The nascent field of quantum cryptography uses the vast power of quantum computers to fundamentally transform cryptosystems used today. Huh? The math works, but the machines barely exist today. Here’s the scoop in layman terms. Researchers postulate that we can build computers that can transmit data based on qubits, rather than simple binary digits. A qubit is a particle that’s a binary digit but captured in time, so it’s almost a 1, for example, or transitioning to a 0. The math is a lot more precise than the terms used here, of course. The key for security is that the state of a qubit is fragile; a hacker intercepting a stream would get only 1’s and 0’s because the qubits would collapse to the full binary state closest to its relative position. Think of this as rounding up or rounding down, like in basic math. This sounds like science fiction, but for relatively short distances, quantum computers work. The field of quantum communication, for example, has established connections between quantum computers over fiber-optic lines that regularly transact business using quantum key distribution (QKD). The connection between Shanghai and Beijing banks using quantum communication is over 2000 kilometers! Quantum cryptography relies on quantum computers to accomplish a couple of things. First, future complex quantum computers (theoretically) can easily crack modern secure cryptosystems, especially RSA and Diffie-Hellman. Second, key distribution using something called quantum entanglement holds the promise that it should become completely secure, a positive development. Quantum cryptography remains in the realm of theory, not practical application today. The math works, but building machines that can handle the complexities involved seems a decade or more in the future. If quantum computing breaks much of classic cryptography, does this mean the end? Not at all. Quantum computing may be wonderful at breaking classic “easy one way but hard the other way” forms of encryption, but cryptographers are already preparing for the future. The flip side to quantum cryptography, called post-quantum cryptography, speculates cryptographic algorithms that can withstand any attack using quantum computers. Wildly complex forms of encryption are already being developed, although it will be years before any form of encryption algorithm will be forwarded for public use. Questions 1. Which of the following types of algorithms encrypts specified sizes of groups of text at a time? A. Asymmetric B. Symmetric C. Streaming D. Block 02-ch02.indd 150 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Questions 151 2. You must implement a cryptography system in your organization. You need to be able to send large amounts of data quickly over the network. The system will be used by a very small group of users only, and key exchange is not a problem. Which of the following should you consider? A. Asymmetric cryptography B. Symmetric cryptography C. Hybrid cryptography D. Key escrow 3. Which of the following asymmetric algorithms uses a maximum key size of 4096 bits? A. AES B. Diffie-Hellman C. RSA D. ECC 4. Which of the following asymmetric algorithms is widely used on mobile devices because of its low computational power requirements? A. ECC B. ElGamal C. Diffie-Hellman D. GPG 5. Which type of algorithm is typically used to encrypt data at rest? A. Symmetric B. Asymmetric C. Streaming D. Block 6. Which of the following places secrecy of the key versus secrecy of the algorithm as the most important factor in developing secure and reliable cryptosystems? A. Data Encryption Standard (DES) B. Advanced Encryption Standard (AES) C. Kerckhoffs’ principle D. Digital Signature Algorithm (DSA) 7. Which of the following algorithms produces a 40-character message digest? A. MD5 B. SHA-1 C. RIPEMD-128 D. Blowfish 02-ch02.indd 151 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 2 Chapter 2: Cryptography 152 8. If an individual encrypts a message with his own private key, what does this assure? A. Confidentiality B. Message authenticity C. Integrity D. Availability 9. Which of the following entities can help distribute the workload of the CA by performing identification and authentication of individual certificate requestors? A. Subordinate CA B. Root CA server C. Authentication authority D. Registration authority 10. Which of the following serves as the master certificate server in an organization? A. Intermediate CA server B. Root CA server C. Subordinate CA server D. Kerberos KDC Answers 1. D. Block algorithms encrypt entire groups of bits of text, usually of specific sizes. 2. B. In this scenario, symmetric key cryptography would probably be the best choice, since the user group is very small and key exchange is not a problem. You also have the requirements of speed and efficiency, as well as the ability to send large amounts of data. All are advantages of using symmetric key cryptography. 3. C. RSA uses key sizes between 1024 and 4096 bits. 4. A. Elliptic-curve cryptography (ECC) is an asymmetric algorithm widely found in use on mobile devices because it requires low amounts of computational power. 5. A. Symmetric algorithms are typically used to encrypt data that resides in storage. 6. C. Kerckhoffs’ principle states that reliable cryptosystems should depend upon the secrecy of the key, rather than the secrecy of the algorithm. 7. B. SHA-1 is a 160-bit hashing algorithm that produces a 40-character hexadecimal message digest, or hash. 8. B. If an individual encrypts a message with his private key, this ensures message authenticity, since he is the only person who could have encrypted it. 9. D. The registration authority (RA) can help distribute the workload of the CA by performing identification and authentication of individual certificate requestors. 10. B. A root CA server is the master certificate server in an organization. 02-ch02.indd 152 25/03/21 2:12 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 CHAPTER Identity and Account Management 3 Be who you are and say what you feel because those who mind don’t matter and those who matter don’t mind. —Dr. Seuss Everything that is networking, everything that is the Internet, the whole reason to run cables, set up routers, configure firewalls and applications, and sit on the phone for hours with balky ISPs is really only to do one job: share resources. These resources are Web pages, e-mail messages, VoIP conversations, games…. The interconnected world has millions of resources for people to use to make work and leisure more convenient, more efficient, more inexpensive … and more fun (Figure 3-1). Resources are useless unless there’s someone or something accessing and using them. A Web page has no value unless someone accesses it. A shared folder does nothing unless users read, modify, and delete files stored in those folders. E-mail messages sit on a server unread until you read them. Users must run client software to use those resources. Offering a resource for anyone to use has major pitfalls. Users are at best ignorant, often nosy, and at worst, downright evil (Figure 3-2). IT professionals manage how users access the many resources. This chapter dives deeply into identity and account management: using methods and technology to control who accesses resources and what they can do with those resources once they have access (Figure 3-3). 153 03-ch03.indd 153 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 154 All for sharing! Figure 3-1 Lots of resources! Web Apps Games Disk Storage E-mail Web Pages VoIP This chapter covers various distinct aspects of access control in six modules: • • • • • • Understanding Authentication Authentication Methods and Access Controls Account Management Point-to-Point Authentication Network Authentication Identity Management Systems I don’t want to PAY for this game. So…Much EVIL!!!! Jane makes more than me! Delete All? Am I sure? YES I AM. Resource Figure 3-2 Unmanaged access to resources is foolhardy. 03-ch03.indd 154 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 155 Figure 3-3 Controlling resources Wait. Who are you?!?!? No Trespassing Games Disk Not You! Storage Email STOP!!! Web Pages Keep Out Module 3-1: Understanding Authentication This module covers the following CompTIA Security+ objectives: • 2.4 Summarize authentication and authorization design concepts • 3.8 Given a scenario, implement authentication and authorization solutions Identity and access management, like most CompTIA Security+ topics, brings a ton of concepts and specific jargon that serious students need to digest before implementing systems in the real world. This module explores identification and AAA (authentication, authorization, and accounting), then looks at concepts of trust, such as authentication structures and federated authentication. Identification and AAA Identification, authentication, authorization, and accounting work together to manage assets securely. This section briefly reprises what you read about in the Introduction on core security concepts. Imagine an asset, a shared resource, as a box. Authentication functions like a lock on that box. For a user to access the box, he must have some kind of key or credentials to get through the lock (Figure 3-4). The information in those credentials identifies the user with respect to that system. (That’s the identification part.) In analogy terms, it’s a pretty complicated lock that opens different portions of the box depending on the key used. Authorization determines what the user can do with the contents of the box with the specific credentials he used. Authorization is nuanced, because of variables in what people can do. Consider a shared folder on a Windows system in a local area network (LAN) that contains a single file. You can do a lot to that file. You can view the file, edit the file, or delete the file. (You can do much more than this, but this is enough for now.) Authorization defines what a user may do to that file. Think of authorization as a checklist (Figure 3-5). 03-ch03.indd 155 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 156 Figure 3-4 Authentication as a lock You have to get past me! Disk Storage Figure 3-5 Authorization as a checklist This key lets you: Read folder contents Modify files Add files Delete files Disk Storage Accounting means to keep a historical record of what users do to shared resources. Look at accounting as a sign-in sheet associated with the shared resource (Figure 3-6). Identification and Authentication The typical locked box and key analogy struggles when taken from physical access to electronic access. Granting access in the physical world, like a door lock on a real door, works fine because people don’t generally hand out a key to someone they can’t identify. In the electronic world, how do we identify individual users? Back in the early days of PC networking—for example, early versions of Windows that predated NTFS—this problem was simply ignored. Resources such as shared folders had no associated user accounts. If you wanted to share a folder, you just gave that folder a single password, which in turn was passed out to everyone to whom you wanted to give access (Figure 3-7). More commonly today, user accounts identify individual users. A user account is generally nothing more than a line in a table (remember the user names in password 03-ch03.indd 156 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 157 Figure 3-6 Accounting as a sign-in sheet What’s been done here? Bob modified file sales.doc. Janet deleted file stuff.doc. Fred tried to delete data2.doc. Penny logged off the system. Disk Storage storage in the previous chapter?) that identifies an individual user by some value, such as a User Name, UserID, Social Security Number, and so on. Figure 3-8 shows one example of a user account in Windows Server. A user account must include some authentication factor(s) or attribute(s) to provide any kind of security. Identification is by itself insufficient for authentication. Figure 3-7 Old Windows shared folder 03-ch03.indd 157 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 158 Figure 3-8 Windows Server user account An authentication factor or attribute reveals some unique aspect of the identified user. Passwords are very common but just scratch the surface. Let’s look at authentication factors and attributes in a lot more detail. Authentication Factors and Attributes Authentication systems use different characteristics of identification to identify a user and validate her credentials. These different methods—factors and attributes—depend upon the method of identification used. Several different factors and attributes can be used either separately or, preferably, together. Single-factor authentication uses only one factor or attribute. Multifactor authentication (MFA) uses more than one factor or attribute. (You’ll also see the term two-factor authentication to describe systems that use two factors or attributes.) Using more than one factor or attribute at a time provides more security and represents better authentication. There are three authentication factors used in computing: • Something you know • Something you have • Something you are There are four common attributes: • • • • Something you do Somewhere you are Something you exhibit Someone you know EXAM TIP The CompTIA Security+ exam will test you on the difference between single-factor and multifactor authentication. Single-factor authentication uses only one factor or attribute; multifactor uses at least two factors or attributes. 03-ch03.indd 158 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 159 Figure 3-9 Knowledge factor I know a password! Something You Know The knowledge factor relates to something you know, typically used when you identify yourself to a system with a user name and password combination. You know your user name and password, and use your memory to present them to the system (Figure 3-9). Although you use two details for this credential, it is still considered a single-factor form of authentication because it involves only something you know. This single-factor form of authentication can be compromised easily if someone gains access to it—in this case, if they learn your user name and password. If you’ve written them down somewhere or told someone your user name or password, you have effectively transferred that factor to the other person, and it could be considered compromised. Something You Have The possession factor relates to something you have. You physically possess an object to use as an authenticator. Scanning a gym membership card to gain access, for example, uses something you have. When used in this manner, the card alone is a single-factor form of authentication. More often than not, however, these types of authenticators require some additional method of authentication. Typically, this could be something you know, such as a personal identification number (PIN) or password. When used in this manner, the card and PIN are a multifactor form of authentication. You use two different types of factors: the possession factor and the knowledge factor. Smart cards and tokens are probably the most commonly used multifactor form of authentication that uses the possession factor. Smart cards are plastic cards with electronic chips in them that contain a limited amount of information related to the user, such as public and private keys. Smart cards enable users to access facilities, secure areas, and computer systems. Physical tokens usually display a complex series of changing numbers. When a token is used to access a system, the user must also enter a PIN or password known only to her in conjunction with the token and its own number. The system uses these two factors to validate the user. Figure 3-10 shows an example of a token. Something You Are The inherence factor relates to something you are, relying on a person’s unique physical characteristics that can be used as a form of identification, such as fingerprints, retinal eye patterns, iris patterns, handprints, and voiceprints (Figure 3-11). These unique biometric characteristics of a person are difficult to replicate or fake. (See “Biometrics” in Module 3-2 for more specific details on how organizations incorporate biometric scanning in security.) 03-ch03.indd 159 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 160 Figure 3-10 Possession factor 142 688 753 I have a hardware token! Inherence factors can also be used in conjunction with an additional factor in an MFA system. Newer laptops and smartphones often arrive with a fingerprint scanner built into them, for example, and the user must scan his fingerprint and enter a PIN or password to access the system. Secure facilities may also require fingerprint or handprint factors in their authentication systems. It’s also not unusual to see multiple inherence factors used for an even stronger authentication system. Something You Do Something you do, meaning that when you present your credentials to the system, you must perform an action (Figure 3-12), is a common attribute that accompanies authentication factors. The best example of this type of authentication attribute is when you use a finger or hand gesture on a smartphone or tablet to log in. The pattern you create using your finger or hand is the something you do. The user credentials database of the system you access stores that pattern. When the authentication system confirms that these patterns match, you gain access to the device or system. Some forms of authentication that use this type of gesture are single-factor if that’s the only thing you’re required to do to access the system. Other authentication systems may also require an additional factor, such as entry of a PIN, making it a multifactor form of authentication. EXAM TIP CompTIA Security+ objective 2.4 adds another word to describe the action attribute: something you can do. Describing a potential action as an authentication attribute seems a little odd, to say the least. Just don’t miss this on the exam. Figure 3-11 Inherence factor 03-ch03.indd 160 I have a fingerprint! 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 161 Figure 3-12 Action attribute I use a pattern! Somewhere You Are The location attribute relates to your location when you authenticate. This attribute could use either physical or logical locations and requires you to be in a certain location when you authenticate to the system (Figure 3-13). From a physical perspective, for example, in a highly secure facility, you may need to use a specific workstation, located in a certain room, to authenticate to the system before you can work on it from any other location. Because you would likely have to authenticate with other physical protections and controls to get into this room, this very secure form of authentication would allow only a limited number of people to access the system. From a logical perspective, a location attribute could be used as an authentication attribute if you are required to authenticate from a certain device that has a specific digital certificate assigned to it, or from behind a certain network device, physical port, or even a subnet. This doesn’t necessarily limit you by requiring authentication from a single physical location; rather, the logical location with respect to the network and the authentication system being used would be important. This might ensure that you do not attempt to authenticate from an untrusted network or device. Something You Exhibit Something you exhibit can refer to something neurological that can be measured or scanned; it could be a personality trait or a mannerism. Speech analysis systems could very easily identify Barak Obama from the cadence of the way he talks, for example, with distinctive pauses. This is not a commonly used attribute today in cybersecurity. Someone You Know The someone you know attribute reflects a trust relationship. John Bob—known and trusted by the system—vouches for Rebecca Sue. Figure 3-13 Location attribute You Are Here 03-ch03.indd 161 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 162 NOTE An additional authentication attribute that you won’t see on the CompTIA Security+ exam is temporal, relating to somewhen you are. Systems can set specific login times and restrict others, for example. You’ll definitely hear arguments that the temporal attribute is a control, not an authentication attribute, and thus belongs in authorization. Knowledge-Based Authentication In knowledge-based authentication (KBA), users provide answers to questions or shared secrets to prove their identities. You’ll see KBA implemented in scenarios involving online banking systems, for example, where users authenticate (or recover a forgotten password) by stating common authentication factors (such as name) and also answer questions presumably only they would know, such as “What was your first pet’s name?” or “What was your first car?” The use of pre-agreed or pre-shared secrets is also known as static KBA. Dynamic KBA, in contrast, uses information about the user gleaned from public data—what the authenticating system can gather from a Web search—and private data, such as a credit history. A lack of shared secrets makes dynamic KBA more secure than static KBA, though it’s more difficult to implement. NOTE As you progress through this chapter, keep in mind the balance among cost, implementation time, and expertise required to put systems in place. The Woodland Heights Community Bank might have the need for multifactor, layered authentication plus serious physical controls. Jane’s coffee shop Wi-Fi network, on the other hand, might need a far lighter touch. Security folks weigh cost versus need when recommending and implementing systems. Authorization Authentication gets you in the door of a shared resource; the key unlocks the box. Authorization defines what you can do once you authenticate. Users have rights or permissions to do certain things to shared resources. This presents some unique challenges because different resources often have wildly different permissions based on the type of resource. To get an idea of how resources can vary, let’s consider two different types of resources: a printer and a Web page. Figure 3-14 shows permissions you can assign to a shared printer in Windows. Note three permissions: Print, Manage this printer, and Manage documents. These permissions make sense, as these are the actions we need to do to a printer. Compare printer permissions to the permissions of a Web server program, shown in Figure 3-15. A simple HTTP server only has two permissions: allow access or deny access. The downside to applying permissions to user accounts is that users and their permissions change over time. People quit, employees get promoted, customers leave, students graduate, and so on. Keeping up with the process of creating/deleting users and adding/changing permissions when people’s situations change can be an administrative nightmare. 03-ch03.indd 162 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 163 Figure 3-14 Printer permissions in Windows 10 Figure 3-15 Web permissions in Internet Information Services 03-ch03.indd 163 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 164 Figure 3-16 Groups in FileZilla Groups streamline this process by organizing similar users into collections. Applying permissions to groups lowers administrative work. When a user needs permission changes, you can assign the user to the group with the appropriate permissions. Almost every type of authorization uses the idea of groups. Figure 3-16 shows group settings for FileZilla, an FTP server program. Authorization goes deeper than simply users, groups, and permissions, but this level of detail should suffice for now. We’ll dive deeper into authorization throughout this chapter. NOTE We touched on onboarding and offboarding policies way back in Chapter 1. Such policies can have a dramatic impact on organizations. That’s why security staffs spend a lot of time analyzing and reviewing decommission and termination policies and procedures. Accounting Accounting or auditing enables security professionals to keep track of the accesses that take place on any given resource over time. Windows enables administrators to set audit policies on many aspects of the computer. Figure 3-17 shows the Local Security Policy snap-in on a standalone Windows 10 computer. Note the categories of audits in the background; the window on top shows auditing set to track failed logon attempts. Windows domain administrators would use the Group Policy Management Console (GPMC) to audit domain-level access to resources. 03-ch03.indd 164 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-1: Understanding Authentication 165 Figure 3-17 Local Security Policy snap-in The technologies that support authentication, authorization, and accounting are known as AAA. We’ll delve into these technologies in more detail in later chapters, but for now make sure you understand that accounting/auditing is very much a part of access management. EXAM TIP You can use Event Viewer in Windows to view logs of what you’ve set the computer or domain to audit. Pay attention to the wording of the question to know whether you’re setting audit policy or viewing logs of audit events, then pick the right tool. Trust Access management builds on the concept of trust in several ways. First, the system must trust that the user presenting credentials is in fact the user represented by those credentials. Second, the system must trust the integrity of the user credentials database, in that the data is current and correct and the system is functioning normally and returns the 03-ch03.indd 165 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 166 correct information so the user can be validated. Third, the system must trust the authenticity of the hardware or software that generated the credentials. Organizations must trust their own authentication systems and, sometimes, those of another entity or organization. In this section, we’ll discuss authentication across organizational boundaries, both from within and outside an organization. This authentication often involves trust relationships that must be established between hosts, systems, and other organizational entities. Centralized and Decentralized Authentication When an organization manages all its user accounts, credentials, and authentication systems as one unified system, this is said to be centralized authentication. In a centralized enterprise authentication system, credentials are stored in one database and user accounts have uniform security policies and requirements that apply across the entire organization. The authentication system performs authentication services for all systems, data, and resources across the enterprise. Often, you will hear the term single sign-on (SSO) in relation to a centralized system; this means that a single set of user credentials is used to access resources across the enterprise. Whether a user is allowed or denied access to those resources depends on the authorization and access control policy in place, not the user’s credentials in the authentication process. In a centralized model, all hosts and resources trust the central credentials database to take care of authenticating the user for them; after that, it’s merely an issue of whether or not that user has the correct rights, privileges, and permissions to access a resource or perform an action. By contrast, in a decentralized authentication model, authentication occurs on a persystem, per-host, and even per-resource basis. No centralized authentication mechanism serves to validate the user’s identity first; each system or resource makes an authentication decision based upon its own user credentials database or access control list. In a small office setting, for example, each user may be an administrator for her own workstation and have the ability to create accounts on that workstation. If another user wants to access a shared folder on another user’s workstation, he would need a separate user name and password—on that workstation—just for that resource. It usually won’t be the same user name and password he uses for his own workstation; even if an effort is made to duplicate these across workstations, both accounts still reside in separate databases on each workstation and are therefore not technically the same. If a password in one set of credentials changes, for example, this doesn’t guarantee that the other set of credentials on the other workstation will be updated as well. Decentralized systems do not trust each other’s credentials database or authentication mechanisms; they require a user to authenticate using his own systems and credentials. Decentralized authentication also means that user account and password policies will be different as well. Trusts and Federated Authentication Outside of organizational boundaries, users must often be authenticated to systems within another organization’s infrastructure. Examples of this include business partner relationships, where employees need to access documents in the partner company’s network, or university students who must access an affiliate university’s shared library resources. 03-ch03.indd 166 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 167 In these examples, each organization may have its own centralized authentication system that trusts its own users and systems but not users outside the organization’s boundaries. Two ways of allowing outside users to access resources internal to an organization, and authenticating those users, are though trust relationships and federated systems. Authentication systems can establish a trust relationship, enabling users from each system to authenticate to the other’s resources. The authentication system in one company, for instance, may trust the authentication decisions (and vice versa) of a partner company, allowing its users to access sensitive resources such as shared folders and files. Trusts can be one-way or two-way (bidirectional); two entities may trust each other’s authentication systems, but the relationship can also be such that entity A trusts entity B’s authentication systems and decisions, but the reverse is not true. One variation on this trust relationship is called a transitive trust. In this type of trust relationship, there are more than two entities; if Company A trusts Company B’s authentication systems, and Company B trusts Company C, then Company A may also trust Company C’s systems by default. More often than not, though, trust relationships between entities must be explicitly established instead of defaulting to transitive trusts. A federated system involves the use of a common authentication system and credentials database that multiple entities use and share. This ensures that a user’s credentials in Company A would be acceptable in Company B and Company C, and only access permissions would be the determining factor in accessing systems and data. Windows Active Directory is a good example of a federated system in practice; user credentials from different domains could be used in other domains if they are all part of the same Active Directory forest. EXAM TIP The CompTIA Security+ objectives refer to use of federated systems as federation. Attestation Strong MFA schemes can incorporate attestation into their authentication. Attestation assures that the hardware or software that created the authentication factors matches the standards and protocols it’s supposed to use. Your key might look great, but was it made on a Cyclon RXP Key machine running genuine BluePart software? As you might expect, enabling attestation requires a lot more work and upkeep. Module 3-2: Authentication Methods and Access Controls This module covers the following CompTIA Security+ objectives: • • • • 03-ch03.indd 167 2.4 Summarize authentication and authorization design concepts 3.7 Given a scenario, implement identity and account management controls 3.8 Given a scenario, implement authentication and authorization solutions 5.3 Explain the importance of policies to organizational security 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 168 Identity, authentication, and authorization enable secure access of resources, as you know from the previous module. This module explores the nuts and bolts involved in implementing these schemes. We’ll start with authentication methods, explore biometrics, and finish with access control schemes employed in authorization. Authentication Methods Organizations need real-world methods, real-world mechanisms to identify, authenticate, and authorize. They need tools that verify the authentication factors (something you know, something you have, and something you are) you learned in Module 3-1. Let’s explore the technologies used to implement authentication. NOTE There are a lot of authentication methods, but the CompTIA Security+ objectives only cover a few of the most important and common ones. In addition, the exam goes into great detail on some of these methods, while barely touching others. To make sure we cover the exam objectives, some of the methods listed in this module (user name/password is a great example) get quite a bit more coverage later in the book. User Name/Password The user name/password combination has been around from the earliest days of authentication. You’d be hard-pressed to find an application or operating system that doesn’t use user name/password as the primary authentication mechanism, from logging into a Linux system to connecting to a game server (Figure 3-18). Figure 3-18 Author’s Steam account login 03-ch03.indd 168 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 169 Operating systems rely on user accounts, secured by user name and password, for basic file system security. The permissions associated with a user account say what that user can do with data stored on the system, such as adding, deleting, or taking ownership. User accounts are a fundamental authentication mechanism for every operating system. Many applications likewise rely on user names and passwords for authentication. You can set up database programs, for example, to require an additional login before a user can access or manipulate data. Such fundamental database security begins with a user name and password. User accounts, user names, and passwords are so important, both to the real world and to the CompTIA Security+ exam, that Module 3-3, “Account Management,” is dedicated to user accounts, groups, permissions, and the many aspects of user name/password used for authentication and access control. There’s a good reason that just about everything turns to user name/password for authentication. User name/password is fast, it takes little storage on systems, it leans completely on the something you know authentication factor (so nothing to lose or accidently drop in a toilet), and possibly most importantly, people are used to entering user names/passwords for just about anything. EXAM TIP Expect a question on the CompTIA Security+ exam on static codes for authentication. These refer to personal identification numbers (PINs) that you use to log into a Microsoft account, for example, or to finish authenticating with an automated teller machine (ATM) at the bank. Most smartphones require a static code for login (i.e., authentication). Password Vaults Relying on user name and password for logging into a single system or application works well enough for many situations, but consider an all-too-familiar scenario where a user needs to log into multiple applications and keep track of multiple passwords. Although a lot of Web applications allow you to establish an identity and verify that identity using a Google or Facebook account that functions similar to single sign-on (discussed in Module 3-1), that’s not always practical or desired. Many organizations and individuals turn to applications called password vaults to retain all the passwords—or password keys—for you. A typical commercial password vault such as Bitwarden can store hundreds of discreet passwords securely. All you have to remember is your master key (and to make very certain it’s robust). The downside to password vaults is that they need to be installed on individual systems and don’t give you the ultimate in flexibility. One-Time Passwords/Tokens In any form of authentication, the best type of password is one that’s used one time then never again. A one-time password (OTP) is generated and used only once, and it is never repeated. But how can two separate parties somehow magically know the same password if it’s only to be used once and then thrown away? 03-ch03.indd 169 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 170 The trick to using an OTP is there must be some type of independent, third-party, separate-from-the-two-sides-of-a-secure-communication tool that generates these passwords/keys in such a way that both sides of a communication trust the third party. This third-party password generator is known generically as a token or token key. Hardware tokens are physical devices such as a USB security key linked to a specific account and plugged into the client computer. Software tokens are applications that generate OTPs. Figure 3-19 shows a software token used for a World of Warcraft account. People use the WoW authenticator for a specific game, but you can also use general authentication applications as a part of two-factor authentication at various Web sites. The https://login.gov Web site, for example, enables users to add one of various apps to their smart devices, such as Google Authenticator, Authy, LastPass, or 1Password, to create that second authentication factor. Hardware and software tokens are great examples of one-time passwords in action. The OTP provided by a token is used in conjunction with another mechanism, such as a regular password, to provide better security in a multifactor environment. Another example of one-time password use is during a secure communications session, where the secure protocols automatically generate a session key that is used only during that session. The session key could be considered a one-time password. Diffie-Hellman Ephemeral (DHE) keys are a great example of OTPs. Figure 3-19 WoW software token 03-ch03.indd 170 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 171 Many security systems use standard communication methods to convey an OTP. Common systems send an OTP via short message service (SMS) to a smartphone, for example, or push notifications to a computer. Other systems make an automated voice phone call to verify and authenticate. TOTP A one-time password, like any password, is going to work whether you use it instantly or later, so it’s important to give a time limit to any OTP you generate. Also, given that no date and time is ever the same, time is a great factor to help generate totally unique OTPs. A time-based one-time password (TOTP) uses time as a factor to assist in generating the OTP. In the previous example regarding a token, the TOTP changes very often, sometimes after only a few seconds. Therefore, it must keep its time synchronized exactly with the authentication database. If the user is even one or two seconds off from using the correct TOTP displayed on the token, authentication fails. Normally, the user has a set number of seconds to input the correct password before it changes and another one must be used. This has many advantages, including the prevention of replay attacks. Another advantage is that it can be very difficult to predict TOTPs, based upon the time factor that is input into the algorithm used to create them. This can make it very difficult for an attacker to guess what TOTPs might be used. Tokens are not the only devices that can use TOTPs. Google, using strong authentication practices, for example, may send a TOTP to a personal device, such as a smartphone, that you would be required to have in your possession during authentication. Your Google account may require you to input this TOTP within a certain amount of time, and after you receive a text message with the TOTP, you would input this password, usually a set of digits, into the corresponding field on the screen. You would then be authenticated and allowed to access your Google account. Figure 3-20 shows TOTP codes for different applications on a smartphone. EXAM TIP The CompTIA Security+ exam may ask about using one-time passwords. OTPs typically are generated by tokens or mobile devices to facilitate multifactor authentication. HOTP One algorithm used to generate OTPs is the HMAC-based one-time password (HOTP) algorithm. If you recall from Chapter 2, the Hash-based Message Authentication Code (HMAC) provides for message authentication and data integrity. HMAC can use either MD5 or the SHA series of hashing algorithms and various key sizes. In the case of HOTP use, the user is authenticated against the centralized authentication database, and the authentication server calculates the HMAC value and sends it to the user via an authentication device such as a token. Several popular authentication mechanisms that use mobile devices, such as smartphones, make use of HOTP. Certificate-Based Authentication Asymmetric encryption, using the exchange of public keys, is a powerful authentication tool. The exchange of public keys, especially in the form of robust PKI certificates, makes a level of identification that’s hard to beat (Figure 3-21). 03-ch03.indd 171 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 172 Figure 3-20 TOTP codes from a smartphone The challenge to using tools like certificates is that they are tricky to carry around for individuals. Since a certificate is nothing more than binary data, there needs to be a method for individuals to carry their certificates. In such a scenario, smart cards, PIV cards, and common access cards ride to the rescue for certificate-based authentication. Smart Cards Adding a storage chip to a standard credit card–sized plastic card creates a way for an individual to store personal information, a smart card. The term “smart card” It is you!!! Figure 3-21 Certificate as an identity tool ate Certific 03-ch03.indd 172 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 173 Figure 3-22 Smart card contacts isn’t a standard by itself, although a number of standards for data organization, physical dimensions, contact versus contactless, voltage, and so on fit under the term. Figure 3-22 shows a few examples of smart card–enabled credit cards. Note the slightly different contact types. Smart cards can store any binary data, not just certificates. Some applications use smart cards that store symmetric keys, digital signatures, PINs, or personally identifiable information (PII). There is no law of physics or law of humans that says how you use a smart card or what is stored on that card. Two NIST documents—Special Publication 800-78-4 and FIPS 201-2—provide frameworks for the adoption, organization, and administration for smart cards. NOTE The most common symmetric key type used on smart cards is 3DES; the most common asymmetric key type is RSA. Personal Identity Verification Card Smart cards for authentication certainly predate the NIST’s involvement, but there were no well-received standards. Almost anyone using smart cards up until the early 2000s used vendor-specific systems and, as you might imagine, there was little to no interoperability. The framework provided by Special Publication 800-78-4 and FIPS 201-2 and the subsequent adoption of that framework by civilian departments in the US federal government spurred the industry to create a single method to use smart cards for identity and authentication. The result of these publications is the Personal Identity Verification (PIV) card. If you’re a civilian and you work for or directly with the US federal government, you almost certainly have been issued a PIV card (Figure 3-23). PIV card standards provide a wide range of interoperability, ease of administration, tremendous flexibility, and rock-solid access control. The PIV standard gives individual agencies quite a bit of leeway as to exactly what is stored on a PIV, but it gives very strict rules on how that data is stored if you choose to use it. This includes physical as well as electronic data. PIV cards must be constructed and printed to strict rules. Specific areas of the card are reserved for a head shot photo, expiration date, smart chip, and so forth (Figure 3-24). 03-ch03.indd 173 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 174 Figure 3-23 PIV card Figure 3-24 PIV card layout (courtesy NIST FIPS 201-2) 03-ch03.indd 174 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 175 Common Access Card The US Department of Defense has its own version of PIV card called the common access card (CAC). CAC builds on the PIV standard, adding different versions for active military, civilian employees, contractors, and so on. Biometrics Biometrics use a person’s physical characteristics (something you are—the inherence factor) to provide strong user identification and verification. The CompTIA Security+ exam objectives list numerous biometric factors, such as fingerprints, retina and iris patterns, voice patterns, and facial features. These physical characteristics are unique to every individual and are very difficult to mimic or fake. This makes biometric authentication an extremely secure form of authentication in theory, although sometimes the methods used to implement it are not as secure and can be circumvented. You should understand some terms and concepts in biometric authentication for the exam and as a security professional. Fingerprints Every person has unique fingerprints, making those swirls and lines perfect for biometric authentication. Fingerprint scanners, like the one shown in Figure 3-25, are common in many keyboards, laptops, and mobile devices. Figure 3-25 Android fingerprint scanner 03-ch03.indd 175 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 176 Figure 3-26 Retinal scanner in Half-Life game Retina/Iris Patterns The human retina and iris have unique patterns that lend themselves to identification. Retinal scanners for access controls date back to the early 1990s, but their cost relegated them to extremely secure environments. They’ve made a huge impression in popular culture (Figure 3-26). Improvements in camera resolution, computing power, and hardware pricing brought iris scanners into the forefront. Iris scanners are far more common than retinal scanners, while providing almost the same degree of accuracy (Figure 3-27). Voice Recognition Voice recognition for speech to text holds a strong niche for dictation. Most mobile devices—like smartphones—and personal assistant hardware use voice recognition tools such as Google Assistant, Amazon Alexa, and Apple Siri. But voice recognition as authentication hasn’t gained any real acceptance due to its low accuracy compared to other biometric technologies. Figure 3-27 Iris scanner 03-ch03.indd 176 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 177 Hello Mike Meyers Password Sign-in Options Figure 3-28 Windows Hello NOTE It’s a lot easier to fake a person’s voice than a person’s iris pattern. Facial Recognition Facial recognition has become a popular and powerful authentication method for several applications. The Windows Hello API, built into every version of Windows 10, is a facial recognition tool (Figure 3-28). Most facial recognition tools require extra functionality, especially cameras that include infrared so the camera can differentiate between a real face and a photograph. Vein Matching and Gait Analysis Two biometric areas show promise in authentication, though they’re not as widely implemented as the five physical characteristics previously discussed: vein matching and gait analysis. Vein matching uses the patterns of a person’s blood vessels to identify that person. The patterns in the palm of the hand, for example, provide data 100 times more unique than fingerprints, can be scanned without touching the skin, and ignore damage to the skin. Vein-matching systems are in use in some hospital systems around the globe. Gait analysis measures the unique way a person walks or runs by using machine vision– based tools—external cameras, in other words—or via the sensors built into existing smartphones. This latter technology shows a lot of promise, because it can tap into the accelerometer every current smartphone has to authenticate the user continuously. 03-ch03.indd 177 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 178 The current systems only offer approximately 75 percent accuracy, so more work needs to be done, but gait analysis shows promise. Biometric Efficacy Rates Biometric systems are not foolproof. The efficacy rates of various systems depend on a lot of factors, such as error rates, security, privacy, user acceptance, and usability. The previous discussions of specific physical characteristics mentioned some of these factors, such as the difficulty of getting affordable and acceptable retinal scanners. Two other specific terms describe efficacy rates: false rejection rate and false acceptance rate. The false rejection rate, or FRR (also known as a type I error), is the rate at which a biometric system erroneously rejects authorized users who should in fact be identified and authenticated as valid users. The false acceptance rate, or FAR (also known as a type II error), is the rate at which a biometric system erroneously identifies and authenticates unauthorized individuals as valid users. Both error rates can be dealt with by tuning the relative sensitivity of the biometric system in question; however, tuning it too much to reduce one type of error usually results in increasing the other type, so a trade-off is involved. This trade-off is usually tuned to the level of the crossover error rate (CER), which is the point at which one error rate is reduced to the smallest point that does not result in an increase in the other error rate. Figure 3-29 illustrates this concept. EXAM TIP The CompTIA Security+ exam may ask questions about the difference between the false rejection rate and the false acceptance rate in biometrics. The FRR is the rate of errors from incorrectly rejecting authorized users. The FAR is the rate of errors from incorrectly authenticating unauthorized users. The crossover error rate (CER) is the point at which the system must be tuned to reduce both types of errors effectively without increasing either one of them. Figure 3-29 The crossover error rate Sensitivity 100 False Rejection Rate Crossover Error Rate False Acceptance Rate 0 20 100 Errors 03-ch03.indd 178 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 179 Authorization and Access Control Schemes/Models Authentication verifies identity and lets a user in the door to access systems in an enterprise. Authorization determines what that user can do once she’s inside. Access controls further refine what that user can do based on specific security policies. We talked about security policies in general way back in Chapter 1, but let’s take it a step further now. A familiar (and perhaps overused) example sets the scenario for this section: a bank. The Woodland Heights Community Bank serves the good people of Woodland Heights. Security policies determine which employees have access to information and assets of the bank. Credential policies define things like how personnel log into the network (password policies, for example), what kind of access third-party companies get, and how service accounts and administrator/root accounts are set up and given to people. Credential policies also apply to devices accessing the network, such as what remote Computer A can share with, store on, and back up to internal Server B. Policies govern which people get access according to a set of rules. The bank tellers, for example, should be able to log into the main system and have access to client records. That way they can accept money and put it into the proper account, for example, and give money to verified users from the proper account. Bank tellers wouldn’t have access to the security camera records; the security team and management would have that additional access. Management would have access to the vault with all the gold bullion, but additional controls would restrict and record their access too. This process of determining who gets what is the basis for the principle of least privilege: only give access to people who need access; restrict access for those who do not. All of this leads to specific access controls that enforce the polices. And all of that is encompassed in the process of authorization. Got it? Enough preamble. Let’s get to the meat (or tofu, depending on your preference). The introduction of electronically stored data in the early days of computing compelled IT entities to start thinking about ways to organize access to ensure good security. Several entities developed access control schemes, but it wasn’t until the US Department of Defense Trusted Computer System Evaluation Criteria (TCSEC) “Orange” book (Figure 3-30) that robust models emerged. The TCSEC quantified several well-known access control schemes; over time, more have been added. Many access control schemes are used in the industry; the CompTIA Security+ exam objectives list several: mandatory access control, discretionary access control, role-based access control, rule-based access control, attribute-based access control, and conditional access. We’ll tack physical access control on the end for completeness. NOTE The international Common Criteria standard replaced TCSEC way back in 2005. That was your history lesson for the day. All the access control schemes/models listed here apply. Mandatory Access Control Mandatory access control (MAC) applies to highly secure environments, such as defense or financial systems. With mandatory access control, a user is granted access to a system 03-ch03.indd 179 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 180 Figure 3-30 TCSEC cover or data based upon his security clearance level. Data is assigned different labels that designate its sensitivity and the security clearance required to access it. Administrators grant users, who also have security clearances assigned to their accounts, access to specific systems or data, based upon their need-to-know requirements. Even on the same system, users who have the requisite security clearances don’t always get access to all of the data at the same clearance level. Each user’s job requirements must also indicate a valid need to access the data. MAC models are typically either confidentiality or integrity models. A confidentiality model emphasizes protection against unauthorized access, and an integrity model emphasizes the need to protect all data from unauthorized modification. Discretionary Access Control Discretionary access control (DAC) is what most users encounter on a normal basis. Microsoft Windows, as well as macOS and Linux systems, typically use DAC in both standalone and network environments. With DAC, the user who has created or owns an object, such as a file or folder, has the discretion to assign permissions to that object as she sees fit. The file system, such as NTFS in Windows, provides the security to do such filesystem permissions. (Note that CompTIA removes the space, so filesystem permissions, 03-ch03.indd 180 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-2: Authentication Methods and Access Controls 181 rather than file-system permissions.) Administrator-level access isn’t required to assign permissions; any user who creates or owns the resource can do so. Discretionary access control is a very flexible model, and users can assign rights, permissions, and privileges both to individuals and to groups of users, which can be logically created in the system based upon different functional or security needs. EXAM TIP The discretionary access control model is the only model that allows normal users to dictate who has permissions to objects such as files, folders, or other resources. Role-Based Access Control Role-based access control, on the surface, sounds like access control using groups, but this isn’t necessarily the case. Although DAC models can be used to assign permissions, rights, and privileges to traditional groups, role-based access controls almost exclusively use predefined roles rather than groups or users. These predefined roles must already exist in the system, and users must be assigned to these roles to have the access levels granted to the roles. A role-based access control model is not discretionary. The creator or owner of a resource cannot necessarily assign a user to a particular role simply to give him access. Normally an administrative-level user must assign a user to a role. Roles might include supervisory roles, administrative roles, management roles, or data change roles that have an increased level of access to systems, data, or other objects. Rule-Based Access Control Rule-based access control is a model that is rarely seen as a standalone type of access control model. It’s typically integrated with other access control models, such as discretionary or mandatory access control. In rule-based access control, all accesses granted in the system are based upon predefined rules, which might include restrictions on when, how, where, and under what circumstances a user may access a system or resource. A rule, for example, may state that between the business hours of 8 a.m. and 11 a.m., only the accounting department may have write access to a particular database, but between 1 p.m. and 4 p.m., users in accounting, marketing, and production may have read and write access to the database. Rules may apply to users or groups of users, and they may even specify the workstations that must be used, the type of permissions that apply to the resource, and so on. An example of rule-based access control is that used in more advanced firewalls, which lists a series of rules that users, network devices, hosts, and network traffic must meet in order to access other hosts and resources on the network. Attribute-Based Access Control All of the previous access control models share a user-centric attitude toward access. Users are important, but limiting. In the last few years a number of more granular, more powerful access control models have been adopted. The attribute-based access control (ABAC) 03-ch03.indd 181 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 182 model replaces users with attributes. While an attribute may be any form of identifying information, it’s commonly divided into functional groups, such as subject attributes (name, clearance, department) or object attributes (data type, classification, color). We then connect policies to the access control. When someone wants to access data, ABAC uses preset rules that consider attributes and policies to make a decision about access. Conditional Access Conditional access policy means to grant specific users or groups access when certain (usually dire) conditions occur. A conditional access policy might apply in case cellular networks go down in an area and two-factor authentication becomes impossible. You’ll see this sort of policy implemented in a lot of modern systems, especially cloud-based systems like Microsoft Azure. Azure offers various “as a service” offerings, such as platform as a service (PaaS), software as a service (SaaS), and infrastructure as a service (IaaS). Having aggressive policies in place to deal with catastrophic circumstances like floods and fires makes perfect sense when your product should be available to customers always. Microsoft 365—as in Office 365, a powerful productivity suite of applications— offers a good example of a current security architecture that includes a layered approach and multiple controls. At the heart of the system is the data storage and configuration, controlled by administrators, privileged accounts. That heart is protected by what’s called privileged access management (PAM), a control to isolate or limit the affect a compromised privileged account can have on the overall system. Layered on that is conditional access. Layered on that is RBAC. In practice, this layered security protects the system from abuse and the users from loss. Physical Access Control Physical access control describes the mechanisms for admitting and denying user access to your space. This applies to doors, door locks, and facilities in general. More specifically, the term refers to the objects used to enable users to gain secure access. Smart cards, discussed previously, can function as physical access control mechanisms. Proximity cards rely on a different frequency, but function similarly. Another typical tool is a key fob (Figure 3-31). These are used at places like gyms that allow 24/7 access. Module 3-3: Account Management This module covers the following CompTIA Security+ objectives: • 3.7 Given a scenario, implement identity and account management controls • 5.3 Explain the importance of policies to organizational security User accounts and passwords provide the bedrock of identity and account management control. This module explores user account types, issues with mingling accounts on a single machine, and managing permissions. We’ll also analyze account policies and account administration best practices. 03-ch03.indd 182 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 183 Figure 3-31 Key fob User Accounts User accounts provide a method to identify, authenticate, and authorize individual users to a resource. In a common scenario, you have some type of server software offering a resource and some type of client software trying to access that resource (see Figure 3-32). NOTE Server software is not necessarily running on the same physical computer as the resource it shares, although it often does. I access shared resources. I provide access to my shared resources. Resource Resource Resource Client Software Server Software Shared Resource Figure 3-32 Client, server, and resource 03-ch03.indd 183 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 184 Give me access to your shared resources! User name and password please! Resource User Database User na me and PASSW ORD Melissa, a3^dkf2cxvb Resource Stephen, j4sam1&fs8)4 Michael, e32*$gHfsQ1 Penny, p&djks$ks@2 Resource Figure 3-33 Authenticating to a server User accounts are data structures, usually stored on the serving system, that store two discrete features: a unique identifier (a user name) that identifies the user and a shared secret (a password) used to handle the authentication (Figure 3-33). Assuming a successful login, the client authenticates and can access any resource the server allows. The server issues to the client software some form of access token. The server software uses the access token to handle the authorization, defining the permissions the user has to the shared resources via some form of access control list. Figure 3-34 shows an access control list as attributes assigned to each resource. NOTE In Windows, the access token is known as a security identifier (SID). Note that when you run a server offering shared resources, sometimes there are housekeeping or security issues—issues that have nothing to do with the resources n ke a To 13 ss e2 ce 5f Ac 2c5 1a Resource A 1a2c55fe213a read, write, execute Resource B 1a2c55fe213a read Resource C read No listing for 1a2c55fe213a here so no permissions to this resource. Figure 3-34 An access token handles authorization. 03-ch03.indd 184 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 185 themselves, but rather the server as a whole—that you must deal with to support good authentication and authorization. For example, what if the server cares about the user’s password length? We call these rights or privileges, and we’ll see more of these shortly. Account Types Serving systems that employ user accounts organize their accounts into different types to help categorize their use and apply the principle of least privilege discussed back in Module 3-2. You should know these user account types: user, administrator/root, privileged, service, and guest. User The user account is created for and allocated to the people needing access to shared resources. In a perfect world, every individual needing access to resources has his or her own user account, although sometimes there are exceptions. Administrator/Root Every serving system, in particular every operating system, has an account that has complete power over the resource as well as the complete serving system. This super account is often automatically created when the OS is installed. In Windows this account is called administrator (often shortened to admin); in macOS and Linux/ UNIX, this account is called root. The admin/root account is powerful. It has complete and total access to all resources on the serving system. It has access to all permissions to the system. In general, avoid using these powerful accounts unless you are performing a job that requires them. Privileged A privileged account sits between a user account and an admin/root account. We generally create privileged accounts to delegate some aspect of system or account management. For example, an admin might assign the right to update software to a user account, making it privileged. Service In some cases individual processes, not actual people, need rights and/or permissions to a serving system. A backup program, for example, might need read access to any file on a computer to make a proper backup. In these cases we create (or the operating system automatically creates) service accounts. NOTE Service accounts usually aren’t held to password complexity or password changing controls, making them a vulnerability to protect. They’re often overlooked or ignored and thus make a great entry point for bad guys. Guest Guest accounts have minimal rights and privileges, often used for temporary access to resources. In most cases guest accounts are premade by operating systems, and in almost every case they are disabled by default. Note the down arrow on the guest account in Figure 3-35 showing that it is disabled. Mingling Accounts Sometimes it’s impossible or impractical to assign a single user account to every individual in your organization. Two important considerations in managing accounts are the use of multiple accounts, usually by one individual, and the use of shared accounts, 03-ch03.indd 185 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 186 Figure 3-35 Disabled guest account on Windows 10 Professional which may be used by multiple individuals. In some circumstances, the use of multiple user accounts, or even shared accounts, may be required. In these cases, we have to balance this functionality with security. Multiple Accounts Normal user accounts are allowed to perform typical user actions, such as editing documents, checking e-mail, and performing daily work. Higher-level account privileges on the host or network may be required by administrative-level or privileged users because of their duty or job position requirements. But if we assign the normal user account higher-level privileges, it increases the potential for bad things to happen. First, the user could routinely abuse his privileges. Second, if a malicious entity obtains the user’s account and password, she could perform harmful actions using those elevated privileges. Finally, if the user is logged into the system with that privileged account, any malware or software that requires elevated user privileges can take advantage of that account, potentially taking harmful and sometimes unknown actions on the system. The answer to this problem is through the controlled use of multiple accounts—in other words, a user would have a normal user account with lower-level privileges, plus a second user account with very specific higher-level privileges. The user would use her lower-level account to perform routine duties—actions such as accessing e-mail and files, editing documents, and other actions that require no special privileges. When the user needs to use higher-level privileges, such as creating accounts, installing devices, and updating 03-ch03.indd 186 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 187 software, she could authenticate to the privileged account and log out of the account when the action is complete. This way, the user restricts her use of the privileged account only to the times when it is needed, and she is not constantly authenticated as a privileged user. This reduces the attack surface on the system or network and the possibility of those privileges being abused. It also makes it easier to hold the user accountable for any actions performed using those higher-level privileges by auditing those accounts. Some general rules for maintaining multiple accounts include the following: • Use different login names, different passwords, and different permissions and privileges for both accounts. • Different group assignments should be made for those accounts, plus a higher degree of auditing of their use. • Users should not stay logged into the system using privileged accounts; they should be allowed to log into the accounts only when they need them. • Users should have to follow a process of logging in and authenticating to the system with those accounts before they are allowed to use them. • Users should be allowed to perform only certain actions while they are logged into those accounts and should be required to log out when they’re done. • Audit multiple accounts, particularly privileged ones, periodically to determine current needs and proper use. Too often, users can get a little lazy and stop using their “lesser” account. Regular audits should keep such misbehavior minimized. Shared Accounts In a shared account, several users can log in using the same user name and password for the account—in other words, several people can access the same account. You can quickly see how sharing accounts could cause issues with accountability and non-repudiation. If someone used that account to change file permissions, delete data, or even create another user account with elevated permissions, who would you trace the action to? The abuser could be anyone who has access to the account and knows its user name and password. Even strictly auditing the account would not tell you who used it (Figure 3-36). Figure 3-36 Not me! Must have been the other User22! 03-ch03.indd 187 We are all User22! 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 188 Don’t use shared accounts/credentials (referred to as shared and generic accounts/ credentials in CompTIA Security+ objective 3.7), period. They represent a gigantic security hole. Administrators can always take over in a pinch, so having multiple people able to access the same systems with the same account credentials is a poor security practice. Although they should be avoided whenever possible, shared accounts should be carefully controlled if they are used. Anyone who has access to the shared account should be documented and briefed on its care and use. Some systems may allow a user to be logged in as a normal user and then authenticate to the shared account. In this case, the system may audit the use of the shared account, the time it is used, the actions performed with it, and the authenticating user, thus ensuring accountability. If the system does not have this capability, users should have to log their use of a shared account manually, as well as what actions they took while using it. These manual and system logs should be scrutinized carefully and often to make sure that people are using the account for its intended purpose, and securely. EXAM TIP Shared and generic accounts/credentials should be used as minimally as possible. When their use is absolutely required, shared accounts must be documented, audited, and carefully controlled. Managing Permissions and Rights with User Accounts Permissions and rights are generally assigned on an individual basis to user accounts or to logical groups that have been created for common functional and security needs. We’ll look at both methods and discuss the need to review and monitor privileges periodically to ensure that they’re being used appropriately. The principle of least privilege, as you’ll recall from Module 3-2, guides policies about account permissions and rights, meaning that administrators never give a user account more rights and permissions—the least amount of privilege—than is needed for the user to do his or her job. A great example of a least privilege policy is time-based logins to make sure that users have access to their systems only during the times they should be at their machines. There’s no reason for Penny in Accounting to have access to her system at 2 a.m. on a Sunday morning (unless Penny works strange hours)! User-Assigned Access Control One of the reasons to create individual user accounts is that it enables administrators to assign the accounts specific rights and permissions. User accounts allow users to identify and authenticate themselves to the system, access and interact with resources, and perform their daily jobs. Set up properly, these accounts also enable administrators to trace the actions performed by the user account to the physical user. When a user requires access to a system or resource, an administrator assigns specific privileges to her user account. When that user requires access to yet another resource, the administrator assigns her even more privileges. At some point, the user may no longer require access to certain resources or privileges to perform actions on the system. When that happens, the administrator can also reduce the user’s privileges or revoke certain permissions. 03-ch03.indd 188 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 189 These types of actions occur daily with most user accounts in large organizations. You’ll find, however, that many user accounts have common functional needs and security requirements. Managing permissions on an individual user account basis can be inefficient and difficult. Although certain user account permissions need to be administered on an individual basis, the preferred way of managing permissions is by assigning them to groups, discussed next. Group-Based Access Control On a system, a group is a logical collection of user accounts that have common functions, access, and/or security needs. The most efficient way to assign user rights and permissions is to assign them to groups. This allows the appropriate privileges to be assigned to the entire group of users only once, rather than assigning privileges to individual user accounts each time new users require the same privileges (Figure 3-37). User accounts can be placed in and removed from groups easily. You can assign user accounts to multiple groups to reflect different functional and security needs. One disadvantage to group-based privileges is that a user account may be placed in a group and eventually forgotten about. Later, if the organization does not want a user to have certain privileges, an admin examining the individual user account wouldn’t see the group privileges there. Another disadvantage is that group privileges are often cumulative. For example, if a user is assigned to the administrators group, he usually has elevated privileges. If he is assigned to a functional group as well, such as accounting or marketing, he may use his administrative-level privileges to affect certain transactions that are not authorized. Group membership should be examined closely, as well as cumulative permissions and the continuing need to have them. Reviewing privilege requirements and continuously monitoring them is important. NOTE Use groups to assign user rights and permissions to resources whenever possible. This makes the process much more efficient and secure. Figure 3-37 Groups assign permissions to users with common functions. 03-ch03.indd 189 All of us sales folks are in the SALES group. 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 190 Account Policies Organizations develop and implement account policies to ensure uniformly created and maintained accounts. Network administrators apply technical policy settings within the system to implement the written account policy for the organization. For example, Windows has several account policy settings that you can use to enforce certain restrictions on user accounts. The following sections explore different aspects of account policy enforcement, including password policies, and circumstances that may require user accounts to be locked out or disabled. Figure 3-38 shows some of the technical policy settings in Windows used to manage accounts. EXAM TIP Policies that determine what a user account can do in a system are also referred to as access policies. Password Length and Complexity Every security professional harps on the need to have strong passwords. But what makes up a strong password? In the early days of computers and the Internet, people used their dog’s and children’s names, birthdays, and other common, easy-to-remember things as Figure 3-38 Windows Server security policies 03-ch03.indd 190 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 191 Figure 3-39 Fido, good boy! f…i…d…o passwords. Passwords were usually very short, five or six letters at best, and normally made up of letters of the alphabet (Figure 3-39). As malicious hackers came on the scene, however, they quickly learned to guess and defeat passwords using simple mathematics (since short passwords did not yield a lot of different combinations to try) or by guessing the users’ passwords by learning different characteristics about them and their personal lives (Figure 3-40). Best practice avoids the use of simple user names and passwords for identification and authentication, but most folks don’t practice . . . best. Although businesses and government agencies use multifactor methods such as smart cards, PINs, and biometrics, the average user (business users included) still relies on user name and password combinations in many of their applications (Figure 3-41). So security professionals still have to account for the possibility that passwords will be stolen and cracked by malicious entities. To make it harder for hackers to steal and crack passwords, create password construction rules that make password guessing and brute-forcing more difficult. A password consists of several linear characters. Fewer characters means easy crackability. If, for example, the password was constructed of only numbers, then a fourcharacter password would have only 10,000 possible combinations. This might seem difficult for a human to guess, but a computer could crack this password in seconds. Even if you added one more character, the password would have 100,000 possibilities—still very easy for a computer to figure out. Figure 3-40 Simple passwords crack easily. 03-ch03.indd 191 Here, Fido! Catch! Really? Fido? I’ll just jot that down for trying later. 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 192 Figure 3-41 Too easy pwd: ilo vefido Well, at least it’s more than 4 characters! Today, the general rule is that the longer the password the better, because the different combinations of password possibilities makes it harder to crack. These days, most organizations recommend, and sometimes require, a password length of at least 14 to 20 characters. A computer can break even a password this long in a matter of minutes, however, if the password uses only numbers or letters. That’s where complexity comes in. Password complexity takes into account the number of character sets that can be used to construct a password. In a four-character password that uses only numbers, for each possible character, there are only 10 possibilities (digits 0–9). Add another character set, such as all lowercase letters of the alphabet, and the number of potential characters increases to 36 possibilities per character (digits 0–9 and lowercase alphabetic letters a–z). This increases the character space and the complexity of the password. A four-character password increases from 10,000 possible combinations to 1,679,616. Again, this sounds like an awful lot of combinations, and it would be very difficult for a human to crack this password in a reasonable amount of time (Figure 3-42). Computers can attempt thousands of combinations per second, however, so it wouldn’t take long to crack a fourcharacter password, even with this many combinations. Adding additional character sets increases the number of password combinations. Rather than using only numbers and lowercase letters, most organizations require the use of uppercase letters and special characters. Ideally, users should construct long passwords that use at least one of each of those four character sets, preferably at least two of each. Password length fundamentally impacts security—the longer the better. Figure 3-42 Better boy, Fido! f…1…d…0 So much better than “fido.” 03-ch03.indd 192 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 193 The more complex a password is, the less likely the user will be able to remember it, and that means he’ll probably write it down; this is something to consider when requiring complex passwords. Users must be trained on how to develop secure passwords that they can remember without compromising them by writing them down. Many users find that constructing a password from an easily remembered phrase is a viable solution to this problem. I’m a military aviation fan, so one of my old passwords was Mikelikesthef14tomcatsapg-71radar. (Yes, I’m a serious nerd.) Watch out for keyboard walks, the process of making a password by just moving up or down the keys on the keyboard. The password Mju7Nhy6Bgt% looks like a really complex password, for example, but watch the keyboard while you type it. It’s a keyboard walk and every password cracker knows it. EXAM TIP Password complexity consists of increased length and character sets. Both contribute to the character space (number of possible combinations) and a password’s security. Password Reuse and History Essential account policies restrict password reuse and maintain a password history. It does no good to require users to change their password periodically if they revert to the same password they’ve used for years. A password reuse account policy restricts users from reusing the same password frequently. For example, setting a password reuse policy to 10 would prevent users from using their last ten passwords, thus ensuring a fresh password. TIP Good account policy restricts password reuse. Also, not on the exam, but worth noting is that good policies can restrict password resemblance as well as reuse. Edgar changes his password from An3wPWD4here1! to An3wPWD4here2! when required by the network policy. Is the new password a complex, long password? Yes, but it differs only one digit from his previous password. That’s not good security! The password history, which stores the user account’s passwords for a certain number of password change cycles, helps enforce the password reuse policy. If the password history policy is set to 10, for example, the system would store the user’s last ten passwords. Beyond this setting, the user can, of course, reuse a password, but setting stringent password aging requirements would prevent the user from reusing passwords for a period of time. If, for example, passwords are required to be changed every 90 days and the password history is set to 10, then the soonest a user could reuse a password would be 900 days. By that time, the user probably won’t even remember the old passwords, so odds are an old password won’t be reused. Figure 3-43 shows a Windows Server password policy management console that includes password history settings and complexity requirements. 03-ch03.indd 193 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 194 Figure 3-43 Managing password policies in Windows Server Account and Password Expiration Accounts and passwords shouldn’t last forever; in fact, some accounts and passwords should be set to expire. Accounts for temporary workers, for example, could be set to expire after a predetermined period of time, such as 90 days. These accounts could be reviewed shortly before the time period expires to see if they are still needed. Passwords, on the other hand, should be set to expire for everyone in the organization, to include administrators and even senior executives, because, over time, passwords could become cracked by malicious hackers, lost, or otherwise compromised. Password expiration shortens the amount of time that an attacker has to crack and use a password (Figure 3-44). Depending on password length and complexity, it can take an inordinate amount of time to crack. The idea is to make sure the passwords expire before they are cracked. When the password is set to expire, the system should notify users a certain number of days (set by the system’s account or password policy) ahead of time so that they have ample opportunity to change to a new password. If a user does not change her password within the allowed amount of time, her account should lock, so that she cannot use the account again until the password is changed. This forces the user to change her password, and when she again creates a new password, the expiration time for that password resets. 03-ch03.indd 194 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 195 Figure 3-44 Drats, foiled again! 3…2…1…change your passwords, people! Noooo!!! Just one more day and I would’ve been in! Disabling Accounts Administrators disable accounts temporarily for various reasons. The organization may not want to revoke, retire, or delete the account permanently, since the user may need it at a later date. Perhaps a user has repeatedly input an incorrect password—the system would automatically disable the account to prevent its compromise in case an attacker is attempting to brute-force the account. Or an administrator may temporarily disable an account when a user takes a vacation—or if he is under investigation for a crime involving the computer. The user may not be allowed to use the account during either of these two circumstances, so an administrator would manually disable the account until management determines that it can be re-enabled. EXAM TIP The CompTIA Security+ objectives use the term disablement to describe the process of disabling user accounts. It’s all part of account policy enforcement, an essential aspect of IT security. For whatever reason an account is disabled, it prevents its use for a set duration. An administrator must re-enable the account and should include a documented reason as to why she both disabled and re-enabled the account. It may be organizational policy to disable an account for a predetermined amount of time after a user has left the organization; in those cases, policies should also set a time after which the account will be permanently deleted. EXAM TIP Disable accounts temporarily whenever a user does not need access to the system. Don’t permanently delete accounts until you determine that a user will never need access to the system again. 03-ch03.indd 195 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 196 Account Lockout Account lockout policies protect user accounts from being compromised. A typical policy disables an account after a number of incorrect password attempts, for example. The account can be locked for a predetermined period, such as an hour or two, or until an administrator manually re-enables the account. This prevents brute-force password attacks. Account lockouts also normally show up in audit logs and could alert the administrator to a potential attack—or, at a minimum, a user who has issues with his account or password. Most account lockout thresholds are set to a small number, usually between three and ten, sufficient to prevent a brute-force attack but forgiving of a user who may have simply forgotten or mistyped his password. Figure 3-45 illustrates the default lockout policy settings in Windows. EXAM TIP You should always set account lockout as part of your organization’s account policies. Without account lockout, a malicious user could use brute-force techniques to guess a password and access an account. Figure 3-45 Default lockout policy settings in Windows 03-ch03.indd 196 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 197 Figure 3-46 Maybe we should just fire the guy? I forgot my password! Kill me. Account and Password Recovery Proper account policies incorporate account and password recovery. Account recovery policies should cover both disabled and deleted accounts. Password recovery generally applies only to forgotten passwords. Those people and their shoddy memories (Figure 3-46)! Account recovery options vary a lot between disabled and deleted accounts. An administrator can easily re-enable a disabled account whenever management or policy dictates. A deleted account, whether by accident or by intent, offers challenging recovery options. Simply re-creating an account isn’t the same thing as re-enabling it. Even if you were to re-create the account with the same user name, the identifier that the system uses for it will differ. The system uses identifiers to assign privileges and allow access to different areas of the system. Re-creating an account means that you’ve created a new account, so the user rights and privileges used on the original account would not apply to the new account—you must reassign them from scratch. NOTE In Windows, the account identifier is known as the security identifier, or SID. In UNIX- and Linux-based systems, account identifiers are known as user identifiers, or UIDs. You can also recover an account by restoring part of the accounts database from a backup. This isn’t always the preferred method, however, because it is difficult to restore only discrete pieces of the database pertaining to the user account. Typically, the entire database might have to be restored, which would also undo any other changes that were made since the account was lost or deleted. Password recovery typically occurs only if the password has been stored somewhere offline, such as in a secure file or container. Often, organizations will record highly sensitive passwords for system services or critical personnel and store them in secured and encrypted files or in a secure container, such as a safe, for example. If passwords have not been stored offline, recovery could be difficult if a system goes down. Some older systems might store passwords in plaintext, which is highly undesirable, but it might make passwords easier to recover. The best way to “restore” a password is to create a new one, especially with a lost or potentially compromised password. 03-ch03.indd 197 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 198 Location-Based and Time-Based Policies The prevalence of accessing e-mail on smartphones has led to security policies based on the network location of devices. If an employee loses a company smartphone that’s set up to receive and send e-mail messages, this presents a clear danger. Smartphones know where they are, for the most part, because of interaction with cell towers. Companies can implement policies that restrict features of smartphones, like e-mail, when the user goes outside a given geographic area. Or the policies can be set up to provide an automated notification about an unsafe location, such as when travelling abroad. In addition to location-based policies, administrators often add time-based login policies as well, providing authentication that includes when a user should or could log in. John logs in successfully each morning at the office at 8:00 a.m., Monday through Friday. Policy determines that he should not log in at 6:00 a.m. during the week, for example, nor at 8:00 a.m. on the weekend. Anomaly Detection Policy Implementing a system based on Microsoft Azure Active Directory, a cloudbased network solution, provides a typical scenario for account policies. Many of the network assets are remote rather than local and thus add a dimension to the account policies beyond a locally based network. Microsoft Cloud App Security offers specific policy options that apply to their Azure AD system, such as anomaly detection policies. Fully automated, these policy options include such gems as impossible travel time, risky login, and activity rate monitoring. After a user logs off from Azure AD at a specific physical location and time, the system can detect if that user attempts to log in at another physical location that is sufficiently distant to represent an impossible travel time from the location of the previous logout. Erin can’t log off her work computer in Houston, Texas, at 5:00 p.m., for example, and then log into her work computer remotely at 5:30 p.m. from Dallas, Texas. The system is smart enough to recognize VPN logins, which reduces the number of false positives. A positive detection triggers a security alert so that administrators can take appropriate action. A risky login reflects a risky IP address, generally from an unknown or suspect location. Erin logs off from her remote connection in Houston on Friday night. She logs in on Monday from an IP address that’s in Brazil, and the system has no clue if she’s on a business trip or somebody hacked her account. Security alerts are triggered and administrators can take appropriate action. Microsoft Cloud App Security policies dictate the degree to which unusual activity gets flagged. This activity can include all sorts of things, from unusually high downloads to excessive file sharing or file deletion. The system will trigger an alert, and administrators can take appropriate action. The cool part about policy systems like Microsoft Cloud App Security is that administrators can fine-tune them to work accurately for their network needs. All of the policies can and should be tweaked over time. 03-ch03.indd 198 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-3: Account Management 199 Account Administration The typical network administrator has common repetitive tasks that affect company security. Policies determine how to handle most of these tasks. Let’s look at onboarding/ offboarding, user audits and reviews, and continuous monitoring. Onboarding/Offboarding Policies on onboarding and offboarding of personnel apply explicitly to the status of the user account. We touched on these back in Module 1-7, but they’re worth putting into context here. During the onboarding process, a new employee should have a new account created, using some form of standard naming convention to enable ease of use by everyone. NOTE Failure to use a standard naming convention is the bane of small businesses that start to grow. Even tiny companies should always pick a standard naming convention for all user names and stick to it. Offboarding is even trickier. When an employee separates, administrators do not typically delete the user account. Instead, they reset the user account with a new password used only by the administrator and the account is disabled for a set amount of time. This makes data recovery easy. Account Audits and Review Network administrators should periodically audit access to systems and resources for several reasons. First, compliance with any organizational access control policy may require periodic review. Second, users often are transferred within an organization, they may be hired or terminated, or they may be promoted or demoted. In all of those cases, users likely don’t require the same access to systems and data. Unfortunately, if access is not reviewed on a periodic basis, users may move around within the organization and retain privileges even when they no longer need them. This is a problem commonly called privilege creep, and it violates the principle of least privilege. The best way to perform these account audits is by looking at two very specific areas: account permissions auditing and review and usage auditing and review. What permissions does the user account have across all shared resources? What resources is he actually using (usage audit)? Is he using all he has? Does he have too many permissions due to privilege creep? Here is where the administrator makes changes to rights and permissions to stick with least privilege. This audit process is an essential part of account maintenance, the collective procedures to make sure users have access to what they need over time, with changing projects and responsibilities, and nothing else. Some highly sensitive systems or data require periodic access reviews called recertification to ensure that unauthorized users have not been inadvertently given inappropriate permissions to sensitive data. Access reviews involve reviewing audit logs, object permissions, access control lists, and policies that specifically direct who should have access to systems and data and under what circumstances. That’s another reason it’s a good idea to document exactly who has access to sensitive systems and data and when that access will expire; it makes access reviews a great deal easier. 03-ch03.indd 199 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 200 Continuous Monitoring Continuous monitoring is a form of auditing that involves examining audit trails, such as logs and other documentation, to ensure accountability for actions any user performs. With continuous monitoring, administrators can continuously check to ensure that systems and data are being accessed properly and by authorized personnel. Monitoring may involve automated means or manual review of logs or documentation. In any event, administrators look for signs of improper access by unauthorized persons or unauthorized actions authorized people may take, such as unauthorized use of account privileges; use of accounts by unauthorized users; unauthorized creation, deletion, or modification of data; and so on. Continuous monitoring enables administrators to be sure that users are performing only the authorized actions they are allowed to perform on the network. This supports the security concepts of authorization and non-repudiation, as well as accountability. Figure 3-47 shows the different options available for auditing in Windows, a necessary part of reviewing user access and continuous privilege monitoring. EXAM TIP The organization should review the need for higher-level privileges on a frequent basis and continually monitor the use of those privileges. This ensures accountability and prevents security incidents from occurring. Figure 3-47 Audit Policy settings in Windows 03-ch03.indd 200 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-4: Point-to-Point Authentication 201 Module 3-4: Point-to-Point Authentication This module covers the following CompTIA Security+ objective: • 3.8 Given a scenario, implement authentication and authorization solutions Now that this chapter has covered most of the critical concepts of access management, it’s time to move from the theoretical into the practical. This module looks at the protocols and methods that enable a client to access a server securely. The best place to start this is at the beginning of the Internet; a time when cable modems, cellular WANs, and fiber to the premises weren’t considered; a time when computers sat in your house, unconnected to any network. If you wanted to connect to the Internet, you had to make a remote connection from your computer to a remote server of an ISP that in turn connected to the Internet. Back in the early 1990s, just about everyone had a physical telephone line. Using an analog modem and a telephone number, we could dial in to a system that was connected to the Internet, and then we were connected as well (Figure 3-48). The protocol that made all this work was the Point-to-Point Protocol (PPP). In essence, PPP turned a modem into a network interface card (NIC). The PPP client dialed up the remote PPP server and made a virtual Ethernet connection, just as if your computer at home was connected to the switch at the remote server’s location. From here the PPP server would send out Dynamic Host Configuration Protocol (DHCP) requests just like a modern system does. NOTE Point-to-point in this context means taking a single computer and making a single, one-to-one connection to a remote network. Don’t confuse these remote connections with modern technologies such as virtual private networking. A VPN requires a system already on the Internet to make a private connection. A point-to-point connection means your client is not on any network. The problem with PPP was that it was remote. A PPP server had a phone number that anyone could call and PPP servers weren’t cheap, so PPP came with several authentication protocols. Three of these protocols—PAP, CHAP, and MS-CHAP—dominated and continue to dominate point-to-point authentication. Figure 3-48 Ancient connection options 03-ch03.indd 201 With this modem I can get 48 K bits PER SECOND! 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 202 PAP The Password Authentication Protocol (PAP) is the oldest authentication protocol used to pass user names and passwords to a central authentication server. PAP was usually seen with older dial-up remote connection methods and actually predates PPP. Unfortunately, PAP does not pass user names and passwords securely during authentication by default; this information is generally sent over the network in clear text, making it easily intercepted by someone using a network sniffer. EXAM TIP The ancient and non-secure PAP has been deprecated. You should always use an authentication protocol that hashes or encrypts user credentials that travel across a network connection. CHAP/MS-CHAP The Challenge-Handshake Authentication Protocol (CHAP) is an Internet standard method (described in RFC 1994) of authenticating users or a host to a centralized authentication server. CHAP is an older protocol that replaced sending user name and password information over clear text, as non-secure implementations of PAP did. CHAP was primarily used over PPP connections, and it was the first of several different versions of challenge-response authentication protocols. In CHAP, the authentication server sends a challenge message to the user or host. The user inputs his password, and the system hashes the combination of the password and challenge together, using a one-way hash function. The host then sends this hashed response back to the authentication server. The authentication server, which knows the user’s password, repeats the hashing process with the password and challenge and produces its own hash value. If the hash values match, then the authentication server knows that the user input the correct password and the user can be authenticated. If the hash values do not match, authentication fails. Figure 3-49 illustrates how this process works. CHAP periodically reauthenticates clients during a session; this process uses a threeway handshake. CHAP can prevent replay attacks and also enables the user to authenticate without directly sending his password over non-secure network connections. Microsoft developed its own version of the CHAP protocol, MS-CHAP, and later MS-CHAP v2, 1. Client requests authentication. 2. Server sends a challenge to the client. 3. Client responds to challenge by hashing response with user’s password. 4. Server compares response to its own computed hash and authenticates if they match. Figure 3-49 The CHAP authentication process 03-ch03.indd 202 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-4: Point-to-Point Authentication 203 which was used in earlier versions of Microsoft Windows. It is been all but deprecated on all recent versions of Windows in favor of more secure authentication mechanisms such as Kerberos. EXAM TIP CHAP relies on challenge and response messages and hashed passwords, as do other modern protocols. This ensures that passwords or other user credentials are never sent over the network in clear text. Remote Access Connection and Authentication Services This section explores various remote authentication services and protocols that enable external authorized users and hosts to authenticate into an internal network. These methods are normally used for older dial-up and Integrated Services Digital Network (ISDN) connections, but we’ll also look at the two primary tunneling protocols that can provide remote access services for VPN connections—the subject of later modules, so we won’t go much in depth here. Authentication, authorization, and accounting (AAA) apply to functions performed by authentication services, such as remote authentication services. In this context, authentication and authorization mean the same thing, although there might be intermediary devices that provide certain related services rather than having a host authenticate directly with a centralized authentication server or database. The accounting function, when used in the context of remote access, describes the process of accounting for connection time and billing functions, another throwback to the older days of dial-up, when users paid for their connection to an ISP by the minute or hour. These days, users typically connect via a broadband method that is “always on,” such as DSL or cable modem. Although users are still charged for their service, it’s typically on a flat-rate basis and not by the minute or hour. Still, the accounting function of remote access takes care of this aspect of the connection, including time of connection, the traffic that was used over the connection, and which hosts connected at which times to make use of the connection. RADIUS The Remote Authentication Dial-In User Service (RADIUS) protocol was originally developed to provide for remote connections through older dial-in services. RADIUS provides AAA services to clients and providers. It is a standardized Internet specification and falls under several different RFCs, including RFC 2865, RFC 2866, and others. A basic client/server protocol, RADIUS uses User Datagram Protocol (UDP) as its transport protocol on ports 1812 (for authentication and authorization) and 1813 (for accounting functions). RADIUS has a few interesting terms you need to know. A RADIUS client is not the host attempting to connect; it is the network access server itself, to which remote hosts connect. This server is an intermediary that processes the connection request and passes it on to other servers, called RADIUS servers, which provide authentication services and can be either Windows or UNIX-based servers. Active Directory, in fact, 03-ch03.indd 203 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 204 can provide for authentication services to RADIUS clients, acting as a RADIUS server, through the Microsoft remote access and VPN services. In terms of security, though, RADIUS is a bit lacking. Although the communications between the RADIUS client and the RADIUS server are encrypted, communications between the RADIUS client and the remote host are not. Unfortunately, user name and password information could be intercepted between the remote host and the RADIUS client. RADIUS can support a variety of authentication methods, including some of the older ones, including PPP, PAP, and CHAP. EXAM TIP A RADIUS client is the network server that receives the connection request from the remote host and communicates with the RADIUS server. It is not the remote host itself. Diameter Diameter is an AAA protocol proposed to replace RADIUS. Its name is actually a pun and doesn’t really stand for anything. It makes sport of the fact that the diameter of a circle is twice the radius. Diameter supports a wider variety of authentication protocols, including the Extensible Authentication Protocol (EAP). It uses TCP port 3868 instead of the UDP that RADIUS uses. It also can handle more advanced security using IPsec and Transport Layer Security (TLS). NOTE Module 7-1, “Networking with 802.11,” covers wireless authentication protocols such as EAP and 802.1X in detail. TACACS, XTACACS, and TACACS+ The Terminal Access Controller Access Control System (TACACS) supplanted RADIUS and allows a remote user to connect and authenticate to a network via an intermediary TACACS server. It works pretty much the same way as RADIUS, with a few exceptions. XTACACS, which stands for Extended TACACS, provides additional functionality for the TACACS protocol. It also separates the authentication, authorization, and accounting functions out into separate processes, even allowing them to be handled by separate servers and technologies. TACACS+ is a Cisco-designed version of the older TACACS protocol that enables newer, more secure authentication protocols to be used over it, such as Kerberos and EAP. It also permits two-factor authentication. It has become an open standard. Unlike the issues that plague RADIUS with encryption between the remote host and the RADIUS client, TACACS+ encrypts all traffic between all connection points, to include user names and passwords. Unfortunately, TACACS+ is not backwardcompatible with the earlier versions of the protocol. TACACS uses TCP or UDP port 49 by default. 03-ch03.indd 204 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-5: Network Authentication 205 Module 3-5: Network Authentication This module covers the following CompTIA Security+ objectives: • 2.4 Summarize authentication and authorization design concepts • 3.1 Given a scenario, implement secure protocols • 3.8 Given a scenario, implement authentication and authorization solutions The point-to-point authentication methods described in the previous module are powerful tools for solutions to situations where a single client needs to authenticate to a single server acting as a gatekeeper to a larger network. Yet what do we do when we have many systems already connected on a single LAN? Unlike point-to-point, a client computer wanting to authenticate connects to many computers at all times (Figure 3-50). Authentication on a LAN has serious issues that methods such as MS-CHAP or RADIUS simply do not or cannot address. Let’s look at issues a LAN brings to access management and then look at the authentication methods and protocols used in most LANs to provide network authentication. The Challenge of LAN Access Management LANs change the concept of access management in a number of ways. First, LANs are much more permanent compared to most point-to-point connections. The desktop computer in your office, connected by a Gigabit Ethernet connection to your main switch, is probably going to spend a few years connected to your LAN. This means that the system needs some form of initial authentication to identify that computer to the network. Plus, you also need some method to authenticate any user who sits down in front of that computer to access network resources. Second, LANs are very fast compared to most Which one of you handles authentication? Figure 3-50 Network authentication is a different animal. 03-ch03.indd 205 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 206 Figure 3-51 Network access control must be flexible. I want to authenticate! Go ahead! Go ahead! Go ahead! point-to-point connections. If you are going to authenticate, you need fast protocols that allow systems to authenticate quickly. Third, most anything done on LANs is broadcast to every other computer on the broadcast domain, requiring authentication methods that allow for many systems to authenticate and authorize each other (Figure 3-51). The permanency of LANs is motivation for a feature you don’t see in point-to-point connections. With a LAN, the systems tend to be relatively fixed and permanent, but users tend to move around. This means that a good LAN access solution has the flexibility to enable any user to sit at any computer and authenticate themselves to the network as a whole. The last and possibly biggest issue is the concept that any single system may offer shared resources to properly authenticated and authorized users on any system. This creates an issue in that every system on the network has its own authentication database, almost always user accounts/passwords. Unless something else is done, a user must authenticate to every system on the LAN individually (Figure 3-52). Every computer on a LAN has an operating system that comes with networking tools for naming systems, sharing resources, and authenticating users. And every modern operating system can easily share files among each other. For sharing, for example, Windows, macOS, and Linux/UNIX use the server message block (SMB) protocol (also known generically as Windows file sharing), so all three operating system families can easily share (Figure 3-53). If you want access to my shared resources you must authenticate to ME! If you want access to my shared resources you must authenticate to ME! If you want access to my shared resources you must authenticate to ME! Figure 3-52 In a LAN each system is an island. 03-ch03.indd 206 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-5: Network Authentication 207 I’m a Windows system. I use SMB for file sharing. I’m a Mac. I also use SMB for file sharing. I’m a Linux system. I too use SMB for file sharing. Figure 3-53 Everybody speaks Windows file sharing! Each operating system also has tools for authentication, particularly for logging into Windows machines. Because Windows dominates the marketplace, Windows authentication methods loom large. The next section explores Windows authentication methods in detail. Microsoft Networking Microsoft networking has been around for a very long time and has gone through an incredible number of changes and iterations, but we can make a few straightforward breakdowns. First, all Windows systems are organized in one of two ways: workgroups or domains. In a workgroup, every Windows system stores local user names and passwords and controls access to its own resources. In a domain, all computers authenticate to a single authentication server known as a domain controller (Figure 3-54). A modern Windows domain stores far more than just user names and passwords. This more advanced, very powerful domain type is known commonly as Active Directory (AD). We each handle our authentications. Workgroup I handle all authentication. Domain Figure 3-54 Workgroup vs. domain 03-ch03.indd 207 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 208 Figure 3-55 Windows Server domains Every Windows computer on earth is a member of either a workgroup or a domain. Using workgroups is the default network organization and is very common in homes and small offices. In a workgroup, a user must have an account on every system from which they wish to access shared resources. A common way to get around this issue is to make the same account with the same password on every system. Domains require a system running special, powerful, and expensive Windows Server operating systems (Figure 3-55). Every computer on the network then goes through a special process of joining the domain. Once a computer joins the domain, it authenticates to the domain controller. A user can log onto any system in the domain and log onto the domain—the perfect example of single sign-on in action. NOTE Windows’ domain single sign-on function is so popular that other operating systems will use Samba to enable individual systems to log onto a Windows domain controller even if they have no interest in sharing folders. Workgroups and domains are very important in that Windows uses very different authentication methods depending on whether there is a workgroup or a domain. In a workgroup, Windows uses the very old, slightly vulnerable but easy to implement and backward-compatible NT LAN Manager (NTLM). Windows domain controllers use the powerful and robust Kerberos authentication protocol. NTLM Microsoft developed a series of proprietary authentication protocols early on during Windows development, and for the most part, they have been deprecated and are no longer included in new versions of the Windows operating system. You should be aware of them for the exam, however, and you may actually run into some of these from time to time in your professional career. The LAN Manager (LANMAN) protocol was developed and included in Microsoft Windows NT. Like any first attempt, it had weaknesses. For example, its hash-stored passwords are easily broken if they are obtained by an attacker. LANMAN was disabled by default starting in Windows Vista and shouldn’t be used unless you’re running legacy clients that require it. 03-ch03.indd 208 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-5: Network Authentication 209 New Technology LAN Manager (NTLM) was created by Microsoft to replace LANMAN and is backward-compatible with the older protocol. It’s also a very non-secure protocol, and it was quickly replaced by NTLM version 2. Both versions are challenge-response authentication protocols and work similarly to CHAP. Version 2 is used in modern iterations of Windows, but only for workgroup authentication. Kerberos is the default authentication protocol for Windows domains (see the next section), but there are still times when NTLM v2 is used, even in domains. These instances include authenticating to a server using only an IP address, authenticating to a different AD network that has a legacy trust enabled, or authenticating a host to a non-AD domain. In these instances, Windows will default to using NTLM v2. EXAM TIP Understand the situations in which Windows will default to using NTLM v2 instead of Kerberos for its authentication protocol. Usually this occurs where there is no AD environment and the host is communicating in a workgroup setup. Kerberos The Kerberos network authentication protocol is used in modern Active Directory implementations. It began as a project of the Massachusetts Institute of Technology (MIT) and has been implemented as a centralized, single sign-on authentication mechanism. It is an open standard, supported officially as an Internet standard by RFC 4120. As of this writing, the most current version of Kerberos widely in use is version 5. Kerberos uses a system based on authentication tickets and time stamps that are issued to the authenticated user. Time stamps help prevent replay attacks because the tickets expire after a short time and must be refreshed, requiring that the user be reauthenticated and the ticket reissued. Kerberos’s time stamps rely heavily on authoritative time sources throughout the network architecture, so many implementations also provide for a network time server. Time synchronization is critical in Kerberos. A classic usage case is the “I can’t log into my domain” problem. If clients are outside a certain tolerance for time difference with the Kerberos server, the users logging into those clients will not be authenticated. The default tolerance for time differences is 5 minutes in an Active Directory network, although this can be changed. Windows systems lean heavily on time synchronization and constantly keep their time synchronized with their domain controller. Kerberos uses several components, which you should be familiar with for the exam. First is the Kerberos Key Distribution Center (KDC), which is responsible for authenticating users and issuing session keys and tickets. In Active Directory implementations, the domain controller serves as the KDC. There is also an Authentication Service (AS) and a Ticket-Granting Service (TGS). Although they are not required to be on the same host, these services frequently are, for simplicity and efficiency’s sake, on AD domain controllers in a Windows environment and are part of the KDC implementation. When a user logs into the system, the AS verifies her identity using the credentials stored in AD. The user is then issued a Ticket-Granting Ticket (TGT) by the AS, which can be used to access resources throughout the domain. The TGT expires after a certain 03-ch03.indd 209 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 210 2. AS authenticates and issues the user a Ticket-Granting Ticket (TGT). 1. Client requests authentication. 3. Client needs to access resource and presents TGT to TGS. 4. TGS issues service ticket for the session. Client/User 5. Server and client communicate using the service ticket issued by the TGS. Resource Server Figure 3-56 Kerberos process in Windows environments amount of time, so it must be periodically reissued. When a user wants to access a resource in the domain, the TGT is presented to the TGS for authentication and the TGS generates a session key for the communications session between the user and the resource server. This is known as a service ticket and is used for the duration of the access to the resource. When a user later needs access to the same or a different resource, the older ticket is not reused and a new service ticket is generated. Note that the process we’ve described is specific to Windows AD implementations of Kerberos, but the principles are the same regardless of what operating system and LDAPbased implementation are in use. A network that uses Kerberos as its authentication protocol is called a Kerberos realm. Kerberos uses both TCP and UDP ports 88, and it uses symmetric key cryptography. Figure 3-56 illustrates the Kerberos process in Windows AD. LDAP and Secure LDAP The power of modern Active Directory networks requires a language that allows different domain controllers to query each other’s ADs. This is where LDAP comes into play. The Lightweight Directory Access Protocol (LDAP) isn’t an authentication protocol; it’s used to assist in allowing already authenticated users to browse and locate objects in a distributed network database (like a Windows AD spread out among two or more domain controllers). It’s also used to facilitate authentication and authorization for these objects. LDAP is a modern replacement for older X.500 directory services protocols 03-ch03.indd 210 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-6: Identity Management Systems 211 (used for authentication). Although the most popular iteration of LDAP (its current version is version 3) can be found in AD, other platforms use LDAP as well, including the popular OpenLDAP. LDAP uses both TCP and UDP ports 389. There is a secure version of LDAP that uses TCP port 636. It’s primarily Lightweight Directory Access Protocol over SSL (LDAPS), and it has been deprecated with LDAP version 2. NOTE Keep in mind that LDAP is not an authentication protocol, but it does facilitate authentication and resource access. Module 3-6: Identity Management Systems This module covers the following CompTIA Security+ objectives: • 3.7 Given a scenario, implement identity and account management controls • 3.8 Given a scenario, implement authentication and authorization solutions Single sign-on (SSO) for network authentication has been around for a long time. We’ve already covered single sign-on in a LAN with Microsoft Windows domains as probably the best single example. As powerful as single sign-on is for LANs, it traditionally has never been used on the Internet. Anyone who has spent any amount of time bouncing from one secure Web site to another appreciates the hassle of remembering user names and passwords for every site. With the proliferation of Internet services comes password fatigue, the user-based syndrome of “I have to set up yet another user account and password to remember for [insert name of new, must-have Web site] service too? Not again!” (Figure 3-57). NOTE In fairness, Windows’ domain single sign-on can span multiple LANs, but it’s not commonly used to secure public Web sites. Figure 3-57 Many passwords to memorize 03-ch03.indd 211 Secure Site A User name Password Secure Site B Username Password Secure Site C User name Password 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 212 The idea of one user name and password to rule them all has merits, certainly, but also opens a huge discussion about how to keep that identity secure. Plus, it requires understanding how to establish trusts such that a user can sign on to one site and in some way then transfer that authentication to other sites in a secure fashion. This module explores identity management systems (IMSs), tools used to simplify secure access to multiple Internet-based services via single sign-on. We’ll start with the physical, with security tokens, then look at shared authentication schemes. The module finishes with single sign-on options. Trust One of the great powers of a Windows domain SSO is the fact that there is always a domain controller (and maybe a few secondary domain controllers) that stores a single repository of users and their associated passwords. When you log onto a Windows domain, you log onto a domain controller. Once your user account authenticates, the different servers provide authorization to their resources via your Windows security identifier. Every computer on the domain trusts the domain controller. Web sites have no domain controller to handle authentication. To make some form of IMS work for the most distributed of all networks, the Internet, requires trust. Every IMS begins by giving any Web site that wants to use it some way to trust someone big like Google, Facebook, or Twitter. The Web site treats the sign-in you use with a trusted big platform as an option or a replacement for your signing in at the Web site itself. The individual sites, however, still handle their own authorization (Figure 3-58). In general, an IMS provides a connection to log into one of these big platforms and, in turn, provides a token that the little sites use. Module 3-2 touched on the concepts of tokens, physical objects that enable access to restricted areas or content. A security token in an online IMS can be a physical thing, like a smartphone, that contains authentication or password information. It might also be a bit of data that stores some form of descriptor for the authentication used. You see this sort of token manifest in game systems, for example, where you change something online and a message is sent to your smartphone. The change will go through only by entering the security code sent to the phone. The stored security information in security tokens is often hashed to prevent access in the event of theft or loss of the device. Figure 3-58 This site has a lot of trust. 03-ch03.indd 212 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Module 3-6: Identity Management Systems 213 EXAM TIP The CompTIA Security+ exam objectives refer to security tokens as simply tokens. Shared Authentication Schemes Shared authentication schemes use various protocols, languages, and mechanisms to provide easier access to online resources for people. The two most prominent schemes are SAML and OpenID. The Security Assertion Markup Language (SAML) provides a format for a client and server to exchange authentication and authorization data securely. SAML defines three roles for making this happen: principal, identity provider, and service provider. The client or user is often the principal. The principal wants something from the service provider (SP), the latter often a Web service of some kind. The identity provider (IdP) contains information that can assure the SP that the principal is legitimately who he says he is. Systems using SAML can use any number of methods for authentication, including passwords and user names. Many companies—big ones, like Amazon, Google, and Microsoft—use OpenID as an alternative to SAML, enabling users to log into other services using their respective credentials. Figure 3-59 shows a typical use of OpenID. The user accesses a new (to him) Web-based service and can log in using his Google account. Figure 3-59 Sign in with Google! 03-ch03.indd 213 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 214 OpenID handles the authentication part of the identification process, but relies on OAuth for authorization. OAuth enables things like users granting information to Web sites without revealing their passwords. Many SSO standards rely on SAML for secure communication between principals and SPs. The SSO standards differ from the previous standards in that the latter require additional use of the same user credentials. SSO standards do not. The Shibboleth SSO system, for example, uses SAML (versions 1.3 and 2.0) to authenticate to various federations of organizations. As discussed in Module 3-1, federations enable content providers to provide content without retaining any personal information about clients or principals. This applies to Web-based systems as well as LAN- and domain-based systems. Questions 1. Which of the following terms describes the process of allowing access to different resources? A. Authorization B. Authentication C. Accountability D. Identification 2. Which of the following states that users should be given only the level of access needed to perform their duties? A. Separation of duties B. Accountability C. Principle of least privilege D. Authorization 3. Which of the following access control models allows object creators and owners to assign permissions to users? A. Rule-based access control B. Discretionary access control C. Mandatory access control D. Role-based access control 4. An administrator wants to restrict access to a particular database based upon a stringent set of requirements. The organization is using a discretionary access control model. The database cannot be written to during a specified period when 03-ch03.indd 214 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Questions 215 transactions are being reconciled. What type of restriction might the administrator impose on access to the database? A. Access restricted by the database owner B. Access based upon membership in a logical group C. Access from a particular workstation D. Time-of-day and object permission restrictions 5. Which of the following allows a user to use one set of credentials throughout an enterprise? A. TACACS B. RADIUS C. Single sign-on D. TACACS+ 6. Which of the following is used to prevent the reuse of passwords? A. Account disablement B. Account lockout C. Password complexity D. Password history 7. Which of the following are the best ways to ensure that user accounts are being used appropriately and securely? (Choose two.) A. Periodically review assigned privileges. B. Allow users to maintain their privileges indefinitely, even during promotion or transfer. C. Continuously monitor accounts, through auditing, to ensure accountability and security. D. Ensure that users’ permissions stay cumulative, regardless of which group or job role they occupy. 8. Which of the following authentication factors would require that you input a piece of information from memory in addition to using a smart card? A. Possession B. Knowledge C. Inherence D. Temporal 9. You are implementing an authentication system for a new company. This is a small company, and the owner has requested that all users be able to create 03-ch03.indd 215 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 3 Chapter 3: Identity and Account Management 216 accounts on their own individual workstations. You would like to explain to the owner that centralized authentication might be better to use. Which of the following are advantages of centralized authentication? (Choose two.) A. Centralized security policies and account requirements. B. Ability of individuals to set their own security requirements. C. Ability to use single sign-on capabilities within the entire organization. D. Requirements have different user names and passwords for each workstation and resource. 10. Under which of the following circumstances would a Windows host use Kerberos instead of NTLM v2 to authenticate users? A. Authenticating to a server using only an IP address B. Authenticating to a modern Windows Active Directory domain C. Authenticating to a different Active Directory forest with legacy trusts enabled D. Authenticating to a server in a Windows workgroup Answers 1. A. Authorization describes the process of allowing access to different resources. 2. C. The principle of least privilege states that users should be given only the level of access needed to perform their duties. 3. B. The discretionary access control model allows object creators and owners to assign permissions to users. 4. D. The administrator would want to impose both a time-of-day and object permission restriction on users to prevent them from writing to the database during a specified time period. 5. C. Single sign-on allows a user to use one set of credentials throughout an enterprise to access various resources without having to reauthenticate with a different set of credentials. 6. D. The password history setting in the account policy is used to prevent the reuse of older passwords. 7. A, C. Periodic reviews and continuous monitoring are two ways to ensure that accounts and privileges are used in accordance with organizational policy and in a secure manner. 8. B. The knowledge factor would require that you input a piece of information, such as a password or PIN, from memory in addition to using a smart card. 9. A, C. Centralized system security policies as well as the ability to use single sign-on throughout the organization are two advantages of centralized authentication. 10. B. When authenticating to a modern Windows Active Directory domain, Windows uses Kerberos as its authentication protocol by default. 03-ch03.indd 216 25/03/21 2:13 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 CHAPTER Tools of the Trade 4 I have a thing for tools. —Tim Allen IT security professionals use a lot of tools to keep networks secure. These tools range from go-to utilities that run from the command-line interface of just about every operating system to more complex tools for scanning network activity. Security professionals spend a phenomenal amount of time setting up and monitoring logs of system activities so that when that bad actor steps in or some odd action occurs, they’re ready to save the day. This chapter explores essential IT security tools in four modules: • • • • Operating System Utilities Network Scanners Protocol Analyzers Monitoring Networks Module 4-1: Operating System Utilities This module covers the following CompTIA Security+ objectives: • 3.7 Given a scenario, implement identity and account management controls • 4.1 Given a scenario, use the appropriate tool to assess organizational security Windows, macOS, and every Linux distro come with a host of tools for security professionals. The tools enable you to query network settings, explore routing options, diagnose connection problems, and much more. Built-in tools give you flexibility and availability—you need to know them. This module covers many of the utilities included in Windows and UNIX/Linux systems. These utilities are listed in the CompTIA Security+ objectives and, more importantly, every good tech should recognize all of these as well as know where and when to use them (Figure 4-1). 217 04-ch04.indd 217 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 218 Figure 4-1 We love utilities! I love my built-in utilities! The CompTIA Security+ objectives break these tools into three groups (no doubt to keep the organization a bit easier): network reconnaissance and discovery, file manipulation, and shell and script environments. Network Reconnaissance and Discovery Sometimes you need to find out details about your system’s network settings and how that system communicates with both your local network and extended network. Both Windows and Linux come with plenty of tools, many of them the same or nearly the same, to do exactly that job. Let’s explore a dozen or so tools: • • • • • • • • • • • • • • ping ipconfig ifconfig ip arp netstat route netcat tracert/traceroute pathping TCPView PingPlotter nslookup dig ping The ping utility enables you to query another system on a TCP/IP network to determine connectivity. ping uses Internet Control Message Protocol (ICMP) packets at OSI Layer 3, Network, for queries. It’s not a perfect tool, because many systems disable ICMP traffic to avoid attacks, but ping is quick and effective enough that you’ll find it very useful. 04-ch04.indd 218 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 219 Figure 4-2 ping in Windows When one system successfully pings another host, you automatically know that the other system is connected and is properly IP addressed. Figure 4-2 shows a successful ping running in a Windows terminal. We know it’s successful because it shows replies from the pinged system (192.168.0.1). By default, ping runs four times in Windows and stops automatically. In Linux, ping runs continuously until you press ctrl-c. To get ping to run continuously in Windows, use the –t switch. The ping utility has uses beyond simply verifying connectivity. Running ping using a DNS name, for example, is a great way to verify you have a good DNS server. Look at Figure 4-3. Note that the ping is unsuccessful (shows Destination port unreachable), but the ping successfully resolves the DNS name (www.cheese.com) to an IP address (195.149.84.153). The ping utility offers many more features that IT security professionals use all the time. Here’s a list of some of the more useful switches: • • • • • 04-ch04.indd 219 –a –t –f –4 –6 Resolve addresses to hostnames Run continuously Set Don’t Fragment flag in packet (IPv4 only) Force using IPv4 Force using IPv6 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 220 Figure 4-3 ping resolving an IP address NOTE Administrators disable ICMP—and thus, ping requests—for a variety of reasons, but most notably because people can use ping maliciously. The ping of death sends malformed packets to a computer, possibly causing a crash. Continuous ping requests—as a denial-of-service attack—can also crash systems. You’ll see more about attacks such as these in Chapter 5. ipconfig Use the ipconfig command in Windows to show the current status of the network settings for a host system. Figure 4-4 shows sample output from ipconfig in Windows 10. You can see the various IPv6 addresses plus the IPv4 address and subnet mask. Typing ipconfig by itself also shows the default gateways. Using switches enhances the ipconfig output; the following six switches are particularly useful. Typing ipconfig /all, for example, lists virtually every IP and Ethernet setting on the system. • • • • • 04-ch04.indd 220 /all Get exhaustive listing of virtually every IP and Ethernet setting /release Release the DHCP IP address lease /renew Renew the DHCP IP address lease /flushdns Clear the host’s DNS cache /displaydns Display the host’s DNS cache 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 221 Figure 4-4 Results from running ipconfig ifconfig Use the ifconfig command in UNIX/Linux and macOS operating systems to show the current status of the network settings for a host system. Figure 4-5 shows ifconfig running in Ubuntu Linux. This shows a lot of configuration settings for the Ethernet connection (enp0s3), including the MAC address (HWaddr), IPv4 address (inet addr), broadcast Figure 4-5 ifconfig in Ubuntu 04-ch04.indd 221 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 222 IP address, and subnet mask. You can see the IPv6 address (inet6 addr) and many more details. The lo connection is the loopback, which is the expected 127.0.0.1. Unlike ipconfig, ifconfig goes beyond basic reporting, enabling you to configure a system. The following example sets the IP address and the subnet mask for the Ethernet NIC eth0: sudo ifconfig eth0 192.168.0.1 netmask 255.255.255.0 NOTE Linux systems also have the iwconfig command exclusively for wireless connections. ip If you’re looking to do anything serious in terms of IP and Ethernet information on a Linux (not macOS) system, the cool kid is the ip command. The ip command replaces ifconfig, doing many of the same tasks, such as viewing IP information on a system, checking the status of network connections, managing routing, and starting or stopping an Ethernet interface. The syntax differs from ipconfig and ifconfig, dropping a lot of the extra nonalphanumeric characters and shortening switch names. To see all the Ethernet and IP information for a system, for example, just type ip addr to get results like Figure 4-6. You can see the loopback address (lo) for both IPv4 (127.0.0.1/8) and IPv6 (::1/128) and the IPv4 and IPv6 addresses assigned to the Ethernet port (eth0). Typing ip addr does not show the MAC address. For that you’d type ip link. Figure 4-6 Running the command ip addr in Kali Linux 04-ch04.indd 222 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 223 arp Every host on a network keeps a cache of mapped IPv4-to-Ethernet addresses for the local network. The arp command enables you to observe and administer this cache. Interestingly, both the Windows version and the Linux version use almost the same switches. If you want to see the current cache, type the command as follows (Windows version): C:\>arp -a Interface: 192.168.1.75 Internet Address 192.168.1.1 192.168.1.58 192.168.1.128 192.168.1.255 224.0.0.2 224.0.0.22 224.0.0.251 --- 0x2 Physical Address 14-dd-a9-9b-03-90 88-de-a9-57-8c-f7 30-cd-a7-b6-ff-d0 ff-ff-ff-ff-ff-ff 01-00-5e-00-00-02 01-00-5e-00-00-16 01-00-5e-00-00-fb Type dynamic dynamic dynamic static static static static (Several output lines have been removed for brevity.) The dynamic entries in the Type column show listings under control of DHCP. Static types are fixed (the multicast addresses that start with 224 never change) or are for statically assigned IP addresses. NOTE The arp command is only for IPv4 addresses. IPv6 uses the Neighbor Discovery protocol. The arp command enables detection of ARP spoofing, when a separate system uses the arp command to broadcast another host’s IP address. Look carefully at this arp command’s output and note that two systems have the same IP address: C:\>arp -a Interface: 192.168.1.75 Internet Address 192.168.1.1 192.168.1.58 192.168.1.58 --- 0x2 Physical Address 14-dd-a9-9b-03-90 88-de-a9-57-8c-f7 23-1d-77-43-2c-9b Type dynamic dynamic dynamic Given that most operating systems return an error when this happens, you might think using arp isn’t helpful. But arp at least provides the MAC address for the spoofing system, which might help you determine the offending system. (A lot of modern switches employ Dynamic ARP Inspection [DAI] to deal with ARP spoofing automatically, though that’s beyond the discussion here.) NOTE The arp command (lowercase) displays information on aspects of the system that use the Address Resolution Protocol (ARP). The mapped cache of IP-to-Ethernet addresses, for example, is the ARP cache. arp and other command-line utilities listed here are lowercase to reflect the casesensitivity of UNIX/Linux systems. 04-ch04.indd 223 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 224 netstat The netstat command is the go-to tool in Windows and Linux to get any information you might need on the host system’s TCP and UDP connections, status of all open and listening ports, and a few other items such as the host’s routing table. Typing netstat by itself shows all active connections between a host and other hosts: C:\Users\Mike>netstat Active Connections Proto Local Address TCP 127.0.0.1:5432 TCP 127.0.0.1:5432 TCP 127.0.0.1:5432 Foreign Address MiKESLAPTOP:50165 MiKESLAPTOP:50168 MiKESLAPTOP:50175 State ESTABLISHED ESTABLISHED ESTABLISHED You can see that the first few lines of any netstat show a number of active connections with the loopback address (the 127.x.x.x). These are used by Microsoft for several different information exchanges such as the Cortana voice recognition utility. Other connections show up as more varied IP addresses: TCP TCP TCP TCP TCP TCP TCP TCP 192.168.1.75:57552 192.168.1.75:58620 192.168.1.75:60435 192.168.1.75:60444 192.168.1.75:60457 192.168.1.75:60461 192.168.1.75:60466 192.168.1.75:60537 167.125.3.3:https msnbot-25-52-108-191:https 61.55.223.14:33033 92.190.216.63:12350 42.122.162.208:https 62.52.108.74:https a14-112-155-235:https 65.55.223.12:40027 CLOSE_WAIT ESTABLISHED ESTABLISHED ESTABLISHED ESTABLISHED ESTABLISHED CLOSE_WAIT CLOSE_WAIT The preceding netstat output shows the open connections on this system, mainly HTTPS connections for Web pages. In the State column on the right, ESTABLISHED identifies active connections and CLOSE_WAIT indicates connections that are closing. Typing netstat in Linux gives the same information, but in a slightly different format. At the very bottom are the associated UNIX sockets. A socket is an endpoint for connections. This data is very long and not very useful. Figure 4-7 shows just the first few lines. Typing netstat –a in Windows or Linux shows the same information as netstat alone, but adds listening ports. This is a very powerful tool for finding hidden servers or malware on a host. Look carefully at the following command. Notice that HTTP port 80 and HTTPS port 443 are listening. This instantly tells you that the host is an HTTP/ HTTPS server. You must then answer the question: “Should this system be running a Web server?” C:\Users\Mike>netstat -a Active Connections Proto Local Address TCP 0.0.0.0:135 TCP 0.0.0.0:445 TCP 0.0.0.0:3780 TCP 127.0.0.1:9990 TCP 127.0.0.1:17600 TCP 192.168.1.75:80 TCP 192.168.1.75:443 TCP 192.168.1.75:6698 TCP 192.168.1.75:13958 Foreign Address MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 MiKESLAPTOP:0 State LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING LISTENING (Lines removed for brevity.) 04-ch04.indd 224 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 225 Figure 4-7 netstat in Linux Running netstat with the –b option displays the executable file making the connection. Here’s netstat running in Windows PowerShell (introduced later in this module) using both the –b and –a options (with many lines removed for brevity): PS C:\WINDOWS\system32> netstat Active Connections Proto Local Address TCP 0.0.0.0:135 [svchost.exe] TCP 0.0.0.0:80 [svchost.exe] TCP 0.0.0.0:17500 [Dropbox.exe] TCP 0.0.0.0:47984 [NvStreamNetworkService.exe] TCP 192.168.1.75:6698 [SkypeHost.exe] TCP 192.168.1.75:58620 [Explorer.EXE] TCP 192.168.1.75:62789 [OneDrive.exe] -a -b Foreign Address MiKESLAPTOP:0 State LISTENING MiKESLAPTOP:0 LISTENING MiKESLAPTOP:0 LISTENING MiKESLAPTOP:0 LISTENING MiKESLAPTOP:0 LISTENING msnbot-65-52-108-191:https ESTABLISHED msnbot-65-52-108-205:https ESTABLISHED Researching open ports and processes in netstat is nerve wracking. What are these programs? Why are they listening? A quick Web search of the filename often gives you excellent guidance as to which programs are good, which are evil, and which you simply don’t need. NOTE The netstat command works perfectly well with IPv6. 04-ch04.indd 225 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 226 netstat is an incredibly powerful tool, and this short description barely touched its capabilities. For the CompTIA Security+ exam, you should experiment with netstat both in Linux and in Windows. route The route command enables you to display and edit a host’s routing table. Inspecting a routing table enables you to find problems if packets leave your system but never get a response. In Linux you type route to see the routing table; in Windows you type route print. Here’s an example of this in Linux: mike@mike-VirtualBox:~$ route Kernel IP routing table Destination Gateway default _gateway 10.0.2.0 0.0.0.0 link-local 0.0.0.0 Genmask 0.0.0.0 255.255.255.0 255.255.0.0 Flags UG U U Metric 100 100 1000 Ref 0 0 0 Use 0 0 0 Iface enp0s3 enp0s3 enp0s3 The operating system automatically generates routing tables on individual hosts based on the network settings. So using route to display the routing table seems logical. On the other hand, you can use route to make changes to the routing table for a variety of reasons. You could set up a static route for security purposes, for example, or remove a route to a specific host to force a secondary gateway. NOTE The route command rarely comes with Linux distros. Use the apt or rpm command to install the net-tools package, which includes plenty more than route as well. netcat netcat (or nc) is a terminal program for Linux that enables you to make any type of connection and see the results from a command line. With nc, you can connect to anything on any port number or you can make your system listen on a port number. Figure 4-8 shows nc connecting to a Web page. The nc command is a primitive tool. To get any good information from the connection, the user must know the protocol well enough to type in properly formed input data. Since this is a Web page, type get index.html HTTP/1.1, as this is what the Web server is expecting. Figure 4-9 shows the result. The challenge and the power of nc come from the fact that it’s a tool for people who know how to type in the right commands, making it great for penetration testing or, if you’re evil, hacking. Imagine making a connection to a server and typing in anything you want to try to fool the server into doing something it’s not supposed to do! Figure 4-8 Connecting to www.google.com with nc 04-ch04.indd 226 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 227 Figure 4-9 Successful connection to www.google.com with nc The nc command even works as a handy scanning command. Find a server, guess on a port number, and try connecting! The nc command works perfectly with scripts. It’s relatively easy to write a script that tries 1024 port numbers one after the other, automating the scanning process. NOTE Windows lacks an equivalent to netcat, but Ncat from https://nmap .org/ncat/ has very similar functionality. tracert/traceroute If you want to know how packets are routed from a host to an endpoint, try the Windows tracert command. Linux can use the almost identical command called traceroute (although it’s not installed by default on many distros, including Ubuntu). Either command sends packets to each connection between the host and the endpoint, checking the time to live (TTL) between those connections. Running tracert returns something like this: C:\>tracert www.robotmonkeybutler.com Tracing route to www.robotmonkeybutler.com [64.98.145.30] over a maximum of 30 hops: 1 5 ms 9 ms 2 5 ms 18 ms 3 15 ms 14 ms [68.85.253.229] 4 14 ms 10 ms [68.85.247.29] 5 ms 10 ms 19 ms 192.168.4.1 10.120.17.101 ae201-sur04.airport.tx.houston.comcast.net 17 ms ae-0-sur03.airport.tx.houston.comcast.net (Hops 5 through 12 removed for brevity.) 13 71 ms 66 [130.94.195.234] 14 63 ms 60 15 65 ms 68 16 59 ms 58 ms 179 ms ms ms ms 69 ms 70 ms 67 ms xe-0-10-0-3-5.r05.asbnva02.us.ce.gin.ntt.net iar02-p3.ash.tucows.net [64.98.2.10] csr-p6.ash.tucows.net [64.98.128.14] url.hover.com [64.98.145.30] Trace complete. 04-ch04.indd 227 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 228 The power of tracert comes by running it before there are any problems. If you look at the previous example, you see the first two hops use a private IP address. This is correct, because this network has two routers between the host and the ISP—in this case, Comcast. Let’s say we run this command again and get this result: C:\>tracert www.robotmonkeybutler.com Tracing route to www.robotmonkeybutler.com [64.98.145.30] over a maximum of 30 hops: 1 5 ms 9 ms 5 ms 192.168.4.1 2 5 ms 18 ms 10 ms 10.120.17.101 3 [10.120.17.101] reports: Destination host unreachable The tracert successfully made it through both internal routers, but couldn’t make it to the ISP. In this case we know there’s something wrong between the gateway and the ISP. It could be that the ISP simply blocks ICMP packets (the protocol used with tracert in Windows). You can test this by running traceroute in Linux or macOS, which use UDP rather than ICMP by default. pathping pathping, a Windows-only utility, is an interesting combination of tracert and ping. pathping first runs a traceroute, but then pings each hop 100 times. All this pinging determines latency much more accurately than tracert does. Pathping is slower than tracert. The following example of pathping forces no DNS resolution and requires only IPv4 addresses. C:\System32\pathping -n -4 www.ibm.com Tracing route to user-att-108-66-144-0.e2874.dscx.akamaiedge.net [104.94.70.94] over a maximum of 30 hops: 0 172.18.13.117 1 172.18.13.1 2 104.186.12.1 3 * * * Computing statistics for 50 seconds... Source to Here This Node/Link Hop RTT Lost/Sent = Pct Lost/Sent = Pct Address 0 172.18.13.117 0/ 100 = 0% | 1 0ms 0/ 100 = 0% 0/ 100 = 0% 172.18.13.1 0/ 100 = 0% | 2 1ms 0/ 100 = 0% 0/ 100 = 0% 104.186.12.1 Trace complete. NOTE In Linux, try either the mtr command or tracepath command rather than the old and often not-even-installed traceroute. Neither tool is mentioned in the CompTIA Security+ SY0-601 objectives, but we think you’ll find them useful. TCPView and PingPlotter Need something a little more graphical in your life? There are many interesting graphical tools that enable you to access these commands graphically. Graphical tools often 04-ch04.indd 228 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 229 Figure 4-10 PingPlotter in action provide easier-to-grasp information that the command-line tools lack. Finding netstat a little frustrating? Try TCPView from Windows Sysinternals instead of netstat. Or maybe replace boring old ping/traceroute with PingPlotter from Pingman Tools (Figure 4-10). There are a ton of great tools out there. Take your time, do some research, and find the ones you enjoy. NOTE tracert is often a great way to determine the ISP just by looking at the router names. DNS Tools DNS security issues can create huge problems for IT security professionals. Techniques such as spoofing or replacing a host’s DNS server settings give an attacker tremendous insight as to whom the host is communicating with. While there are multiple tools and techniques used to diagnose DNS issues, two built-in OS utilities can be very useful: nslookup and dig. nslookup The nslookup tool, built into both Windows and Linux, has one function: if you give nslookup a DNS server name or a DNS server’s IP address, nslookup will query that DNS server and (assuming the DNS server is configured to respond) return incredibly detailed information about any DNS domain. For example, you can run nslookup to ask a DNS server for all the NS (name server) records for any domain. This power of nslookup has been used for evil purposes. For that reason, almost no public DNS server supports nslookup anymore for anything but the simplest queries. But there are still good reasons to use nslookup. 04-ch04.indd 229 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 230 NOTE nslookup works similarly in both Linux and Windows. The most basic way to run nslookup is to type the command followed by a domain. For example: C:\WINDOWS\system32>nslookup www.totalsem.com Server: cdns01.comcast.net Address: 2001:558:feed::1 Non-authoritative answer: Name: www.totalsem.com Address: 75.126.29.106 The first server is an assigned DNS server for a host. The non-authoritative answer is the returned IP address for www.totalsem.com. The URL www.totalsem.com is a public Web server. The totalsem.com domain has a private file server, however, named server1 .totalsem.com. If that URL is queried by nslookup the following happens: C:\WINDOWS\system32>nslookup server1.totalsem.com Server: cdns01.comcast.net Address: 2001:558:feed::1 *** cdns01.comcast.net can't find server1.totalsem.com: Non-existent domain This is good. The authoritative DNS server is configured to protect this private server and therefore not respond to an nslookup query. nslookup can tell you if an IP address is a functioning DNS server. Run nslookup interactively by typing nslookup to get a prompt: C:\WINDOWS\system32>nslookup Default Server: cdns01.comcast.net Address: 2001:558:feed::1 > Then type in the IP address of the DNS server you want to check: > server 8.8.8.8 Default Server: google-public-dns-a.google.com Address: 8.8.8.8 > Note that it returns a DNS name. This means there is a reverse DNS zone; a very good sign, but still not proof. Let’s make it resolve a known-good DNS name: > www.totalsem.com Server: google-public-dns-a.google.com Address: 8.8.8.8 Non-authoritative answer: Name: www.totalsem.com Address: 75.126.29.106 > 04-ch04.indd 230 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 231 But look at this alternate response: DNS request timed out. timeout was 2 seconds. *** Request to [4.7.3.4] timed-out > This could mean that the server IP address is not a functional DNS server. Or, at the very least, that the DNS service on this particular server isn’t working. dig The dig command is a Linux-based DNS querying tool that offers many advantages over nslookup. dig works with the host’s DNS settings, as opposed to nslookup, which ignores the host’s DNS settings and makes queries based on the variables entered at the command line. dig also works well with scripting tools. The dig tool is unique to Linux, although you can find third-party Windows dig-like tools. dig is simple to use and provides excellent information with an easy-to-use interface. Figure 4-11 shows a basic dig query. Try other dig options. For example, if you want to know all the mail server (MX) servers for a domain, just add the MX switch, as shown in Figure 4-12. NOTE The Linux host command isn’t listed on the CompTIA Security+ objectives, but is a great tool and one of our favorites. Know nslookup and dig for the exam, but check out the host command too! File Manipulation Commands generate readable output. If you want to preserve output from a command for future reference, you can save the command output as a text file. In Linux, pretty Figure 4-11 Simple dig query 04-ch04.indd 231 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 232 Figure 4-12 Querying for MX records (output reduced for brevity) much all log files (we’re diving into log files later in Module 4-4) are text files that you can review, search, and edit. Several Linux utilities provide this capability: cat, chmod, grep, head, tail, and logger. NOTE The CompTIA Security+ objectives don’t mention several important commands that you should know as an IT security professional, such as sudo, ls, cd, cp, mv, and delete. Because of their practical importance as IT security tools, you should review them. cat The cat command enables you to combine—concatenate—files. Concatenate two files to the screen with the following command: cat file1.txt file2.txt To concatenate these same two files and create a new file, use the following command: cat file1.txt file2.txt > file3.txt The cat utility also enables you to view the contents of any text file. Just type cat followed by the text file you wish to see and it appears on the screen: mike@mike-VirtualBox:~/Desktop$ cat onelinefile.txt This is the one line in this file The cat utility provides a quick, powerful, and versatile tool for working with text files from the command line. You can view log files, for example, and combine multiple logs. To search the log files, you can combine cat with grep (which is discussed shortly). cat is a go-to tool for Linux users. 04-ch04.indd 232 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 233 NOTE cat is a fine tool, but explore another tool for current systems (that’s not on the exam) called less. chmod All files on a Linux system, including all log files and text files, have file permissions, or modes. File permissions are read (r), write (w), and execute (x). Type ls -l to see these permissions: mike@mike-VirtualBox:~/Desktop$ ls -l -rw-rw-r-- 1 mike mike 18626 Jul 11 16:09 -rw-rw-r-- 1 mike mike 18635 Jul 11 16:14 -rw-rw-r-- 1 mike mike 9 Jul 11 15:50 -rwxrwxrwx 1 mike mike 31 Jul 11 16:42 drwxrwxr-x 2 mike mike 4096 Jul 11 16:43 file2.txt file3.txt file.txt program.bin timmy on s mis si s per ne ryo Eve up p erm issi on sio n Gro mis per Ow ner Figure 4-13 Linux permissions s Examining this output from left to right, the first character determines the type of entry: a hyphen denotes a regular file and a d denotes a directory. You can see the file or directory name on the far right of each line. The first four lines show the permissions for regular files, and the last line shows the permissions for the directory named timmy. Permissions are listed in three sets of three permissions each, all in a row. The first set shows the permissions for the owner/creator; the second set defines the group permissions; the third set describes permissions for everyone else, or other (Figure 4-13). If a set includes r, w, and x, it means all three of those permissions are assigned. A hyphen in place of a letter means that specific permission is not assigned. For example, the file2 .txt file in the previous ls -l output has read and write permissions assigned for the owner and group, but only read permission for other. No one has execute permission (probably because it really is just a text file!). The directory timmy, in contrast, shows read, write, and execute permissions for both the owner and the group, plus read and execute (but not write) for other. The chmod command enables you to change permissions—or change modes—for a file or directory. A common way to edit these permissions is to give each set of three permissions a single numeric value between 0 and 7, representing the combined values of read (4), write (2), and execute (1). For example, if owner is assigned 0, owner has no rwxrwxrwx 04-ch04.indd 233 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 234 permissions for the file or directory; if assigned 7, owner has all three permissions. Using three numbers with chmod can set permissions for any file. Here are some examples: • chmod 777 <filename> sets permissions to rwxrwxrwx • chmod 664 <filename> sets permissions to rw-rw-r-• chmod 440 <filename> sets permissions to r--r-----Suppose you have a file called mikeconfig.pcap with the following permissions: -rw-r----- 1 mike mike 18626 Sep 22 8:09 mikeconfig.pcap If you wanted to give read and write permissions to everyone, you’d type this command: chmod 666 mikeconfig.pcap grep Text files sometimes get large, making it challenging to find a specific bit of data in them you need. The grep command looks for search terms (strings) inside text files and returns any line of that text file containing the string you requested. To illustrate, here is a text file called database.txt that contains four lines of personal data: mike@mike-VirtualBox:~$ cat database.txt mike meyers 1313 mockingbird lane Houston TX scott jernigan 555 garden oaks Houston TX dave rush 1234 anytown Spring TX nasa wissa 5343 space center blvd Clear Lake TX Watch the following grep commands and see the result. • Find the word “mike” in database.txt: mike@mike-VirtualBox:~$ grep mike database.txt mike meyers 1313 mockingbird lane Houston TX • Find the phrase “dave rush” in database.txt and identify the line on which it is found: mike@mike-VirtualBox:~$ grep -n "dave rush" database.txt 3:dave rush 1234 anytown Spring TX The grep utility isn’t limited to files. You can take any output to the terminal and then “pipe” the output through grep to filter out anything you don’t want. The handy ps aux command shows all the running processes on a Linux system, but the output can be massive. Let’s say you want to see all the Firefox processes on your system. The command ps aux | grep firefox tells the system to send (to pipe) the output to the grep command, not to the screen. The output runs through the grep command and then goes to the screen. mike@mike-VirtualBox:~$ ps aux | grep firefox mike 2970 16.5 13.4 3234952 273148 ? 04-ch04.indd 234 Sl 15:13 0:06 /usr/lib/ 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-1: Operating System Utilities 235 firefox/firefox -new-window mike 3019 23.9 14.7 2719736 299288 ? Sl 15:13 0:08 /usr/ lib/firefox/firefox -contentproc -childID 1 -isForBrowser -prefsLen 1 -prefMapSize 219196 -parentBuildID 20200630195452 -appdir /usr/lib/firefox/ browser 2970 true tab The grep utility is a wonderful tool to filter output to and from files or the screen. This quick introduction is just that—an introduction and enough to get you through the exam—but anyone who works with Linux should on their own dig deeper into grep. head/tail Sometimes you want to see only the beginning of a text file to get a clue about what data is stored in that file. Alternatively, there are times where you just want to see the end of a text file, maybe to see if records were added. That’s where head and tail are used. head displays the first ten lines of a text file. tail shows the last ten lines. logger The logger command enables you to add text to log files manually. You would do this when you want to add comments. We’ll get to log files in Module 4-4. Shell and Script Environments Security experts understand operating system shells, the command-line interfaces (such as Command, Bash, Terminal, etc.) that enable you to do a ton of things quickly and with authority. And the CompTIA Security+ objectives aggressively assume that knowledge. EXAM TIP CompTIA inadvertently listed OpenSSL rather than OpenSSH in objective 4.1. Expect to see OpenSSH (discussed later in this section) on the exam. A huge part of working at the command prompt is using scripting languages. Scripting languages enable automation of complex tasks and, with the right shells, take advantage of powerful operating system features (like updating registry settings in Windows) that would otherwise require writing actual compiled code. The funny part is that the CompTIA Security+ objectives only mention one shell—Windows’ PowerShell—and only one scripting language, Python. OK, PowerShell also includes its own scripting language, but CompTIA Security+ seems to skip popular shells such as GNU Bash (a Linux shell) and scripting languages like JavaScript. PowerShell For decades, Microsoft leaned heavily and exclusively on the Command shell. Compared to UNIX/Linux, Command was (and still is) extremely primitive and Microsoft knew this. After a few (better forgotten) attempts, Microsoft introduced PowerShell back in 2006. Since then PowerShell has gone through multiple improvements, making it arguably the best combination of shell and scripting language, certainly for the Windows platform. Figure 4-14 shows the default PowerShell interface. 04-ch04.indd 235 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 236 Figure 4-14 Windows PowerShell interface PowerShell’s built-in scripting language has a unique feature that makes it vastly more powerful than any other language when it comes to working with the Windows operating system, a direct connection to the internals of Windows. Want to see a list of local users on a system? Try this PowerShell cmdlet (pronounced “command let”): Get-LocalUser | Select * Need to see a setting for a key in the Windows registry? That’s easy for PowerShell: Get-ItemProperty -Path HKCU:\Software\ScriptingGuys\Scripts -Name version). version Feel free to integrate PowerShell cmdlets into the powerful scripting language to do, well, anything you can imagine. Create GUIs, access databases . . . PowerShell can do it all. NOTE PowerShell scripts normally end with a .ps1 file extension. Don’t feel like using PowerShell scripting in your PowerShell terminal? No worries. The PowerShell terminal supports other languages such as JavaScript and Python. PowerShell is a fabulous shell as well as scripting language, and if you’re working on or developing on a Windows platform, you need to know how to use it. 04-ch04.indd 236 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-2: Network Scanners 237 Python Most security folks consider Python to be the “go to” scripting language for anything that’s cross platform, because Python works perfectly and equally on Windows, macOS, and UNIX/Linux systems. Python has been around for a very long time, is totally free, is well known and well supported, and has easy-to-find tutorials and support. NOTE PowerShell is also cross platform (but good luck finding anyone who runs PowerShell for a living outside of Windows systems). SSH Sometimes you just can’t physically be in front of a machine to open a terminal and do whatever you need to do. That’s where the Secure Shell (SSH) protocol comes into play. Applications using the SSH protocol can manifest a terminal to a remote machine, assuming you have a user name and password on that remote machine (and that remote machine is running an SSH-compatible server). SSH runs on TCP port 22, and almost every operating system comes with a built-in SSH client, if not an SSH server as well. SSH servers and clients must first create an encrypted connection. The SSH protocol has several ways to do this, but one of the more common methods is for the SSH server to generate SSH keys: a traditional RSA asymmetric key pair. The server then treats one key as public and the other as private. When an SSH client attempts to access an SSH server for the first time, the server sends the public key (Figure 4-15). Most SSH implementations today rely on the OpenSSH suite of secure networking utilities. First released in 1999 and in continuous development since then, OpenSSH offers best-in-class secure connectivity between systems. NOTE OpenSSH is hosted at https://www.openssh.com/. Check it out— maybe you can use OpenSSH to develop the next great SSH server! Module 4-2: Network Scanners This module covers the following CompTIA Security+ objective: • 4.1 Given a scenario, use the appropriate tool to assess organizational security What is on your network? This is IT security professional must answer. you need to go through the process of software and hardware tools, known complete this process. 04-ch04.indd 237 one of the most important questions a good When you want to see what’s on a network, network reconnaissance and discovery. Several collectively as network scanners, help you to 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 238 Figure 4-15 SSH client receiving a server key Network scanners use protocols on a network, almost always a LAN, to determine as much information about the LAN as possible. In essence, a scanner is an inventory tool. There’s no single standard or type of network scanner. Different network scanners use a variety of protocols, standards, and methods to query the hosts on the LAN. Given that virtually every network in existence uses the TCP/IP protocol stack, it might be more accurate to use the term IP scanner when describing these tools. EXAM TIP IP scanners are any class of network scanner that concentrates on IP addresses for network discovery. 04-ch04.indd 238 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-2: Network Scanners 239 Scanning Methods Every scanner scans differently, but they try to find certain common data. Here’s a short list of some of the more important items every network scanner will inventory: • • • • • • Topology MAC addresses IP addresses Open ports Protocol information on open ports Operating systems A good network scanner compiles this information and presents it in a way that enables security people to understand what’s going on in the network. A network scanner enables network mapping on many levels. The one area that IP scanners do not usually cover are protocols underneath TCP/IP. For example, a TCP/IP scanner isn’t commonly going to verify the Ethernet speed/type. Some network scanners do inventory lower protocol information, but they tend to be more specialized. With that in mind, let’s dive into network IP scanners. In general, we turn to this information for two reasons: baselining and monitoring. Scanning Targets Think of a baseline as a verification of the network assets. Security professionals run baselines to make sure of exactly what is on the network. This a great time to build an “official” inventory that defines and details every computer, server, printer, router, switch, and WAP in the network infrastructure. Once you know what’s on a network, you can then occasionally reapply a network scan to verify that there are no surprises on the network. Compare recent scans to the baseline and look for differences. Any sort of baseline deviation—things that have changed—can help secure the network. In such a scenario, monitoring enables rogue system detection, such as finding rogue WAPs, unauthorized servers, and other such security breaches. Network scanners are everywhere. If you go into Network and Sharing Center in Windows (assuming your firewall settings aren’t too restrictive), you’ll see a perfectly functional, although very simple, network scanner (Figure 4-16). Scanner Types Network scanners tend to fit into one of two categories: simple or powerful. Simple scanners make quick, basic scans. They require little or no actual skill and only provide essential information. Powerful network scanners use many protocols to drill deeply into a network and return an outrageous amount of information. 04-ch04.indd 239 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 240 Figure 4-16 Windows network information NOTE You won’t see anything on the CompTIA Security+ exam that divides network scanner types into simple versus powerful. We make that distinction purely for ease of teaching the subject. Simple Network Scanners Simple scanners are easy to use and invariably have pretty graphical user interfaces (GUIs) to improve usability. The free and surprisingly powerful Angry IP Scanner from Anton Keks (https://angryip.org) does a good job using simple protocols, mainly ping, to query a single IPv4 address or an address range. If you just want to count the systems in a simple LAN and you have confidence that your internal network isn’t blocking ICMP messages, Angry IP Scanner is a great tool (Figure 4-17). Angry IP Scanner is good for a single network ID and it does some basic port scanning, but that’s about it. NOTE Angry IP Scanner and, in fact, most scanning tools will set off your anti-malware tools. In most cases you’ll need to shut off the anti-malware; or better yet, go through whatever process is needed to make these scanners exempt from the anti-malware software. Simple scanners aren’t limited to Windows. macOS users have similar tools. One of the more common and popular is IP Scanner by 10base-t Interactive (https://10base-t .com). Like Angry IP Scanner, this tool uses only the simplest protocols to query a local network. Compare Figure 4-18 to Figure 4-17 and see how they share a somewhat similar interface. 04-ch04.indd 240 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-2: Network Scanners 241 Figure 4-17 Angry IP Scanner Figure 4-18 IP Scanner 04-ch04.indd 241 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 242 Figure 4-19 Fing scanner on Android There are also several excellent simple network scanners for smart devices running Android and iOS operating systems. Given that these devices all have dedicated 802.11 connections, almost all of these simple IP network scanners tend to give excellent wireless information. One of our favorite scanners is Fing (https://www.fing.com). Note the screenshot of Fing in Figure 4-19. Nmap: A Powerful Network Scanner Simple scanners are wonderful tools if you’re looking for quick scans that grab IP addresses, open ports, and maybe a Windows network name, but little else. But what if you’re looking for more? What if you have multiple address ranges? What if you have a routed network and you want to install multiple sensors that all report back to a single system? In that case you’ll need to turn to a powerful network scanner. Among the many contenders in the network scanner market, the one that every security professional should know, and the one explicitly listed in the CompTIA 04-ch04.indd 242 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-2: Network Scanners 243 Figure 4-20 Nmap used in The Matrix Security+ exam objectives, is Nmap (from https://nmap.org). Originally written back in the mid-1990s by Gordon Lyon, Nmap established itself as the gold standard for TCP/IP network scanners early on and has retained its prominence through ongoing updates from the Nmap community. Nmap is so popular that it shows up in popular media, such as the movies The Matrix (Figure 4-20) and Judge Dredd. NOTE Nmap runs on most operating systems, but it runs best on Linux/ UNIX systems. Having said all these nice things about Nmap, be warned: Nmap is a command-line tool with a powerful and incredibly complex number of switches and options. Nmap is complicated to master; there are many thick books and long online Web page Nmap tutorials that do a great job showing you the power of Nmap. (Also, GUI overlays that run on top of Nmap are available, such as Zenmap, discussed shortly.) It is impossible to give you any more than the lightest of touches on Nmap in this module. Fortunately, the CompTIA Security+ exam will not test you intensely on this tool, but it will expect you to have a good understanding of its capabilities and some of the basic syntax, and that we can do here. Do yourself a favor, download Nmap and try it. Nmap Basics In its simplest form, Nmap is run from a command line. I can run a very simple Nmap command, as shown in Figure 4-21, against my home router. Nmap scans the 1000 most common port numbers by default. In this case it located four open ports: 53 (my router is a DNS forwarder), 80 (the router’s Web interface), and 515 and 9100 (I have a printer plugged into the network). Nmap can just as easily scan an entire network ID. For example, this Nmap command will run the same command except generate a very long output to the terminal: nmap 192.168.1.* 04-ch04.indd 243 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 244 Figure 4-21 Basic Nmap command By adding a few extra switches, –A to tell Nmap to query for OS version and –v to increase the “verbosity” (in essence telling Nmap to grab more information), you can get a lot more information. Nmap also works perfectly fine for any public-facing server. Figure 4-22 shows part of the Nmap scan against Nmap.org’s purpose-built public server scanme.nmap.org. Figure 4-22 Part of a more aggressive Nmap scan 04-ch04.indd 244 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-2: Network Scanners 245 Note that not only does Nmap detect open ports, it pulls detailed information about each port, including the RSA key for the SSH server, the HTTP server version, and the title to the index page as well as NetBIOS ports. CAUTION Before you grab a copy of Nmap and start blasting away at random public-facing servers, a word of caution. Don’t! Multiple laws protect businesses and individuals from unauthorized scanning. You could end up in a world of legal hurt if you don’t have permissions to scan. Getting those permissions as an authorized (white hat) hacker or penetration tester— someone who tests networks to help identify potential security holes—is a great idea. Be careful out there! Zenmap Nmap outputs can be massive, so in many cases security professionals don’t use this interactive mode of terminal screen output; instead, they direct output to XML files other tools can analyze, including graphical tools. Nmap provides a wonderful GUI called Zenmap that enables you to enter Nmap commands and then provides some handy analysis tools. Figure 4-23 shows the topology screen from Zenmap, showing a complete network. Figure 4-23 Zenmap 04-ch04.indd 245 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 246 As previously mentioned, this is just the lightest of tastes of the powerful Nmap scanner. Nmap is a critical part of many Linux security packages, including the powerful Metasploit framework. Module 4-3: Protocol Analyzers This module covers the following CompTIA Security+ objectives: • 4.1 Given a scenario, use the appropriate tool to assess organizational security • 4.3 Given an incident, utilize appropriate data sources to support an investigation Protocol analyzers collect and inventory the network traffic on a network. The CompTIA Security+ exam uses the term protocol analyzer, but that’s a fairly broad term. The IT industry defines protocol analyzers as any type of hardware or software that analyzes any form of communication. In IP networks, all data transmits via Ethernet frames or IP packets contained in those frames, so the better term is packet analyzer (Figure 4-24). Yet another term you’ll hear many folks in the IT industry use is packet sniffer (or just sniffer). If something is going to analyze packets, it is first going to need, well, packets! It needs some program that can put a NIC into promiscuous mode so that the NIC grabs every packet it sees. This frame/packet grabber program needs to monitor or sniff the wired or wireless network and start grabbing the frames/packets. So, a packet analyzer is really two totally separate functions: a packet sniffer that captures the frames/packets, and the packet analyzer that replays the collected packets and analyzes them (Figure 4-25). This combination of sniffer and analyzer leads to a funny name issue. Any of the following terms are perfectly interchangeable: packet analyzer, network sniffer, network analyzer, and packet sniffer. NOTE Different network technologies need different sniffers. If you want to analyze a wired network, you need a wired sniffer. If you want to sniff a wireless network, you need a wireless sniffer. Figure 4-24 I’m a protocol analyzer. 04-ch04.indd 246 I’m checking these packets. 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-3: Protocol Analyzers 247 Figure 4-25 Sniffers and analyzers Thank you! Here are your packets! Analyzer Sniffer Networks generate a huge number of packets. Even in a small home network, moving a few files and watching a few videos generates hundreds of thousands of packets. A good analyzer needs two features. First, it must provide some type of interface that allows the security professional a way to inspect packets. Second, it must provide powerful sorting and filtering tools to let you look at the packets that interest you while eliminating the ones you do not want to see. Why Protocol Analyze? Collecting and analyzing data via a protocol analyzer enables you to perform wildly detailed analyses. A protocol analyzer enables security professionals to access and use data sources to support an investigation in case of an incident. The protocol analyzer output— the data source—can provide critical information. A protocol analyzer can reveal all sorts of information, providing huge benefits to the security of your network. Here are six examples: • Count all the packets coming through over a certain time period to get a strong idea as to your network utilization. • Inspect the packets for single protocols to verify they are working properly (of course, this means you must know how these protocols work in detail). • Monitor communication between a client and a server to look for problems in the communication. • Look for servers that aren’t authorized on the network. • Find systems broadcasting bad data. • Find problems in authentication by watching each step of the process in detail. NOTE Protocol analyzers require skilled operators with a firm grasp of TCP/IP protocols. The more a tech understands protocols, the more useful a protocol analyzer will be. 04-ch04.indd 247 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 248 You can find quite a few protocol analyzers today, but the CompTIA Security+ exam focuses on two very good protocol analyzers: Wireshark and tcpdump. Both tools enable packet capture and replay. You can get some great work done without detailed knowledge of either tool, but in the hands of a skilled professional who understands both the tool and TCP/IP, a protocol analyzer can answer almost any question that arises in any network. The CompTIA Security+ exam isn’t going to ask detailed questions about protocol analyzers, so we’ll only cover a few of the more basic aspects of these tools. But like Nmap from the previous module, it would behoove you to make an investment in learning and using one or the other of these amazing tools. Wireshark Wireshark is the Grand Old Man of packet analyzers, originally developed in 1998 by Gerald Combs as Ethereal. In 2006, Ethereal was forked from the original development team and renamed Wireshark. Wireshark may be old, but it has an amazing development team that keeps this venerable tool sharp with a huge number of updates. Wireshark is not only powerful but completely free and works on all major operating systems (and quite a few not so common ones as well). Its default GUI is so common that even a few competing protocol analyzers copy it for theirs. NOTE Some anti-malware programs will flag Wireshark. It’s stupid, but they do. You might need to disable anti-malware to get results. Let’s start with that interface, as shown in Figure 4-26. The interface has three main panes. At the top is a list of all the frames currently captured. (Wireshark shows each Figure 4-26 Wireshark main screen 04-ch04.indd 248 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-3: Protocol Analyzers 249 Figure 4-27 Selecting a network interface Ethernet frame, a feature that few other protocol analyzers provide.) In the middle are the gritty details of the frame currently selected in the top frame. At the bottom is the raw frame data in hexadecimal. Wireshark employs an application programming interface (API) to enable a NIC to ingest all traffic passing by, rather than the default of only traffic intended for the box. Wireshark uses the libpcap API in Linux or the WinPcap API on Windows systems. You begin the process of using Wireshark by starting a capture. As shown in Figure 4-27, Wireshark locates your network interfaces and gives you the opportunity to select which interface you want to start capturing. Once you start a capture, at some point you then stop the capture. From there you can filter and sort the capture by source or destination IP address, source or destination port number, protocol, or hundreds of other criteria. Wireshark has an expression builder to help you with complex filters. In Figure 4-28 the expression builder is creating a filter for a DHCP server response that is passing out the IP address 192.168.1.23. NOTE You can use a filter on the incoming packets or you can just sniff everything and filter afterward. 04-ch04.indd 249 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 250 Figure 4-28 Expression builder Wireshark by default captures and analyzes packets in real time, so you can analyze as things happen. Sometimes, on the other hand, you need to record data over a period of time and then run tools for analysis for baselining or historical reference. Imagine a situation in which a tech wants to capture all HTTP traffic between 12 a.m. and 4 a.m. on a specific server. In this case, instead of running Wireshark all night, he or she will turn to a capture-only tool such as TShark. TShark is a command-line tool that works well with scripting and scheduling tools (Figure 4-29). TShark saves the capture in a format called pcap that a tech can load into Wireshark the next day for analysis. Figure 4-29 TShark in action 04-ch04.indd 250 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-3: Protocol Analyzers 251 Figure 4-30 tcpdump tcpdump As popular as Wireshark is, especially in Windows, many Linux/UNIX techs swear by tcpdump. tcpdump predates Wireshark by almost a decade and was the only real protocol analyzer option for Linux/UNIX until Wireshark was ported over in the very late 1990s (Figure 4-30). tcpdump is amazing at sniffing packets, but it can be time consuming to use as a protocol analyzer, relying on complex command-line switches for sorting and filtering. No worries! Plenty of graphical protocol analyzers, even Wireshark, run on Linux (Figure 4-31). Figure 4-31 Wireshark in Linux 04-ch04.indd 251 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 252 Module 4-4: Monitoring Networks This module covers the following CompTIA Security+ objectives: • 1.7 Summarize the techniques used in security assessments • 4.3 Given an incident, utilize appropriate data sources to support an investigation Every organization with proper security includes continuous network monitoring to recognize and address performance and security events. This monitoring manifests as the collection of data from a wide variety of sources, one being the standard device and system logs inherent to every operating system. The metadata from applications, such as Microsoft Office 365, provides a great source, because it includes e-mail logs, mobile device records, Web traffic, and file manipulation details. Another source is logs from devices running protocols designed specifically for network monitoring, such as the Simple Network Management Protocol (SNMP). SNMP data collected for network monitoring includes intrusion detection/prevention system alerts, firewall alerts and logs, and real-time network monitoring. Real-time network monitoring involves protocol and traffic monitoring (also known as sniffing) using a protocol analyzer, so that the data may be collected and stored for later analysis. SNMP provides bandwidth monitoring in real time, enabling security professionals to assess data in the face of an incident. Similarly, the Cisco-based NetFlow and the more generic sFlow offer analytical tools for security people by assessing the flow of IP traffic. Such tools are invaluable when an incident occurs. More complex systems rely on advanced monitoring tools such as a security information and event management (SIEM) application that monitors log files—brought into the monitoring tools using protocols like SNMP—to provide managers powerful, easy to read and understand toolsets. These toolsets enable them to react to situations on their network in real time (Figure 4-32). Figure 4-32 A security event 04-ch04.indd 252 tW Ϯ KŚ͕ŶŽ͘dŚĂƚĐĂŶ͛ƚďĞŐŽŽĚ͊ 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-4: Monitoring Networks 253 To understand the critical process of network monitoring, let’s begin by exploring the many types of log files found on devices in a network. From there, we’ll see how these files can be centralized for easier monitoring and then finish with a discussion on log file management and analysis. Exploring Log Files Logs are databases, usually distinct files that record events on systems. You’ll most commonly hear them referenced as event logs, as in the case of Microsoft Windows operating systems. Linux systems refer to them as syslogs, or system logs. Whatever the name, log files are everywhere! You’d be hard-pressed to find a networking device or almost any form of software that doesn’t make log files, or at least has the capability to create log files as needed. Operating systems also store log files in various locations and in various formats. Security personnel often refer to these logs as security or audit trail, or sometimes as audit log, because they provide information on events that are of a security interest. Security logs audit access to a particular resource or system. Audit logs can record very specific information about an event, to include user names, workstation or host names, IP addresses, MAC addresses, the resource that was accessed, and the type of action that occurred on the resource. This action could be something such as a file deletion or creation; it also could be use of elevated or administrative privileges. Very often, security personnel may audit when users with administrative privileges create additional user accounts, for example, or change host configurations. Figure 4-33 shows an example of a Linux audit trail. Visitor logs are resource-oriented and list all the different types of access that occur on a resource (such as a shared folder, file, or other object). Most systems can produce visitor logs for a specific resource, but often this must be configured on the resource itself to generate those logs. You can use visitor logs that are not system-generated. For example, you can have manually generated visitor logs for entrance into a facility or restricted area. Security experts work hard to keep up with all the different log files available and use them in the most efficient and reasonable way possible. Log File Examples Students of CompTIA Security+ reasonably ask what they need to know about log files to pass the exam. It’s a fair question, but rarely do people like my answer: “You need to know very little about log files other than what’s inside the log files themselves.” What I’m trying to say is that if you think about what a log records, then you should have a good feel about the types of data stored in that log file. Luckily for students of the SY0-601 exam, CompTIA has specific types of log files for consideration, all listed prettily under objective 4.3! Let’s run down that list. Network It you have a device or a piece of software that deals with networking, then you almost certainly have some kind of network log. A network log varies by the type of device using the network. A router might have a network log that tracks the number of connections per hour on every route. A switch might record packets per seconds for VLANs. On an individual host, you might log the usage of a particular NIC. 04-ch04.indd 253 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 254 Figure 4-33 An example of a Linux audit trail log file System A system log file records issues that directly affect a single system but aren’t network functions. System log files will show reboots, executable files starting, and edited files on the system, for example. Application An application may have its own log file. What appears in this application log file requires some knowledge of the application that is using the log. Probably one of the most common application logs is for a Web server. Web server software is an application to share Web pages. In this case, since we know what Web servers do, we can assume the Web log keeps track of the number of pages served per hour/minute, perhaps even a listing of the different IP addresses asking for the Web page, or maybe the number of malformed HTTPS packets. Security Both systems and applications typically include security logs that record activities that potentially impact security. Security logs might track all successful and/or unsuccessful logon attempts. They track the creation or deletion of new users and also keep track of any permission changes to resources within the system or application. 04-ch04.indd 254 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-4: Monitoring Networks 255 DNS Any good DNS server is going to keep a log. DNS logs are application logs that keep track of things appropriate to a DNS server application. DNS logs typically include entries for activities such as the creation of new forward lookup zones, cache updates/ clearing, and changes to critical settings like root server. Authentication An authentication log is a special type of security log that tracks nothing other than users attempting to log onto a system. This includes tracking failed logons as well as successful logons. Dump Files On some operating systems, a dump file is generated when an executable program crashes. These dump files record memory locations, running processes, and threads. Dump files are almost always used exclusively by the developers of the executable file that needs . . . dumping. VoIP and Call Managers Voice over IP (VoIP) and call manager software solutions create logs that store information about the calls themselves. Phone numbers and duration of calls are the two most common items logged, but items from other VoIP tools such as billing might also be included. Session Initiation Protocol Traffic Session Initial Protocol (SIP) traffic is usually a subset of VoIP traffic but exclusive to the SIP protocol. In this case, a SIP traffic log tracks where the IP address to/from is logged as well as any details about the call itself. Windows Log Tools Every Windows systems contains the venerable Event Viewer as the go-to log observation tool. Event Viewer contains a number of preset logs (notice the System logs folder in Figure 4-34). You can create new logs here or in the local security policy application. Figure 4-34 Event Viewer 04-ch04.indd 255 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 256 Figure 4-35 Linux journalctl log viewer Linux Logs Linux loves to make log files, dedicating an entire folder to nothing but all the logs you’ll ever need. In most distros, this folder is called /var/log. Log files end with a .log extension and, unlike in Windows, there is no single log viewing app. You can add various GUI log readers, such as LOGalyze or glogg. The go-to log viewer on most Linux systems, journalctl, displays all logs in a system in a single format. journalctl also takes all the common Linux terminal arguments. Figure 4-35 shows journalctl using grep commands to filter on the term “warn.” Linux logs are almost as simple as Windows logs in that there’s basically a single source for all your log needs: syslog. OK, that’s not exactly true, as syslog is over 30 years old and has been supplanted by two improved syslog versions: rsyslog, which came out in the late 1990s and is basically just an improved syslog, and syslog-ng, which is an object-oriented version of syslog. Right now syslog is probably the most popular version of these three syslog-like tools, but deciding which tool is best is really up to the individual user, as syslog, rsyslog, and syslog-ng all have their fans and detractors. In most cases, you’ll end up using the form of syslog that works best for whatever system you want to use. (See the upcoming “Centralizing Log Files” section.) The one good thing about all versions of syslog is their superb standardized format for all log entries. This format is considered the standard for all log files. Even Windows log files can manifest in this format. NOTE If you need to add a notation to syslog, use the logger command, discussed back in Module 4-1. It creates a single entry, properly timestamped, that users can access later. It’s an excellent way to make inline documentation for any log file. Device Logs Every enterprise-level (and many SOHO-level) devices come with some form of logging built into them. In most cases, you just need to log onto that device (often a Web interface) to see the logs on that device in action. Figure 4-36 shows one example of these logs on a home router. The challenge to using these log files is that you have to access the device every time you want to see what’s happening on that system. A better solution is where multiple devices send log files to a central source that can, in turn, analyze that information. 04-ch04.indd 256 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-4: Monitoring Networks 257 Figure 4-36 Home router log file Then that centralized analysis can display what’s happening on the network in a way that administrators can react to the needs of the network. To do that requires centralization of far-flung log files into a single source. Centralizing Log Files The idea of gathering log files from disparate hosts within a network and placing them in a central location for storage and analysis isn’t a new idea. Many tools and protocols help you accomplish exactly this task. Let’s start by organizing some of the major players out there for centralization and eventually lead to the Holy Grail of network monitoring, SIEM. syslog syslog and its alternative forms are more than just log tools. syslog is a complete protocol for the transmission and storage of Linux logs into a single syslog server, configured by the network administrators. Once all the files are stored in a single location, we can use tools such as journalctl to monitor the entire network. NOTE Can you imagine using syslog to combine log files from all over a network? Imagine the complexity of just trying to read, analyze, and store these files. This is a big shortcoming of syslog and the reason we use other tools on top of syslog to do the big-picture jobs of network monitoring. Keep reading! 04-ch04.indd 257 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 258 SNMP The Simple Network Management Protocol (SNMP) enables proactive monitoring of network hosts in real time. Among other things, SNMP is a bandwidth monitor, providing up-to-the-second information for network administrators. This real-time information can provide critical data sources to support investigations in the face of an incident. Devices that use SNMP have a small piece of software known as an agent installed on them, and this agent can report certain types of data back to a centralized monitoring server. This agent is configured with a Management Information Base (MIB), which is a very specific set of configuration items tailored for the device. Using the MIB, the agent can relay very specific event information to a centralized console in real time. These events are known as traps and are essentially specific events configured with certain thresholds. If a configured threshold is reached for a particular event, the trap is triggered and the notification or alert is sent to the management console. These traps and messages can let an administrator know about the device status and health. In other words, the administrator could get information on when the device is up or down, whether its hardware is functioning properly or not, if its memory or CPU use is too high, and other interesting details about the device. In some cases, these trap messages could indicate an active attack against the device or some other type of unauthorized access or misuse. NOTE Chapter 8 covers SNMP security in more detail. NetFlow/sFlow The Cisco-based NetFlow utility provides real-time information about all the IP traffic in a system. sFlow provides similar information, but, unlike NetFlow, runs in hardware. NetFlow is a software implementation. Numerous switch and router manufacturers deploy sFlow chips/technology, so it is not limited to Cisco hardware. In concept, a flow represents the movement of an IP packet through a network. By monitoring such information, NetFlow/sFlow can pick up very quickly when patterns diverge from what would be considered normal traffic. Flow information is stored in logs or flow caches that the tools can analyze. Spawned from NetFlow version 9, Internet Protocol Flow Information Export (IPFIX) provides more flexibility in the types of information that can be combined and saved for analysis, such as mail records, HTTP URL information, SIP data, and more. IPFIX is an Internet Engineering Task Force (IETF) specification (RFC 7011), is backwardly compatible to NetFlow v9, and is widely adopted in the industry. EXAM TIP CompTIA uses title case for NetFlow, so Netflow. Cisco uses camel case, so that’s what we use too. 04-ch04.indd 258 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-4: Monitoring Networks 259 NXLog NXLog is one example of many solutions out there that provide centralized log monitoring. NXLog is cross platform and takes advantage of darn near every and any protocol out there (including syslog and SNMP) to bring log data together. On Linux systems, NXLog reads from both a local system’s syslog and NXLog’s installed daemon. On Windows, NXLog runs its own agent and also uses SNMP. NXLog is a powerful logging tool, but it is not designed to provide pretty desktops or to analyze the log data. NXLog is ready and able to give this log data to those types of systems, but that means we need to start talking about SIEM. Security Information and Event Management The traditional way to manage logging and monitoring in a network was to sit down at a system and look at the log files generated by the system, reviewing them for the events of interest. This is not the most efficient way to manage network monitoring and analysis activities. Almost every organization now uses security information and event management (SIEM), an enterprise-level technology and infrastructure that collects data points from every host on the network, including log files, traffic captures, SNMP messages, and so on. SIEM can collect all this data into one centralized location and correlate it for analysis to look for security and performance issues, as well as negative trends, all in real time. NOTE SIEM is pronounced “sim” most frequently, not “seem” or “see-em.” For clarity, network professionals can simply enunciate the initials. Note that although SIEM requires real-time monitoring technologies, just because you’re using some of these real-time technologies doesn’t necessarily mean you are using SIEM. SIEM unifies and correlates all the real-time events from a multitude of disparate sources, including network alerts, log files, physical security logs, and so on. You could still have real-time monitoring going on, but without combining and correlating all those different event sources. A true unified SIEM system is required to do that. SIEM Infrastructure SIEM isn’t a law or a standard. It’s an integrated approach to monitoring networks that enables security professionals to react on a timely basis to incidents. SIEM systems employ certain components, discrete or combined with others, but you can count on the following: • • • • 04-ch04.indd 259 Sensors/collectors Server Analyzers Dashboard 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 260 Sensors/Collectors All SIEM solutions rely on sensors/collectors to acquire data about the network. These collectors manifest as special software running on a Windows system, an SNMP connection to a switch, or perhaps a third-party tool like NXLog providing information from a gateway router. Whatever the case, these devices must work together to bring the data into a single source, a SIEM server. Server A SIEM server stores all the data coming in from multiple collectors. A single SIEM server might be a subserver that in turn reports to a main SIEM server. Analyzers Analyzers take data from SIEM servers and, using a myriad of tools, look at the data to try to locate signatures of something that an organization would consider an incident. Dashboard A SIEM dashboard presents the analyzed data in a way that makes sense to those monitoring the data and informs them of incidents taking place. Most SIEM dashboards provide graphs and counters. Figure 4-37 shows one style of dashboard from Elastic Cloud, a popular SIEM solution available today. A good SIEM dashboard provides security monitoring—tools for watching and recording what’s happening on your network. Beyond that, though, you can count on a SIEM dashboard to supply the following information: • Sensor list/sensor warning If an incident is taking place at a certain point, which sensor is giving that information? The sensor list or sensor warning provides that information. • Alerts Alerts enable the SIEM dashboard to inform the person(s) monitoring of a potential incident. This can be a warning ribbon at the bottom of the screen, an audible alarm, or a log entry shown in red. • Sensitivity How sensitive is a certain setting that might detect an incident? Too high and you’ll get false positives. Too low and you’ll get false negatives. • Trends Certain incidents make more sense when seen as a trend as opposed to an alert. Network usage is one good example. Techs can watch usage grow on a chat and consider those implications, as opposed to just getting some alert. Anyone who owns an automobile with an oil pressure gauge instead of an idiot light knows this feeling. • Correlation A good dashboard will recognize relationships between alerts and trends and in some way inform the person(s) monitoring of that correlation. This is often presented as line graphs with multiple data fields. SIEM Process The SIEM process closely maps to the infrastructure. Let’s discuss some of the more important parts of this process as data goes through a typical SIEM infrastructure. Data Inputs SIEM solutions grab data from many different sources. Most SIEM solutions use log collectors—tools for recording network events—and SNMP inputs, of course, but many go far beyond those sources. For example, it’s not uncommon for a 04-ch04.indd 260 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Module 4-4: Monitoring Networks 261 Figure 4-37 Elastic Cloud dashboard SIEM solution to employ agents that perform packet capture for situations where that might be needed. Log Aggregation SIEM servers can’t just have data dumped on them. First, data needs to be normalized, to regularize the same type of data among multiple logs. One great example of this is log aggregation. What if one log stores all source IP address information as “SRC_IP” while another log stores the same data as “Source”? Proper log aggregation will make the data output under a single label. Another example is too much data. Does the server need to store every IP packet going through a switch if all it really needs to know is the number of packets per second? 04-ch04.indd 261 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 262 Analysis SIEM analysis is a massive topic, but CompTIA only wants you to consider two types of analyses, user behavior analysis and sentiment analysis. User behavior analysis, as the name implies, considers how users behave on a network. Does Maria always log onto the same machine every day? Does Mario add new users to his department within a day after they are hired? When users move outside their anticipated behaviors, that may be indicative of trouble. Sentiment analysis tries to parse actual language used to determine the meaning behind that use. The system monitors things like publications for negative sentiment to determine intentions of a threat group, for example. Review Reports No SIEM system is perfect. Review reports detail the results of examining the success rate of a SIEM system over a certain timeframe. These review reports tell the administrators of the SIEM system where they need to improve. Log File Management Log management refers to the logistics of managing all the device logs in a network. In addition to reviewing log files on a periodic basis, you’ll need to consider a few other aspects of log management. First, you should decide how long to keep log files, since they take up a lot of space and may not exactly contain a lot of relevant information—unless you need to look at a specific event. Sometimes governance, including regulations and other legal requirements, may require you to keep system log files for a certain amount of time, so log management is also concerned with retention of archived log files for a defined period. Secure storage, retention, and retrieval of archived logs are required simply because log files can contain sensitive information about systems and networks, as well as other types of sensitive data. You must ensure that only personnel authorized to view log files have access to them and protect those log files from unauthorized access or modification. You must also be able to retrieve the log files from storage in the event of an investigation or legal action against your organization, as well as comply with audit requirements imposed by law. Log management applies to all of these things, and effective policy regarding managing the logs in the organization should address all these issues. Security professionals look for particular types of information on a routine basis, and thus should configure logging to provide only that pertinent information. This helps to find the relevant information and eliminate the massive amounts of unnecessary information. For event-specific information, such as a major performance issue, an outage, or even a significant security event, a lot more information may be needed during those specific circumstances only. In such a case, security professionals may temporarily configure logging to provide far more detailed information. Getting that level of detail on a routine basis, however, would likely make logs unmanageable and limit their usefulness. For example, let’s say that you are monitoring a potential hacking attempt. You may change the audit level of your network devices or internal hosts to include more detailed information on processes, threads, and interactions with lower-level hardware. This level of detail can produce a vast amount of logs very quickly, which can fill up device storage and be very unwieldy to examine. Because of this, you’d want to enable this level of logging only for a short while, just long enough to get the information you need. After that, you’d want to reduce the logging level back to normal. 04-ch04.indd 262 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Questions 263 Questions 1. What does nslookup do? A. Retrieves the name space for the network B. Queries DNS for the IP address of the supplied host name C. Performs an ARP lookup D. Lists the current running network services on localhost 2. What is Wireshark? A. Protocol analyzer B. Packet sniffer C. Packet analyzer D. All of the above 3. One of your users calls you with a complaint that he can’t reach the site www .google.com. You try and access the site and discover you can’t connect either but you can ping the site with its IP address. What is the most probable culprit? A. The workgroup switch is down. B. Google is down. C. The gateway is down. D. The DNS server is down. 4. What command do you use to see the DNS cache on a Windows system? A. ping /showdns B. ipconfig /showdns C. ipconfig /displaydns D. ping /displaydns 5. Which of the following tools enables you to log into and control a remote system securely? A. ipconfig B. remoteconfig C. rlogin D. SSH 6. Which protocol do tools use to enable proactive monitoring of network hosts in real time? A. ipconfig B. nslookup C. SNMP D. SSH 04-ch04.indd 263 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Chapter 4: Tools of the Trade 264 7. The Windows tracert tool fails sometimes because many routers block __________ packets. A. ping B. TCP C. UDP D. ICMP 8. Which tools can you (and hackers) use to query LISTENING ports on your network? (Choose three.) A. Port scanner B. Nmap C. Angry IP Scanner D. Hostname command 9. Which tool enables you to view the contents of a text file in Linux? A. cat B. dig C. notepad D. nslookup 10. Which of the following commands would change the permissions of the file timmy.exe to read-only for all users but execute for the owner? A. chmod 440 timmy.exe B. chmod 664 timmy.exe C. chmod 744 timmy.exe D. chmod 777 timmy.exe Answers 1. B. The nslookup command queries DNS and returns the IP address of the supplied host name. 2. D. Wireshark can sniff and analyze all the network traffic that enters the computer’s NIC. 3. D. In this case, the DNS system is probably at fault. By pinging the site with its IP address, you have established that the site is up and your LAN and gateway are functioning properly. 4. C. To see the DNS cache on a Windows system, run the ipconfig /displaydns command at a command prompt. 04-ch04.indd 264 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 4 Answers 265 5. D. Use Secure Shell (SSH) to log in and control a remote system securely. rlogin is an alternative to SSH, by the way, but lacks encryption. 6. C. The protocol for tools to do real-time network monitoring is SNMP. 7. D. The Windows tracert tool fails because it relies on ICMP packets that routers commonly block. 8. A, B, C. The hostname command simply returns the host name of the local system. All other tools mentioned can scan ports to locate network vulnerabilities. 9. A. The cat command enables you to view and combine text files in Linux. 10. C. Using the command chmod 744 timmy.exe sets the permission as rwxr--r-for the file. The owner has read, write, and execute permissions. The group and others have only read permissions. 04-ch04.indd 265 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Blind Folio 266 This page intentionally left blank 04-ch04.indd 266 25/03/21 2:14 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 CHAPTER Securing Individual Systems 5 Adapt what is useful, reject what is useless, and add what is specifically your own. —Bruce Lee A typical security professional bandies about the term attack surface, meaning a cumulation of all the vulnerabilities for a specific infrastructure item. For a gateway router, for example, the attack surface refers to every option that an attacker might use to compromise that router, from misconfiguration to physical damage or theft (Figure 5-1). This chapter explores the attack surface of one of the most vulnerable parts of networks, the individual systems. An individual system for the purposes of this chapter is a single computer running Windows, macOS, Linux/UNIX, or Chrome OS, in use every day. This includes desktops, laptops, servers, and workstations. It also includes mobile devices, but only to a lesser degree. We’ll see more of those systems in later chapters. The typical individual system on a network has hardware, software, connections, and applications, all of which are vulnerable to attack. The chapter first examines some of the more common attack methods, building on concepts that you learned in earlier chapters. This follows with an extensive discussion of the effects malware can have. Module 5-3 examines system resiliency options and methods. Subsequent modules explore different angles of individual system attack surfaces, from hardware to operating systems and applications, including host-based firewalls and intrusion detection (Figure 5-2). The chapter finishes with a brief discussion of ending the life of individual systems securely. 267 05-ch05.indd 267 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 268 Figure 5-1 An attack surface We attack here! NOTE One attack surface variety this chapter does not cover is Internet applications—that is, Web apps. While these applications certainly run on individual server systems, local users on a LAN generally do not use those systems. These applications have their own class of problems that warrant their own chapter. We’ll go into Internet application attacks—and how to stop them—in Chapter 11. This chapter explores methods for securing individual systems in six modules: • • • • • • Types of System Attacks Malware Cybersecurity Resilience Securing Hardware Securing Endpoints System Recycling Figure 5-2 We need to protect systems. 05-ch05.indd 268 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-1: Types of System Attacks 269 Module 5-1: Types of System Attacks This module covers the following CompTIA Security+ objectives: • 1.3 Given a scenario, analyze potential indicators associated with application attacks • 1.4 Given a scenario, analyze potential indicators associated with network attacks • 1.6 Explain the security concerns associated with various types of vulnerabilities Any network is nothing more than a series of systems connected via fiber, copper, or wireless connections. But a physical connection isn’t enough. To function on a network, the system must possess the necessary hardware and software to connect to a LAN and communicate via IP, sending and receiving properly formatted TCP/UDP/ICMP segments/datagrams (lumped together here as TCP/IP packets). To perform this, a system consists of four independent features: network-aware applications, a network-aware operating system, a network stack to handle incoming and outgoing packets, and proper drivers for the network interface. Collectively, these features are the attack surface for an individual system. NOTE Physical access to a system provides a rather robust attack surface, although most of these topics fall outside the scope of CompTIA Security+. Module 5-4 explores this further. To understand the types of attacks unleashed on systems, let’s put all these features in order, as shown in Figure 5-3. We can then explore how bad actors can take advantage of vulnerabilities in each of these features to compromise individual systems. Figure 5-3 Individual systems’ attack surfaces Here are attack surfaces Application Operating System Network Stack Drivers 05-ch05.indd 269 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 270 Attacking Applications Applications contain their own unique set of vulnerabilities, but the impact of the vulnerabilities often remains, such as taking control of the application, shutting down the application, and accessing data from the application. This section looks at several attack surfaces for applications: • • • • • • • • • • • Race conditions Improper input handling Error handling Memory/buffer vulnerabilities Pointer/object dereference Resource exhaustion Weak encryption DLL injection API attacks Privilege escalation Services NOTE Just about every application attack type listed starts with or interacts with the operating system on which the application runs. This section could have easily been titled “Exploiting Operating System Vulnerabilities to Attack Applications,” but we went with the shorter title. You’ll see this interaction between OS and apps throughout. Race Conditions Most applications take advantage of multitasking to run multiple processes/functions at the same time. Sometimes the effect of two or more simultaneous transactions can result in undesired results called a race condition. Race conditions manifest as counters, totals, and other usually integer (whole number) values that simply don’t add up correctly, such as when a program runs subroutine A and subroutine NOT A at the same time. Another bug that can happen with a race condition is time-of-check to time-of-use (TOCTOU), where exploits can happen between the program checking the state of something and doing something about the results. Attackers can create or exploit race conditions. The impact of race conditions varies from incorrect values in Web carts to system stops to privilege escalation (see “Privilege Escalation” for more details on the last). EXAM TIP The CompTIA Security+ objectives drop the hyphens and the “to” for TOCTOU, so you’ll see the term on the exam as time of check/time of use. 05-ch05.indd 270 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-1: Types of System Attacks 271 Improper Input Handling Programmers write software to take in and output data and results. That seems fairly obvious from a user standpoint, whether it’s typing in Microsoft Word or changing data in an Access database and seeing changes made appear on the screen. Programs also get input from less visible sources and need to validate that input. A poorly written program—or a great program attacked by a clever attacker—can take in or handle improper information. This improper input handling can lead to unauthorized access to data, unexpected or undesired commands executed on a Web server, and more. NOTE Programmers write apps with certain expectations. Users provide input, processors process, and the app provides output. Input validation routines accept proper input and, in theory, reject improper input. Unexpected input can wreak havoc, though, so app developers will hire folks to throw all sorts of stuff at their app, just to see if it will break. That’s part of the programming process. (You won’t be tested on this, but thought you might like to know.) Error Handling What happens following an exception, an unexpected input or result, depends on how the programmers anticipated error handling by the application. Attackers could exploit a weak configuration or a bug in the code to do some serious damage. As a result of such vulnerabilities, some programs might crash, while others might reboot or restart. A more graceful response would send the application or server into a safe state that stops a bad actor from continuing an attack or malformed packets from causing problems. A Web server could restart in a maintenance mode, for example, so bad guys couldn’t keep manipulating it. The Web server could inform administrators that it has switched to the error/ maintenance mode. These would be good examples of error handling. NOTE Programmers dance delicate steps with error handling and reporting. Saving logs or error reports helps developers find and fix unexpected issues. Too precise an error report, on the other hand, can tell an attacker exactly what happened. That can lead the attacker to a new, more effective path, and that’s not a good thing. Memory/Buffer Vulnerabilities All code uses memory to handle the active operation of that code. RAM may be cheap these days, but applications must be programmed properly to be aware of the amount of memory they’re using. The CompTIA Security+ objectives include three vulnerabilities that are so closely related that it makes sense to treat them as a single issue: • Memory leak • Integer overflow • Buffer overflow 05-ch05.indd 271 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 272 All three of these vulnerabilities describe some part of memory being filled beyond the programmed capacity. A memory leak is a general issue where a single process begins to ask for more and more memory from the system without ever releasing memory. Eventually, the system reaches a memory full state and stops working. Integer overflows are when a value greater than an integer variable causes the application to stop working. The program might have a field that accepts whole numbers from 0–64,535, for example, and receive a number of 128,000. Ouch! A buffer is a temporary storage area in memory to hold data, such as the results of a form input. Buffers are fixed in size. If too much data gets into the buffer, causing unpredictable results, that’s a buffer overflow. The impact of all these situations is similar in that the system will at best kick out an error (that hopefully is well handled) and at worst cause a system lockup. Pointer/Object Dereference A pointer is an object used in most programming languages that “points to” another value in memory. Unlike a variable, a pointer references a memory location. When a pointer accesses the stored value, this is known as pointer/object dereference. If a bad actor can get a pointer to point incorrectly, a dereference can cause havoc to the code. If the bad actor can get a pointer to point to no memory location—a null pointer dereference—this can cause some very negative results. The impact of this vulnerability mirrors the impacts of previously discussed vulnerabilities, such as crashes, freezes, reboots, and worse. Resource Exhaustion Resource exhaustion isn’t a vulnerability itself but rather the result of an attack that takes advantage of one or more of the memory-specific vulnerabilities previously described to bring down the system. Another example is sending malformed packets to a system, such as bad pings, that cause the server to churn so hard that it becomes inoperable. Resource exhaustion is the basis for denial-of-service (DoS) attacks that seek to make resources (servers, services, and so on) unavailable for legitimate users. (We’ll see more on DoS and related attacks in Chapter 8.) Weak Encryption Securing any app is an ongoing battle between the good guys keeping encryption strong versus bad guys working to crack that encryption. One of the most obvious examples of this ongoing battle is in wireless networking. When Wi-Fi first arrived, WEP for security was fine-ish, but it was quickly cracked. Weak configurations and, in this case, weak encryption exposed wireless users to vulnerabilities. The industry came out with WPA, then WPA2, and then WPA3, trying to stay ahead of the bad guys. You’ll remember all this from your CompTIA A+ and Network+ studies. The same vulnerabilities apply to every type of encryption used in modern networks. NOTE Many people will argue that WEP wasn’t/isn’t an encryption standard. As its name implies, Wired Equivalent Privacy was intended to provide security and confidentiality as good as a wired network. We get it. 05-ch05.indd 272 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-1: Types of System Attacks 273 Part of the struggle faced by developers is maintaining backward compatibility with older encryption standards while supporting newer, more secure encryption standards. A typical Web server can support 10–20 different types of encryption to enable different clients to connect and do business securely. A clever bad actor can take advantage of this by requesting the weakest type of encryption from a Web server in the hopes of getting something easily crackable. Organizations need to update and patch operating systems, firmware, and applications regularly just to keep up with the bad guys. You’ll see this evolution and battle as we discuss encryption implementations in subsequent chapters. NOTE The Padding Oracle On Downgraded Legacy Encryption (POODLE) attack from a few years back offers a stark example of clever attacks like the one listed above. Attackers used exploits to make apps drop from TLS to SSL security and then took advantage of known vulnerabilities of SSL to get information. We’ll look at more attacks like this in Chapter 6. DLL Injection A dynamic-link library (DLL) is a file used in Windows systems that provides support code to executable files. Every Windows system has hundreds of DLLs, most commonly stored in the \Windows\System32 folder (Figure 5-4). Most applications provide their own DLLs as well. DLLs help reduce code size and speed up processing. Figure 5-4 Just a few of the DLLs on Mike’s laptop 05-ch05.indd 273 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 274 DLL injection is a technique used by bad actors to get users to run malicious code. The code runs in the address space of another process and loads a malicious DLL. Once the DLL runs, all the usual impacts come into play: system control is one of the most common, used to zombify systems for distributed denial-of-service (DDoS) attacks—where attackers use many systems to hammer a server to try to shut it down. (See Chapter 8 for more details about DDoS and related attacks.) NOTE Injection-style attacks don’t stop with DLLs. You’ll see them again with SQL, XML, and more in Module 11-3. (I see you trembling with anticipation!) API Attacks No program is an island. When you fire up Microsoft Word, for example, you’re actually starting a program called winword.exe. The winword.exe executable acts as an orchestra conductor, automatically opening dozens or hundreds of other executables and DLLs as needed to enable Word to open and close files, to spell check, to access files across a network, and more. Interconnecting applications requires functions and procedures— programming—that can bridge the gap to, in effect, translate from one application to the other. These helper/translator applications are called application programming interfaces (APIs). Like most things in computing, APIs started with little to no security. This has changed over time and version updates. Bad actors look for unpatched or earlier versions of APIs in use to take advantage of discovered weaknesses and perform an API attack. If you have software of any form, that software uses one or more APIs, and at some time or other, bad guys have figured out ways to take advantage of that software. Web browsers, for example, interact with APIs on Web servers. Bad actors exploit weaknesses in these APIs to intercept data, disrupt systems, take down systems, and so forth. Privilege Escalation Privilege escalation, the process of accessing a system at a lower authentication level and upgrading (escalating) authentication to a more privileged level, presents attack opportunities against applications. All of the common operating systems require every user and every process accessing the system to go through some form of authentication/authorization procedure. If an attacker can access a system using a low-level access account such as public, everyone, or guest, he or she may find a bug that gets him or her to the highest access levels (root, administrator, etc.). NOTE A service account, unlike an account used by people (guest, user, root), is used by some process running on the system that needs access to resources. The nature of service accounts prevents typical authentication methods because they lack anyone to type in a password. This makes service accounts a prime target for attacks. Over the years hundreds of well-known exploits have used service account privilege escalation as an attack surface. 05-ch05.indd 274 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-1: Types of System Attacks 275 Operating systems are designed to prevent privilege escalation. Attackers need to find some type of bug, sometimes even through an application running on the operating system, that gives them higher privilege. Alternatively, attackers can find an alternative login that may not have a higher privilege but might give access to something that lets them do what they need to do. If an attacker wants to access a printer, he doesn’t need root access, just some account that has access to that printer. NOTE Well-patched operating systems are extremely resilient to privilege escalation. Services Operating system services provide an attack surface for bad actors to attack applications. For a Windows-centric person, a service is any process that works without any interface to the Windows Desktop. You can access all running Windows services using the aptly named Services app (Figure 5-5). Attacking a Windows service is pretty much the same as attacking an application. Attackers can use man-in-the middle attacks if possible, or they can use privilege escalation if they can find an exploit. Figure 5-5 Services in Windows 05-ch05.indd 275 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 276 Figure 5-6 Internet services NOTE The CompTIA Security+ objectives version 3 changed man-in-themiddle attacks to on-path attacks. We’ll discuss these sorts of attacks in much more detail in Chapters 6 and 11. A more Internet-centric person would define services as processes that listen on a TCP/UDP port to provide some sort of (again aptly named) service. In Windows, you can see TCP/IP services, including the process providing that service, using netstat –a –b (Figure 5-6). Linux users don’t have this confusion. A Linux service is only a process listening on a TCP/UDP port. Linux does not separate processes that interface to the desktop from those that do not. There is no Linux equivalent to Windows’ Services app. Driver Manipulation Every piece of hardware on a computer (with the exception of RAM) communicates with the operating system via device drivers. Attackers either can send communications to device drivers to make them do things they were never supposed to do, or can replace the device drivers with corrupted device drivers to gain privilege escalation or launch spoofing attacks. 05-ch05.indd 276 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-1: Types of System Attacks 277 There are two attack surfaces to manipulate device drivers to do malicious things, driver refactoring and driver shimming. Neither attack surface is unique to device drivers—both are present in any type of code—but they are the two best ways to attack an individual system via its device drivers. Refactoring Programming is all about inputs and outputs. A piece of code takes input and, based on that input, does some type of output. For software developers, refactoring means to rewrite the internals of a piece of code without changing the way it reacts to input or how it performs output. The many device drivers that talk to system hardware are certainly code. Hardware manufacturers always want to make their drivers faster and smaller, so refactoring is a common feature with device drivers. Refactoring can have a slightly different, malevolent definition. Refactoring can mean to reprogram a device driver’s internals so that the device driver responds to all of the normal inputs and generates all the regular outputs, but also generates malicious output. A refactored printer driver that works perfectly but also sends all print jobs to an evil remote server is an example of this other type of refactoring. EXAM TIP Every operating system provides a method of driver signing that is designed to prevent refactoring attacks on device drivers. Shimming Refactoring was a very common attack for many years, but today all operating systems use driver signing that confirms the exact driver files used. The operating system detects any changes and deals with them in one way or another, so replacing a device driver’s files isn’t as easy as it used to be. To get around this issue as an attacker, instead of replacing a signed file (or files), why not just throw another file or two (with the extra evil code) into the system? A shim is a library that responds to inputs that the original device driver isn’t designed to handle. Inserting an unauthorized shim, called shimming or a shim attack, is more common than refactoring because it does not require replacing an actual file—it merely relies on listening for inputs that the original device driver isn’t written to hear. Malicious Code or Script Execution Modern computing systems are filled with tools to enable properly written code or scripts to do all kinds of powerful actions to the operating system or applications. CompTIA’s Security+ objective 1.4 lists the following: two shells, PowerShell and Bash; one compiled general-purpose language, Visual Basic for Applications (VBA); one interpreted generalpurpose scripting language, Python; and the word “macros” (a lovely generic term that the author assumes CompTIA uses to refer to the combination and automation of commands built into an application like Microsoft Excel). 05-ch05.indd 277 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 278 PowerShell Python Bash Macros VBA Figure 5-7 We’re totally different, but we can do the same jobs! These five things are very different in what they do, where they work, and how they’re used. Yet collectively these five shells/languages/macros provide virtually identical tools to write amazing code to get work done (Figure 5-7). NOTE I don’t want to enumerate these five shells/languages/macros every time they come up, so let’s have a little fun and invent a term, just for this one small section: PPBMV (PowerShell, Python, Bash, Macros, Visual Basic for Applications). Once we’re done here, feel free to forget it. Let’s consider one example, changing file permissions. Every single member of PPBMV can change file permissions. PowerShell has the set-acl command to change NTFS permissions. Bash and Python can just run a chmod. VBA and most macros in Windows applications can change file permissions as well. Changing file permissions is just one example of what PPBMV can do. These tools can edit the registry (in Windows), change IP addresses or computer network names, manipulate files; this list goes on and on. These capabilities enable PPBMV to do good work, and we want PPBMV to have these features. But there’s a downside. Actions such as changing file permissions is also a dangerous thing done maliciously. We provide security to systems by first limiting what PPBMV can do and second, by watching for indicators of compromise such as unauthorized changes in permissions. Don’t blame the tool; blame the way it is used (Figure 5-8)! Limiting what PPBMV can do is done on a platform-by-platform basis. You can enable features such as execution policies and Constrained Language mode to limit what PowerShell can do, for example. You can isolate PPMBV on hosts with host-based firewalls. You can even completely delete these tools from your host unless they are needed. The trick here is understanding the power of PPBMV and doing your best to limit that power unless you need it. 05-ch05.indd 278 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-2: Malware 279 Figure 5-8 Don’t blame PPBMV, blame the attacker Do Evil ! Yessir ! VBA Module 5-2: Malware This module covers the following CompTIA Security+ objective: • 1.2 Given a scenario, analyze potential indicators to determine the type of attack Programmers with evil intent write software that attacks systems to gain control, do damage, or extract financial gain. This malicious software—malware—comes in many forms, for evil programmers can be just as clever as good programmers. The CompTIA Security+ exam will challenge you with scenario questions that expect you to recognize the symptoms of certain types of malware. Let’s go through the following types and make sure you’re aware of the differences: • • • • • • • • • • • 05-ch05.indd 279 Virus Cryptomalware/ransomware Worm Trojan horse Potentially unwanted programs (adware, spyware, crapware) Bots/botnet Logic bomb Keylogger RAT Rootkit Backdoor 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 280 Each section explores the malware, then finishes with a description of the symptoms and action(s) you should or could take to deal with an attack of that type. Some of the fixes involve actions to ameliorate the problems; others just acknowledge the obvious and recommend rebuilding and cutting your losses. Let’s take a look. Virus A virus is a piece of malicious software that must be propagated through a definite user action. In other words, it normally cannot spread by itself. It requires a user to initiate, in some way, the execution of the virus. Sometimes this action is very subtle, and the unsuspecting user may not even know that his actions are executing a virus. For example, he may open an infected file or executable, spawning the virus. Normally, viruses are propagated via download from malicious Internet sites, through removable storage media (USB sticks, for example) passed along from person to person, or through the transmission of infected files from computer to computer via e-mail or file sharing. Viruses have a variety of effects on computers and applications. These effects range from affecting performance by slowing down the system, filling up storage space, and slowing down the host’s network connections, to more serious impacts, such as recording passwords and other sensitive information, and rendering the host completely unusable or even unbootable. Some viruses infect files, while others, usually more serious ones, infect the boot sector of media. These boot-sector viruses automatically execute in the computer’s memory when the host boots up; at that moment, there is no OS-based antivirus software loaded to detect or eradicate it, so it has already done its damage by the time the OS loads. Usually, the only way to get rid of a boot-sector virus is to boot the host off of a known good (meaning clean and free of malware) media, such as a new hard drive, bootable optical disc, or a USB stick. The boot media should also have specialized antivirus software loaded on it to detect and clean the infection. A particularly vicious form of malware—called fileless malware (CompTIA calls it fileless virus)—behaves in some ways like a virus, attacking and propagating, but differs in one fundamental aspect. Fileless malware lives only in memory, not writing any part of itself to mass storage. Fileless malware often uses tools built into the operating system, such as PowerShell in Windows, to attack that very system. Anti-malware software struggles to identify, let alone mitigate, fileless malware. You might have wondered why it seems so easy for hackers to create viruses that can do so much damage; in fact, there are many programs on the Internet that help hackers create viruses easily. Some require extensive programming skills, and others are simple graphical programs that require almost no knowledge at all. Figure 5-9 gives an example of one such program, TeraBIT Virus Maker, but there are hundreds more out there. • Symptoms: System slowdown; some action against your system. • Action: Use an anti-malware program from a live boot to clear the virus from the system. 05-ch05.indd 280 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-2: Malware 281 Figure 5-9 TeraBIT Virus Maker, a virus creation program Cryptomalware/Ransomware Cryptomalware uses some form of encryption to lock a user out of a system. Once the cryptomalware encrypts the computer, usually encrypting the boot drive, in most cases the malware then forces the user to pay money to get the system decrypted, as shown in Figure 5-10. When any form of malware makes you pay to get the malware to go away, we call that malware ransomware. If a cryptomalware uses a ransom, we commonly call it crypto-ransomware. Crypto-ransomware is one of the most troublesome malwares today, first appearing around 2012 and still going strong. Zero-day variations of cryptomalware, with names such as CryptoWall or WannaCry, are often impossible to clean. • Symptoms: System lockout; ransom screen with payment instructions. • Action: Use anti-malware software from a live boot to clear the cryptomalware from the system. NOTE Most cryptomalware propagates via a Trojan horse. See the upcoming “Trojan Horse” section for more information. 05-ch05.indd 281 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 282 Figure 5-10 CryptoWall, an infamous crypto-ransomware Worm A worm is much like a virus, in that it can cause disruptions to the host, slow down systems, and cause other problems. However, a worm is spread very differently from a virus. A worm is usually able to self-replicate and spread all over a network, often through methods such as instant messaging, e-mail, and other types of network-based connections. The big difference between a virus and a worm is that a virus can’t spread itself; in other words, a virus requires a user action to replicate and spread. A worm doesn’t have this problem and can automatically replicate over an entire network with very little user 05-ch05.indd 282 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-2: Malware 283 intervention. This unfortunate characteristic of a worm is what causes it to be a significant problem in large networks. Examples of famous worm infections include MyDoom, Blaster, and the Win32Conficker worm. • Symptoms: System slowdown; unauthorized network activity; some action against your system. • Action: Use an anti-malware program from a live boot to clear the worm from the system. Trojan Horse A Trojan horse isn’t really a type of malware; it’s more a method by which malware propagates. Named after the Greek Trojan Horse of mythological fame, a Trojan horse is a piece of software that seems to be of value to the user. It could be in the form of a game, utility, or other piece of useful software. It is malware, however, and serves a specific function. Usually a Trojan horse has the goal of collecting personal information from a user, including user credentials, financial information, and so on. It can also be used as a generic container used to spread viruses and worms. (Note that symptoms and actions will follow the payload type, so will vary a lot.) EXAM TIP The CompTIA Security+ exam refers to Trojan horse malware as simply “Trojans.” Potentially Unwanted Programs Although technically not malware, some programs installed on your computer have negative or undesirable effects. Makers of the programs resented labels such as adware, spyware, bloatware, crapware, and so on, and sued the anti-malware companies to stop the use of such terms. For legal reasons, therefore, the industry adopted the term potentially unwanted programs (PUPs) as a blanket term for these programs that have negative effects on your computer. PUPs differ from malware because users consent to download them. That “consent” typically is obtained through sneaky, deceitful, or underhanded means. Often the user might seek to download a perfectly legitimate, useful application, but then clicks what seems to be the download option, only to install some PUP instead. Figure 5-11 shows a common bait-and-switch operation. Using a reputable thirdparty download site—CNET—I clicked the option to download CPU-Z (an excellent system hardware reporting tool, by the way). Rather than the download starting immediately, I was kicked to the page in Figure 5-11. At the top of the page in fine print it says “Your download will begin in a moment. If it doesn’t, restart the download.” Fine; companies like CNET make money off ads. That’s just capitalism. But at the bottom of the page, you see the giant “Start” button? Click that and you’ll install a nasty PUP, not the desired utility program. 05-ch05.indd 283 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 284 Figure 5-11 Underhanded and sneaky ad trying to trick user into installing a PUP Adware Adware is the name given to annoying advertisements that come in the form of pop-up messages in a user’s browser or on a user’s screen outside of a browser session. These messages usually want the user to visit a site, buy a product, or click the ad itself. At best, these messages can be irritating, interrupting a user’s activities with the pop-up message, but sometimes they are a real hindrance to productivity, often redirecting the user’s home pages in the browser or spawning several (sometimes dozens to hundreds) of pop-ups or Web sites at once. Computers get adware infections pretty much the same way they get other types of malware. The user may click a Web link or download something that changes browser or other configuration settings on the host, resulting in the continuous stream of pop-ups. Adware can even be included with purposefully downloaded, seemingly unrelated applications. Sometimes the user is asked to allow the installation of an add-in or browser helper object (BHO) to view a certain file type or run a piece of browser-based software. Most of the time, unsuspecting users will allow the installation by default, opening the door to pop-ups, automatically spawned programs, and browser redirection. • Symptoms: Unauthorized Web browser redirection; pop-up ads. • Action: Use an anti-malware program from a live boot to clear the adware off the system. 05-ch05.indd 284 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-2: Malware 285 Spyware Spyware isn’t a type of malware; it’s more of a goal for some types of malware. Spyware is a virus or Trojan horse in form, but we tend to classify spyware by its function rather than type. Spyware is used for the specific purpose of surreptitiously observing a user’s actions and recording them, as well as stealing sensitive data, such as passwords, credit card information, and so forth. Spyware can send data back to the attacker, quietly of course, so that the user can’t easily detect it. Spyware can also dump data into a file so an attacker can later retrieve it directly from the system if she has physical access. Spyware can affect hosts through various means, in usually the same way that other malware does. NOTE The spyware aspect of a malware can take many forms. Look to the specific payload type for all the malware symptoms and the actions you should take to combat it. Crapware The rather derogatory term crapware describes software that purports to help users accomplish tasks, but instead directs the users to sites that primarily benefit the software developers. The most common of these programs are the free, additional toolbars that install in Web browsers. These have built-in search and help features, but they don’t take you to the excellent Google or Bing search tools. Instead, they send the unsuspecting user to ad-filled mediocre search pages, track user searches, and more. Educate users not to install these foul things! Bots/Botnets A botnet is a distributed type of malware attack that uses remotely controlled malware that has infected several different computers. The idea is to create a large robot-like network used to wage large-scale attacks on systems and networks. Once the malware is installed on the host, the attacker can control hosts remotely and send malicious commands to them to be carried out. The hosts are called bots, or zombies, because they obey only the orders of the attacker once the attack begins. One of the common implementations of bots and botnets involves servers that control the actions of the bots. These command and control (C2) protocols try to automate the control, not requiring human interaction after the initial programming. See Chapter 8 for more details about C2 protocols, botnets, and the brutal attacks they can deliver, such as DDoS attacks. Among the different attack methods that botnets can use is sending massive amounts of malware to different computers, sending large volumes of network traffic, and performing other methods designed to slow down or completely disable hosts and networks. Botnet attacks can spread rapidly once activated and can be very difficult to counter. 05-ch05.indd 285 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 286 In fact, one of the attack methods used during an attack is to infect other hosts and have them join the botnet: • Symptoms: Usually undetectable until activated. System slowdown in some cases. • Action: Use an anti-malware program from a live boot to clear the bot from the system. Logic Bomb A logic bomb is often a script set to execute either at a specific time or if a certain event or circumstance takes place on the system. It is designed to take malicious actions when it executes. An example of a logic bomb is a script that has been written to begin erasing file shares or disk storage at a certain time or date. Most logic bombs are timed to execute by including them as a scheduled event using the operating system’s event scheduling facility, such as the AT command in Windows or the cron utility in Linux-based systems. A logic bomb is not necessarily a form of malware—at least it’s not the kind that can easily be detected by anti-malware software. Logic bombs are usually planted by a malicious insider or a disgruntled administrator; most of the logic bomb attacks recently sensationalized in the news media involved a rogue administrator dissatisfied with an employer for whatever reason. Detecting a logic bomb can be troublesome; it usually requires examining any files, utilities, and scheduled jobs the malicious user had access to, as well as auditing the user’s actions and reviewing the access logs that recorded any use of his privileges. • Symptoms: Usually undetectable until activated. System damage, data loss. • Action: Restore system from backups. Keylogger A keylogger is a piece of malware that records keystrokes. Most keyloggers store a certain number of keystrokes and then send the stored keystrokes as a file to the bad actor. Recorded keystrokes are one of the best ways to collect passwords, filenames, and other highly personalized types of information. Keyloggers are not all evil. They are a very common feature for parental control software. Figure 5-12 shows one example, Spyrix Free Keylogger. NOTE Keyloggers also manifest as malicious hardware dongles that sit between your keyboard and your system. Hardware keyloggers manifest as tiny USB adapters that fit between a keyboard USB connector and the USB port on the system. They’re nondescript and do not show up as system devices, so you won’t know they’re present without physical inspection. They 05-ch05.indd 286 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-2: Malware 287 Figure 5-12 Keylogger interface come in a couple of varieties. Some have flash memory built in and require periodic physical removal for scanning. Others transmit wirelessly to a receiving system. • Symptoms: Often no symptoms at all. System slowdown; unauthorized network activity. • Action: Use anti-malware software from a live boot to remove the keylogger software. Removing keylogger hardware requires suspecting such a device might exist, finding it, and physically removing it from the system. Then smashing it with a hammer. RAT RAT stands for one of two things. First, RAT stands for remote administration tool, which is some form of software that gives remote access for administrators and IT support. We use this kind of RAT all the time in IT to log into servers, remote cameras, Internet of Things (IoT) devices (lightbulbs, thermostats, etc., connected to the network), and to provide support for users all over local networks and the Internet. Second, RAT also stands for remote access Trojan, which is a remote administration tool maliciously installed as a Trojan horse to give a remote user some level of control of the infected system. This can be as simple as just opening a Telnet server on the infected system to full-blown, graphical remote desktops. RATs are often an important part of a botnet. • Symptoms: Usually undetectable until activated. System damage, data loss. • Action: Restore system from backups. 05-ch05.indd 287 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 288 Rootkit A rootkit is a piece of malware that attempts to infect critical operating system files on the host. Often, anti-malware software cannot easily detect rootkits, so they can reside on the system for quite a while before detection. Additionally, rootkits can thwart anti-malware software because they can send false system information to it, preventing it from detecting and eradicating not only itself but other malware as well. • Symptoms: Often no symptoms at all. System slowdown; unauthorized network activity. • Action: Although you can find anti-malware software that claims it can remove a rootkit, always opt for the better solution: wipe the drive and reload. Backdoor A backdoor is an entry method into a piece of software (application or operating system) that wasn’t intended to be used by normal users. Most backdoors are created as a maintenance entry point during software development, usually by the programmers creating the software. These maintenance backdoors should be closed prior to software release, but often they are either forgotten about or left open intentionally to bypass security mechanisms later after the software is released, either by the programmer or a malicious entity. NOTE A few smartphones and other mobile devices manufactured in China have been found to have backdoors. Backdoors can also be created by hackers during an intrusion into a system; often their goal is to have a way back into the system if their primary entry point is taken away or secured. Again, backdoors usually bypass security mechanisms that normally require identification and authorization, so this is a serious security issue. Vulnerability testing can often detect these unauthorized entry points into a system, but sometimes more in-depth testing methods, such as penetration testing or application fuzzing, may be required to find them. NOTE Like Trojan horses, a backdoor is a method of entry into a system, not a malware type. Look for the specific payload type to determine symptoms and actions you should take to protect or remediate. Module 5-3: Cybersecurity Resilience This module covers the following CompTIA Security+ objective: • 2.5 Given a scenario, implement cybersecurity resilience 05-ch05.indd 288 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 289 Was that an attack? Figure 5-13 I rebuff your pathetic attempts! Attack tor Vec What if you could design a system such that even if successfully attacked, the system could in some way quickly (as in a matter of seconds) rebuild itself or, even better, weather an attack without the attack being able to do any real damage? That’s the idea behind cybersecurity resilience: adding technologies and processes that don’t stop attacks, but enable the system to recover easily (Figure 5-13). EXAM TIP Resilient systems don’t eliminate risk. That’s impossible! Resilient systems fight off attacks more readily than systems with less resilience. They handle risks better, in other words. The principles here apply to individual systems and to larger “systems,” such as an enterprise network. There are many ways to make systems more resilient, but it helps to organize these methods into three main categories: non-persistence, redundancy, and diversity. Nonpersistence simply means to possess a method to bring a system back quickly to its preattack state. Redundancy means to have more than one of some functioning feature of a system or even another complete system. Diversity refers to the practices of using a variety of technologies, vendors, cryptographic systems, and controls to avoid the possibility that all systems have the same vulnerability and can be taken out en masse. Non-persistence A typical individual system is persistent in that it has a fixed set of hardware, a fixed operating system, and a fixed configuration. If you turn off a system and turn it back on, you have the same hardware, the same operating system, and the same configuration. It is persistent. The downside to a persistent system is that if an attack takes place, that attack will in some way change some aspect of that persistent state. The attack might wipe a hard drive. It might inject evil device drivers. It might create privileged users you don’t want on the OS. If any attack takes place, there’s a good chance you’ll have to go through some painful recovery process. This might include reinstalling an operating system or rebuilding from backups. These are time-consuming processes and ones to avoid by using less persistent systems. 05-ch05.indd 289 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 290 Achieving non-persistence means pursuing one of these options: • • • • Virtualization/snapshots Revert to known state VMs and automation Live boot media Virtualization/Snapshots There are many reasons virtualization has taken over the world of serving systems these days. One reason is the ease of recovery by simply shutting down a virtual machine (VM) and then restarting it without affecting any of the underlying hardware. But another feature, and the one that very much fits under the idea of non-persistence, is the snapshot. A snapshot is the stored difference between the files in one version of a VM and the files in another version. While the snapshot procedure varies from one virtualization platform to another, imagine a perfectly functional VM where you change a single device driver, only to discover over time that the device driver is buggy and keeps causing your VM to crash. If this were a classic persistent system, you’d have to reinstall the device driver. If you made a snapshot of the system before you installed the device driver, however, you could simply revert to the earlier snapshot and bring the system back to its original function (Figure 5-14). Snapshots are a critical non-persistence tool for VMs. Every time you change a driver, update an application or service, patch a client OS, or take any other action that makes any significant change to your VM, run a snapshot. Revert to Known State Every technician has made some change to an operating system, only to find that the change he or she made is flawed in some way. A bad driver, a poorly distributed patch, or an OS update that fails to perform the way the tech thought and causes problems can Figure 5-14 Snapshots in VirtualBox 05-ch05.indd 290 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 291 Figure 5-15 Restore points in Windows make the tech want to go back to the way things were before the change was made. If you have a virtual system, you can easily erase such changes via a snapshot. On a fixed traditional system, it’s not that easy. Every major OS has some form of revert/rollback method to bring a system back to a previous state, what the CompTIA Security+ objectives call revert to known state. All revert/rollback methods work by making the OS aware of changes and then storing files or settings in such a way that techs can look up previous states and tell the OS to go back to one of those states. Microsoft Windows enables you to create a restore point—a capture of the overall operating system and drivers at that moment in time—that enable you to revert the operating system to an earlier configuration (Figure 5-15). Windows restore points aren’t perfect. They don’t save user information or installed applications; but other than those two issues, restore points are very powerful. Device drivers, especially video card drivers, often have unforeseen problems that motivate a return to a previous driver version. Equally, a refactored device driver might wreak havoc on an otherwise perfectly good system. Again, Windows has an elegant solution in the Roll Back Driver feature, as shown in Figure 5-16. 05-ch05.indd 291 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 292 Figure 5-16 Roll Back Driver in Windows Apple macOS machines rely on Time Machine, a program that records snapshots of the state of the computer over time to an external drive (Figure 5-17). If you support Macs, establish Time Machine for every system. Apple macOS doesn’t have a roll back driver feature similar to that in Windows for two reasons. First, Apple checks all drivers much more aggressively than Microsoft; so bad, refactored, or shimmed drivers almost never happen. Second, Time Machine supports drivers as well, making a separate rollback feature unnecessary. EXAM TIP Older Windows versions (such as Windows 7) offered a boot feature called last known good configuration that enabled quick recovery from installation of a buggy driver. The feature was especially useful with buggy video card drivers. The inability to get into the Windows graphical user interface made troubleshooting or uninstalling problematic. Windows 10 has much more powerful tools through Advanced Recovery options. Not sure why CompTIA left last known-good configuration in the Security+ objectives, but now you know what it is. 05-ch05.indd 292 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 293 Figure 5-17 Time Machine in macOS VMs and Automation Many modern networks use virtualization technologies to provide both rollouts and rollbacks of many systems all at once. With a master image—the desktop environment for users of very specific hardware and configurations—a central server can push that image to every local computer. Automation/scripting can make rollouts regular, such as after patch Tuesday—and configuration validation (i.e., it works!)—so users always have up-to-date builds. This kind of automated course of action helps keep systems current. EXAM TIP You’ll see this aspect of VMs—the capability to push out multiple identical copies—categorized as replication on the CompTIA Security+ exam. Plus, master images enable network administrators to respond very quickly to problems. With continuous monitoring, as you’ll recall from Chapter 3, network administrators keep up with the reporting from network monitoring and managing tools. If a recent rollout hits snags, the network techs can fix the master image and, with a manual rollout, essentially “roll back” the problematic build. Similarly, if a new bug or attack causes problems, a fixed and validated master image can be quickly deployed. 05-ch05.indd 293 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 294 NOTE Virtual machine developers, like VMware, enable you to create a template of a completed VM that you can use to create identical versions of the VM. Templates provide excellent flexibility and rapid deployment of additional servers as needed. Live Boot Media If you want the ultimate in non-persistence on a non-VM system, you can always use some kind of live boot media. Live boot media are complete, installed operating systems that exist on bootable media. The names change to match the media. On optical media, for example, they’re called live CDs; for consistency, bootable flash-media drives should be called live sticks (they’re not), but they’re usually just called bootable USB flash drives. You boot a system to the live boot media and use the OS as configured. Your system doesn’t even need a hard drive. Live boot media are very popular in Linux environments, giving you an opportunity to try a Linux distro without installing it on your hard drive (Figure 5-18). Live boot media go way beyond test-driving Linux. You can easily install a carefully configured system, say a DNS server, to a live boot and run the entire server in that fashion. As long as the serving system doesn’t need to store any persistent data (like a database Figure 5-18 Live CD installation option in Linux 05-ch05.indd 294 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 295 Figure 5-19 Kali Linux downloads that changes), you can run almost any OS/application combination from a live boot media. One of the most popular live boots is Kali Linux, the go-to Linux distro, stuffed full of many IT security tools (Figure 5-19). Redundancy Non-persistence provides excellent resiliency in most cases, but falls short in data storage when there are big changes in the state of the stored data. Snapshots/reverts are wonderful for subtle changes in operating systems, such as a security patch or a driver update, as they don’t require much mass storage space. They simply aren’t designed to deal with big changes to data, such as customer databases, inventories, users’ file storage, and other such data that requires a lot of hard drive space. Traditionally, this type of data is backed up daily; in this situation, turn to redundancy to provide the system resiliency needed. But where to apply redundancy? There are several options. You can create redundant mass storage, redundant systems (including their mass storage), even redundant 05-ch05.indd 295 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 296 networks (including all the systems and all their mass storage). You can create more than one copy of non-OS critical data so that if one copy dies, another copy is ready to go to keep the systems up and running. Redundancy is everywhere! The Benefits of Redundancy At first glance, it’s easy to look at redundancy as nothing more than a backup of storage, systems, or even networks, but true redundancy is far more powerful. First is fault tolerance. With fault tolerance, the secondary storage, the system, and the network are online and ready to go. If something goes wrong, the data on the storage or the services provided by the system can have a minimal amount of disruption. Second, redundancy provides high availability. High availably means using redundancy in such a way as to ensure that certain levels of operational performance are balanced against risk. Third, you can work on one of your services offline with minimal impact to your customers, whether that’s adding capacity or repairing a component. Let’s look at the redundancy technologies that provide both fault tolerance and high availability. RAID Redundant array of inexpensive disks (RAID) is a fault tolerance technology that spans data across multiple hard disk drives or solid state drives within a server or workstation. This level of fault tolerance specifically addresses hard drive failure and balances the need for data redundancy with speed and performance. RAID uses multiple physical mass storage drives to create logical drives, usually making it transparent to users. Data is spanned across the different physical drives, along with metadata (usually parity information), so that if any one drive fails, the other drives in the RAID set can continue to provide data while the single drive is replaced. NOTE Many IT specialists prefer to describe RAID as “redundant array of independent disks,” rather than the original inexpensive. You’ll definitely see the terms out in the wild both ways. CompTIA goes with the original wording. Just remember RAID and you’ll be fine on the exam. There are several different RAID levels; which one you should use for a system depends upon different factors, including the number of available disks and the balance of total available space for storage, as well as the levels of speed and performance the system requires. RAID levels can be implemented in several ways. Striping typically means writing pieces of data equally across two physical disks. Mirroring, in contrast, completely duplicates data on each disk. Using more disks, you can include parity information, which enables data to be restored in the event of a single disk failure. You’ll find combinations of all these. Figure 5-20 illustrates examples of different RAID levels using these techniques. There are trade-offs for each of these different methods, which include total amount of storage space, speed, performance, and the number of disks required in the RAID array. Table 5-1 summarizes some of the different RAID levels and their details. 05-ch05.indd 296 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 297 Disk Mirroring Figure 5-20 Examples of RAID configurations Duplicate data on both drives Disk Striping (with parity) 1 2 3 4 P Data written in blocks across all drives, with parity bits Storage Area Networks A typical LAN has file servers that store data that is accessed via network stacks. It also has local storage that your system accesses via block-level controllers that access the drives. A storage area network (SAN) is a network storage that enables you to access the shared folders by using block-level controls rather than the network stack. This gives SANs some unique capabilities, mainly on-the-fly volume creation/manipulation. On most systems, Minimum Number of Physical Drives Required RAID Level Details RAID 0 Disk striping; does not use mirroring or parity; provides for performance only with no redundancy. 2 RAID 1 Disk mirroring; all data is completely duplicated on both disks; uses no striping or parity but provides for full redundancy at the expense of the loss of half the total available disk space for duplication. 2 RAID 5 Disk striping with parity; parity information is spread across all disks evenly; 1/n of the total disk space available is used for parity. 3 to n RAID 6 Disk striping with double distributed parity; this allows for failure of up to two drives. 4 RAID 1+0 (or sometimes seen as RAID 10) Disk mirroring with striping; combines both RAID levels 0 and 1 for performance and redundancy; a stripe of two mirrored arrays. 4 RAID 0+1 Disk striping with mirroring; combines both RAID levels 0 and 1 for performance and redundancy; a mirror of two striped arrays. 4 Table 5-1 Summary of RAID Levels 05-ch05.indd 297 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 298 if you want to add storage, you first get a storage device, configure it, mount it, and format it. On a SAN, you just tell the SAN controller to add another disk to your local system. You can create a new volume or you can mount an existing volume. System Redundancy RAID is certainly the go-to technology to provide fault tolerance for mass storage, but what about systems? What happens if the Web site sits only on one Web server and that server fails? Server redundant technologies such as multipath, NIC teaming, geographic dispersal, and virtualization provide both fault tolerance and high availability. Multipath A multipath solution provides more than one way to access storage. A RAID 1 implementation with two controllers, one for each drive, is the traditional multipath solution (called disk duplexing, as you might recall from CompTIA A+ studies). More than one connection to a SAN is also a typical implementation of multipath. NIC Teaming Network interface cards rarely fail, but when one does, the system with the bad NIC is offline until the NIC is replaced. Network interface card (NIC) teaming addresses this issue by using two or more NICs on a single system that act as though they are a single NIC with one MAC address and one IP addresses. Not only does NIC teaming increase throughput (sort of ), but if one NIC fails, the other continues to work (Figure 5-21). Figure 5-21 File server with NIC teaming 05-ch05.indd 298 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-3: Cybersecurity Resilience 299 NOTE NIC teaming doesn’t suddenly turn two Gigabit Ethernet NICs into 2-Gbps throughput for a system, although that’s a common misconception. Moving one large file still tops out at 1 Gbps. Where you’ll see better performance is when moving multiple files at the same time. The additional NIC or NICs essentially offer additional 1-Gbps lanes for traffic. Geographic Dispersal The gold standard for system redundancy is to make perfect copies of the same system and spread them apart geographically, then use the Internet to keep the copies identical. Geographic dispersal protects from natural disasters and widespread Internet disruption. You can set up your own dispersed servers, but virtualization services make it easy. Virtualization/Cloud Services For decades we used real servers in real locations (on-premises), but those days are over. Nothing beats virtualization, especially cloudbased services, for giving you all the benefits of redundancy, especially high availability, without outrageous cost and time. First, virtualization solutions are incredibly scalable. Let’s say you develop a new Web app and launch it on a single Amazon S3 server, and suddenly your product is a huge hit (and the single server is swamped). Virtualization services like Amazon S3 make it easy to spin up more copies of your server (although you can do this locally—on prem, as they say—as well). Add as many copies as you want and need! EXAM TIP Expect a question on the CompTIA Security+ exam that explores on-premises vs. cloud in terms of redundancy, high availability, and scalability. Virtualization also makes geographic dispersal easy to achieve. Is your new Web site huge in Japan? Just tell Amazon to spin up some new servers over in Japan so your customers in Tokyo get the same speed and response as your US users (Figure 5-22). The other amazing high-availability power of virtualization comes from elasticity. Going back to the Web app idea, some Web apps have cycles of high and low demand (tickets sales, sports broadcasts, etc.). These cases require scalability both in terms of Figure 5-22 Virtualization makes geographic dispersal easy. 05-ch05.indd 299 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 300 expanding and contracting on an as-needed basis, better known as elasticity. All virtualization providers have simple features to add or remove server instances automatically based on predetermined load values. NOTE Industry uses the term template to describe a server purchase. For example, you might order a certain tier of stuff. “I want a medium cluster with a blue level of security and redundancy.” That’s the template. Once you get it, you take a snapshot of it and can rebuild it at any time. So sweet! Diversity Security people have a tendency to stick with single technologies, crypto, and controls from preferred vendors. Why not? We know they work, we know how to use them, and we know how to fix them. The danger with such a lack of diversity is the possibility that all systems have the same vulnerability and can be taken out en masse. When organizations rely on multiple redundant technologies, vendors, cryptographic systems, and security controls, that diversity provides cybersecurity resilience. If a single technology fails, a vendor disappears, the crypto system is cracked, or security controls change and conflict, an organization that employs multiple systems through diversity can quickly pivot and implement fixes. Diversity takes more work, sure. Security and network people need to master multiple systems, vendor relations multiply with more than one vendor, and so on. But diversity enhances cybersecurity resilience. Module 5-4: Securing Hardware This module covers the following CompTIA Security+ objectives: • 1.2 Given a scenario, analyze potential indicators to determine the type of attack • 2.5 Given a scenario, implement cybersecurity resilience • 2.7 Explain the importance of physical security controls • 3.2 Given a scenario, implement host or application security solutions • 3.3 Given a scenario, implement secure network designs • 3.8 Given a scenario, implement authentication and authorization solutions Many years ago, an overly cocky security tech friend presented a challenge to me. He said that he had secured a server system so perfectly that no unauthorized person could access the data, and he challenged me to try. Accepting the challenge, I didn’t waste a moment trying to attack the system remotely. Instead, I simply put on some work clothes to look like a maintenance man, went to the location, and used my social engineering skills to gain entry. Once inside, I found the server and yanked out every hard drive. With plenty of time and completely nonsecure hardware, it was just a matter of cracking a Windows login and … success! 05-ch05.indd 300 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-4: Securing Hardware 301 There’s a strong lesson here for any security person. Physical possession of mass storage—or complete systems that hold the mass storage devices—is every attacker’s dream. Granted, getting to the data might be a challenge, but every pawn shop, every classified advertising medium, and every law enforcement office in the USA is filled with stolen systems. If an attacker can get to the physical system, no firewall, no network login, no wireless access point is going to prevent him from eventually getting to the precious data. Secure hardware presents the last line of defense for these types of attacks. Virtually every piece of hardware that runs an Intel- or ARM-based CPU comes prepackaged with powerful tools to lock down a system to secure individual computers from physical attacks. This module starts with a discussion of a few of the nasty types of physical attacks on systems. The module then covers many of the technologies used to protect systems from attacks, both intentional and unintentional. We’ll finish with more specific options for securing boot integrity. Physical Attacks If a threat actor is allowed to get physical access to a system, even for the shortest of moments, there are plenty of interesting tools the threat actor may physically connect to the system to gather all kinds of information about the system, the users, and even the network. Malicious USB Cable/Drives Any unused USB port on a system is a huge vulnerability. A bad actor can easily plug in a Bluetooth adapter and instantly use his or her own Bluetooth keyboard. Figure 5-23 shows one of my favorite tools, a HAK5 USB Rubber Ducky. I just plug it into any USB port and it starts sending preconfigured commands, such as capturing keystrokes and delivering a payload to compromise the system. The downside to a malicious flash drive is that someone is going to notice it eventually. That’s why my good friends down at HAK5 make a similar tool that looks like a cable! HAK5’s O.MG cables can plug between any two USB devices: smartphone to desktop, smartphone to power charger, desktop to USB device (such as an external drive or keyboard). While still working as any USB cable should, the O.MG steals any information it can based on how it is connected (Figure 5-24). The O.MG exemplifies a malicious Universal Serial Bus (USB) cable as defined in the CompTIA Security+ objectives. NOTE HAK5.org makes awesome tools for testing systems, part of the field of pentesting. Check them out at https://shop.hak5.org. I recommend disabling every unused USB port, usually leaving only one open in front of the system, thus easily observed. See the following sections for more options. 05-ch05.indd 301 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 302 Figure 5-23 HAK5 USB Rubber Ducky Figure 5-24 HAK5 O.MG cable (Image: Berkah, Getty Images) 05-ch05.indd 302 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-4: Securing Hardware 303 EXAM TIP Look for an exam question on controlling removable media. The correct answer to the question likely will be related to disabling USB ports or, more specifically, not allowing access to USB ports to malicious actors. Attacking Cards Attackers love to copy and clone our plastic cards—credit cards, loyalty cards, office issued IDs … anything on a card is fair game to the right bad actor. The main weakness to any form of plastic card is the magnetic stripe on the back. The information on those stripes is easily read by a card scanner and can then be placed on another card. We call this card cloning. So how do the bad guys read our cards? By using card skimmers. These devices sit surreptitiously on top of the card readers at ATMs, vending machines, gasoline pumps— wherever users insert cards—and read the stripe, a process called skimming. Card skimmers also usually come with cameras to capture users typing in a PIN code, a ZIP code, or a CVV code as well. Figure 5-25 shows an ATM skimmer. Some security tools, in particular the EMV card format (the cards with the little chip), make skimming and cloning a lot harder than it used to be, but the many countries that have yet to fully adopt the EMV standards (such as the United States) are still happy hunting grounds for skimmers and cloners. Securing the Systems The first thing on any security person’s list when new hardware comes in is to do what can be done to secure the systems. These steps are always carried out when new systems arrive and are brought online. Well, if not carried out, then at least considered! Theft Prevention All new equipment is given an inventory tag and tracked by installation location. Portable devices are issued to specific individuals who are solely authorized to use them and hold Figure 5-25 ATM skimmer (Image: Chalongrat Chuvaree / EyeEm, Getty Images) 05-ch05.indd 303 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 304 some degree of responsibility for keeping them secure. Static devices are often secured when possible. You can stop theft with some good physical security. First, almost all desktop and server system cases come with anti-intrusion alarms. If anyone opens the case, the system sets off an audible alarm. Second, get a cable lock, particularly if you place a laptop in a tempting location for thieves. All laptops come with a reinforced cable lock port. You should consider Kensington Computer Products Group (www.kensington.com) for a variety of excellent cable locking systems. Finally, don’t forget a screen filter. Screen filters are excellent tools to narrow the field of vision. This prevents shoulder surfers from observing the content of your screen. Securing Physical Ports As previously mentioned, an unused USB port is a huge vulnerability. Account for every port on a system. USB ports are everywhere! Many monitors/displays have handy USB ports. Most printers and multifunction devices (MFDs) have USB ports. Even many home routers have USB ports. Those are the most important ones to turn off because you rarely observe them. If at all possible, turn off all unneeded ports. If a port cannot be turned off, physically block it. Certain devices such as ports on portable devices need those ports working, so it’s common to install USB data blockers, devices that you insert into a USB port that deny any data flow into the port, while still providing power for charging smartphones and such. See Figure 5-26. With a USB data blocker installed, devices like the previously discussed HAK5 tools won’t work. Securing Power Good power is critical. All the locks, guards, and firewalls mean nothing if your systems don’t have reliable, clean electrical sources. Let’s consider what an organization can do to secure the power it has and needs. EXAM TIP All this electrical stuff is more in the realm of data centers and distribution frames that power lots of servers and networking devices. Most of this equipment would make no sense in a home or office. Dual Supply Many higher-end devices support dual power supplies. These aren’t complicated: if one power supply goes out, the other takes over. The only trick to dual power supplies is to make sure you buy a product that supports them and also make sure that product comes with two power supplies. Figure 5-26 USB data blocker 05-ch05.indd 304 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-4: Securing Hardware 305 Figure 5-27 Power generator (Image: Westend61, Getty Images) Uninterruptible Power Supply An uninterruptible power supply (UPS) uses a small battery (often the same type used in motorcycles) as a backup power source if the power ever sags or goes out completely. It’s very common to place a UPS at the bottom of an equipment rack, powering all the devices on the rack with quality, dependable power. A UPS is designed to power a system for a few minutes to enable an orderly shutdown. Generator If you need to ensure that a system has uninterrupted power for an extended period of time after a power failure, you need to consider an onsite generator as a source of backup electricity. Generators are expensive, but if you need real backup power, this is your only choice. Most generators run on either natural gas or diesel (Figure 5-27). Managed Power Distribution Units Great. You have a rack full of equipment and that equipment needs power. You have a UPS at the bottom of your rack, but now you need to distribute the power coming from your UPS to the devices. Plus you need to ensure that you have sufficient outlets for all the gear on the rack. That’s where a power distribution unit (PDU) comes into play. At the simplest end a simple power strip is a PDU, but if you’re going to distribute power, why not use a managed PDU that can monitor power usage, send alarms, and so forth? Securing Boot Integrity IT professionals need to plan for many contingencies so that users have secure computers with which to work. At the system level, for example, they must assure the security of individual system components by securing the supply chain. Second, they must implement 05-ch05.indd 305 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 306 technologies that will protect data in the event of theft or unauthorized physical access to systems. This section explores these aspects of physical security: • • • • Using TCG technologies Using TPM for boot security Using disk encryption Incorporating HSMs Using TCG Technologies The IT industry knew back in the mid-1990s that ensuring cross-platform technology security was going to take a lot of big companies working together, so AMD, HewlettPackard, IBM, Intel, and Microsoft got together and formed an organization now called the Trusted Computing Group (TCG). Over the years, TCG has included roughly 100 of the most important hardware and operating system manufacturers (Figure 5-28). Figure 5-28 Trusted Computing Group 05-ch05.indd 306 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-4: Securing Hardware 307 TCG is solely responsible for all the most popular technologies that, when used collectively, make your system very secure. Let’s look at those technologies and see how they work. Using TPM for Boot Security Most modern computers ship with a chip called a Trusted Platform Module (TPM) (see Figure 5-29) that works with system firmware—UEFI in current PCs, for example— to provide a baseline level of security and trust. The operating system relies on this hardware root of trust to check for low-level changes at bootup. These changes can happen from malware, for example. Depending on the system, any tampering could lead to automatic loading of a last known-good system or a system stop. EXAM TIP Modern personal computers rely on Unified Extensible Firmware Interface (UEFI) for firmware, as you’ll recall from your CompTIA A+ studies. Look for a question on the CompTIA Security+ exam that points to boot security/Unified Extensible Firmware Interface (UEFI) as the preferred method for assuring boot integrity. This boot-level security, called generically secure boot, can also work with more centrally controlled systems. During the boot process, the TPM and UEFI generate reports about the process and can send those reports to a remote system, like a central authentication server. This process is called boot attestation. A typical scenario would describe analyzing the reports or reporting process involving TPM as an example of authentication management. With Windows 10, Microsoft added another tool called Measured Boot that interacts with UEFI and TPM over a network to verify the integrity of the boot files. This architecture blocks malware such as rootkits. EXAM TIP Windows 8 and later feature Secure Boot to take advantage of TPM and UEFI to provide boot attestation. The Linux folks tend to use the open-source Opal Storage Specification. Figure 5-29 TPM chip 05-ch05.indd 307 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 308 Using Disk Encryption Security professionals use various forms of disk encryption to protect data at rest (DAR), files and folders stored on mass storage and not in transit/motion or in processing (active use). Disk encryption has been around in one shape or another for a long time and certainly predates TPM chips, but the presence of TPM provides a powerful tool for encrypting drives. Every operating system supports full disk encryption (FDE), which typically means every part of a drive is encrypted except the boot sector. The FDE tool that comes with Windows Pro versions is called BitLocker. To encrypt a drive with BitLocker, you must have a motherboard with a TPM chip and you must have TPM enabled in UEFI (Figure 5-30). EXAM TIP Expect a question (or an answer) on the CompTIA Security+ exam that equates disk encryption as a method or part of the process of hardening an operating system. So think beyond securing data here to seeing solutions for a whole system. You can go even more secure with disk encryption by using a self-encrypting drive (SED) that automatically encrypts and decrypts all data on the drive. From the outside, a SED looks exactly like any other drive. It works on both traditional hard disk drives (HDDs) and solid state drives (SSDs). A SED often comes with extra features, such as instantaneous drive wiping, that high-security folks really enjoy. EXAM TIP The Trusted Computing Group publishes the specifications for the Opal Storage Specification that enables SED for Linux as well as Windows. Figure 5-30 BitLocker in Windows 05-ch05.indd 308 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-4: Securing Hardware 309 Incorporating Hardware Security Modules The many processes that take advantage of asymmetric key storage, authentication, encryption/decryption, and other functions can often swamp general-purpose CPUs and operating systems. For Web servers, automated teller machines, or other applications that perform an unusually high amount of key handling, it’s usually a good idea to offload this work to other hardware. A hardware security module (HSM) is any type of hardware that’s designed to do this work. An HSM might look like a network appliance, supporting one or more servers; it might be a USB device; or like Figure 5-31, it might look like a PCIe card you install on a system. When cryptography is slowing down a server’s response time, an HSM, with its optimized processors designed to handle cryptographic functions hundreds of times faster than an equivalent general-purpose CPU, will speed up key handling dramatically. HSMs are expensive, but when time is of the essence, HSMs are the way to go. EXAM TIP A typical scenario would describe deploying HSMs as an example of authentication management. NOTE You can use an HSM for secure boot (which is why it’s placed here in the book). Often this manifests with a combination of flash media, system on a chip (SoC) systems, and certificates. The process is well beyond this discussion, but worth noting. Figure 5-31 HSM PCIe card 05-ch05.indd 309 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 310 Module 5-5: Securing Endpoints This module covers the following CompTIA Security+ objectives: • 1.6 Explain the security concerns associated with various types of vulnerabilities • 2.1 Explain the importance of security concepts in an enterprise environment • 3.2 Given a scenario, implement host or application security solutions The previous module discussed several tools to secure hardware and made more than one reference to securing operating systems and applications. This module carries the story forward, focusing on applying well-known security controls to design the right endpoint protection, for both operating systems and applications. Hardening Operating Systems Hardening an operating system means several things, but mostly it’s about configuring the operating system and setting security options appropriately. Security professionals should adhere to the golden rule for hardening: If you don’t need it, remove it. If you can’t remove it, turn it off. Although all operating systems provide methods and interfaces for secure configurations, we’re not going to focus on one specific operating system in this module. Instead, we’ll focus on several configuration settings that should be considered regardless of operating system. NOTE The federal government and various organizations publish guidelines on specific settings for hardening systems. Check out the Department of Defense (DoD) Security Technical Implementation Guides (STIGs) as a great example: https://public.cyber.mil/stigs/. Regardless of the operating system in use, you should focus on privilege levels and groups (administrative users and regular user accounts); access to storage media, shared files, and folders; and rights to change system settings. Additional settings you should evaluate include encryption and authentication settings, account settings such as lockout and login configuration, and password settings that control strength and complexity, password usage, and expiration time. You also should consider other system settings that directly affect security, including user rights and the ability to affect certain aspects of the system itself, such as network communication. These configuration settings contribute to the overall hardening of the operating system. 05-ch05.indd 310 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-5: Securing Endpoints 311 Figure 5-32 Security options in Windows 10 Figure 5-32 shows a sample of some of the different options that you can configure for security in Windows. Figure 5-33 shows other options that you can configure in a Linux operating system. EXAM TIP You might see a question about endpoint security solutions that explicitly state the need to harden the Windows Registry, the central database in Windows for configuration of just about everything. For the most part, applying hardening techniques discussed in this module will lock down access to the Registry to only those accounts that need to access it— administrators, in short—and provide more than adequate security. Trusted Operating System A trusted operating system is a specialized version of an operating system, created and configured for high-security environments. It may require very specific hardware to run on. Trusted operating systems are also evaluated by a strict set of criteria and are usually used in environments such as the US Department of Defense and other government agencies, where multilevel security requirements are in place. 05-ch05.indd 311 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 312 Figure 5-33 Security options in Linux An example of the criteria that a trusted OS must meet is the Common Criteria, a set of standards that operating systems and other technologies are evaluated against for security. A lot of national governments worked together to create the Common Criteria, including the United States, the United Kingdom, Canada, Germany, France, the Netherlands, and more. Trusted operating systems have very restrictive configuration settings and are hardened beyond the level needed for normal business operations in typical security environments. Examples of trusted operating systems include Trusted Solaris, SE Linux, and Trusted AIX. Some operating systems, such as Windows 10 and Windows Server, have been certified as trusted operating systems. Host-Based Firewalls and Intrusion Detection In addition to setting up security configurations on a host, you need to protect the host from a variety of network-based threats. Network-based firewalls and network-based intrusion detection/prevention systems—covered in detail in Chapter 6—work to protect the entire network from malicious traffic. Host-based versions of these devices are usually software-based, installed on the host as an application. Their purpose is to filter traffic coming into the host from the network, based upon rules that inspect the traffic and make decisions about whether to allow or deny it into the host in accordance with those rules: • A host-based firewall, like the excellent Windows Defender Firewall, blocks unwanted access based on port numbers and other criteria. 05-ch05.indd 312 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-5: Securing Endpoints 313 • A host-based intrusion detection system (HIDS) serves to detect patterns of malicious traffic, such as those that may target certain protocols or services that appear to cause excessive amounts of traffic, or other types of intrusion. • A host-based intrusion prevention system (HIPS) actively scans incoming packets and blocks potentially harmful ones aggressively. Host-based firewalls, HIDS, and HIPS may be included in the operating system, but they can also be independent applications installed on the host. You should carefully configure them to allow into the host only the traffic necessary for the host to perform its function. You should also baseline them to the normal types of network traffic that the host may experience. You should update host-based firewalls/HIDS/HIPS with new attack signatures as needed and tune them occasionally as the network environment changes to ensure that they fulfill their role in protecting the host from malicious traffic, while permitting traffic the users need to do their jobs. Figure 5-34 shows a side-by-side example of Windows and Linux firewalls. NOTE In real-world implementations of host-based security measures, weigh the overall security posture of the device in question. Yes, you can lock down a resource completely, protecting it from attackers. But will this impede the effective use of that device? Balance is important. Figure 5-34 Comparison of Windows and Linux firewalls 05-ch05.indd 313 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 314 Disabling Open Ports and Services Almost every host runs services that it doesn’t need. In addition to wasting processing power and resources, a host that runs unnecessary services poses security risks. Services can be vulnerable to attacks for a variety of reasons, including unchecked privilege use, accessing sensitive resources, and so on. Adding unnecessary services to a host increases the vulnerabilities present on that host, widening the attack surface someone might use to launch an attack on the host. Disable any unnecessary services or open ports as a basic hardening principle. If you have a public-facing Web server, for example, don’t run any services that offer avenues of attack into the host or, worse, into the internal network. A public-facing Web server shouldn’t run e-mail, DHCP, DNS, and so on. Internal hosts have the same issues; workstations don’t need to run FTP servers or any other service that the user doesn’t explicitly need to perform his or her job functions. You should take the time to inventory all the different services that users, workstations, servers, and other devices need to perform their functions, and turn off any that aren’t required. Often, when a device is first installed, it runs many unnecessary services by default; often these do not get disabled. Administrators should disable or uninstall those services, or at least configure them to run more securely. This involves restricting any unnecessary access to resources on the host or network, as well as following the principle of least privilege and configuring those services to run with limited-privilege accounts. Application Security Often, security administrators identify software that is harmful to computers or the organization for various reasons. In some cases, software may contain malicious code; in other cases, the organization may want to allow the use of certain applications, such as chat programs, file sharing programs, and video games (Figure 5-35). You can restrict access to these applications in several different ways, one of which is blacklisting. Blacklisting (or Figure 5-35 But I need to play CounterStrike! During working hours? OK 05-ch05.indd 314 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-5: Securing Endpoints 315 configuring a block list/deny list) involves an administrator adding an undesirable piece of software or an application to a list on a content filtering device, in Active Directory group policy, or on another type of mechanism, so that users are not allowed to download, install, or execute these applications. This keeps certain applications off the host. Applications may be blacklisted by default until an administrator has decided on whether to allow them to be used on the host or the network. Whitelisting (or configuring an allow list) works similarly to blacklisting, except that a whitelist contains applications that are allowed on the network or that are okay to install and use on hosts. A whitelist would be useful in an environment where, by default, applications are not allowed unless approved by an administrator. This ensures that only certain applications can be installed and executed on the host. It also may help ensure that applications are denied by default until they are checked for malicious code or other undesirable characteristics before they are added to the whitelist. EXAM TIP On the CompTIA Security+ 601 exam, you might see the more neutral terms “block list/deny list” and “allow list” rather than the traditional terms “blacklisting” and “whitelisting.” CompTIA replaced the traditional terminology with the new terminology in version 2 of the 601 exam objectives. Applications and software can be restricted using several different criteria. You could restrict software based upon its publisher, whether you trust that publisher, or by file executable. You could also further restrict software by controlling whether certain file types can be executed or used on the host. You could use these criteria in a whitelist or a blacklist. Figure 5-36 shows an example of how Windows can do very basic whitelisting and blacklisting using different criteria in the security settings on the local machine. When using blacklisting in a larger infrastructure—using Active Directory, for example—you have many more options to choose from. Open Permissions Most operating systems and devices default these days to requiring at least some minimal form of identification and authentication at login. Windows 10, for example, makes it very difficult to set up an account with no password requirement. Earlier versions of Windows weren’t quite as strict, so people who wanted no-frills logins left their systems open to easy attacks. About the only places you’ll find open permissions are kiosks at conventions and trade shows that enable users to access the Internet easily. As you should also know, don’t use those systems to access any systems that require any personal account information. Don’t log into Facebook from the trade show floor, in other words! EXAM TIP For the CompTIA Security+ exam, keep in mind that open permissions equates to no security at all for any accessible system. 05-ch05.indd 315 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 316 Figure 5-36 Application control in Windows Disabling Default Accounts/Passwords Out-of-the-box, operating systems often include default accounts with blank passwords or passwords that don’t meet the organization’s complexity requirements. Some of these default accounts may not even be necessary for the normal day-to-day operation of the host. A good example of such an account is the Windows default guest account (disabled by default in Windows 10). Linux operating systems are also vulnerable to this issue. A default Linux installation includes many accounts, all of which you should examine to determine whether they are necessary for the day-to-day operation of the host, and then disable or delete any that aren’t necessary. EXAM TIP Expect a question or two on the CompTIA Security+ exam that explores default settings or default accounts as examples of vulnerabilities caused by weak configurations. Some operating systems enable setup with unsecure root accounts, such as a local administrator with no password, which, as you should suspect, would be a bad thing! Patch Management Operating system vendors release patches and security updates to address issues such as unforeseen vulnerabilities. For the most part today, operating systems auto-update, meaning they seek out and download patches from their manufacturers automatically, 05-ch05.indd 316 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-5: Securing Endpoints 317 although in some cases this must be done manually. This process is called patch management. In a home environment, it’s probably okay for hosts to download and install patches automatically on a regular basis. In an enterprise environment, however, a more formalized patch management process should be in place that closely relates to configuration and change management. EXAM TIP Legacy platforms, such as Windows 7 don’t get security updates. No patches equates to increasing vulnerabilities, because bad guys like to keep looking for them. Do yourself and your users a solid and move away from legacy platforms as quickly as you can. In a robust patch management process, administrators review patches for their applicability in the enterprise environment before installing them. Admins should research a new patch or update to discover what functionality it fixes or what security vulnerabilities it addresses. Admins should then look at the hosts in their environment to see if the patch applies to any of them. If they determine that the patch is needed, they should install it on test systems first to see if it causes issues with security or functionality. If it does cause significant issues, the organization may have to determine whether it will accept the risk of breaking functionality or security by installing the new patch, or will accept the risk incurred by not installing the patch and correcting any problems or issues the patch is intended to solve. If there are no significant issues, then the admins should follow the organization’s formal procedure or process for installing the patch on the systems within the environment. Typically, this is done automatically through centralized patch management tools (software), but in some cases, manual intervention may be required and the admins may have to install the patch individually on each host in the enterprise. In addition, admins should run a vulnerability scanner on the host both before and after installing the patch to ensure that it addresses the problem as intended. They also should document patches installed on production systems, so that if there is a problem that they don’t notice immediately, they can check the patch installation process to determine if the patch was a factor in the issue. EXAM TIP Improper or weak patch management can lead to vulnerabilities that bad people can and will exploit. IT managers should update everything properly, including firmware, operating systems (OS), and applications. That includes third-party updates as well, especially any custom software applications or utilities used by the organization. Anti-malware Anti-malware has come a long way from the early antivirus programs we used back in the 1990s. These first tools were drive scanners, using signatures to look for known viruses and doing their best to clean them out of systems. As time progressed, more features came online such as e-mail scanners, HTTP scanners, and RAM scanners. It wasn’t uncommon for a single anti-malware tool to possess five or six different scanning types. 05-ch05.indd 317 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 318 EXAM TIP Look for exam questions specifically addressing the output from antivirus software. Just substitute anti-malware software and you’ll see the obvious answer. Today’s anti-malware tools include point scanners—often called real-time scanners— that provide real-time scanning of all incoming data, looking for malware signatures. Point scanners don’t care about the type of data. They look for malware signatures in e-mail and Web browsers. Whatever application you use, a good point scanner will find and stop the malware before it infects your system (Figure 5-37). Figure 5-37 Windows Defender detecting malware 05-ch05.indd 318 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-5: Securing Endpoints 319 Figure 5-38 DEP settings in Windows 10 Data Execution Prevention In the early 2000s, a series of worms attacked the Internet, infecting memory areas with buffer overflows and propagating themselves by attempting to contact random IP addresses. These worms were relatively easy to detect, but their ability to execute code in areas of memory normally used only for data storage proved to be a bit of a problem. To stop these types of attacks, Intel and AMD implemented a CPU feature called the No eXecute (NX) bit. All operating systems were updated to support the NX bit. In Microsoft Windows, NX bit support is called Data Execution Prevention (DEP). The generic term for this is executable space protection. I’ll use DEP in this explanation for ease of use (and what you might see on the CompTIA Security+ exam). EXAM TIP The CompTIA Security+ 601 objectives do not mention the NX bit or DEP, except to include the latter in the standard acronym list. It’s doubtful you’ll get tested on something that’s been an enabled standard for nearly two decades. DEP is on by default on every Windows operating system. Be aware that you can disable it in the system setup utility. Assuming DEP is enabled in firmware, there’s always a place to check it in your operating system. Figure 5-38 shows DEP in Windows 10. NOTE DEP should always be on, quietly protecting systems from buffer overflows. The need to turn off DEP is rare. File Integrity Monitors If malware is to be persistent, it must find a place to hide in mass storage. One popular strategy of malware is to create its own place to hide by replacing otherwise perfectly good files, both executable and data files, with refactored versions (Figure 5-39). 05-ch05.indd 319 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 320 I’m the real one! Figure 5-39 Which is the real one? WindowsCodecsRaw.dll I’m the real one! WindowsCodecsRaw.dll To defeat these bad actors, use a file integrity monitor as part of an anti-malware routine. As the name implies, a file integrity monitor makes sure the right files are in the right place. Most file integrity monitoring starts with a hash of the file itself, but may also add several other options: • • • • File date/time Version number (if executable) Digital signature Metadata (modify date) By recording these values at installation of the operating system or application, a file integrity checker can verify without a doubt that the files being checked are the right ones. NOTE See Chapter 8 for more details on fully featured file integrity monitoring (FIM) systems that scale up to handle enterprise networks. Data Loss Prevention If your data is precious, you might want to add some data loss prevention (DLP) tools to the individual servers storing that data. Most DLP solutions are designed not only to keep your data’s integrity at 100 percent but also to do several other jobs. Some DLP packages verify backups exist and are in good order. Some DLP packages monitor if data is being moved or copied (they call this data in transit/motion). Some DLP packages provide removable media control—called USB blocking—to prevent local copies being created. DLP works in all sorts of appliances, from enterprise routers to cloud-based services. You’ll find DLP employed in mail gateways, protecting e-mail messages and delivery. The mail gateway might employ DLP along with a spam filter to proactively delete known unsolicited messages and with encryption features for secure e-mail. (See also Chapter 11 for more discussion on secure protocols.) 05-ch05.indd 320 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-6: System Recycling 321 Figure 5-40 Shredded computers Module 5-6: System Recycling This module covers the following CompTIA Security+ objective: • 4.1 Given a scenario, use the appropriate tool to assess organizational security There comes a time when hard-working individual systems must say farewell. Technology becomes dated, upgrading is impossible or not cost-effective, feature sets are lacking, or a massive hardware failure (like a smoked motherboard) makes a repair simply not worth the cost in money and time. The process of disposing of systems is called system recycling. There are two different ways to recycle. First, take a complete system to a scrapper that shreds the system—plastic, metal, everything—and recycles the core materials (Figure 5-40). Alternatively, system recycling means to give the computer to someone else who needs it. Charitable organizations, schools, and private individuals badly need computers and will gratefully accept even somewhat dated systems. In either case, the great issue for IT professionals is to ensure that none of the data on the soon-to-be-recycled mass storage devices survives. This process, called data sanitization, takes on several forms and steps, but a handy publication that provides helpful guidance is NIST Special Publication (SP) 800-88 Revision 1, Guidelines for Media Sanitization (Figure 5-41). NIST SP 800-88 Rev. 1 breaks data sanitization into three main methods: clear, purge, and destroy. Each of these methods ensures the data on mass storage won’t leave the infrastructure, but the methods vary in terms of security, convenience, and cost. Clear Clear means to tell the device through user commands inherent to the mass storage device to sanitize the data. One example of a clear would be to send commands to a hard drive to erase data. Clearing isn’t, however, just a simple erase. It must eliminate data 05-ch05.indd 321 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 322 Figure 5-41 NIST SP 800-88, Revision 1 from the mass storage device in such a way as to ensure the data cannot be read again, even if forensic tools are used to try to recover the data. The biggest question marks when it comes to clearing mass storage are HDDs and SSDs. The built-in erase/delete, format, and partition commands from any operating system generally do not remove data. True removal requires disk wiping utilities that overwrite the data on the entire drive. Figure 5-42 shows the interface of a highly regarded clearing/wiping tool, Parted Magic (https://partedmagic.com). There’s an old wives’ tale that claims (depending on who you hear this story from) that you must overwrite data six or seven or nine times before the underlying data cannot be recovered forensically. In response to this, SP 800-88 Rev. 1 says the following: For storage devices containing magnetic media, a single overwrite pass with a fixed pattern such as binary zeros typically hinders recovery of data even if state of the art laboratory techniques are applied to attempt to retrieve the data. For the overly paranoid, or for those whose employers require you to be so, however, the US Department of Defense wiping standard, DoD 5220.22-M, performs many overwrites. It should be noted that even the US DoD no longer requires this standard for data sanitization. 05-ch05.indd 322 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Module 5-6: System Recycling 323 Figure 5-42 Parted Magic NOTE A general rule on clear: if the device is an appliance (a router, a smartphone, a multipurpose printer), a factory reset will often sufficiently clear the device. This isn’t a guarantee, and it’s always a good idea to refer to the manufacturer directly. Purge Purge means to use anything other than an internal command to sanitize the data on the media. Probably the best example of purging is degaussing magnetic media. Degaussing means to expose the media to very powerful magnetic fields. Degaussing is 100 percent effective on HDDs, but is useless with SDDs as they do not store data magnetically. Degaussing machines are expensive, so most organizations that need to degauss take advantage of third-party solutions. Figure 5-43 shows the Web page of a company that specializes in data destruction, including degaussing. Figure 5-43 Data Killers degaussing service Web page 05-ch05.indd 323 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 324 Unfortunately, degaussing also destroys the media. Once an HDD is degaussed, the drive is destroyed. But not all purging is destructive. One potential alternative that might be available is cryptographic erase (CE). If by chance you have something on mass storage that is encrypted with an asymmetric key, you can render the data undecipherable by eliminating the key pair, or at least the public key. Destroy Destroy quite literally means the physical destruction of the media. Secure data destruction methods depend on the media, but here are the four common techniques. • Burning Flammable media isn’t as common as it used to be, but burning is still available for disks and tapes. • Pulping Exclusively for paper, pulping dissolves and cooks the paper, creating new paper. • Shredding Shredding means two different things. You can use shredders to chop up paper (or cards or tapes or optical media) into tiny pieces. If you’re talking about hard drives, the proper term is pulverizing (see next). • Pulverizing Pulverizing mechanically rips apart the media or data storage. There are some excellent YouTube videos on this topic—assuming you like watching hard drives shredded into thousands of tiny pieces! Questions 1. Rick logs into a public system as Guest and guesses correctly on a simple password to gain administrative access to the machine. What sort of attack surface does this represent? A. Angle plane B. Privilege escalation C. Service vector D. Zero-day 2. John receives a driver-signing error for a specific DLL file in his Windows system. This a classic symptom of what sort of attack? A. ARP poisoning B. MAC spoofing C. Refactoring D. Shimming 3. Samantha recommended new systems for a group of developers at remote locations. Each system is identical, with high-end processing components. For storage, she needs a solution that provides storage redundancy and performance. 05-ch05.indd 324 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Questions 325 She goes with RAID for each system, selecting four drives. Each user can lose up to two drives and not lose data. What RAID did she select? A. RAID 0 B. RAID 1 C. RAID 5 D. RAID 6 4. The Trusted Computing Group introduced the idea of the __________, an integrated circuit chip that enables secure computing. A. TCP B. TPM C. EMP D. EMI 5. John’s home system has automatic updates from Microsoft, yet at his office, his organization has a more formal method of updating systems called __________. A. Automatic updates B. Patch management C. TOS D. Allow listing 6. What sort of malware requires the user to pay to remove the malware? A. Trojan horse B. Keylogger C. Adware D. Ransomware 7. Marisol notices a small dongle between her USB keyboard and her system. Which of the following is most likely? A. She is using an inline encryption device. B. She has a TPM. C. Someone has installed a keylogger. D. Someone has installed a logic bomb. 8. Degaussing is associated with which form of data sanitization? A. Clear B. Purge C. Destroy D. Recycle 05-ch05.indd 325 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 5 Chapter 5: Securing Individual Systems 326 9. Jake gets a call from a user complaining about things seeming “squished” on the screen. Upon further review, Jake determines that the Edge browser on the user’s laptop has a lot of nonstandard toolbars taking up part of the screen, thus making it harder to see Web pages and images at agreeable sizes. What sort of malware has infected the user’s computer? A. PUP B. Ransomware C. Trojan horse D. Worm 10. Erin needs to implement a solution to provide redundancy of network connections for a critical server. What should she implement? A. Multipath B. NIC teaming C. RAID D. Virtualization Answers 1. B. Privilege escalation scenarios have the bad guy increasing the scope of what he can do once authenticated to a system. 2. C. A refactoring attack tries to replace a device driver with a file that will add some sort of malicious payload. 3. D. A RAID 6 array requires at least four drives, but can lose up to two drives and still not lose data. 4. B. Trusted Platform Module (TPM) chips store a unique 2048-bit RSA key pair for security purposes. 5. B. Patch management describes the process used to keep systems updated in the enterprise. 6. D. Ransomware demands payment to restore files. 7. C. A random USB dongle can be a malicious device, such as a keylogger. 8. B. Although a degausser essentially renders a hard drive unusable, it falls into the category of purge. 9. A. Jake’s user clearly has one or more potentially undesirable programs installed! 10. B. Erin should install and configure a second network interface connection in NIC teaming to provide redundancy of network connection. 05-ch05.indd 326 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 CHAPTER The Basic LAN 6 Mesh, smesh. Just point me to the bus. —Anonymous Luddite Most computing devices interact within a TCP/IP broadcast domain, a local area network (LAN), a crazy mélange of devices, from PCs to printers to smartphones to switches to thermostats to refrigerators. Securing each computing device requires attention and specific tools and technologies, as you learned in Chapter 5. Networks bring an extra layer of complexity and attack surfaces and, as you undoubtedly suspect, a whole new set of tools for security. This chapter explores securing a LAN in five modules: • • • • • Layer 2 LAN Attacks Organizing LANs Implementing Secure Network Designs Virtual Private Networks Network-Based Intrusion Detection/Prevention Module 6-1: Layer 2 LAN Attacks This module covers the following CompTIA Security+ objective: • 1.4 Given a scenario, analyze potential indicators associated with network attacks LANs offer great attack surfaces. This module explores Layer 2 (Data Link in the OSI seven-layer model) attacks, such as ARP poisoning, on-path attacks, MAC flooding, and MAC cloning. Why worry about Layer 3, Layer 4, or even Layer 7 for that matter, when you can attack way down the network stack? Let’s check them out. NOTE That question was a joke and a segue. Security professionals definitely need to worry about attack surfaces up and down the OSI layers. We’ll get to other attacks shortly. 327 06-ch06.indd 327 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 328 ARP Poisoning Most every network in existence is Ethernet, and every network interface card (NIC) on an Ethernet network has a media access control (MAC) address. For one computer to send an IP packet to another computer on an Ethernet network, the IP packet must sit inside an Ethernet frame. An Ethernet frame consists of both a destination MAC address and a source MAC address. The sending system needs both the destination host’s IP address and the destination host’s MAC address. But what if the sending system knows the destination IP address but doesn’t know the destination MAC address? In that case the sending system performs an Address Resolution Protocol (ARP) broadcast to determine the MAC address for that host. Typically, when a system wants to send an IP packet, it broadcasts an ARP request that looks something like Figure 6-1. The system then caches the ARP discovery for a minute or two. In Windows you can type the arp -a command at the command line to see the cached ARP addresses. In the following example, dynamic addresses are the temporary addresses that must be renewed with new ARP commands every few minutes. Static addresses are permanent and do not require new ARP updates. C:\Users\Michaelm>arp -a Interface: 172.18.13.117 --- 0x10 Internet Address Physical Address 172.18.13.1 d4-b2-7a-03-26-4d 172.18.13.102 a8-a1-59-06-08-82 172.18.13.107 16-07-f2-c0-44-89 172.18.13.255 ff-ff-ff-ff-ff-ff 224.0.0.22 01-00-5e-00-00-16 224.0.0.251 01-00-5e-00-00-fb 224.0.0.252 01-00-5e-00-00-fc 239.255.255.250 01-00-5e-7f-ff-fa 255.255.255.255 ff-ff-ff-ff-ff-ff Type dynamic dynamic dynamic static static static static static static Hi 192.168.4.33! I’m 192.168.4.2. 192.168.4.2 Who has IP address 192.168.4.2? Tell 192.168.4.33. 192.168.4.231 192.168.4.59 Figure 6-1 Typical ARP request 06-ch06.indd 328 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-1: Layer 2 LAN Attacks 329 I’m a bridge to 192.168.4.5! My MAC is DD-EE-FF-11-22-33. But… but… but! 192.168.4.11 Who has 192.168.4.5? Tell me (192.168.4.33). 192.168.4.5 192.168.4.35 Figure 6-2 ARP spoofing in action Note that most of the 172.18.13.x addresses in this example are other systems on the network that use dynamic IP addressing. The broadcast addresses 172.18.13.255 and 255.255.255.255 are static. Most of the other addresses are for multicast addresses. So ARP’s job is to resolve MAC addresses based on IP addresses using systems that broadcast requests and then update their ARP caches with the responses from other computers. But ARP has no security. Any computer can respond to an ARP request, even if that computer is an evil actor (Figure 6-2). Any time an attacking system pretends to be another system in any way—by faking an IP address, a URL, or an e-mail address—it is spoofing. A system that responds with another system’s MAC address via ARP requests is ARP spoofing. On the other hand, if some system gives false ARP information to another system, this poisons the victim system’s ARP cache. The attacking system performs ARP poisoning. Figure 6-3 explores the differences. Figure 6-3 ARP spoofing vs. ARP poisoning 06-ch06.indd 329 I fake other systems' MAC addresses so I’m spoofing. My spoofing puts false information on other systems' ARP caches so I’m ARP cache poisoning. 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 330 Figure 6-4 Switch MAC table MAC Table Port 1 - 00-98-BA-2D-C2-AA Port 2 - 02-1A-34-D2-8C-25 Port 3- Empty Port 4- Empty Port 5- 7D-88-01-BB-AC-43 Port 6- Empty Port 7- 14-dd-a9-9b-03-90 Port 8- Empty 12345 67 8 Router ARP poisoning doesn’t stop with a single attacking system going after another system’s ARP cache! Remember that every LAN has a Layer 2 switch that interconnects all the LAN devices. This switch keeps a listing of the MAC addresses to all connected systems (Figure 6-4). An ARP poisoning program can confuse the switch by sending ARP commands directly to the switch, redirecting traffic to the attacking system. In Figure 6-5, the attacker impersonates a legitimate system. ARP poisoning software can send false ARP commands. What havoc can this provoke? Two common types of attack use ARP spoofing/ARP poisoning: man-in-themiddle attacks and MAC flooding. Man-in-the-Middle Attacks Let’s assume that you, the evil actor, have used your “Mission: Impossible” skills and infiltrated an office. You’re sitting next to an RJ-45 connection on the target LAN. Your goal, should you choose to go further, is to get user J. Bond’s user names and passwords for, well, just about everything he does online. To intercept his Web activity, for example, you set up an ARP poisoner to tell the switch that the ARP poisoner is now the router, thereby fooling the switch to send all the data from J. Bond’s system directly to your system. You don’t want J. Bond to get wise to you, so after all of his data comes into your system, you keep a copy but at the same time make sure the traffic goes on to the router and does whatever he wanted it to do. Your ARP poisoning system is now in the middle between J. Bond’s computer and the Web server he is trying to connect to (Figure 6-6). You have now created a classic man-in-the-middle (MITM) attack! Excellent work, evil actor! Muwhawhawhaw! 06-ch06.indd 330 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-1: Layer 2 LAN Attacks 331 Hey switch ! I am MAC address 00-98-BA-2D-C2-AA. MAC Table Port 1 - 00-98-BA-2D-C2-AA Port 2 - 02-1A-34-D2-8C-25 Port 3- Empty Port 4- Empty Port 5- 7D-88-01-BB-AC-43 Port 6- Empty Port 7- 14-dd-a9-9b-03-90 Port 8- Empty 12345 67 8 Router What the heck? Figure 6-5 ARP poisoning the switch NOTE Apologies to the reader here. The primary author of this chapter— not naming names, but his initials are MM—can’t keep his movie franchises straight, not even for one million dollars. – SJ I see EVERYTHING!!! J. Bond’s System Evil System Web Server Figure 6-6 MITM J. Bond’s system 06-ch06.indd 331 25/03/21 2:15 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 332 You should note two items here. First, this isn’t the only way to do an MITM attack. This scenario uses ARP poisoning to create an MITM attack. There are hundreds, if not thousands, of ways to execute MITM attacks. Any form of attack that places something between two systems for the job of acquiring data is an MITM attack. You could do an MITM attack by setting up a fake e-mail server and stealing someone’s e-mail. You could do an MITM attack by setting up a rogue WAP and tricking users into connecting to it. EXAM TIP The CompTIA Security+ 601 exam objectives refer to an MITM attack as a form of on-path attack. This is a more general term that can apply to any sophisticated attack where you insert something on the path between a legitimate system and a trusted resource. You might see the term “on-path attack” on the exam, but will definitely see “man-in-the-middle” in the field for the foreseeable future. The other type of on-path attack discussed in this book is a man-in-thebrowser (MITB) attack. As the name implies, it’s essentially an MITM attack directed at Web browsers. We’ll get to it in Chapter 11. MAC Flooding Switches filter traffic based on MAC addresses, very quickly establishing and maintaining a table—called a content addressable memory (CAM) table—that contains all the MAC addresses of the hosts connected to it. Traffic goes into the switch and then only to the specific recipient listed in the frame (Figure 6-7). If a switch does not know the intended MAC Table Port 1 - Empty Port 2 - 02-1A-34-D2-8C-25 Port 3- Empty Port 4- Empty Port 5- 7D-88-01-BB-AC-43 Port 6- Empty Port 7- 14-dd-a9-9b-03-90 Port 8- Empty 12345 67 8 Computer A I can’t see what Computers A and B are saying to each other! Computer C Computer B Figure 6-7 A properly running switch 06-ch06.indd 332 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-1: Layer 2 LAN Attacks 333 MAC Table Port 1 - Empty Port 2 - 02-1A-34-D2-8C-25 Port 3- Empty Port 4- Empty Port 5- My 7D-88-01BB-AC-43 MAC table is Port 6- Empty invalid so... Port 7- 14-dd-a9-9b-03-90 HUB MODE!!! Port 3- Empty I see all the traffic! 12345 67 8 Computer C Computer A Computer B Figure 6-8 MAC flooding recipient of a frame, the switch will broadcast that frame to all the connected devices, behaving much like an ancient hub. This is typical during the initial connection of a new device to the network, for example, until the switch’s CAM table updates. Attackers can take advantage of this aspect of switches through media access control (MAC) flooding attacks, sending many frames with “new” source MAC addresses, seeking to overwhelm the limited capacity of the CAM table (Figure 6-8). Using an ARP poisoner, for example, an attacker can broadcast hundreds of invalid ARP commands every few seconds. Once filled, the switch will flip to broadcast mode for LAN traffic. Not only does MAC flooding force switches to broadcast all traffic, it’s also a great way to open up an ARP poisoning attack. Once the switch goes into “hub mode” (my term, not an industry term), it will quickly send out a flurry of ARPs to try to rebuild the CAM table. This is a terrific opportunity for an ARP poisoner to send ARPs that tell the switch it is another system. MAC Cloning An attacker can use MAC cloning—changing the MAC address of a device to match the MAC address of another device—to gain illicit access to the network. MAC cloning is a legitimate and fairly common action. Figure 6-9 shows how to change the MAC address of a NIC in Windows using the NIC’s properties. Unlike ARP poisoning, MAC cloning is a permanent setting. The trick to making MAC cloning work as an attack is to remove or disable the device that originally had the MAC address. You can’t have two devices with the same MAC address on a LAN for more than a few moments, as that will confuse the switch as well as other systems and will force a huge number of new ARPs as the network tries to figure out what’s happening. 06-ch06.indd 333 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 334 Figure 6-9 Changing the MAC address in Windows Many switches use a scheme called port security to protect against MAC cloning attacks. One of the more important features of port security is maintaining an inventory of every MAC address of allowed systems on the switch. Better switches do not allow a system with a MAC address that isn’t listed in the MAC address inventory to access the network. They literally turn off the port where the offending system connects. Attackers will attempt to avoid this by using a system with a known MAC address. NOTE MAC cloning has legitimate uses as well. It’s common to change the MAC address of a small office/home office (SOHO) router issued by an ISP to the MAC address of the previous router to speed up installation of the new router. Wireless access points commonly have a MAC setting that functions similarly to port security. The WAP stops systems that aren’t “on the list” from authorizing to the SSID. Module 6-2: Organizing LANs This module covers the following CompTIA Security+ objectives: • • • • 06-ch06.indd 334 2.1 Explain the importance of security concepts in an enterprise environment 2.5 Given a scenario, implement cybersecurity resilience 2.7 Explain the importance of physical security controls 3.3 Given a scenario, implement secure network designs 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-2: Organizing LANs 335 Figure 6-10 This is more than a CompTIA Network+ review. I can haz netwerking? Goodness, no! We’re going way beyond CompTIA Network+ here! This module reviews local area network (LAN) technologies, including devices, architectures, and secure networking principles. Although the book has already briefly discussed secure network protocols, this section takes an in-depth look at network security, discussing network devices and how to configure them securely, the design elements that go into a secure network, and different security methods and technologies that help make up secure network administration. Network security is an extremely important part of security in general, so reach back into your mind for all the knowledge and experience you’ve gained from CompTIA Network+ studies, as well as real-life experience. Also understand that this module is not a CompTIA Network+ exam review, although it discusses topics that may serve as a reminder of those studies. This module focuses on the security aspects of networking (Figure 6-10). We’ll specifically touch on three aspects of secure network design here: configuration management, network segmentation, and load balancing. Configuration Management Configuration management (CM) in general refers to how an organization keeps track of everything that affects its network, including the hardware in place, operating system versions and ordering, policies implemented, physical placement and layout of systems, and much more. CM directly relates to disaster recovery, which we’ll cover in more detail in Chapter 13. If you know precisely the systems and software in place, you can more effectively deal with breaches, failures, software glitches, and so on. This module touches on a few specific examples to include in the detailed documentation required for good CM, such as diagrams, standard naming conventions, IP schema, and baseline configuration. Just keep in mind that the topic goes way beyond CompTIA Security+ and into enterprise networking design, administration, and security. NOTE Other, more specialized certifications test much more deeply on CM topics, such as the ITIL certification from AXELOS. 06-ch06.indd 335 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 336 Diagrams Thorough and detailed diagrams map out the physical hardware of the network, including connectivity among devices, make and model of devices, operating system and version, firmware version, and so on. Network diagrams should function in layers, similar to the classic anatomy books with simple bones, arteries, organs, and more all on colored transparencies (Figure 6-11). Figures 6-12 and 6-13 show simple and more complex diagrams of the same network. NOTE When it comes to network diagrams, learn Microsoft Visio, the industry-standard tool. Get it as soon as you can and start practicing. Standard Naming Conventions All documentation should use standard naming conventions—standard for your organization, at least—so network administrators and security professionals can glance at something labeled FS3-E4 and differentiate it from FS3-W7 easily. (C’mon, file server 3 on floor 4 in the East building in the campus area network versus file server 3 on floor 7 in the West building, right?) This standardization applies to every network asset, including system identification and network IDs. Standard naming conventions enable new team members to get up to speed quickly and avoid rookie mistakes that would cause problems for the organization. Figure 6-11 Classic anatomy overlay (Image: ilbusca, Getty Images) 06-ch06.indd 336 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-2: Organizing LANs 337 BWC CAN 802.11ac Server IDF 10 Gigabit w/Access Switch Gigabit Cat 6a Main Office IDF Gigabit Cat 6a SCADA Gigabit Cat 6a 802.11ac Gigabit Cat 6a Gigabit Cat 6a 10 Gigabit w/Access Switch 10 Gigabit w/Access Switch IDF Warehouse and Shipping Gigabit Cat 6a Gigabit Cat 6a Gigabit Cat 6a Gigabit Cat 6a Gigabit Cat 6a Factory Gigabit Cat 6a Gigabit Cat 6a Gigabit Cat 6a Gigabit Cat 6a 802.11ac Figure 6-12 Diagram of the Bayland Widgets’ campus area network Main Office server room Utility Room 402 Manager: Mike Meyers (812)555-8160 (text) Top: File Server Dell PowerEdge R450 00:C0:4F:22:08:01 11.12.13.10 Cent: Main Switch Dell EMC Powerswitch N2924 11.12.13.2 Lower: UPS Dell DLT 1800 00:C0:4F:49:90:AD 11.12.13.11 Figure 6-13 Closeup with details of the Bayland Widgets’ campus area network 06-ch06.indd 337 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 338 IP Schema Part of good configuration management means implementing IPv4 addresses in a logical and consistent manner—the Internet Protocol (IP) schema. In one common IP schema, for example, the main router is set to x.x.x.1. Switches get range x.x.x.2–10, printers get range x.x.x.11–16, and workstations get all the rest. Most networks organize the first or last useable address in their subnet for the default gateway. Consistency and explicit documentation are the keys here. Baseline Configuration Once you have the network set up, run tests to determine the baseline performance of the network based on the baseline configuration you’ve implemented. In other words, CM means knowing how each part of the network should perform so it becomes rapidly apparent when something doesn’t perform as expected. We’ll see more about baselining in Chapter 13, but keep it in your head that it’s an integral part of effective configuration management. Network Segmentation A good, secure network architecture organizes components into physical or logical groupings, enabling better security for the enterprise. Network segmentation generally means partitioning a single enterprise network into two or more subnetworks using either switches (at Layer 2) or routers (at Layer 3). Layer 2 switches use VLAN capabilities to turn single broadcast domains into multiple broadcast domains. Layer 3 routers split the enterprise into separate network IDs. Network-based firewalls work at this level; we can also implement screened subnets. This splitting either at Layer 2 or Layer 3 for different functions of the network gives us tremendous control over the data moving among systems and enables us to address security in many different ways. Network segmentation also refers to separating the enterprise network both within (to reduce overhead and general traffic) and without (connecting to an ISP or some other organization’s network). We’ll glance briefly at the terminology and documentation that refers to these other connectivity points. EXAM TIP The CompTIA Security+ objectives list Zero Trust under network segmentation. Zero Trust operates on the principle of “never trust, always verify,” which means exclude any traffic from anyone until you can prove that traffic is legitimate. Zero Trust uses network segmentation as some of the methods for excluding traffic. Typical implementations of Zero Trust also operate at Layer 7, so they don’t really fit the classic network segmentation models of Layers 2 and 3. You’ll see the term again in Module 6-3 under “Internet Connection Firewalls.” Keep in mind the concept as it relates to network segmentation, though, so you can properly parse questions on the CompTIA Security+ exam. 06-ch06.indd 338 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-2: Organizing LANs 339 VLANs You know that the defining characteristics of a LAN are that hosts are on the same subnet; that they communicate with each other without the need to be routed; and that they use hardware (MAC) addresses to identify each other during communications. Better switches can segment a network logically into two or more distinct and separate networks by implementing virtual local area network (VLAN) technology. A VLAN doesn’t depend upon the physical layout of the network; it doesn’t matter if the hosts are physically sitting next to each other or are located several buildings apart. A VLAN creates a logical network in which to assign hosts. Once a host is assigned to a VLAN, it follows LAN conventions, as if it were physically a part of a LAN. You create VLANs on switches by configuring the switches to establish and recognize VLANs with certain characteristics. These characteristics include an IP subnet and VLAN membership. VLAN membership can be based on the switch port the host is plugged into (called a port-based VLAN); it can also be based on the MAC address of the client (a MAC-based VLAN). You could also have a protocol-based VLAN, which would ensure that any client with an IP address on a subnet would be assigned to a VLAN by default. You can assign different hosts to different VLANs, even if they plug into the same switch and sit right next to each other. EXAM TIP Implementation of VLANs falls squarely in the CompTIA Network+ certification bailiwick. CompTIA Security+ cares that you know VLANs enhance network security through network segmentation. Since VLANs operate with the same characteristics as normal LANs, broadcasts are not passed between them. In fact, it’s necessary to route traffic between VLANs. You could use a traditional router for this, or, more often, you could configure the switch to route between VLANs (called inter-VLAN routing). If VLANs need to access networks that aren’t controlled by the switch, the traffic must pass through a traditional router. Figure 6-14 illustrates an example VLAN setup. VLANs contribute to security because they enable administrators to separate hosts from each other, usually based upon sensitivity. In other words, you can assign sensitive hosts to a VLAN and control which other hosts access them through the VLAN. Since VLANs are logical (and software-based), you can control other aspects of them from a security perspective. You can control what types of traffic can enter or exit the VLAN, and you can restrict access to hosts on that VLAN via a single policy. You can also provide for increased network performance by using VLANs to eliminate broadcast domains, the same as you would with a traditional router. Network-Based Firewalls A network-based firewall, like the host-based firewall discussed in Chapter 5, filters IP traffic based on rulesets known generically as access control lists (ACLs). A networkbased firewall manifests as a specialized hardware device (commonly but not exclusively a router), a type of network appliance. 06-ch06.indd 339 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 340 Layer 3 Switch Figure 6-14 VLANs on a switch VLAN 3 172.16.30.0 VLAN 1 192.168.10.0 VLAN 2 172.29.20.0 NOTE Given that routers interconnect LANs, adding firewall features to a router is a natural combination. Network-based firewalls typically protect entire network segments. Traditionally, firewalls were thought of in terms of separating only public networks from private networks; but modern security theory also emphasizes the use of firewalls in an internal network to separate sensitive network segments from other internal networks. Firewalls can filter traffic based upon a wide variety of criteria, including port, protocol, network service, time of day, source or destination host, and even users or entire domains. More advanced firewalls can also do deep-level traffic inspection, so even traffic that meets rules allowing it to pass through the firewall could be denied due to the content of its traffic. NOTE Module 6-3 goes into specific types of network-based firewalls. Screened Subnets The best way to connect a LAN to the Internet is to use a firewall-capable router to act as the interconnect between the LAN and an ISP. While simple LANs handle this nicely, a network that includes public servers must have a more complex topology that protects Internet systems but still enables less-protected access for public servers. To do this, create a screened subnet—also known as a demilitarized zone (DMZ)—a LAN, separate from the 06-ch06.indd 340 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-2: Organizing LANs 341 LAN DMZ To the Internet Router Router Web Server Whatever Server Game Server Figure 6-15 A screened subnet (DMZ) internal LANs that contain workstations and private servers. The DMZ connects to the Internet via a lightly firewalled router, and an internal network connects to the DMZ via a much more aggressively firewalled router (Figure 6-15). EXAM TIP The third iteration of the CompTIA Security+ 601 objectives changed the traditional term “demilitarized zone (DMZ)” to “screened subnet.” You might see the latter term on the exam, so don’t miss the question. You’ll only see DMZ in the real world for the next few years— assuming the politically correct term catches on at all, so be prepared for that as well. A lot of modern networks that employ a screened subnet use a specialized network appliance called a jump server that enables secure management of devices within the DMZ. The typical jump server enables logging and auditing and provides a single management point for user accounts. Interconnecting Within and Without Even relatively simple enterprise networks—like the Bayland Widgets’ CAN illustrated earlier in this module—have multiple connections among servers within the network and, of course, connections to the outside world as well. Internal server-to-server communication can add a lot of overhead to a network if not managed properly. Proper network segmentation can reduce overall traffic by putting a server-to-server connection in a unique VLAN, for example, or separating the servers with routers. 06-ch06.indd 341 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 342 The network documentation folks have long called the internal server-to-server connection east-west traffic, not because of any geographic necessities, but because the network diagrams tend to show them as horizontal connections. A network using VLANs or routers that’s essentially a single enterprise network is called an intranet. A private TCP/IP network that provides external entities (customers, vendors, etc.) access to their intranet is called an extranet. The biggest TCP/IP network of all, the one we all know and love, is called the Internet. And just for completeness here, connections between an enterprise network and an external network, such as an ISP, are generally drawn in diagrams as a vertical connection. Can you guess what term describes this connection? That’s right, north-south traffic. Load Balancing A load balancer is a network device used to provide efficient and seamless workload sharing between network devices (such as routers or firewalls) or hosts, typically Web or file servers or storage devices. Placed strategically between devices, a load balancer enhances security and efficiency. You can also purchase network devices with native load balancing capability allowing the same functionality with a paired device, but the implementation is more complicated. As you might suspect from the name, load balancers provide load balancing to the network. Implement load balancers in a scenario where you need to enhance cybersecurity resilience. High-Availability Clusters A load balancer contributes to security by providing for high availability. If a server goes down, the load balancer can transparently and immediately provide for availability by transferring network and resource requests to an identically configured backup server. This is considered persistence in networking, meaning the network resources are always available. An active/passive high-availability cluster like this has one server active and the second passive, acting as a failover or backup. NOTE A cluster in this use is a group of servers that work together to provide a service, such as a Web site, Web service, or database. In an active/active high-availability cluster, the load-balanced services perform the same functions at the same time, but with different transactions. As an example, two load-balanced Web servers would respond to different users’ browser requests. The load balancer manages the traffic and requests going to each of the members of the service or device cluster for which it is responsible. This helps provide for efficiency, eliminates delays or latency, and provides for system and data availability if a member of the cluster is unable to fulfill requests or requires maintenance. Scheduling Load balancers may use several different criteria to determine scheduling—that is, which device gets a particular request. A load balancer may base its decisions on network traffic 06-ch06.indd 342 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 343 conditions, for example; it may use a turn-based system (otherwise known as a roundrobin type of system); or it can send traffic based on available resources on the target systems in more advanced products. It is important to note that Web sites and applications need to maintain session affinity across load-balanced resources. If there are two Web servers behind a load balancer and a user’s initial session is sent to Web server A, for example, the affinity between that user and the application thread active on Web server A must be maintained. Otherwise, the user’s experience on the Web site would not be consistent—Web server A would have some of the information and Web server B would have other parts, resulting in a useless session, broken shopping cart, and so on. A load balancer receives traffic for other devices or services via a virtual IP address. In a simple application, one Web server would receive and process all user sessions. In the preceding Web site example, both Web servers have individual IP addresses and both need to receive and process network traffic. To enable this, all the traffic is sent to a virtual IP address that is hosted on the load balancer, which forwards the relevant traffic to each resource behind it. This address is labeled “virtual” because it only exists for the purpose of routing traffic, and it is assigned to a device that already has a hardware-relevant IP address. A load balancer in an enterprise environment could host hundreds of virtual IP addresses for different applications. EXAM TIP The use of virtualization—with virtual servers and systems— requires the same high degree of diligence with security as is required for physical machines and networks. The concepts and implementations of segmentation and isolation apply to virtualized networks just as much as to physical networks. Module 6-3: Implementing Secure Network Designs This module covers the following CompTIA Security+ objectives: • 2.1 Explain the importance of security concepts in an enterprise environment • 3.2 Given a scenario, implement host or application security solutions • 3.3 Given a scenario, implement secure network designs NOTE Wireless networks also need security and are an important part of just about every network out there. Wireless security gets its own discussion in Chapter 7. Securing the LAN To have a LAN you must have at least one switch. A perfectly functional LAN consists of nothing more than a single host and a single dumb switch, although in all but the smallest LANs you’ll usually see two or more managed switches, creating the broadcast domain that defines a LAN. Most installations use rack-mounted switches with professionally installed structured cabling (Figure 6-16). 06-ch06.indd 343 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 344 Figure 6-16 Switches in a rack Structured Cabling Switches Servers Traditionally, a switch filters and forwards Ethernet frames, memorizing the MAC addresses of all the connected hosts and then creating point-to-point connections for all unicast traffic while at the same time remaining completely capable of supporting broadcasts. EXAM TIP The CompTIA Security+ objectives remind readers of an important secure network design and implementation tip, securely accessing servers for configuration. Typically, we access servers through in-band management software, such as VNC or SSH. The server operating system and software enable that access. With out-of-band management, in contrast, the network administrator can access the server even if the server isn’t running, directly interfacing with the firmware of the server. You might recall a common out-of-band management feature from your CompTIA Network+ studies, lights-out management (LOM). Expect a question on secure network design that features out-of-band management. Port Security Bad actors love access to a network’s switch. Access to a switch opens vulnerabilities to attacks. ARP spoofers steal the MAC addresses of legitimate systems, enabling man-inthe-middle/on-path attacks. Denial-of-service attacks can flood a switch with confusing 06-ch06.indd 344 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 345 I’m one plug away from totally nailing your network. Sweet! Figure 6-17 Just give me one port, just one… MAC information. An attacker can plug in a rogue DHCP server, knocking systems off the network. They can start sending out IPv6 neighbor discovery packets, telling the hosts that the attacking system is their gateway and redirecting traffic (Figure 6-17). Switch ports require security to protect against these attacks. Flood guards and loop prevention are a few of the features you’ll see in all better switches. Keep in mind that port security is applied to individual ports. Broadcast Storm Prevention Attackers use traffic floods primarily to conduct denialof-service attacks on networks and hosts, since many hosts and network devices don’t always react very favorably to excessive amounts of traffic or malformed traffic. Because flooding is a routine tactic of attackers, most modern network devices (and even some hosts) have flood protection built into their operating systems. These flood guards or broadcast storm prevention features work by detecting excessive traffic (by volume, as well as by rate of speed) and take steps to block the traffic or even turn off the offending port, so that the host doesn’t have to process it. Most security devices, such as intrusion detection systems, firewalls, and robust network devices like better switches, have flood guards built in. NOTE Flood guards protect against DoS attacks by limiting the number of new MAC addresses accepted. Another common feature on better switches is called media access control (MAC) filtering (or persistent MAC or sticky MAC addressing). In many networks, a tech plugs a host into a port and the host stays there for years. The network administrator configures the switch port for that host to accept frames from only that MAC address, preventing bad actors from unplugging the host and plugging in their evil system. Many enterprise-level switches come with a feature known as Dynamic Host Configuration Protocol (DHCP) snooping. With a DHCP snooping–capable switch, the switch is either automatically or manually given the IP addresses of the DHCP servers on your 06-ch06.indd 345 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 346 I’m a legit DHCP Server! WANTED No. You’re not! 12-34-56 78-9A-BC 12-34-56-78-9A-BC Figure 6-18 Trusted DHCP server network. If any device other than the DHCP servers with the known IP addresses tries to send DHCP information, the server will automatically turn off its associated port (Figure 6-18). Loop Prevention Some floods happen just from misconfiguration. If two or more pathways connect two switches, for example, this creates a loop, which then causes a broadcast storm—a type of flood (Figure 6-19). All but the simplest switches implement some kind of loop prevention, such as the Spanning Tree Protocol (STP). STP is almost always enabled in the switch’s configuration. When turned on, STP switches send out Bridge Protocol Data Unit (BPDU) guard frames every two seconds, quickly stopping loops by automatically turning off one of the ports that’s supporting the loop (Figure 6-20). Network Access Control Network access control (NAC) provides network protection and security by prohibiting hosts from connecting to the organization’s infrastructure unless they meet certain criteria. A NAC device provides an entry point or gateway into the network, typically for remote or mobile clients. This device checks the health and security settings of the client—a host health check—against a specified set of criteria before allowing it to access the network. For example, a NAC device could check the client for the latest antivirus signatures, the latest security updates, and other Figure 6-19 Loops are bad. Bridge Loop 06-ch06.indd 346 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 347 Figure 6-20 STP to the rescue! Turn off this port! security configuration items. If the client does not meet these requirements, the NAC device does not allow the client to connect to the network. Additionally, the NAC device might be able to update the client dynamically or reconfigure certain options so that the client could proceed with authentication and connection to the infrastructure. NAC could also be used to authenticate devices, allowing only authorized devices to connect. Normally, a NAC device would be placed on a secure segment within a DMZ network. NOTE Most networks that use NAC adopt a security position called Zero Trust (described in Module 6-2). No device is trusted at all until it passes a health check. NAC supports devices using agents or runs agentless. Agent-based NAC tracks many features of potentially inbound devices, such as software versions and so on. The agentbased approach enables very fine control over allowing a device to connect to the network. The criteria used for an agent-based approach can be permanent or dissolvable. The former means the device that wants access to the network must have some software loaded—that software stays loaded. A dissolvable agent system runs something once on the device and admits or denies access; the software is then deleted. Agentless NAC (such as one based on Windows Active Directory) would apply group policy rules to enforce the controls that an agent-based NAC device would do directly. Internet Connection Firewalls We’ve covered firewalls twice so far in this book, first for individual hosts, then as a tool to segment networks. Let’s move back to firewalls one more time, this time to the place that most folks think about when they hear the word firewall: the default gateway. Systems inside a LAN get their messages out of their LAN via a default gateway. The default gateway connects directly (or indirectly through in-house routers) to an ISP, which in turn connects to a router higher up on the Internet. Given the position of the default gateway at the edge of the network, it is a natural location to place a firewall to protect the local network. Network-based firewalls manifest in many ways, but the most common is at the default gateway, which includes a bevy of firewall features (Figure 6-21). 06-ch06.indd 347 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 348 Figure 6-21 Typical gateway EXAM TIP Given the setup of most networks these days, the default gateway often also acts as a network address translation (NAT) gateway, enabling many internal devices to use private IP addresses and access the Internet through a single public IP address. You’ll recall how NAT works from CompTIA Network+. For CompTIA Security+, think of scenarios using NAT as a typical implementation of secure network designs. This firewall manifests in many ways. SOHO environments see firewalling software added to the router directly. Larger networks require a different solution. As with so many other network components, firewalls can be software-based or dedicated hardware boxes. They come as open-source software or as proprietary software. 06-ch06.indd 348 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 349 EXAM TIP Look for comparison questions on the CompTIA Security+ exam that explore hardware vs. software firewalls and open-source vs. proprietary firewall software solutions. The primary function of any firewall is to inspect incoming IP packets and block the packets that could potentially hurt the hosts on the LAN. To do this, today’s firewalls have three very different methods: stateless, stateful, and application-based. The more advanced firewalls —called next-generation firewalls—combine multiple methods. Stateless Firewalls A stateless firewall looks at every incoming packet individually without considering anything else that might be taking place (ergo stateless). Stateless firewalls, also called packet filters, are the oldest type of firewall. If you’re going to have a firewall inspecting every packet, you must have some form of checklist that the firewall uses to determine whether a packet should be blocked. This is the router’s access control list (ACL). The ACL for an Internet gateway firewall is a unique tool that defines what makes a packet good or bad. A stateless firewall’s ACL can only define aspects of an IP packet to filter. A typical ACL would include these aspects: • IP address Block specific incoming/outgoing, destination/source IP addresses or complete network IDs • Port number Block specific incoming/outgoing, destination/source port numbers or ranges of port numbers • Time/date Block based on time of day, day of week A stateless firewall makes it easy to combine filters to create surprisingly sophisticated ACL rules. You can set up a basic home firewall, for example, to keep your child’s desktop system from accessing any Web pages (ports 80 and 443) between the hours of 10 p.m. and 6 a.m. on school nights. Figure 6-22 shows the ACL interface for a home router with a built-in firewall. One feature of all ACLs is the idea of implicit deny. Implicit deny means that by default there is no access unless the ACL specifically allows it. For example, every firewall’s ACL denies all incoming IP packets unless a particular packet is a response from a request initiated by one of the hosts on your LAN. Stateless firewalls are simple and work well in many situations, but fail miserably where inspecting and blocking without consideration of the state isn’t helpful. Consider a simple FTP session, run in the classic active mode: 1. A host inside the LAN (1.2.3.4) initiates a connection to an outside FTP server (2.3.4.5) using destination port 21 and, for this example, a source port of 12,345. 2. The firewall notes that an internal host has initiated an outgoing connection on port 21. 3. The FTP server responds to 1.2.3.4, port 12,345 with source IP address 2.3.4.5 and source port 21. The firewall recognizes this incoming connection as a response and does not block it. 06-ch06.indd 349 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 350 Figure 6-22 Firewall ACL interface 4. The FTP server initiates a data connection to 1.2.3.4, port 12,345 with source address IP 2.3.4.5 and source port 20. 5. The firewall does not recognize this incoming connection and, because of implicit deny, blocks the connection. Stateless firewalls were such a problem for FTP that the FTP protocol was redesigned to use a second, passive mode. Passive mode only uses port 21. Just as you can harden a switch against bad actors spoofing a legitimate system’s MAC addresses, you can protect against IP address spoofing with a firewall. Helping to prevent IP address spoofing on our networks is one area where stateless firewalls still do a great job. Routers can use several antispoofing techniques. A very popular one is to have a router query its DHCP server for legitimate systems on the network. Every initial packet going out is cross-checked against the DHCP server’s IP address list. 06-ch06.indd 350 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 351 Stateful Firewalls A stateful firewall understands the procedures and processes of different Internet protocols and filters any form of communication that is outside of proper procedures. A stateful firewall understands several functions expected in normal TCP and UDP communication and uses that intelligence to inspect the state of that connection. Stateful firewalls collect several packets in a connection and look at them as a state to determine if the communication meets correct protocol steps. One great example is how a stateful firewall can monitor a TCP connection. Every TCP connection starts with three messages, known as TCP’s three-way handshake: 1. The initiating system sends a SYN message, requesting a TCP connection. 2. The responding system sends a SYN/ACK message, informing the initiating system it is ready to start a connection. 3. The initiating system sends an ACK message, acknowledging the responding system. Figure 6-23 shows a Wireshark capture of a three-way handshake. Let’s say we have a stateful firewall protecting a Web server. It allows the incoming SYN connection from an unknown Web browser (a firewall protecting a public-facing server must allow incoming connections), but it stores a copy of the incoming packet in a table. It also allows the outgoing SYN/ACK packet from its server and keeps a copy of Figure 6-23 TCP three-way handshake 06-ch06.indd 351 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 352 that as well. When the Web browser responds with a proper ACK message, the firewall sees this as a good connection and continues to keep the connection open. If the Web browser does anything that makes the stateful firewall think the connection is outside of the protocol, on the other hand, it will block the connection for a certain amount of time. Stateful firewalls don’t have ACLs. They come from the manufacturer with all the state-smarts they’re ever going to have. For most stateless firewalls, it’s simply a matter of turning them on or off to enable or disable firewall duties. NOTE Very advanced stateless firewalls (from companies like Cisco or Juniper) may have a few filters (don’t call them ACLs) for their stateless firewalls, but those are outside the scope of the CompTIA Security+ exam. Application Firewall An application firewall has deep understanding of both the stateful and stateless aspects of a specific application (HTTP is by far the most common type of application firewall) and can filter any traffic for that application that could threaten it. Application firewalls can be thought of in two different contexts. In the first, an application firewall is an appliance—a box—or network device that works at all seven layers of the OSI model and can inspect data within protocols. Think of a situation in which HTTP traffic is filtered in a firewall. In an ordinary stateful firewall, the traffic is filtered based upon an established connection from an internal host. HTTP traffic is allowed in or out based upon whether the protocol itself is allowed, over which port the traffic is destined, its source or destination IP address, if it is the result of an established connection, and so on. This means that filtering is done based upon the characteristics of the traffic itself, rather than the content of the traffic. Application firewalls look at the content of the traffic as well, in addition to its characteristics. So, if HTTP is otherwise allowed into the network, an application firewall also looks at the content of the HTTP traffic, often detecting whether the content itself is allowed. EXAM TIP A typical application firewall acts as a content/URL filter, blocking traffic based on the content of the traffic and on the source URL. Application firewalls can be network-based or host-based; in the context of our discussions for this module, host-based firewalls are more relevant. Although most industrial static hosts do not use application firewalls specifically on their platforms, some of the more modern hosts, especially consumer devices, do have them. A host-based application firewall controls the applications and services on that device only, and it secures their connections to the network and interfaces with each other. NOTE Application firewalls are often referred to as Layer 7 firewalls because OSI Layer 7 is also known as the Application layer. 06-ch06.indd 352 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 353 Figure 6-24 Barracuda cloud WAF settings Given the huge number of Web applications living in the cloud, just about every manufacturer of application firewalls for Web apps—appropriately named Web application firewalls (WAFs)—also provides cloud-based virtual appliances (Figure 6-24). EXAM TIP Look for questions on the CompTIA Security+ exam that compare firewall implementations, from appliance vs. host-based vs. virtual. Appliance assumes a dedicated hardware box; host-based relies on software running on a workstation; virtual has software running in a virtual machine to handle the firewall duties. In a way, we can separate application firewalls from stateless and stateful firewalls in terms of their primary job. Application firewalls are designed to protect public-facing servers providing specific applications, so we can call them application-based firewalls. Stateless and stateful firewalls mainly protect LANs from the many evils that come from the Internet, so we can call them network-based firewalls. If you don’t have a public Web application server or an e-mail server (or a few other applications), you have no need for this type of firewall. Next-Generation Firewalls A next-generation firewall (NGFW) functions at multiple layers of the OSI model to tackle traffic no traditional firewall can filter alone. A Layer 3 firewall can filter packets based on IP addresses, for example. A Layer 5 firewall can filter based on port numbers. Layer 7 firewalls understand different application protocols and can filter on the contents of the application data. An NGFW handles all of this and more. 06-ch06.indd 353 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 354 An NGFW implements all sorts of traffic inspection policies at all layers. These include Ethernet rules (Layers 1 and 2), NAT rules (Layer 3), and HTTPS rules (Layer 7). An NGFW can grab and decrypt SSL/TLS traffic (HTTPS) and inspect it. This helps protect against and remove malware before it nails the network. EXAM TIP You’ll see NGFW at work in the CompTIA Security+ exam doing Secure Sockets Layer (SSL)/Transport Layer Security (TLS) inspection. That’s all about grabbing and examining encrypted packets. As you might suspect, NGFW appliances function just fine with both IPv4 and IPv6 networks, or both for that matter. A typical NGFW can get an IP address from DHCP or DCHCv6 and play well with stateless IPv6 auto-configuration. When thinking about implications of IPv6 for a network, moving to an NGFW might make the best option for future-proofing your security. Securing Servers Anyone providing a server that offers any service to the public Internet has a big security job ahead of them, and the CompTIA Security+ exam objectives reflect the importance of this effort with many security topics covering what it takes to protect servers. In fact, all of Chapter 8 goes into detail on what’s needed to protect different Internet services, such as Web and e-mail. Before we start lighting up Web or e-mail servers, there’s a lot we can do to place them in a safe place in which they can operate quickly and safely. We can choose from among many specialized security appliances to add to any network that supports one or more Internet servers, regardless of what type of Internet service they provide, to provide security. Proxy Servers The Internet is filled with servers and the clients that access them. In many situations, we find it helpful to put a box between the client and the server for certain applications. These boxes accept incoming requests from clients and forward those requests to servers. Equally, these boxes accept responses from servers and then forward them to the clients. These boxes are known as proxy servers or often just proxies. EXAM TIP Proxies work at the application level. There are Web proxies, e-mail proxies, FTP proxies, and so forth. Multipurpose proxies support multiple applications. Proxies come in one of two forms: forward or reverse. A forward proxy is known to the client system, often in the same LAN, taking the requests from the client, maybe doing something with the request, and then forwarding the request to the server just like any other client (Figure 6-25). Forward proxies are popular in organizations such as schools where the network administrators need to apply security controls to Internet access. A forward Web proxy 06-ch06.indd 354 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-3: Implementing Secure Network Designs 355 Hey Proxy, please forward my SYN request to Server? Hey Server, I’m just a client, here’s a request. SYN! Oh, OK! SYN/ACK! Sure. Forward Proxy Client Server Figure 6-25 Forward proxy almost always includes a strong firewall to check outgoing requests for blocked URLs, time-of-day restrictions, and anything else that needs be monitored to support the security policies of the organization. A reverse proxy is used to protect servers. Reverse proxies are usually inside the same LAN as the servers. They always contain an application firewall to check the incoming requests for attack vectors and then pass the good requests to the server (Figure 6-26). Proxies work at the application level, so traditionally a system’s application must be configured to use a proxy. If a client is to use a forward Web proxy, then every Web browser on every client is configured to use it. Figure 6-27 shows the proxy settings in a Web browser. All this configuration is a pain, especially if you have a thousand users all using different Web browsers. So why not let your router simply inspect all the data going out on the application’s port numbers and simply redirect those packets to your proxy? That’s the idea behind a transparent proxy. Most forward proxies support a transparent mode to do just this. Hey Server, I’m just a client, here’s a request. SYN! Hey Server, I’ve got a request. SYN! Oh, OK! Proxy. SYN/ACK! Sure. Client Reverse Proxy Server Figure 6-26 Reverse proxy 06-ch06.indd 355 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 356 Figure 6-27 Web proxy settings Deception and Disruption Network security professionals and network administrators can set up systems to entice and lure would-be attackers into traps. These deception and disruption systems are so very sweet: honeyfiles, honeypots, and honeynets. And then there’s the DNS sinkhole, a related technology. Let’s take a look. A honeyfile baits attackers to access it on a file server. The file name “passwords” could trigger an alarm when anyone accesses the honeyfile. A honeypot is a host designed to be compromised, so it has multiple vulnerabilities. A honeypot is placed on the network to attract the attention of malicious hackers, hopefully drawing them away from other, more sensitive hosts. If an attacker victimizes a honeypot, you can study his methods and techniques to help you better protect the actual network against those same methods and techniques. Honeypots can be boxes that are misconfigured or intentionally not patched, or they can be prebuilt virtual machines. There’s even software out there that can emulate dozens or hundreds of hosts at the same time, spanning several different operating systems, including different versions of Windows, Linux, macOS, UNIX, and so on. 06-ch06.indd 356 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-4: Virtual Private Networks 357 A honeynet, as you might guess, is an entire network of honeypots on their own network segment, used to get a hacker bogged down in a decoy network while the administrator locks down and secures the sensitive network and records and tracks the actions of the hacker. Network deception techniques such as these can use fake assets, fake data, and fake telemetry (like server load, availability, memory consumption), all to gather intelligence on hacker techniques and sophistication. A DNS sinkhole acts as a DNS server (or a DNS forwarder) for a LAN. The DNS sinkhole contains a list of known domains associated with malware, ad networks, and other forms of undesirable code. When a host on the LAN requests a DNS resolution, the DNS sinkhole compares the request to the list of known negative sites and, if there is a match, responds with a blank or null IP address. The effect of a working DNS sinkhole is the blocking of almost every advertisement for every system on the LAN with almost no negative performance impact on the LAN. Module 6-4: Virtual Private Networks This module covers the following CompTIA Security+ objectives: • 3.1 Given a scenario, implement secure protocols • 3.3 Given a scenario, implement secure network designs A virtual private network (VPN) uses the public Internet as a direct connection between a single computer and a faraway LAN or between two faraway LANs. This is not a remote desktop connection or a terminal or a Web page connection. A VPN puts a single system or a separate LAN on the same broadcast domain, the same Layer 2 connection, just as if the faraway system plugged directly into the LAN’s switch. A successful VPN connection gives your remote system an IP address on your LAN. You can print from the remote system to your LAN’s printers. You can see all the shared folders on other computers on the LAN. You are there. Well, at least your Ethernet frames are there. VPNs are incredibly powerful for remote single users or remote networks that need to get to a LAN’s internal servers. VPNs are a well-established technology and are easy to implement. Most enterprise environments have VPN access for employees and, in some cases, vendors. SOHO environments can use VPNs as well. My home network, for example, is configured to let me access my home network from anywhere on the Internet. Given the popularity of VPNs and given the fact that they enable people to move potentially sensitive data securely across the wide-open Internet, VPNs are a very attractive target for the CompTIA Security+ exam. This module dives into VPNs, first describing how they work and then looking at the many protocol choices available for setting up a VPN. 06-ch06.indd 357 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 358 EXAM TIP Expect several questions on VPN scenarios on the CompTIA Security+ exam. In essence, a VPN boils down to making a secure connection to access remote resources as if they were local resources. Implement secure protocols (like IPsec) to make the VPN connections and thus implement secure network designs. How VPNs Work To make a faraway computer manifest as a local computer on your LAN, you need to do several actions. First, you need to connect to the other network over the Internet. That means you need a system with a public IP address that accepts VPN connections. Second, you need to create a second network connection that uses the Internet connection you’ve established to allow you to send LAN traffic over the Internet. Third, you should encode your data to keep private whatever files, print jobs, or other information you send to the faraway LAN. VPNs work in one of two different ways. You can connect a single system to an existing LAN in what is called remote access, or you can connect two complete LANs in siteto-site. Figure 6-28 shows the two options. To make a connection, at least one system must have a VPN server, more commonly called a VPN concentrator, designed to accept remote connections from either a single system (for remote access) or another VPN concentrator (for site-to-site). A VPN concentrator is often special VPN software installed on edge routers, or it may be VPN server software installed on a system inside your network. In either case, one system connects to the VPN server and makes a connection (Figure 6-29). VPN connections require tunneling or embedding of IP traffic inside other packets. The VPN to VPN connection gets made, in other words, and then the true traffic happens inside the secure connection. The VPN concentrators continually insert the local How do I join that faraway network? How do we join that faraway network? Remote Access Site-to-site Figure 6-28 Remote access vs. site-to-site 06-ch06.indd 358 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-4: Virtual Private Networks 359 Internet VPN Concentrator Internet Figure 6-29 VPN concentrators added traffic in Internet packets and send them through the tunnel; or they receive incoming Internet packets, strip away the outer IP information, and send the remaining frame to the local network (Figure 6-30). EXAM TIP Site-to-site VPN concentrators generally never disconnect. We call these always-on VPNs. One early problem with VPNs was that once you connected to a LAN, that was your only connection. Your IP address and default gateway were on that LAN; you used that LAN’s DHCP and DNS servers. That meant if your computer was connected to a VPN and opened a Web browser, your computer went through the VPN connection and then went back out and used the Internet connection on your LAN. This is called a full tunnel and is a terrible way to get to the Internet. Current VPN technologies enable you Figure 6-30 VPN tunnel on one endpoint Internet TUNNE L 06-ch06.indd 359 LAN PACKET 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 360 to configure a VPN connection to send only LAN traffic through the tunnel. All other traffic ignores the tunnel. This is a split tunnel and is the most common type of tunnel. EXAM TIP The CompTIA Security+ exam will most likely ask you to differentiate between split-tunnel vs. full-tunnel VPN connections. Early VPNs The first VPNs used one of two competing protocols. The Point-to-Point Tunneling Protocol (PPTP) was developed by Microsoft to include VPN connection technologies within Microsoft operating systems. PPTP enables a client to send data in it, much as you would a letter in an envelope. The PPTP packet contains the destination IP address of the network you are attempting to connect to. Inside this PPTP envelope is the traffic that will pass through the external VPN connection device intended for the destination network. This traffic would not be secure using PPTP alone; Microsoft uses its proprietary Microsoft Point-to-Point Encryption (MPPE) protocol to secure traffic traveling over PPTP. PPTP uses TCP port 1723. It’s rarely seen over VPN connections these days, as most modern VPNs use some form of IPsec or SSL/TLS VPNs, described later. Layer 2 Tunneling Protocol (L2TP) was developed jointly by Microsoft and Cisco, but it has become an Internet standard. Microsoft contributed aspects of its PPTP, while Cisco used its proprietary Layer 2 Forwarding (L2F) protocol. Like PPTP, L2TP is only an encapsulation protocol, simply providing transport services and protecting data through untrusted networks (such as the Internet) to get it to a destination network. L2TP still sees some adoption but is also fading to IPsec and SSL/TLS VPNs. IPsec VPNs Internet Protocol Security (IPsec) is a security protocol that works at the Network layer of the OSI model. IPsec was developed to provide security services (authentication and encryption) for IP traffic, since IP does not have any built-in native security protections. Three major protocols make up IPsec: AH, ESP, and ISAKMP. NOTE CompTIA lists IPsec with an uppercase S, IPSec. That’s not accurate and never has been, but CompTIA uses the incorrect casing on every certification objective (not just Security+) that references IPsec. The Authentication Header (AH) protocol provides authentication and integrity services for IP traffic. AH can be used on the entire IP packet, including the header and data payload. The Encapsulating Security Payload (ESP) protocol takes care of encryption services. ESP can provide protection for the entire IP packet, depending the IPsec mode used, transport or tunnel. 06-ch06.indd 360 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-4: Virtual Private Networks 361 Encrypting the IP header can cause problems if routers and other devices can’t read the header information, including the source and destination IP addresses. Between hosts on a network, the header information isn’t usually required to be encrypted, so ESP doesn’t have to be used. This is called IPsec’s transport mode. In transport mode, header information is not encrypted so that hosts and network devices can read it. The data, on the other hand, can be encrypted to protect it, even within a LAN. IPsec tunnel mode is used when IP traffic is encapsulated and sent outside of a LAN, across WAN links to other networks. This is what happens in VPN implementations that use IPsec. In tunnel mode, since the IP packet is encapsulated in a tunneling protocol (such as L2TP), all the information in the packet, including headers and data payload, can be encrypted. So, ESP is typically used only in tunnel mode. The third IPsec protocol—Internet Security Association and Key Management Protocol (ISAKMP)—is used to negotiate a mutually acceptable level of authentication and encryption methods between two hosts. This acceptable level of security is called the security association (SA). An SA between two hosts defines the encryption type and method, algorithms used, types of cryptographic keys and key strengths, and so on. The Internet Key Exchange (IKE) protocol—IKEv2 these days—is used in ISAKMP to negotiate the SA between hosts. IKE uses UDP port 500 to accomplish this. While IPsec is usually seen in VPN implementations paired up with L2TP as its tunneling protocol, IPsec can be very effective in securing traffic within a LAN, particularly sensitive traffic between hosts that an organization wouldn’t want to be intercepted and examined. IPsec offers a wide variety of choices for encryption algorithms and strengths and is very flexible in its configuration. You can choose to protect all traffic between certain hosts or protect only certain aspects of traffic, such as certain protocols or traffic that travels between certain ports. TLS VPNs The only serious competitor to IPsec VPNs is VPNs using the SSL/TLS protocol. This is the same SSL/TLS protocol used in secure Web pages. SSL/TLS VPN connections don’t require special client software installed on the system that wants to connect to the remote network. That system uses only a Web browser and SSL/TLS security to make the VPN connection. EXAM TIP Sophos has a Unified Threat Management (UTM) system on Amazon Web Services (AWS) that enables you to log into AWS and get a list of predefined network services. The system requires an HTML5-compliant browser—so the latest Chrome, Firefox, or Safari work fine—but the catch is interesting: you can only access content remotely; you can’t download content to your local machine. Sophos calls its service a VPN portal—and CompTIA includes HTML5 VPN as a VPN option. Be aware that this exists for the exam. 06-ch06.indd 361 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 362 Module 6-5: Network-Based Intrusion Detection/Prevention This module covers the following CompTIA Security+ objectives: • 3.2 Given a scenario, implement host or application security solutions • 3.3 Given a scenario, implement secure network designs Network-based intrusion detection systems (NIDSs) and network-based intrusion prevention systems (NIPSs) look at attacks coming into the network at large instead of into a host. Attacks could be in the form of malformed network traffic or excessive amounts of traffic that would easily exceed a host’s threshold to handle effectively. An attack could also manifest as malicious content embedded in traffic or other forms of malware. Network intrusion handling also might look at massive DDoS conditions, such as those caused by botnet attacks. (More on this specific attack in Chapter 8.) Detection vs. Prevention One point of interest is the difference between a NIDS and a NIPS. A NIDS is a passive device and focuses on detection alone, making it a detection control. It detects network traffic issues and alerts an administrator to these issues, also logging the events in the process. A NIPS, in contrast, is an active (CompTIA Security+ uses the term inline) device and focuses not only on detecting network attacks but also on preventing them. EXAM TIP The CompTIA Security+ exam will most likely ask you to contrast inline vs. passive network-based intrusion systems. NIPS are inline; NIDS are passive. In addition to performing the same functions as a NIDS, a NIPS also tries to prevent or stop attacks by taking a series of preconfigured actions, based upon the characteristics of the attack. A NIPS may dynamically block traffic from a certain source address or domain, for example, or block a certain port or protocol if it detects issues with it. A NIPS can take other actions as well, such as shunting traffic to other interfaces, initiating other security actions, tracing the attack back to its origin, and performing some analysis on the attack, but whether a particular NIPS can perform these actions depends on the feature set of that NIPS. Detecting Attacks Whether your goal is to detect and prevent attacks or solely to detect them, networkbased intrusion tools need some method to detect attacks. In general, NIDS/NIPS solutions act very much like firewalls in that they inspect packets. Detection falls into four types: behavior, signature-based, rule, and heuristic. 06-ch06.indd 362 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-5: Network-Based Intrusion Detection/Prevention 363 NOTE Many NIDS/NIPS vendors’ detection solutions perform combinations of these four types of detection. Behavior/Anomaly A behavior- or anomaly-based system detects attacks after comparing traffic with a baseline of patterns considered normal for the network. For this to work, the intrusion detection system must be installed and then given the opportunity to “learn” how the normal flow of traffic behaves over the network. This can take time, but once the NIDS/NIPS establishes a good baseline of normal network traffic, the system will detect any unusual or anomalous traffic patterns that don’t fit into the normal network traffic patterns and issue alerts on them as potential attacks. NOTE Anomaly-based systems rely on rules and heuristic methods to determine when behavior on the network differs from normal. See the upcoming “Rule” and “Heuristic” sections for more details. Signature A signature-based system, on the other hand, uses preconfigured signature files (similarly to how anti-malware applications work), which are stored in the NIPS/NIDS database. These signatures define certain attack patterns based upon known traffic characteristics. Like an anti-malware solution, a signature-based NIDS/NIPS must also have its signatures database updated frequently, since the security community records new attack patterns often. These updates will usually come through a subscription-based service from the NIDS/NIPS vendor, although some community or open-source signatures may be available as well. Rule A rule-based system uses preconfigured rules in a ruleset, much like a firewall, to detect possible attacks. For example, if the system detected an excessive (beyond a set number or threshold) number of ICMP packets directed at a destination IP address on the network, the system would activate a rule, send an alert to administrators, and, in the case of a NIPS, stop the attack. Obviously, an administrator could configure unique rules for the organization based on its network environment and historical attack experiences, but these types of systems are also usually included as part of either a signature- or behavior-based system. Heuristic Finally, a heuristic system combines the best of both anomaly-based and signature-based systems. It starts out with a database of attack signatures and adapts them to network traffic patterns. It learns how different attacks manifest themselves on the network in which it is installed and adjusts its detection algorithms to fit the combination of network traffic behavior and signatures. 06-ch06.indd 363 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 364 Which Is Best? There’s no way to answer that question, and in fact, detection systems are evolving so quickly that even these four types, while sufficient for purposes of the CompTIA Security+ exam, are arguably too simple when applied to the most modern NIDS/NIPS solutions. Although there are advantages and disadvantages to both anomaly-based and signature-based systems, often, modern NIDS/NIPS are hybrid systems and may use both techniques. NOTE Host-based IDS/IPS solutions are almost always signature-based products. The big measurement for the quality of a NIDS/NIPS boils down to the solution’s detection analytics, as in how accurately they parse data. The goal of a NIDS/NIPS is to detect attacks and, in the case of the NIPS, do something about them. The great issues are false positive and false negative rates. Too many false positives will give you heartburn as you continually jump up and down from alarms that mean nothing. A false negative is even worse, as that means your NIDS/NIPS fails to catch actual attacks. The secret is to adjust the sensitivity of the NIDS/NIPS to create the best balance possible. EXAM TIP Look for an exam question about advanced persistent threats (APTs), such as a terrorist organization trying to hack into a government agency, and the tools used to stop these attacks. Better security appliances implement unified threat management (UTM), marrying traditional firewalls with other security services, such as NIPS, load balancing, and more. Configuring Network-Based IDS/IPS In general, a NIDS/NIPS consists of many components. The core component of any IDS/IPS is the sensor, the device that monitors the packets, searching for problems. Given the nature of detection versus prevention, a NIPS sensor must be installed in-band to your network traffic, while a NIDS sensor, being passive, is normally installed out-ofband. In-band in this context means the sensor processes all the traffic flowing through the network in real time. An out-of-band sensor processes traffic, in contrast, but not in real time. Figure 6-31 shows two sensors installed in a DMZ as examples of in-band versus out-of-band installation. All packets must go through in-band sensor devices. Out-of-band sensor devices need some form of network connection that enables them to see all the traffic. Just plugging it into a switch only allows the sensor to see traffic to and from the switch plus broadcast traffic. If you want an out-of-band device to grab packets, you need a network tap or a port mirror. 06-ch06.indd 364 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Module 6-5: Network-Based Intrusion Detection/Prevention 365 Figure 6-31 In-band and out-of-band installations Out-of-band In-band DMZ LAN Network TAP A network TAP—test access point—is a device that you can insert anywhere along a run to grab packets. The network TAP in Figure 6-32 works for 10/100/1000-BaseT Ethernet runs. You place this in the run (you’ll need to run a few patches and cables for in/outs) and then add an out-of-band sensor to the right-hand side. Port Mirroring A port mirror (also called a Switched Port Analyzer, or SPAN, in Cisco devices) is a special port on a managed switch configurable to listen for all data going in and out of the switch. Unlike a network TAP, port mirroring is convenient and easily changed to reflect any changes in your NIDS/NIPS monitoring strategy. Port mirroring solutions are very handy when you want to monitor more than one VLAN at a time. Be careful about terminology here. Some folks refer to port mirroring as copying the data from a single switch port to a monitoring port, while referring to port spanning as grouping multiple ports (or all of them) to a monitor port. Figure 6-32 Garland Technology Network TAP P1GCCB (Photo courtesy of Garland Technology, www.garlandtechnology.com) 06-ch06.indd 365 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 366 EXAM TIP For some reason, objective 3.3 on the CompTIA Security+ exam blurs some terms, calling a network TAP a port tap, for example, and SPAN under port mirroring, port spanning. Don’t get confused between a TAP and a SPAN. UTM Many vendors sell single-box solutions to handle routing, firewalling, proxy, antimalware, and NIPS. These unified threat management (UTM) boxes are excellent for several situations (especially when you have a single Internet access and no public-facing server). One area in which UTM thrives is monitoring: with only a single appliance to query, it’s easy to get the information you need. Yet if you have a more complex NIDS/ NIPS setup, monitoring the NIDS/NIPS gets a bit more complex. Monitoring NIDS/NIPS A newly installed NIDS/NIPS is only as good as the organization around it that handles the monitoring. Even the most automated NIPS needs a surprisingly high degree of monitoring, making sure humans react to attacks and remediate as needed. When you find yourself in a situation where this much monitoring takes place, you’ll find security information and event management (SIEM). We’ve already discussed SIEM broadly back in Chapter 4, but now that we have a specific job to do, let’s revisit SIEM. This time we’ll plug in a few parts of a typical SIEM installation for aggregation and correlation. Collecting Data When it comes to SIEM, it’s all about aggregation: collecting data from disparate sources and organizing the data into a single format. Any device within a SIEM system that collects data is called a collector or an aggregator. In a simpler NIPS setup with three sensors, it’s common to have a single server that acts as a collector, querying the sensors for data in real time. Correlation The next part of SIEM that fits nicely into NIDS/NIPS is correlation. Correlation is the logic that looks at data from disparate sources and can make determinations about events taking place on your network. (Note that a correlation engine could be in-band or outof-band, depending on the placement of the NIDS/NIPS.) In its simplest form, a correlation engine might query a log, see that the same event is logged from three different sources, and eliminate duplicates (event deduplication). A correlation engine uses the event of time constantly, so it’s critical that all devices have time synchronization for correlation engines. A well-correlated log will have common fields for which we can configure the NIPS system for automated alerts and triggers. Finally, it’s critical that all logs are archived. 06-ch06.indd 366 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Questions 367 Endpoint Detection and Response Several security manufacturers have taken a further step in integrating security solutions to their advanced network appliances. Firewalls provide classic endpoint protection, blocking traffic from getting to a user’s system, for example, or blocking attackers from accessing network resources. NIPSs actively monitor traffic that could pose a threat and act decisively to stop that activity. Very sophisticated systems called endpoint detection and response (EDR) essentially combine an NGFW with a NIPS on steroids to provide end-to-end monitoring, analysis, response to threat, and forensics for additional research. Full EDR systems have rolled out since 2017 and will undoubtedly gain market share, at least at the high-end enterprise level. Questions 1. Which network device enables sharing among multiple servers to provide security and efficiency? A. Load balancer B. Proxy server C. Screened subnet D. VPN 2. Which network device is used to send traffic to different physical networks, based upon logical addressing? A. Router B. Switch C. Load balancer D. Firewall 3. Which type of device is used to provide network protection and security by preventing hosts from connecting to the organization’s infrastructure unless they meet certain criteria? A. Switch B. NAT device C. Firewall D. NAC device 4. All of the following characteristics describe VLANs, except: A. VLANs require routing between them. B. VLANs separate hosts into logical networks. C. VLANs can be used to apply security policies and filtering to different segments. D. VLANs allow any host plugged into the switch to become a member of the virtual segment. 06-ch06.indd 367 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Chapter 6: The Basic LAN 368 5. Which of the following would be needed to block excessive traffic from a particular protocol? A. Broadcast storm prevention B. Loop protection C. ACL D. 802.1X 6. Which of the following describes a network appliance that intercepts user or host requests and then makes those requests to other hosts or networks on behalf of the user? A. Proxy B. Firewall C. NIDS D. NIPS 7. Alix sets up a firewall for her organization that inspects traffic at Layers 2, 3, and 7. What type of firewall did she most likely install? A. Application B. NGFW C. Stateful D. Stateless 8. A NIPS is considered a __________ type of control. A. detective B. preventive C. network D. host 9. Which of the following terms refers to a combination of multifunction security devices? A. NIDS/NIPS B. Application firewall C. Web security gateway D. Unified threat management 10. Which of the following does an application firewall focus on for traffic filtering? A. Traffic content B. Protocol and port C. Source or destination IP address D. Domain name 06-ch06.indd 368 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 6 Answers 369 Answers 1. A. A load balancer enables sharing among multiple servers to provide security and efficiency. 2. A. A router is used to send traffic to different physical networks, based upon logical addressing. 3. D. A network access control (NAC) device is used to provide network protection and security by preventing hosts from connecting to the organization’s infrastructure unless they meet certain criteria. 4. D. VLANs do not allow any hosts plugged into the switch to automatically become a member of the virtual segment; membership is based upon switch port, MAC address, or IP address. 5. A. A broadcast storm prevention implementation, such as a flood guard, is used to block excessive traffic from a particular protocol. 6. A. A proxy is a network appliance that intercepts user or host requests and then makes those requests to other hosts or networks on behalf of the user. 7. B. A next-generation firewall works at multiple layers of the OSI model. 8. B. A network-based intrusion prevention system (NIPS) is considered a preventive type of control. 9. D. Unified threat management (UTM) refers to a combination of multifunction security devices. 10. A. An application firewall focuses on traffic content for filtering, rather than on traffic characteristics. 06-ch06.indd 369 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Blind Folio 370 This page intentionally left blank 06-ch06.indd 370 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 CHAPTER Securing Wireless LANs 7 It’s all about sound. It’s that simple. Wireless is wireless, and it’s digital. Hopefully somewhere along the line somebody will add more ones to the zeros. When digital first started, I swear I could hear the gap between the ones and the zeros. —Eddie Van Halen Modern networks incorporate wireless networks using the 802.11 standard, Wi-Fi, enabling laptops, tablets, and smartphones to connect to the wired resources, such as file servers and printers. Wireless networks, however, represent a broad attack surface that, if not secured properly, provides excellent opportunities for attackers to access those same resources. Thus, a key component of network security is to lock down wireless networks sufficiently to keep out attackers yet still enable authorized users to access network resources easily. This involves installing and configuring wireless security settings, such as cryptographic and authentication protocols, to secure the 802.11 wireless network, as described in this chapter. This chapter explores topics in securing wireless LANs in three modules: • Networking with 802.11 • Attacking 802.11 • Securing 802.11 Module 7-1: Networking with 802.11 This module covers the following CompTIA Security+ objectives: • 3.4 Given a scenario, install and configure wireless security settings • 3.8 Given a scenario, implement authentication and authorization solutions A reader posed this question: “If you could pick one attack surface to try first to penetrate a network, what would it be?” Perhaps not surprisingly at this point in the book, my answer was “Go for the Wi-Fi!” From the day 802.11 first rolled out in the very late 1990s, the 802.11 standard has shown several vulnerabilities, from the well-documented WEP and WPS exploits to more sophisticated attacks such as the TLS handshake. 371 07-ch07.indd 371 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 372 Figure 7-1 Wireless systems provide a tempting attack surface. ? C’mere, little WAP! C’mere, boy! An astute security professional, capable of properly configuring good-quality wireless access points (WAPs), should have no problem making an 802.11 network relatively secure. Unfortunately, very few people have that capability, and that’s why wireless provides a tempting attack surface (Figure 7-1). It is impossible to understand how to attack 802.11 or how to secure it without a solid understanding of 802.11. For that reason, this module explores two threads. We’ll start with an overview of 802.11 security protocols (and some non-802.11 protocols that 802.11 uses). We’ll then tour 802.11 authentication methods, including advanced authentications that only the most secure wireless networks implement. NOTE I assume you know the essentials about 802.11 networks from studying CompTIA A+ or Network+ (or equivalent wireless network training) before tackling CompTIA Security+. If that’s not the case, check out one of my All-in-One or Passport books on the subject. Wireless Cryptographic Protocols When wireless networking was first adopted in the consumer and business markets, no secure wireless protocols were available to prevent eavesdropping and traffic interception. As people became more security conscious, they realized that they needed encryption and authentication protection on wireless networks, as they had on wired networks. Even though the wireless medium is different, security was still a necessity. This resulted in the development of several cryptographic protocols—protocols meant to ensure security via encryption and cryptography, with varying degrees of effectiveness, which have been implemented in wireless networks over the years. As technologies have improved, these wireless cryptographic protocols have improved as well, including newer and more secure methods of authenticating devices and encrypting traffic. In the next few sections, we’ll discuss the different wireless security protocols, their advantages and disadvantages, and how you should implement them in your wireless network. 07-ch07.indd 372 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-1: Networking with 802.11 373 Figure 7-2 WEP is still out there (source: https://wigle.net/stats). The Legacy of WEP Wired Equivalent Privacy (WEP), the first security iteration of 802.11, used a shared password encryption scheme that within a few years was discovered to be mathematically crackable. The primary reason for this weakness came from poor key usage with the RC4 encryption. Today’s WEP cracking tools will extract a WEP key in just a few minutes. NOTE To be fair to the original Wi-Fi developers, they didn’t intend WEP as an encryption protocol. WEP was intended to provide wireless users the same level of security they could expect from a wired network (hence the name). You’d think that, knowing WEP is so easily cracked for so long, no one would use WEP, correct? Wrong. According to Wigle.net, the popular 802.11 database, around 5 percent of all 802.11 networks use WEP encryption as I type this, although the number is slowly dropping (Figure 7-2). RC4 Rivest Cipher version 4 (RC4) was built into WEP as its encryption protocol and was very efficient because, as a streaming protocol, it rapidly encrypts 1 bit (rather than entire blocks) of plaintext at a time. It uses a wide range of key sizes, from 40-bit to 2048-bit keys. RC4 alone is not necessarily a weak protocol and is found in other secure protocol implementations beyond WEP. WEP poorly implemented the RC4 protocol, however, adding to the already numerous security flaws found in its design. For this reason, as well as the issues involved with small initialization vectors (IVs), small key size, and static key repetition, never use WEP in modern wireless networks. 07-ch07.indd 373 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 374 WPA When the wireless industry (specifically, the Wi-Fi Alliance) recognized the inherent security flaws in WEP, they realized they needed to do something very quickly to stem the growing problem of unsecured wireless networks using WEP. Simultaneously, the Institute of Electrical and Electronics Engineers (IEEE) began developing a new security protocol standard for wireless networks, known as 802.11i, but the standard was delayed for various reasons. The Wi-Fi Alliance implemented what was really a stopgap measure in the interim to replace WEP. The result was Wi-Fi Protected Access (WPA), introduced in 2003. WPA has several advantages over WEP, including the use of dynamic keys and larger key sizes. WPA, also unlike WEP, requires either no authentication (what some manufacturers call open mode), authentication to a RADIUS server (Enterprise Mode – WPA-ENT), or the use of a pre-shared key (PSK). Originally conceived for personal or small business infrastructure networks, the PSK setup is called WPA-Personal (sometimes referred to as WPA-PSK) and can be used to authenticate wireless client devices and wireless access points mutually. WPA-Enterprise, robust but complex and hard to use, was developed for larger infrastructures and requires the use of the 802.1X authentication protocol, which we will cover a bit later in the module. Figure 7-3 shows the various protocol options found on wireless routers. WPA uses the Temporal Key Integrity Protocol (TKIP) for generating encryption keys. TKIP makes it possible to use dynamic keys, which are generated on a per-packet basis. This means the keys are not repeated for different transmissions, but require a different encryption key on each individual packet. TKIP, combined with an improved implementation of the same RC4 stream cipher that WEP uses, provides WPA encryption. TKIP enables backward-compatibility with legacy WEP, uses 128-bit keys, and uses a 48-bit initialization vector. Figure 7-3 Wireless protocol choices on a wireless network 07-ch07.indd 374 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-1: Networking with 802.11 375 The 802.11i task group came up with a very clever patch for WEP in WPA with TKIP, but it was a patch built on the bones of WEP. Within a very short while, researchers showed ways to exploit the underlying WEP structures. WPA remained very difficult to crack for many years, but the full 802.11i standard needed to be implemented. WPA2 Wi-Fi Protected Access 2 (WPA2) is the name of the first official implementation of the 802.11i wireless security protocol standard developed by the IEEE. It offers several improvements over the original WPA, such as replacing TKIP with AES, a 128-bit symmetric block cipher that’s much more robust but is backward-compatible due to its inclusion of TKIP in its protocol suite. Like WPA, WPA2 also has two different implementations: WPA2-Personal (using a pre-shared key) and WPA2-Enterprise, which work the same way as they do in WPA. A WPA/WPA2 passphrase can be from 8 to 63 case-sensitive ASCII characters, or 64 hexadecimal characters. Now, this passphrase is not the actual WPA/WPA2 key; the passphrase is used to generate the 256-bit pre-shared key that must be entered into all wireless devices on the same wireless network. Note that this is different from the way WEP implements its passwords; the WPA/WPA2 passphrase is not the key itself. EXAM TIP Remember that WPA uses TKIP; WPA2 uses AES. AES The Advanced Encryption Standard (AES)—which you read about back in Module 2-3— is used by a wide variety of encryption applications. It was adopted as the official encryption standard for the United States by the National Institute of Standards and Technology (NIST), after an open competition with several different competing algorithms. AES uses the Rijndael encryption algorithm and is considered much stronger than previous symmetric algorithms used in wireless networking, such as RC4. AES is the encryption algorithm used in WPA2 and uses a particular process, or mode, within WPA2 to encrypt traffic. This mode is called the Counter Mode Cipher Block Chaining Message Authentication Code Protocol, which CompTIA shortens to Countermode/CBC-MAC Protocol (CCMP). CCMP uses a 128-bit key and 128-bit block size (since it is a block symmetric cipher, as opposed to the streaming RC4 symmetric cipher used in WEP and WPA), as well as 48-bit initialization vectors. The larger IV sizes help prevent replay attacks from being conducted against WPA2 (see “Replay Attacks,” later in the chapter). NOTE Wireless devices often have an encryption setting that lets you choose between AES, TKIP, and mixed mode. In mixed mode, both AES and TKIP are supported. It is not recommended. 07-ch07.indd 375 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 376 WPA3 WPA2 has served the 802.11 industry since 2004, more than a lifetime in the IT industry. In this time frame WPA2 has started to show some weaknesses that enable skilled bad actors to break into wireless networks. One of the biggest weaknesses of WPA2 is the pre-shared key. Anyone in possession of the single PSK can give it to others and they can use it to access the network. Worse, there are a number of attacks—in particular the infamous KRACK on-path (MITM) attack—that work on any WPA2 network. By the middle aughts, it was clearly time to improve on WPA2 with the next generation of 802.11 security. The Wi-Fi Alliance released the replacement for WPA2, called Wi-Fi Protected Access 3 (WPA3), in 2018. WPA3 brings many improvements over WPA2. Most notably, Simultaneous Authentication of Equals (SAE) replaces PSK—at least for encryption. If you set up an “open” SSID with a WPA3-capable WAP, SAE automatically forces every WPA3-capable device connecting to that WAP to use a Diffie-Hellman–style authentication/encryption process. In other words, the day of the unencrypted wireless connection no longer exists in WPA3. EXAM TIP Look for a comparative question on the CompTIA Security+ exam that explores pre-shared key (PSK) vs. enterprise vs. open. This applies primarily to WPA2, not WPA3, but PSK means using personal mode, enterprise means connecting to a RADIUS server, and open means having no security at all (i.e., open season on your network). WPS You can fairly easily join to a wireless network any system that has a screen and input method (keyboard, mouse, or touch screen). Joining a system, such as a printer, that lacks a screen and input device is much harder. In many cases they require separate setup programs or painfully complex configurations through tiny text screens and pressing up and down buttons through entire alphanumeric strings to type in passwords. Recognizing the popularity of wireless devices in non-enterprise networks, the Wi-Fi Alliance introduced Wi-Fi Protected Setup (WPS) in 2006. The goal of WPS is to enable anyone to join a WPS-capable device to a WPS-enabled wireless network just by pressing two buttons. Press the button on the WAP (Figure 7-4), then press the button on the device you want to join to the network; your device connects to the SSID and takes on the WAP’s WPA2 encryption. Neat! Alternatively, every WPS-enabled WAP comes with a fixed eight-digit PIN code to allow devices without a WPS button (like a laptop) to connect to the WAP. You press the button on the router and then enter the router’s PIN code as the SSID’s password. Unfortunately, the eight-digit code has two problems. First, only seven of the eight digits are used (the eighth digit is only a checksum). Additionally, the seven digits are confirmed in two groups: the first three values, then the last four. This means it only takes about 11,000 guesses to crack a WPA PIN code. Yipe! 07-ch07.indd 376 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-1: Networking with 802.11 377 Figure 7-4 Typical WPS button on home router WPS button So What Do We Use? If you install an 802.11 network, the Wi-Fi Alliance states that you must use either WPA2-ENT or WPA2-PSK with a robust password. On all my PSK networks I make a point to use a 15- to 20-character password. Here’s one of my favorites (please don’t hack me): ioncelivedinsedalia. Wireless Authentication Protocols We’ve spent some time discussing wireless encryption, as well as wireless authentication, between a simple wireless client and its access point. Most of the discussion has been very general and could apply to small home wireless networks, small business networks, and even, to a degree, large enterprise-level wireless networks. Now let’s take a moment to talk about the enterprise side of wireless networking, which usually involves more complex authentication methods and may involve using a wireless network to connect into a larger corporate wired network. We’ll talk about different authentication methods and protocols that are primarily used in enterprise infrastructures, particularly when using the more advanced features of WPA and WPA2. EXAM TIP Authentication protocols, as the name suggests, authenticate users to a network. Cryptographic protocols provide security mechanisms, such as encryption. Secure networks, wireless as well as wired, require use of both types of protocols. 802.1X 802.1X is an IEEE standard, just like the 802.3 Ethernet standards and 802.11 wireless networking standards. The great thing is that, while 802.1X is probably encountered most often on corporate wireless networks as the preferred form of authentication and access management control, it is not a wireless standard at all and can be used in wired networks as well. This actually makes it easier for wireless and wired networks to 07-ch07.indd 377 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 378 interoperate, since they can use the same authentication methods and can connect to each other quite easily. 802.1X is called a port-based access control method and can use a wide variety of different security protocols. In that respect, it’s more of a security authentication framework than a protocol itself, since it allows various protocols to be used for authentication. 802.1X uses some interesting terms you may need to be familiar with for the exam. First, a wireless client device is known as a supplicant in an 802.1X environment. A wireless access point that uses 802.1X authentication methods is called the authenticator, and the source providing the authentication services to the wireless network is called the authentication server. 802.1X is interoperable with a number of remote access services and protocols, such as RADIUS and TACACS+, as well as centralized authentication databases such as Active Directory. This enables wireless clients to authenticate to traditional infrastructures using these different types of services. 802.1X can use several different types of authentication protocols, such as EAP, EAP-TLS, EAP-TTLS, PEAP, LEAP, and EAP-FAST. Let’s check out this string of acronyms now. EAP Like the 802.1X authentication protocol, the Extensible Authentication Protocol (EAP) isn’t so much a protocol as a security framework that provides for varied authentication methods. Many different protocols fit into the EAP framework, and that’s really why it was devised in the first place. EAP recognizes that there are several different authentication methods, including certificate-based authentication and other multifactor authentication methods, such as smart cards and so on. EAP can still allow the traditional user name/ password combination of authentication as well. EAP also allows for mutual authentication between devices as well as directory-based authentication services. There are several different variations of EAP, some older, and some more suitable for use than others. These include EAP-TLS, EAP-TTLS, PEAP, and EAP-FAST (plus others you won’t see on the exam). Let’s cover the EAP versions mentioned in the CompTIA Security+ exam objective. EAP-TLS EAP Transport Layer Security (EAP-TLS) was for years the primary EAP variation used on high-security wireless networks. As the name implies, EAP-TLS uses the same TLS protocol used on secure Web pages. EAP-TLS requires both a server-side certificate and a client-side certificate (client-side certificates are rarely used on Web pages, but the TLS protocol certainly supports their use). Client-side certificates are an administrative headache because every laptop, smartphone, tablet, or printer on the network must have a unique certificate. Losing a device requires disassociating the missing device’s certificate to ensure security. If you want the ultimate in 802.11 authentication security, however, EAP-TLS is the way to go. EAP-TTLS EAP Tunneled Transport Layer Security (EAP-TTLS) may share a similar-sounding acronym to EAP-TLS, but it is a completely different EAP variation (Figure 7-5). EAP-TTLS 07-ch07.indd 378 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-1: Networking with 802.11 379 Figure 7-5 Configuring 802.1X on a Windows wireless client goes beyond the TLS protocol, adding a tunnel to provide better security. EAP-TTLS only requires a server-side certificate. EAP-TTLS is considered to be functionally equivalent to PEAP (see next). PEAP Protected Extensible Authentication Protocol (PEAP), another version that uses TLS, addressed problems with EAP and was developed as an open protocol by several vendors, such as Microsoft, RSA, and Cisco. PEAP is similar to EAP-TLS and requires a digital certificate on the server side of a connection to create a secure TLS tunnel. There are different versions of PEAP, depending upon the implementation and operating system, but all typically use digital certificates or smart cards for authentication. LEAP and EAP-FAST Lightweight Extensible Authentication Protocol (LEAP) is a proprietary protocol developed by Cisco and was used in their wireless LAN devices for authentication. LEAP uses dynamic WEP keys and provides for mutual authentication between wireless clients and a centralized RADIUS server. LEAP requires wireless clients to reauthenticate periodically, and when they do, they must use a new WEP key. Cisco has replaced LEAP with EAP-FAST (for Flexible Authentication via Secure Tunneling), which addresses LEAP’s security issues. EAP-FAST is lightweight but uses TLS tunnels to add security during authentication. 07-ch07.indd 379 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 380 EXAM TIP The CompTIA Security+ objectives refer to a Remote Authentication Dial-in User Service (RADIUS) Federation authentication protocol, which mashes two terms you explored back in Chapter 3. A federated system involves the use of a common authentication system and credentials database that multiple entities use and share. A RADIUS federation could connect those systems wirelessly using RADIUS servers. Module 7-2: Attacking 802.11 This module covers the following CompTIA Security+ objectives: • 1.3 Given a scenario, analyze potential indicators associated with application attacks • 1.4 Given a scenario, analyze potential indicators associated with network attacks Attacks on wireless networks have never been more common than they are today, but why? Given that 802.11 wireless networks have been around for more than 20 years, you’d think by now we’d be better at securing them. Truth is, we are better, but the bad guys have gotten better as well. Plus, the wireless footprint keeps expanding. Wireless is everywhere. In this module, we’ll discuss various wireless threats and attacks that can be carried out against wireless networks and unsecure wireless protocols (such as the surprisingly still relevant WEPCrack). This module will discuss the attacks at length, so that by the next module, you’ll be ready to learn the various ways you can harden wireless access points and networks against these types of attacks. We’ll also glance at the other wireless standard, Bluetooth, at the tail end to examine attacks along that vector. If you want to do some attacking (of the ethical variety, of course!), the first thing you’ll need are some tools. There are many tools out there to attack 802.11, but in general you’ll need three separate items: • A good survey/stumbler tool to locate wireless networks and obtain detailed information • Some kind of tool to start grabbing wireless packets • Some type of attack tool that analyzes the data you’ve collected and grabs the passwords, keys, credentials, or whatever you want to grab With those concepts in mind, let’s turn to the specific toys in the attacker’s toolbox. You’ll see these on the CompTIA Security+ exam and, hopefully, use them for good in the real world. Wireless Survey/Stumbler To attack a wireless network, you first need to find one to attack. To do this, you use wireless survey/stumbler utilities. There are many such tools. Even the wireless client 07-ch07.indd 380 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-2: Attacking 802.11 381 Figure 7-6 Wi-Fi analyzer on Android built into your operating system easily locates the wireless networks and will tell you the channel and encryption type. That’s OK for users, but if you want to attack, you need a more serious survey tool. You need a survey tool like a Wi-Fi analyzer that not only sees the wireless network but also grabs critical information such as GPS location, WAP MAC address, detailed encryption type, WPS enabled, and so on. Figure 7-6 shows an Android Wi-Fi analyzer I use. Packet Capture Once you’ve found a target, you then need to start grabbing packets. To do this, you’ll need some form of packet-capture tool that grabs wireless packets and gives you some control as to what packets you want to grab. Again, you have choices, but Airodumpng—one of the many powerful tools that are part of the Aircrack-ng wireless suite, is very common and well supported (Figure 7-7). Attack Tools The entire goal of attacking wireless networks is to gather information. Every attack requires some type of utility that helps you do whatever you want to do. Do you want to crack WPS? There’s a tool for that. Want to crack WEP? There’s a tool for that. Want to intercept credentials? There’s yet another tool for that. 07-ch07.indd 381 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 382 Figure 7-7 Selecting a specific WAP with Airodump-ng The problem with any attack tool is that none of these tools are intuitive; you can’t just throw your average script kiddie in front of one of these tools and expect results. The tools are not necessarily difficult to use, but they aren’t so simple that you can plug and chug. With that understanding in mind, there are some pretty great tools out there for wireless attacks. As a starting point, check out the previously mentioned Aircrack-ng, a suite of tools that handles several popular attacks, concentrating on WEP and WPA cracking. CAUTION Please, please, please note that using hacking and cracking tools can land you in jail. That’s not a joke. You can attack your personal systems all you want, of course. That’s how to gain skills. But you need a signed agreement before you turn your newly minted mad hacking skills against an organization. Without that agreement, you risk committing a felony, and that, as we say in the business, is a bad thing. Rogue Access Point A rogue access point can indicate a potential wireless network attack, because it features an unauthorized WAP within a secure network that attracts people to connect to it. A rogue AP can be benign, for example, where a network user sets up a WAP to provide better signal strength in his or her area. As an attack, though, a malicious person deliberately places a rogue AP with the intent to monitor all of the connected victims’ network traffic. In both cases, the rogue AP enables connectivity to the legitimate network. The malicious kind seeks information. 07-ch07.indd 382 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-2: Attacking 802.11 383 Hackers use several techniques to set up rogue APs. In a basic attack, the attacker uses an AP configured for very weak or nonexistent authentication. This makes the victim think that it’s an open or free Internet AP. NOTE Different parts of the wireless industry use either AP or WAP to describe a wireless access point. You’ll see this throughout industry literature and hear it in discussions. The CompTIA Security+ 601 objectives refer to WAPs in one section and rogue access point in another, for example, where the “wireless” part is implied. The same applies to AP—the acronym implies wireless. Often a rogue AP will broadcast a very strong signal so that users think it’s the best free Internet access point compared to several others. Rogue APs work very well where there are several APs already transmitting, such as areas within range of businesses or establishments that offer free wireless access to their customers. In another variation of this attack—called an evil twin attack—a hacker sets up a rogue AP that broadcasts the same (or very similar) Service Set Identifier (SSID), which appears as the wireless network’s name to ordinary users. Often, however, the evil twin does not use the same security level as the legitimate AP, making it easier to connect to the evil twin. Unsuspecting users connect to this AP, thinking that it’s one to which they normally should connect. Once connected to the evil twin’s network, the attacker can intercept the user’s network traffic through the evil twin, including user names, passwords, and any other traffic passed over the AP. The evil twin attacker can gain user credentials that may also be used on other wireless networks, allowing the attacker to connect to the legitimate APs and begin an attack on those networks. The hacker may even further connect this rogue AP to the Internet, so the user never suspects that she is connected to the rogue AP. Figure 7-8 shows an example of how an evil twin wireless network also appears with a legitimate one. Notice that the two are named similarly but are not configured the same in terms of required security. Jamming Occasionally, a wireless network can experience interference from another wireless device, which can occur, for example, when two wireless access points use adjacent frequencies or channels. Interference can interrupt and interfere with wireless network transmission and reception. For the most part, this interference is unintentional. Jamming is a form of intentional interference on wireless networks, designed as a denial-of-service (DoS) attack. This type of attack overpowers the signals of a legitimate wireless access point, typically using a rogue AP with its transmit power set to very high levels. Attackers can use other electronic devices as well to create interference, or jamming, in wireless networks, including specialized devices easily acquired from the Internet or put together by hobbyists. Jammers are also commonly used to help evil twin attacks. By jamming a legitimate WAP’s channel, all clients will automatically try to go to the evil twin (Figure 7-9). Even 07-ch07.indd 383 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 384 Figure 7-8 An evil twin rogue wireless access point is named similarly to a legitimate network AP. if your legitimate WAP tries to switch to another channel, a good jammer tracks the channel changes and continues to jam. The only way to prevent jamming and interference is to look proactively for sources of wireless signals that are not coming from the corporate wireless network. The sources are usually in the same frequency range and may come from malicious wireless clients or rogue wireless access points. NOTE Legally owning a jammer requires appropriate permission and licensing. In many countries even owning a jammer is illegal. Figure 7-9 Jammer working with an evil twin Jam channel 6 with Wi-Fi jammer Legit WAP on channel 6 SSID: Thunderbird 07-ch07.indd 384 Evil Twin WAP on channel 1 SSID: Thunderbird 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-2: Attacking 802.11 385 Figure 7-10 Packet sniffing a wireless network Packet Sniffing Just as with wired networks, attackers can sniff wireless networks for unencrypted data to capture and analyze, although the techniques and tools required differ. Usually, an attacker has to have a special wireless network card that can intercept packets and inject traffic on to the network. The attacker usually also must have a special driver for the network card, if he is using the Windows operating system, or he must put a network card into what’s called monitor or promiscuous mode in Linux. Once the attacker has his equipment set up, it’s simply a matter of using the sniffing software of choice, such as Wireshark, for example. Figure 7-10 shows a Wireshark capture of a packet sniffing session conducted on a wireless network. NOTE All wireless sniffer tools require a special wireless NIC driver. Deauthentication Attack Encrypted wireless communication, as you might suspect, does not enable an attacker to run simple tools to capture data and glean important or sensitive information. That’s the point of encryption, right? An attacker can grab beacon frames and management traffic and a bunch of encrypted traffic he can’t read. The 802.11 frames that make the initial connection between a WAP and a wireless client offer a unique attack vector. These standard management frames enable a client to connect, then establish credentials and so forth so that encrypted communication can happen happily. 07-ch07.indd 385 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 386 Figure 7-11 Conducting a deauthentication attack against a wireless client and its AP In a deauthentication attack, a malicious actor sends a deauthentication frame to the WAP with a spoofed MAC address—picked up by simple sniffers in the clear from traffic between the WAP and the intended target client. The WAP dutifully disconnects the client (or station, as the Wi-Fi folks like to say). The client will then automatically try to reconnect—associate—with the WAP. What happens after this DoS attack (“I deny you access to the WAP!”) depends on the bad guy’s intent. The client could unsuspectingly connect with an evil twin WAP and the bad guy could use various attacks—man-in-the-middle attack, brute-force attack, and so on—to get the client’s password. Once the attacker has the password in hand, it’s game over for the client. The bad guy could just be a jerk, doing a DoS for some sick laughs. Regardless of the subsequent actions, the deauthorization attack starts the process. Figure 7-11 shows an example of a deauthentication attack, conducted using the aireplay-ng command in the Aircrack-ng tool suite. This tool is popularly found on Linux-based systems, particularly security distributions. EXAM TIP You’ll hear the term disassociation attack as a form of deauthentication attack. Near-Field Communication Near-field communication (NFC) enables devices to send very low-power radio signals to each other by using a special chip implanted in the device. NFC requires that the devices be extremely close—like within four inches—to each other. NFC can be used for a wide variety of consumer and business applications, including quick payments with NFC-enabled smartphones and cash registers, parking meters, and other really cool and convenient transactions. NFC uses radio-frequency identification (RFID) technologies and, unfortunately, is vulnerable to several types of attacks. These attacks include eavesdropping by another NFC device, man-in-the-middle attacks, and relay attacks (relaying modified information back and forth from the victim’s device, pretending to be the victim). Many WPS-enabled devices (see “WPS Attacks” later in this module) also use NFC, making wireless hacking of WPS-enabled networks easy. 07-ch07.indd 386 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-2: Attacking 802.11 387 Here are my credentials. Got them! I got them too! Figure 7-12 A replay attack starts with a man-in-the-middle. Replay Attacks In a replay attack, data, particularly credentials such as user names and passwords, is intercepted and replayed back on the network to an unsuspecting host. The goal of the replay attack is to retransmit those credentials back to a host, effectively allowing the attacker to impersonate the victim. Credentials or other data passed in clear text is most vulnerable to replay attack, although certain versions of weak encryption algorithms can also be vulnerable to these types of attacks. Even if the attacker can’t read the victim’s credentials due to encryption, weak authentication methods may allow retransmitted credentials to be used to authenticate to a host. Note that this type of attack isn’t unique to wireless networks; wired networks also suffer from replay attacks (Figure 7-12). Strong encryption methods help defend against this type of attack. Another defense against this attack is through the use of timestamping, which limits the use of the credentials to a very narrow time period. The use of the Kerberos authentication protocol in Windows Active Directory networks, which makes heavy use of time stamps, counters replay attacks. Still another way of defending against this type of attack is for the originating host to digitally sign the traffic it sends. This assures the receiving host that the credentials or other data it receives is authentic. EXAM TIP The CompTIA Security+ objectives categorize a replay attack as a type of application attack. Others that fall into this category are DLL injections and privilege escalation attacks that you saw back in Chapter 5. You’ll see many more in Chapter 11. WEP/WPA Attacks Like any streaming encryption, RC4 needs initialization vectors (IVs) to seed its encryption methods for protecting wireless traffic. Unfortunately, the IVs in WEP are considered weak, in that they are only 24 bits in length. This short length guarantees that WEP must repeat the IVs frequently, meaning that after sniffing a few million packets, an attacker can crack the WEP key mathematically (an IV attack). Today a number of off-the-shelf tools (such as the freeware Aircrack-ng) make cracking any WEP-encrypted SSID easy. 07-ch07.indd 387 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 388 WPA has its weaknesses. It uses RC4 encryption, and cracking methods were developed to crack WPA—although it is much harder to crack WPA than WEP. Although both WPA and WPA2 are very strong wireless security protocols, if your SSID uses a pre-shared key with a weak passphrase, they are both easily cracked, since the four-way handshakes they use to negotiate a connection between devices contain the WPA/WPA2 encryption key. This four-way handshake can be intercepted after a deauthentication attack forces a wireless client and AP to reestablish their connection and reauthenticate with each other. Once intercepted, a weak key can be cracked using standard dictionary or brute-force attacks, again using tools such as Aircrack-ng. WPS Attacks A WPS-enabled wireless router can connect to another WPS device (wireless printers are the most common) through a number of different methods. These methods all use a WPS personal identification number (PIN), which is enabled simply by pushing a button on the wireless router and the device. This PIN is used as the network’s secure WPA key. This WPS PIN is susceptible to brute-force attacks. EXAM TIP The CompTIA Security+ exam might query you about an attack used in older Microsoft networks. A pass the hash attack takes advantage of weak points in the NT LAN Manager (NTLM) and LANMAN protocols. If the attacker has the hash of a user’s password, the attacker can skip any kind of brute-force attack and use the hashed password to access the network. Modern Windows systems mitigate against this sort of attack, though the best defense is to not allow network administrators to log in to suspect systems and thus expose their passwords. Wireless Peripherals Wireless peripherals such as wireless keyboards and wireless mice are common and convenient, freeing us from messy cables and allowing more freedom of configuration. The problem with wireless peripherals is that they typically use Bluetooth as the wireless connection. Although Bluetooth is a mature and secure technology, an improperly configured Bluetooth peripheral is easy to hack. Let’s take a moment and talk about the two old but still valid Bluetooth attacks, bluejacking and bluesnarfing. NOTE Bluetooth is not Wi-Fi, but a different wireless standard that you’ll recall from CompTIA A+ or CompTIA Network+ studies. Bluejacking Although becoming rarer these days, Bluetooth attacks happen. In the early days of Bluetooth, protocols did not have adequate security measures built in, and devices by default allowed themselves to connect with any Bluetooth device that requested it. This enabled 07-ch07.indd 388 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-3: Securing 802.11 389 attackers to connect their Bluetooth device surreptitiously with an unsuspecting person’s device and steal information from it, such as contacts and other personal information. These attacks are becoming rare because the Bluetooth protocol has evolved over time, and now more security measures are built into the protocol by default. Additionally, most Bluetooth devices have to undergo a type of authentication with each other, called pairing, which makes intercepting traffic between them more difficult. Another factor contributing to the rarity of these types of attacks is that Bluetooth has a very limited range: an attacker would have to be within around 35 feet of the victim to conduct the attack successfully. Legacy devices still in use, however, as well as new devices improperly configured for security, are susceptible to Bluetooth attacks. One of the classic attacks on Bluetooth is called bluejacking. Bluejacking involves sending data to a target device, such as a smartphone, usually in the form of unsolicited text messages. Although mostly harmless, bluejacking can be annoying at best and constitutes harassment at worst. Bluejacking does not involve removing data from the device. Bluesnarfing Bluesnarfing is yet another classic Bluetooth attack, in which the attacker steals data from the target device by connecting to an unsuspecting user’s device. Bluesnarfing can be used to get contacts, e-mails, text messages, pictures, videos, and other sensitive data. Once again, this type of attack is very rare these days, since most vendors have fixed vulnerabilities in their device operating systems and because of upgrades to the protocol itself. You can stop both bluejacking and bluesnarfing attacks easily by making sure you don’t leave your device in discoverable mode to prevent anyone from pairing to your device. Module 7-3: Securing 802.11 This module covers the following CompTIA Security+ objective: • 3.4 Given a scenario, install and configure wireless security settings Despite what you might think after reading the many scary stories from the previous module, it’s not difficult to create a robust and secure 802.11 wireless network. This module discusses a number of installation considerations, security features, and administration tools to make a Wi-Fi network as secure as possible. Installation Considerations Network design that incorporates wireless connectivity offers choices these days in the type of access points to use, site surveys, and WAP placement. Let’s start with installing WAPs. Fat vs. Thin Access Points An organization’s choice of which technology to employ to provide wireless connectivity depends on several factors, including the location and complexity of its primary office network and the design philosophy and needs of individual enterprise offices. You’ll hear 07-ch07.indd 389 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 390 the terms fat and thin access points to describe various APs, and we’ll look at those in detail next. Terms aside, the choice boils down to where you want to manage the security on the network. A fat AP has all the bells and whistles, including a management console where you can configure typical security controls, such as access control lists (ACLs), allow and block lists, encryption, and so on. A fat or thick AP is also called a controller-based AP. You manage each fat AP individually or, in the case of some vendors, manage all APs by sending them instructions from a global console to enact locally. A thin AP typically just acts as a repeater, taking the wireless signal and pushing it to a managed access control (AC) switch that handles encryption and other security. A thin AP is referred to as a standalone AP. Here’s an example of how design philosophy, location, and complexity dictate which technology to employ. A standalone satellite office in Brazil might need a fat AP to handle the wireless needs of its ten users and provide connectivity back to the home office. A building with multiple floors and hundreds of users might rely on one awesome switch (plus a redundant backup) to control dozens of thin access points. Site Surveys In a site survey, a network tech makes a technical assessment of the area in which a wireless network will be installed and operating. Usually, the tech performs a site survey before installing the wireless network, although sometimes it might be performed periodically when looking at network performance or before expanding the wireless network to accommodate new access points or additional capacity. Site surveys help technical personnel understand the different issues that may be present in an area where the wireless network will be operational. These issues may affect considerations such as area coverage, network growth, access point and antenna placement, required power levels, and even network capacity (level of usage of the wireless network). NOTE Security professionals in the field of penetration testing love fake site surveys. People simply ignore folks walking around with a clipboard and survey uniforms…. This is social engineering—manipulating people to get into systems—at its finest. Chapter 12 covers social engineering techniques in detail. Some of these issues include proximity to potential interference sources, channel overlaps from other SSIDs in the area, environmental and physical considerations (physical obstacles that may limit wireless signals, such as buildings, for example), and, of course, potential security issues (public areas where war driving may happen, for instance). A Wi-Fi analyzer tool will scan an area for existing wireless networks, providing essential information for assessing an area for potential problems or obstacles when planning an installation of a Wi-Fi network. Figure 7-13 illustrates some of the data collected during a survey when using a Wi-Fi analyzer tool, in this case inSSIDer from MetaGeek (www.metageek.com). A quick scan of a local area shows many networks, including named and hidden; the signal strength relative to the position of the scanning device in 07-ch07.indd 390 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-3: Securing 802.11 391 Figure 7-13 Viewing the Wi-Fi spectrum when performing a site survey decibels (lower number is stronger); number of radios, the security level, such as WPA, WEP, WPA2, open; and mode, such as 802.11b/g for the open network and 802.11a/b/ g/n/ac/ax for one of the locked down networks. Additionally, the screenshot shows the Madrid network selected so you can see the channels in use graphically in the lower third of the screen—3 and 11 in the 2.4 GHz band; 34, 46, and 50 in the 5 GHz band. EXAM TIP Wi-Fi networks use radio-frequency spectrums or bands split into channels, which you might recall from your CompTIA Network+ studies. The 2.4 GHz band has a fairly small number of channels, several of which overlap. Excessive traffic on overlapping channels—even with separate SSIDs— can cause problems. This is sometimes referred to as adjacent-channel interference, which the CompTIA Security+ objectives shorten to channel overlaps. When conducting a site survey, a technician measures potential coverage distances, identifies obstacles that may block wireless signals, and performs various tests to determine optimal placement of antennas and access points. The technician will usually map out the area and identify potential sources of interference, such as power cabling, cell towers, or other radio-frequency interference (RFI)–producing sources. Technicians also should plan for capacity, meaning that they need to know how many users will connect to the wireless network at any given time and what types of data or applications they will use over the wireless network. 07-ch07.indd 391 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 392 Figure 7-14 AirMagnet Survey Pro There are plenty of tools to support a wireless survey, like AirMagnet Survey Pro (Figure 7-14). All good survey utilities share some common ways to report their findings. One of the most powerful reports that they generate is called a heat map. A heat map is nothing more than a graphical representation of the radio-frequency (RF) sources on a site, using different colors to represent the intensity of the signal. Figure 7-15 shows a sample heat map. Some companies take heat map tech to the minute, showing the precise location of User Joe in the building based on his network traffic. This can be a great tool. Although this might not seem like a security consideration, remember that availability of data is directly tied to security (remember the CIA triad: confidentiality, accountability, integrity). After completing the site survey, the technician usually provides recommendations to managers and the team that will install or expand the wireless network, so they can configure it optimally for both performance and security. WAP Placement Wireless access point (WAP) placement matters not only in making sure that people can get a strong enough signal to access the wireless network, but also for security reasons. A WAP with a standard omnidirectional antenna located too close to an outer wall of a facility makes the wireless signal easier to pick up outside the facility, which makes 07-ch07.indd 392 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-3: Securing 802.11 393 Microwave e Reinforced Rein nfo f rced Wall Wall Refrigerator Microwave Figure 7-15 Site survey with heat map it easier for bad actors to pick up the wireless signal and attempt to hack the network. Ideally, both for performance and security reasons, centralize WAP placement within a facility; in other words, place WAPs with omnidirectional antennas centrally throughout different areas of the facility so that they can adequately span all areas of coverage within a facility, without being too close to exterior walls or the roof whenever possible. Place a WAP with a directional antenna, in contrast, so that the signal points to the area of desired coverage. Placing such a WAP on the inside of an outer wall, pointed into the interior, can provide excellent coverage with little chance of signal spillage. Wireless Configuration A good layout of enterprise-level WAPs, properly placed and using the right antennas, is a great start for any wireless network. Now it’s time to take advantage of the many 802.11 features to protect your network. Controller and Access Point Security No wireless network has any hope of security without serious consideration of controller and access point security. Start with the basics in a SOHO network and replace default passwords for any wireless access point to something much more secure. Also, if possible, change any factory-configured SSID passwords. (See Figure 7-16.) Don’t use the same password on every WAP. Finally, be sure to restrict physical access to the WAP. 07-ch07.indd 393 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 394 Figure 7-16 Factory passwords are well known. MIKEOSOFT WAP MODEL 234567 Part Number: 23593837499 S/N: 2223-1234544-0 SSID: MIKEOSOFT1 WPA2 PWD: Everyoneknowsthis You’d be shocked how often admins use the default password or the factory configured password! Once you get beyond a SOHO network, as you’ll recall from your CompTIA Network+ studies, access point management becomes more centralized. A typical mediumsized organization, for example, might deploy a dozen managed access points across their offices that require a controller to handle setup, configuration, and security. You secure access to the controller software the same way you secure access to any critical application, through proper account management, as in making sure only the appropriate user accounts can access the controller software. When you scale up further—think campus area network (CAN) here with 100+ APs—many organizations use dedicated hardware AP controllers to configure access point security. Secure access to the AP controllers just as you would any mission-critical network appliance, through limiting physical access as well as proper account management. SSID Broadcasting The SSID is the wireless network name. This name is usually broadcast out to let wireless clients know that it exists. Nontechnical users rely on SSID broadcasting to locate and connect to networks. The SSID has absolutely nothing to do with security. Early in the wireless revolution, standard security practices held that to secure a wireless network, you should keep the SSID from broadcasting; this was a practice called SSID hiding or cloaking. This practice prevented casual wireless snooping and was meant to keep unauthorized people from connecting to a wireless network. The theory was that if they couldn’t see the network name, they couldn’t connect to it. These days, most wireless network clients can pick up all the nearby wireless networks, even if they have cloaked SSIDs, as you can see in the Wi-Fi analyzer scan in Figure 7-13, above. And you can easily install software on a wireless client that can tell you what the wireless SSID is, simply because wireless clients can also broadcast SSID information out. Even if people can’t see the network name, they will see that an unknown wireless network does exist. Then a determined hacker can connect to it. In addition to cloaking SSIDs, some security administrators also recommend renaming the SSIDs from the default wireless access point name that is usually broadcast when you first install an access point. This may be a good idea to help users connect to the 07-ch07.indd 394 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-3: Securing 802.11 395 correct network, but from a security perspective it isn’t effective and may actually confuse users, causing them not to be able to connect to a wireless network. EXAM TIP An SSID has nothing to do with security. It’s just the network name for a Wi-Fi network. MAC Filtering Remember that the MAC address is burned into every single network card manufactured, including wireless network cards, and these addresses are used the same way. The MAC address is a 12-digit hexadecimal number that identifies the manufacturer of the card and the individual card itself. Because it can identify the individual network card, and by extension the client, some administrators filter wireless network access by the MAC address of the client. Most wireless access points have the ability to do MAC filtering, as you’ll recall from Chapter 6, either allowing or denying a particular MAC address (and the host that has the MAC address) on the network. MAC filtering is frequently used as a security measure, since it can deny access to wireless network cards that are listed in a table on the access point. However, you should know that it’s quite simple to spoof a MAC address, so, like SSID cloaking, this isn’t an effective security measure and should not be used by itself to protect a wireless network. The other part about MAC filtering is that if you use it as a security measure (in conjunction with other more secure measures, hopefully), you should configure MAC filtering to allow certain MAC addresses only, rather than attempt to deny certain MAC addresses. This is simply because you can deny only what you know about; of course, it’s difficult to deny a MAC address that you don’t know exists. So MAC address filtering should be used on a default deny basis (deny all), with only a few addresses as exceptions. Figure 7-17 shows my home WAP’s MAC filtering settings. Power Level Controls You may be tempted to think that boosting the power on your wireless access point gives you better performance and enables your clients to connect to your network with a stronger signal. You’d be right about that, except for a couple of things. The first thing is that raising the power levels on your WAP beyond a specified level may be illegal in certain areas. Most WAPs have preset power levels, usually a balance between what’s legally acceptable in its intended region and performance requirements. It isn’t too difficult to download nonstandard firmware or software that allows you to change those power levels, however, sometimes beyond the legal limit allowed in your area. The second thing is that the higher power levels on your WAPs can adversely affect the security on your network. This is because the more powerful the signal, the farther out that signal will transmit. So, in addition to all of your authorized clients being able to see the wireless network, get a really good signal, and connect to it, unauthorized people (read: hackers or people looking for free Internet connectivity) will also be able to do the same thing. In addition to limiting omnidirectional-antenna WAP placement to centralized areas within your facility, you should reduce antenna power levels on those WAPs to the lowest 07-ch07.indd 395 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 396 Figure 7-17 Configuring MAC filtering acceptable point at which users can still receive a strong signal from the network. This prevents the signal from leaving your facility as much as possible. You may even have to lower the power levels and simply provide more access points throughout the facility to keep the signals confined to the immediate area as a sort of trade-off. It’s probably not realistic to think that you’re going to be able to limit stray signals fully, but limiting them to as short a distance as possible outside your facility can help your security posture, since any would-be hacker may have to get unacceptably close to your building to hack into or connect to your network. Captive Portals Many organizations set up Wi-Fi networks so clients default to a captive portal when logging in. A captive portal is a Web page that prompts clients to enter proper credentials to gain further access to the network (Figure 7-18). This enables the organization to control 07-ch07.indd 396 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Module 7-3: Securing 802.11 397 Figure 7-18 Mike’s captive portal or limit access to clients accessing from an acceptable location and with proper authentication. You’ll see captive portals used in many hotels, for example, as a way to provide paying guests access to the Internet via Wi-Fi and stopping freeloaders from getting in and leaching bandwidth. Captive portals provide a secure method for authenticating a wireless client in a couple of ways. First, it may be impractical to share a pre-shared key or device certificate with everyone who is authorized to use the wireless network (think airport customers or hotel guests, for example), but the wireless network may still require some sort of authentication. A captive portal setup allows a wireless client to connect to the wireless network and reach only a single Web site, where the users must authenticate to the wireless network before they can use it any further. A business may provide wireless access for its external partners or customers rather than allowing them to use its interior corporate wireless network. The captive portal would help serve such a function in this case. It enables authentication and can assist in accounting for wireless network access that has been paid for by a customer. For authorized employees connecting to a corporate network, a captive portal can also serve as a type of network access control (see Chapter 6 for more details on NAC), since an otherwise authorized wireless device may have to use certain protocols or have certain requirements present to connect to the network (patches, antivirus signatures, and so on). Security Posture Assessment Part of a network professional’s job is to use tools to assess the security posture of a network. With wireless networks, that means to run assessment tools to probe the network, looking for any errors in implementation or any weaknesses. 07-ch07.indd 397 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 398 The cool part for you is that you already know the assessment tools—you used them to attack wireless networks in Module 7-2! Use Aircrack-ng, Wireshark, and any number of Wi-Fi analyzers and wireless scanners/crackers to probe wireless networks. Organizations often hire third parties to assess a network security posture. Many companies have created in-house groups dedicated to performing and maintaining posture assessments. Questions 1. Erin is tasked to design a wireless network for the new wing of her office, which consists of two large rooms with cubicles. Her budget allows for two high-end WAPs that support WEP, WPA, WPA2, or WPA3 or four medium-end WAPs that support WEP, WPA, or WPA2. In such a scenario, which option will provide the best security? A. Install the two high-end WAPs enabled for WPA2 to provide the best coverage and security. B. Install the two high-end WAPs enabled for WPA3 to provide the best coverage and security. C. Install the four medium-end WAPs enabled for WPA to provide the best coverage and security. D. Install the four medium-end WAPs enabled for WPA2 to provide the best coverage and security. 2. Ellen gets a call from a local café she provides tech support to, complaining that some users on older devices can’t connect to the newly upgraded WAP (but they could connect to the previous WAP). What could be the problem? A. She set up the WAP to use WPA and TKIP. B. She set up the WAP to use WPA2 and only AES. C. She set up the WAP to use mixed mode. D. She set up the WAP in open mode. 3. Which Cisco authentication protocol provides the best wireless security? A. 802.1X B. EAP-TLS C. EAP-FAST D. LEAP 4. Jane runs a coffee shop that shares walls with two other businesses. She wants to install a Wi-Fi network for her clients, but wants to make sure she’s neither sharing the network with the other businesses nor interfering with their wireless 07-ch07.indd 398 25/03/21 2:16 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Questions 399 networks. She has the option of installing one or more 802.11ac WAPs with omnidirectional antennas. What’s her best option in this scenario? A. Jane should install one WAP in the center of her establishment. B. Jane should install one WAP in the center of her establishment and then reduce the power level. C. Jane should install one WAP in the center of her establishment and then increase the power level. D. Jane should install two WAPs, one on either wall, and point the antennas to the center of her establishment. 5. Andre wants to hack a Wi-Fi network (for learning purposes!). Which type of tool would enable him to find the wireless signals to start the attack? A. Wireless survey B. Packet capture C. WEP cracking D. WPA cracking 6. Which of the following can happen if an attacker sets the power levels on a rogue access point to overpower the wireless transmissions of a legitimate access point? A. Jamming B. Beaconing C. Deauthentication D. Spoofing 7. Jaime was working on a term paper at the local café and noticed that her connection to the WAP kept dropping. Her system would reconnect rapidly, but the behavior was odd. Which of the following kind of attack would most likely create this scenario? A. Bluejacking B. Deauthorization attack C. Jamming D. Replay attack 8. Which of the following technologies requires that two devices be within four inches of each other in order to communicate? A. 802.11i B. WPA C. Bluetooth D. NFC 07-ch07.indd 399 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 7 Chapter 7: Securing Wireless LANs 400 9. Ezra has been tasked to provide for a hotel a Wi-Fi solution that enables hotel staff to control who can access the wireless resources. The solution should include both location and login authentication. What might accomplish those goals? A. Captive portal B. Disable SSID broadcast C. MAC filtering block list D. MAC filtering allow list 10. Which of the following options will provide a graphical representation of the wireless signals—including their strength—in a site survey? A. Bluesnarfing B. Captive portal C. Heat map D. RFID map Answers 1. B. WPA3 completely trumps earlier Wi-Fi encryption standards in terms of security. 2. B. Most likely, Ellen set up the WAP to allow only traffic encrypted with WPA2 and only AES. Although it will reduce security, changing the WAP to mixed mode would provide support for older Wi-Fi clients. 3. C. Of the two Cisco authentication protocols listed here, EAP-FAST offers way better security (through TLS) than LEAP (WEP and RC4). 4. B. It’ll require some experimentation, but reducing the power level for a centered WAP should make the signal available only for her customers. Such a setup reduces signal bleed into other spaces. 5. A. Starting with a wireless survey or stumbler tool would enable Andre to find the signals he wants to capture. He could follow up with a packet capture tool, like Airodump-ng, and then hammer the packets for content with an attack tool. 6. A. Jamming, intentional interference on a wireless network to cause denial of service, can occur if an attacker sets the power levels on a rogue access point to overpower the wireless transmissions of a legitimate access point. 7. B. Although you could make an argument for a jamming type of attack, this is most likely a deauthorization attack, kicking Jaime’s system off the WAP in hopes that it would connect to an evil twin WAP. 8. D. Near-field communication (NFC) requires that two devices be within four inches of each other in order to communicate. 9. A. Creating a captive portal would provide the desired solution, especially the login authentication. 10. C. A heat map provides a graphical representation of the wireless networks—and their relative signal strengths—in an area. 07-ch07.indd 400 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 CHAPTER Securing Public Servers 8 With Cloud Computing, it is no longer a question of If, but rather When and How. —Ludmila Morozova-Bussva The world accesses public servers—resources on the Internet—to live and prosper in the global economy. IT security professionals must secure public servers or the world will simply fail. (Dramatic enough intro to this chapter? It’s good stuff, so read on!) This chapter explores how security professionals deal with public servers, emphasizing cloud computing, in four modules: • • • • Attacking and Defending Public Servers Virtualization Security Cloud Deployment Securing the Cloud Module 8-1: Attacking and Defending Public Servers This module covers the following CompTIA Security+ objectives: • 1.4 Given a scenario, analyze potential indicators associated with network attacks • 2.2 Summarize virtualization and cloud computing concepts • 3.3 Given a scenario, implement secure network designs Anytime you connect a server to the Internet, you expose that server to all the evils and troubles lurking out there. The fact that anyone can at least attempt to connect to your server gives bad actors with access to a DNS name or IP address a lovely attack surface, thus giving them the opportunity to try to do something nefarious to your server. This module first describes a distributed denial-of-service attack and then discusses some of the tools used to secure public-facing servers and mitigate the effect of these attacks. 401 08-ch08.indd 401 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 402 Distributed Denial-of-Service If a bad actor wants to disrupt your organization’s normal operations, one of the most disruptive actions they can attempt is to make one of your Internet-connected servers stop working so that server can no longer provide essential resources. There are plenty of ways to attempt this, but for the most part security professionals have learned from experience how to stop the vast majority of attacks, with one exception. A distributed denial-of-service (DDoS) attack is when many systems send requests to a server with the goal of swamping the server with clients so that it responds too slowly for legitimate users or, in some cases, causes the server to reboot/lockup/fail in some way (Figure 8-1). The attack can stop a specific application (such as a Web server) or drop an entire network if successful. DDoS attacks on operational technology (OT) sites such as power plants that might be running on older systems can prove particularly disruptive and devastating. NOTE A denial-of-service (DoS) attack involves one system sending lots of requests to a single server. A DDoS attack is when hundreds, if not thousands, of systems send requests to a single server. So how do we get lots of systems to work together to attack a specific server? Why, malware of course! A bad actor might send hundreds of thousands of e-mail messages to infect as many systems as possible. The zombie computers may run for months with malware that doesn’t affect the systems . . . until it’s time to attack! The problem with this simple DDoS attack is the fact that most servers are designed to handle a huge number of requests per second. To make the server work harder, attackers Figure 8-1 The basic DDoS One moment please! HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... HTTP ACK REQUEST...HTTP ACK REQUEST... Web Server DDoS Attackers 08-ch08.indd 402 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-1: Attacking and Defending Public Servers 403 not only send lots of requests, they do things to the requests so the server has to spend relatively large amounts of time per request to deal with them. Here are a few ways an attack can do this: • Send lots of UDP packets to random port numbers on the server, making it respond to them with errors • Use lots of bogus IP addresses, forcing the server to wait for a response from a client that doesn’t exist • Send intentionally mangled requests, forcing the server to try to read them and hopefully timeout (Figure 8-2) • Send lots of requests without ever responding • Send lots of requests but respond just slow enough that the server keeps the connection • Take advantage of some weakness in the server software to make bad things happen Keep in mind that each of these ways is just a strategy. There are many methods that are useful in DDoS attacks. DDoS attacks plague networks today. As quickly as certain forms of attacks are discovered and stopped, bad actors only need to make subtle changes as they discover new weaknesses and then repeat the same types of attacks. Protecting public-facing servers from DDoS starts with making server configuration secure. Can’t...Keep...Up... Arrggg!!! Malformed ACK REQUEST...Bad ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Malformed ACK REQUEST...Bad ACK REQUEST... Bad ACK REQUEST...Malformed ACK REQUEST... Web Server Extra Evil DDoS Attackers Figure 8-2 Making DDoS harder 08-ch08.indd 403 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 404 Route Security Routers enable networks to interconnect. Network engineers focus on secure network design principles with routers to ensure the information that enables that interconnectivity stays safe and uncorrupted. The details of the routing tables matter. A lot of this you’ll remember from your CompTIA Network+ (or equivalent) studies, that every routing protocol—RIPv2, BGP, EIGRP, OSPF—supports route authentication. Neighbor authentication, for example, makes certain that routers know which neighbor to trust and accept only reliable routing information. Protections such as this prevent bad routes from getting into routing tables and stop naughty information, like malformed packets, from messing up routing. Implementation of route security measures goes well outside the scope of CompTIA Security+. But you need to know that ensuring route security is an essential part of network design. Quality of Service The quality of service (QoS) router feature enables you to control the bandwidth of different protocols coming through a router. With QoS you can assign a minimum or a maximum bandwidth set either as a percentage of the router’s total bandwidth or as a set speed (MB/sec, for example). The QoS feature makes sure that certain protocols never max out the router and ensure that critical protocols always have adequate bandwidth. Figure 8-3 shows a typical implementation of QoS that sets the maximum any application on the network can grab, thus making sure other applications have bandwidth too. QoS is also a relatively handy way to provide some security to your router. Let’s say that you want to enable SFTP on your router but only to occasionally update a single small file. This will never take much bandwidth, correct? So why not give SFTP only a tiny amount of bandwidth just in case a bad actor wants to try to use it to do a lot of downloading? It won’t stop them, but it will slow them down dramatically. Monitoring Services It’s generally a bad thing if a public-facing server stops serving. The server’s administrators need to know as soon as possible if any issue arises that prevents the server from serving on a timely basis. The only way to determine a server’s status is by monitoring the server. Monitoring might be as simple as trying to log onto the server or as complex as using remote tools to query logs and events and comparing them to baselines to see how the server is performing. File integrity monitors, for example, check for baseline deviations and can alert administrators of problems. Basically, any file integrity monitoring (FIM) needs to answer these three questions: • Is the system up? • Is the system too busy? • Are strange things happening? 08-ch08.indd 404 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-1: Attacking and Defending Public Servers 405 Figure 8-3 Smart Queue Management QoS on a Ubiqiti EdgeMAX router System monitoring is a thankless job but a necessary one. Any competent administrator should have little difficulty setting up a monitoring system, but start adding more servers (and more servers requiring 24/7 monitoring), and the workload becomes unrealistic for all but the largest of organizations. Luckily, moving your servers to the cloud gives administrators access to organizations who will take over the monitoring of your servers for a (relatively) small monthly cost. You give these monitoring services access to your server, usually by giving them an account on the server or by installing a software “agent” on your servers, and they’ll happily take over all the mundane monitoring for you. NOTE Monitoring services are most common on the cloud, but they’re perfectly capable of monitoring on-premises servers as well. Companies that provide security monitoring services are one example of managed security service providers (MSSPs), a subset of managed service providers (MSPs). An MSP is an organization that provides some form of IT service for a fee. MSPs provide backup, 08-ch08.indd 405 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 406 infrastructure, and storage services. If you have a need for any type of IT service, there’s an MSP out there for you! An MSSP is nothing more than an MSP that concentrates on IT security, such as a monitoring service. Module 8-2: Virtualization Security This module covers the following CompTIA Security+ objective: • 2.2 Summarize virtualization and cloud computing concepts Virtualization dominates today’s computing world. If you’re accessing a Web app on the Internet, you are almost certainly accessing a virtual machine. If you use iCloud, Dropbox, or Google Drive, your files, photos, and songs are stored on virtual machines. Even within most LANs, the Windows and Linux servers are commonly virtualized. This module covers virtualization and the many security issues involved with virtualization. Security features span both virtualization and the cloud, as you’ll see (Figure 8-4). EXAM TIP The CompTIA Security+ exam might ask you to compare various virtualization and cloud services, noting the location of these services. Pay attention in this module and the next to the differences between on-premises vs. off-premises (also called hosted or cloud), primarily about who’s responsible for maintenance and service. (On-premises means you have to do the work; off-premises means you don’t. Hosted services have techs who don’t work directly for you; cloud abstracts the whole thing away and you just don’t worry about it.) You probably have an idea of what virtualization involves. You may have learned about only part of it, however, or perhaps you have been peripherally involved in setting up a virtual environment. Maybe you’ve put together a test lab on a single PC and run a few virtual machines on it, or perhaps you’ve designed and architected an entire virtualized environment for a large organization. In any case, you’ll need to be familiar with several important concepts for the exam, so we’re going to cover them here. These concepts include virtualization architecture, containers, virtualization risks, and virtualization for security. Figure 8-4 Cloud and virtualization are closely related They’re like peas and carrots. Virtualization The Cloud 08-ch08.indd 406 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-2: Virtualization Security 407 Virtualization Architecture In the basic sense, virtualization means to run an entire instance of an operating system on a host physical machine. The virtual machine (VM), or guest, exists as a file in an application. Applications known as hypervisors create and use these files to initiate a VM. When the VM is turned on, the hypervisor acts as a mediator between the host operating system and the guest operating system, providing access to both physical and logical resources. These resources could include sound cards, network connections, hard drives, USB drives, and any other peripherals that a physical machine could use. EXAM TIP Oddly, CompTIA dropped hypervisor from the Security+ objectives when going from SY0-501 to SY0-601. We assure you that any discussion of virtual machines in the real world includes hypervisors. Don’t be surprised to see the term in questions on your exam. As far as the virtual machine is concerned, it doesn’t “know” that it is not a physical machine; it functions as if it were a completely solid physical device. That means that it behaves as a physical device and can run applications, service user requests, make network connections, and so on. You can use VMs as file servers, user workstations, DNS servers, Web servers, and almost anything else that a physical machine can do. Unfortunately, this also means VMs have the same weaknesses as physical devices, and they must be secured and hardened against attack. You can run almost any operating system as a VM—Windows, Linux, UNIX, BSD, and (to a lesser extent) macOS. Even the Android operating systems used in mobile devices can be run as a VM. The host machine, on the other hand, can also run various operating systems, including Windows, Linux, or macOS. The real requirement is that a compatible application must create and run VMs on a particular host operating system. That brings us to the discussion of hypervisors. There are two types of hypervisors: Type 1 and Type 2 (Figure 8-5). A Type 1 hypervisor is a limited-function, stripped-down operating system in its own right. It runs the host machine and serves to provide the single functionality of managing the VMs installed on it. These types of hypervisors are usually called bare-metal (or sometimes native) hypervisors, because they provide a very limited functionality and only boot up the physical machine and handle resource access from the VMs. Several popular Type 1 hypervisors are available; some of them are even free to use. Microsoft has a Windows-based hypervisor (Hyper-V); the Linux community has a lot, such as Kernel-based Virtual Machine (KVM). Commercial hypervisors are also available, such as those developed by VMware. NOTE You’ll see Roman numerals used by some sources for the hypervisor types, so Type I and Type II. For the most part, Type 1 hypervisors are usually installed and then run in “headless” mode, meaning that they don’t require a user to sit down at a keyboard console or monitor. They are usually managed remotely through a Web browser on a workstation 08-ch08.indd 407 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 408 Virtual Machine Virtual Machine Virtual Machine Type 2 Hypervisor (e.g., VirtualBox) Figure 8-5 Virtual Machine Virtual Machine Virtual Machine Host OS (Windows, Linux) Type 1 Hypervisor (Hyper-V, ESX) Hardware Hardware Type 1 and Type 2 hypervisors after their network connectivity has been set up. Figure 8-6 shows an example of how VMware’s ESXi server, a popular bare-metal hypervisor, is accessed and managed remotely via a browser (Apple Safari, in this case). Rarely, an administrator might have to sit at a console at the host server to perform configuration tasks that can’t be done remotely. A Type 2 hypervisor is an application that runs on top of a host operating system. You may have used a hypervisor product such as VMware Workstation, Oracle VirtualBox, or Parallels for macOS. These are Type 2 hypervisors that can be used to create and manage Figure 8-6 08-ch08.indd 408 Accessing an ESXi server through the Safari Web browser 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-2: Virtualization Security 409 a limited number of virtual machines. Usually these types of hypervisors are used in small environments to create and test different aspects of virtualization. For larger production environments used in businesses, Type 1 hypervisors are normally used and are typically installed on very powerful, robust physical hardware. Figure 8-7 shows the user interface of VirtualBox, a popular free hypervisor application produced by Oracle. Virtual machines can also have unique network architectures. They can use multiple network configuration options, depending upon the type of host system they are installed on. You can configure a network connection that is directly connected to the outside network through the host machine’s network interface card, and the VM receives its IP addressing information from the outside network. This is called bridging. A VM could also receive its IP addressing information directly from the hypervisor installed on the host. In this regard, the hypervisor acts as a Dynamic Host Configuration Protocol (DHCP) server and provides private IP addressing (through network address translation, or NAT) to the virtual host—the VMs within the host machine. The host would then act as the default network gateway for any VMs installed on it. You can set up a virtualized network within the host so that only virtual hosts can communicate with it and each other. In other words, they can’t contact the outside world through the virtual network unless the host is configured to allow it. You can Figure 8-7 08-ch08.indd 409 VirtualBox Type 2 hypervisor 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 410 configure the network portion of the virtual environment in several different ways, based upon how you want VMs to communicate with the outside network, the host, and each other. Containers VMs are great. VMs enable you to use the wildly powerful hardware of modern computers to create full operating system environments that you enable or disable at will. The OSes run applications. They network. They are, for all intents and purposes, unique computing machines. A VM requires an operating system, a license for that OS, configuration, security, and so on. But what if your network needs are simpler? Containers offer a related experience to a VM, except that they include only the essentials of a network application—what you might think of as a server, plus programming that enables that application to run on any OS and network with other systems. Putting applications into containers—called application cells in some systems—enables software developers and distributors to spin up any number of copies of their functioning applications for testing purposes and more. When done right, containers enable application spin-up to happen almost instantly and make it much easier and simpler for network admins to manage servers. Docker provides the most common platform, or management system, for containers (Figure 8-8). NOTE Docker didn’t invent containers; they’ve been around for decades. Docker just packaged containers as a great way to manage application development and deployment in a clever and easy-to-use way. Figure 8-8 08-ch08.indd 410 Docker architecture 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-2: Virtualization Security 411 Virtualization Risks Of course, even beneficial technologies like virtualization have inherent risks. Virtualization is the solution to many problems, such as scalability, hardware production, and even security in some respects, but it also has risks. For example, with virtualization, single points of failure for host machines are risks, because if the host machine becomes unavailable, loses connectivity, or encounters a serious hardware error, all the virtual machines that reside on it are also lost. In addition, because multiple VMs may be running on a host, and some may have several services running on them, this adds to the attack surface of the host. All the services that the VMs run communicate with the outside world and the network, so they all represent different attack vectors as well. These represent a threat not only to each VM but also overall to the host. Yet another risk involves redundancy and availability. Although virtualization helps in ensuring redundancy and availability, failure on the part of administrators to take advantage of these features could result in the loss of critical data if a VM fails and it has not been backed up or otherwise preserved. Security could also be considered at risk with VMs because complacent administrators often mistakenly think that securing the host machine is enough, and sometimes they forget to secure the VMs as well. So don’t be surprised when you encounter a fairly secure host machine that has VMs running on it that have blank passwords or default security configurations. Remember that almost any risk that a physical machine can incur can also be incurred on a VM. You should take the same security measures on VMs that you take on a physical machine. VM Sprawl Once you have a hypervisor up and running, authorized users can easily whip up new VMs anytime they wish; that creates a problem called VM sprawl. VM sprawl is the outof-control creation of VMs outside your security control. Your marketing department spins up a new Web server for a job fair; the engineering department makes a VM to test some new software they’re thinking about buying; the IT department adds extra servers to run, as they say, stuff. VM sprawl is a huge problem without a simple answer other than good monitoring. Network administrators need to implement policies or practices for VM sprawl avoidance. Every hypervisor has authentication tools to limit who can make VMs. Use those tools. Make clear policies that prohibit users from building their own hypervisors or, even worse, buying their own cloud VMs! Other than that, your job is to maintain good inventory of all existing VMs and to perform ongoing monitoring to look for new VMs that shouldn’t be there. VM Escape VM escape takes place when a user inside a VM finds a way to break out (escape) the VM and somehow get into the underlying hypervisor/host operating system. Network security people need to know the problem and implement, as much as possible, VM escape protection. On the good side, VM escape exploits terrify the IT world and, once detected, are very quickly patched. On the downside, there is no anti-VM escape tool. Hopefully, you’ll have 08-ch08.indd 411 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 412 intrusion detection or intrusion prevention tools to mitigate the attack, like any other attack. As mentioned earlier, VMs need all the same security tools used on physical systems. Hardening Virtual Machines Locking down and securing virtual machines is not much different from doing the same to physical hosts. All the security considerations for physical hosts also apply to VMs. They require frequent patching and updating; they require locking down configuration settings; they need secure account settings; and when setting up users, you should follow the principle of least privilege. One nice thing about a VM is that once you have hardened the configuration as needed, you can always use it as a baseline and replicate it multiple times, so that each VM you create starts out with that hardened baseline and requires only recent patches or configuration changes. This makes it much easier to deploy VMs on a large-scale basis. VMs require network connectivity to ensure that patches get updated in a timely manner. You also need to make sure that you install anti-malware on the VMs, since, like all networked hosts, they are susceptible to malware from Web sites, malicious files, and so forth. They should all also have host-based firewalls or multipurpose packages that take care of firewall, anti-malware, and intrusion detection software. In addition to the normal things that you would do to secure physical hosts, VMs lend themselves to some other security measures. When not active, VMs are simply files located in storage, and as such they can be protected through permissions, encryption, and separation, the same as you would protect any other types of sensitive data files. They can also be copied and stored securely on secure media. Also like physical machines, VMs should be backed up periodically to ensure availability, as discussed next. Snapshots and Backups Like physical machines, virtual machines also need to be backed up from time to time. VMs have some advantages, however, in that they are native files located on a file system of some sort, so you can treat them like files for backup purposes. You could perform file backups to network-based or offline storage, and you could also encrypt these files when they’re backed up. You can also restore these files at will if a VM fails or becomes inaccessible. And you can use them to create additional duplicate VMs for redundancy purposes. You can also perform snapshots on VMs. A snapshot is a point-in-time backup of the current system state of the VM. This means the VM would back up and preserve any applications in use, user data, or other configuration details specific to that system’s state at that moment. You could take a snapshot of a VM before installing a new application or a critical patch, for example, and save the snapshot so that if the patch or software caused a functionality or security issue, the snapshot could be restored, enabling you to revert to the state the VM was in before the installation. You can use incremental sets of snapshots or combine them with traditional backup methods to maintain highly focused, comprehensive system state backups for availability. Using Virtualization for Security Virtual environments can provide stable, segregated environments in which to test applications, software, and even malicious code. Virtualization can also contribute to system 08-ch08.indd 412 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-2: Virtualization Security 413 and data availability by maintaining multiple redundant copies of identical virtual machines. In the next few sections, we’ll go into a bit more detail on how virtualization contributes to the overall security posture in the organization. Patch Compatibility You already know that you should test patches before applying them to production environments. This is because sometimes patches have unforeseen negative effects on production hosts, which can quickly take down critical operations. One thing that a virtual environment can give you is a complete test environment that mirrors the production environment. You can copy a physical machine and create an identically configured VM out of it. You can use this to your advantage by creating an almost exact replica of your physical environment in the virtual world, and test your patches, configuration changes, and updates in this test environment before you apply them to the physical machine. This helps avoid unintentional issues when you apply patches to production machines. It also provides you an opportunity to see where issues may exist and determine ways to correct them before the patch goes into production. Host Availability and Elasticity Virtual environments offer organizations real flexibility in the use of their infrastructure for both availability and elasticity. Virtualization supports availability in that you can almost instantly duplicate production hosts (whether physical or virtual) in a virtual environment, adding redundant capabilities for availability purposes or assets for use when existing hosts aren’t enough. You can copy physical machines and convert them to virtual machines and, because VMs are merely files, you can copy and reinstantiate them as new additional VMs (with a few basic configuration changes, of course). Virtualization provides elasticity, meaning you can expand, duplicate, reconfigure, repurpose, and reuse resources in the environment (in this case, virtual hosts) on the fly, as the need for them arises or shrinks. This provides an organization flexibility in its use of resources, saving physical machines and reallocating, activating, and deactivating hosts as needed in dynamic-use situations. Virtual machines can be provisioned, configured, and stored in advance for just such instances. Virtualization applies to networking components as well, enabling rapid scalability and adaptability of networks of VMs. Software-defined networking (SDN) enables centralization of portions of the routing and switching (such as creating and maintaining routing tables), which can then be rapidly pushed to routers and switches that only handle the packets and frames. Current SDN boxes employ security features that can rapidly respond automatically to attacks such as DDoS attacks. Security Control Testing Virtualization enables security professionals to test various security controls on virtual hosts, either before implementing them in production or as changes to the production environment occur. You can configure different controls to test effectiveness and functionality, to ensure that the appropriate control is implemented correctly for the environment. This can help confirm whether a new security patch will break an application; whether a configuration change is effective in reducing a vulnerability; whether a 08-ch08.indd 413 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 414 change to an operating system’s function or configuration breaks its security baseline; and whether a target host is configured as securely as you need it to be for vulnerability and penetration-testing purposes. Sandboxing Sandboxing provides an enclosed environment in which to run potentially dangerous applications, or even malware, to determine the effect they would have on the environment. Often, security professionals need to see the effects of an application or software on a host to determine how it interacts with the system and the network. This can help them identify potential issues with untrusted software, such as executables and scripts. Sandboxing allows you to test potentially harmful software in a controlled, isolated environment, without the possibility of affecting other hosts or allowing unwanted communication to the network. Virtualization provides sandboxing capabilities by giving you the option of running an isolated virtual host for that purpose. Module 8-3: Cloud Deployment This module covers the following CompTIA Security+ objectives: • 2.2 Summarize virtualization and cloud computing concepts • 2.4 Summarize authentication and authorization design concepts • 3.6 Given a scenario, apply cybersecurity solutions to the cloud It didn’t take very long after the introduction of virtualization for some clever people to realize something simple yet amazing. They could build a big server farm in a central location, fill it with servers, load a VM hypervisor on each of those servers, and add a (relatively) easy-to-use, Web-based interface so that thousands of paying customers could create and manage their own VMs. That’s the core of what cloud computing is all about. Cloud computing simply means to move computers, or at least some aspect of those local computers, to a location only identified with an IP address or a DNS name. Think of cloud computing just as you would any other service you pay for—such as water, electricity, cable, phone, Internet, and so on—except that now you’re paying for computing as a service. Those computing services run the full gamut, from processing power, storage, applications, and more. NOTE Cloud computing isn’t just for the public Internet. You’ll see private clouds as well later in this module. Cloud computing got its name from the many network architectural diagrams, such as the one shown in Figure 8-9, where the Internet is portrayed as a cartoonish cloud figure, meaning it’s abstracted from the rest of your network beyond your perimeter and Internet service delivery point. 08-ch08.indd 414 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 415 The Internet et WAN Connection Exterior Router Firewall Access Switch Company Servers Figure 8-9 The cloud Cloud computing offers many advantages, because it removes all the responsibility and overhead for maintaining data storage and processing in your computer, or even on your premises, and hands it over to a cloud service provider. A cloud service provider (CSP) essentially is a third party that owns a data center full of virtual servers, with multiple fast connections to the Internet. The CSP installs different types of operating systems and applications on its servers so that it can provide different services to customers via the Internet. Interestingly, with the shift of responsibility over mundane aspects of computing, like hardware maintenance, operating system updates, application patches, and updates from on-premises administrators to the CSP, the overall responsibility for authentication and authorization remains in the hands of local administrators. In a typical small office, for example, the local admin runs a Microsoft Active Directory domain and handles user accounts, groups, permissions, and so forth. Scaling up to a medium or larger organization, teams will handle the various aspects of Active Directory, but it’s essentially the same. Moving to the cloud with software as a service (SaaS) offerings such as Microsoft 365 just shifts the security structure from local Active Directory to Azure Active Directory. 08-ch08.indd 415 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 416 The local or enterprise administrators continue to handle user accounts, groups, permissions, and so forth, but they’re Azure Active Directory accounts, groups, etc. What the organization’s administrators gain by going to the cloud is that they don’t have to deal any more with maintenance and upgrades of hardware, operating systems, and applications. The CSP handles all that. Authentication and authorization remain the responsibility of the organization’s IT administrators. EXAM TIP Expect a question on the CompTIA Security+ exam that compares or contrasts cloud vs. on-premises requirements. In a nutshell, cloud deployments put fewer demands on local hardware, but higher demand on network bandwidth; security focuses on cloud solutions (see Module 8-4 for specifics). On-premises networks require more local hardware firepower and a lot more local expertise from techs and administrators. And the differences are about responsibility for security. As you’ll see in the next several sections of this module, cloud service providers can offer all types of services. Let’s look at cloud deployment models, cloud architecture models, and then wrap with “Cloud Growing Pains.” Let’s Talk Amazon Before we go any further, we have to take a moment to recognize the king of all cloud service providers: Amazon Web Services (Figure 8-10). Amazon certainly didn’t invent cloud computing, but Amazon was the first public CSP that made the idea of cloud computing popular and widespread. Using innovative ideas and deep economies of scale, AWS dominates the cloud and stands as the one of the largest public CSPs. All hail AWS! Over the years AWS has seen many superb competitors enter the cloud marketplace: Google Cloud, Microsoft Azure, and IBM Cloud, just to name a few. Although the organizations backing these competitors are also very large, Amazon was the first to market, Figure 8-10 AWS is the king of the cloud service providers I’m the King of the Cloud! Amazon Web Services 08-ch08.indd 416 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 417 and as the cloud leader AWS created many terms that are common lexicon for the cloud industry. The CompTIA Security+ exam leans heavily on some of these terms, so you need to know them. Let’s dive right in with regions, zones, compute, storage, and network. Regions AWS divides the globe into over 20 regions. By default, your location is based on your physical location, but you may add regions (for extra cost) when you need wider coverage. The following are a few sample AWS regions: • us-west-1 US West (Northern California) • us-west-2 US West (Oregon) • af-south-1 Africa (Cape Town) Zones AWS divides regions into multiple availability zones to provide even more geographic separation to get your application even closer to end users. Here are some examples of AWS zones, part of the us-west-1 region used in the United States: • us-west-2-lax-1a US West (Los Angeles) • us-west-2-lax-1b US West (Los Angeles) Amazon Product Categories When AWS first opened, it basically offered a single product: public-facing virtual machines that you could configure and run individually. You want two VMs? Great! Just spin up a second one! You want more? Go nuts! Over time, AWS has invented (or copied) so many more products beyond this single system that Amazon was compelled to invent an organization for these product categories, which initially consisted of three categories: Compute, Storage, and Network. As you can see in Figure 8-11, the categories have gotten a lot more granular since then. EXAM TIP AWS uses the terms Compute, Storage, and Network. Know them, as they are objectives on the CompTIA Security+ exam. Compute Products Any product that has to do with computation is a Compute product. AWS’s Amazon Elastic Compute Cloud (Amazon EC2) is the compute product you use to create VMs (AWS calls an individual VM an instance). Need to run containers on the cloud without spinning up your own instance? Then try Amazon Elastic Container Service (Amazon ECS). Storage Products AWS Compute products generally come with just enough storage to boot your OS and that’s about it. If you need more data storage, you’re going to want an AWS Storage product; the secret here is knowing what you need to store. Looking for general-purpose storage, the equivalent of adding an extra drive to the system? You want Amazon Simple Storage Service (Amazon S3). Want a cheap backup solution? 08-ch08.indd 417 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 418 Figure 8-11 AWS main product page (https://aws.amazon.com/products) Try AWS Backup. Got a huge FTP/SFTP/FTPS site and want to move it all to AWS? Then you need the AWS Transfer Family. Network Products If you can move individual systems up to the cloud, then why not move a network up there as well? Any AWS product that provides or supports networking on the cloud goes into the Network product line. If you have multiple instances on the cloud, why not tie them together with a virtual network? That’s Amazon Virtual Private Cloud (Amazon VPC). On AWS, never call your virtual network a virtual network—call it your VPC if you want other techs to understand you. Would you like your on-premises servers to talk easily to your VPC? Then grab AWS Transit Gateway. Get Used to AWS Terms! If you want to get into cloud security, if you want to pass the CompTIA Security+ exam, you need to get comfortable with these terms that AWS has introduced. The cloud industry may be over ten years old, but it continues to grow in terms of size and services. This is in no way a complete list of AWSisms, but this will get you started—and most importantly through the CompTIA Security+ exam. NOTE These terms are now standard across the cloud industry, but AWS invented them. 08-ch08.indd 418 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 419 Software as a Service Platform as a Service Infrastructure as a Service Figure 8-12 A notional cloud service architecture Cloud Deployment Models There’s not really a one-size-fits-all cloud deployment model—online services that people can rent or buy. The next few sections explore several types of cloud services offered by cloud service providers. Some of these services are simplistic, such as data storage, for example, but others are very complex and can supplement or even replace parts of enterprise-wide infrastructures. Many of these types of services are scalable, meaning that anyone from home users, to small businesses, to large corporations can make use of them. We’ll discuss these services from a business perspective, of course, but similar principles apply, whether a business is a small-office/home-office type of setup or a large corporate enterprise that spans several geographical locations. In Figure 8-12, you can see an example of how cloud services might be organized. Software as a Service With software as a service (SaaS), customers run software that’s stored in the cloud (almost always on a virtualized server) and used via a Web URL or, in some cases, a client program stored on a local system. SaaS is wildly popular today. Voice over IP (VoIP) services such as Skype and Google Voice provide voice/video communication. Cloud storage solutions such as Dropbox and Microsoft OneDrive provide terabytes of storage for files; by definition, that storage resides outside the physical network. Even traditional office applications are now available via SaaS. Microsoft offers Office as an SaaS solution via Microsoft Office 365 (Figure 8-13). 08-ch08.indd 419 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 420 Figure 8-13 We wrote this textbook entirely with Office 365 SaaS offers several advantages to businesses. First, software licensing costs less via the cloud. The software licensing may be subscription-based, so an organization may purchase licenses based upon numbers of users or concurrent connections. Second, an organization can avoid the legal ramifications of software piracy, since an application on the cloud can’t be easily copied and transferred from computer to computer or taken home by employees. In fact, the organization doesn’t have to store or manage any media at all, because the software is stored and used in the cloud, with the exception of occasional small components downloaded to a user’s workstation. Security as a service (SECaaS) is a subset of SaaS that focuses only on bundling security solutions. As you might imagine, the security solutions offered run the gamut of every security solution you would implement on premises, such as security assessments, vulnerability scanning, and so on. Infrastructure as a Service Infrastructure as a service (IaaS) goes beyond posting simple software applications in the cloud. IaaS provides entire machines, such as Windows or Linux hosts, for example, for remote connection and use. Of course, these aren’t physical machines; they are virtual machines hosted by a CSP’s infrastructure. Users simply connect to them via the Remote Desktop Protocol (RDP) or another secure remote connection protocol and use them as they would any other computer. Users can run applications installed on the virtual machine, create content, process data, and perform any other typical tasks they would perform on a physical machine. An example of IaaS is Amazon EC2; Figure 8-14 shows the EC2 interface for creating a new VM (AWS calls VMs instances). 08-ch08.indd 420 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 421 Figure 8-14 Interface for Amazon EC2 Usually, however, IaaS implementations provide servers rather than workstations; most businesses that leverage an IaaS provider do so for server VMs. The advantage of having virtual servers through an IaaS provider is that the business doesn’t have to provision, manage, or maintain huge server farms or data centers—all that’s done for them by the provider. The provider handles patches, updates, configuration, and so on. Additionally, licensing for servers provided through an IaaS contract is usually far more streamlined, and cheaper. Platform as a Service Platform as a service (PaaS) offers a business a computing platform—such as a Web application server or database server, for example—that it can use to provide services both internally and to customers on the Internet. Many online storefronts use this model to conduct business, rather than hosting on their own premises the physical servers, Web sites, databases, and applications. Again, the advantages of using this type of service are cost savings, no requirement to build and maintain the infrastructure on site, and the guarantee of around-the-clock availability—plus, the PaaS provider takes care of the patching and configuration work. Anything as a Service The big three—SaaS, IaaS, and PaaS—get a lot of attention, but today anyone can develop virtually (pardon the pun) any type of resource, software, or application that anyone might need. With anything as a service (XaaS) your choices are vast. 08-ch08.indd 421 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 422 Monitoring as a Service (MaaS), for example, provides continuous tracking of the health of online services used by an organization, such as systems, instances, networks, and applications. Like with other cloud services, this XaaS variety puts the maintenance and security into the hands of the CSP, relieving on-premises administrators from those responsibilities. Another interesting XaaS is desktop as a service (DaaS), which provides users with their own virtual desktops. Their actual physical machines don’t really matter: they can be full desktops, thin clients, tablets, or smartphones. No matter where users are located or what they have at hand, they have instant access to their desktop. EXAM TIP You’ll recall thin clients from your CompTIA A+ studies, essentially a keyboard, mouse, and monitor that access an operating system, applications, and data remotely. Expect a question on the CompTIA Security+ exam that explores thin clients as direct components of cloud computing. DaaS competes directly with more traditional Citrix-developed virtual desktop infrastructure (VDI), where an enterprise sets up a central server to provide desktop interfaces for users. Just like with other virtualization and cloud-based services, DaaS takes the managing of hardware and software out of the hands of local IT staff, freeing them up for other tasks. NOTE The CompTIA Security+ acronym list includes Virtual Desktop Environment (VDE), but that’s not all that common a usage. VDE usually stands for Virtual Distributed Ethernet, a networking virtualization technology used in Linux. Neither use of VDE is synonymous with VDI. Cloud Architecture Models Although we stated that cloud environments are operated primarily by large companies with huge data centers, this isn’t always the case. In fact, an increasing number of clouds are popping up that follow a few different architecture models. These include private clouds, public clouds, and a few other models we’ll briefly go over. Any of these various cloud architectures may be used, depending on the organization’s specific needs and its reliance on third-party providers or its requirements to keep computing resources in house. Private Cloud In a private cloud, as you might expect, one party uses the cloud environment—the infrastructure, network devices, connections, and servers. A private cloud doesn’t necessarily mean that the infrastructure also resides physically within the business’s own data center on its physical premises. It could certainly be that way (military organizations and very large corporations often host their own private cloud, for example), but a private cloud can also be hosted by a third-party provider as a contracted service. Regardless of where the environment is hosted, a private cloud is for the use of the business that’s paying for it—it’s not for public or shared use. It can still host the same types of services described earlier. 08-ch08.indd 422 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 423 A private cloud may cost the organization a bit more if it’s hosted within a data center it owns and operates, but this cost is usually absorbed by the cost of operating the data center itself. An organization can save a bit of money if a third-party provider operates the data center for the organization, however. Another advantage of a private cloud, other than exclusive use, is that the organization may be able to exert more control over data security and availability levels. NOTE One of the challenges to private clouds is the connection between a private cloud service provider and on-premises systems. Companies like AWS provide an interface called a transit gateway that gives any system a simple way to connect to your cloud. In most cases the connection is via a VPN. Public Cloud A public cloud is usually operated by a third-party provider that sells or rents “pieces” of the cloud to different entities, such as small businesses or large corporations, to use as they need. These services and the “size” of the piece of cloud an organization gets may be scalable, based on the customer’s needs. Customers usually don’t get direct connections to the provider, as they might in a private cloud model; the connections are typically made over the customers’ existing Internet connections. Several business models are used for these types of clouds, including subscription models, pay-per-use, and so on. Unlike a private cloud, the security and availability levels are pretty much standardized by the provider and offered as part of the contract; organizations purchasing those services may not have any control over those terms. Examples of public cloud service providers include offerings from Amazon Web Services (AWS), Google Cloud Storage, and the Microsoft Cloud. Community Cloud A community cloud is made up of infrastructures from several different entities, which may be CSPs, business partners, and so on. In this structure, common services are offered to all participants in the community cloud, to one degree or another. An example of a community cloud is one that is shared among universities or educational institutions. Each institution provides a piece of infrastructure, and the cloud may include third-party providers as well, to form a cloud shared by all. Hybrid Cloud A hybrid cloud is any combination of the cloud models described previously. You could have public/private hybrids, private/community hybrids, and so on. A hybrid might be used because all parties need common cloud services (common application or Web platforms, for instance, on linked or connected Web sites), while maintaining their own private or community clouds for other purposes. Hybrid clouds could be constructed in many different ways, using third-party providers, private or shared data centers, and so on, as well as different types of connections (direct, Internet-only, and so on). Figure 8-15 sums up the relationships between the different cloud types. 08-ch08.indd 423 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 424 Community Cloud Hybrid Cloud Public Cloud Community Cloud Internal/On-Premises Private Cloud Figure 8-15 Private Cloud Hosted by Third Party The relationships between the different cloud types EXAM TIP Over time, an organization can find itself in a situation where it’s using services from multiple providers—IaaS here, PaaS there, XaaS everywhere. This self-evolving mess only gets more complicated with hybrid clouds that include third-party access to their services (or vice versa). Services integration is a type of propriety solution offered by companies to streamline, organize, and simplify (as much as possible) a wide-ranging array of services into a single source. There’s no set definition for services integration. Solutions are customized to fit an organization’s specific components and vendor solutions. You might find the term service integration and management (SIAM) used instead of services integration as well. Cloud Growing Pains The explosive growth in cloud computing has led to some issues where a one-size-fits-all solution doesn’t work efficiently for an organization, specifically in terms of latency and scalability. Several solutions fine-tune cloud-based networks to address these issues. 08-ch08.indd 424 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-3: Cloud Deployment 425 Latency A standard cloud computing system moves the processing of data from the local network to the cloud servers. That simplifies the needs of the local network and optimizes the processing—that’s the ideal. The downside of cloud-based processing is that it induces latency. Data has to flow to the cloud, get processed, and then get pushed back to devices. A lot of devices and systems handle this latency without problems. But an increasing number of smart devices—phones, tablets, Internet of Things (IoT) devices, surveillance systems, and so forth—need low-latency processing of immediate data. Two related options—fog computing and edge computing—address the latency issue. In essence, the buzz-sounding solutions of fog computing and edge computing push some of the processing in a cloud network back to the local network. Fog computing devices do a lot of local processing before syncing to the cloud so that, for example, you know quickly when someone’s ringing your smart doorbell. Edge computing adds local processing and data storage, sometimes with dedicated processing stations. If this sounds familiar, it’s because that’s the way networks worked before the cloud phenomenon! It’s as if providers pushed everyone to cloud solutions and then had to dial it back to address latency issues, and they could use cool new marketing terms. Scalability Scalability in cloud networks means giving organizations flexibility to grow on demand. Two options help address this issue efficiently, microservices and serverless architecture. Microservices/API More sophisticated Web applications are complex beasts, requiring teams of programmers and potentially services all working together to make these applications do what they do. To that end, there’s motivation to split up and delegate the work needed to make a Web app work. That’s where microservices and APIs come into play. Consider a typical Web app that includes merchant functions for purchases and inventory and a user logon function for special pages. Instead of making the Web app monolithic (one big pile o’ code), we can separate the application into free-standing microservices—programming sections—that support the application as a whole. One microservice might handle user logins, another the inventory database, and so forth. These microservices might be written in-house, provided by third parties, or even treated like an XaaS. Complementing microservices are application programming interfaces (APIs), the interfaces that enable different programs or different parts of a program to access another’s code. APIs aren’t new, but in this context APIs mean the interfaces that different parties use to access Web applications. Employing microservices (and APIs to make connections) means developers can focus on the parts of an application under demand, rather than try to make everything scale up. If the database is getting slammed and needs updating, the programmers can focus on the microservices that address the database needs and not have to worry about the unaffected parts. This increases scalability efficiently. Serverless Architecture Classically in the cloud there is some amount of work placed on administrators to set up servers. In a typical cloud service—let’s consider IaaS for this 08-ch08.indd 425 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 426 example—the cloud service requires you to configure a server and then use that server as, well, a server. Even with PaaS, you still need to configure a server and make sure it’s running whatever essential service. In a serverless architecture, the CSP offers services directly to end users. This usually manifests as functions or software downloaded as needed for provider services such as storage or messaging. Serverless solutions such as AWS Lambda merely require your endpoints to “point” toward a domain name for those services. NOTE Serverless architecture isn’t truly serverless. It’s just that you aren’t required to set up a server. Your CSP provides services directly to your endpoints. Module 8-4: Securing the Cloud This module covers the following CompTIA Security+ objectives: • 1.2 Given a scenario, analyze potential indicators to determine the type of attack • 1.6 Explain the security concerns associated with various types of vulnerabilities • 2.2 Summarize virtualization and cloud computing concepts • 3.6 Given a scenario, apply cybersecurity solutions to the cloud Replacing on-premises networks with cloud-based networks presents a security challenge. In the first place, many vulnerabilities and attacks don’t really change very much between cloud and on-premises. On the other hand, cloud infrastructures bring up a number of interesting security controls and capabilities that work differently than onpremises. Let’s look at some of these. EXAM TIP Look for questions on the CompTIA Security+ exam that compare cloud-based vs. on-premises attacks and cloud-based vs. on-premises vulnerabilities. The physical component of on-premises vulnerabilities and attacks doesn’t apply to cloud-based vulnerabilities and attacks. All of the network-specific vulnerabilities and attacks to exploit those vulnerabilities apply to cloud-based and on-premises networks. Cloud Security Controls Cloud security controls address the unique features of cloud computing to mitigate several security issues. This section first explores zones as a cloud security control and various security controls for storage, network, and compute cloud services. We’ll finish with a nod to SDN/SDV and cloud native controls. Zones Zones are the bread and butter of AWS cloud security controls. Zones usually come in pairs. Zones are real-time copies of each other, providing extremely high availability across 08-ch08.indd 426 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-4: Securing the Cloud 427 zones as well as making integration and auditing easier. There’s not much to add here from a security standpoint. NOTE Other cloud service providers use the concept of zones. Microsoft Azure has regions that subdivide into zones, for example. Regardless of the specific label used by CSPs, the idea is to provide high availability so customer downtime or lag is reduced to as near zero as possible. Storage Nothing does mass storage like the cloud! From databases accessed millions of times per second to long-term archival materials, cloud storage is wonderfully convenient. For example, simply placing mass storage on the cloud instantly takes care of mundane items such as backup because all of your data is stored in zones, providing automatic replication and high availability. Cloud storage services require permissions just like any resource. File servers need permissions. Mail servers need permissions. You get the idea. Cloud service providers—let’s just say AWS, as Amazon invented this term—call their permissions resource policies. A policy is an object in AWS that defines the permissions to an identity or resource. AWS defines two types of resource policies: identity-based policies and resource-based policies. Identity-based policies are assigned to users, groups, or roles. Resource-based policies are attached to a resource. Given the fact that the cloud is always a remote connection, encryption is essential. Encryption is generally an easy thing to implement given that everything we might ever want to do application-wise has a secure protocol. The challenge with encryption in cloud solutions isn’t the actual encryption per se; it’s the storage and administration of all the passwords, keys, certificates, RSA tokens, and other secret stuff needed to keep all these encryptions working. A secrets management solution takes all those secrets away from the apps that traditionally store them and locks them away in a separate database, giving administrators a one-stop-shop location to manage the secrets without affecting the application that needs them. Network Many small cloud customers tend to build a single-server system on the cloud, accessing the system as needed to keep it running properly. As customer needs increase, it’s very common to create multiple systems and connect them into virtual networks, all residing on the cloud. The most important concept about virtual networks is that they work exactly like an on-premises network. IP assignment (static or DHCP), DNS, subnetting, firewalls, and similar issues all apply to a virtual network—it’s simply a matter of figuring out how your CSP offers the tools necessary to make these configurations. AWS calls a virtual network a virtual private cloud (VPC). But what happens if you want public-facing servers on your AWS cloud? No problem. Just make separate subnets and make one of those subnets public! That’s right, with AWS you make a virtual private cloud and then make part (or all) of the VPC public. 08-ch08.indd 427 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 428 EXAM TIP Expect a question on the CompTIA Security+ exam that asks you to compare options or solutions for public and private subnets. The actual steps of segmentation of a network vary among CSPs, but the process is similar. First, define network IDs. Second, connect separate network IDs using virtual routers, adding firewalls as needed. API Inspection and Integration Odds are good that if your organization were to develop a Web application, that application would use some form of API to connect to other applications. APIs do so much of the heavy lifting today interconnecting applications. These other applications might be as simple as tools to share some database information; or they may connect two apps to enable single sign-on. If you’re going to use an API with a Web application, consider two items. First, how does the application perform API integration? In other words, how does the application connect to another application’s API (or vice versa)? Second, how does the application perform API inspection to ensure that only the correct data moves between the apps? A cloud app provider creates one or more APIs to enable access to its products. Various cloud security providers such as Microsoft Cloud App Security work with that cloud app provider to optimize interaction with the APIs, which includes API inspection for account information, audit trails, app permissions, and so on. Ensuring secure access between APIs enables functional use of Web applications. Firewalls in the Cloud Cloud networks need all the same protections from external attackers that any on-premises network needs. Where an on-premises firewall protects physical networks, cloud firewalls protect cloud networks. EXAM TIP With AWS cloud networks you can create (up to five) security groups with each VPC that act as a virtual firewall for the instance. They control inbound and outbound traffic and can each have different rules for handling traffic. There are several firewall considerations in a cloud environment. First, what does your cloud network need for segmentation? For small operations, a Web application firewall in front of a single instance may be all you need (Figure 8-16). Maybe in a larger situation you would place an edge firewall in front of multiple servers. Larger still and you might need multiple next-generation firewalls (NGFWs) segmenting many subnets at multiple Open Systems Interconnection (OSI) layers. Cloud service providers can offer firewalling at one or more OSI layers, depending on the needs of the organization. They can make Layer 3 firewalls available for specific purposes, for example, and Layer 4 for others, plus NGFW solutions for overall security. A key factor for an organization needing firewalling isn’t capability, per se, but cost. A CSP may offer many types of firewalls, but not for free! CSPs use a metered pricing system, charging by the gigabits/month. These prices are usually inexpensive relative to the overall cost of your cloud . . . until they are not. An aggressive DDoS attack, for 08-ch08.indd 428 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-4: Securing the Cloud 429 Figure 8-16 Traditional firewall configuration in AWS example, can increase your monthly firewall as a service (FWaaS) costs by a factor of tens of thousands. NOTE All cloud service providers offer some form of “How much am I spending and why” reporting/alarms. Take advantage to avoid costly surprises! Compute Securing compute components means focusing on immediate, active processing. That means securing VPC endpoints, dynamic resource allocation, software-defined visibility, instance awareness, and container security (plus security groups, discussed previously). VPC Endpoint When CSPs offer XaaS, you need some method to enable your cloud to connect to these services. In the AWS world, your VPC needs a connection to that service. Instead of wasting potentially valuable IP addresses, virtual routers, and such, AWS creates a private IP address to the service you choose—called a virtual private cloud (VPC) endpoint—and your VPC just… connects to it. Dynamic Resource Allocation It’s not hard for a CSP to adjust resources allocated to a customer based on need. Some examples of resources are CPU and memory bandwidth, storage capacity and speed, network connection, and number of instances of the server (there are many more). The challenge is how to do this dynamically, to adjust the resource allocation to the customer so that the utilization is as close to 100 percent as possible. 08-ch08.indd 429 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 430 Dynamic resource allocation is agreed upon between the CSP and the client as part of their mutual service-level agreement (SLA). How this SLA manifests varies greatly. In most cases, even the SLA is automatically adjusted by a client clicking some button that changes the agreement. If you agree to allow your CSP to add more instances, for example, then you’ll pay for those instances when they are brought online. NOTE Dynamic resource allocation is a wonderful feature of the cloud— just keep an eye on your bill! Instance Awareness It’s very common for an organization to run many instances of cloud services. For example, an organization might be running hundreds of instances of Google Drive—corporate instances that are shared by users; individual instances for personal use; and instances shared by groups within the organization. Firewalls, NGFWs, SDV—these tools do not have a method to differentiate between instances, i.e., they don’t have instance awareness. Sure, they can turn off access to Google Drive, but if only one instance is being naughty, then we need other solutions that can locate the naughty instances causing problems and shut them down without killing everything. NOTE Netskope (https://netskope.com)—and other companies—offers solution for protection and prevention among cloud instances that lack instance awareness. Container Security Containers are the way to go in the world of application development due to their convenience, tiny footprint, and ease of use, but they come with their own security issues. The best way to consider those issues is to think of any container as three distinct components. First is the underlying operating system, second is the container software, and last is the application running inside the container. The underlying OS isn’t anything special in terms of security requirements other than your awareness that the usual security applied to a host might affect the container itself. Never patch an OS without first investigating anything that might affect the security of the container software. Also monitor file permissions and user accounts that might provide unauthorized access to the container software. Container applications like Docker and Kubernetes have their own access control lists (ACLs) to the application as well as the images they store. Careful auditing and monitoring are required, especially in environments where many hands are working on the same product. Take advantage of the container application’s role-based controls as well as segmentation of the application into separate images as needed. Also make sure any container software updates do not affect your images. Last, consider the security of your images. It’s common to use signed images to verify image integrity. Never add third-party files to your image without careful inspection. 08-ch08.indd 430 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Module 8-4: Securing the Cloud 431 Software-Defined Visibility Monitoring a complex network can easily become messy. IDS/IPS, firewalls, and SIEM setups aren’t nearly as static in a cloud as they are in a classic on-premises network. In particular, software-defined networking (SDN) setups make it challenging to monitor cloud networks using classical tools. Enter software-defined visibility (SDV). By applying software (called APIs in this area) to every (or at least most) devices on the network—including end nodes—any part of the network is now visible to your defensive tools. Any device can detect and respond to an attack. SDV all but removes potential blind spots on your network. Most SDV solutions are proprietary and only seen on larger, more secure networks. Cloud Native Controls vs. Third-Party Solutions AWS provides a huge number of amazing controls built into the AWS space. These hundreds of controls, created by and offered by AWS, are known collectively as native controls (Figure 8-17). AWS, like all other CSPs, however, gives third parties access to AWS VPCs via APIs. This has created an entire industry of third parties that provide solutions for thousands of niche situations. Figure 8-17 08-ch08.indd 431 AWS native controls 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 432 Unique Cloud Security Solutions The cloud introduced not only a whole new class of security controls but many security solutions as well. Let’s look at three here: • CASB • SWG • Application security Cloud Access Security Broker Cloud access security broker (CASB) refers to a service that manifests as a layer of software between a cloud application and an enterprise or organization, designed to provide security. Most commonly, the major cloud organizations—like Google, Amazon, Microsoft, and so on—have invested heavily in automated controls implemented through APIs. You can rely on these companies for proper security. A proxy-based CASB, in contrast, relies on a third party’s software in between the cloud service provider and an organization or enterprise that uses those services. Proxy-based services inject more security problems rather than reduce security risks. The proxy-based services seem to have briefly appeared but flamed out. If you get asked about CASBs on the exam, focus on the API-based models. Next-Generation Secure Web Gateway As quickly as cloud-based applications develop new solutions to address previously unconsidered vulnerabilities, new issues come into focus, requiring yet another class of security solutions. Arguably the newest solution is the next-generation secure web gateway (SWG). An SWG stands between a Web application and all of the services that Web application uses. Application Security Chapter 11 covers a lot about secure Web development, but the term application security is so cloud-centric that it warrants a mention here. Cloud applications need a lot of security in development and during runtime. Tools that provide that form of security are under the umbrella of application security. Questions 1. What’s the minimum number of computers needed for a DDoS attack? A. 1 B. 2 C. 10 D. 1000 08-ch08.indd 432 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Questions 433 2. What is a company that provides security monitoring for a fee called? A. IaaS B. MSP C. MttF D. Security broker 3. Virtual machines must have a __________ in which to run. A. bare metal B. container C. database D. hypervisor 4. Docker is a popular management system for what sort of product? A. Containers B. Security C. Shoes D. VMs 5. The accounting department built their own hypervisor and added four virtual machines without letting anyone know. This is an example of what virtualization issue? A. Hypervisor B. Unauthorized zone C. VM escape D. VM sprawl 6. John’s cloud service provider enables him to set up virtual machines. He can add any operating system he wants. This is an example of which type of service? A. IaaS B. PaaS C. SaaS D. XaaS 7. Total Seminars deploys both a public cloud and a private cloud. What kind of cloud solution do they have? A. Community cloud B. Hybrid cloud C. Private cloud D. Trusted cloud 08-ch08.indd 433 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 8 Chapter 8: Securing Public Servers 434 8. AWS divides the world into more than 20 __________. A. cubits B. regions C. sectors D. zones 9. A(n) __________ solution takes secrets away from apps that traditionally store them and locks them away in a separate database. A. BitLocker B. Internet key exchange C. password vault D. secrets management 10. Bill’s company provides every employee with personalized storage space. His cloud service provider gives him a tool called __________ that enables him to shut down any individual instance if there’s a problem. A. instance awareness B. NGFW C. SWG D. VPC endpoint Answers 1. B. A distributed denial-of-service attack needs two or more computers to carry out its attack. 2. B. A managed service provider provides security monitoring for a fee. 3. D. VMs rely on a hypervisor to run. 4. A. Docker is a popular management system for containers. 5. D. Unauthorized creation of VMs in an organization is an example of VM sprawl. 6. A. An infrastructure as a service enables deployment of full systems running a variety of operating systems. 7. B. A hybrid cloud combines different types of cloud solutions. 8. B. Amazon Web Services divides the world into 20+ regions to enhance efficiency. 9. D. A secrets management solution takes secrets away from apps that traditionally store them. 10. A. Instance awareness tools enable quick and effective control over instances. 08-ch08.indd 434 25/03/21 2:17 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 CHAPTER Securing Dedicated Systems 9 Hey, Scott! Let’s combine embedded, specialized, and mobile systems into the same chapter! What could go wrong? —Mike Meyers What makes embedded systems, specialized systems, and mobile systems sufficiently similar to cover them in a single chapter? That’s a valid question, considering they run on a wide array of operating systems—from Windows, Linux, and macOS to Android, iOS, and customized single-platform OSes—and have a variety of uses, including singlepurpose devices (e.g., an Internet-connected refrigerator), specific-purpose devices (e.g., a home automation hub), and multipurpose devices (e.g., a smartphone or tablet). So what’s the connection? Every one of these devices, which we dub dedicated systems, comes from the factory as complete and unchangeable computing hardware. When you buy a fitness watch, for example, you buy a sophisticated computing device, but one that you can’t upgrade or change. When you buy a new Apple iPad with 64 GB of storage, 64 GB of storage is all you’ll ever get with that machine. The CPU will never change. The RAM will never change. EXAM TIP Dedicated systems is a term we coined and not one you’ll see on the CompTIA Security+ exam. That unchanging hardware coupled with changeable firmware or software presents unique challenges in security. These devices are part of your network, interconnected with general-purpose computing devices (like a Windows PC or a Linux server), and absolutely must be part of your overall security posture. Not securing them puts everything else in your system at risk. 435 09-ch09.indd 435 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 436 This chapter explores securing dedicated systems in four modules: • • • • Embedded, Specialized, and Mobile Systems Connecting to Dedicated Systems Security Constraints for Dedicated Systems Implementing Secure Mobile Solutions Module 9-1: Embedded, Specialized, and Mobile Systems This module covers the following CompTIA Security+ objectives: • 2.6 Explain the security implications of embedded and specialized systems • 3.5 Given a scenario, implement secure mobile solutions Embedded, specialized, and mobile systems power a huge portion of modern computing tasks, and they come in a variety seemingly as diverse as the fish in the sea. This section touches on the dedicated systems you’ll encounter on the CompTIA Security+ exam: • • • • • Embedded systems SCADA/ICS Internet of Things Specialized systems Mobile systems Embedded Systems The definition of embedded system is a moving target depending on the author. For some in the IT industry, the term “embedded system” refers to any computing component packaged as a discrete part of a larger package. A network interface chip soldered onto a motherboard, for example, could be considered an embedded system. It’s a processor. It has discrete functions that enable the larger system to accomplish things. This broad definition encompasses thousands of other examples, such as a point-of-sale system at a supermarket checkout, which handles local tasks (taking credit card information) but depends on a larger system (the store’s network infrastructure) to complete transactions. As these examples suggest, such a broad definition of embedded system is too unwieldy to be practical. CompTIA uses the term embedded system more narrowly to describe discrete hardware components that make up portions of systems. Specifically, the 601 objectives describe embedded systems as those running a Raspberry Pi, a field-programmable gate array processor, or an Arduino. Let’s look at all three examples. 09-ch09.indd 436 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 437 Figure 9-1 Raspberry Pi SoC (Image: Future Publishing / Contributor, Getty Images) Raspberry Pi The Raspberry Pi powers an array of embedded devices and systems, most notably the DNS Pi-hole and custom industrial control solutions. The Raspberry Pi exemplifies the system on chip (SoC) design concept, where all the processing components reside on a single circuit board—that includes CPU, RAM, system BIOS, Ethernet networking, and Wi-Fi networking; plus connectivity points for peripherals such as a keyboard, mouse, and monitor. Figure 9-1 shows a Raspberry Pi 3b. NOTE A DNS Pi-hole uses a Raspberry Pi at the outer edge of a network, with the DNS server running special software to block any extra links on Web sites that display ads. Implementing a Pi-hole will transform your computing experience without sacrificing network performance. Goodbye, ads! Check out the Dave Rush Pi features on the TotalSeminarsChannel channel on YouTube for the scoop. The Raspberry Pi models can run various Linux distros, including Ubuntu, Kali Linux, and the dedicated Raspberry OS. As such, you can use a Pi as a standalone multipurpose 09-ch09.indd 437 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 438 computer that replaces a Windows or macOS desktop (and apply all the standard security measures for desktop systems). But the Pi’s small size and very small price have made it a favorite component in embedded systems, from manufacturing to industrial sensor controls. Zaro’s Family Bakery in New York City, for example, employs a Pi along with wireless sensors to monitor temperatures in the bakery’s freezers. This frees employees from physically checking temps and thus adds efficiency to their operations. From a security standpoint, Raspberry Pi systems act, smell, and taste like a typical desktop system, just writ small. The typical Pi can plug into standard peripherals— keyboard, mouse, monitor—and connect to wired and wireless networks. The Linux operating systems that run Pis require the same security considerations of desktop Linux computers, with secure passwords, accounts, and so on. Physical access to a Pi presents the same danger as physical access to a PC or Mac. Field-Programmable Gate Array Embedded systems that require flexibility in processing capabilities use field-programmable gate array (FPGA) computers that, as the name suggests, you can reprogram to optimize for various tasks. An FPGA does not have a fixed CPU, like the Raspberry Pi, but rather has integrated circuits (ICs) that developers can redefine as needed. You’ll see FPGAs used in vehicular systems, such as airplanes and automobiles, where switching hardware to make changes would be prohibitively expensive. Reprogramming the hardware for updates or corrections makes more sense. Embedded systems running on an FPGA tend to run a real-time operating system (RTOS), such as Windows Embedded Compact (Figure 9-2). An RTOS is designed to respond in real time to inputs. An RTOS is critical for anti-lock brakes, safety stops, and so forth. Figure 9-2 Windows Embedded Compact 09-ch09.indd 438 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 439 Figure 9-3 Arduino board with breadboard From a security standpoint, keeping the firmware up to date to work through bugs helps. Plus, limiting physical access to control ports or connections minimizes the potential for an attacker to damage your systems. Arduino Circuit boards and microcontrollers made by the Arduino company enable embedded systems used in motion detection, robotics, thermostats, drones, diagnostic systems, and more. Arduino products are open source and programmable using the programming languages C and C++. Open source combined with low cost, approachable programming and many connection options have made the Arduino boards the go-to devices at both the professional and enthusiast level for embedded devices. Figure 9-3 shows a typical Arduino system with an attached breadboard (for extending the capabilities of the board, in this case, for music). You might think that “open source” and “approachable” would make embedded systems with Arduino at the heart susceptible to hacking, but it’s usually the other way around. A lot of people use Arduino systems to power their hacking of other systems! Arduino systems have security concerns. Physical access, like with FPGA systems, presents a clear danger. The limited memory on Arduino-based systems leaves them vulnerable to buffer overflow and heap attacks. The systems often connect automatically to the nearest access point when the default connection fails, again providing an opportunity for mischief. As with all computing systems, assume Arduinos need careful thought and preparation for security. SCADA/ICS Supervisory control and data acquisition (SCADA) systems are used in industrial applications, such as energy utilities (electric plants, nuclear power plants), production facilities (for logistics and control of manufacturing systems, for example), sewage treatment centers, and other specialized applications. Heating, ventilation, and air conditioning 09-ch09.indd 439 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 440 (HVAC) controls also fall into this category and are often automated and connected to the Internet or other networks to monitor and control environmental elements such as temperature and humidity in a facility. You’ll often hear the term industrial control system (ICS) associated with SCADA. SCADA systems are more and more often being connected to the Internet, and often in an unprotected state. They run TCP/IP protocols and use embedded versions of some of the popular consumer operating systems, such as Windows or Linux. This makes SCADA systems prime targets for hackers, who attack them to damage critical infrastructure, launch denial-of-service (DoS) attacks, and generally create mischief and outright harm. Since SCADA systems often connect to very critical systems, it’s not too hard to imagine a hacker attacking and gaining control of these systems and seriously affecting power, water, and other utilities and services on a massive scale. There have even been reported instances of hackers compromising SCADA systems and launching attacks on an organization’s traditional internal network infrastructure through them. One such attack allegedly carried out by the United States and Israel—the Stuxnet worm attack, code-named “Olympic Games”—blasted through Iranian industrial processes for refining nuclear material. No one on any side will confirm anything—hello international espionage and sabotage—but the attack destroyed upwards of 1000 nuclear centrifuges, putting a serious dent in Iran’s nuclear enrichment capabilities. Methods of mitigating these types of attacks include the traditional ones, such as encryption, authentication, and patch management. In the case of many of these systems, infrastructure controls, such as intrusion detection systems (IDSs) and firewall devices, should also be implemented. One other method that should be examined is the complete separation of these networks and their devices from public networks, such as the Internet, a form of air gap. (See Chapter 10 for the scoop on air gaps.) Internet of Things The term Internet of Things (IoT) describes the many computing devices (other than PCs, routers, and servers) that connect through the Internet, which is about as broad a definition as it gets. IoT often refers to smaller helper devices, such as lightbulbs you can turn on or off remotely, but it also applies to heating and cooling systems (facility automation tools), smart devices like a refrigerator that can tell you how much milk is left, diapers that inform you when junior needs a change, and so on. You’ll find a lot of devices marketed as part of the Internet of Things, such as wearables like the Fitbit fitness watch (Figure 9-4). Wearables have sensors for things like heart rate and number of steps taken; better ones have location tracking systems. The highest-end wearable devices, like the Apple iWatch, function as an alternative or extension of a smartphone, enabling text messaging, music, and more, all connected through the Internet via the cellular networks. Some devices that might seem an odd fit fall into the IoT category, such as multifunction devices (MFDs) that combine printers, scanners, and copiers into one machine and then add Internet capabilities. You can print to MFDs from a variety of devices, including smartphones like the Apple iPhone via AirPrint, plus scan and send PDF files directly to Internet or e-mail destinations. 09-ch09.indd 440 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 441 Figure 9-4 Fitbit IoT watch (Image: Smith Collection/Gado / Contributor, Getty Images) EXAM TIP The CompTIA Security+ 601 exam objectives refer to multifunction devices as multifunction printers (MFPs), so be prepared for either term on the exam. IoT device manufacturers use a wide variety of different operating systems for their devices. The big players have their own operating systems, such as Android Things (Google), Windows IoT (Microsoft), and Amazon FreeRTOS (Amazon). Plus there are at least a dozen open-source operating systems, many based on a Linux core, such as Snappy (Ubuntu), or on the C programming language, such as TinyOS. As you might imagine, with such incredible diversity of hardware and operating systems, combined with the dizzyingly efficient wireless networking capabilities, IoT security is a nightmare. Additionally, what IoT devices have in common from a security standpoint are weak default settings. Most manufacturers of IoT devices in the consumer sphere, for example, err on the side of ease of use for the consumer rather than rigorous security for the power user or IT security specialist. Fine-tuning options such as connectivity and notification settings can go a long way toward adding worthwhile security to IoT devices. Specialized Systems Both CompTIA and many writers throw up their hands at the rest of the dedicated systems, calling them simply specialized systems. A specialized system offers all the hallmarks of other dedicated systems, such as relying on an SoC or using an RTOS. The specialized systems that you’ll run into most commonly fall into several categories: • • • • • 09-ch09.indd 441 Medical systems In-vehicle computing systems Smart meters Surveillance systems Voice over IP 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 442 Medical Systems The push to smaller and increasingly powerful computing devices that can connect to the Internet has revolutionized some medical systems. People with irregular heartbeats have benefitted from pulses from an electronic device called a pacemaker for decades. The pacemaker simply stabilizes the heartbeat, granting the wearer generally a much longer lifespan. For 50+ years, pacemakers were (relatively) simple devices, implanted in patients and replaced periodically as their batteries depleted. Spin to today. IoT pacemakers not only provide stimulus to regularize the heartbeat but also transmit over the Internet so doctors and technicians can monitor the patient’s heart and the current level of battery power. IoT pacemakers eliminate the guesswork of when to replace or recharge a traditional pacemaker, yet another example of a breakthrough in medicine made possible through IT. See Figure 9-5. Other Internet of Medical Things (IoMT) devices—both wearable and implanted— monitor all sorts of things, from general vital signs to specific things like glucose levels in diabetic patients. The IoMT field continues to grow, combining medical systems with phenomenal technology advances. The inherent security risks involved with IoMT devices cannot be dismissed. Any device that connects to a network has vulnerabilities and the potential for hacking. A hacked medical lifesaving device could have deadly consequences. So far in the field attacks have been theoretical. There’s hope for humanity? NOTE As soon as you venture into the medical field, take into consideration the Health Insurance Portability and Accountability Act of 1996 (HIPAA) discussed way back in Chapter 1. HIPAA stipulates rules governing personal/ private medical information that security professionals absolutely need to account for in the planning and deployment of systems. Figure 9-5 IoT pacemaker shown in X-ray (Image: Trout55, Getty Images) 09-ch09.indd 442 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 443 Figure 9-6 Connected automotive computing system (Image: mbbirdy, Getty Images) In-Vehicle Computing Systems Automobile manufacturers have incorporated computing devices into their products for decades. Adding connectivity to the global network was but a matter of getting systems and electronics in place. The consumer market demands automobiles with built-in systems that provide navigational functions, entertainment functions, and even access to the Internet (Figure 9-6). Automobile manufacturers want to cater to consumers by including all of these great features, as well as the ability to access vehicle health information via network connections. These network connections may include Bluetooth, Wi-Fi, or even, in some cases, cellular connectivity. NOTE Although not included in the CompTIA Security+ exam, not surprisingly vehicle-to-vehicle (V2V) communications have standards, notably the IEEE 1609 Wireless Access in Vehicular Environments (WAVE) protocol stack. Also related are vehicular ad hoc networks (VANETs), connectivity options for on-the-fly interconnectivity among automobiles. These technologies, protocols, and standards have been around for years, but the push to selfdriving cars seems to furthering the cause. Again, V2V and VANET are not on the CompTIA Security+ 601 exam, but where there are interoperable wireless computer systems, you’ll find vulnerabilities that require careful consideration by IT security professionals. So if computers are now being built into automobiles or added in as aftermarket devices, what are the security ramifications? And how do you secure in-vehicle computer systems? Will it become necessary to install a firewall in your car? And it’s not just automobiles that have computing systems. Aircraft of all sorts, both manned and unmanned, have increasingly sophisticated computing systems, many connected to extended networks and the Internet. Your next unmanned aerial vehicle (UAV)—that’s a drone, for all you normal folks—guaranteed will have multiple embedded camera systems, high-end wireless networking capabilities, and an SoC to run them all (Figure 9-7). 09-ch09.indd 443 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 444 Figure 9-7 DJI drone with one SoC to rule them all! (Image: ROBYN BECK / Contributor, Getty Images) From a security perspective, in-vehicle computing systems have some of the same common vulnerabilities that other systems have, which may include network security issues, such as the vulnerabilities inherent to Bluetooth, Wi-Fi, and cellular technologies. There are also issues involving firmware and patch updates to the systems. Many of these systems have USB or SD card ports, for example, to upload firmware updates or play media content on the devices. Perhaps someday someone will develop a virus or other type of malware that could be injected into these types of systems via a removable media device. Other security issues may be only the speculative fantasies of geeks, such as a hacker taking over your car and driving it while you’re going down the road or conducting a DoS attack on your engine or transmission, resulting in the car coming to a complete halt on the Autobahn. However remote these possibilities may be, they may not be too far down the road (pun intended). In short, vehicular computing systems are a new frontier, for both security professionals and hackers. Although traditional security methods and controls will probably work to a large degree, other methods will have to be developed to ensure that these types of static hosts are well protected from malicious users and attacks. Smart Meters Smart meters rely on cellular and wireless networks to communicate to consumers and utility companies real-time information about power usage, usually electricity, but also natural gas or water. A smart meter can alert when something spikes unexpectedly—such as water usage, indicating a possible water main break that starts wastefully dumping liters of water—and help consumers and providers optimize power usage. Figure 9-8 shows a smart meter that records and reports on the electricity usage at my house. Surveillance Systems Consumer use of surveillance systems has exploded with the advent of phenomenal camera technologies, SoC capabilities, and cellular and Wi-Fi connectivity. Grainy footage of people trying to penetrate government facilities back in the day has evolved into 09-ch09.indd 444 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 445 Figure 9-8 Smart meter gloriously high-definition footage and audio of people stealing packages from your front porch. The wireless Ring doorbell at my front door (Figure 9-9), for example, enables me to interact in real time with people at the door, regardless of whether I’m in the house or across the planet (Figure 9-10). The security implications and considerations with modern IoT surveillance systems run from paranoia to downright scary. Ring devices, for example, interface with Amazon Figure 9-9 Ring doorbell (Image: Chip Somodevilla / Staff, Getty Images) 09-ch09.indd 445 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 446 Figure 9-10 Ring app Alexa home infotainment devices to send your security footage to “the cloud.” Nothing stops “the cloud” from sharing your footage with local law enforcement or companies that can monetize the information in some other way. Other device manufacturers have been accused of sending personal information gathered from their devices secretly to other nation states. EXAM TIP Surveillance systems are a good example of point-to-multipoint communication, where the base station interacts with multiple wireless nodes (the cameras). The nodes don’t communicate with each other, but rather all report back to the base. Voice over IP Office telephone systems used to have their own dedicated wiring and devices, all functioning on the antique POTS signaling standards. Telephone connections centered on a PBX block and used Cat 1 cabling with RJ-11 jacks (Figure 9-11). It became increasingly obvious that installing dual cable runs (Cat 1 and Cat 5) in new buildings late last century was a waste because Cat 5 could do the work of either cabling standard. Eventually developers came up with Voice over IP (VoIP), a way to do telephony over TCP/IP networks, with no need to use ancient technology. Many (most?) enterprises today have ditched the old PBX telephone systems for modern VoIP systems. Figure 9-11 RJ-45 and RJ-11 jacks (Image: pablohart, Getty Images) 09-ch09.indd 446 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-1: Embedded, Specialized, and Mobile Systems 447 This is all stuff you should remember from CompTIA Network+ or even CompTIA A+ training, so I doubt we’re telling you something new here. The real question for CompTIA Security+ is what security implications VoIP systems pose. You need to secure VoIP communications just like you would any other IP network. Typical VoIP attacks include denial of service, spoofing telephone numbers, and just harassment. Mobile Systems The term mobile systems refers to all of the general computing devices not tethered to a cable, such as laptop computers (running Windows, macOS, Linux, or Chrome), tablets (running iOS or Android), and smartphones (also iOS or Android). Figure 9-12 shows a Microsoft Surface portable computer running Windows 10. Mobile systems, as general-purpose devices, function similarly to other Internet of Computing (IoC) devices (workstations, servers, routers) and have similar security issues and solutions. Keep the OS and apps updated. Keep the firmware updated to ward off attacks. Manage the devices with firewalls and other standard security options. Mobile systems differ from the wired IoC devices in connectivity, on the other hand, which we’ll look at next, and in mobile-specific security issues (in Module 9-4). We’ll also explore problematic areas when introducing mobile devices to the enterprise. Figure 9-12 Microsoft Surface (and yes, I have a ping pong table in my dining room . . . Don’t judge!) 09-ch09.indd 447 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 448 Module 9-2: Connecting to Dedicated Systems This module covers the following CompTIA Security+ objectives: • 2.6 Explain the security implications of embedded and specialized systems • 3.5 Given a scenario, implement secure mobile solutions Dedicated systems rely on many of the same technologies to enable communication among devices. This module first explores the security implications in common technologies shared among the devices and then looks at low-power technologies exclusive to IoT devices. NOTE This module assumes you have CompTIA Network+ knowledge of how these various technologies work. If you need a refresher, check out the excellent CompTIA Network+ Certification All-in-One Exam Guide by yours truly. To put all of the communication technologies in context, this module offers several examples based on the following hypothetical scenario. The Bayland Widgets Corporation (BWC) main campus has several buildings connected via fiber-optic cabling and Ethernet. (The details of those connections are unimportant for this discussion; we’re just setting the stage.) One of the buildings houses the factory that builds BWC’s worldfamous widgets. A SCADA system—including processors, control modules, sensors, actuator arms, robotics, etc.—controls the production machines. The main office building has employees, naturally, and a diverse collection of IoC and IoT devices. These devices include standard workstations and servers, plus many portable computers, tablets, smartphones, wearables, and so on. Plus, the entire campus has a surveillance system comprising cameras and control units, all of which feed back to the security center. The menagerie of devices introduces a plethora of device communication types, all of which have security implications. Let’s look first at communication technologies prevalent in most of the devices, then turn to specific IoT communication technologies. Common Communication Technologies Many devices in the BWC campus connect with common technologies. These include cellular networks, 802.11 Wi-Fi, Bluetooth, NFC, and infrared. Cellular Current cellular networks rely on either 4G or 5G technologies connecting cells (geographical areas) via various radio frequencies. Cellular radio towers with base transceiver stations enable the networks to cover enormous areas. 4G networks provide excellent coverage using the 450- to 3800-MHz bands, enabling download speeds at up to 300 Mbps and upload speeds of 75 Mbps. 5G networks operate 09-ch09.indd 448 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-2: Connecting to Dedicated Systems 449 at three distinct bands: Low-band, Mid-band, and High-band. The higher the band, the faster the connection speed, but the shorter the range. 5G devices connect automatically at the fastest speed available at range. Most cellular devices also use a subscriber identity module (SIM) card (Figure 9-13) that stores identity (hence the name) and enables authentication between the device and mobile carriers. All sorts of devices use SIM cards, from smartphones to cameras to wearable IoT devices. NOTE SIM cards can be hacked, especially in older devices. The CompTIA 601 objectives don’t mention SimJacker, but the attack exploits a common software installed on SIM cards from virtually every manufacturer, called S@T Browser. The fix? Upgrade to a device that uses a current SIM card without that vulnerability. The BWC campus has several cellular towers nearby, providing Internet connectivity (and thus interconnectivity) with a ton of employee devices. Every employee has a smartphone, for example, and many have tablets with cellular connection capabilities. Cellular voice and data services these days offer very robust security. Direct sniffing of these networks is difficult at best (assuming you’re using a late-generation 4G/LTE or 5G phone). Carriers will quickly detect and act on any attempts to emulate a cell tower, for example, which could lead to serious legal ramifications for the bad actor. An attacker has the best potential for success attacking cellular by avoiding cellular altogether. The switch point for devices between cellular and Wi-Fi provides an excellent attack surface because Wi-Fi offers much weaker security than cellular. Finally, privacy issues should concern users and IT security folks when working with cellular. Turning off geolocation services—where the cellular provider can track your whereabouts at all times—can enhance privacy, although you’ll lose useful functionality. Getting directions from Siri or from Google Maps goes right out the window, because geolocation services access the Global Positioning System (GPS) satellite network to show where you are in relation to other places. Figure 9-13 Typical SIM card (Image: Thomas Trutschel / Contributor, Getty Images) 09-ch09.indd 449 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 450 Wi-Fi/Bluetooth Chapter 7 covered Wi-Fi in detail and Bluetooth a bit more lightly. Every wireless security aspect covered previously applies to mobile and IoT devices, but they add a few more problems. One of the most challenging issues in Wi-Fi comes from stored profiles. Mobile devices can grab standardized hotspot SSIDs pushed out by ISPs such as “xfinitywifi” or “attwifi,” and some will in turn become mobile hotspots that seem very similar to the initial hotspot (Figure 9-14). You can enhance or upgrade some dedicated devices by adding the latest generation Wi-Fi or Bluetooth card via a universal serial bus (USB) port. Conversely, some users might try to skirt air gap rules (where their devices should not connect with other devices) by plugging in a USB cellular device. These shouldn’t be common variances, but they might show up on a Security+ exam in your near future. EXAM TIP Bluetooth is an example of point-to-point communication, from one device to another device. BWC has a mesh Wi-Fi network throughout the campus, providing both interior and exterior space connectivity for mobile devices. For security, the IT department implements WPA3 encryption throughout, though also providing access using WPA2 for older devices during the transition year. The mixed encryption system isn’t ideal, but it’s good enough. Figure 9-14 Author’s Xfinity hotspot 09-ch09.indd 450 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-2: Connecting to Dedicated Systems 451 Near-Field Communication Many mobile devices use near-field communication (NFC), just like you read about in Module 7-2, for quick payments and such. NFC uses radio-frequency identification (RFID) technologies to enable communication with unpowered electronic tags on an unlicensed ISM radio-frequency band (13.56 MHz). All the security issues for NFC apply to its use in mobile devices. While NFC contains basic encryption, the technology relies on the short distances (within four inches) and quick communication to provide security. Modern payment services that use NFC, such as Apple Pay, add their own security protocols as well to ensure safety of personal information. NOTE Android embraces NFC heavily. Apple typically uses NFC only for the Apple Pay app, although Apple is slowly opening iOS to more NFC options. Infrared One of your authors loves his Android phones if for no other reason than only Androids (and not all of them) come with an infrared (IR) transmitter—enabling connectivity via light waves—known generically as an infrared blaster. IR blasters can emulate any IR remote control, turning any Android into a universal remote. Since these devices only transmit simple remote-control commands, there is no risk to your mobile device. The risk is that any IR blaster can quickly take complete control of any device designed to receive those commands, making the Android the bad actor. The only real defense is to block the IR receivers. NOTE The other author eschews Android, fully embracing the Apple iOS ecosystem. He’s clearly the more cultured of the two, even if it means not being able to hijack the hotel lobby television. IoT-Specific Communication Technologies IoT developers use communication technologies created specifically for low-powered IoT devices. There are quite a few proprietary and open-source technologies in use. Four common ones are Narrowband IoT, Bluetooth Low Energy, Zigbee, and ANT. Narrowband IoT Developers use the Narrowband Internet of Things (NB-IoT) technology for high connection density IoT deployment, specifically with an eye to maximizing battery life and minimizing costs. Narrowband means NB-IoT uses only a single radio frequency—200 KHz. The goal with NB-IoT is to provide good coverage and devices that don’t need recharging for years. 09-ch09.indd 451 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 452 EXAM TIP Part of the underlying physical layer of NB-IoT can rely on devices that use baseband radio processors that manage radio functions from multiple devices. Sounds like a circular definition, but you might see the term on the exam. Bluetooth Low Energy The inexpensive devices that employ the Bluetooth Low Energy (BLE) networking technology consume very little electricity, yet have a range similar to their big brother Bluetooth. BLE devices are not compatible with Bluetooth, but the technology is part of the Bluetooth 4.0 and Bluetooth 5 standards. Like Bluetooth, BLE creates a personal area network (PAN) for devices interconnecting. Every major mobile and desktop OS supports BLE. BLE devices range from security to home entertainment to medical. Zigbee Devices and systems that rely on the Zigbee communication protocols offer ad hoc personal area networks that use very low-power radios. This low-bandwidth solution works perfectly for things like medical device data collection and home automation. Zigbee is an open standard, so adoption by manufacturers is increasing. BWC has implemented centrally monitored Zigbee systems in its new buildings to control lighting, window blinds, access control, and climate control. The cost savings provided by the smart IoT systems compared to the older dumb systems in the original buildings will most likely lead to systems upgrades in the near future. Old might be quaint or picturesque, but energy efficiency helps everyone. ANT ANT is a low-speed, low-power networking technology. Wi-Fi and Bluetooth are powerful wireless tools, but both of these technologies require rather chatty, relatively powerhungry devices. Bluetooth isn’t nearly as power hungry or as fast as Wi-Fi, but when you have very small devices such as heart rate monitors, even Bluetooth uses too much power. Garmin introduced the proprietary ANT protocol around 2007 for low-power sensors that don’t send a lot of data and that often go for extended periods of time without transferring data (like your author’s heart rate monitor that’s used at most once a week). The latest version of ANT is called ANT+. ANT/ANT+ is a superb protocol that’s incredibly low powered and has enough bandwidth for many devices. ANT is encrypted with AES, so hacking isn’t an issue (yet). The only downside to ANT/ANT+ is that Apple devices lack an ANT radio. In that case you’d need an ANT/ANT+ USB dongle to talk to an ANT device (Figure 9-15). EXAM TIP You won’t be tested on ANT or ANT+ on the CompTIA Security+ exam. We’ve included the technology here as useful real-world information. 09-ch09.indd 452 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-3: Security Constraints for Dedicated Systems 453 Figure 9-15 ANT USB dongle ANT+ Module 9-3: Security Constraints for Dedicated Systems This module covers the following CompTIA Security+ objectives: • 2.6 Explain the security implications of embedded and specialized systems • 2.8 Summarize the basics of cryptographic concepts IT security specialists need a solid understanding of the security constraints and concerns for embedded systems, IoT systems, and specialized systems to help clients secure their networks. This section explores hardware, programming, and connectivity. Hardware Embedded and specialized systems come in an astonishing variety, but they have one feature in common: the static nature of their hardware. When you buy a device built around an SoC, for example, you can’t change or upgrade the core computing capabilities of the device. (That’s the compute portion of devices, in industry jargon.) You can certainly add all kinds of additional features to a Raspberry Pi, but the core CPU, RAM, and connection options don’t change. That static nature also applies to the security built into the device by the manufacturer, especially when dealing with IoT devices. Competition in the market drives manufacturers to reduce costs or provide low-cost devices for consumers. This often means serious resource constraints to favor price over security. Further, manufacturers release devices into the market with the assumption that they’re “place and forget” devices for consumers; in other words, once set up, consumers will assume they’re done configuring or messing with the devices. This leads to a lot of problems, especially when dealing with the flip side of hardware, software. Programming Dedicated systems—especially IoT—have glaring security weaknesses because of the nature of the systems. Consumers have deployed billions of IoT devices; manufacturers have chosen low cost and ease of use over security. Many IoT devices have very specialized operating systems based in read-only memory (ROM) of some sort that requires 09-ch09.indd 453 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 454 user interaction to upgrade or patch. Other dedicated devices rely on light Linux distros that may not have all the security locked down. I’m not exaggerating the problem here. A group of undergraduate students at Rutgers University in the United States developed the Mirai botnet, a simple and ingenious software program that did a blanket scan for open Telnet ports on IoT devices over a wide geographic area. Mirai targeted the IoT devices and automatically tried 61 user name and password combinations to build an enormous botnet army. And then the Mirai developers attacked. In September 2016, Mirai was successfully used against a French hosting company that provided tools to stop distributed denial-of-service (DDoS) attacks on Minecraft servers. You read that correctly. “Anna-Senpai,” the leader of the Mirai developers, was a serious Minecraft player. And he led a DDoS attack against a company specializing in anti-DDoS protection. NOTE Anna-Senpai’s real name is Paras Jha. His cohorts were Josiah White and Dalton Norman. All of them were just supersmart college students trying out a new technology. They served a lot of hours of community service after confessing to the FBI and, presumably, are deep in the white hat security world now. Unfortunately for the world, after the first successful Mirai botnet attack, the developers released the Mirai source code online. The next serious attack happened a month later against Dyn, Inc., which was a major provider of DNS services in the United States (subsequently acquired by Oracle). This attack caused some major players on the Internet to go dark for a few hours, including Twitter, Reddit, and Spotify. And the Mirai source code is still out there, getting modified and refined. The risk is real. Updating the programming that secures dedicated systems offers the best route to security. Let’s look at obstacles to updating and then paths to updating. Inability to Patch Dedicated systems often don’t lend themselves to automatic updates. This constraint could be caused by several factors: • Some of these dedicated systems are not always connected to the Internet—a network constraint. In the case of SCADA systems or medical devices, for example, there may be no way to connect them to the Internet without incurring a security risk. • The vendor may not have included an automated update process with the device. Some devices may require the download of a patch, an image, or a piece of firmware that has to be manually installed on the device using a very specific process, often resulting in rebooting the device into a special maintenance mode. • The data sensitivity of the systems in question might be so high that the organization can’t perform automatic updates or connect them to the Internet for classification reasons. For example, some US government systems, particularly those of a classified nature, cannot be connected to the Internet. 09-ch09.indd 454 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-3: Security Constraints for Dedicated Systems 455 For these reasons, manual updates may be required for some static dedicated systems. If you have the ability to automate device updates, then obviously you should use that method as much as possible, since it ensures that updates are applied in the most efficient way possible. On the other hand, manual updates can give you the opportunity to test patches and other software updates before applying them to a production system. Often, you can download updates manually, test them in a test environment that mirrors your production systems, and then apply them to the production systems only after you are sure that they will cause no ill effects. You should also record manual updates, so that you can trace any issues that arise from them back to a particular patch or update. Firmware Version Control Many devices running dedicated systems get firmware updates. Remember that firmware is typically applied as updates to programming in the chips on the hardware portion of the system, rather than as patches to the operating system or application software. Firmware updates can fix issues with both the operating system and hardware on a device, as well as provide for security patches. Firmware updates can also add new features to a device. For personal devices, firmware version control may not be a big issue; often if the user experiences any issues with the device after the firmware has been updated, the user can reverse the update process and regress to an earlier version rather easily. In an enterprise environment, however, it’s extremely important to maintain version control on firmware updates, because a firmware update may cause issues with production software or devices that the organization needs to fulfill its business purposes. As I mentioned previously when discussing manual updates, you should first test firmware updates in an appropriate environment, and then apply them to production devices only after you have confirmed that they cause no ill effects. You also should record firmware versions in a central database. Read the documentation accompanying the firmware updates to learn about any known issues with other software or hardware used by the organization. Connectivity Dedicated systems for the most part connect to other computing devices. Systems running multipurpose operating systems like Linux and hooked up with Ethernet or 802.11 Wi-Fi generally use the standard protocols used for connectivity with IoC devices. Moving over to IoT device connectivity, on the other hand, brings up a lot of security issues in communication and cryptography. Low-powered IoT devices rely on low-power protocols, such as Zigbee, Bluetooth Low Energy (BLE), and IPv6 over Low-Power Wireless Personal Area Networks (6LoWPAN), that enable connectivity over a short range (compared to 802.11 Wi-Fi). (You read about Zigbee and BLE in Module 9-2.) Low-powered IoT devices rely on lightweight cryptographic algorithms that don’t offer as much security as heavier ones—because they need to function using much lower computing power. Worse, because of their static nature, the IoT devices cannot upgrade to more secure protocols in the future. And the previously mentioned “place and forget” nature of IoT means consumers won’t even think about upgrading with more secure components down the road. 09-ch09.indd 455 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 456 Most IoT devices rely on simple password-based authentication methods, though the process and security involved vary tremendously. There is no universal authentication protocol for IoT, but rather a multitude of frameworks, all constrained by the relatively limited processing power of IoT devices. Some ecosystems from the big players, like Amazon and Google, use the same authentication as their desktop applications, but smaller players that create light bulbs, refrigerators, and so on? Their devices rely on simple passwords. Compounding the security issues with IoT devices is the implied trust among devices within a network space. Implied trust traditionally refers to all the networked computers inside an enterprise or single building. You trust that employees won’t hack each other or do malicious things. You protect against outside threats, but not inside. (This is rapidly changing, as we’ll discuss in a moment.) In the context of consumer IoT devices, implied trust refers to the trust consumers have in device vendors. Consider the scenario of a consumer purchasing a series of home automation devices to control lighting, heating and cooling, security, and so on. Assuming that the consumer purchases from a single vendor, such as Google or Amazon, the consumer implicitly trusts the vendor to provide security in two areas. First, inside the home, the consumer implicitly trusts that the vendor has made its devices interoperable and secure. Second, beyond the home, the consumer implicitly trusts that the vendor has a secure cloud to support all the cloud features of its devices. In practice, this trust model breaks down swiftly because consumers mix and match IoT devices from different vendors all the time. These heterogenous vendor devices often don’t communicate well together straight out of the box. What is the typical consumer’s solution? Lower the security settings that stop the devices from talking amongst themselves. This, as we say in the business, is a bad thing. And at the consumer level, all the security issues outlined previously remain the unfortunate current state of affairs. At the enterprise level, in contrast, a lot of companies have adopted (or are in the process of adopting) the National Institute for Standards and Technologies (NIST) zero trust architecture (ZTA) guidelines that recommend organizations require proper authentication and authorization in all interactions with assets. In other words, ZTA throws out the implicit trust model and insists on secure connections within as well as without the enterprise. In practice it means that Joe’s iPad should not connect to any network shares without proper authentication, even though Joe has been a loyal employee for 22 years. NOTE See NIST Special Publication 800-207, Zero Trust Architecture, for more on ZTA. Module 9-4: Implementing Secure Mobile Solutions This module covers the following CompTIA Security+ objectives: • 3.5 Given a scenario, implement secure mobile solutions • 3.7 Given a scenario, implement identity and account management controls 09-ch09.indd 456 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 457 When so-called “smart” devices entered the consumer market, they were all the rage because, beyond traditional voice communications, they enabled users to communicate with friends, family, and associates nearly simultaneously in several new ways, by using social media sites, sharing photos and videos, using text and chat messages, and so on. They also became the ubiquitous computing platform, replacing traditional desktops and laptops to a large degree, enabling users to play games, manage their finances, dictate short documents, and perform other tasks. The problem was, however, that users expected to see the same cool, wide-ranging functions on their work computers as well, but the business world hadn’t caught up with the mobile device app explosion. As a result, many users started bringing their devices to work, most of the time without management approval, and doing company work on them. Figure 9-16 shows examples of some of the personal mobile devices that wander into the office. That’s all changed now, of course, as businesses rapidly adopted mobile devices into their infrastructures. Businesses issue smartphones and tablets to employees, provide for their communications links and Internet services, and allow employees to use these devices to perform work functions—and, in some cases, even do some of their personal stuff on them. Unfortunately, any new technology or change in the business infrastructure introduces new security issues. Sometimes organizations are in such a hurry to implement new technology that they overlook security issues, and their main focus is on how much stuff the technology or device can do. In other words, the focus is on the functionality of the device or technology rather than on security. With the infiltration of mobile devices into the business world, however, developers and engineers, business managers, and even users to a certain degree have worked to make use of mobile devices more secure. Figure 9-16 Personal mobile devices that tend to show up at work (photo courtesy of Sarah McNeill Photography, used with permission) 09-ch09.indd 457 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 458 The next few sections explore some of the security features that mobile devices offer and how to integrate them into the corporate infrastructure and networks. We’ll do this in six sections: • • • • • • Mobile device management Deployment models Inventory control and asset tracking Application management and security Encryption and authentication Enforcement and monitoring for device security Mobile Device Management Mobile device management (MDM) is a process in the business infrastructure in which the company can bring mobile devices under the umbrella of the company’s existing enduser device management for traditional desktops and laptops. MDM enables a company to manage all the devices that connect to the company’s network centrally—not just the devices tied to a desk that don’t exit the building in someone’s pocket. Many considerations go into MDM, including the wide variety of vendors, platforms, operating systems, applications, features, and even telecom providers for these devices. Unless the business standardizes on one vendor or platform, it may find that managing all of these different devices is challenging. Essentially, through MDM, a business can manage a mobile device using the same technologies and methods used for traditional desktops, and with the same level of control. Figure 9-17 shows an example of a basic MDM software user interface. Figure 9-17 Basic MDM software 09-ch09.indd 458 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 459 Subsets or related technologies to MDM include MicroSD hardware security modules, unified endpoint management, and Security Enhanced Linux for Android. Let’s explore these technologies. MicroSD Hardware Security Module The MicroSD hardware security module (HSM) works specifically with Android-based smartphones and tablets to provide robust encryption and security via a microSD smart card. The smart card includes public key encryption, public key authentication, and crazy levels of encryption, including 256-bit AES, 521-bit ECC, and 4096-bit RSA. Add a MicroSD HSM card to devices in your enterprise to enhance security. NOTE We covered HSM in general way back in Module 5-4. Check out that section to refresh your memory if necessary. Unified Endpoint Management Unified Endpoint Management (UEM) tools take MDM to the next level, providing the enterprise with centralized control over all endpoints, including mobile devices (smartphones, tablets, laptops) and IoT devices such as wireless MFDs (introduced in Module 9-1) and wearables. EXAM TIP UEM products currently seem to be as much about marketing as about technology, but expect a question about the awesome control offered by UEM for the enterprise on the CompTIA Security+ exam. Security Enhanced Linux for Android Increasingly, Android-based devices rely on a mandatory access control (MAC) mechanism to provide security called Security Enhanced Linux (SELinux). SELinux gives security experts security policies that govern all aspects of deployed Android devices, such as operations, objects, and processes. This granular security enhances the traditional security in Android devices which was based on discretionary access control (DAC). DAC worked well enough in the beginning, but malicious or faulty apps could leak data; DAC permissions lacked subtleties or granularity to work well in some situations; and root or superuser accounts could run all sorts of setuid programs or system daemons with no control. SELinux for Android—or SEAndroid, in CompTIA speak—provides a serious security upgrade over DAC. Deployment Models The deployment model with mobile devices specifies how employees get a mobile device in their hands. The deployment model defines issues such as whether the corporation provides devices to employees or employees bring their own devices. The deployment model defines aspects of mobile device management. 09-ch09.indd 459 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 460 Corporate-Owned, Business Only A corporate-owned, business only (COBO) deployment model means that the organization issues mobile devices to employees and holds ownership of the devices, the maintenance of the devices, and the applications and the data on the devices. Bring Your Own Device Everyone already has a smartphone, and bring your own device (BYOD) deployment means to have employees bring their own devices and use them for business purposes. This brings up a number of security issues, as BYOD compels employees to offer some amount of control of their personal systems to the organization. Choose Your Own Device With the choose your own device (CYOD) deployment model the organization offers a selection of mobile devices from which employees can choose. Either employees buy the devices outright or the organization owns the device and offers employees an attractive rental for the duration of their employment. In either case, the organization has complete control over the mobile device (although employees may install personal apps). Corporate-Owned, Personally Enabled Similar to COBO, with the corporate-owned, personally enabled (COPE) deployment model the organization issues a mobile device, but unlike COBO, employees are allowed to install a specific number of preapproved (white-listed) apps for their personal use. Containerization BYOD, CYOD, and COPE all share a common problem: how can we separate the organization’s applications and data from the employee’s applications and data on the same device? Every mobile operating system supports containers to address this issue. A container is nothing more than a virtual operating system just as a virtual machine is virtual hardware. Using containerization enables the organization to create a separate operating system on the mobile device, completely separating the employee’s applications and data from the organization’s. Figure 9-18 shows one example of containerization offered on an Android system. Note that there are two Contacts, two Calendars, and two Play Store apps. Using containerization enables this feature. Containerization normally relies on storage segmentation, the practice of partitioning off storage areas in the device, usually to provide separate areas for company or sensitive data and personal data. Through storage segmentation, it’s possible to impose different access controls on specific types of data. Figure 9-19 describes the concepts of sandboxing (which you read about in Module 8-2) and containerization. Storage segmentation can be imposed on the device’s built-in storage area or on removable media as well. Virtual Desktop Infrastructure If an organization wants to avoid the issue of device ownership altogether, it can get around the problem completely by offering a virtual desktop infrastructure (VDI), which 09-ch09.indd 460 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 461 Figure 9-18 Containerization on an Androidbased mobile device you also read about in Module 8-3. With a VDI, every employee has a virtual machine running on a server owned by the organization. The employee may access this machine via any device running any operating system and is presented a virtual desktop with the applications the employee needs. Figure 9-19 Containerization used to separate apps and data from each other Sandboxing Containerization App Personal Data App Corporate Data Hardware Interface Mobile Device 09-ch09.indd 461 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 462 Inventory Control and Asset Tracking One of the great things about using mobile devices in the enterprise is that employees can use them anywhere. Unfortunately, however, that means that the devices don’t always reside on the company property. They walk off with the user, so the company often doesn’t know exactly where they are and what they’re being used for, or even who’s using them. As with traditional desktops, inventory control is important with mobile devices, perhaps more important, since they are portable. Several technologies make it easier to manage mobile devices, even when they are off the company campus. We will discuss many of these technologies later when we get into device-specific security methods, but for now understand that companies can’t implement any of them well unless they are part of an overall MDM infrastructure. MDM enables centralized control of devices, including inventory control, so IT management always knows the location of devices and, in many cases, knows which authorized users have control over them. Since mobile devices tend to talk to the MDM infrastructure often, IT management can have an almost 100 percent real-time inventory of mobile devices via the MDM software. Of course, the traditional method of having a user bring the device to the office to scan it with a barcode reader can also make sure that IT management knows the device is safely checked in or out. Along with inventory control, asset tracking is important. Asset tracking means knowing the location of devices at all times, who has them, and how they are being used. Asset tracking can be provided through the MDM infrastructure as well as via the device— through features such as GPS and other location-based services, as well as software agents that can be placed on the devices when they come under management control. Combined with strong security policies applied to mobile devices through MDM, asset tracking can provide visibility into what’s happening with these devices at all times. Figure 9-20 illustrates how location services can show the exact location of a device. Figure 9-20 Location services make it easier to track mobile device assets. 09-ch09.indd 462 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 463 Device Access Control Yet another management goal of business when integrating mobile devices into its networks is to control what data, systems, and resources the mobile devices connect to and access— device access control. As with any other device or user, the goal is to make sure that people using mobile devices can access only the data and systems they need to do their job and no more. Your organization can and should definitely use traditional access controls, which include restrictive rights, permissions, and privileges. You can implement these controls at the resource level, such as assigning permissions to a folder or file, but you can also implement them at the network level. For example, modern mobile devices can use strong authentication mechanisms, such as certificate-based authentication, which you can integrate with your network’s directory services, such as Active Directory. This can prevent an unauthorized user from stealing a mobile device and attempting to connect to your network and access your resources. Other traditional methods of access control that you can use in conjunction with mobile devices include firewalls, network access control devices, and so on. On the flip side of device access control, in addition to the desire to control access to network resources within the business perimeter, most administrators also want to control what a device can access and do when it leaves the company network. This can be harder to control since the device is no longer under the physical or logical control of the company. It may connect to unsecure home or hotel networks, for example, or to unsecure free Wi-Fi networks that have no required authentication or encryption. These are challenges when trying to control devices remotely and control what they can access offsite. Fortunately, administrators can apply MDM security policies to devices to control access to certain content (content management), applications, and Internet sites. These policies prevent users from doing things or accessing content that’s prohibited by the company. Figure 9-21 illustrates how this works. Geotagging Geotagging is the process of including in a file, such as a picture or video file, metadata that contains the location information of the device when the file was created or processed. For example, people often take pictures and geotag them with location information, which might include the GPS coordinates, time and date stamps, and other types of information, to include a description of an event. Geotagging is useful from several perspectives in the corporate environment. An investigator conducting a forensic analysis of a device, for example, could look at geotag information in the file metadata to try to determine patterns of where the device has been and how it has been used. Geotagging also may serve a purpose in verifying the time, date, and location of an employee who performs a certain action, which may be required for compliance or policy reasons. NOTE The CompTIA Security+ exam objectives use the term GPS tagging for geotagging. These terms are synonymous. The use of geotagging in tracking employees and their activities must be carefully considered, however, in environments where users are allowed to process corporate data on their own personal devices. As with all personal data, geotagging can give away information 09-ch09.indd 463 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 464 Figure 9-21 MDM can push security configuration and policies to all mobile devices in the enterprise. MDM Server Different Security Policies 1 2 3 Device Group 2 Device Group 1 Device Group 3 that an employee might not want the company to have, especially if it involves information of a personal nature. We’ll discuss that scenario later in the module. As with all the other issues discussed here, geotagging should be addressed in policy documents. Remote Management Remote management is the key to protecting data in the corporate infrastructure. As mentioned, once the device leaves company property, it’s difficult to control—that is, unless the company has installed and configured remote management capabilities. This requires admins to configure the MDM software properly, as well as the settings on the device itself. Remote management enables a business to reach out and touch the device virtually to monitor its location and use, as well as to protect data in the event the device is lost or stolen. You need to be aware of a few different remote management functions for the Security+ exam, as well as for use on the job. Geolocation uses the GPS feature of the mobile device to locate it. Figure 9-22 shows the Google device manager (called Find My Device) locating the author’s phone as he watches the Houston Astros instead of working on this book. Remote wiping (or remote wipe) is a capability you should use in the event a device is lost or stolen and is not likely to be recovered. In this scenario, the MDM software would enable you to send commands to the device that will completely wipe its storage areas, erasing sensitive data, configuration, and so on. Wiping the device could effectively render it useless, or at least reset it back to factory conditions. 09-ch09.indd 464 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 465 Figure 9-22 Google device manager Remote control is another security feature that you can enable on the device through MDM software. You can use this feature to take over the device if a user can’t figure out how to do something, of course, but a more useful security feature might be to take control of the device to prevent its misuse or to extract data from it before it’s wiped. You can also remotely unlock a device using this feature if the user has forgotten a passcode and doesn’t want to keep typing it in and risk wiping the device after several incorrect entries. Onboarding/Offboarding Managing mobile devices starts with the processes the organization uses in onboarding and offboarding mobile devices. Onboarding encompasses all of the processes used to introduce a new mobile device into the network and assign it to the user. This includes provisioning the device to ensure that the device has the right settings to access the mobile service provider or telecom provider, as well as installing all of the companyapproved applications on the device. Provisioning also entails making sure the right user permissions and accesses are installed on the device, such as user names and passwords, digital certificates, and so on. The point of onboarding and provisioning a device is to make sure that the device is fully functional so that a user can use it to process company data. Offboarding, as you might guess, is almost the exact opposite of onboarding and provisioning. During offboarding, IT management collects the device from the user and takes away access to the network with this device. In an orderly offboarding process, user data is removed from the device and, if applicable, returned to the user. Corporate data is also removed from the device and stored or disposed of as appropriate. 09-ch09.indd 465 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Chapter 9: Securing Dedicated Systems 466 The device might be decommissioned completely, removing it from inventory and disposing of it, in the case of legacy devices or devices that no longer function properly. If the device is not disposed of, it might be reused within the enterprise and issued to another user; in that event it would go through the onboarding and provisioning process again (although it may not require as much in terms of device activation and so on). If the device has been collected from the user based upon a violation of policy or the law, the device might also be subject to forensic analysis and examination, as well as retention of any personal and corporate data on the device. In any event, a process should be established within the organization for both onboarding and offboarding mobile devices securely. Application Management and Security Application management means that the organization determines what applications can be installed and used on the mobile device, as well as where it gets those applications from. The organization can impose technical policies on devices that prohibit them from downloading applications from certain app stores, for example, and restrict them to downloading applications only from the internal company app repository or a specific vendor or platform app store. Application management also means exercising control over what apps can do on the device, as well as what data they can access. For example, an organization can use certain methods to prevent a user’s personal app from accessing any corporate data stored on the device. These methods may include restricting copy and paste operations, restricting a user’s personal e-mail app from accessing the corporate e-mail’s contacts list, and other controls. Application control can be imposed on the device using different technical policies, as well as tight control over user rights and privileges on the device. Other methods, such as sandboxing and containerization (discussed earlier in this module), can be used to separate applications and data from each other so that no interaction is possible between them. Application Security The organization should exert some sort of control over the security of the applications themselves, simply because there may be security and interoperability issues with all the different apps on mobile devices. This is dubbed application management. Some of these applications may not work well with company-approved enterprise applications, and some of these apps may not store, process, or transmit sensitive data securely. The organization may want to control which types of apps can be installed and used on mobile devices, using either MDM or mobile application management (MAM) technologies. The company may also want to set up its own app store, rather than allowing users to download apps from a vendor’s app store. An admin can use push notifications to get services to devices, defining what apps are included (rather than relying on users to check for and download important apps or updates). Application Whitelisting In application whitelisting, the organization allows only certain trusted applications to be installed on mobile devices. The organization may exclude certain applications due 09-ch09.indd 466 25/03/21 2:18 PM All-In-One / Mike Meyers’ CompTIA Security+™ Certification Guide, 3e / Meyers & Jernigan / 369-4 / Chapter 9 Module 9-4: Implementing Secure Mobile Solutions 467 to security, interoperability, or licensing issues. Applications acceptable in the organization might include secure e-mail applications, file transfer applications, and productivity applications. Whitelisting enables the organization to include accepted applications in policy configuration files that are sent to and maintained on the mobile device. These policies may prevent a user from downloading and using unapproved apps or from using certain vendor app stores. Often, secure configuration files for these apps are also included for an app when the device is provisioned. EXAM TIP The CompTIA Security+ 601 exam objectives replaced the term whitelisting with allow list in objective 3.2 and application approved list in objective 4.4. You will most likely see the commonly used term— whitelisting—on both the exam and certainly in the real world, but be prepared if CompTIA updates their question pool to see the newer terms. Encryption and Authentication Using encryption on mobile devices can protect data while it is stored on the device or during transmission from the device back to the corporate network through untrusted networks, such as the Internet. Mobile devices can make use of encryption in various ways, includ