IRJET-Foster Hashtag from Image and Text
advertisement
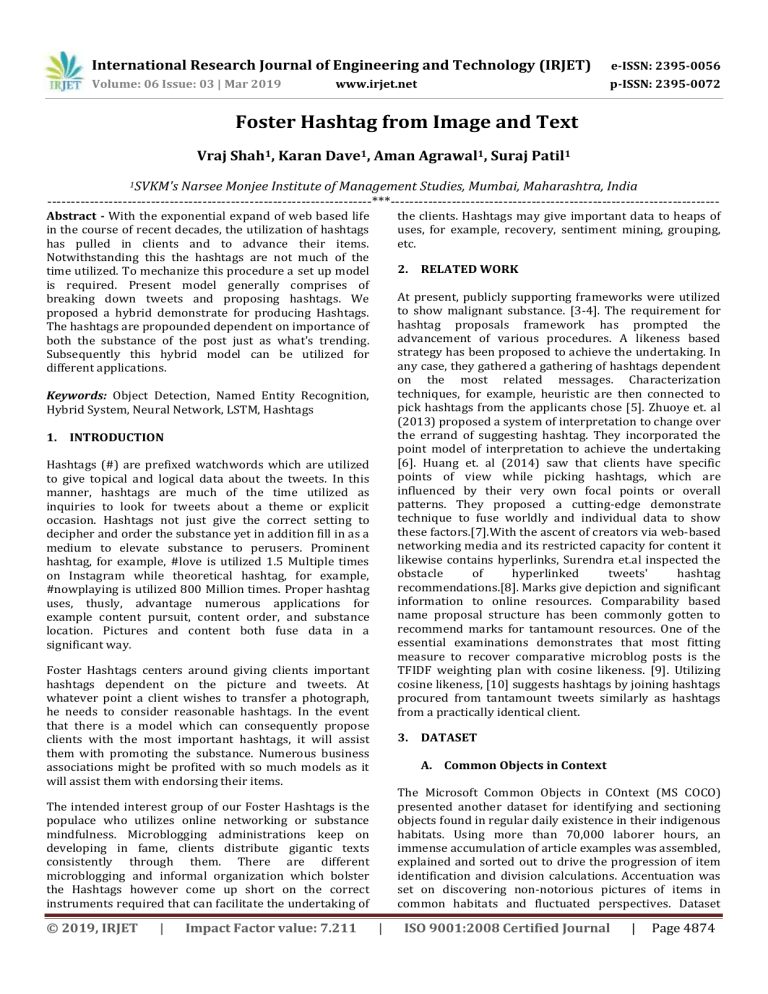
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056 Volume: 06 Issue: 03 | Mar 2019 p-ISSN: 2395-0072 www.irjet.net Foster Hashtag from Image and Text Vraj Shah1, Karan Dave1, Aman Agrawal1, Suraj Patil1 1SVKM's Narsee Monjee Institute of Management Studies, Mumbai, Maharashtra, India ---------------------------------------------------------------------***---------------------------------------------------------------------- Abstract - With the exponential expand of web based life in the course of recent decades, the utilization of hashtags has pulled in clients and to advance their items. Notwithstanding this the hashtags are not much of the time utilized. To mechanize this procedure a set up model is required. Present model generally comprises of breaking down tweets and proposing hashtags. We proposed a hybrid demonstrate for producing Hashtags. The hashtags are propounded dependent on importance of both the substance of the post just as what's trending. Subsequently this hybrid model can be utilized for different applications. the clients. Hashtags may give important data to heaps of uses, for example, recovery, sentiment mining, grouping, etc. 2. RELATED WORK At present, publicly supporting frameworks were utilized to show malignant substance. [3-4]. The requirement for hashtag proposals framework has prompted the advancement of various procedures. A likeness based strategy has been proposed to achieve the undertaking. In any case, they gathered a gathering of hashtags dependent on the most related messages. Characterization techniques, for example, heuristic are then connected to pick hashtags from the applicants chose [5]. Zhuoye et. al (2013) proposed a system of interpretation to change over the errand of suggesting hashtag. They incorporated the point model of interpretation to achieve the undertaking [6]. Huang et. al (2014) saw that clients have specific points of view while picking hashtags, which are influenced by their very own focal points or overall patterns. They proposed a cutting-edge demonstrate technique to fuse worldly and individual data to show these factors.[7].With the ascent of creators via web-based networking media and its restricted capacity for content it likewise contains hyperlinks, Surendra et.al inspected the obstacle of hyperlinked tweets' hashtag recommendations.[8]. Marks give depiction and significant information to online resources. Comparability based name proposal structure has been commonly gotten to recommend marks for tantamount resources. One of the essential examinations demonstrates that most fitting measure to recover comparative microblog posts is the TFIDF weighting plan with cosine likeness. [9]. Utilizing cosine likeness, [10] suggests hashtags by joining hashtags procured from tantamount tweets similarly as hashtags from a practically identical client. Keywords: Object Detection, Named Entity Recognition, Hybrid System, Neural Network, LSTM, Hashtags 1. INTRODUCTION Hashtags (#) are prefixed watchwords which are utilized to give topical and logical data about the tweets. In this manner, hashtags are much of the time utilized as inquiries to look for tweets about a theme or explicit occasion. Hashtags not just give the correct setting to decipher and order the substance yet in addition fill in as a medium to elevate substance to perusers. Prominent hashtag, for example, #love is utilized 1.5 Multiple times on Instagram while theoretical hashtag, for example, #nowplaying is utilized 800 Million times. Proper hashtag uses, thusly, advantage numerous applications for example content pursuit, content order, and substance location. Pictures and content both fuse data in a significant way. Foster Hashtags centers around giving clients important hashtags dependent on the picture and tweets. At whatever point a client wishes to transfer a photograph, he needs to consider reasonable hashtags. In the event that there is a model which can consequently propose clients with the most important hashtags, it will assist them with promoting the substance. Numerous business associations might be profited with so much models as it will assist them with endorsing their items. 3. DATASET A. Common Objects in Context The Microsoft Common Objects in COntext (MS COCO) presented another dataset for identifying and sectioning objects found in regular daily existence in their indigenous habitats. Using more than 70,000 laborer hours, an immense accumulation of article examples was assembled, explained and sorted out to drive the progression of item identification and division calculations. Accentuation was set on discovering non-notorious pictures of items in common habitats and fluctuated perspectives. Dataset The intended interest group of our Foster Hashtags is the populace who utilizes online networking or substance mindfulness. Microblogging administrations keep on developing in fame, clients distribute gigantic texts consistently through them. There are different microblogging and informal organization which bolster the Hashtags however come up short on the correct instruments required that can facilitate the undertaking of © 2019, IRJET | Impact Factor value: 7.211 | ISO 9001:2008 Certified Journal | Page 4874 International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056 Volume: 06 Issue: 03 | Mar 2019 p-ISSN: 2395-0072 www.irjet.net measurements show the pictures contain rich relevant data with numerous items present per picture. The dataset contains 91 regular article classifications with 82 of them having in excess of 5,000 named cases, Fig. 6. Altogether the dataset has 2,500,000 named occasions in 328,000 pictures. SSD utilizes VGG16 to extract features. At that point, it identifies objects utilizing the Conv4_3 layer. For delineation, we take the Conv4_3 to be 8 × 8 spatially (it ought to be 38 × 38). For every cell (likewise called area), it makes 4 object forecasts. Every expectation makes out of a limit box and 21 scores for each class (one additional class for no item), and we pick the most astounding score as the class for the limited article. Conv4_3 makes a sum of 38 × 38 × 4 forecasts: four expectations for each cell paying little mind to the profundity of the element maps. Of course, numerous expectations contain no item. SSD holds a class "0" to demonstrate it has no items. B. CoNLL 2003 The mutualundertaking of CoNLL-2003 concerns language-free named substance acknowledgment. They will focus on four sorts of named elements: people, areas, associations and names of different elements that don't have a place with the past three gatherings. They will utilize the information for building up a named-element acknowledgment framework that incorporates an AI part. For every language, extra data (arrangements of names and non-commented on information) will be provided too. Each word has been put on a different line and there is an unfilled line after each sentence. The main thing on each line is a word, the second a grammatical feature (POS) tag, the third a syntactic piece tag and the fourth the named substance tag. The lump labels and the named element labels have the arrangement I-TYPE which implies that the word is inside an expression of sort TYPE. Just if two expressions of a similar sort quickly pursue one another, the primary expression of the second expression will have label B-TYPE to demonstrate that it begins another expression. A word with label O isn't a piece of expression. Here is a precedent: U.N. NNP I-NP I-ORG official NN I-NP O Ekeus NNP I-NP I-PER heads VBZ I-VP O For IN I-PP O Baghdad NNP I-NP I-LOC . 4. . O SD does not utilize an assigned area proposition arrange. Rather, it sets out to a straightforward strategy. It processes both the area and class scores utilizing little convolution channels. Subsequent to extricating the component maps, SSD applies 3 × 3 convolution channels for every cell to make expectations. (These channels figure the outcomes simply like the customary CNN channels.) Each channel yields 25 channels: 21 scores for each class in addition to one limit box. B. Named Entity Recognition Named Entity Recognition (NER) alludes to the errand of finding and ordering named of elements, for example, individuals, associations, areas and others inside a content. It is a pivotal pre-handling venture in numerous Natural Language Processing (NLP) applications, for example, exchange administrator and question noting framework with the goal that clients can inquiry for data in regards to these elements. LSTM arrange performs well when prepared on information that has conditions that are seen inside the forward heading (future). Be that as it may, it performs seriously on succession marking errands which expects access to both past and future setting. [11] proposed a bidirectional LSTM system to exploit the data of both past and future information includes inside a given time span. Figure 2 demonstrates a case of bidirectional LSTM organizes for an NER arrangement task. In vanilla LSTM systems, the concealed state just takes data just from past yet in bidirectional LSTM structure, the shrouded state is unfurled forever ventures of past and future. At that point, these two concealed states are joined to shape the last yield [12]. Other change incorporates resetting the shrouded state to 0 toward the start of each sentence to guarantee the system observes the start and the finish of the information focuses. O FOSTER HASHTAGS A. Single Shot Multibox Detector The SSD approach depends on a feed-forward convolutional network that delivers a fixed-measure gathering of boxes and scores for the nearness of item class examples in those containers, trailed by a non-most extreme concealment venture to create the last location. The SSD object identification makes out of 2 sections: ● ● Extracting the features, and Apply filters to identify the objects © 2019, IRJET | Impact Factor value: 7.211 | ISO 9001:2008 Certified Journal | Page 4875 International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056 Volume: 06 Issue: 03 | Mar 2019 p-ISSN: 2395-0072 www.irjet.net ON, 2010, IAT.2010.63 pp. 492-499. doi:10.1109/WI- 2) Wang, Xiaolong, Furu Wei, Xiaohua Liu, Ming Zhou, and Ming Zhang. “Topic Sentiment Analysis in Twitter.” Proceedings of the 20th ACM International Conference on Information and Knowledge Management - CIKM ’11 (2011). doi:10.1145/2063576.2063726. 3) Lee, Kyumin, Steve Webb, and Hancheng Ge. “Characterizing and Automatically Detecting Crowdturfing in Fiverr and Twitter.” Social Network Analysis and Mining 5, no. 1 (January 9, 2015). doi:10.1007/s13278-014-0241-1. Figure 1: Bi-directional LSTM network 4) Wang, Gang, Christo Wilson, Xiaohan Zhao, Yibo Zhu, Manish Mohanlal, Haitao Zheng, and Ben Y. Zhao. “Serf and Turf.” Proceedings of the 21st International Conference on World Wide Web WWW ’12 (2012). doi:10.1145/2187836.2187928. C. Foster Hashtag The model which we have implemented is based on generating hashtags from both the image as well as text. The SSD model works on image processing and is used to find objects from the image. The objects identified in this image are then further used to generate relevant hashtags. 5) Gassler, Wolfgang, Eva Zangerle, Martin Bürgler, and Günther Specht. “SnoopyTagging.” Proceedings of the 21st International Conference Companion on World Wide Web - WWW ’12 Companion (2012). doi:10.1145/2187980.2188102. Similarly, for the captions provided by the user, we perform Named Entity Recognition which is used to identify keywords from the text. These keywords are then further used to generate relevant hashtags. The objects and keywords extracted from both models are used to generate the trending hashtags. 6) Ding, Zhuoye, Qi Zhang, and Xuanjing Huang. "Automatic hashtag recommendation for microblogs using topic-specific translation model." Proceedings of COLING 2012: Posters (2012): 265-274. doi:10.1145/2348283.2348339 The trending hashtags are derived from a corpus which is built by us. We have collected a set of trending hashtags for each object as well as for different keywords which will be used to generate the hashtags. We also give abstract trending hashtags which can be used by user even when there is no object or keyword identified in image/text. 7) Zhang, Qi, Yeyun Gong, Xuyang Sun, and Xuanjing Huang. "Time-aware personalized hashtag recommendation on social media." In Proceedings of COLING 2014, the 25th International Conference on Computational Linguistics: Technical Papers, pp. 203-212. 2014. doi: 10.24963/ijcai.2017/478 5. CONCLUSION Hashtags play a crucial role in promoting content as well as to attract customers attention. The users need to think of these hashtags when uploading a content on the social websites. Instead of this, if we created a model which automatically suggest the users with trending hashtags, it would be easy for the users to use them. However, the task of providing suitable hashtags to user is an important task. The model suggested in this paper is an integration of both the image as well as text to generate relevant hashtags. This model outperforms the other models as other models worked only on either text or image. 8) Sedhai, Surendra, and Aixin Sun. "Hashtag recommendation for hyperlinked tweets." In Proceedings of the 37th international ACM SIGIR conference on Research & development in information retrieval, pp. 831-834. ACM, 2014. doi: 10.1145/2600428.2609452 9) Zangerle, Eva, Wolfgang Gassler, and Günther Specht. "On the impact of text similarity functions on hashtag recommendations in microblogging environments." Social network analysis and mining 3.4 (2013): 889-898. REFERENCES 1) S. Asur and B. A. Huberman, "Predicting the Future with Social Media," 2010 IEEE/ACM International Conference on Web IntelligenceIntelligent Agent Technology (WI-IAT), Toronto, © 2019, IRJET | Impact Factor value: 7.211 10) Duan, Yajuan, et al. "An empirical study on learning to rank of tweets." Proceedings of the | ISO 9001:2008 Certified Journal | Page 4876 International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056 Volume: 06 Issue: 03 | Mar 2019 p-ISSN: 2395-0072 www.irjet.net 23rd International Conference on Computational Linguistics. Association for Computational Linguistics, 2010 11) Graves, Alex, Abdel-rahman Mohamed, and Geoffrey Hinton. “Speech recognition with deep recurrent neural networks.” Acoustics, speech and signal processing (icassp), 2013 ieee international conference on. IEEE, 2013. 12) Ma, Xuezhe, and Eduard Hovy. “End-to-end sequence labeling via bi-directional lstm-cnnscrf.” arXiv preprint arXiv:1603.01354 (20 © 2019, IRJET | Impact Factor value: 7.211 | ISO 9001:2008 Certified Journal | Page 4877