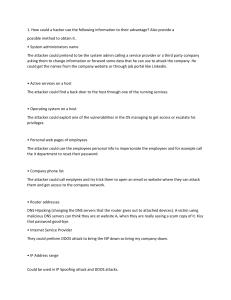
1. How could a hacker use the following information to their advantage? Also provide a possible method to obtain it. • System administrators name The attacker could pretend to be the system admin calling a service provider or a third party company asking them to change information or forward some data that he can use to attack the company. He could get the names from the company website or through job portal like Linkedin. • Active services on a host The attacker could find a back door to the host through one of the running services. • Operating system on a host The attacker could exploit one of the vulnerabilities in the OS managing to get access or escalate his privileges. • Personal web pages of employees The attacker could use the employees personal info to impersonate the employees and for example call the it department to reset their password. • Company phone list The attacker could call emplyees and try trick them to open an email or website where they can attack them and get access to the company network. • Router addresses DNS Hijacking (changing the DNS servers that the router gives out to attached devices). A victim using malicious DNS servers can think they are at website A, when they are really seeing a scam copy of it. Kiss that password good-bye. • Internet Service Provider They could preform DDOS attack to bring the ISP down so bring my company down. • IP Address range Could be used in IP Spoofing attack and DDOS attacks. 2. Describe a method to stop a distributed denial of service (DDoS) attack. On-premise appliances The on-premise approach to DDoS protection uses hardware appliances deployed inside a network, placed in front of protected servers. Such appliances usually have advanced traffic filtering capabilities armed with a combination of geoblocking, rate limiting, IP reputation and signature identification. Typical mitigation appliances can be effectively used to filter out malicious incoming traffic. This makes them a viable option for stopping application layer attacks. 3. Datagram Number P1 P2 P3 P4 Desired Action Deny Permit Permit Deny Datagram Number P1 P2 P3 P4 Desired Action Deny Permit Permit Deny R2, R1, R3 Deny(R2) Deny(R2) Deny(R2) Deny(R3) R1, R2, R3 Deny(R2) Permit(R1) Permit(R1) Deny(R3) R1, R3 Deny(R3) Permit(R1) Permit(R1) Deny(R3) 4. First we take instruction detection system to connect to engineering systems and we take Firewall and or screening router system to connect to sales and marketing and also accounting then we take External web and ftp server and Email server and to connect the engineering and marketing and we take email services to connect to engineering college and marketing and mainly u know about internet and ISP routers provide services. The given below we provide details about internet and ISP routers and some above given scenarios. Intrusion Detection System: An Intrusion Detection System (IDS) is a system that monitors network traffic for suspicious activity and issues alerts when such activity is discovered. It is a software application that scans a network or a system for harmful activity or policy breaching. Firewall: In computing, a firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. A firewall typically establishes a barrier between a trusted internal network and untrusted external network, such as the Internet external web: In fact, an external or hyperlink is any link that was posted on another website but points to your web resource. Same way, when you insert a link to another resource on your site – it is called an external or outbound link. The hyperlink points to an external domain. Email server: A mail server (sometimes also referred to an e-mail server) is a server that handles and delivers email over a network, usually over the Internet. A mail server can receive e-mails from client computers and deliver them to other mail servers. A mail server can also deliver e-mails to client computers. Admin server Internet: A server administrator, or admin has the overall control of a server. This is usually in the context of a business organization, where a server administrator oversees the performance and condition of multiple servers in the business organization, or it can be in the context of a single person running a game server.