Uploaded by
IAEME PUBLICATION
Anomaly Detection Method: Cyber-Attack Detection in Fuzzy Environments
advertisement
International Journal of Mechanical Engineering and Technology (IJMET)
Volume 10, Issue 03, March 2019, pp. 220-235. Article ID: IJMET_10_03_023
Available online at http://www.iaeme.com/ijmet/issues.asp?JType=IJMET&VType=10&IType=3
ISSN Print: 0976-6340 and ISSN Online: 0976-6359
© IAEME Publication
Scopus Indexed
DETECTION ENVIRONMENT FORMATION
METHOD FOR ANOMALY DETECTION
SYSTEMS
Nazym Zhumangaliyeva
Kazakh national womens teacher traning university
Kazakh National Research Technical University after K.I. Satpayev,
Anna Korchenko
Department of Information Technology Security, National Aviation University
Aliya Doszhanova
Kazakh national womens teacher traning university
Aigul Shaikhanova
Shakarim State University of the City of Semey
Shangytbayeva Gulmira
K.Zhubanov Aktobe Regional State University
Serik Smagulov
Shakarim State University of the City of Semey
Shaikhametov Erzhan
Shakarim State University of the City of Semey
ABSTRACT
Due to the intensive development of the digital business, malicious software and
other cyber threats are becoming more common. In order to increase the level of
security there are needed appropriate special countermeasures, which are able to
remain effective when new types of threats occur, and which allow to detect cyberattacks targeting on a set of information system resources in fuzzy conditions.
Different attacking effects on the corresponding resources generate various sets of
anomalies in a heterogeneous parametric environment. There is known a tuple model
of the formation of a set of basic components that allow to identify cyber-attacks. For
its effective application a formal implementation of the approach to the formation of
sets of basic detection rules is necessary. For this purpose, there has been developed a
method that focuses on solving problems of cyber-attacks detection in computer
systems, which is implemented through three basic steps: formation of anomaly
http://www.iaeme.com/IJMET/index.asp
220
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
identifiers subsets; formation of decisive functions; formation of conditional detection
expressions. Using this method, it is possible to form the necessary set of detection
rules, which determine the level of anomalous state of values in a heterogeneous
parametric environment, characteristic for the impact of a certain type of attack. The
use of this method at the creation intrusion detection systems will expand their
functionality regarding the cyber-attacks detection in a weakly formalized fuzzy
environment.
Keywords: detection rules, attacks, cyber-attacks, anomalies, intrusion detection
systems, anomaly detection systems, attack detection systems.
Cite this Article: Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova,
Aigul Shaikhanova, Shangytbayeva Gulmira, Serik Smagulov and shaikhametov
Erzhan, Detection Environment Formation Method for Anomaly Detection Systems,
International Journal of Mechanical Engineering and Technology, 10(3), 2019, pp.
220-235.
http://www.iaeme.com/IJMET/issues.asp?JType=IJMET&VType=10&IType=3
1. RELEVANCE
Nowadays, the intensive development, as well as the enormous scale and rate of information
technology implementation in modern business have become a natural process for developed
corporations. The level of company informatization is one of the main factors for its
successful development, and in the conditions of a large market dynamism and complication
of its infrastructure, information becomes a strategic resource. The development of
information technologies is being transformed so quickly that the classic protection
mechanisms cannot remain effective and provide adequate security for information system
resources, and malicious software and other cyber threats are becoming more common. In this
regard, there are needed special tools in order to detect and to prevent security breaches.
Intrusion detection systems are used for this, which are an integral part of any serious security
system, and the global trend is that intrusion and anomalies detection will become a
mandatory function of any operating system and will already be used in various software.
Expanding the functionality of such systems by identifying previously unknown cyber-attacks
characterized by unspecified or unclearly defined criteria will allow actually to remain
functional in a weakly formalized fuzzy environment. The use of the necessary methods,
models and methodologies of information security based on fuzzy sets for the creation of
appropriate means of detecting intrusions and anomalies is the basis for successfully
countering to these cyber-attacks. One of the important stages in the anomalies detection is
the creation of fuzzy (detection) rules [1]-[10]. According to this, the actual scientific task is
the formalization of the detection rules creation process, which make it possible to detect
cyber-attacks targeting on various information system resources in fuzzy conditions.
2. ANALYSIS OF EXISTING RESEARCH
Effective security tools used to solve problems of cyber-attacks detection are: the tuple model
for generating a set of basic components for cyber-attacks detection [11], fuzzy approaches
for intrusions detection [12]-[13] and for anomalies detection [14]; corresponding fuzzy
models [11], [15], methods [16]-[23] and intrusion detection systems [24]-[27]; sets of fuzzy
rules [1]-[10]; as well as other developments used to solve protection problems under fuzzy
conditions [28], [29]. These researches have shown the effectiveness of using the
mathematical apparatus of fuzzy sets, and its use in order to formalize the approach for cyberattacks identifying will improve the process of creating appropriate intrusion detection
http://www.iaeme.com/IJMET/index.asp
221
editor@iaeme.com
Detection Environment Formation Method for Anomaly Detection Systems
systems. It should be noted that the set of attacking effects on the information systems
resources gives a rise to many anomalies among the values in a heterogeneous parametric
environment [11],[15]. For an effective application of the well-known model [11], a formal
implementation of the formation process of sets of basic detection rules is necessary, which
will allow searching for an identifying term [17], [21]-[23] in a given linguistic variable.
Using this term, using the appropriate set of rules, we can determine the level of the
anomalous state generated by the influence of the corresponding class of cyber-attacks.
3. MAIN OBJECTIVE OF RESEARCH
On the basis of the analysis of existing researches and the relevance of the task, the main
objective of this work is to develop a detection environment formation method (DEFM) for
anomaly detection systems operating in a weakly formalized fuzzy environment. Using this
method (at solving problems of cyber-attacks detection), it is possible effectively to detect the
level of the anomalous state characteristic for a certain type of attacks regarding to a specific
heterogeneous parametric environment in a given time interval.
4. MAIN PART OF RESEARCH
In order to create subsets of the basic detection rules DR i (see (19) in [11]), we will develop
an appropriate method that will allow to formalize the process of obtaining the corresponding
rules used to detect the i -th cyber-attack based on parametric sub-environments of various
dimensions [11], [15]. The proposed DEFM is focused on solving problems of attacks
detection in computer systems and is based on three stages: formation of anomaly identifiers
subsets; formation of decisive functions; formation of conditional detection expressions.
Stage 1 – formation of anomaly identifiers subsets.
The subset IAi is built on the basis of the set of all possible IA anomaly identifiers (ID),
represented as
{
IA =
о 1
IAо } { IA1 , IA2 , ..., AI }
,
( о 1, ) ,
(1)
and by means of which (in linguistic form) it is possible to display possible levels of an
anomalous state in a m -dimensional heterogeneous parametric environment that can be
generated by a cyber-attack with ID CAi [11], and – an amount of anomaly ID.
For example, at 9 according to (1) the set IA can be represented as follows:
9
{
IA =
IAо } { IA1 , IA2 , ..., AI 9 }
о 1
{ IAН , IAБНВ , IAНС , IAС , IAВС ,
IAБВН , IAВ , IAП , IAГ } {"Н", "БНВ", "НC", "C",
"ВC", "БВН", "В", "П", "Г"}
(2)
where: IA1 IAН "Н" , IA2 IAБНВ "БНВ" , IA3 IAНС "НС" , IA4 IAС "С" , IA5
IAВС "ВС" , IA6 IAБВН "БВН" , IA7
IAВ "В" , IA8 IAП "П" , IA9 IAГ "Г" are
respectively the anomaly IDs by which in linguistic forms: “LOW (L)” (at 1 ), “MORE
LOW THAN HIGH (MLTH)” (at 2 ), “BELOW AVERAGE (BA)” (at 3 ),
http://www.iaeme.com/IJMET/index.asp
222
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
“AVERAGE (A)” (at 4 ), “ABOVE AVERAGE (AA)” (at 5 ), “MORE HIGH THAN
LOW (MHTL) (at 6 ), “HIGH (H)” (at 7 ), “LIMIT (L)” (at 8 ), “BOUNDARY
(B)” (at 9 ), possible anomaly levels can be displayed.
Next, we form a subset of the anomaly ID for the subset of rules DR i [11] i.e.:
n
{
i 1
IAi } = {IA1 , IA 2 , …, IAn } , ( i 1,n ) , (3)
where IAi IA will be defined as:
vi
IAi = {
u 1
IAiu } { IAi1 , IAi 2 , ..., IAivi } ,
( u 1,vi ) , (4)
in this case vi denotes the amount of anomaly IDs, by which in linguistic forms it is
possible to display possible anomaly levels generated by cyber-attacks with ID CAi .
Therefore, an expression (3) taking into account (4) will be presented in the following form:
n
{
i 1
vi
n
IAi }
{
=
{
i 1
IAiu }}
u 1
=
{{ IA11 , IA12 , ..., IA1v1 } , { IA21 , IA22 , ..., IA2v2 } , …,
{ IAn1 , IAn2 , ..., AI nvn }}
(5)
For example, at n 3 (i.е. for cyber-attacks with ID CA1 = CASN = SN , CA2 = CADS = DS and
CA3 = CASP = SP ) and v1 v2 v3 5 taking into account (1), we define the necessary IDs in
order to display the corresponding anomaly level. Then the expression (5) taking into account
(2) will have the following form:
3
{
3
vi
IAi } { { IAiu }}
i 1
= i 1 u 1
=
{{ IA11 , IA12 , IA13 , IA14 , IA15 } , { IA21 , IA22 , IA23 , IA24 , IA25 } ,
{ IA31 , IA32 , IA33 , IA34 , IA35 }}
{{ IASNН , IASNБНВ , IASNБВН , IASNВ , IASNП } , { IADSН , IADSБНВ , IADSБВН , IADSВ , IADSП } ,
{ IASPН , IASPБНВ , IASPБВН , IASPВ , IASPП }}
{{"Н", "БНВ", "БВН", "В", "П"} , {"Н", "БНВ", "БВН", "В", "П"} ,
{"Н", "БНВ", "БВН", "В", "П"}}
(6)
where: SN – Scanning of ports, DS – Denial of service, SP – Spoofing, as well as
IA12 IASNБНВ "БНВ" , IA13 IASNБВН "БВН" , IA14
IASNВ "В" ,
IA15 IASNП "П" , respectively, the IDs of such anomalous states in the attacking
environment, which represent a different degree of expert confidence regarding to the
influence of a cyber-attack with an ID CA1 = CASN [11]; IA21 IADSН "Н" ,
IA22 IADSБНВ "БНВ" , IA23 IADSБВН "БВН" , IA24 IADSВ "В" , IA25 IADSП "П"
IA11 IASNН "Н" ,
http://www.iaeme.com/IJMET/index.asp
223
editor@iaeme.com
Detection Environment Formation Method for Anomaly Detection Systems
IA15 IASNП "П" , respectively, the IDs of such anomalous states in the attacking
environment, which represent a different degree of expert confidence regarding to the
influence of a cyber-attack with an ID CA2 = CADS ; IA31 IASPН "Н" , IA32 IASPБНВ "БНВ" ,
IA33 IASPБВН "БВН" , IA34 IASPВ "В" , IA35 IASPП "П" IA15 IASNП "П" , respectively,
the IDs of
IA15 IASNП "П" , respectively, the IDs of
such anomalous states in the attacking environment, which represent a different degree of
expert confidence regarding to the influence of a cyber-attack with an ID CA3 CASP .
Stage 2 – formation of decisive functions.
In order to implement this stage, we introduce the set of all arguments of the decisive
functions АF and a subset of such arguments АFi .
n
{
i 1
АFi } = {АF1 , АF2 , …, АFn } ,
( i 1,n ) ,
(7)
where АFi АF , will be defined as:
АFi = { i АF } = {АFi1 АFi 2 ... АF } ,
ia
iw i
w
a 1
( a 1,wi )
(8)
in this case wi – the amount of subsets of arguments of the decisive functions used to
detect the i -th cyber-attack, and the symbol indicates the direct composition of the sets.
Taking into account the expression (8) the formula (7) will be written in the following form: =
{{АF11 , АF12 , ..., АF }
1w1
{АF21 , АF22 , …,
n
{
i 1
n
АFi } = {
wi
{ АFia }} АF2w 2 } …
i 1 a 1
{АFn1 , АFn 2 , …, АF } ,
nw n
( i 1,n, a 1,wi )
(9)
The subset АFia АFi will be defined as:
АFia = {
rj
АFias } =
s 1
{ АFia1 , АFia 2 , ..., АFiarj } , ( s 1,rj )
(10)
where rj – amount of units in АFia (that displays the amount of units in Tije (see (13) in
[11])).
http://www.iaeme.com/IJMET/index.asp
224
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
n
wi
n
АFi } { { АFia }}
i
1
Then the expression (9) taking into account (10) takes the following form:
= i 1 a 1
=
{
n
{
i 1
wi
{ {
rj
a 1 s 1
АFias }}}
=
{{{ АF111 , АF112 , ..., АF11rj } { АF121 , АF122 , ..., АF12rj } ... { АF1w1 1 , АF1w1 2 , ..., АF1w1rj }},
{{ АF211 , АF212 , ..., АF21rj } { АF221 , АF222 , ..., АF22rj } ... { АF2w2 1 , АF2w2 2 , ..., АF2w2rj }},
...,
{{ АFn11 , АFn12 , ..., АFn1rj } { АFn21 , АFn22 , ..., АFn2rj } ... { АFnwn 1 , АFnwn 2 , ..., АFnwnrj }}}
{{ AF111 , AF121 , ..., АF1w 1 , AF111 , AF121 , ..., АF1w 2 , ..., AF111 , AF121 , ...,
1
1
1
АF1w1 r
2
1
1
АF1w1 r
АF1w1 r
АF1w1 r
АF112 , АF12 r , ..., АF1w 1 , АF112 , АF12 r , ..., АF1w 2 , ..., АF112 , АF12 r , ...,
1
2
1
АF1w1 r
1
2
1
1
1
1
1
1
АF11r , AF122 , ..., АF1w 1 , АF11r , AF122 , ..., АF1w 2 , ..., АF11r , AF122 , ...,
1
АF1w1 r
1
1
АF11r , АF12 r , ..., АF1w 1 , АF11r , АF12 r , ..., АF1w 2 , ..., АF11r , АF12 r , ...,
2
1
1
2
1
1
АFn11 , АFn22 , ..., АFnw 1 , АFn11 , АFn22 , ..., АFnw 2 , ..., АFn11 , АFn22 , ...,
АF1w1 r
1
2
2
n
АFnwn rj
n
n
АFn12 , АFn22 , ..., АFnw 1 , АFn12 , АFn22 , ..., АFnw 2 , ..., АFn12 , АFn22 , ...,
n
АFnwn rj
n
АFn12 , АFn2r , ..., АFnw 1 , АFn12 , АFn2r , ..., АFnw 2 , ..., АFn12 , АFn2r , ...,
2
2
n
АFnwn rj
2
n
АFn1r , АFn21 , ..., АFnw 1 , АFn1r , АFn21 , ..., АFnw 2 , ..., АFn1r , АFn21 , ...,
1
n
1
n
n
1
http://www.iaeme.com/IJMET/index.asp
n
225
1
АFnwn rj
,
,
, ...,
, ...,
АFnwn rj
1
АFn1r , АFn22 , ..., АFnw 1 , АFn1r , АFn22 , ..., АFnw 2 , ..., АFn1r , АFn22 , ...,
1
А Fnwn r j
АFnwn rj
АFn12 , АFn21 , ..., АFnw 1 , АFn12 , АFn21 , ..., АFnw 2 , ..., АFn12 , АFn21 , ...,
,
, ...,
2
n
},
АFnwn rj
n
АFn11 , АFn2r , ..., АFnw 1 , АFn11 , АFn2r , ..., АFnw 2 , ..., АFn11 , АFn2r , ...,
,
, ...,
2
..., { АFn11 , АFn21 , ..., АFnwn 1 , АFn11 , АFn21 , ..., АFnwn 2 , ..., АFn11 , АFn21 , ...,
n
, ...,
АF1w1 r
АF11r , AF121 , ..., АF1w 1 , АF11r , AF121 , ..., АF1w 2 , ..., АF11r , AF121 , ...,
1
, ...,
1
1
1
,
1
1
1
,
1
2
АF112 , AF122 , ..., АF1w 1 , АF112 , AF122 , ..., АF1w 2 , ..., АF112 , AF122 , ...,
1
, ...,
1
АF112 , AF121 , ..., АF1w 1 , АF112 , AF121 , ..., АF1w 2 , ..., АF112 , AF121 , ...,
1
,
1
1
AF111 , АF12 r , ..., АF1w 1 , AF111 , АF12 r , ..., АF1w 2 , ..., AF111 , АF12 r , ...,
2
АF1w1 r
1
AF111 , AF122 , ..., АF1w 1 , AF111 , AF122 , ..., АF1w 2 , ..., AF111 , AF122 , ...,
2
=
,
, ...,
editor@iaeme.com
Detection Environment Formation Method for Anomaly Detection Systems
АFn1r , АFn2r , ..., АFnw 1 , АFn1r , АFn2r , ..., АFnw 2 , ..., АFn1r , АFn2r , ...,
1
2
n
2
1
n
АFnwn rj
2
1
}} =
{{ SAF11 , SAF12 , …, SAF1w1 } , …, { SAFi1 , SAFi 2 , …, SAFiwi } , …, the
{SAFn1 , SAFn 2 , …, SAFnwn }}
(11)
where, for clarity, there are used angle brackets " " , " " , which separate the subsets of
arguments of the decisive functions ( SAFia ), which reflect the values of terms Tijep .
Taking into account the expression (11), we determine that in order to identify the i -th
cyber-attack, the total amount of argument subsets is calculated using the formula
mi
wi rj
j 1
, ( j 1,mi ) .
(12)
Then (11) taking into account (12) it can be written in the following form
n
{
n
wi
AFi } { { SAFia }}
i 1
= i 1 a 1
, ( a 1,wi )
(13)
Next, we introduce the set of all binary decisive functions SF and a subset of such
functions SFi
n
{
i 1
SFi } = {SF1 , SF2 , …, SFn } , ( i 1,n )
(14)
where SFi SF , ( i 1,n ) will be defined as
SFi = {
wi
a 1
SFia } = { SFi1 , SFi 2 , …, SFiwi } а
(15)
SFia SFia ( SAFia )
(16)
We should note that the function SFia defines the relationships in SAFia , formed by the
expert in form of logical chains (based on disjunctions and conjunctions) for the subsequent
construction of detection expressions, focused on identifying the i -th cyber-attack.
An expert in order to obtain a specific set of binary functions that reveals a i -th cyberattack creates a corresponding template that defines relationships in SAFia .
For example, if SAFia = АF111 , АF112 , АF113 , and the templates have the form АF АF
АF or АF ( АF АF ) , then respectively SF11 = АF111 АF112 АF113 or SF11 = АF111
( АF112 АF113 ) .
The specific values of the elements of a subset АFi ( i 1,n ) are formed on the basis of
the binary equivalence function E( x , y ) , which takes the value 1 only if x and y are equal,
ie,:
1, при x y
E( x , y ) = 0, при x y.
http://www.iaeme.com/IJMET/index.asp
(17)
226
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
on the basis of this we define, that АFias E ( NUM iа , s ) , and as arguments E( x , y ) , we will
use fuzzy terms indexes Tijep and Pi p .
f
Let consider an example of the formation of decisive functions, at n 3 , i 1,3 ( CA1 =
f
f
f
= SN f , CA 2f = CA DSf = DS f and CA 3f = CASP
= SP f ),
CASN
r2 r3 3 (see the example (15) in [11]).
m1 m3 2 ,
r1 5 ,
m2 3 ,
According to (12)
m1
w1 rj r1 r2 5 3 15 ,
j 1
m2
w2 rj r1 r2 r3 5 3 3 45 ,
j 1
m3
w3 rj r1 r2 5 3 15 ,
j 1
and the expression (11) will be defined as:
3
3
{
i 1
AFi }
wi
3
wi
rj
{ AFia }} { { { AFias }}}
= {AF1 , AF2 , AF3 } = i 1 a 1
= i 1 a 1 s 1
=
{
{{{ AF111 , AF112 , AF113 , AF114 , AF115 } { AF121 , AF122 , AF123 }},
{{ AF211 , AF212 , AF213 , AF214 , AF215 } { AF221 , AF222 , AF223 } { AF231 , AF232 , AF233 }},
{{ AF311 , AF312 , AF313 , AF314 , AF315 } { AF321 , AF322 , AF323 }}}
{ AF111 , AF121 , AF112 , AF121 , AF113 , AF121 , AF114 , AF121 , AF115 , AF121 , ...,
AF111 , AF123 , AF112 , AF123 , AF113 , AF123 , AF114 , AF123 , AF115 , AF123 },
{ AF211 , AF221 , AF231 , AF212 , AF221 , AF231 , SF213 , AF221 , AF231 ,
AF214 , AF221 , AF231 , AF215 , AF221 , AF231 ...,
AF211 , AF223 , AF233 , AF212 , AF223 , AF233 , AF213 , AF223 , AF233 ,
AF214 , AF223 , AF233 , AF215 , AF223 , AF233 },
{ AF311 , AF321 , AF312 , AF321 , AF313 , AF321 , AF314 , AF321 , AF315 , AF321 , ...,
AF311 , AF323 , AF312 , AF323 , AF313 , AF323 , AF314 , AF323 , AF315 , AF323 } =
{{ SAF11 , SAF12 , …, SAF1 15 } , {SAF21 , SAF22 , …, SAF2 45 } ,
{SAF31 , SAF32 , …, SAF }}
3 15
(18)
In [11] there was determined that in order to detect cyber-attacks SN ( CA1 = CASN
= SN )
and SP ( CA 3 = CASP
= SP ), it is necessary simultaneously to use two parameters defining
the 2 -dimensional parametric sub-environment (NVC-AV-(КВК-ВВК)-sub-environment and
NSС-NPSA-(КОП-КПОА)-sub-environment), and for a cyber-attack DS ( CA 2 = CA DS = DS
) – three parameters defining the 3 -dimensional parametric sub-environment (NSС-SPRDBR-(КОП-СОЗ-ЗМЗ)-sub-environment) (see (9) in [11]). And also:
f
f
f
f
f
f
f
http://www.iaeme.com/IJMET/index.asp
227
f
editor@iaeme.com
f
Detection Environment Formation Method for Anomaly Detection Systems
NVC (КВК) – “Number of virtual channels)”,
AVC (ВВК) – “Age of virtual channel (),
NSC (КОП) – “Number of simultaneous connections to the server
NPSA (КПОА) – “Number of packets with the same sender and recipient address
SPR (СОЗ) – “Speed of processing requests from customers
DBК (ЗМЗ) – “Delay between requests from one user
An expert in order to obtain a specific set of functions that detect SN and SP creates a
template АF АF , and for DS – АF ( АF АF ) .
Further, according to the generated templates, as well as according to (15) and (18), we
define, for example, SF3 :
SF3 = {
w3
SF3a } =
a 1
{( E ( NUM 31 , 1 ) E ( NUM 32 , 1 )) ,
( E ( NUM 31 , 2 ) E ( NUM 32 , 1 )) ,
( E ( NUM 31 , 3 ) E ( NUM 32 , 1 )) ,
( E ( NUM 31 , 4 ) E ( NUM 32 , 1 )) ,
( E ( NUM 31 , 5 ) E ( NUM 32 , 1))} ,
{( E ( NUM 31 , 1 ) E ( NUM 32 , 2 )) ,
( E ( NUM 31 , 2 ) E ( NUM 32 , 2 )) ,
( E ( NUM 31 , 3 ) E ( NUM 32 , 2 )) ,
( E ( NUM 31 , 4 ) E ( NUM 32 , 2 )) ,
( E ( NUM 31 , 5 ) E ( NUM 32 , 2 ))} ,
{( E ( NUM 31 , 1 ) E ( NUM 32 , 3 )) ,
( E ( NUM 31 , 2 ) E ( NUM 32 , 3 )) ,
( E ( NUM 31 , 3 ) E ( NUM 32 , 3 )) ,
( E ( NUM 31 , 4 ) E ( NUM 32 , 3 )) ,
( E ( NUM 31 , 5 ) E ( NUM 32 , 3 ))} .
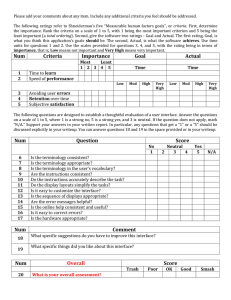
Figure 1 shows the expert distribution of all possible levels of anomaly generated by the
attacking environment and displayed by the identifiers of the attacking actions through
different values of the parameters of the NSC-NPSA-(КОП-КПОА)-sub-environment.
From the graphical interpretation (Fig. 1) it can be seen that the support blocks with the
БВН, Б and П (“MORE HIGH THAN LOW”, “HIGH”, “LIMIT”) identifiers are the most
significant for identifying SN.
On the basis of this, an example of concrete calculations will be presented only for the
decisive functions ( SF3 11 , ..., SF3 15 ) from SF3 , i.e.
http://www.iaeme.com/IJMET/index.asp
228
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
SF3 11
SF3 12
SF3 13
( E ( NUM 31 ,1 ) E ( NUM 32 ,3 )) ,
( E ( NUM 31 , 2 ) E ( NUM 32 , 3 )) ,
( E ( NUM 31 , 3 ) E ( NUM 32 , 3 )) ,
SF3 14
( E ( NUM 31 , 4 ) E ( NUM 32 , 3 )) ,
SF3 15 (E(NUM 31 ,5) E(NUM 32 ,3)).
(19)
Note that at j 1 , r1 5 , NUM 31 3 and s 1,5 for T (see (27) in [16])
e
31
5
T31e = {
ep
T31s
}=
s 1
~
ep
{T311
~
ep
,
ep
ep
ep
~T312 , ~T313 , ~T314 , ~T315 } =
ep
ep
ep
ep
{ ОМ 31ep М 31
~ , ~ , ~С31 , ~Б31 , ОБ
~ 31 }
the equivalence function according to (17) takes the value
E( NUM 31 , 1 ) E( NUM 31 , 2 )
E( NUM 31 , 4 ) E( NUM 31 , 5 ) 0
because NUM 31 3 1 2 4 5 .
T ep T ep T ep T ep T ep
С ep
This follows from the fact that ~313 ~ 311 ~ 312 ~ 314 ~ 315 , i.е. ~ 31
ОБ
ep
ОМ 31
~
ep
М 31
~
~Б31
ep
31
~ .
p
еp
μ ОМ
~ 31
еp
C
~ 31
еp
Б31
~
еp
ОБ
~ 31
AL317
AL316
AL315
AL314
AL313
AL312
AL311
Н
Н
Н
Н
1
КОП 1
КОП 2
КОП 3
КОП 4
0,9
,
0,8
0,7
0,6
0,5
0,4
0,3
0,2
0,1
0
0,280
0,095
0,580
x
0,500
0,008
0,063
0,250
1,000
0,010
1
0,9
,
0,8
0,7
0,6
0,5
0,4
0,3
0,2
0,1
0
КПОА1
еp
М
~ 31
БНВ
БНВ
Н
Н
~C 32
КПОА2
П
В
БВН
БНВ
AL321
AL322
AL323
AL324
AL325
x
1,000
Н
(КОП 1, КПОА2) (КОП 2, КПОА2) (КОП 3, КПОА2) (КОП 4, КПОА2)
0,820
~
М32
еp
Н
0,100
0,082
(КОП 1, КПОА1) (КОП 2, КПОА1) (КОП 3, КПОА1)(КОП 4, КПОА1)
еp
~Б 32
еp
μ
p
f
~PSPКПОА
еp
ТSРКПОА
f
~PSPКОП
Н
еp
Т SРКОП
http://www.iaeme.com/IJMET/index.asp
229
editor@iaeme.com
ep
Detection Environment Formation Method for Anomaly Detection Systems
Figure 1 Graphical interpretation of expert distribution of identifiers of attacking actions
(displayed by two-dimensional support areas Н, БНВ, БВН, В, П)
and fuzzy values of current parameters P31 , P32 regarding to linguistic standards T31еp ,
~ ~
T32еp , respectivelyAlso E( NUM 31 , 3 ) 1 because NUM 31 3 ,
f
f
T ep T ep
С31ep С31ep
which follows from the fact that ~313 ~313 , i.е. ~
~ .
Similarly, for
3
T32e = {
T32eps } =
s 1
~
еp
{Т 321
~
еp
,
еp
~Т 322 , ~Т 323 } =
{ М 32ep С32ep Б32ep }
~ ,~ ,~
at j 2 , r2 3 , NUM 32 3 , s 1,3 (see (27) in [16]
the equivalence function according to (17) takes the value
E( NUM 32 , 1 ) E( NUM 32 , 2 ) 0
because NUM 32 3 1 2 .
ep
ep
еp
ep
T321
T322
This follows from the fact that T323
, i.е. Б32еp М 32
С32ep , and E( NUM 32 , 3 ) 1
~
~
~
~
~
~
~
ep
ep
T323
because NUM 32 3 , which follows from the fact that T323
, i.е. Б32еp Б32еp .
~
~
~
Therefore
SF3 11 ( E ( NUM 31 , 1 ) E ( NUM 32 , 3 )) = ( 1 0 ) 0 ,
SF3 12 ( E ( NUM 31 , 2 ) E ( NUM 32 , 3 )) = ( 1 0 ) 0 ,
SF3 13 ( E ( NUM 31 , 3 ) E ( NUM 32 , 3 )) = ( 1 1) 1 ,
SF3 14 ( E ( NUM 31 , 4 ) E ( NUM 32 , 3 )) = ( 1 0 ) 0 ,
SF3 15 ( E ( NUM 31 , 5 ) E ( NUM 32 , 3 ))
=(1 0 ) 0
(20)
Stage 3formation of conditional detection expressions.
The conditional detection expressions that display the generated basic rules for identifying
the i -th cyber-attack (see (19) in [11]) can be represented in the following way:
DR i {
wi
a 1
DR ia } = {DR i1 , DRi 2 , …, DR iw i } =
vi
{ DR i1 { if SF then {
i1
IAiu }},
u 1
DRi 2 { if SF then {
i2
vi
IAiu }}, …,
u 1
DR iwi { if SFia then {
vi
IAiu }}} ,
u 1
( a 1,wi , u 1,vi )
http://www.iaeme.com/IJMET/index.asp
230
(21)
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
We should note that, formally, each SFia can be associated with the vi -th amount of
identifiers of the anomaly and, therefore, each basic rule can be generated by the vi amount of
detection expressions, i.e.:
DR i {DR i1 , DRi 2 , …, DR }
iw i
{ DR i1 { if SFi1 then IAi1 , if SFi1 then IAi 2 , ..., if SF then IA },
i1
iv
i
DRi 2 { if SFi 2 then IAi1 , if SFi 2 then IAi 2 , ..., if SF then IA }, …,
i2
ivi
DR iwi {if SFiwi then IAi1 , if SFiwi then IAi 2 , ..., if SFiwi then IAivi }} or
DR i {
wi
vi
{
a 1
if SFia then IAiu }} ,
u 1
( a 1,wi , u 1,vi )
(22)
Obviously, the possible amount of conditional detection expressions for identifying of the
i -th cyber-attack is determined by the formula
CDRi wi vi ,
(23)
and their amount to identifying of n attacks is calculated by the expression CDR
n
CDR
i 1
i
It should be noted that from the total amount of possible detection expressions, not all are
decisive (i.e., they affect the intrusion detection process) for identifying the i -th cyber-attack,
which also follows from Fig. 1 and (20) (here the decisive will be DR 3 11 – DR 3 15 ).
Regarding this, we consider an example of the implementation of the stage 3 at i 3 (
CA3 CASР SР ), j 1,2 ( P31 PSPКОП КОП , P32 PSPКПОА КПОА ), u3 5 , w3 15 .
Then the total amount of rules is determined by the formula (23), i.e.
CDR3 w3 v3 15 5 75 ,
And the expression (22) will be represented in the following way:
DR 3 { ... ,
DR 3 11 {if SF3 11 then IA31 , if SF3 11 then IA32 , if SF3 11 then IA33 ,
if SF3 11 then IA34 , if SF3 11 then IA35 },
DR 3 12 { if SF3 12 then IA31 , if SF3 12 then IA32 , if SF3 12 then IA33 ,
if SF3 12 then IA34 , if SF3 12 then IA35 },
DR 3 13 {if SF3 13 then IA31 , if SF3 13 then IA32 , if SF3 13 then IA33 ,
if SF3 13 then IA34 , if SF3 13 then IA35 },
DR 3 14 {if SF3 14 then IA31 , if SF3 14 then IA32 , if SF3 14 then IA33 ,
if SF3 14 then IA34 , if SF3 14 then IA35 },
http://www.iaeme.com/IJMET/index.asp
231
editor@iaeme.com
Detection Environment Formation Method for Anomaly Detection Systems
DR 3 15 { if SF3 15 then IA31 , if SF3 15 then IA32 , if SF3 15 then IA33 ,
if SF3 15 then IA34 , if SF3 15 then IA35 }} . (24)
According to the initial data, specified in the example, as well as taking into account the
expression (20) and graphical visualization (see Fig. 1) it is clear that the decisive function is
a decisive function SF3 13 that is included in a subset of detection expressions DR 3 13 , i.e.:
DR 3 13 {if SF3 13 then IA31 , if SF3 13 then IA32 , if SF3 13 then IA33 ,
if SF3 13 then IA34 , if SF3 13 then IA35 }
{ if ( E ( NUM 31 , 1 ) E ( NUM 32 , 3 )) then IA31 ,
if ( E ( NUM 31 , 2 ) E ( NUM 32 , 3 )) then IA32 ,
if ( E ( NUM 31 , 3 ) E ( NUM 32 , 3 )) then IA33 ,
if ( E ( NUM 31 , 4 ) E ( NUM 32 , 3 )) then IA34 ,
if ( E ( NUM 31 , 5 ) E ( NUM 32 , 3 )) then IA35 } =
{ if ( E ( NUM SPКОП , 1 ) E ( NUM SPКПОА , 3 )) then "Н" ,
if ( E ( NUM SPКОП , 2 ) E ( NUM SPКПОА , 3 )) then "БНВ" ,
if ( E ( NUM SPКОП , 3 ) E ( NUM SPКПОА , 3 )) then "БВН" ,
if ( E ( NUM SPКОП , 4 ) E ( NUM SPКПОА , 3 )) then "В" ,
if ( E ( NUM SPКОП , 5 ) E ( NUM SPКПОА , 3 )) then "П"} .
After checking all the rules in DR 3 13 , we determine that the identification of the
anomalous state is carried out by means of a conditional expression
if ( E( NUM SPКОП ,3 ) E( NUM SPКПОА ,3 ))
then "БВН" = if ( 1 1 ) then "БВН" .
The Figure 1 graphically shows the current block (in the form of a shaded rectangular area
formed by P31 , P32 ) interpreting the anomaly in the 2 -dimensional parametric NSC-NPSA~
~
(КОП-КПОА)-sub-environment generated by the corresponding attacking SP-environment at
the moment of time f .
f
f
Here, even during visual comparing, it can be determined that the obtained current block
is more closer to the fuzzy two-dimensional support area with the identifier "БВН" (“MORE
HIGH THAN LOW”), and the used rule can literally be interpreted as: “If the current value of
the fuzzy parameter “Number of simultaneous connections to the server (КОП)” at the
moment of time f is more closer to the standard fuzzy number “Average (Среднее – С)”
and, at the same time, the current value of the fuzzy parameter “Number of packets with the
same address of the sender and recipient (КПОА)” at the moment of time f is more closer to
the standard fuzzy number “High (Большое – Б)”, then the level of the anomalous state that
can be generated by the spoofing will be “More High than Low (БВН)”.
Also, using the developed software for the formation of standards of parameters for cyberattack detection systems [30], using various initial data, there is created the current state area,
http://www.iaeme.com/IJMET/index.asp
232
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
which allows visually to assess the anomalous state in the system in order to make the
necessary decision. Here, the current block is generated, for example, in the form of a red
rectangular area formed by P31 and P32 , which interprets the anomaly in the 2 -dimensional
~
~
parametric NSC-NPSA--(КОП-КПОА)-sub-environment generated by the corresponding
attacking SP-environment at the moment of time f [11].
f
f
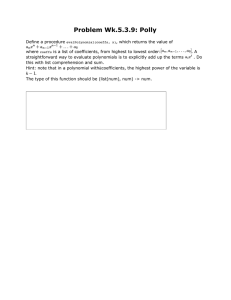
An example of the work of software for the formation of standards of parameters with
different input data is shown on Fig. 2.
This software allows to automate the process of formation of standards of parameters for
modern systems of anomaly detection and to display the results of the detection of an
anomalous state in a given period of time f .
Similarly, with different initial data there are identified other types of cyber-attacks,
generating certain anomalies in information systems.
Figure 2 Example of the work of software for the formation of standards of parameters
(Determination of the current state of the system)
5. CONCLUSIONS
Therefore, in the work there was proposed the DEFM, which on the basis of the basic tuple
model [11], using the mechanism of formation the subsets of anomaly identifiers, formalizing
the process of creation of decisive functions and conditional detection expressions, allows to
form the necessary set of detection rules used to determine the level of anomalous state which
is characteristic to a certain type of attacks. The use of this method at the creation anomaly
detection systems will expand their functionality regarding to the detection of cyber-attacks in
a weakly formalized fuzzy environment.
REFERENCES
http://www.iaeme.com/IJMET/index.asp
233
editor@iaeme.com
Detection Environment Formation Method for Anomaly Detection Systems
[1]
[2]
[3]
[4]
[5]
[6]
[7]
[8]
[9]
[10]
[11]
[12]
[13]
[14]
[15]
[16]
Mohammad Almseidin, Szilveszter Kovacs, «Intrusion detection mechanism using fuzzy
rule interpolation», Journal of Theoretical and Applied Information Technology, vol. 96,
no. 16, pp. 5473-5488, 2018.
Shanmugavadivu R., Nagarajan N. «Network Intrusion Detection System Using Fuzzy
Logic», Indian Journal of Computer Science and Engineering (IJCSE), Vol. 2, No. 1, pp.
101-111, 2011.
Linda O., Vollmer T., Wright J., Manic M. «Fuzzy Logic Based Anomaly Detection for
Embedded Network Security Cyber Sensor», in Proc. IEEE Symposium Series on
Computational Intelligence, Paris, France, April 2011, pp. 202-209.
Bridges S.M., Vaughn R.B. «Fuzzy data mining and genetic algorithms applied to
intrusion detection». In: Proceedings of the 23rd National Information Systems Security
Conference. October 2000, pp. 13-31.
Shahaboddin Shamshirband, Nor Badrul Anuar, Miss Laiha, Mat Kiah, Sanjay Misra
«Anomaly Detection using Fuzzy Q-learning Algorithm» Acta Polytechnica Hungarica.
Vol. 11, № 8, 2014, pp. 5-28.
John E. Dickerson, Jukka Juslin, Ourania Koukousoula, Julie A. Dickerson «Fuzzy
Intrusion Detection» IFSA World Congress and 20th NAFIPS International Conference,
2001. Joint 9th. Vol. 3, pp. 1506-1510.
Chi-Ho Tsang, Sam Kwong, Hanli Wang « Genetic-Fuzzy Rule Mining Approach and
Evaluation of Feature Selection Techniques for Anomaly Intrusion Detection » Pattern
Recognition, Vol. 40, №. 9, Sept. 2007, pp. 2373-2391.
Zadeh L.A. «Outline of a New Approach to the Analysis of Complex Systems and
Decision Processes» IEEE Transactions on Systems, Man, and Cybernetics, Vol. SMC-3,
№. 1, January 1973, рр. 28-44.
Gómez J., González F., Dasgupta D. «An Immuno-Fuzzy Approach to Anomaly
Detection» The 12th IEEE International Conference on Fuzzy Systems, FUZZ-IEEE 2528 May 2003, рр. 1219-1224.
Mohammed Ali Tawfiq «Security Measurements of Internet Website Zone for IE9 Based
on Fuzzy Logic» Journal of Engineering and Development. Vol. 17, № 1, Mar. 2013, pp.
255-269.
Korchenko A.А. The tupel model of basic components' set formation for cyberattacks,
Legal, regulatory and metrological support information security system in Ukraine, 2014,
V.2 (28), pp. 29-36. (in Russian)
Yao J.T., Zhao S.L., Saxton L.V. «A study on fuzzy intrusion detection» Proc. of SPIE
Data Mining, Intrusion Detection, Information Assurance, And Data Networks Security,
Orlando, Florida, USA, Vol. 5812, 2005, pp. 23-30.
Fries P. «A Fuzzy-Genetic Approach to Network Intrusion Detection Terrence» Genetic
and Evolutionary Computation Conference, GECCO (Companion) July 12-16, 2008, рр.
2141-2146.
Akhmetov, B., Kydyralina L, Lakhno V., Mohylnyi G., AkhmetovaJ., Tashimova A.,
model for a computer decision support system on mutual investment in the cybersecurity
of educational institutions //International Journal of Mechanical Engineering and
Technology (IJMET)//, Volume 9, Issue 10, October 2018, pp. 1114–1122,
A. Korchenko, K. Warwas, A. Kłos-Witkowska, «The Tupel Model of Basic Components'
Set Formation for Cyberattacks», in Intelligent Data Acquisition and Advanced
Computing Systems: Technology and Applications (IDAACS), 2015 IEEE 8th
International Conference on, 2015, pp. 478-483.
Korchenko A.А. The formation method of linguistic standards created for the intrusion
detection systems, Zahist ìnformacìï, vol. 16, №1, 2014, pp. 5-12. (in Russian)
http://www.iaeme.com/IJMET/index.asp
234
editor@iaeme.com
Nazym Zhumangaliyeva, Anna Korchenko, Aliya Doszhanova, Aigul Shaikhanova,
Shangytbayeva Gulmira, Serik Smagulov and shaikhametov Erzhan,
[17]
[18]
[19]
[20]
[21]
[22]
[23]
[24]
[25]
[26]
[27]
[28]
[29]
[30]
В. Akhemetov, А. Korchenko, S. Akhmetova, N. Zhumangalieva, «Improved method for
the formation of linguistic standards for of intrusion detection systems», Journal of
Theoretical and Applied Information Technology, vol. 87, no. 2, pp. 221-232, 2016.
Tereykovsky I., Korchenko A., Vikulov P., Shakhoval O., The etalons models of
linguistic variables for sniffing attacks detection, Zahist ìnformacìï, vol. 19, №3, 2017, pp.
228-242. (in Russian)
Mikolaj Karpinski, Poland, Anna Korchenko, Pavlo Vikulov, Ukraine, Roman Kochan.
The Etalon Models of Linguistic Variables for Sniffing-Attack Detection // Proceedings of
the 2017 IEEE 9th International Conference on «Intelligent Data Acquisition and
Advanced Computing Systems: Technology and Applications» (IDAACS’2017),
Romania, Bucharest, September 21-23, 2017: Vol. 1. – Pp. 258-264.
Tereykovsky I., Korchenko А., Vikulov Р., Ireifidzh I., Etalons models of linguistic
variables for email-spoofing-attack detection systems, Bezpeka ìnformacìï, vol. 24 №2,
pp. 21-28, 2018. (in Russian)
Korchenko А. Method of parameter fuzzification based on linguistic standards for cyberattacks detection, Bezpeka ìnformacìï, 2014, vol. 20, issue 1, pp. 21-28. (in Russian)
Korchenko А., The method of -level of nominalization for intrusion detection systems,
Zahist ìnformacìï, vol. 16, №4, 2014, pp. 292-304. (in Russian)
Korchenko А.О. The detection method of identification terms for intrusion detection
system, Bezpeka ìnformacìï, 2014, Vol.20, №3, pp. 217-223. (in Russian)
Tereykovsky I., Korchenko А., «Cyber-attack detection system», Bezpeka ìnformacìï,
2017, Vol.23, №3, pp. 176-180. (in Russian)
Deep neural networks in cyber-attack detection systems / Bapiyev, I.M., Aitchanov, B.H.,
Tereikovskyi, I.A., Tereikovska, L.A., Korchenko, A.A. // International Journal of Civil
Engineering and Technology Vol. 8, Issue 11, November 2017, PP. 1086-1092.
Lakhno, V., Akhmetov, B., Korchenko, A., Alimseitova, Z., Grebenuk, V., Development
of a decision support system based on expert evaluation for the situation center of
transport cybersecurity, Journal of Theoretical and Applied Information Technology,
2018, 96(14), с. 4530-4540.
Intelligent systems for monitoring and recognition of cyber-attacks on information and
communication systems of transport / Al Hadidi M., Ibrahim Y.K., Lakhno V., Korchenko
A., Tereshchuk A., Pereverzev A., International Review on Computers and Software Vol.
11, Issue 12, 2016, P P 1167-1177.
Korchenko A., Shcherbyna V., Vyshnevska N., A methodology for building cyberattackgenerated anomaly detection systems, Zahist ìnformacìï, vol.18, №1, 2016, pp. 30-38.
Korchenko A.G. The development of information protection systems based on the fuzzy
sets, The theory and practical solutions, Kuev, 2006, 320 р. (in Russian)
Korchenko A, Zaritskyi O., Taras P., Bychkov V., The software for the formation of
parameters etalons for cyber-attacks detection systems, Zahist ìnformacìï, vol.20, №3,
2018, pp. 133-148. (in Russian)
http://www.iaeme.com/IJMET/index.asp
235
editor@iaeme.com
 0
0
advertisement
Download
advertisement
Add this document to collection(s)
You can add this document to your study collection(s)
Sign in Available only to authorized usersAdd this document to saved
You can add this document to your saved list
Sign in Available only to authorized users