!
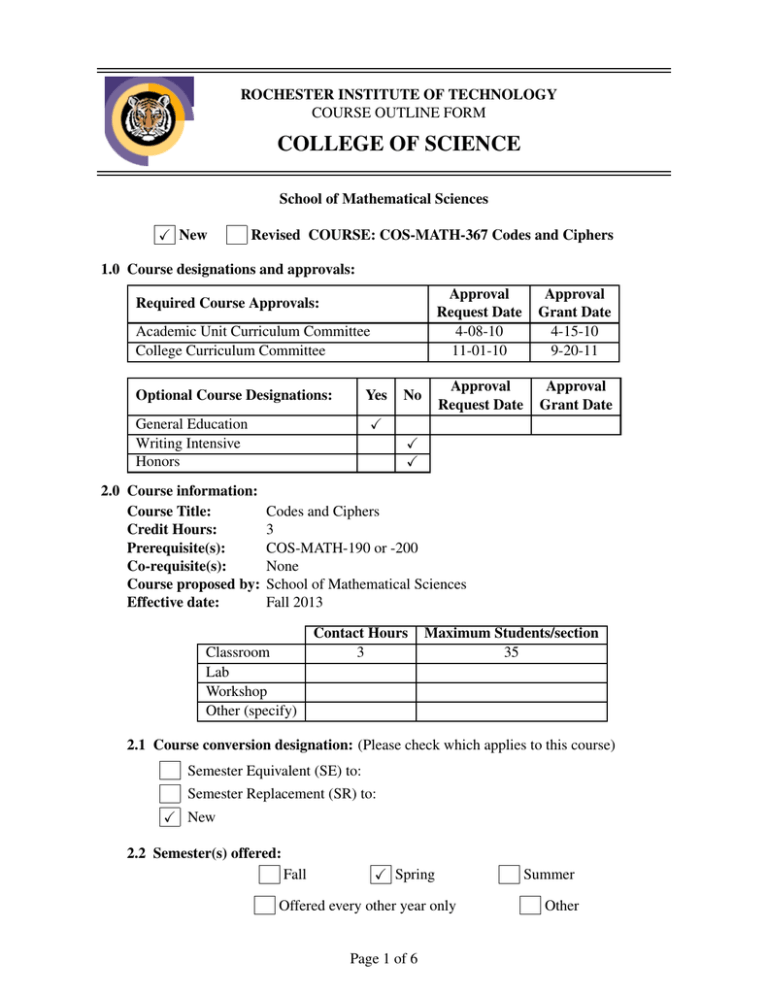
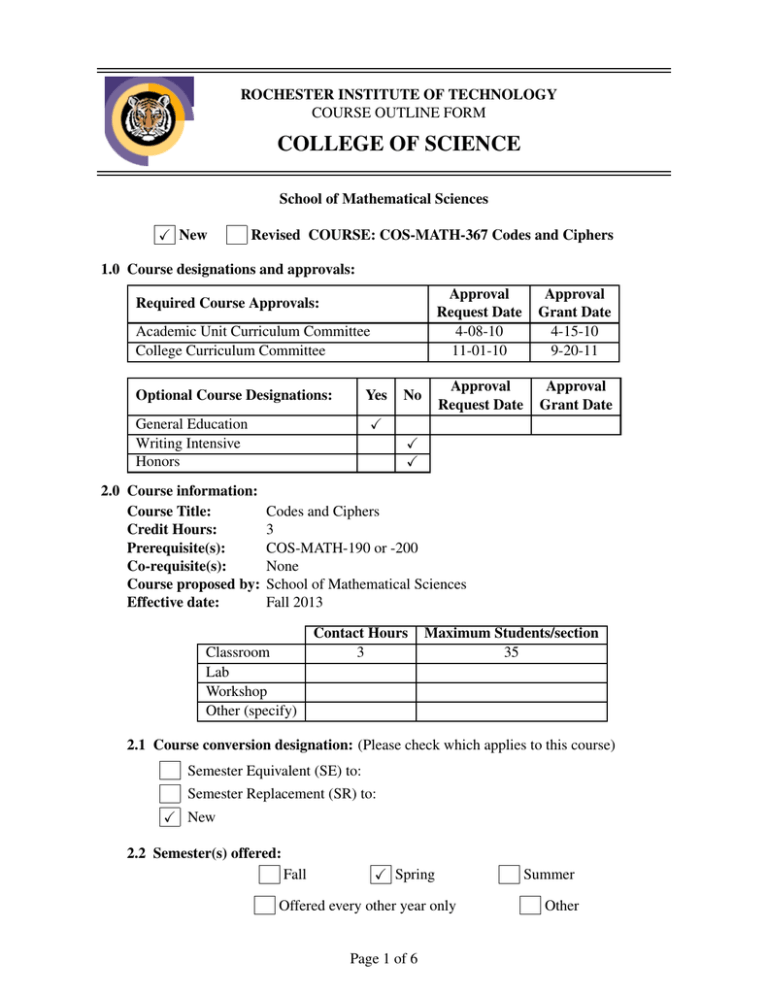
ROCHESTER INSTITUTE OF TECHNOLOGY
COURSE OUTLINE FORM
COLLEGE OF SCIENCE
School of Mathematical Sciences
X New
Revised COURSE: COS-MATH-367 Codes and Ciphers
1.0 Course designations and approvals:
Required Course Approvals:
Academic Unit Curriculum Committee
College Curriculum Committee
Optional Course Designations:
Yes
Approval
Grant Date
4-15-10
9-20-11
Approval
Request Date
Approval
Grant Date
X
General Education
Writing Intensive
Honors
2.0 Course information:
Course Title:
Credit Hours:
Prerequisite(s):
Co-requisite(s):
Course proposed by:
Effective date:
No
Approval
Request Date
4-08-10
11-01-10
X
X
Codes and Ciphers
3
COS-MATH-190 or -200
None
School of Mathematical Sciences
Fall 2013
Classroom
Lab
Workshop
Other (specify)
Contact Hours
3
Maximum Students/section
35
2.1 Course conversion designation: (Please check which applies to this course)
Semester Equivalent (SE) to:
Semester Replacement (SR) to:
X New
2.2 Semester(s) offered:
Fall
X Spring
Offered every other year only
Page 1 of 6
Summer
Other
2.3 Student requirements:
Students required to take this course: (by program and year, as appropriate)
None
Students who might elect to take the course:
Students majoring in Applied Mathematics, Computational Mathematics, or Applied
Statistics, Mathematics minors, and students seeking to strengthen their technical
background in mathematics
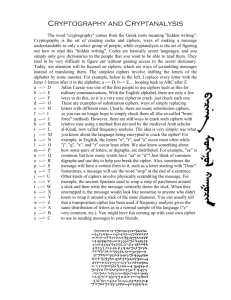
3.0 Goals of the course: (including rationale for the course, when appropriate)
3.1 To become familiar with enciphering.
3.2 To encode and decode using classical enciphering and deciphering techniques.
3.3 To learn and practice the use of current enciphering techniques.
3.4 To learn the basic principles of cryptograhy and how it is used in modern computer and
communication systems.
4.0 Course description: (as it will appear in the RIT Catalog, including pre- and co-requisites,
semesters offered)
COS-MATH-367
Codes and Ciphers
This course will introduce, explain and employ the basic techniques of cryptography, both
classical and modern. Topics will include the Vignère cipher, affine ciphers, Hill ciphers,
one-time pad encryption, Enigma, cryptosystems such as DES (Data Encryption Standard)
and AES (Advanced Encryption Standard), public key encryption schemes (RSA), and hash
functions. The course will include an introduction to number theoretic tools used in cryptography. (COS-MATH-190 or -200) Class 3, Credit 3 (S)
5.0 Possible resources: (texts, references, computer packages, etc.)
5.1 W. Trappe and L. Washington, Introduction to Cryptography with Coding Theory,
Pearson-Prentice Hall, Upper Saddle River, NJ.
5.2 J. Buchmann, Introduction to Cryptography, Springer, New York, NY.
5.3 P. Garrett, Making, Breaking Codes, Prentice Hall, Upper Saddle River, NJ.
5.4 R. Lewand, Cryptological Mathematics, MAA, Washington, DC.
5.5 T. Barr, Invitation to Cryptology, Prentice Hall, Upper Saddle RIver, NJ.
5.6 A. Young, Mathematical Ciphers: From Caesar to RSA, AMS, Providence, RI.
5.7 D. Kahn, The Codebreakers: The Comprehensive History of Secret Communication
from Ancient Times to the Internet, Scribner, New York, NY.
5.8 Fiction: Stephenson, Cryptonmicon, Avon, New York, NY.
5.9 Movies: Tora, Tora, Tora; U 571; Windtalkers; Firewall.
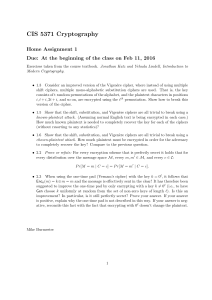
6.0 Topics: (outline) Topics with an asterisk(*) are at the instructor’s discretion, as time permits
6.1 Simple Ciphers
6.1.1 The shift cipher
Page 2 of 6
6.1.2
6.1.3
6.1.4
6.1.5
6.1.6
One-time pad
Symmetric and asymmetric cryptosystems
Affine ciphers and their cryptanalysis
Permutations
Substitution ciphers
6.2 Serious Ciphers
6.2.1
6.2.2
6.2.3
6.2.4
6.2.5
6.2.6
6.2.7
6.2.8
Introduction to matrices
The Vignére cipher
Kasiski and Friedman tests
Cryptanalysis of Vignére cipher
Block ciphers
Hill ciphers
Attacks on Hill ciphers
Stream ciphers and linear feedback shift registers
6.3 Basic Number Theory
6.3.1
6.3.2
6.3.3
6.3.4
6.3.5
6.3.6
6.3.7
Divisibility
Solving linear diophantine equations
Introduction to modular arithmetic and congruences
Euler totient function and its properties
Modular exponentiation
Fermat’s and Euler’s theorems (without proofs)
Square roots modn
6.4 Data Encryption Standard (DES)
6.4.1
6.4.2
6.4.3
6.4.4
Feistel ciphers
DES algorithm
Security of DES Algorithm
Advanced Encryption Standard (AES)
6.5 Public Key Cryptography (PKC)
6.5.1
6.5.2
6.5.3
6.5.4
6.5.5
6.5.6
6.5.7
6.5.8
Idea of PKC and trapdoors
RSA cryptosystem
Attacks on RSA
Miller-Rabin cryptosystem
Idea of discrete log problem
Diffie-Hellman key exchange
El-Gamal cryptosystem
Merkle-Hellman knapsack cipher
6.6 Cryptographic Hash Functions
6.6.1 Hash functions and compression functions
6.6.2 Hash functions from compression functions
Page 3 of 6
6.6.3 Birthday attack
6.6.4 Efficient hash functions
6.6.5 Message authentication codes
6.7 Games and Secret Sharing
6.7.1 Flipping coins over the telephone
6.7.2 Poker over the telephone
6.7.3 Shamir’s and other threshold schemes
7.0 Intended learning outcomes and associated assessment methods of those outcomes:
7.1 Recognize computationally hard mathematical problems
7.2 Describe the fundamentals of cryptographic protocol design
7.3 Evaluate the correctness of cryptosystems
7.4 Compare and contrast the security of various cryptosystems
7.5 Encode and decode messages using historically interesting
techniques
7.6 Identify the different approaches to quantifying secrecy
X
X
Class Presentation
X
X
X
X
X
Computer Work
X
X
X
X
X
Project
Quiz/Exam/Final
Learning Outcomes
Homework
Assessment Methods
8.0 Program goals supported by this course:
8.1 To develop an understanding of the mathematical framework that supports engineering,
science, and mathematics.
8.2 To develop critical and analytical thinking.
8.3 To develop an appropriate level of mathematical literacy and competency.
8.4 To provide an acquaintance with mathematical notation used to express physical and
natural laws.
Page 4 of 6
9.0 General education learning outcomes and/or goals supported by this course:
9.1
9.2
9.3
9.4
X
X
Page 5 of 6
Class Presentation
Computer Work
General Education Learning Outcomes
Communication
Express themselves effectively in common college-level
written forms using standard American English
Revise and improve written and visual content
Express themselves effectively in presentations, either in
spoken standard American English or sign language (American Sign Language or English-based Signing)
Comprehend information accessed through reading and discussion
Intellectual Inquiry
Review, assess, and draw conclusions about hypotheses and
theories
Analyze arguments, in relation to their premises, assumptions, contexts, and conclusions
Construct logical and reasonable arguments that include anticipation of counterarguments
Use relevant evidence gathered through accepted scholarly
methods and properly acknowledge sources of information
Ethical, Social and Global Awareness
Analyze similarities and differences in human experiences
and consequent perspectives
Examine connections among the world’s populations
Identify contemporary ethical questions and relevant stakeholder positions
Scientific, Mathematical and Technological Literacy
Explain basic principles and concepts of one of the natural
sciences
Apply methods of scientific inquiry and problem solving to
contemporary issues
Comprehend and evaluate mathematical and statistical in- X X
formation
Perform college-level mathematical operations on quantita- X X
tive data
Describe the potential and the limitations of technology
Use appropriate technology to achieve desired outcomes
Project
Quiz/Exam/Final
Homework
Assessment Methods
X
9.5
Class Presentation
Computer Work
Project
General Education Learning Outcomes
Creativity, Innovation and Artistic Literacy
Demonstrate creative/innovative approaches to coursebased assignments or projects
Interpret and evaluate artistic expression considering the
cultural context in which it was created
Quiz/Exam/Final
Homework
Assessment Methods
10.0 Other relevant information: (such as special classroom, studio, or lab needs, special
scheduling, media requirements, etc.)
None
Page 6 of 6