Finding a Hamiltonian Path in a Cube with Specified Turns is Hard
advertisement

Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
[DOI: 10.2197/ipsjjip.0.1]
Regular Paper
Finding a Hamiltonian Path in a Cube
with Specified Turns is Hard
Zachary Abel1,a) Erik D. Demaine2,b) Martin L. Demaine2,c)
Sarah Eisenstat2,d) Jayson Lynch2,e) Tao B. Schardl2,f)
Received: xx xx, xxxx, Accepted: xx xx, xxxx
Abstract: We prove the NP-completeness of finding a Hamiltonian path in an N × N × N cube graph with
turns exactly at specified lengths along the path. This result establishes NP-completeness of Snake Cube
puzzles: folding a chain of N 3 unit cubes, joined at face centers (usually by a cord passing through all the
cubes), into an N × N × N cube. Along the way, we prove a universality result that zig-zag chains (which
must turn every unit) can fold into any polycube after 4 × 4 × 4 refinement, or into any Hamiltonian polycube
after 2 × 2 × 2 refinement.
Keywords: Hamiltonian path, NP-Completeness, puzzle, Snake Cube puzzle
1.
Introduction
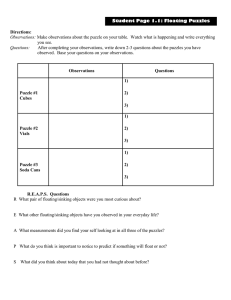
Snake Cube puzzles [6–8] are physical puzzles consisting
of a chain of unit cubes, typically made out of wood or plastic, with holes drilled through to route an elastic cord. The
cord holds the cubes together, at shared face centers where
the cord exits/enters the cubes, but permits the cubes to
rotate relative to each other at those shared face centers.
Fig. 1 shows photographs of a wooden Snake Cube from its
initial to solved state. As in most physically existing Snake
Cube puzzles, it consists of 27 cubes and the goal is to make
a 3 × 3 × 3 cube.
The origin of Snake Cube puzzles seems to be unknown;
the simplicity of the idea may have led to many copies and
variations. Singmaster’s puzzle collection [9] lists his earliest
purchase of such a puzzle as 1990 in Paris. Jaap’s Puzzle
Page [8] lists two tradenames for different versions of the
puzzle: Kev’s Kubes (wooden, made by Trench Puzzles),
and Cubra Finger Twisting Puzzler (plastic, made by Parker
Hilton Ltd circa 1998 [5], later acquired by Falcon Games)
which has five color-coded variations—Mean Green, Bafflin’
Blue, Twist yer ’ead Red, ’Orrible Orange, and Puzzlin’ Purple. Fig. 2 shows a packaged Cubra Puzzlin’ Purple. The
two Snake Cube puzzles we own (including Fig. 1) happen
to match the geometry of the Cubra Bafflin’ Blue puzzle.
1
2
a)
b)
c)
d)
e)
f)
MIT Department of Mathematics, 77 Massachusetts Ave.,
Cambridge, MA 02139, USA
MIT Computer Science and Artificial Intelligence Laboratory,
32 Vassar St., Cambridge, MA 02139, USA
zabel@math.mit.edu
edemaine@mit.edu
mdemaine@mit.edu
seisenst@mit.edu
jaysonl@mit.edu
neboat@mit.edu
c 1992 Information Processing Society of Japan
→
→
A commercially available Snake Cube puzzle consisting of
27 cubes in the pattern SSTSTSTSTTTTSTSTTTSTTSTTTSS.
Fig. 1
Fig.
2
The commercially available Cubra Puzzlin’ Purple puzzle consisting of 27 cubes in the pattern
STTTTSTSTTTTTTTTTTTSTSTTTTS. Photo from the Slocum
Collection [5] courtesy of The Lilly Library, Indiana University, Bloomington, Indiana.
1
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
Larger 4 × 4 × 4 puzzles are sold under the name “King
Snake” [1]. A custom 5×5×5 puzzle was built at the Smith
College Mathematics Department [6].
1.1 Our results
In this paper, we study the natural generalization of Snake
Cube puzzles to a chain of N 3 cubes whose goal is to fold
into an N × N × N cube. The puzzle can be specified by a
sequence of N 3 binary symbols (S or T), each representing
a cube whose cord either passes straight through the cube
and thus prevents the chain from turning (S), or turns 90◦
at the cube and thus forces the chain to turn (T).
We prove that it is NP-complete to decide whether such a
puzzle has a folded state in the shape of an N ×N ×N cube.
Our NP-hardness reduction is from the classic 3-Partition
problem, whose goal is to divide 3n integers, v1 , . . . , v3n ,
into n triples of equal sum. We represent each integer vi as
a sequence of cubes that must effectively fold into a narrow
“peg” of width proportional to vi . In sections 4 and 5, we
build an infrastructure for these pegs to fit into, consisting
of n “slots” whose widths are proportional (with the same
constant as pegs) to the target sum of each triple. Finally,
in section 8, we connect the infrastructure and pegs together
with “filler” that lets the pegs move freely relative to each
other and the infrastructure.
To develop “filler” gadgets for our hardness proof, we also
prove universality results about zig-zag puzzles, which consist solely of turning cubes (T). Specifically, in section 6, we
show that the zig-zag puzzle of (4N )3 unit cubes can fold
into the shape of any N -cube polycube after 4 × 4 × 4 refinement. Furthermore, in the special case of Hamiltonian
polycubes (whose dual graph has a Hamiltonian path), we
show how to reduce the required refinement to just 2×2×2.
1.2 Related work
A few research papers have already been motivated by
Snake Cube puzzles. Scherphuis [8] wrote a computer program to exhaustively enumerate all 11,487 possible 3 × 3 × 3
Snake Cube puzzles, and found that 3,658 have unique solutions. (For example, the puzzle in Fig. 1 has a unique solution, but the puzzle in Fig. 2 has six solutions.) Ruskey and
Sawada [7] characterized when an M N K-cube zig-zag puzzle can fill an M × N × K box, and generalized this result
to d dimensions and toroidal space. McDonough [6] analyzed cube Hamiltonian paths that form nontrivial knots,
and multiple spanning paths that form nontrivial links.
2.
Definitions
For convenience, we work on the standard, Cartesian
coordinate system, identifying the positive x-, y-, and zdirections with right, forward, and up, respectively. We divide space into unit cubes, which we call cells, according
to the integer lattice, Z3 . Each cell is identified by its left,
back, bottom corner; in other words, the cell at (x, y, z)
has opposite corners (x, y, z) and (x + 1, y + 1, z + 1). A cell
has six faces, and we identify co-located faces on adjacent
c 1992 Information Processing Society of Japan
Fig. 3
A depiction of the puzzle STS3 TS2 T2 . In terms of real
Snake Cube puzzles, the blue and purple pipe illustrates
the cord inside the cubes to distinguish straight cubes
from turn cubes.
cells. For example, we identify the right face of cell (x, y, z)
with the left face of cell (x + 1, y, z).
An (abstract) puzzle of cubes is a sequence of Ss and Ts,
representing straight cells and turn cells, respectively. A
configuration of a length-n abstract puzzle is a sequence
of distinct cells c1 , . . . , cn and faces f0 , . . . , fn , such that
• for each 1 ≤ i ≤ n, fi−1 and fi are distinct faces of cell
ci , and
• if the ith symbol in the puzzle is an S then fi−1 and fi
are opposite faces on cell ci ; if this symbol is a T, faces
fi−1 and fi are adjacent.
In other words, such a configuration is a path of cells whose
straight and turn cells correspond to the specification of the
abstract puzzle. Faces f0 and fn are called the starting
face and ending face of the configuration, respectively.
A puzzle may be notated simply as a sequence of symbols
S and T and superscripts to indicate symbol repetition. For
example, Fig. 3 shows the puzzle STS3 TS2 T2 . We introduce
a run-length encoding shorthand as follows: For positive
integers d1 , . . . , dr , we define
hd1 , . . . , dr i = Sd1 −1 TSd2 −2 T · · · TSdr−1 −2 TSdr −1
if r > 1 and hd1 i = Sd1 ; the integers di describe the lengths
of the bars, or maximal subsets of collinear cubes. For example, the puzzle in Fig. 3 is abbreviated as h2, 5, 4, 2, 1i.
Note that 1s may appear in this notation only at the start
or end of the sequence, and, unless r = 1, they indicate that
the first or last symbol of the puzzle is a T. Two notable
examples are h1i = S and h1, 1i = T.
For two puzzles C1 and C2 of n and m cubes respectively,
we define their concatenation C1 ◦ C2 as the puzzle of
n + m cubes obtained by concatenating the underlying S-T
sequences of C1 and C2 . In run-length encoding notation,
hd1 , . . . , dr i◦he1 , . . . , es i = hd1 , . . . , dr−1 , dr +e1 , e2 , . . . , es i.
2
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
8t
8t
8t
8t
z
(0, 0, 0)
y
ℓ
x
hℓ
8
hw
Fig. 4
(hw , −hℓ , 8)
A depiction of the different parts of the hub-and-slots
shape. Not drawn to scale.
For example, if C1 = h1, 3, 4, 1i = TSTS2 T and C2 = h5, 6i =
S4 TS5 , then C1 ◦C2 = TSTS2 TS4 TS5 = h1, 3, 4, 6, 6i. A notation for iterated concatenation is also useful: For a puzzle
C, the notation C k means C ◦C ◦· · · ◦C, with k total copies
of C.
Finally, we reduce from the 3-Partition problem, defined
as follows. An instance of this problem is a (multi)set V =
P
{v1 , . . . , v3n } of positive integers such that n1 3n
i=1 vi = t
is an integer. We require additionally that t/4 < vi < t/2
for each i. A 3-partition of V is a partition of V into
n groups each with sum equal to the target sum, t; each
group necessarily has three elements. The instance V is a
YES instance if and only if it has a 3-partition. The 3Partition problem was shown to be strongly NP-hard by
Garey and Johnson [4].
3.
Overview
We first provide an informal description of the reduction
that also serves as an outline for the remainder of the paper.
From a 3-Partition instance V = {v1 , . . . , v3n } with
target sum t, we will construct a puzzle R = R(V ) that exactly fills a u × u × u cube (where u = poly(n, t), specified
later) if and only if there exists a 3-partition for V .
The key idea for our reduction is as follows. Imagine a
large box—the “hub”—with n separate, long and skinny
“slots” sticking out of it, each with width 8t, length ℓ, and
height 1. Fig. 4 illustrates this “hub-and-slots” shape. Now
suppose that we have 3n separate puzzles, or “pegs”: for
each 1 ≤ i ≤ 3n, form the puzzle Pi = hℓ, 2, ℓ, 2, . . . , ℓi,
where there are 8vi bars of length ℓ. If ℓ is long enough,
then for any peg Pi to fit into the hub-and-slots, it must
in fact zig-zag along one of the slots, occupying 8vi of its
width (possibly partially poking into the hub). It follows
that all pegs P1 , . . . , P3n can fit without overlap into the
hub-and-slots if and only if V has a 3-partition.
Our reduction exactly sets up this situation. Specifically,
from the 3-Partition instance V , our reduction constructs
the puzzle
R = R(V ) = R1 ◦ R2 ◦ R3 ◦ R4 ,
(1)
where each Ri solves a specific, isolated task.
The first two portions, R1 and R2 , “carve out” the huband-slots shape from the u × u × u cube. In other words, no
c 1992 Information Processing Society of Japan
8t
matter how R1 ◦ R2 is positioned inside the u × u × u cube,
it must fill everything except the exact hub-and-slots shape
needed. More specifically, puzzle R1 (Section 4) carves out
an a×b×c box (with carefully chosen dimensions a < b < c)
from the u × u × u cube, and then R2 (Section 5) carves out
the hub-and-slots shape from this box.
Puzzle R3 (Section 7) includes the pegs P1 , . . . , P3n described above, so R1 ◦ R2 ◦ R3 can fit into the u × u × u cube
only when there exists a 3-partition. Inside puzzle R3 , the
pegs Pi are separated by zig-zagging “filler material” (analyzed in Section 6) that is sufficiently flexible to allow each
peg to be independently placed in the slots. This ensures
that, when a 3-partition of V exists, puzzle R3 can indeed
fit into the hub-and-slots.
Finally, more zig-zagging filler material comprises puzzle
R4 (Section 8). Its purpose is to fill all space inside the
hub that was not filled by R3 . This ensures that, when a
3-partition exists, the puzzle R1 ◦ R2 ◦ R3 ◦ R4 can fill all
cells in the u × u × u cube without gaps.
4.
Cube to Box
We first formalize the notion of “carving out,” or excising
a region from a larger region as described in the Overview
(Section 3). This allows us to analyze different sections of
R separately, for example, arguing that R1 excises a box
from the u × u × u cube and therefore the R2 portion of
R1 ◦ R2 must operate entirely inside this box. Since we wish
to analyze R1 and R2 separately, some care must be taken
to ensure that their endpoints join properly.
Definition 1. A region is a face-connected collection of
cells in the unit grid. A nontrivial mark on a region S is
a pair (c, f ), where c is a cell in S and f is a face of c. A
puzzle configuration in S starts/ends at mark (c, f ) if
its first/last cell-and-face pair is (c, f ). For convenience,
we also introduce a trivial mark, notated by (∅, ∅), and
we declare that any puzzle configuration in S vacuously
starts/ends at the trivial mark. A marked region is a
region with a mark, which may be trivial or nontrivial.
The trivial mark is simply a notational convenience: it
allows uniform treatment of regions with a chosen start or
end location (nontrivially marked regions) and regions with
no preferred start or end (trivially marked regions). Also,
though it is not required, face f of a nontrival mark will
usually be a boundary face of S. Such marks may be specified from face f alone, because cell c ∈ S is then uniquely
determined.
Suppose we have two marked regions S and S ′ , with marks
(c, f ) and (c′ , f ′ ) 6= (∅, ∅) respectively, where f ′ is on the
boundary of S ′ . We would like to say that a puzzle C “excises” S ′ from S if every configuration of C inside S starting
at (c, f ) must fill all of S except for a region congruent to S ′
and must end at face f ′ of this copy of S ′ . This is not quite
the condition we need: for example, if puzzle C ends with
a T cube, then even if the configuration leaves an S ′ -shaped
hole, the last cube may be turned away from S ′ . We disallow this by requiring that the configuration be “extensible”
3
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
inside S, in such a way that this extension must enter cell
c′ via face f ′ .
Definition 2. Let S and S ′ be two (trivially or nontrivially) marked regions with marks (c, f ) and (c′ , f ′ ) respectively, where f ′ is on the boundary of S ′ if (c′ , f ′ ) 6= (∅, ∅).
A puzzle C excises S ′ from S if, for every configuration
of C inside S starting at (c, f ) and ending at some celland-face pair (c′′ , f ′′ ) in S, if the cell adjacent to f ′′ other
than c′′ is in S and not filled by the configuration, then
the unfilled portion of S must be congruent to S ′ in such
a way that, if (c′ , f ′ ) 6= (∅, ∅), then f ′′ = f ′ . Furthermore,
at least one such configuration of C must exist.
At least in the case where S ′ is nontrivially marked, the
following fact (which follows directly from the previous definition) shows that such an excision allows perfect separation
of matters inside S ′ from those outside it:
Theorem 3. If C excises marked region S ′ with nontrivial mark (c′ , f ′ ) from marked region S (with mark (c, f )),
and if C ′ is any other nonempty puzzle, then C ◦ C ′ can be
configured inside S starting at (c, f ) if and only if C ′ can
be configured inside S ′ starting at (c′ , f ′ ).
With these definitions in place, the following two lemmas
show how to excise an arbitrary box from an appropriately
chosen cube. These lemmas use puzzles called tribars, each
of which consists of three consecutive bars of length greater
than 2. A horseshoe configuration of a tribar is one
where the three bars lie in a plane and the two parallel bars
point in opposite directions, thus forming a “horseshoe” or
“U” shape.
Lemma 4. Given integers a < b < c, let B be an a × b × c
box, marked at a unit square in the corner of an a × c face
of the box. Let B ′ be an a × b′ × (c − 1) box satisfying
a < b′ < (c − 1) and 2(b′ + 2) > b, marked at a unit square
in the corner of an a × (c − 1) face of the box. Then there
exists a puzzle C excising B ′ from B.
Proof: We construct C by concatenating a “filler” puzzle
to a sequence of tribar puzzles. The filler puzzle is a puzzle
hc, 2, c, 2, . . . , c, 1i. The relevant tribar puzzle in this proof
has shape h1, c, b′ +2, c, 1i. Let us first consider the behavior
of the filler puzzle in B and then examine the behavior of
the tribar puzzles.
A filler puzzle must lie inside B with its length-c bars
along the long axis of B. The filler puzzle can fill a box of
size a × (b − b′ − 2) × c with a(b − b′ − 2) length-c bars
if the long bars are laid next to each other in a × c × 1size layers. The filler puzzle alone does not, however, excise
an a × (b′ + 2) × c box from B, because the puzzle may
adopt other configurations in B. Hence, we use the additional structure imposed by the tribar puzzles to excise B ′
from B.
A tribar h1, c, b′ +2, c, 1i must lie inside B with its length-c
bars along the long axis of B. Because b′ +2 > a, the length(b′ + 2) bar must lie along either the length-c or length-b
axis of B, and because it lies in a different direction from
the length-c bars, it must lie along the length-b axis of B.
This tribar must then be in a horseshoe configuration.
c 1992 Information Processing Society of Japan
In a sequence of tribars as above, the subsequent horseshoe configurations must lie on top of each other, since two
horseshoe configurations cannot lie side-by-side in B because
2(b′ + 2) > b. Thus, from box B, a sequence of a tribars
cuts out two or three rectangular regions. One region (inside the horseshoes) has dimensions a × b′ × (c − 1), and the
final cube in the sequence of tribars must be a turn cube
in the corner of an a × (c − 1) face of this region. The
remaining two regions, meanwhile, must have total volume
a × (b − b′ − 2) × c.
Prepending a filler puzzle with a(b − b′ − 2) length-c bars
to a sequence of a tribars as above produces a puzzle where,
inside box B, the filler puzzle must fill an a × (b − b′ − 2) × c
box. Hence, the puzzle C consisting of a filler puzzle of
a × (b − b′ − 2) length-c bars concatenated to a sequence of
a tribar puzzles excises box B ′ from B.
Lemma 5. Given integers a < b < c with c − b ≥ 2, let B
be an a × b × c box marked at a unit square in the corner
of an a × c face of the box. Then there exist u < 4c and
a puzzle C that excises B from an unmarked u × u × u
cube U .
Proof: Our first step is to excise a (u − 1) × (u − 3) × a
box from U . To excise this shape, we first use a sequence
of tribars H = h1, u, u, u, 1i. Consider the possible ways to
arrange the puzzle H 2 = H ◦ H = h1, u, u, u, 2, u, u, u, 1i inside the cube. Without loss of generality, the first two edges
of H 2 must lie in a plane P parallel to the bottom face of
the box, with the first bar pointing forward and the second
pointing right.
For the sake of contradiction, suppose that the third bar
of H 2 lies perpendicular to P . This implies that the end of
the third bar is in either the right, forward, upper corner or
the right, forward, lower corner of U , and hence, no matter which direction the subsequent length-2 bar points, the
other end of the length-2 bar cannot be in a corner. The
second H must therefore lie in a plane perpendicular to P ,
and all four such configurations intersect one of the bars already placed in U . Hence the first three bars of H 2 must all
lie in P , forming a horseshoe configuration where the end of
the third bar lies along the front right edge of the cube.
Now consider how the remainder of H 2 can be arranged.
If the length-2 bar points left, then both of the possible arrangements of the subsequent H intersect one of the bars
that has already been placed. The length-2 bar must therefore point up or down, and without loss of generality, let
this bar point up. In this case the subsequent H forms a
horseshoe that lies on top of the first horseshoe in either the
same arrangement or a similar arrangement rotated by 90◦ .
Suppose now that we extend puzzle H 2 to H u . By a similar argument, H u must adopt an arrangement in the cube
in which each H forms a horseshoe, and the set of Hs together form a stack of u horseshoes in the cube, possibly
with different rotations. We say that a stack of horseshoes
is orderly if all horseshoes have the same rotation.
To complete this first excision and guarantee that the
4
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
stack of horseshoes formed from packing H u into U are orderly, we concatenate onto H u a “filler” puzzle followed by
a sequence of tribar puzzles I = h1, u, u − 1, u, 1i. Consider
concatenating the filler puzzle F = h1, u, 1i(u−1)(u−2−a)
followed by the sequence I a to H u . Notice that the puzzle
H u ◦ h1, u, 1i must be packed into U with the final lengthu bar perpendicular to the length-u bars in H u , and thus
concatenating h1, u, 1i to H u forces the horseshoes formed
from packing H u to be orderly. Hence, let us assume that
the horseshoes in H u are orderly and focus on the behavior
of F ◦ I a inside a u × (u − 1) × (u − 2) box X marked at
a corner of a u × (u − 1) face. This analysis is very similar
(though not identical) to that in the proof of Lemma 4.
First, consider packing I a into the volume of X. To pack
a
I inside X, each length-u bar in I a must lie parallel to
the length-u edge of X. Because the length-(u − 1) bars in
I a cannot also lie parallel to the length-u edges of X, each
such bar must lie in the direction with extent (u − 1). Consequently, each tribar I in X must be packed in a horseshoe
configuration, and the resulting stack of horseshoes must be
orderly.
Now, consider packing F ◦ I a into X. To pack F into
X, each length-u bar of F must lie in the direction with
extent u. Furthermore, in order to pack I a into X afterwords, F must be packed to fill a (u − 2 − a) × (u − 1) × u
volume that shares a (u − 1) × u face with X. Finally, the
last cube in the puzzle I a must lie adjacent to a corner of an
a × (u − 1) face of the remaining volume. Let X0 denote the
a × (u − 3) × (u − 1) empty space left after packing F ◦ I a
into X, and consider X0 marked at a corner of an a×(u−1)
face.
To complete the proof, we excise the desired a × b × c
box B from X0 using repeated applications of Lemma 4.
For i > 0, let Xi denote the box of dimensions a × bi × ci
that results from applying Lemma 4 to Xi−1 with bi =
max(⌈bi−1 /2⌉ , b). Notice that the markings on region Xi
are compatible with the markings on Xi−1 . At most r ≤
u−3 lg b + 1 applications of Lemma 4 are needed to obtain
br = b and thus to excise an a × b × (u − 1 − r) box Xr
from X0 . Choosing u such that c = u − 1 − r completes the
proof.
The first part of the reduction is as follows:
Definition 6. From an instance V = {v1 , . . . , v3n } with
target sum t, define (a, b, c) = (8, 120tn + 1, 240tn + 9), and
define R1 (V ) as the puzzle excising an a×b×c box (marked
at a corner of an a × c face) from a u × u × u cube as in
Lemma 5, where u ≤ 4 · (240tn + 9) is as guaranteed in the
lemma.
5.
Hub and Slots
We now describe the precise measurements of the huband-slots shape, illustrated in Fig. 4, and show how to excise
it from an appropriately-chosen box.
Definition 7. Fix a 3-Partition instance V =
{v1 , . . . , v3n } with target sum t. The shape of the hub is
c 1992 Information Processing Society of Japan
an hw × hℓ × 8 box, where hw = 120tn and hℓ = hw + 4.
For convenience, we introduce a coordinate system so
that the hub is situated with opposite corners at (0, 0, 0)
and (hw , −hℓ , 8). There are n slots, each an 8t × ℓ × 1
box where ℓ = hℓ + 4, with the ith slot having opposite
corners at (16i + 8t(i − 1), 0, 0) and (16i + 8ti, ℓ, 1). In
particular, the slots are spaced 16 units apart adjacent
to the bottom of the front face of the hub, with width-16
padding on the left and width-(hw − 8tn − 16n) padding
on the right. We refer to the union of these box shapes as
the hub-and-slots shape.
For technical reasons, we also discuss an augmented
hub-and-slots shape. This shape is obtained by adjoining
to the hub-and-slots shape the box with opposite corners at
(−1, −hℓ , 1) and (0, 0, 8). Equivalently, this shape is the
result of widening the hub by one unit in the negative x
direction and then removing a 1 × hℓ × 1 box from the
bottom-left edge.
Puzzle R1 , as defined in Section 4, excises a box of dimensions 8 × (hw + 1) × (hℓ + ℓ + 1) from a cube. We next
show how to excise the augmented hub-and-slots shape from
a box of these dimensions:
Lemma 8. Let B be the box with opposite corners at
(−1, −hℓ , 0) and (hw , ℓ + 1, 8) marked at the left face of
cell (−1, −hℓ , 0). Let S ′ be the trivially-marked augmented
hub-and-slots shape, using the same coordinates as in Definition 7. There exists a puzzle C excising S ′ from B.
Furthermore, there exists a configuration of C in B ending at the front face of cube (−1, 0, 7) (in the coordinate
frame chosen for S ′ ).
Proof: We construct C by combining three smaller puzzles:
C = C1 ◦ C2 ◦ C3 , where C1 traces the outline of the slots,
C2 can be used to fill in the rest of the bottom two layers,
and C3 can be used to fill the remaining six layers.
The puzzle C1 is given as follows:
C1 = h1, hℓ + 1, 2i ◦ h15, ℓ + 1, 8t + 2, ℓ + 1, 1in ◦
hhw − 8tn − 16n − 1, 1i .
When configuring C1 starting at the left face of cell
(−1, −hℓ , 0), each of the bars longer than hw (namely, those
of length hℓ + 1 and length ℓ + 1) can only fit along the y
direction, and so the other bars must lie in the x direction
(as they are longer than the vertical dimension of 8). In
fact, because 2ℓ + 1 is longer than the longest dimension
of the enclosing box, the length-(ℓ + 1) bars must alternate
between the positive and negative y direction. Furthermore,
the bars between these must all face in the positive x direction; otherwise, an intersection is quickly forced. It follows
that, when C1 is configured starting at the left face of cell
(−1, −hℓ , 0), it must trace the outline of the slots and the
front edge of the hub, terminating in cell (hw − 1, 0, 0).
The next portion, C2 , is defined in pieces. Define
H0 = h1, ℓ, 2, ℓ − 1, 2, ℓ − 1, 2, ℓ, 1i, whose preferred (but
not forced) configuration is shown in Fig. 5. Also define
H1 = h1, ℓ, 2, ℓ, 2, . . . , 2, ℓ, 1i, where there are 8t + 2 bars of
5
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
Fig. 5
(a)
(b)
(c)
(d)
An example of how the chain H0 is arranged to fill part
of the space between slots.
length ℓ. We define
h /2−4tn−8n−1
C2 = hℓ − 1, 2, ℓ, 1i ◦ H0 w
◦ (H1 ◦ H07 )n ◦ H0 .
Though it is not forced, puzzle C2 can be configured (starting at the end of C1 ’s configuration) to cover the first two
layers of the enclosing box with the exception of the interiors of the slots: the H0 instances are in their preferred
configurations and fill the portions between the slots, while
each H1 covers one of the slots. Again, this configuration
for C2 is not forced, but it exists.
The final portion, C3 , is quite simple:
C3 =
h1, ℓ, 2, ℓ, 2, . . . , 2, ℓi, where there are 6(hw +1) bars of length
ℓ. If C2 is configured as described in the previous paragraph,
then C3 may be configured, starting at the end of C2 ’s configuration, to fill the remaining six layers lying over the slots,
one layer at a time. In this configuration, C3 ends at the
back face of cube (0, 0, 7), proving that C1 ◦ C2 ◦ C3 has a
configuration whose complement is the hub-and-slots shape
and whose endpoint is the required face.
It remains to show that C1 ◦C2 ◦C3 must cut out the huband-slots shape. Consider any configuration of C1 ◦ C2 ◦ C3
with the specified starting face. We already showed that
C1 must trace the outlines of the slots. In puzzle C2 ◦ C3 ,
there are long bars of length at least ℓ − 1 alternating with
length-2 bars. By a similar argument as used for C1 , these
long bars must alternate between the positive and negative
y direction in the y ≥ 0 portion of the enclosing box. Because of the design of C2 ◦ C3 , it can be observed that each
of these long bars must touch the front-most face of the enclosing box. It follows that none of these long bars can lie
inside a slot, because C1 blocks the front box-face. So the
slots must remain empty. Because the total number of cubes
in C2 ◦ C3 equals the total amount of space in the y ≥ 0
portion of the box not covered by C1 or the slots, it follows
that C2 ◦ C3 must exactly fill this region. So C1 ◦ C2 ◦ C3
does indeed excise the hub-and-slots shape.
Definition 9. For a 3-Partition instance V , the second
portion of the reduction, R2 (V ), is defined as the puzzle C
excising the hub-and-slots shape from an 8 × (hw + 1) ×
(hℓ + ℓ + 1) box as in Lemma 8.
6.
Zig-Zag Universality
Define the length-k zig-zag puzzle as Z(k) = Tk =
c 1992 Information Processing Society of Japan
Fig. 6
The configurations of Z(8) that can be used to connect
adjacent cubes.
h1, 2, 2, . . . , 2, 1i, where the run-length encoding has k − 1
twos. In preparation for the second half of the reduction,
we prove a few universality results for classes of regions that
can always be filled with zig-zags. In particular, zig-zags can
fill arbitrary paths of 2 × 2 × 2 cubes (i.e., paths of cells as
defined in Section 2 after 2 × 2 × 2 subdivision of each cell)
and arbitrary paths of 4 × 4 × 4 cubes, as well as arbitrary
polycubes of 4 × 4 × 4 cubes. As usual, we must be careful
about starting and ending positions. All three of these positive results will be used in the following sections to cleanly
navigate and fill the hub.
We say that cell (i, j, k) is even or odd depending on the
parity of i + j + k; this defines a checkerboard-style labeling
of the cells in the infinite grid.
Theorem 10. Suppose we are given a path A of r faceadjacent 2 × 2 × 2 cubes of cells, two cells c0 , c1 of opposite parity in the first and last cubes of A respectively, and
boundary faces f0 , f1 of c0 , c1 on the boundaries of their
respective 2 × 2 × 2 cubes of A. Then the puzzle Z(8r) can
be configured inside A starting at (c0 , f0 ) and ending at
(c1 , f1 ).
Proof: First we verify the case r = 1. As c0 and c1 have
opposite parity, these cells are either adjacent or diametrically opposite in cube A. In the former case, one of the
three configurations of Z(8) shown in Fig. 6 suffices, up to
symmetry of the cube and/or reversal of direction. If c0 and
c1 are opposite, then one of the paths in Fig. 7 works.
The general statement follows by induction on r. Suppose
r ≥ 2, and write A’s cubes in order as A0 , . . . , Ar−1 . We
may assume that c0 is an even cell. Let c′0 be one of the
odd cells in A0 adjacent to A1 along the cell face f0′ . By the
base case there is a configuration of Z(8) in A0 starting at f0
and ending at f0′ , and by induction there is a configuration
of Z(8r − 8) inside A \ A0 from f0′ to f1 .
Next we show an analogous statement for 4 × 4 × 4 cubes.
6
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
(a)
Fig. 7
(b)
The configurations of Z(8) that can be used to connect
two opposite cubes.
The proof will be almost identical, except that the r = 1
case requires more casework.
Theorem 11. Suppose we are given a path A of r faceadjacent 4 × 4 × 4 cubes of cells, two cells c0 , c1 of opposite parity in the first and last cubes of A respectively, and
boundary faces f0 of c0 and f1 of c1 on the boundaries of
their respective 4×4×4 cubes of A. Then the puzzle Z(64r)
can be configured inside A starting at (c0 , f0 ) and ending
at (c1 , f1 ).
Proof: As above, it suffices to check only the case r = 1. A
4×4×4 box decomposes as the union of eight 2×2×2 boxes
called its octants. Let V0 and V1 be the octants containing
c0 and c1 respectively. We consider four cases depending on
the relative position of V0 and V1 .
If V0 and V1 are adjacent, then the desired result follows
from Theorem 10 using a path of the eight octants starting
at V0 and ending at V1 . The same argument works if V0
and V1 are opposites. In the other two cases no such path
of octants exists, so we must work a bit harder.
If V0 and V1 share an edge but not a face, as in Fig. 8,
we may proceed as follows: Choose faces f0′ and f1′ as
in Fig. 8(b); use Theorem 10 to join faces f0 and f0′ while filling the upper-right octants; connect this to H from Fig. 8(a),
which connect faces f0′ and f1′ while filling the upper-left octants; and use Theorem 10 to connect f1′ and f1 while filling
the bottom octants.
Finally, suppose V0 = V1 . Up to symmetry, there are six
cases to check (recall that c0 and c1 have opposite parity).
These are shown in Fig. 9, and in each case we use Theorem 10 to join faces f0′ and f1′ while filling all octants except
V0 = V1 .
Finally, we show that zig-zags can cover not only paths of
4 × 4 × 4 blocks, but also arbitrary polycubes formed from
4 × 4 × 4 blocks, at the expense of slightly less control over
endpoints:
Theorem 12. Let A be a connected polycube of r faceadjacent 4 × 4 × 4 cubes of cells, and take any mark (c, f )
on A. Then the puzzle Z(64r) can be configured in A starting at (c, f ).
Proof: As shown in [2], if we subdivide each 4 × 4 × 4 block
of A into its eight octants and consider A as a polycube of
2 × 2 × 2 cubes, then there is a hamiltonian cycle through
all of these 2 × 2 × 2 cubes. This implies that A may be
represented as a path of 2 × 2 × 2 cubes starting at the one
c 1992 Information Processing Society of Japan
(a) The chain H. The red face is f0′ , the
green face is f1′ .
(b) An example of how to select the faces f0′ and
f1′ , given f0 and f1 .
Fig. 8
How to connect f0 to f1 when V0 (upper right back) and
V1 (lower right front) share an edge but not a face.
containing mark (c, f ); if (c, f ) = (∅, ∅), we may pick this
starting cube arbitrarily. By Theorem 10, this path may be
filled by Z(64r).
7.
Fitting the Pegs
We now define the third part of the reduction, R3 , showing roughly that it fits into the hub-and-slots shape if and
only if the 3-Partition instance V has a 3-partition.
Definition 13. For each 1 ≤ i ≤ 3n, define peg Pi =
hℓ, 2, ℓ, 2, . . . , 2, ℓi, where there are 8vi bars of length ℓ.
Then define
R3 = C0 ◦ Z1 ◦ P1 ◦ Z2 ◦ P2 ◦ Z3 ◦ · · · ◦ Z3n ◦ P3n ,
where
• C0 = h1, 7, 2, 7, 2, . . . , 2, 7, 1i, with hℓ bars of length 7,
• Z1 = Z(128t + 256 + 16hℓ ), and
• Z2 = · · · = Z3n = Z(k), with k = 64 · 30tn.
First we prove the easier direction:
Lemma 14. If R3 can be configured in the augmented
hub-and-slots shape (with unconstrained starting and ending positions), then V has a 3-partition.
Proof: In fact, if just the pegs P1 , . . . , P3n can be configured in the hub-and-slots shape without overlap, then V
has a 3-partition. Call the length-ℓ bars in the pegs Pi long
7
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
(a)
Fig. 9
(b)
(c)
(d)
(e)
(f)
Given any pair of faces f0 and f1 on the outside surface of
the 4 × 4 × 4 cube, these are the different ways to connect
f0 to f0′ (the red face) and f1 to f1′ (the green face) within
a single 2 × 2 × 2 box.
bars; there are 8tn long bars among the pegs.
Because ℓ > hℓ and ℓ > hw + 1, each long bar cannot fit
fully in the hub and must therefore stick (at least partially)
into a slot, meaning it must lie parallel to the y-axis and in
the z = 0 plane. Furthermore, no two long bars can occupy
the same x-coordinate (because 2ℓ > hℓ + ℓ), so the 8tn
long bars must occupy exactly the 8tn x-coordinates of the
slots. Finally, each peg Pi must have all of its long bars
in a single slot, because the length-2 bars force the parallel
long bars of a single peg to be adjacent. So the widths of
the pegs in each slot add exactly to the width of the slot,
and these widths (divided by 8) exactly give a 3-partition
for {v1 , . . . , v3n }.
The other direction is more difficult: we must show that,
if there is a 3-partition, then R3 can be configured in the
hub-and-slots shape. As usual, we pay special attention to
the endpoints.
Lemma 15. If V has a 3-partition, then there is a configuration of R3 in the augmented hub-and-slots shape starting
at the front face of cell (−1, 0, 7), such that the unfilled region is a face-connected polycube of 4 × 4 × 4 cubes and
c 1992 Information Processing Society of Japan
Fig. 10
An example of how Zi might be configured. Each cube
is a 4 × 4 × 4 brick; the path indicates the order that Zi
passes through the bricks. Within each brick, the configuration of Zi will be determined by Theorem 11; the
oscillations serve as a visual reminder that the path of
cubes winds through the 64 cells in each brick.
such that the configuration ends at a boundary face of this
polycube.
Proof: The hub—specifically, the box with opposite corners at (0, −hℓ , 0) and (hw , 0, 8)—may be partitioned into
4 × 4 × 4 boxes, which we refer to as bricks and identify in
coordinates by their left, back, bottom corners.
Because there exists a 3-partition of V , the pegs
P1 , . . . , P3n may be positioned to exactly fill the slots. Do so
in such a way that each peg starts and ends on the boundary of the hub, with the starting face to the right of the
ending face. The brick adjacent to the starting face of Pi is
the starting brick for Pi , and the ending brick is defined
similarly. We may further assume that peg P1 is chosen as
the rightmost peg in the leftmost slot, so its starting brick
is located at (8t + 12, −4, 0). The 3n starting bricks and the
3n ending bricks are all distinct, and their left, back, bottom
corners all have y = −4 and z = 0.
Configure C0 to fill the “augmentation” of the augmented
hub-and-slots: it starts at the front face of cell (−1, 0, 7), has
its length-7 bars in the z-direction and its length-2 bars in
the negative y-direction, and ends at the right face of cell
(−1, −hℓ , 7).
Now everything has been filled except for the hub, which
is currently empty. We must show how to configure
Z1 , . . . , Z3n in the hub so that they connect where they
must, don’t overlap each other, and leave a connected polyomino of bricks as their complement.
First we position Z1 . Consider the path of bricks that
starts at brick (0, −hℓ , 4) in the left, back, top corner of
the hub, then moves right, down, and then forward to the
starting brick of P1 , namely (8t + 12, −4, 0). This path has
2t+4+hℓ /4 bricks. By Theorem 11, we may configure Z1 to
exactly fill this path of bricks starting at the left face of cell
(0, −hℓ , 7) (an odd cell) and ending at the front face of cell
(8t + 15, −1, 0) (an even cell). These faces are, respectively,
where C0 ends and where P1 starts.
Finally, we describe how to configure each puzzle Zi , for
2 ≤ i ≤ 3n. Construct a path of bricks connecting the ending brick of Pi−1 (say this brick has coordinates (4q, −4, 0)
with q odd) to the starting brick of Pi (with coordinates
(4r, −4, 0) with r even) as follows. If q < r, then:
8
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
• Start at (4q, −4, 0),
• proceed back, then up, then right to (s, −12i, 4) (parameter s is explained below),
• step forward one brick to (s, −12i + 4, 4),
• then move left, then down, then forward to the starting
brick of Pi , (4r, −4, 0).
An example is shown in Fig. 10. If q > r, follow these
instructions instead from (4r, −4, 0) to (4q, −4, 0) and then
reverse its direction. Here, s > max(4q, 4r) is chosen so that
the path covers a total of 30tn bricks: s = 60tn + 2(q + r) −
12i − 2, and we indeed have s > 60tn − 36n ≥ 8tn + 16n >
max(4q, 4r). (Note also that 4 | s because q + r is odd.)
Now, by Lemma 11, we may configure path Zi to exactly
fill this path of bricks, starting at the ending brick of Pi−1
and ending at the starting brick of Pi . More specifically,
we may configure Zi in this path so that it starts at the
front face of cell (4q, −4, 0)—this cell is even and this face
is the ending face of Pi−1 —and ends at the front face of cell
(4r + 3, −4, 0)—an odd cell and the starting face of Pi .
Why do these configured puzzles Zi not intersect each
other? In the top layer of bricks, each Zi is contained in a
different set of rows: for 2 ≤ i ≤ 3n, Zi touches only rows
−12i and −12i + 4, and Z1 touches only row −hℓ < −36n.
In the bottom layer of bricks, each Zi for 1 ≤ i ≤ 3n is
contained only in the columns corresponding to the starting
and/or ending bricks it touches, and these columns are all
distinct.
Let M be the complement of the Zi configurations in the
hub. Why is M connected? The top layer of M is connected
because no individual configuration Zi separates any bricks
in the top layer, and no two configurations Zi and Zj are
adjacent in the top layer. For each column in the bottom
layer, the portion of the row contained in M is a connected
sequence of bricks that is adjacent to at least one of the
bricks in the top layer of M . Hence, M is indeed connected.
Finally, P3n ends at a face adjacent to its ending brick,
and this brick is contained in M .
8.
Filling the Gaps
In the final portion of the reduction, we define R4 (V ) as
a zig-zag with enough cubes to exactly fill the remaining
portion of the original cube: R4 (V ) = Z(u3 − vol(R1 (V ) ◦
R2 (V ) ◦ R3 (V ))), where vol counts the number of cubes in
the puzzle. With the results built up in the previous sections, the full result is now readily proved:
Theorem 16. Take a 3-Partition instance V and build
the resulting puzzle R(V ) = R1 (V )◦R2 (V )◦R3 (V )◦R4 (V )
of u3 cubes as in the previous sections. Then puzzle R(V )
can be configured to exactly fill a u × u × u box if and only
if there exists a 3-partition of V .
Proof: If R1 ◦ R2 ◦ R3 can be configured in a u × u × u
box, then Lemmas 5, 8, and 14 guarantee that V has a 3partition. Conversely, if V has a 3-partition, then Lemmas
5, 8, and 15 imply that R1 ◦R2 ◦R3 may be configured so that
the unfilled portion is a connected polycube of 4×4×4 cubes,
c 1992 Information Processing Society of Japan
ending at a face adjacent to this polycube. By configuring
R4 in this region by Theorem 12, we obtain a configuration
of R1 ◦ R2 ◦ R3 ◦ R4 filling the entire cube.
Corollary 17. The problem of deciding if a given puzzle
can exactly fill a cube is NP-complete.
Proof: Such a configuration may be easily verified, so
the problem is in NP. By Lemma 5, for an instance V =
{v1 , . . . , v3n } with target sum t, the chosen cube side-length
u is at most 4(hℓ + ℓ + 1) = poly(t, n), and the length of
R(V ) is u3 = poly(t, n). The explicit map V 7→ R(V ) may
be computed in polynomial time, and Theorem 16 guarantees this is a valid Turing reduction. Because 3-Partition
is strongly NP-complete, the result follows.
9.
Open Questions
In this paper we have analyzed a natural generalization of
the Snake Cube puzzles, but many related questions remain
open:
• We only address whether a solved configuration of
the puzzle exists. The actual puzzle, however, must
be physically moved into its solved state. Can every
solved configuration be reached by a continuous, nonself-intersecting motion from the initial (flat and monotone) configuration? If not, can this decision problem
be solved efficiently?
• Is the analogous 2-dimensional problem also hard?
Specifically, is it NP-complete to decide whether an
S-T sequence of squares can pack into an N × N
grid of squares, where S and T represent “straight”
and “turn” squares as before? This is equivalent to
the 3-dimensional problem of packing a puzzle into an
N × N × 1 box. This also relates to the problem of finding simple, planar configurations of fixed-angle chains,
a version of which was shown to be NP-hard in [3]. The
methods from this paper, however, do not seem to directly apply to this setting.
• What if the target shape is allowed to have large
“holes”? For example, is it still NP-hard to decide if
a puzzle of α · N 3 cubes can be configured inside an
N × N × N cube, for all constants 0 < α < 1?
Acknowledgments These results arose from an open
problem session organized for the Geometric Folding Algorithms: Linkages, Origami, Polyhedra course taught by
Erik D. Demaine at MIT in Fall, 2010. We thank the other
participants of this session for a productive and stimulating
research atmosphere.
References
[1]
[2]
[3]
Creative Crafthouse. King snake.
Erik D. Demaine, Martin L. Demaine, Jeffrey F. Lindy, and
Diane L. Souvaine. Hinged dissection of polypolyhedra. In
Proceedings of the 9th Workshop on Algorithms and Data
Structures (WADS 2005), volume 3608 of Lecture Notes
in Computer Science, pages 205–217, Waterloo, Ontario,
Canada, August 15–17 2005.
Erik D. Demaine and Sarah Eisenstat. Flattening fixed-angle
chains is strongly NP-hard. In Proceedings of the 12th Algorithms and Data Structures Symposium (WADS 2011), pages
9
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
[4]
[5]
[6]
[7]
[8]
[9]
314–325, Brooklyn, New York, August 15-17 2011.
M. R. Garey and D. S. Johnson. Complexity results for multiprocessor scheduling under resource constraints. SIAM Journal on Computing, 4(4):397–411, 1975.
Indiana University Lilly Library. The jerry slocum mechanical
puzzle collection.
http://webapp1.dlib.indiana.edu/images/splash.htm?
scope=lilly/slocum. Acquisitions 024867, 024868, 024869,
024870, and 024871. http://webapp1.dlib.indiana.edu/
images/item.htm?id=http://purl.dlib.indiana.edu/iudl/
lilly/slocum/LL-SLO-024867, etc.
Alison Elizabeth McDonough. Snake cube puzzles: Hamilton
paths in grid graphs. Honors project, 2009.
F. Ruskey and Joe Sawada. Bent hamilton cycles in ddimensional grid graphs. The Electric Journal of Combinatorics, 10(1):R1, 2003.
http://www.combinatorics.org/ojs/index.php/eljc/
article/view/v10i1r1.
Jaap Scherphuis. Jaap’s puzzle page: Snake cubes. http:
//www.jaapsch.net/puzzles/snakecube.htm, 2010.
David Singmaster. Singmaster cube and puzzle collection. CD
distributed at Gathering 4 Gardner 6, March 2004.
Zachary Abel is a Ph.D. candidate
in the Department of Applied Mathematics at the Massachusetts Institute
of Technology (MIT) working with
Professor Erik D. Demaine in the Computer Science and Artificial Intelligence Lab (CSAIL). His primary research is in computational and discrete
geometry, including such topics as computational origami
and geometric rigidity theory. Mr. Abel is currently funded
under the National Science Foundation (NSF) Graduate Research Fellowship Program, and he received his Bachelors of
Arts in Mathematics and Computer Science from Harvard
in 2010.
Erik D. Demaine received a B.Sc.
degree from Dalhousie University in
1995, and M.Math. and Ph.D. degrees
from University of Waterloo in 1996
and 2001, respectively. Since 2001,
he has been a professor in computer
science at the Massachusetts Institute
of Technology. His research interests
range throughout algorithms, from data structures for improving web searches to the geometry of understanding
how proteins fold to the computational difficulty of playing games. In 2003, he received a MacArthur Fellowship
as a “computational geometer tackling and solving difficult
problems related to folding and bending—moving readily
between the theoretical and the playful, with a keen eye to
revealing the former in the latter”. He cowrote a book about
the theory of folding, together with Joseph O’Rourke (Geometric Folding Algorithms, 2007), and a book about the
computational complexity of games, together with Robert
Hearn (Games, Puzzles, and Computation, 2009).
c 1992 Information Processing Society of Japan
Martin L. Demaine is an artist
and mathematician. He started the
first private hot glass studio in Canada
and has been called the father of Canadian glass. Since 2005, he has been the
Angelika and Barton Weller Artistin-Residence at the Massachusetts
Institute of Technology. Both Martin
and Erik work together in paper, glass, and other material.
They use their exploration in sculpture to help visualize and
understand unsolved problems in mathematics, and their
scientific abilities to inspire new art forms. Their artistic
work includes curved origami sculptures in the permanent
collections of the Museum of Modern Art (MoMA) in New
York, and the Renwick Gallery in the Smithsonian. Their
scientific work includes over 60 published joint papers,
including several about combining mathematics and art.
Sarah Eisenstat is a Ph.D. student
in the Department of Electrical Engineering and Computer Science at the
Massachusetts Institute of Technology,
working with Professor Erik D. Demaine. Her current research interests
include computational geometry and
algorithms. She received her Sc.B. and
Sc.M. degrees from Brown University in 2008 and 2009, respectively.
Jayson Lynch is an undergraduate
in Physics and Computer Science at
the Massachusetts Institute of Technology (MIT). He is a member of
MIT’s Computer Science and Artificial Intelligence Laboratory (CSAIL)
where he works with Professor Erik
Demaine. His research interests include computational origami, games and computation, algorithms, and the interplay between physics and computation.
10
Journal of Information Processing Vol.0 No.0 1–11 (??? 1992)
Tao B. Schardl is a Ph.D. candidate in the Department of Electrical Engineering and Computer Science
(EECS) at the Massachusetts Institute of Technology (MIT). He is a
member of MIT’s Computer Science
and Artificial Intelligence Laboratory
(CSAIL), and works in the Supertech
group with Professor Charles Leiserson. His primary research is on developing parallel algorithms and parallel data
structures. His previous research includes developing a
work-efficient parallel breadth-first search algorithm, designing a theoretical framework for analyzing Cilk programs
with nonconstant-time reducer hyperobjects, and developing mechanisms to support deterministic parallel randomnumber generation. Mr. Schardl received his Bachelor of Science in Computer Science and Electrical Engineering from
MIT in 2009 and his Masters of Engineering in Computer
Science and Electrical Engineering from MIT in 2010.
c 1992 Information Processing Society of Japan
11