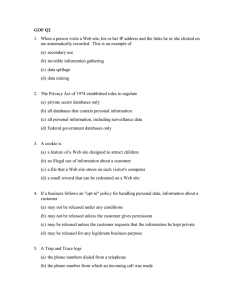
government and corporative internet surveillance
advertisement

UFRGSMUN | UFRGS Model United Nations ISSN: 2318-3195 | v.2, 2014| p. 411-443 GOVERNMENT AND CORPORATIVE INTERNET SURVEILLANCE Gabriela Jahn Verri1 Luiza Bender2 Eduardo Dondonis3 ABSTRACT Although surveillance is often recognized as a social phenomenon rather than as state practice, the vertical employment of surveillance techniques by powerful actors such as governments and economic corporations has acquired a bold and extensive character in the last few decades. Accompanying the technological revolution the world has been undergoing since the dawn and popularization of keen communications and information technologies such as, and most notably, the Internet, surveillance practices adopted yet another shape: cyber surveillance. The inestimable power of acquiring and processing immense amounts of data about a growing number of subjects presents as much an instrument as a menace to the global society. This essay briefly analyzes the historical context of surveillance and the technologies that allow its employment today. We further attempt to outline the most common cyber surveillance practices, it’s basic technical features, and how states and corporations relate to cyber surveillance domestically and internationally, as active as well as passive agents. Finally, a discussion is drawn regarding the legitimacy and legality of cyber surveillance practices in the context of transnational relations and human rights protection. 1 Fourth-year law undergraduate at the Federal University of Rio Grande do Sul (UFRGS). 2 Luiza Bender Lopes is a 6th semester student of International Relations at the Federal University of Rio Grande do Sul (UFRGS). 3 Eduardo Dondonis Pereira is a 6th semester student of International Relations at the Federal University of Rio Grande do Sul (UFRGS). World Summit on the Information Society Forum Power does not reside in institutions, not even in the state or in large corporations. It is located in the networks that structure society. (Castells 2010, 342) 1 HISTORICAL BACKGROUND It is undeniable that as the nature of communication changes, the means to attain information follows. And information is key to the well being of states, not only strategically, but also from a human rights perspective. Surveillance, as means of obtaining information, is in no way an illegitimate policy per se. As any power the democratic state legitimately holds, surveillance ultimately exists to preserve human rights and social values. Nonetheless it can be a dangerous weapon against them, as it frequently is the case with power. 1.1 THE CONCEPT OF PRIVACY To properly understand what it means to be under surveillance it is necessary to clarify what the term ‘privacy’ actually entails. Despite being used in philosophical, political and legal discussions, there is no single definition for the term. Its most accepted origin is in Aristotle’s work, most notably in his distinction between the public sphere of political activity and the private sphere associated with family and domestic life (DeCew 2013). Currently, most dictionaries define privacy as “the state or condition of being free from being observed or disturbed by other people”. Before the written concept of privacy appeared with the development of privacy protection in American law from the 1890s onward, amendments in the United States Constitution already addressed the issue, most notably the Fourth Amendment of 1789 (Richars 2012). As a part of the American Bill of Rights, it prohibited unreasonable searches and seizures and required any warrant to be judicially sanctioned. The amendment was adopted in response to the abuse of a general search warrant issued by the British government, a major source of tension in pre-Revolutionary America (DeCew 2013). English Common Law, as it was, had no recognized right to privacy, only offering minor protection in the form of the breach of confidence clause, which was employed when information delivered in confidence was disclosed to others (Phillipson & Fenwick 2000). At the same time, a more systematic discussion of the concept of privacy arose with an essay published in the Harvard Law Review, entitled “The Right to Privacy” by Samuel Warren and Louis Brandeis. The essay focused on violations caused by 412 UFRGSMUN | UFRGS Model United Nations recent inventions such as photography and newspapers, and it emphasized the invasion of privacy brought about by public dissemination of details related to a person’s private life (DeCew 2013). Warren and Brandeis thus laid the foundation for a concept of privacy that has come to be known as “control over information about oneself” (Warren and Brandeis 1890). 1.2 THE EMERGENCE OF GUIDELINES FOR CORRESPONDENCE INTERCEPTION AND WIRETAPPING Included in the Fourth Amendment of the American Constitution, as well as in several constitutions from European countries, is a basic legal principle know as the secrecy of letters. It states that sealed letters in transit shall not be opened by government officials or any person that not the sender or the receiver. However, many countries that usually oblige to such law are known for having committed postal censorship at different times in their history. This inspection of mail, including the opening, reading and selective obliteration of letters, most often by government authorities, is known to happen during wartime and periods of civil disorder. During both World War I and II, countries members of both sides organized enormous operations for the monitoring of letters and their contents (Fiset 2001). With the innovations in means of communication, the principle of the secrecy of letters was naturally extended to telephony and electronic information. Nevertheless, most national telecommunications laws had breaches that allowed the interception and monitoring of information by wiretapping and similar methods (Richards 2012). In the United States, warrantless wiretapping was not considered a constitutional harm for a long time. When cases of wiretapping were taken to the American courts, they were soon dismissed because of the lack of success that the subjects had in proving that the government had actually targeted them. Martin Luther King Jr., for example, had all his telephones wiretapped from 1963 to 1965, when he was considered a threat to public order by the FBI. The wiretap was an attempt to obtain information on King’s private activities to discredit him (Richards 2012). 1.3 IMPORTANT LANDMARKS OF REGULATION The first steps for the regulation of the protection of privacy, both in the public and in the private spheres, were taken by the end of the Second World War. Founded in 1934, the United Nations aimed at reaffirming people’s faith in fundamental human rights and in the dignity and worth of the human person. Soon after, in 1948, the UN’s General Assembly approved the Universal Declaration of Human Rights (UN 1948). Two of the thirty-five clauses of the Declaration deal directly 413 World Summit on the Information Society Forum with issued related to privacy. Article 12 states that no one should be subjected to arbitrary interference with his or her privacy, family, home or correspondence, being protected of do by law. Article 19 states that everyone has the right to freedom of though and the right to receive and impart information through any media and regardless of frontier (UN 1948). As supplement for the Universal Declaration of Human Rights, the General Assembly approved two further international treaties in 1966, the International Covenant on Civil and Political Rights and the International Covenant on Economic, Social and Cultural Rights. On the ICCPR, Articles 17 and 19 referred to issues of privacy, mostly with the same wording as the corresponding articles in the Universal Declaration of Human Rights. In the 1970s, two important sets of regulations were approved. The first was drafted by the International Telecommunication Union. An independent organization born from the International Telegraph Union, the ITU officially joined the UN after its foundation, becoming a specialized agency responsible for issues relating to information and communications technologies. The International Telecommunication Convention was approved in 1973. Despite having recommendations using member countries to develop important telecommunication structures and to safeguard the privacy of international correspondence, the Convention recognized the sovereign right of each country to regulate its own telecommunications (ITU 1973). The second set, approved in the same year, was The Code of Fair Information Practices. Created by the United States’ department of Health, Education and Welfare, it affirmed that no personal data record-keeping systems whose very existence was a secret should exist. It also stated that any person had a right to find out what information about them was recorded and for what it was used (Gellman 2014). Another landmark for privacy protection, especially addressing state surveillance, was the Foreign Intelligence Surveillance Act (FISA) in the United Sates. During the 1970s major domestic surveillance programs came to light. The FBI, the CIA and other government agencies had been engaging in “pervasive surveillance of politicians, religious organizations, women’s rights advocates, anti-war groups, and civil liberties activists” since the beginning of the Cold War (O’Harrow 2006, 18). Such schemes were not restricted to communications interception but went as far as to interfere with civilian’s private lives by anonymously contacting employers and relatives. These revelations brought about social upheaval to which the government responded with the 1974 Patriot Act and the FISA in 1978, both of which established further legal instruments to protect civilians’ information and communications from government interference. Despite the fact that both are often viewed as “key safeguard[s] against domestic spying” by civil rights activists, there is still criticism regarding the actual 414 UFRGSMUN | UFRGS Model United Nations effectiveness of these regulations1 (O’Harrow 2006). Finally, in 1980, the Organization for Economic Co-operation and Development published the Guidelines on the Protection of Privacy, the first internationally agreed set of privacy principles (OECD 1980). Eight important principles were elaborated for national application by each member state. The most prominent were the ones that referred to purpose specification of the collection of data and to the safeguard of personal information. The signatories were urged to adopt appropriate domestic legislation on topics regarding privacy, to support self-regulation, to provide for reasonable means for individuals to exercise their rights and to ensure that no unfair discrimination occurred against data subjects (OECD 1980). 1.4 SURVEILLANCE AND THE INTERNET It wasn’t until the development of the Internet that ICT acquired the vigorous character for which they are known today. The Internet exceptionally increased people’s capacity to communicate and generate information. Its fluid and democratic character is, however, not only responsible for unprecedented possibilities for sharing and networking, but it also creates an environment of vulnerability for information flowing online. Thus, with the advent of the Internet, privacy protection dialogues and initiatives became even more crucial for human rights promotion as a whole (CCHRP 2013). The Internet dates from the Cold War period and has its beginning in the ARPANet (Abbate 2000). In response to the apparent technological superiority achieved by the Soviet Union in the 50s, the Advanced Research Project Agency (ARPA) is established in the United States in 1958 as a centre for research and development linked to the U.S. Department of Defense (Launius 2014; Hafner and Lyon 1998). By the end of the 1960s, Robert Taylor, the director of ARPA’s Information and Processing Techniques Office, had the project of the ARPANet under way, a system of electronic links between computers that would allow researchers around the country with similar work to share resources and results more easily. On december 1st, 1969, the ARPANet was born (Abbate 2000; Hafner and Lyon 1998). In 1972, the ARPANet went public during the First International Conference on Computers and Communication. The presentation stimulated further research on the subject among the scientific community throughout the western world, and subsequently, new networks emerged (Griffiths 2002). Throughout this period of diffusion, networks were still a multitude of different techniques and protocols, with 1 For instance, the Foreign Intelligence Surveillance Court (FISC), established by the FISA to supervise government investigations and communications interception, is known for its recurring permissive character, rarely denying applications for electronic surveillance. 415 World Summit on the Information Society Forum the ARPANet still as the backbone of the entire system. The preponderance of the ARPANet in regard to the other network models developed was mostly due to the centrality of the American academical community and the substantial funding by the American government. By 1982, other similar systems around the world started to adopt the TCP/IP standard – and this is the point generally considered as the birth of the Internet as we know today (Griffiths 2002). The Internet may be conceptualized, therefor, as a network which allows connection of comupers, databases and computed networks through technological specifications, protocols and communication standards (Canabarro 2012). In 1989, Tim Berners-Lee, a British scientist from the European Organization for Nuclear Research (CERN), suggested the standard World Wide Web, whose aim was to facilitate access and organize large amounts of information circulating on the Internet (Johnson 1994). The standard World Wide Web has facilitated the popularization of the Internet, once it allowed the common people to post and share information through websites. In spite of having invaluably linked its intermediate structures to sovereign territories, the Internet was conceptualized as a world free from government regulation. This assertion of autonomy was represented by both the Electronic Frontier Foundation, institutionally, and documented through the Declaration of Cyberspace Independence (Barlow 1996). However, by 1991 the establishment of the Internet Assigned Numbers Authority (IANA) structured official government regulation of the Internet. The IANA was the result of an agreement between the then ‘root authority’2 controller Information Science Institute (ISI) of the University of Southern California and the United States Department of Commerce. The United States then made its pledge to Internet governance by means of the publication of the Green Paper, which claimed total authority over the Internet Root by the US government (Goldsmith & Wu 2008; Drake 2008). With the increasing number of users and technical capabilities, digital media gradually became the focus of national intelligence agencies, giving rise to cyber surveillance practices used to date. Combining the everyday-use character of the Internet with its potential for “processing speed, storage capacity, miniaturization, affordability, availability, portability, spatial reach, and scope of application”, states attain means to keep themselves well-informed at the same pace that civilians’ fundamental rights, which had already been secured in the eras of telephony and mail, are put in jeopardy (Benett, Clement & Milberry 2012). And do, the recurring trade-off between freedom and security is given yet another shape. 2 Described by Wu & Goldsmith (2008, 29-30) as “the power to issue orders respecting domain names and numbers and have those orders obeyed.” 416 UFRGSMUN | UFRGS Model United Nations 2 STATEMENT OF THE ISSUE 2.1 DEFINITION OF CYBER SURVEILLANCE Until pioneer author Michel Foucault studied and described the phenomenon, surveillance was commonly associated with autocratic and totalitarian states and their control over their populations (Richards 2012, 5). This interrelation, however, has become essentially inaccurate with the advent of electronic communication technologies and, especially, the Internet (Boyle 1997, 186-88). Even before communication acquired such dynamic character, surveillance was already perceived as much more than a top-down means of exercising power, but as a complex network composed of numerous agents (Foucault 1977, 135-69). Today, the use of surveillance technology has not only found overall acceptable justification in democratic societies, but has completely crossed the public-private border and expanded to the corporative sphere (Richards 2012, 7-8). David Lyon describes governmental and corporative surveillance as the “focused, systematic, and routine attention to personal details for purposes of influence, management, protection, or direction” (Lyon 2007, 14). The most common form this practice takes in the context of information and communication technologies (hereinafter ICT) is still so-called data surveillance, which implies the collection and retention of information about an “identifiable individual”, often from multiple sources3, which help recognize multiple activities and establish a pattern of behavior in both the virtual and material realms (Stanley & Steinhardt 2003, 3). Although less common and fairly recent, institutional Internet surveillance may also acquire the shape of media surveillance, done by means of – recognized or ignored – image (still or video) and sound hoarding through a subject’s personal apparatus such as private webcams and microphones, as well as screen-recording (RWB 2013, 9-33; Stanley & Steinhardt 2003, 2-4)4. The so-called Information Society we now experience, where “the amount of stored information grows four times faster than the world economy” (MayerSchönberger & Cukier 2013, 9) is said to be a new social system in which expansion of the quantity of information generated is reshaping the way we relate to information, communication and, therefor, with each other (Webster 2014). There are many aspects of the digital revolution that has brought change in the way we deal with information. From the rise of social media to the plummeting costs of communications technologies behind mobile phones and computers, the staggering amount of technological 3 Identified within digital networks. 4 For practical as well as academic reasons, “communications surveillance” will be grouped under both data and media surveillance (Tokson 2009; Stanley & Steinhardt 2003). 417 World Summit on the Information Society Forum innovation continuously expands our capabilities to produce and stack information in an unprecedented scale (Webster 2014; Castells 2000). In a context of massive and rapid flows of information, such as is the case of the Internet, personal data is increasingly being stripped of its intimate character (Hope 2011, 8). Public entities have long had the means of legally obtaining private details about citizen’s lives through warranted criminal investigations and allegedly justifiable preservation of national security, complying with the principles of necessity and proportionality (Brown & Korff 2009; LaRue 2013, 3). However, the lack of international as well as self regulation by states when it comes to data and communication interception on the Internet – arguably because of the ever changing and evolving nature of such technologies – has made users unsure about the safety of their information and communications. Not to mention the evident breach in private Internet surveillance regulation in most states as well as by the international community as a whole (La Rue, 2013). 2.2 BASIC TECHNICAL ASPECTS OF CYBER SURVEILLANCE Data retention and analysis has been increasingly incorporated in the social and institutional spheres in many areas: public health, business and global economy, national and public security, government-citizen relationships, environmental resource management, among many others. Big data analysis5 is responsible for a revolutionary way of making decisions in which information is formatted into quantified data to allow insights based on correlation (Mayer-Schönberger & Cukier 2013). For purposes such as this, data retention is as much a menace – for its invasive potential – as it is a highly advantageous tool. Thus, a critical analysis of corporative and governmental surveilling strategies is due. Internet surveillance performed by public and private actors are mainly shaped into two categories: mass and targeted surveillance. Both have become equally popular among governmental agencies for their usefulness and effectiveness in criminal investigations, protection of national security, fight against cybercrime, among other purposes. However, both are also equivalently dangerous when imprudently used by authorities and powerful enterprises. It’s important to technically decipher these technologies in order to better understand their uses and appeal as well as their risks to society. 5 Described by Mayer-Schönberger & Cukier as “the ability of society to harness information in novel ways to produce useful insights or goods and services of significant value” (Mayer-Schönberger & Cukier 2013, 2). 418 UFRGSMUN | UFRGS Model United Nations 2.2.1 Mass Surveillance of Network Activity As an extensive cyber surveillance method, mass surveillance of network activity allows institutions to intercept, collect and keep an immense amount of data through searches on online communication flows. Using narrow filters (such as specific terms, dates and locations) these software are able to quickly browse through network communications and simultaneously trace enormous quantities of specific data as well as its sources (Hosein & Palow 2013, 1081-83). This kind of technology is commonly associated with two main purposes. Firstly, its use as a consumers marketing research tool has been gaining popularity among the private sector. Intelligence companies as well as Internet service providers (hereinafter ISPs) and other technical intermediaries are selling personal data of millions of users to enterprises that, at the very least, want to be informed of consumers’ personal characteristics on an intimate level (Lyon 2010, 238). Virtually non of the United Nations member-states have any regulation concerning the trade of personal information among private institutions (La Rue 2013). Again, the justification for this commonly lies on the recent character of this type of activities which requires public policy to continuously evolve in order to accompany them (Wagner 2011, 15). Secondly, governmental bodies have also been accredited for using these technologies “lawfully” against national security threats, particularly in campaigns against terrorism and cyber crime (Chen & Wang 2005). Surveillance of network activities is predominantly associated with state practice through communications surveillance (Hosein & Palow 2013). Many public intelligence agencies around the globe6 are known to use systems that operate extensively tracing communications data (RWB 2013, Fuchs 2012). This practice consists basically of tracking, storing and analyzing information about the character of communications (i.e. when, from where, from and to whom an e-mail was sent), rather than their contents. This information is often referred to as ‘metadata’, and is the essence of arguably the least invasive exercise of governmental cyber surveillance (NISO 2004). Notwithstanding, such mild employment of this technology is the basis for a more aggressive genre of cyber surveillance: so-called ‘dataveillance’. As described by Brown and Korff (2009, 123), dataveillance is the monitoring of the ‘data trails’ left by individuals in various transactions. Through broad metadata analysis, operators are able to combine communication flows and databases into shaping a single person’s online activities. Ultimately, these compositions can generate thorough and detailed behavioral outlines, a practice known as ‘profiling’ (Brown & Korff 2009, 123-30). Profiling through metadata analysis is becoming increasingly cheaper, 6 Namely from the United States, the United Kingdom, France, Germany, Australia, New Zealand, China, Syria, Egypt, Tunisia, Iran, Vietnam etc. (Cupa 2013; Fuchs 2012; RWB 2010; RWB 2013; Stanley & Steinhardt 2003) 419 World Summit on the Information Society Forum especially for public entities (La Rue 2013, 11). A growing number of governmental intelligence agencies confirm to have their own communications surveillance software such as the FBI’s ‘Carnivore’ and ‘Echelon’, a program run in collaboration by the ‘Five Eyes’ intelligence agreement between the United States, Great Britain, Canada, Australia and New Zealand (MacDonald, Ben-Avie & Carrion 2013, 9; Stanley & Steinhardt 2003, 8-9). Nevertheless, profiling requires neither groundbreaking technology nor specific software. Much like enterprises with commercial purposes, as mentioned above, authorities can get the information they need for profiling from third party service providers by making plain requests (which in many cases do not require judicial approval) to ISPs and Internet companies (La Rue 2013, 12; Mac Donald, Ben-Avie & Carrion 2013). For instance, by the end of 2013 the number of communications data to the estimative of such requests the United Kingdom and France make per year (UK 2011, 29; European Commission 2011). Even so, states do not have to go as far as collecting communications data and strictly private online information to create portraits of an individual’s persona and activities. Through mechanisms of social media monitoring, intelligence and investigative agencies can acquire accurate information about one’s location, relationships, opinions, beliefs, political views and a vast amount of other information states conventionally should not supervise (La Rue 2013). 2.2.2 Targeted Electronic Surveillance Instead of loosely scouring the Net for potential wrongdoers or threats to the public interest, this intensive cyber surveillance method is used to monitor each specific target at a time. Unlike mass surveillance, targeted electronic surveillance typically involves a suspect or a specific piece of information. Due to its meticulous features, it allows its operators to go much deeper into a subject’s electronic information than simply online and communications data. In fact, so-called ‘offensive surveillance technologies’ not only allow total access to all information stored in one’s computer and online accounts, but are able to map every single click in a spied device (Cupa 2013; Hosein & palow 2013; La Rue 2013; Stanley & Steinhardt 2003). On the one hand, this surveillance system as most harmful for its qualitatively thorough character, considering that the level of privacy violation is much grater than that experienced with mass surveillance (Hosein & Palow 2013). On the other, however, its specificity and the fact that these intrusions are usually justified by suspicion – reasonable or otherwise – supports the assertions that targeted surveillance is less dangerous to society as a whole when it comes to freedom of speech and privacy protection (MacDonald, Ben-Avie & Carrion 2013). 420 UFRGSMUN | UFRGS Model United Nations The latter argument, however, is based on two inaccurate assumptions. The first is the notion that these highly invasive software are always deliberately operated. Yet, they can be unknowingly installed by their very subjects as a virus alongside another program or even disguised as a completely different software. For example, in August 2012, a program called AntiHacker, which declared to protect computers from invasion, was discovered in Syria. Once installed the program actually ran a version of DarkComet, a software that can activate webcams, record keystrokes and retrieve passwords from the victim’s device (RWB 2013, 33). Secondly, that argument would only be valid if government surveillance was always accurately proportionate, judicially warranted and based on concrete legitimate suspicions. But as access to these software rises and their costs decrease, their use becomes worryingly arbitrary (La Rue 2013; PCLOB 2014; RWB 2013; Wagner 2012). This is just one of the increasingly popular electronic surveillance techniques commonly referred to as Trojan horse software (Fuchs 2012). These intrusion programs are able to attain remote access to computers and smartphones through backdoors or system vulnerabilities. In other words, operators can not only extract any stored information, but can also monitor and control all activities performed in the device, including tracking keystrokes and activating cameras and microphones already attached to it (Hosein & Palow 2013, 1080). Spread around the globe, there are numerous companies in the billionaire market of surveillance that produce this kind of technology, such as Gamma International (United Kingdom), Hacking Team (Italy), Amesys (France), ZTE Corp (China), Trovicor (formerly known as Nokia Siemens Networks; Germany/ Sweden) and Blue Coat (United States). All of the aforementioned companies have reportedly engaged in business or at least verifiably negotiated with governments of several countries7 (Hosei & Palow 2013, Fuchs 2012, RWB 2013, Wagner 2012). 2.3 STATE AND CORPORATIVE PRACTICES 2.3.1 State Internet Surveillance The purposes and modalities of employment of cyber surveillance technologies take numerous forms. In the public sphere it can be related to issues of public health, public safety, national security, economic protection, all the way to media censorship and political repression (Hosein & Pallow 2013; RWB 2013). Although 7 Egypt (Gamma International), Libya (Amesys, ZTE Corp), Tunisia (Trovicor, Blue Coat), Syria (Blue Coat), Burma (Blue Coat), Iran (Trovicor), Germany (Trovicor), United Arab Emirates (Hacking Team) and China (Blue Coat). 421 World Summit on the Information Society Forum some justifications are more reasonable than others, given the considerable power states – and particularly intelligence agencies – hold in our modern society, no cyber surveillance operation is excused from scrutiny. Illustratively, a software that allows authorities to uncover the identity of a child pornographer and make a lawful arrest may do the same to a dissident journalist in a dictatorial regime, resulting in their apprehension and execution (Tokson 2009, 2129-58; RWB 2013, 45). Intelligence agencies hold power that is ultimately directed at protecting social values and interests, and precisely for being backed by this raison d’être have great potential to violate them. In the words of Bruneau and Matei (2008, 915) “[a]ny armed force strong enough to defend a country is also strong enough to take it over”. Transparency is key to ensure that the ends to which means such as surveillance aspire are proportionate, justifiable, and thus welcome by civilians, paradoxically, secrecy may be indispensable for such institutions to work efficiently and effectively (Cepik 2001). The dilemma of efficiency versus oversight in democratic societies sustains that institutions such as governmental intelligence agencies must operate under supervision while calling for secrecy to operate efficiently8 (Bruneau 2008). States employ these confidential strategies through cyber surveillance in a determined set of circumstances and for specific purposes. Formally, these are usually: during criminal investigations, for the preservation of national security, public health management (particularly control of infectious diseased), for the protection of public order and morals and for governmental intelligence and strategic purposes (UK 2012; UNESCO 2014; European Commission 2011). However, the vague significance of some of these grounds allow surveillance practices that, in a more meticulous perspective, lack in necessity and proportionality. Although privacy law in international legal instruments is often broad and, thus, rather delicate, according to customary international law, the violation of privacy usually requires certain circumstantial prerequisites, which may or may not be in accordance with domestic legislations. For instance, there is the question of control over the controllers. A surveillance operation would ideally only be admissible if the endeavor and the actors performing it are being supervised by an independent, equitable authority9 (Boraz & Bruneau 2006; Bygrave 1998). In criminal investigations, the lawful and typical use of cyber surveillance firstly, requires judicial order and secondly, is applied individually to the suspect in search of a particular piece of information. In such cases, there must be a compelling reason to believe the procedure is valuable and even indispensable (European Commission 8 Cepik (2003) argues that accountability mechanisms and external oversight are essential to legitimate classified operations of such organisms. While Luban (1996) reasons that the justification for secretive activities must be publicly declarable as to legitimately sustain these practices. 9 Legal provisions for violation of the right to privacy will be more thoroughly discussed further in this session. 422 UFRGSMUN | UFRGS Model United Nations 2011, 23). Hence, Internet surveillance for the purpose of criminal investigations should be essentially targeted ones. Nevertheless, random and extensive operations involving third-parties and searches for unspecific data are increasingly common. Moreover, the judicial oversight has become dispensable, not only because procuring it is time-consuming, but also for its undesirably – from an investigative perspective – rigorous criteria for granting warrants (Mihr 2013). Considering the requirements for lawful surveillance during criminal investigations – proportionality, necessity, precision – as they are understood by international customary law, as well as by mainstream interpretations of international treaties such as the UDHR and the ICCPR, mass network surveillance would seem unemployable, considering that an enormous amount of subjects and information are examined, most of which are useless for crime detection and prevention (Kerr 2003). But the fact is that these practices are used by investigative agencies in search of information that might lead to legitimate arrests. However effective and beneficial mass surveillance technologies might be for public safety, it cannot be ignores that they compromise the right to privacy of thousands of individuals, “subjecting entire population[s] to routine criminal investigation” (Walter-Echols 2009, 31). Extensive cyber surveillance methods find greater admissibility under national security and moral protection purposes, mainly because of the topics’ broad nature (Heywood 2011, 296). From identifying and defusing terrorist activities to persecuting ideological dissidents, - a practice which is not restricted to authoritarian regimes – the cyber surveillance operations grounded on national security take many different shapes and underlying motivations. For instance, communications and metadata (a.k.a. ‘communications data’) have been systematically examined by national security agencies around the globe under suspicion of threat to national security in diverse ways (terrorist attack, espionage, fraud, disclosure of classified information etc.). Yet, after being collected and analyzed, these data are often retained for no specific reason or period of time, a practice which clearly violates a number of local, regional and global principles and norms that regulate the right to private life (UK 2012; Wagner 2012; RWB 2013; Cupa 2013; European Commission 2011; HRW 2014). A recurrent dilemma brought about by domestic national security surveillance lies on the grounds for suspicion and the surveillance operations carried out because of them. The focus of such type of surveillance is usually individuals with seemingly “unorthodox political beliefs” (Hosein & Palow 2013, 1103). Meaning that those who are most frequently targeted for official cyber surveillance supported by national security justifications (i.e. political dissidents) are precisely the ones whose right to privacy should be most rigorously protected, once these subjects’ political subversion is not only essential to democracy, but may put them in a vulnerable position in the face of governmental power (Hosein & Palow 2013, 1104). Originally used in the monitoring and notification of infectious diseases, 423 World Summit on the Information Society Forum surveillance as means to preserve public health is older than Internet itself. But with the emergence of ICT its uses have broadened and with it the potential for overstepping private information. Today, health-related surveillance technology are most notably related to electronic patients’ records (EPRs) and genetic research – besides its inceptive purpose (Graham &Wood 2003, 240). Data collected and stored by EPRs is highly valuable for fast and accurate diagnosis and treatment. They comprise vast databases with patients’ medical history, medication, test results, procedures and therapies, not only facilitating individual patient care, but fueling medical intelligence to an unprecedented degree (van der Ploeg 2002, 62). However, this massive accumulation of personal information is not only beneficial, considering that access to it may not be restricted to public healthcare bodies, reaching private ones – such as insurance companies – as well as other public spheres – such as law enforcement agencies – for purposes far beyond health promotion (Hu 2013). For Stanley & Steinhardt, this is where major worries about genetics assortment lie. Firstly, insurance companies with access to customers genetic information may grossly affect what they’re charged and even if the service will be provided to them, “with the result that a certain proportion of the population could become uninsurable”. Secondly, genetics-based employment discrimination is already on the rise, with employers searching for the healthiest most capable employees (Stanley & Steinhardt 2003, 5). Finally and most tangible is the use of medically stored genetic information for law enforcement purposes. The pressure to integrate, for example, medical and police databases for law enforcement purposes will become more and more intense as forensic science improves and with the increasing popularity of biocriminology and the pressure for pre-emptive law enforcement policies such as DNA screening (Graham & Wood 2003, 241). Cyber surveillance may also be associated with intelligence and strategic activities. However, due to the nebulosity of these matters, when surveillance operations related to them are publicized – which is rarely the case – they are formally put under the national security umbrella. Such practices commonly include cyber espionage10 and cyber warfare11 and have been gravely addressed by, for example, the United Nations Security Council Working Group Report and the United Nations General Assembly in 2013 (Mihr 2013). 10 Described by Anja Mihr (2013, 18) as the “stealing of national intelligences or industrial data stored in digital formats on computers and IT networks.” 11 Namely the “combination of technical warfare instruments in the cyberspace” performed by states or international organizations through military or intelligence agencies (Mihr 2013, 17). 424 UFRGSMUN | UFRGS Model United Nations Data collected by ISPs arouses the interest of both private and public bodies. The most notable use by the first is, as mentioned above, in consumers marketing (Lyon 2010). Companies buy users’ personal information “to get certain behaviors, preferences, usages, interests and choices of customers in order to […] supply them with targeted advertisements” (Allmer 2011, 580). This extensive range of private information and metadata can also be sold to surveillance enterprises or directly to public entities. In fact, states normally do not have to purchase this data from ISPs considering they can acquire them through simple requests, as aforementioned (MacDonald, Ben-Avie & Carrion 2013). The real core of the information market, however, is represented by the surveillance corporations that master the business of data interception and collection as an end in itself (Lyon 2003). Other private institutions take advantage of the services provided by these companies, but their number one customer is still in the public sphere. Virtually all of the national intelligence agencies around the globe which conduct cyber surveillance operations are fueled by the expanding market of surveillance technologies. If states themselves cannot always be relied upon to manage cyber surveillance appropriately and in accordance with human rights standards, than the control held by the private sector over such technologies are considerably unsettling (Wagner 2012). Proposed regulation of these companies’ practices comes from basically two directions. The first is the alleged commitment some enterprises express toward selfregulation, which translates to a voiced resistance to sell their services to authoritarian regimes that, ironically, constitute a menace to human rights protection12 (Laidlaw 2012). Secondly and most naturally, the pressure for state-regulation grows with the rapid technological developments the surveillance industry brings about. Currently, there is still virtually no domestic or international regulation to restrain the industry’s activities (La Rue 2013, 20). 2.4 HUMAN RIGHTS PROTECTION Considering cyber surveillance is also a state practice, it is assumed it exists for the purpose of populations’ well-being. As previously stated, state surveillance aims at reinforcing a series of interests that contribute to the public good and, consequently, to human rights preservation and promotion. This is not always so easily accomplished, as the realization of some rights tend to compete with others. Moreover, non-state practices also threaten said fulfillment, seeing as private 12 In spite of the fact that many of these companies have showed such reluctance in engaging in buisiness with certain controversial regimes, many authors have questioned and even more reports have contradicted those positions. See Morozov 2011. 425 World Summit on the Information Society Forum companies also have interests to protect. If the importance and usefulness of cyber surveillance is to be recognized, an analysis from a human rights perspective is due. 2.4.1 Right to Privacy Information technologies have laid out an overwhelming number of possibilities for states to carry out investigations – both official and unofficial – in a much more effortless fashion than ever before. That combined with the recurrent breach of privacy protecting laws in the cyber world may normalize the use of surveillance and data retention technologies in a way that disregards the right to privacy (Brown & Korff 2009), designated in Article 12 of the Universal Declaration of Human Rights (United Nations 1948) and in Article 17 of the International Covenant on Civil and Political Rights (United Nations 1966). Although global legal standards regarding restriction of the right to privacy are generally rather vague – mentioning “unlawful”, “arbitrary” and “abusive” interference – (UDHR 1948, art. 12; ICCPR 1966, art. 17), on practice, the requirements for such restrictions comply with those of the European Convention on Human Rights, which states: There shall be no interference by a public authority with the exercise of this right except such as is in accordance with the law and is necessary in a democratic society in the interests of national security, public safety or the economic well-being of the country, for the prevention of disorder or crime, for the protection of health or morals, or for the protection of the rights and freedoms of others (ECHR 2004; art. 8 (2)). Although still not particularly well-defined, the premises for exemption of the right to privacy are more clearly outlined in the ECHR. However, as mentioned before, the imprecision of terms such as “national security”, “public safety” and “protection of morals”, to mention a few, give grounds for cyber surveillance operations that are often disproportionate in regard to the human rights violations they bring about (UNESCO 2013). Traditionally it is expected that privacy violations conducted by the state are previously authorized by a judicial or executive organ. This assumption was adapted from legal standards of privacy relating to correspondence and telephonic communication (Richards 2012, 4). On account of the notable differences between these classic means of communication and the Internet, existing regulations that should be applicable to all of these vehicles commonly fall short on protecting this fundamental right in the context of ICT (Brown & Korff 2009). Additionally, since surveillance was initially regulated, two requirements for its 426 UFRGSMUN | UFRGS Model United Nations use were laid out: accountability and transparency. The first relates to information data subjects13 must have about which organs have access to their personal data, which of these, specifically, and for what purposes. The second designates the obligation states have to keep society well-informed about what are the types and purposes of surveillance techniques to which they might be subjected (Fuchs 2012, Lyon 2007). These principles are encompassed by a more specific and exhaustive rule of surveillance, which is prohibition of secrecy. According to international standards, surveillance must never be concealed from its subject. As Richards (2012, 3) bluntly states “secret surveillance is illegitimate”. Yet, privacy-disrupting cyber surveillance operations are continuously undertaken by both the public and the private sector without the slightest awareness of their targets (La Rue 2013). 2.4.2 Freedom of Expression The violation of the right to privacy is not exhaustive regarding compliance with human rights. Privacy protection relates to freedom of expression in various, and even contrasting ways (UNESCO 2012). By depriving individuals of their privacy and even anonymity before uninvolved third parties, cyber surveillance agents are also hindering freedom of expression. Expressing one’s thoughts, especially through communications technologies, requires trust in the recipient and the medium. If that trust is broken for fear of having one’s communications intercepted, sharing information and expressing one’s mind become immensely restricted (UNESCO 2012; MacDonald, Ben-Avie & Carrion 2013; Laidlaw 2012; LaRue 2013) . On the other hand, the right to privacy may also conflict with and prevent the realization of freedom of expression. Sharing private information acquired by systematic data mining, while possibly violating the privacy of the data subjects, may be considered of essential public interest, vindicating the right to disclose this data and exercise one’s right to freedom of expression (Castells 2010). When such information is obtained through clearly unlawful means, the overpowering of privacy in relation to freedom of expression is somewhat easily defensible. However, when, for instance, publicly shared personal data is collected, analyzed and published the antagonism between freedom of expression and privacy becomes blurred and more debatable. Regulation of these principles and their interrelations is key to ensure that human rights are protected to the possibly fullest, 13 Individuals subjected to data interception, collection or analysis (Brown & Korff 2009). 427 World Summit on the Information Society Forum [...]recognizing that the exercise of the right to privacy is an essential requirement for the realization of the right to freedom of expression and to hold opinions without interference, and one of the foundations of a democratic society.(UNGA 2013). 3 PREVIOUS INTERNATIONAL ACTION In 2013 the world saw a decisive moment in the issue of cyber surveillance. Major revelations about state and non-state practices related to online data interception surfaced, sparking debates already underway about an alternative attitude toward Internet governance. The notorious Snowden case (further examined below), at least indirectly, brought to light other exploits in the world of cyber surveillance among the international community. Thus, pressing discussions about a global, pluralized Internet arose and efforts for the improvement of privacy protection standards in the cyber world eventually became unavoidable. The International Covenant on Civil and Political Rights (ICCPR) of 1966, in its Article 17, makes provisions for the protection of the right to privacy, but it wasn’t until 1988 that the Human Rights Council issued a General Comment regarding the interpretation of this article in specific regard to data protection. The Comment states that authorities should only call for individuals’ personal information if it’s “essential in the interests of society as understood under the Covenant”, that such gathering of information should always be regulated by law, and that “individuals should have the right to ascertain […] what personal data is stored […] and for what purposes” and which authorities hold control over these files, among other requirements (UNHRC 1988). In 2011, the European Court of Human Rights issued a report on the Court’s Internet-related case-law. It was only later that the documents would come to be regarded as a groundbreaking submission for international legal frameworks on privacy protection on the Internet (Mihr 2013). The report argues that there is a positive obligation14 by states to protect individuals’ personal data from interference, being by third parties or by the state itself. Moreover, it asserts that “personal information stored in the interests of national security” must be accompanied by “adequate and effective guarantees against abuse by the State” (ECHR 2011, 7). Finally, on the topic of secret surveillance, the Court observes that “system[s] of secret surveillance designed to protect national security entail the risk of undermining or even destroying democracy on the ground of defending it”, but also acknowledges 14 In the sense that states should protect personal data and the right to private life not only by reprimanding unlawful practices of the kind, but by actively ensuring “an effective deterrent against grave acts to a person’s personal data” (ECHR 2011, 7). 428 UFRGSMUN | UFRGS Model United Nations the legality of the practice if adequate safeguards are guaranteed by law to supervise these activities (ECHR 2011, 8). The UNHRC, in its 20th session, affirmed that “the same rights that people have offline must also be protected online” (UNHRC 2012, para. 1). This expression was subsequently repeated by several other documents on the subject, among which, a statement by Reporters Without Borders before the HRC in its 24th session. The organization called for the adoption of the “International Principles on the Application of Human Rights to Communications Surveillance”15. RWB pointed to a shift from surveillance of communications based on the rule of law (in particular legally authorized targeted surveillance based on clear criteria) to mass surveillance through untargeted collection of communications data of ordinary citizens where no lawful grounds for surveillance exist (RWB 2013a, 2). The NGO stated that the set of principles it urged UN Member states to adopt was in total accordance with the reports issued by the Special Rapporteur on the promotion and protection of the right to freedom of opinion and expression, Frank La Rue, in his April 2013 report on state surveillance on the Internet. The report made by the Special Rapporteur identifies and describes cyber surveillance practices around the globe, as well as analyzes numerous countries legal provisions for the protection of online data, ultimately making recommendations concerning private sector regulation, government transparency, effective legal protection, among others (UNGA 2013a). During a meeting held in October 2013, several organizations responsible for the Internet’s technical infrastructure, such as the Internet Corporation for Assigned Names and Numbers (ICANN) and major ICT corporations, met in Uruguay to discuss, among others, questions related to cyber surveillance, finally issuing the Montevideo Statement, which “expressed strong concern over the undermining of the trust and confidence of Internet users globally due to [...] revelations of pervasive monitoring and surveillance” (ICANN 2013). In November 2013, during the 68th meeting of the General Assembly, a resolution was introduced by Brazil and Germany concerning the protection of the right to privacy in the digital age. The document is said to be a cornerstone on the regulation and policing of privacy protection and data interference practices on the Internet (Zilowkowski 2013), calling upon states to review their procedures, practices and legislation regarding the surveillance of 15 A set of principles “developed by [NGOs] Access, Electronic Frontier Foundation and Privacy International” in a “global consultation with international experts in communications surveillance law, policy and technology from civil society, industry and elsewhere” (RWB 2013a, 2) (Available at https:// en.necessaryandproportionate.org/text). 429 World Summit on the Information Society Forum communications, their interception and collection of personal data, including mass surveillance, interception and collection […] (UNGA 2013a). The resolution as well as the heads of states’ presentations represented a trend toward a decentralization of the cyber world, which, since its inception, has been managed, developed and expanded by the United States. This recently forged process of de-Americanization of the Internet can be explained by a variety of different factors. For instance, the leaked information about control the U.S. holds over online data everywhere shone a light over a fact that many suspected, although few were conscious of its significance: the United States – and its companies – are startlingly well-informed of what flows on the Internet. This insurgence also called for an overdue worldwide democratization and diversification of the Internet through the Global Multistakeholder Meeting on the Future of the Internet Governance held in São Paulo to discuss the new, multipolarized directions of Internet governance. During the conference, also known as NETmundial, stakeholders from various relevant groups (state agents, companies, civil society) gathered to discuss the future of the Internet in many of its aspects, particularly stating that surveillance “undermines trust in the Internet and trust in the Internet governance ecosystem” and calling for further dialogue on the topic (NETmundial 2014). 4 BLOC POSITIONS The European Union holds in its jurisdiction a significant number of intelligence companies that develop surveillance-oriented software and, on that account, has regulated some private practices in this sector. For instance, in 2011 the European Parliament passed a resolution banning European companies from providing ICT systems to countries which the EU fears might employ these technologies for purposes contrary to human rights standards16 (Fuchs 2012). Moreover, Internet companies in Europe are also prohibited from providing personal users’ data to nations with privacy protection policies regarded as “inadequate” by the organization17 (Stanley & Steinhardt 2003, 15). The European Commission is also following the shift in Internet dominance which aims to decentralize the Internet’s structural core. As a personal advocate for the multipolarization of the Internet, the vice-president of the EC, Neelie Kroes stated in her letter to the 50th ICANN High Level Governmental Meeting, held in June 2014, that “it is our political responsibility to ensure that the governance 16 Namely Argentina, China, Croatia, India, Russia, South Africa, South Korea, Turkey and Ukraine. 17 A typification commonly applied to non-Western countries, but which also include the United States. 430 UFRGSMUN | UFRGS Model United Nations of the Internet is open and inclusive of all stakeholders, compliant with human rights and respectful to the rule of law” (Kroes 2014). In March 2014, the European parliament supported a resolution suspending a data protection agreement between Europe and the United States that allows “U.S. firms [to] self-certify as being in compliance with EU privacy law18” (Cleland 2014). In April 2014, the controversial Data Retention Directive (approved by the European Commission in 2006) was declared invalid by the European Court of Justice after being questioned by constitutional courts across Europe – most notably Germany and Sweden. The Directive’s content, which was being challenged for its incongruity with Article 8 of the European Convention on Human Rights, included mandates for indiscriminate metadata retention for time periods not inferior to six months and not superior to two years for possible future criminal investigations (ECJ 2014). Germany has publicly expressed its concerns over American-centered information and communication networks and the contribution of this phenomenon to the scandalous revelations made in 2013 regarding the American National Security Agency (NSA) and the surveillance power it holds globally19 (Brown 2010). Thus, the country has been promoting the idea of a “national Internet”, which studies how their “citizens’ online information can be stored on domestic servers” – a position also held by Brazil, China and Russia (Jiang & Okamoto 2014; Aaltola 2013). Nevertheless, Germany reportedly makes use of various electronic monitoring programs mostly for the purpose of criminal investigation. In October 2011, the use of a Trojan horse program code-named R2D2 came to light, and a subsequent discussion over its legality and proportionate use arose (CCC 2011). Switzerland was also accredited for the employment of the R2D2 in investigations carried out by national security agencies (Cupa 2013, 419). Swiss legislation requires ISPs to keep communication records for at least six months, and the apprehension of this data by national authorities is only granted by court order (RWB 2003b, 111). In December, 2013, weeks after making statements reproaching American surveillance schemes, France passed legislation that allows for real-time online data interception by several public officials (Willsher 2013; Segura 2013). Due to their knowledge-based society and economy, Sweden and Norway represent one of the most notable regions when it comes to online activity and dependence. Added to the countries’ frequently unsurpassable – even by the United States – levels of connectivity and innovation, their geographical position is one of the factors that makes them key actors in the ICT international setting (Giacomello 2005). For instance, most of the Russian cyber flows to the West, particularly the United States, passes through submarine cables in the Baltic Sea, giving the Scandinavian 18 EU Directive 95/46/EC on the protection of personal data. 19 Discussed further in this section. 431 World Summit on the Information Society Forum nations great potential for data interception as well as, and thus, loading them with significant responsibility for data and privacy protection (Aaltola 2013). The United Kingdom was one of the initial sponsors of the Data Retention Directive and, as such, has internal regulation that mandates ISPs to retain user communications data for at least one year (Brown 2010, 95). The British government argues that it is the indiscriminate use of communications data, rather than its storage, that threatens the efficacy of Article 8 of the ECHR (Brown 2010, 102). However, the legislation that outlines the requirements for national authorities to access collected data is also a point of controversy. The Regulation of Investigatory Powers Act of 2000 allows over 200 governmental agencies to retrieve metadata of online activities without warrants or court orders, but “using a self-certified administrative notice” (La Rue 2013, 15; Brown 2010, 102). Furthermore, along with the UK, the United States, Canada, Australia and New Zealand make up the “Five Eyes” arrangement, which runs the Echelon surveillance system, monitoring communication flows around the globe through data-mining. Each of the five national intelligence agencies oversees a designated region, examining political, military, diplomatic and economic content of communications (Che 2007; Lyon 2006; Ziolkowski 2013, 440). Nonetheless, Echelon is only one of the American surveillance programs that focused media and public attention in 2013, when other exploits of the National Security Agency came to light through the unauthorized disclosures of one of its contractors, Edward Snowden. Snowden exposed – among other, telephone-based surveillance operations – a program run by the NSA called Prism, which targeted individuals’ electronic communications, such as e-mails and phone calls, through filter taps placed in fiber-optic cables throughout the world. The program was originally authorized by the Foreign Intelligence Surveillance Court, but was subsequently changed and operated outside of the limits set forth by the FISC. For instance, only non-US persons believed to be located outside of the American territory were to be targeted, but these provisions were often understatedly disregarded (USPCLOB 2014; Ziolkowski 2013; Aaltola 2013). On March 14, 2014, the U.S. Commerce Department’s National Telecommunications and Information Administration (NTIA) stated its intentions of “transition[ing] key Internet domain name functions to the global multistakeholder community” (NTIA 2014). Particularly, the NTIA intends to entrust the Internet Corporation for Assigned Names and Numbers (ICANN) with the “root-zonefile”20 by October 2015. With this, the American administration hoped to show its apparent intentions to loosen its hold on the Internet’s core in contribution to a global Internet community (Cleland 2014; NTIA 2014). 20 “The essential core-addressing database that the Internet depends upon to ensure any Internetaddressed device can link to any other Internet-addressed device.” (Cleland 2014). 432 UFRGSMUN | UFRGS Model United Nations Russia’s recent asylum grant to whistleblower Edward Snowden was officially grounded on the country’s voiced commitment to the protection of privacy and freedom of expression (HRW 2014). Contrastingly, since 2007, the Russian government has been increasingly employing and investing in its system of electronic communications intervention, the System of Operative-Investigative Measures (SORM), run by its Federal Security Service (FSB). Every ISP in the country is physically linked to the FSB by underground cables, and although a court order is necessary for the agency to monitor online activity, the warrant does not have to be presented to the ISPs, but to a supervisors inside the FSB itself. Whether for fear of a US-dominated Internet and American surveillance programs, which the Russian government argues threatens their nationals’ online privacy, or for aspirations of greater supervision over their online activities, the country has been bringing ICT inwards and promoting a campaign for Internet de-globalization21 (Soldatov & Borogan 2013; Jiang & Okamoto 2014). Furthermore, SORM has also been imported by other Commonwealth of Independent States members. As one of the system’s employers, Ukraine has also installed a Russian social network monitoring program, the so-called Semantic Archive (Soldatov & Borogan 2013, 30). Ukraine’s National Security Council was also criticized by local human rights activists for its lack of transparency. The Council allegedly controls around 80% of the country’s cyber traffic and has been reported to only grant licenses to Internet Service Providers that agreed to install the agency’s technological system that allows it to keep these supervision operations (Ligabo 2008, 12). China’s “great firewall” has long been the country’s reliance when it comes to information and communication restriction on the Internet. The Chinese firewall allows authorities to block foreign websites and restrict online content by word filtering. As the number of Internet users in the country rises (42,1% in 2013), the monitoring of online activity, carried out by at least five governmental bodies, grows harder (RWB 2013b). With the largest population of netizens in the globe, the Chinese struggles to keep control of its cyber space at the same time that they are faced with the need to keep it open to the outside, particularly for the sake of business and contact between Chinese citizens and emigrants (Yang 2013). Lewis (2006) argues that, with the swelling number of users and the rise of social media, control over online content decreases and the Chinese firewall, which was once enough to keep their netizens within reasonable boundaries, is now falling short on protecting individuals from undesirable content. Therefore, the government’s solution has been, in the last few years, to gradually complement the nation’s Internet control 21 On July 31st 2014, Prime Minister Dmitry Medvedev signed a decree that makes it mandatory for individuals to provide identification whenever accessing public WiFi hotspots. Companies providing the services are required to register its users. 433 World Summit on the Information Society Forum apparatus (previously greatly operated by humans) with surveillance software, in it’s majority, bought from both Chinese and Western (American in tis majority) intelligence companies (RWB 2013; Lewis 2006, Mueller, Kuhen & Santoso 2011). Furthermore, in 2013 Mandiant Corporation, an American cyber security consultant, uncovered a Chinese hacking group directly linked to the People’s Liberation Army. The cyber espionage scheme APT1, profiled by Mandiant, was found to have infiltrated over 100 American companies (141 across the Western world), keeping business records by the terabyte and with attacks lasting as long as four years (Mandiant 2013). Contrastingly, an outraged response to the American surveillance system disclosed in 2013 was manifested on the 20th of June 2014 when China published a book entitled “How is the United States Surveilling China”. The book is said to describe American surveillance schemes on China and it’s leaders and several other countries and was compiled by China’s Internet Media Research Centre (Xihnua 2014). With a remarkably high rate of communications data requests22, the Republic of Korea was classified by the 2013 “Freedom on the net” report23 as partly free in regard to its cyber space (La Rue 2013, 12; Freedom House 2013). After the 2001 spying scandal performed on Japanese subjects by the intelligence network Echelon, Japan expanded its then feeble Internet monitoring framework. Although some insist on the precedence of Japan’s link to the ‘Five Eyes’ over this incident, the fact is that the country has been reportedly engaging in surveillance activities with this coalition since, at the least, 2001 (RWB 2003, 70; Giacomello 2005, 74). The Philippines has state-of-the-art criminal legislation concerning a range of cyber crimes, including data interception, alteration and theft and Internet interference and sabotage. Reporters Without Borders drew attention to the Cyber Crime Prevention Act 2012, identifying it as a hindrance to the realization of freedom of expression in the Philippine web (RWB 2013). Malaysia, on the other hand, has overall weak legal oversight on the Internet according to NGOs and other international organizations (RWB 2010; ASPI 2014). Moreover, cyber regulation that does exist in the country has been reported to have “the potential to allow government to strongly regulate information within the country” (ASPI 2014, 33). Cambodia has been addressed by several NGOs for its weak privacy and freedom of expression legislation. Moreover, the government has expressed its aspirations to combat the abuse of freedom of expression on the Internet and stated that its online privacy policies aim at preventing terrorism and trans-boundary crimes as well as protecting national security and social order (HRW 2013). In Laos 22 - 37 million requests per year in a country with a population of 50 million. 23 Survey conducted by the NGO Freedom House analyzing 60 countries’ level of freedom on the Internet. 434 UFRGSMUN | UFRGS Model United Nations the government controls domestic ISPs as well as the content of online publications. Although the country legally protects Laotians privacy on the Internet, they are prohibited from “publishing information that could damage the country’s unity and integrity” and there have been numerous complaints of e-mails being intercepted or even edited before reaching their destination (Thierer & Crews 2003, 6). Websites like Google and Facebook have issued figures that put India only behind the United States in number of requests for personal user information (HRW 2013, 337). Nevertheless, these numbers are bound to decrease for in 2013 the country got its Central Monitoring System underway. The system allows Indian authorities to intercept and store communications data directly from ISPs (as well as Telecommunication Service Providers) without a court order or warrant or even having to request companies fort such information (India 2013; Xynou 2013; Moody 2013). Pakistan has been addressed by local as well as international NGOs regarding its mass cyber surveillance program on civilians, especially after the joint statement, issued on behalf of other nations24, during the 24th meeting of the United Nations Human Rights Committee (Privacy International 2013; Freedom Network 2013; Bytes for All 2013). The pronouncement called for more rigorous Internet regulation by states as to better secure privacy protection. Criticism to the country’s standpoint is founded on worries about Pakistan’s ambition to enhance its surveillance capabilities, which has been verified by research institutions and Pakistani civil society. In a Citizen Lab report, researchers have found that the country has installed surveillance and remote control software purchased from Canadian “web threat manager” Netsweeper (Citizen Lab 2013). Iran has been conspicuously monitoring Iranian cyber space since it went online in the 1990s. Although in the last few years many Iranian ISPs have been privatized, the government still holds tight control over its population’s Internet activities (Freedom House 2012; RWB 2013). Furthermore, the country is developing its own search engine as part of an ambitious plan of creating so-called “Halal Internet”, Iran’s own Intranet, which, given the government’s total control over the network, would “allow large-scale surveillance and the systematic elimination of dissent (RWB 2013, 25). In Saudi Arabia, all 30 ISPs are connected to the country’s Internet monitoring organ for the purpose of examining content for “offensive or sacrilegious material”. This link compromises not only Saudi individuals’ freedom of expression, but also gives the Saudi government broad access to communications data and even content, jeopardizing the right to privacy in the country (Thierer & Crews 2003, 227). Saudi authorities have justified their close watch over Internet activity as a legal measure 24 Cuba, Venezuela, Zimbabwe, Uganda, Ecuador, Russia, Indonesia, Iran, and China. 435 World Summit on the Information Society Forum for combating radical ideology and extremism in the kingdom (Ansary 2008). In the United Arab Emirates, evidence of the employment of electronic monitoring devices by at least three major online security companies has been found25 (RWB 2013). The country admittedly uses Internet filtering software on political and religious content. Ultimately, there is no legal protection for users, rather, “Internet misuse” is criminalized (OpenNet 2005). Although Israel hosts many companies that provide electronic data monitoring software around the world, its government’s alleged cyber surveillance venture – if it exists – is yet to be uncovered. However, the country’s law on data protection, the Information and Technology Authority, has been praised for its regular updates concerning online privacy protection (Sage 2013). Although, human rights watchdogs and NGOs have often regarded netizens in South Africa as overall free in the cyber world (RWB 2005; Freedom House 2013), recent reports have criticized the country’s communication interception regulatory framework, RICA26, describing it as being as invasive as the American monitoring apparatus (Hutchison 2013; De Wet 2013). Nigeria has purchased intelligence devices from both Blue Coat and Israeli defense company Elbit Systems with the intent of implementing a comprehensive Internet surveillance facility by 2016 (RWB 2013, 8; Freedom House 2013). As for Rwanda, the country’s cyberspace is considered “partly free” by the NGO Freedom House, which has addressed recently passed legislation that, although aimed at protecting online media and journalists, presents a threat to freedom of expression online, by allowing high ranking officials to intercept and monitor online communications (Freedom House 2013). Most notably expressed through President Rousseff’s statement after the reports of mass surveillance carried out by the United States and the United Kingdom on Brazilian subjects (UNGA 2013b; Boadle 2013), Brazil positioned itself as a leading actor in the “development of a global Internet governance mechanism to protect the right to privacy” (HRW 2014, 223). Along with Germany, the country proposed, in November 2013, a resolution in the United Nations General Assembly which set forth guidelines for privacy protection, inspection of communications and personal data collection online and their regulation (UNGA 2013b). Moreover, Brazil’s recently sanctioned Internet civil framework, the so-called “Marco Civil”, represents the country’s commitment to human rights protection on the Internet, establishing the roles and responsibilities of actors such as the state, ISPs and users, regulating personal data protection and safeguarding Net Neutrality, privacy and the free flow of information online (RWB 2013, 40; Brazil 2014). 25 Namely Blue Coat, Gamma International and Hacking Team. 26 Acronym of Regulation of Interception of Communication and Provision of CommunicationRelated Information Act 436 UFRGSMUN | UFRGS Model United Nations Such as is the case with President Rousseff and other Brazilian political leaders, communication records of authorities in Mexico were also found in the NSA records, including those of president Enrique Peña Nieto, who condemned the unlawful surveillance operations (Ziolkowski 2013, 445-449). A stand regarding the incident also came from Argentina and Venezuela. Although the latter was identified by a study that located devices by American online security company Blue Coat which had surveillance and tracking potential (RWB 2013, 28). Lastly, Uruguay has been commended for its freedom of expression and privacy protection legal framework and its overall institutional competence for guaranteeing these rights online (Freedom House 2013; US 2013). QUESTIONS TO PONDER 1. How can binding legal frameworks be established internationally for the protection of the right to privacy and freedom of expression in face of cyber surveillance practices? 2. How can a balance be established between national security and public order and privacy protection on the Internet? 3. How can the international community protect civilians from surveillance in the digital age? 4. What are legitimate circumstances in which state and private actors can employ data interception mechanisms? 5. To what extent can states acceptably carry out cyber surveillance activities extraterritorially? REFERENCES Aaltola, Mika. “Finland should aim to be a cyber connector,” FIIA Comment (The Finnish Institute of International Affairs), 2013. Adams, Andrew A.; Murata, Kiyoshi and Orito, Yohko. “The Development of Japanese Data Protection,” Policy & Internet 2(2): 95-126, 2010. Allmer, Thomas. “Critical Surveillance Studies in the Information Society,” TripleC 9(2):566-592, 2011. 437 World Summit on the Information Society Forum Bennett, Colin J.; Clement, Andrew and Milberry, Kate. “Editorial: Introduction to Cyber-Surveillance,” Surveillance & Society 9(4): 339-347, 2012. Boadle, Anthony. “Brazil’s Rousseff calls off state visit to U.S. over spying.,” Reuters.com, September 17, 2013. http://www.reuters.com/article/2013/09/17/ us-usa-security-snowden-brazil-idUSBRE98G0VW20130917. Boyle, James. “Foucault in Cyberspace: Surveillance, Sovereignty, and Hardwired Censors,” University of Cincinnati Law Review 66(1997): 177-204. Brazil, Law n. 12.965, 23 April 2014 (available at http://www.planalto.gov.br/ ccivil_03/_ato2011-2014/2014/lei/l12965.htm). Brown, Ian. “Communications Data Retention in an Evolving Internet,” International Journal of Law and Information Technology 19(2): 95-109, 2010. Brown, Ian and Korff, Douwe. “Terrorism and the Proportionality of Internet Surveillance,” European Journal of Criminology 6(2): 119-134, 2009. Castells, Manuel. “Communication, Power and Counter-power in the Network Society,” International Journal of Communication (2007): 238 – 266. Castells, Manuel. The Rise of The Network Society: The Information Age: Economy, Society and Culture (New York: Wiley, 2000). Castells, Manuel. The Power of Identity (Chichester: Blackwell, 2010 (1997)). Che, Eliot. “Securing a Network Society Cyber-Terrorism, International Cooperation and Transnational Surveillance,” Research Institute for European and American Studies Research Paper No. 113, 2007. Chen, Hsinchun and Wang, Fei-Yue. “Artificial Intelligence for Homeland Security,” IEE Intelligent Systems, September/October 2005. Cleland, Scott. “Accelarating the De-Americanization of the Internet.” DailyCaller.com, Marc 16, 2014, http://dailycaller.com/2014/03/16/accelerating-the-de-americanization-of-the-internet/ Cupa, Basil. “Trojan Horse Resurrected: On the Legality of the Use of Government Spyware (Govware).” Living in Surveillance Societies: ‘The State of Surveillance’, 419-428 (2013). De Cew, Judith. Privacy. (Stanford University: Edward N. Zalta, 2013). http://plato.stanford.edu/archives/fall2013/entries/privacy/ (accessed 26 April 2014) 438 UFRGSMUN | UFRGS Model United Nations De Wet, Phillip. “Spying far worse in South Africa than the US,” MG.co.za, June 13, 2013. http://mg.co.za/article/2013-06-14-00-spying-far-worse-in-south-africa ECHR (European Court of Human Rights). Internet: case-law of the European Court of Human Rights. 2011. European Court of Justice (ECJ). “The Court of Justice declares the Data Retention Directive to be invalid” Press Release (2014). European Union. “Directive 2006/24/EC of the European Parliament and the Council,” Official Journal of the European Union, 2006. Foucault, Michel. Discipline and Punishment (New York: Random House, 1977). European Commission. Evaluation report on the Data Retention Directive (Brussels: Directive 2006/24/EC, 2011). Fiset, Louis. “Return to Sender: U.S Censorship of Enemy Aalien Mail in World War II,” Prologue Magazine, 2001. Fuchs, Christian. “How Can Surveillance Be Defined?” The Internet & Surveillance Research Paper Series, 2010. Fuchs, Christian. “Implications of Deep packet Inspection (DPI) Internet Surveillance,” The Privacy & Security Research Paper Series 1, 2012. Gellman, Robert. Fair Information Practices: A Basic History (Washington: Robert Gellman, 2014). http://www.bobgellman.com/rg-docs/rg-FIPShistory.pdf. (accessed 02 May 2014). Giacomello, Giampiero. National Governments and Control of the Internet (Oxon: Routledge, 2005). Goldsmith, Jack and Wu, Tim. Who Controls the Internet? Illusions of a Borderless World (Oxford: Oxford University Press, 2006). Graham, Stephen and Wood, David. “Digitizing Surveillance: Categorization, Space, Inequality,” Critical Social Policy 23(2): 227-248, 2003. Hope, Dunstan Allison. Protecting Human Rights in the Digital Age. BSR, 2011. Hosein, Gus and Palow, Caroline Wilson. “Modern Safeguards for Modern Surveillance: An Analysis of Innovations in Communications Surveillance Techniques,” Ohio State Law Journal 74(6): 1071-1104, 2013. HRW (Human Rights Watch). World Report 2013 (New York: Humans Rights Watch, 2014). 439 World Summit on the Information Society Forum Hu, Margaret. “Biometric ID Cybersurveillance,” Indiana Law Journal 88: 14751558, 2013. Hutchison, Megan. “Rica puts South Africa under closer surveillance than Americans,” TheSouthAfrican.com. Last modified 20 June 2013. http://www. thesouthafrican.com/news/rica-puts-south-africa-under-closer-surveillance-than-americans.htm. ICANN (Internet Corporation for Assigned Names and Numbers). “Montevideo Statement on the Future of Internet Cooperation.” ICAN.org, 7 October 2013. https://www.icann.org/news/announcement-2013-10-07-en (accessed 5 August 2014). IGF (United Nations Internet Governance Forum). The Charter of Human Rights and Principles for the Internet. Internet Rights and Principles Coalition. (2013). International Telecommunication Union (ITU). International Telecommunication Convection. (Genebra: ITU,1973). Jiang, Min & Okamoto, Kristen (Forthcoming). “National identity, state ideological apparatus, or Panopticon? A case study of Chinese national search engine” Jike. Policy & Internet (2014). Kerr, Orin S. “Internet Surveillance Law After the USA Patriot Act: The Big Brother That Isn’t.”. Northwestern University Law Review 97(2): 607-674 (2003). Kroes, Neelie. “Life begins at 50: keeping the Internet unified, open and inclusive.” EC.europa.eu. June 19,2014. http://ec.europa.eu/commission_2010-2014/ kroes/en/blog/life-begins-50-keeping-internet-unified-open-and-inclusive Kurbalija, Jovan. An Introduction to Internet Governance. (Genebra: Diplo Foundation, 2010). La Rue, Frank. Report of the Special Rapporteur on the promotion and protection of the right to freedom of opinion and expression. UN Doc. A/HRC/23/40 (2011). Laidlaw, Emily B. “The responsibilities of free speech regulators: an analysis of the Internet Watch Foundation.” International Journal of Law and Information Technology 20(4): 312-345 (2012). Leisert, Oliver. “Resistance against Cyber-Surveillance within Social Movements and how Surveillance Adapts.” Surveillance & Society 9(4): 441-456 (2012). Lewis, James A. The Architecture of Control: Internet Surveillance in China. (Washington: Centre for Strategic and International Studies, 2006). Liang, Bin & Lu, Hong. “Development, Censorship and Cyber Crimes in China” Journal of Contemporary Criminal Justice 26(1): 103-120 (2010). 440 UFRGSMUN | UFRGS Model United Nations Ligabo, Ambeyi. “Addendum 2: Mission to Ukraine” Promotion and Protection of All Human Rights, Civil, Political, Economic, Social and Cultural Rights, Including the Right to Development. A/HRC/7/14/Ass.2 (2008). Lyon, David. Surveillance as Social Sorting: Privacy, risk, and digital discrimination. (New York: Routledge, 2003) Lyon, David. “Liquid Surveillance: The Contribution of Zygmunt Bauman to Surveillance Studies.” International Political Sociology 2010(4): 325-338 (2010). MacDonald, Reagan, Jochai Ben-Avie, and Fabiola Carrion. “Internet freedom and the right to private life, protection of personal data and due process of law.” MCM (Council of Europe Conference of Ministers responsible for Media and Information Society) 08 (2013). Mayer-Schonberger, Viktor and Cukier, Kenneth. Big Data: A Revolution that Will Transform how We Live, Work, and Think. (New York: Houghton Mifflin Harcourt Publishing Company, 2013) Anja Mihr, Public Privacy: Human Rights in Cyberspace (Netherlands: Institute of Human Rights of the University of Utretch (SIM), 2013) Moody, Glyn. “Indian Government Quietly Brings In Its ‘Central Monitoring System’: Total Surveillance Of All Telecommunications.” TechDirt.com. May 9, 2013.. https://www.techdirt.com/articles/20130508/09302923002/indian-government-quietly-brings-its-central-monitoring-system-total-surveillance-all-communications.shtml Milton Mueller, Andreas Kuehn and Stephanie Michelle Santoso. “DPI and copyright protection: A comparsion of EU, US and China” Cyber-Surveillance in Everyday Life: An International Workshop (2011). NISO (National Information Standards Organization). Understanding Metadata (Bethesda: NISO Press, 2004). National Telecommunications and Information Administration. “NTIA Announces Intent to Transition Key Internet Domain Name Funcions”, Ntia.doc. gov. March 14, 2014. http://www.ntia.doc.gov/press-release/2014/ntia-announces-intent-transition-key-internet-domain-name-functions OECD. OECD Guidelines on the Protection of Privacy and Transborder Flows of Personal Data. 1980. OPENNET Initiative. “Internet Filtering in the United Arab Emirates in 20042005: A Country Study”, Opennet.net, December 14, 2005. https://opennet.net/studies/uae#toc1 441 World Summit on the Information Society Forum Phillipson, Gavin and Fenwick, Helen. “Breach of Confidence as a Privacy Remedy in the Human Rights Act Era”, Oxford University Public Law Review, 627-650 (2000). Neil Richards, “The Dangers of Surveillance.”, Harvard Law Review Symposium on Privacy and Technology (2012). RWB (Reporters Without Borders). The Internet Under Surveillance (Paris: New Media Desk, 2003). RWB (Reporters Without Borders). Enemies of the Internet: Countries under surveillance. (Paris: New Media Desk, 2010). RWB (Reporters Without Borders). Enemies of The Internet: 2013 Report (Paris: New Media Desk, 2013) RWB (Reporters Without Borders). “Countries Under Surveillance: France”. RSF.org. August 5, 2014. http://en.rsf.org/surveillance-france,39715.html. Soldatov, Andrei and Borogan, Irina. “Russia’s Surveillance State”, World Policy Journal 30(23), 2013. Thierer, Adam and Crews Jr, Clyde Wayne. Who rules the net? : Internet governance and jurisdiction, (Washington: Cato Institute, 2003). Stanley, Jay and Steinhardt, Barry. Bigger Monster, Weaker Chains: The Growth of an American Surveillance Society (New York: American Civil Liberties Union, 2003). Tokson, Matthew J. “The Content/Envelope Distinction in Internet Surveillance Law.” William & Mary Law Review, Vol. 50, No. 6. (2009). Taslitz, Andrew E. “Cybersurveillance Without Restraint? The Meaning and Social Value of the Probable Cause and Reasonable Suspicion Stantards in Governmental Access to Third-Party Electronic Records”, Journal of Criminal Law and Criminology, Vol. 103, No. 839 (2013). http://papers.ssrn.com/sol3/papers. cfm?abstract_id=2348244 The Stationery Office of the United Kingdom. 2011 Anual Report of the Interception of Communications Commissioner. (London: Crown, 2012). United Nations. The Universal Declaration of Human Rights. (New York: UNGA, 1948). United Nations General Assembly. Report on the Promotion and Protection of human rights: human rights questions, including alternative approaches for improving the effective enjoyment of human rights and fundamental freedoms, A/68/456/Add.2. (New York: UNGA, 2013). 442 UFRGSMUN | UFRGS Model United Nations United Nations General Assembly. The right to privacy in the digital age, A/C.3/68/L.45/Rev.1. 20 (New York: UNGA, 2013). United Nations General Assembly. Statement by H. E. Dilma Rousseff, President of the Federative Republic of Brazil at the Opening of the Geberal Debate of the 68th Session of the United Nations General Assembly (New York: UNGA, 2013). United Nations Human Rights Council. Written statement submitted by Reporters Without Borders International, a non-governmental organization in special consultive status, A/HRC/24/NGO/31 (Genebra: UNHRC, 2013). United Nations Human Rights Council. General Comment 16, A/43/40. (Genebra: UNHRC, 1988). United Nations Human Rights Council. The Promotion, protection and enjoyment of human rights on the Internet. (Genebra: UNHRC, 2012). United States Department of State. Country Reports on Human Rights Practices for 2012. (Washington, D.C: DOS, 2013). UNESCO. Global Survey on Internet Privacy and Freedom of Expression (Paris: UNESCO, 2013). United States Privacy and Civil Liberties Oversight Board (USPCLOB). Report on the Telephone Records Program Conducted under Section 215 of the USA PATRIOT Act and on the Operations of the Foreign Intelligence Surveillance Court (Washington, D.C: USPCLOB, 2014). Xihnua. “China Publishes book on U.S. Global Surveillance.” China Daily, June 23, 2014.. http://www.chinadaily.com.cn/culture/2014-06/23/content_17608217.htm. Wagner, Ben. Exporting Censorship and Surveillance Technology (The Hague: HIVOS, 2012). Walter-Echols, Michael. Panopticon: Surveillance and Privacy in the Internet Age (BA thesis, Faculty of Worcester Polytechnic Institute, 2009). Webster, Frank. Theories of The Information Society (New York: Routledge, 1995). Wilsher, Kim. “French Officials Can Monitor Internet Users in Real Time Under New Law,” The Guardian, December 11, 2013. http://www.theguardian.com/world/2013/dec/11/french-officials-internet-users-real-time-law. Ziolkoski, Katharina. Peacetime Regime for State Activities in Cyberspace (Tallinn: Nato Cooperative Cyber Defense Centre of Excellence, 2013). 443