Pattern Recognition 36 (2003) 1583 – 1595
www.elsevier.com/locate/patcog
Finding optimal least-signi"cant-bit substitution in image
hiding by dynamic programming strategy
Chin-Chen Changa , Ju-Yuan Hsiaob;∗ , Chi-Shiang Chana
a Department
of Computer Science and Information Engineering, National Chung Cheng University, Chiayi, Taiwan 621, ROC
of Information Management, National Changhua University of Education, Changhua, Taiwan 500, ROC
b Department
Received 27 July 2002; received in revised form 19 August 2002; accepted 19 August 2002
Abstract
The processing of simple least-signi"cant-bit (LSB) substitution embeds the secret image in the least signi"cant bits of the
pixels in the host image. This processing may degrade the host image quality so signi"cantly that grabbers can detect that
there is something going on in the image that interests them. To overcome this drawback, an exhaustive least-signi"cant-bit
substitution scheme was proposed by Wang et al. but it takes huge computation time. Wang et al. then proposed another
method that uses a genetic algorithm to search “approximate” optimal solutions and computation time is no longer so huge.
In this paper, we shall use the dynamic programming strategy to get the optimal solution. The experimental results will show
that our method consumes less computation time and also gets the optimal solution.
? 2003 Pattern Recognition Society. Published by Elsevier Science Ltd. All rights reserved.
Keywords: Image hiding; Least-signi"cant-bit substitution; Dynamic programming; Genetic algorithm; Image embedding
1. Introduction
In the Internet, tons of various kinds of data are sent, transmitted and received every single moment. Some of them
may be secret information of commerce and others con"dential messages from the government, both of which are
candidate preys for grabbers to access. In order to keep the
grabbers away, a variety of techniques have been proposed.
One of the most famous methods is data encryption [1,2],
which uses a certain algorithm to transform data into cipher
texts. Only the user that has keys can decrypt the secret data
from the cipher texts. For any grabber who does not have
a key, the cipher texts will look like nothing but streams of
meaningless codes. Although data encryption is a good way
to prevent grabbers from accessing secret data, it still has
some weaknesses. The appearance of cipher texts would give
∗
Corresponding author. Fax:+886-4-7211162.
E-mail addresses: ccc@cs.ccu.edu.tw, ccs88@cs.ccu.edu.tw
(C.-C. Chang), hsiaojy@cc.ncue.edu.tw (J.-Y. Hsiao).
grabbers an impulse to recover them. Moreover, grabbers
might even simply destroy the cipher texts out of rage when
they have trouble recovering them so that the legal receivers
cannot get the data in time. That is the reason why data
hiding [3,4] has been researched recently. Data hiding techniques embed the important data into multimedia data such
as images, videos or movies. In this paper, we take an image
for a carrier of secret data and name it as a host image. After
embedding the secret data into the host image, the output
image of this hiding process is called a stego- image. When
we discuss image hiding, one of the most important things is
that the quality of the stego-image must not be degraded too
much after embedding. The goal of data hiding is to make
the stego-image invisible to grabbers. Thus, if the process
of embedding degrades the quality of the stego-image too
much, any grabber will easily take notice of it. Techniques
of least-signi"cant-bit-based substitution are simple ones to
achieve data hiding. A least-signi"cant-bit-based substitution method replaces some least signi"cant bits of the host
image with the secret data. After least-signi"cant-bit-based
data hiding, the researches of data hiding focus on the
0031-3203/03/$30.00 ? 2003 Pattern Recognition Society. Published by Elsevier Science Ltd. All rights reserved.
PII: S 0 0 3 1 - 3 2 0 3 ( 0 2 ) 0 0 2 8 9 - 3
1584
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
diHculty of removing the embedded data through operations of images. Most researches concerned are concentrated
upon watermarking [5–7]; the capacity of embedding is not
the key point in those methods. However, in our opinion,
one of the important things in data hiding is the embedding capacity. When we want to transmit important secret
data via a certain technique of data hiding, it is obviously
not practical if we have no choice but to break the secret
data into pieces and put each piece in a large host image
due to the limited capacity. On the other hand, the simple
least-signi"cant-bit substitution method directly replaces
some least signi"cant bits of each pixel value in the host
image with the secret data; it does not focus on the diHculty of removing secret data through images operations
but rather on the capacity of embedding. When talking
about the capacity of embedding, the major concern is to
make stego-image extremely hard for grabbers to sense the
existence of the secret data. There exists one method to
achieve this aim. The method "rst sets a bijective mapping
function and transforms values of secret data into another
set of values according to a bijective mapping function.
It then replaces the rightmost least signi"cant bits of each
pixel in host image with transformed values to form the
stego-image. It goes without saying that if we can "nd
an optimal solution of bijective mapping function, we can
use a bijective mapping function to make the stego-image
have the best quality. In order to "nd the optimal solution
of a bijective mapping function, the procedure of the exhaustive least-signi"cant-bit substitution must exhaustively
go through all possible bijective mapping functions. When
the rightmost k least signi"cant bits of the host image are
replaced by the secret data, k being large, it takes huge
computation time and makes the method impractical. In
2001, Wang et al. [8] proposed a method that uses a genetic
algorithm to search for an approximate optimal solution of a
bijective mapping function, and the computation time is no
longer so huge as that of the exhaustive least-signi"cant-bit
substitution. Although Wang et al.’s method reduces the
computation time, the solution it comes up with is not
an optimal one of the bijective mapping function but an
“approximate” optimal solution instead. In order to get
an optimal solution of a bijective mapping function, we
propose the method that uses a dynamic programming strategy to achieve this purpose. Our method not only gets an
optimal solution of a bijective mapping function but also
signi"cantly reduces the computation time.
The rest of this paper is organized as follows. We shall describe the related works "rst in Section 2. We shall introduce
the image hiding in detail by using the least-signi"cant-bit
substitution in Section 2.1 and Wang et al.’s genetic algorithm in Section 2.2. After that, we shall describe our method
in Section 3. Details of our method for "nding an optimal
solution are "rst introduced in Section 3.1, and then some
properties about our solution are discussed in Section 3.2.
In Section 4, the experimental results show how our method
performs. Finally, the conclusions are presented in Section 5.
2. Related works
In this section, the related works are introduced.
We will "rst look at the image hiding technique using
least-signi"cant-bit substitution. After least-signi"cant-bit
substitution, we will continue to describe exhaustive
least-signi"cant-bit substitution. Wang et al.’s genetic algorithm to search for an optimal or approximate optimal
solution is described in Section 2.2.
2.1. Least-signi3cant-bit substitution
In this subsection, the simple least-signi"cant-bit substitution and exhaustive least-signi"cant-bit substitution are introduced. Suppose our embedded data is an image called
the secret image S, and the host multimedia data is also
an image called the host image. Both the images are 8-bit
gray-scale images. We assume that the size of the host image is a multiple of the secret image S.
There exist two steps to the method of simple
least-signi"cant-bit substitution. In the "rst step, the method
gathers all the 8-bit pixel values in the secret image S sequentially. It, then, decomposes the bit streams into several
k-bit unit and takes each single k-bit unit as a single k-bit
pixel. Let this k-bit pixel secret image be called S . The
value of k is decided on the basis of a calculation to make
the height and width of S be the same as that of the host
image. The second step replaces each k least signi"cant
bit of the 8-bit pixel value in the host image with the corresponding k-bit in S to get the stego-image. According
to our description above, the quality of the stego-image
produced by simple least-signi"cant-bit substitution may
not be acceptable. It means that the method degrades the
image quality so signi"cantly that the stego-image may
probably attract grabbers’ attention. Once a grabber notices
the stego-image, she/he can simply extract and analyze the
least signi"cant bits to get the secret image. To improve
the security and the quality of the stego-image, a method
of exhaustive least-signi"cant-bit substitution is presented
in [8].
For convenience, let the k-bit residual image denote the
k-bit gray-scale image which is derived by extracting the
rightmost k least signi"cant bits from each pixel in a host
image. With regard to exhaustive least-signi"cant-bit substitution, some additional works will be done for S to increase
the security and image quality. In the "rst step, a bijective
(i.e., one-to-one and onto) mapping function is set up that
transforms the positions of each pixel in S into random
positions. More speci"cally, we "rst number all pixels in S sequentially from left to right and top to bottom. After numbering, the original position, x, a pixel is transformed into
a new position, F(x), according to the following bijective
mapping function [8]:
F(x) = (k0 + k1 × x) mod N:
(1)
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
Here k0 and k1 are taken as keys and N is the size of S . The
greatest common divisor of k1 and N is 1. After position
transforming, we get a meaningless image S , and grabbers
can never again analyze the data of the least signi"cant bits
plane from the stego-image to get the secret data. In the
second step of exhaustive least-signi"cant-bit substitution,
the diLerence between k-bit residual image of the host image and S is reduced. It is easy to see that the values of
each pixel in S are in the range from 0 to 2k − 1. The
method of exhaustive least-signi"cant-bit substitution sets
up another bijective mapping function that transforms each
value in [0; 2k − 1] into another value in [0; 2k − 1]. The bijective mapping function can be represented by an N × N
substitution matrix, MN ∗N = {m[i][j] | 0 6 i; j 6 2k − 1},
where N is equal to 2k and the value of m[i][j] is 1 or 0.
If the value of m[i][j] is 1, it means that each pixel with
value i in image S will be transformed into value j. Because the mapping function is a bijective function, the critical restriction of the substitution matrix is that exactly one
position, whose value is equal to 1, exists in each row and
column in the substitution matrix MN ×N . Given a feasible substitution matrix MN ×N , we can transform each k-bit
pixel value of S into the corresponding value according to
MN ×N . We name this transformed k-bit gray-scale image
as S .
A simple example of the transforming procedure is illustrated as follows. We assume that the value of N is 4 and
the image S and the substitution matrix MN ×N are listed
below:
S =
11
01
10
00
1
0
M4∗4 =
0
0
=
2
3
1
2
0
0
;
10
0
0
0
1
1
0
0
:
0
0
0
1
2
The result S , which is transformed from the S according
to the substitution matrix MN ×N , is listed below:
S
=
3
2
1
0
=
10
11
10
01
00
:
2
As we have a substitution matrix MN ×N , we can derive
S from S . Now, the critical problem is how to "nd an
optimal substitution matrix such that S is “closest” to the
k-bit residual image of host image. The meaning of “closet”
is that they have the smallest summation of square diLerences between residual image and S . In Wang et al.’s
exhaustive substitution method, it tries all the substitution
matrices and "nds out some special substitution matrix that
makes S closest to the k-bit residual image of the host
1585
image. We name this S as S ∗ and the corresponding substitution matrix the optimal solution of substitution matrix.
By replacing the rightmost k least signi"cant bits of each
pixel in the host image with S ∗ to form the stego-image, we
degrade the least quality from the host image. To describe
the quality of the stego-image precisely, we use value of the
peak signal-to-noise ratio (PSNR) to judge the similarity
between the host image and the stego-image. The PSNR
function is de"ned as follows:
PSNR = 10 log
(255)2
dB:
MSE
(2)
Here MSE is the mean square error. Subsequently, we de"ne
MSE as follows:
MSE =
W
H
1 ((I; J ) − (I; J ))2 :
(WH ) I =1 J =1
(3)
The symbols (I; J ) and (I; J ) separately represent the
pixel values of the host image and the stego-image in position (I; J ), and W and H represent the pixel numbers
of the width and the height of the image separately. The
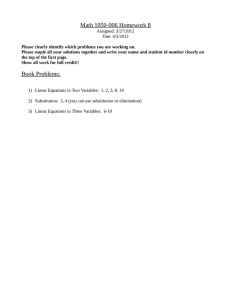
Nowchart of the method of exhaustive least-signi"cant-bit
substitution is plotted in Fig. 1. The method of exhaustive
least-signi"cant-bit substitution exhaustively calculates all
the values of PSNR between the host image and all the
stego-images to "nd the maximal value. Once we "nd
the maximal value among all values of PSNR, its corresponding stego-image is the most similar to the host
image. We can easily "gure out that the total number of
possible substitution matrices is (2k )! According to our
perception, the number of possible substitution matrices
will grow exponentially as k increases. Wang et al. indicated that, if k was greater than 3, it was very impractical
to compute all values of PSNR between the host image
and the stego-images as it is time consuming. Wang et
al. introduced their genetic algorithm instead. The main
purpose of the genetic algorithm is that it reduces time
consumption by "nding an approximate optimal solution
of the substitution matrix. We shall roughly describe it
below.
2.2. The method of genetic algorithm
In using genetic algorithm for solving a certain kind of
problem, the "rst step is to convert some candidate solution
to the problem into chromosomes containing many genes.
According to the operations of reproduction, crossover
and mutation, the genetic algorithm gets many chromosomes. Those chromosomes are the candidate solutions of
the problem. A function used to judge the quality of the
chromosomes is called the "tness function. Using the "tness function to judge those chromosomes, if we can "nd
a good chromosome, we are guaranteed to "nd a good solution for our problem. Wang et al. followed the steps to
1586
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
S
Secret image
(n-bits/pixel)
H
Decomposition
S'
Host image
(n-bits/pixel)
Least significant bits extraction
Secret image
(k-bits/pixel)
Residual image
(k-bits/pixel)
R
H-R
((n-k)-bits/pixel)
Positions transform
Replace
and attach
S''
Try all substitution matrices
…
S1'''
S2'''
…
Sm'''
Z
Finding an
Stego-image
(n-bits/pixel)
optimal solution
S*
Fig. 1. The Nowchart of embedding by exhaustive least-signi"cant-bit substitution.
"nd a good substitution matrix for solving the problem of
image hiding. First of all, the candidate substitution matrices must be converted into chromosomes. In Wang et
al.’s method, the chromosome is represented by an N array,
GN = {g[i] | 0 6 i; g[i] 6 2k − 1}, where N is 2k . In the
procedure of converting a substitution matrix MN ×N into a
chromosome, the method uses g[i] to record the position,
whose value is equal to 1, in the ith row of the substitution
matrix MN ×N . A simple example of the converting procedure is illustrated as follows. The substitution matrix MN ×N
is listed below:
1
0
M4∗4 =
0
0
0
0
0
0
1
1
0
0
:
0
0
0
1
2
The result for the chromosome of this substitution matrix
M4×4 is
0
2
G4 = :
1
3
10
It is easy to see that the values of each element in G4 are
diLerent from all the others because there must be exactly
one element, whose value is equal to 1, in each row and
column of the substitution matrix MN ×N . The function of
chromosomes is the same as substitution matrices that transform the pixel value i into g[i]. In the "rst step of the genetic
algorithm, the substitution matrices are selected randomly
from all possible substitution matrices. After converting
the selected substitution matrices into chromosomes, other
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
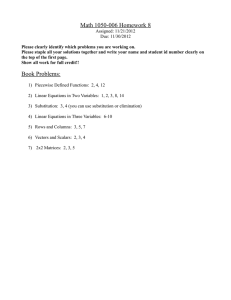
S
Secret image
(n-bits/pixel)
H
Decomposition
S'
1587
Host image
(n-bits/pixel)
Least significant bits extraction
Secret image
(k-bits/pixel)
Residual image
(k-bits/pixel)
R
H-R
((n-k)-bits/pixel)
Positions transform
Replace
and attach
S''
Substitution matrices from
genetic alogrithm
…
S1'''
S2'''
…
Sm'''
Z
Finding an
approximate
Stego-image
(n-bits/pixel)
optimal solution
S^
Fig. 2. The Nowchart of embedding by genetic algorithm.
procedures of the genetic algorithm are carried out, that is,
the series of reproduction, crossover and mutation. Reproduction duplicates some chromosomes for other operations.
Crossover randomly combines the front half of one chromosome with the rear half of another chromosome into a
new chromosome. This new chromosome must be scanned
to discard the values of repetition and discarded elements
are assigned new values to discarded elements to make
all the elements in chromosome diLer from each other.
Mutation randomly selects a chromosome and randomly
exchanges the values of two elements to form a new chromosome. After getting new chromosomes from the above
operations, the genetic algorithm uses the "tness function to
judge the quality of all chromosomes such that good quality
chromosomes can be used for the next generation. Taking
PSNR as a "tness function is not suitable because computing the value of PSNR is time consuming. Looking into the
PSNR function, the PSNR value relates to the value of the
function ((I; J ) − (I; J ))2 . The smaller the value of the
function ((I; J ) − (I; J ))2 , the larger the value of PSNR.
The genetic algorithm will take the ((I; J ) − (I; J ))2 function as a "tness function. In Fig. 2, each k-bit gray-scale
image S comes from transforming the values of pixels
in S according to a chromosome. For each chromosome,
the "tness function just calculates the ((I; J ) − (I; J ))2
function between S and the k-bit residual image of the
host image to judge the quality of the chromosome. If a
certain k-bit gray-scale image S has a smallest value of
the ((I; J ) − (I; J ))2 function, the genetic algorithm will
take this chromosome as a good chromosome. When doing
the experiment of genetic algorithm, 10 chromosomes are
randomly picked up as the initial state. After creating new
chromosomes by reproduction, crossover and mutation, 10
best quality chromosomes are picked up, 10 which form the
1588
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
initial state of the next generation. The genetic algorithm
repeats the above procedures eight times and the best quality chromosome in the last generation is taken as the "nal
solution. After transforming S according to the "nal solution of chromosome, we can get an image called Sˆ. Replacing the rightmost k least signi"cant bits of each pixel
in the host image with Sˆ to form the stego-image, a good
quality stego-image can be obtained. The Nowchart of genetic algorithm is shown in Fig. 2. It is obvious that the
solution of genetic algorithm cannot guarantee to "nd an
optimal solution of the least-signi"cant-bit substitution. In
this paper, we propose a method that uses the dynamic programming strategy to solve this problem. The main contribution of our method is in "nding an optimal solution of the
least-signi"cant-bit substitution and it requires little time for
computation. The following section will describe our new
method.
3. The proposed method
In this section, we shall introduce our method. We
will "rst look at how to "nd the optimal solution of
least-signi"cant-bit substitution by using our method.
Then, we shall move on and demonstrate that our method
can achieve the task of "nding an optimal solution of
least-signi"cant-bit substitution.
3.1. Our method
In our method, we "rst rede"ne the matrix MN ∗N =
{m[i][j] | 0 6 i; j 6 2k − 1}, where N is equal to 2k . The
main diLerence between the rede"ned matrix and substitution matrix in Section 2.1 is the contents of their elements.
The contents of m[i][j] in our rede"ned matrix MN ×N are
the summation of the square diLerences. That is, if we
transform the pixels with value i in S into value j, the
m[i][j] represents how many square diLerences are derived
between the transformed pixels and the pixels of the corresponding positions in the residual image. To be more
precise, we "rst set all the initial values of the elements in
MN ×N as 0. The method then scans the pixels in S sequentially. We assume that the scanned pixel value is i and
its position is (t; r) in S . As the value of scanned pixel is
i, the relative values that we have to modify are m[i][j] for
all j in the range from 0 to 2k − 1. Thus, we calculate the
square diLerence between the pixel value j and the pixel
value of the k-bit residual image in (t; r). Getting the square
diLerence value, we add it to m[i][j] and restore this new
m[i][j] back to MN ×N . After scanning all the pixels in S ,
we can "ll out the whole matrix MN ×N . After "nishing the
procedure of scanning S and "lling out the whole matrix
MN ×N , we continue to pick up N elements from MN ×N .
We must obey the rule that exactly one element is picked
up in each row and column in MN ×N .
Assume that those N elements that are picked up are
m[k][jk ]; k = 0; 1; : : : ; N − 1. It is clear that jk = jk if k =
k , where 0 6 k; k 6 N − 1. We list j0 ; j1 ; : : : ; jN −1 and
call it a substitution list. According to the substitution list,
we can transform the pixel value 0 in S into j0 and pixel
value 1 into j1 , and so on to derive S . The summation
of the square diLerence between the k-bit residual image
of the host image and S is m[0][j0 ] + m[1][j1 ] + · · · +
m[N − 1][jN −1 ]. It is obvious that if we can "nd out a
substitution list that makes m[0][j0 ]+m[1][j1 ]+· · ·+m[N −
1][jN −1 ] minimum, then we can "nd an optimal solution of
least-signi"cant-bit substitution. However, what should we
do to get the substitution list that makes m[0][j0 ] + m[1][j1 ]
+ · · · + m[N − 1][jN −1 ] minimum? We know that exactly
one element will be picked up in each row and column in
MN ×N . We cannot just pick up the minimum element in
MN ×N , because it may contradict with the above rule. In the
next paragraph, we use the dynamic programming strategy
to solve this problem.
First, we de"ne the input and output of our method more
precisely. The input of our method is an N × N matrix
named MN ×N , and m[i][j] denotes the element at the position of row i and column j in MN ×N . The output of our
method is a substitution list that makes the total cost of
m[0][j0 ]+m[1][j1 ]+· · ·+m[N −1][jN −1 ] minimum on the
condition that jk = jk if k = k , where 0 6 k; k 6 N − 1.
Suppose Set is a subset of {0; 1; : : : ; N − 1}. Let Cost[r; Set]
denote the minimum cost of the substitution list picked up
from the submatrix M of MN ×N , where submatrix M is
constructed by the rows from N − 1 to r and the columns
listed in Set. Again, there is exactly one element that will
be picked up in each row and each column of M . Let the
initial value of Cost[N; { }] be equal to zero. It is easy to
see that Cost[0; {0; 1; : : : ; N − 1}] is the minimum cost of
m[0][j0 ] + m[1][j1 ] + · · · + m[N − 1][jN −1 ]. According to
the de"nition of Cost[r; Set], we have the following dynamic
programming formula.
Cost[r; Set] = min {m[r][j] + Cost[r + 1; Set − {j}]}: (4)
j∈Set
According to our formula and initial condition, we can
quickly get the minimum cost of MN ×N . The Nowchart of our
method to "nd the optimal solution of least-signi"cant-bit
substitution is shown in Fig. 3. We give a simple example
to illustrate our method. Assume that S and R, the residual
image of the host image, are 2-bit gray-scale images of size
2 × 2. The value of N is 22 = 4 so that we can get the matrix
M4×4 from S and R, all of which are listed below:
S =
R=
11
01
10
00
11
10
00
00
=
2
=
2
3
1
2
0
3
2
0
0
;
10
;
10
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
S
Host image
(n-bits/pixel)
H
Secret image
(n-bits/pixel)
Least significant bits extraction
Decomposition
S'
1589
Secret image
(k-bits/pixel)
Residual image
(k-bit/pixel)
R
H-R
((n-k)-bits/pixel)
Positions transform
Finding an optimal
S''
Replace
and attach
solution by dynamic
programming strategy
MN×N
Z
Finding an
Stego-image
(n-bits/pixel)
optimal solution
S*
Fig. 3. The Nowchart of embedding by our method.
0
4
M4∗4 =
0
9
9
1
4
1
0
1
4
1
:
9
4
1
0
=
0+4
1+9
Cost[2; {0; 2}] = min
10
We now use the dynamic programming formula to "nd the
minimum cost from M4×4 , that is, Cost[0; {0; 1; 2; 3}]. The
initial value of Cost[4; {}] is 0. Our processing steps are
listed below.
=
Cost[2; {0; 3}] = min
Cost[3; {1}] = m[3][1] + Cost[4; { }] = 4;
=
Cost[2; {1; 2}] = min
Cost[2; {0; 1}] = min
m[2][0] + Cost[3; {1}]
m[2][1] + Cost[3; {0}]
=
m[2][0] + Cost[3; {2}]
m[2][0] + Cost[3; {3}]
m[2][3] + Cost[3; {0}]
0+0
= 0;
9+9
Cost[3; {2}] = m[3][2] + Cost[4; { }] = 1;
Cost[3; {3}] = m[3][3] + Cost[4; { }] = 0;
= 4;
m[2][2] + Cost[3; {0}]
0+1
= 1;
4+9
Cost[4; { }] = 0;
Cost[3; {0}] = m[3][0] + Cost[4; { }] = 9;
m[2][1] + Cost[3; {2}]
m[2][2] + Cost[3; {1}]
1+1
= 2;
4+4
1590
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
Cost[2; {1; 3}] = min
=
1+0
Cost[0; {0; 1; 2; 3}] = min
= 1;
9+4
Cost[2; {2; 3}] = min
m[2][3] + Cost[3; {1}]
=
m[2][1] + Cost[3; {3}]
m[2][2] + Cost[3; {3}]
m[2][3] + Cost[3; {2}]
4+0
9+1
= 4;
m[1][1] + Cost[2; {2; 3}]
Cost[1; {1; 2; 3}] = min m[1][2] + Cost[2; {1; 3}]
m[1][3] + Cost[2; {1; 2}]
1+4
= 0 + 1 = 1;
1+2
m[1][0] + Cost[2; {2; 3}]
Cost[1; {0; 2; 3}] = min m[1][2] + Cost[2; {0; 3}]
m[1][3] + Cost[2; {0; 2}]
4+4
= 0 + 0 = 0;
1+1
m[1][0] + Cost[2; {1; 3}]
Cost[1; {0; 1; 3}] = min m[1][1] + Cost[2; {0; 3}]
m[1][3] + Cost[2; {0; 1}]
4+1
= 1 + 0 = 1;
1+4
m[1][0] + Cost[2; {1; 2}]
Cost[1; {0; 1; 2}] = min m[1][1] + Cost[2; {0; 2}]
m[1][2] + Cost[2; {0; 1}]
4+2
= 1 + 1 = 2;
0+4
=
m[0][0] + Cost[1; {1; 2; 3}]
m[0][1] + Cost[1; {0; 2; 3}]
m[0][2] + Cost[1; {0; 1; 3}]
m[0][3] + Cost[1; {0; 1; 2}]
0+1
1+0
4+1
9+2
= 1;
The "nal value of Cost[0; {0; 1; 2; 3}] is 1 and it is easy to
trace back to get the substitution list; that is, j0 ; j1 ; j2 ; j3 =
0; 2; 1; 3 or 1; 2; 0; 3. This is how we "nally get the substitution list. If we transform the pixel values of S from 0
to 0, 1 to 2, 2 to 1 and 3 to 3, according to the substitution
list 0; 2; 1; 3, we can get
3 2
∗
S =
1 0 10
and the summation of the square diLerence between R and
S ∗ is 1. Replacing the rightmost k least signi"cant bits of
each pixel in the host image with S ∗ to form the stegoimage, we degrade the least quality from the host image.
That concludes our method.
3.2. About the solution
Our theorem states that we can get an optimal solution by using dynamic programming strategy if it satis"es
the rule of “Principle of Optimality” [9]. The meaning of “Principle of Optimality” is that an optimal solution can be generated from the optimal subsolutions;
in an optimal sequence of decisions, each subsequence
must also be optimal. We "rst assume that the substitution list, which is gained from tracing our method, is
j0 ; j1 ; : : : ; jN −1 . It is obvious that Cost[r; Set] is generated
from the optimal subsolutions, that is Cost[r + 1; Set −
{j}], where j is an element of Set. The subsequence
jk ; jk+1 ; : : : ; jN −1 of j0 ; : : : ; jk ; jk+1 ; : : : ; jN −1 , where k is
in the range from 0 to N − 1, is also optimal because of
Cost[k; {jk ; jk+1 ; : : : ; jN −1 }]. It goes without saying that we
can generate an optimal solution obeying the principle of
optimality.
4. Experimental results
We discuss the experimental results in this section. Our
programs are run in a personal computer whose operation
system is Red Hat Linux 6.1. The CPU of the personal
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
1591
(a)
(b)
(a)
(b)
(c)
(d)
(c)
(d)
Fig. 5. A comparison of the stego-images by using our method and
genetic algorithm to hide the secret image named “Jet” with size
256 × 512: (a) and (b) use our method, (c) and (d) use the method
of genetic algorithm. (a) Lena, (b) Pepper, (c) Lena, (d) Pepper.
(e)
(f)
Fig. 4. The images of our test data. (a) Lena, (b) Barb, (c) Pepper,
(d) Jet, (e) TiL, (f) Boat.
computer is AMD-K6II 300, and its main memory is
64 Mbyte. In our experimental test, all images are 256 gray
levels, 512 × 512 of size. We take the images Lena, Barb
and Pepper separately shown in Fig. 4(a), (b) and (c) as
host images. Three images Jet, TiL and Boat are taken as
secret images. They are separately shown in Fig. 4(d), (e)
and (f). The size of the original secret images is 512 × 512
with 256 gray levels. We resize all secret images into
256 × 512, 192 × 512 and 128 × 512 with 256 gray levels.
Then, we use bijective mapping function to transform the
positions of pixels and embed those secret images into,
respectively, 4, 3 and 2 least signi"cant bits of the host
image. We use the same bijective mapping function that is
described in the experimental part of [8]:
F(x) = (1019 + 17 × x) mod 262144:
In the experiments, we used three methods: exhaustive least-signi"cant-bit substitution, genetic algorithm and
our method, to "nd the optimal or approximate optimal
solutions. The experiments focus on not only computation
time but also the MSE between the stego-images and host
images. The stego-images are shown in Fig. 5. The computation time and MSE are shown in tables from Tables
1–6. Tables 1, 2 and 3 record the "gures of computation
time of various methods where the secret images are 128 ×
512; 192 × 512 and 256 × 512, respectively. On the other
hand, Tables 4, 5 and 6 show the MSE between the host
images and the stego-images where the secret images are
128 × 512; 192 × 512 and 256 × 512, respectively. From the
results listed in Tables 1–3, we can see the comparison of
those three methods. The computation time of the exhaustive
least-signi"cant-bit substitution method is approximately the
same as that of our method when we embed the secret images into the least signi"cant 2 bits of the host images. The
computation time of exhaustive least-signi"cant-bit substitution method rises quickly when we embed the secret images into the least signi"cant 3 bits of the host images. If
we embed the secret images into the least signi"cant k bits
of the host images where k is greater than or equal to four,
the computation time becomes so huge that we do not put it
in the tables. The method of genetic algorithm has a smooth
performance on computation time. The reason for this is that
the number of iterations is "xed in the genetic algorithm.
The computation time of our method is much less than for
the other two methods in all cases, especially when k is
growing up. Then, we analyze Tables 4–6 for checking the
qualities of the solutions that are generated by those three
1592
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
Table 1
The computation time (unit: second) with Lena as host image
Method
Jet
TiL
Boat
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.071
2.283
18.338
1.065
2.283
18.342
1.072
2.282
18.442
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.251
3995.985
19.228
1.252
4050.577
19.398
1.248
4058.817
19.255
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.739
Too huge
20.742
1.731
Too huge
20.714
1.732
Too huge
20.740
Jet
TiL
Boat
Table 2
The computation time (unit: second) with Barb as host image
Method
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.040
2.301
18.197
1.050
2.305
18.377
1.044
2.303
18.226
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.238
4079.252
19.081
1.235
4065.584
19.271
1.237
4115.977
19.090
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.729
Too huge
21.012
1.728
Too huge
20.978
1.730
Too huge
20.979
methods. We use MSE, which is introduced in Formula
(3) in Section 2.1, to judge the quality of the stego-images.
According to the formula of MSE, if the value of MSE
is smaller, the quality of stego-images is better. Since both
the exhaustive least-signi"cant-bit substitution method and
our method get optimal solutions, two methods derive the
smallest value in Tables 4–6. The solutions oLered by genetic algorithm are not absolutely optimal solutions, so the
values may be either equal to or greater than the values
that are derived by exhaustive least-signi"cant-bit substitution method and our method. In part (a) of Tables 4–6, the
genetic algorithm gets the optimal solution because there
are few least-signi"cant-bit substitution samples. We can see
that all the values for the three methods are the same. The
situation is not quite the same as that in parts (b) and (c) of
Tables 4–6. The diLerence between the values of the genetic
algorithm and our method increases when k, the number of
least signi"cant bits of the embedded image to be embedded, grows bigger.
5. Conclusions
Image hiding plays an important role in data transmission. It goes without saying that the computation time and
quality of the stego-image are important research topics.
The exhaustive least-signi"cant-bit substitution method explores all the candidate substitution matrices to get the optimal solution. It becomes impractical when the number of
replaced bits is large. Although the genetic algorithm keeps
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
1593
Table 3
The computation time (unit: second) with Pepper as host image
Method
Jet
TiL
Boat
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.035
2.264
18.257
1.036
2.250
18.267
1.038
2.262
18.183
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.229
4062.495
19.048
1.232
4066.779
19.213
1.232
4068.489
19.067
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
1.712
Too huge
20.587
1.710
Too huge
20.565
1.714
Too huge
20.594
Table 4
The MSE between Lena and stego-image
Method
Jet
TiL
Boat
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
2.3460
2.3460
2.3460
2.2950
2.2950
2.2950
2.2530
2.2530
2.2530
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
9.7210
9.7210
9.7956
9.3782
9.3782
9.3955
9.4737
9.4737
9.5165
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
33.3233
Not available
34.1974
the computation time in a certain range, the solutions are
merely near optimal. It directly inNuences the quality of
the stego-images. In this paper, we proposed an optimal
least-signi"cant-bit substitution in image hiding using the
dynamic programming strategy. Both the computation time
and the quality of the stego-images are both better than
the methods proposed in [8]. The experimental results also
demonstrate that our method gives quite an impressive performance.
6. Summary
Data hiding techniques embed important data into multimedia data such as images, videos or movies. In this
33.2183
Not available
34.7052
34.8507
Not available
36.1665
paper, we take an image for a carrier of the embedded data
and name it a host image. When we discuss image hiding,
one of the most important things is that the quality of the
multimedia data must not be degraded too much after embedding. The goal of data hiding is to make the embedded
data invisible to grabbers. Thus, if the embedding degrades
the quality of the multimedia data too much, any grabber will easily take notice of it. Least-signi"cant-bit-based
(LSB-based) data hiding techniques are simple to achieve
this purpose. A least-signi"cant-bit-based method replaces
some least signi"cant bits of the medium data with the
embedded data. In this research, the major task is to make
it extremely hard for grabbers to sense the existence of
the embedded data. The optimal least-signi"cant-bit substitution here uses human perceptual models to achieve
1594
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
Table 5
The MSE between Barb and stego-image
Method
Jet
TiL
Boat
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
2.3530
2.3530
2.3530
2.3060
2.3060
2.3060
2.2653
2.2653
2.2653
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
9.7187
9.7187
9.7617
9.3823
9.3823
9.4476
9.4704
9.4704
9.4876
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
33.3242
Not available
34.6808
33.2026
Not available
35.1498
34.8720
Not available
36.3747
Jet
TiL
Boat
Table 6
The MSE between Pepper and stego-image
Method
(a) The secret images are 128 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
2.3506
2.3506
2.3506
2.3022
2.3022
2.3022
2.2647
2.2647
2.2647
(b) The secret images are 192 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
9.7111
9.7111
9.7818
9.4126
9.4126
9.4303
9.4616
9.4616
9.5103
(c) The secret images are 256 × 512
Our method
Exhaustive least-signi"cant-bit substitution
Genetic algorithm
33.2655
Not available
34.7647
this goal. In order to "nd the optimal result, the procedure
of the exhaustive least-signi"cant-bit substitution must go
exhaustively through all possible least-signi"cant-bit substitutions. When the embedded data take the place of the
rightmost k least signi"cant bits of the host image, k being
large, it takes huge computation time and makes the method
impractical. In 2001, Wang et al. proposed the method that
uses a genetic algorithm to search for approximate optimal
solutions of least-signi"cant-bit substitution, and the computation time is no longer as high as that of the exhaust
least-signi"cant-bit substitution. Although Wang et al.’s
method reduces the computation time, the results it achieves
are not optimal but “approximate” optimal solutions. In this
paper, we have used the dynamic programming strategy to
solve the optimal least-signi"cant-bit substitution problem.
The experimental results show that our method signi"cantly
33.0889
Not available
34.5167
34.7991
Not available
36.5978
reduces the computation time and also achieves optimal
solution.
References
[1] Y.H. Chu, S. Chang, Dynamical cryptography based on
synchronized chaotic systems, Electron. Lett. 35 (12) (1999)
974–975.
[2] H.J. Highland, Data encryption: a non-mathematical approach,
Comput. Security 16 (1997) 369–386.
[3] D.W. Bender, N.M. Gruhl, A. Lu, Techniques for data hiding,
IBM Systems J. 35 (1996) 313–336.
[4] W.D. Chun, T.E. Hsiang, Data hiding in images via
multiple-based number conversion and lossy compression,
IEEE Trans. Consumer Electron. 44 (4) (1998) 1406–1412.
C.-C. Chang et al. / Pattern Recognition 36 (2003) 1583 – 1595
[5] C.C. Chang, K.F. Hwang, M.S. Hwang, A block based
digital watermarks for copy protection of images, Proceedings
of Fifth Asia-Paci"c Conference on Communications/Fourth
Optoelectronics and Communications Conference, Beijing,
China, Vol. 2, 1999, pp. 977–980.
[6] S.D. Lin, C.F. Chen, A robust DCT-based watermarking for
copyright protection, IEEE Trans. Consumer Electron. 46 (3)
(2000) 415–421.
1595
[7] C.F. Wu, W.S. Hsieh, Image re"ning technique using digital
watermarking, IEEE Trans. Consumer Electron. 46 (1) (2000)
1–5.
[8] R.Z. Wang, C.F. Lin, J.C. Lin, Image hiding by optimal LSB
substitution and genetic algorithm, Pattern Recognition 34
(2001) 671–683.
[9] E. Horowitz, S. Sahni, S. Rajasekaran, Computer Algorithms/
C++, Computer Science Press, New York, 1998, 254pp.
About the Author—CHIN-CHEN CHANG received his BS degree in Applied Mathematics in 1977 and his MS degree in Computer and
Decision Sciences in 1979, both from the National Tsing Hua University, Hsinchu, Taiwan. He received his Ph.D. in Computer Engineering
in 1982 from the National Chiao Tung University, Hsinchu, Taiwan. During the academic years of 1980 –1983, he was on the faculty of
the Department of Computer Engineering at the National Chiao Tung University. From 1983–1989, he was on the faculty of the Institute
of Applied Mathematics, National Chung Hsing University, Taichung, Taiwan. Since August 1989, he has worked as a professor in the
Institute of Computer Science and Information Engineering at National Chung Cheng University, Chiayi, Taiwan. Dr. Chang is a Fellow
of IEEE, a Fellow of IEE and a member of the Chinese Language Computer Society, the Chinese Institute of Engineers of the Republic of
China, and the Phi Tau Phi Society of the Republic of China. His research interests include computer cryptography, data engineering, and
image compression.
About the Author—JU-YUAN HSIAO received his BS degree in Computer Engineering in 1986 from the National Chiao Tung University,
Hsinchu, Taiwan and the MS degree in Applied Mathematic in 1988 from the National Chung Hsing University, Taichung, Taiwan. He
received his Ph.D. in Computer Science and Engineering in 1992 from the National Tsing Hua University, Hsinchu, Taiwan. During the
academic years of 1995 –2000, he was on the faculty of the Department of Business Education at the National Changhua University of
Education, Changhua, Taiwan. Since August 2000, he has worked as a professor and chairman in the Department of Information Management
at National Changhua University, Changhua, Taiwan. Dr. Hsiao’s research interests include information security, algorithm design, and
image processing.
About the Author—CHAN CHI-SHIANG received his BS degree in Computer Science in 1999 from the National Cheng Chi University,
Taipei, Taiwan and the MS degree in Computer Science and Information Engineering in 2001 from the National Chung Cheng University,
ChiaYi, Taiwan. He is currently a Ph.D. student at the Institute of Computer Science and Information Engineering at the National Chung
Cheng University, Chiayi, Taiwan. His Research "elds are image hiding and image compression.