Supports for Identity Management in Ambient Environments
advertisement

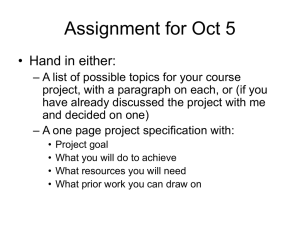
Supports for Identity Management in Ambient Environments – The HYDRA Approach I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Hasan Akram (MSc.-Inform.) Researcher Fraunhofer Institute for Secure Information Technology Mario Hoffmann (Dipl.-Inform.) Head of Department “Secure mobile Systems“ Fraunhofer Institute for Secure Information Technology Wireless becomes ambient and intelligent Loss of control Surveillance ss e c e i eevvic01177““ d ss dn 220 s e s lle le iin ruumm e r e i r opple h FFoor i w w nn ppeeo earrcch o i l o irillli lliioonn Reessea r t 77 t bbiill orrldld R “ “ 77 sFP6)WWo (SWAMI-Safeguards in a World of Ambient Intelligence,rEU-Project, o r ffo irelelesss ire Profiling W W “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Rapidly Increasing Amount of Personalisable Information “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Identity Management Roadmap “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta User-centricity A question of the perspective IN COMPANY DATABASES INTELLIGENT ENVIRONMENTS GOVERNMENT & ADMINISTRATION PERSONALISED ONLINE SERVICES PROFESSIONAL ATTACKERS “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta (Research) Challenges for User-centric Identity Management Citizen Employee • User Empowerment – – – – User-controlled Identity Management Informational Self-determination Minimisation of Information Disclosure Transparency • Support of Anonymity & Pseudonymity Customer Individuum Victim – Application level – Middleware – Access and Core Networks • Privacy-enhanced Personalisation – Best Practice – Rise Awareness • New Development Tools for Ambient Environments – Efficient and flexible Service Creation – Security & Privacy by Design (default configuration) “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta The Backend for Ambient Intelligent Systems Networked Embedded System Middleware for Heterogeneous Physical Devices in a Distributed Architecture The Hydra project is co-funded by the European Commission within the Sixth Framework Programme under contract IST-2005-034891 Partners 1 2 3a 3b 4 5 6 7 8 9 10 11 12 13 C International Ltd., UK CNet Sweden AB, SE Fraunhofer Institute for Applied Information Technology, DE Fraunhofer Institute for Secure Information Technology, DE In-JeT ApS, DK Priway, DK T-Connect, IT Telefónica I+D, ES University of Aarhus, Dept. of Computer Science, DK Innova S.p.A., IT University of Reading, Informatics Research Centre, UK MESH Technologies, DK Siemens Business Services, DE Technical University of Kosice The main challenge for implementation of ambient computing in networked embedded systems is to support the self-adaptive interplay of a vast range of existing and new components. 3 major objectives: - middleware tool that allows developers to develop systems with embedded, autonomic ambient intelligence computing - middleware tool that hides the complexity of the underlying infrastructure - make new and existing distributed device networks trustworthy and secure, robust and fault tolerant “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Outlook: Prototype ICT Summit, 25th-27th Nov 2008, Lyon, France The photo shows the so-called “Kosice scenario“ realising an ambient intelligent heating breakdown. The demonstrator comprises: - Hydra-based Building Automotion System (HBAS) on Sony Playstation 3 - Larger-than-life smart phone model receiving the breakdown message - The technician‘s Tablet PC with Smartcard unit (left outside the photo) - Animated Flash cartoons explaining the process “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta HYDRA Scenario: 1. Breakdown of the Heating System • 2. Resident receives error • 3. Send request with context specific token Approach of the service agent • 4. Context information to enhance resolution process Token is co-signed by service provider Firmware update • Restricted access to internet based on context “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Hydra‘s Security by Design Approach Ambient Security 15 1 H e a tin g S y s te m HYDRA P ro x y 14 11 10 S e rv ic e Agent 2 12 F irm w a re D a ta b a s e 13 Confidentiality Integrity Authenticity Authorisation Availability Non-repudiation Privacy 8 Authorisation H Y D R A -b a se d B u ild in g A u to m a tio n S y s te m 9 D Step: « 6 7 8 » D oor Lock 5 Sub-Process Semantics Middleware Network Devices 7 3 6 S e rv ic e A gent 4 R e s id e n t 16 17 “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann S e rv ic e P ro v id e r I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Hydra‘s Security by Design Approach Virtualisation Ambient Security 15 1 H e a tin g S y s te m HYDRA P ro x y Integration of Trust Models 14 11 10 S e rv ic e Agent 2 12 F irm w a re D a ta b a s e 13 Semantic Resolution of Security Confidentiality Integrity Authenticity Authorisation Availability Non-repudiation Privacy 8 H Y D R A -b a se d B u ild in g A u to m a tio n S y s te m 9 Step: « 6 7 8 » D oor Lock 5 Authorisation D Sub-Process Semantics Middleware Network Devices 7 Support of Identity Management 3 6 S e rv ic e A gent 4 R e s id e n t 16 17 “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann S e rv ic e P ro v id e r I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta HYDRA‘s Ten Laws of Identity 1. 2. User Empowerment: Awareness and Control Minimal Information Disclosure for a Constrained Use 3. Non-repudiation 4. Support for directional identity topologies 5. Universal Identity Bus 6. Provision of defining strength of identity 7. Decoupling identity management layer from application layer 8. Usability issue concerning identity selection and disclosure 9. Consistent experience across contexts 10. Scalability “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta HYDRA Identity Law 1 • User Empowerment: Awareness and Control e e r ? r a ? ? a ? ? w ? s w a s e a e r c r c e n e s n e s u e u u u e q e q h e h e t s t s n s IIs ccoon e e h h t t f f oo “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta HYDRA Identity Law 4 • Support for directional identity topologies “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta HYDRA Identity Law 7 • Decoupling identity management layer from application layer “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Architecture/Implementation “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta 1. User Empowerment 2. Minimal Disclosure 3. Non-repudiation 4. Directional Identity 5. Universal Identity Bus 6. Strength of Identity 7. Decoupling Layers 8. Usability 9. Context Consistency 10. Scalability + o + ++ “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann + ++ o o ++ ++ ++ + o ++ + ++ ++ ++ ++ Sh ib ol et h H ig gi ns Li be rt y H IM Sp ac e ar d C pe nI D O Hydra Identity Laws SA M L State of the Art Evaluation ++ o o + + + ++ ++ ++ ++ ++ ++ + o + ++ o o ++ ++ ++ ++ + ++ + + ++ ++ ++ + I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Socio-Political Frameworks & Legal Aspects http://www.privacyinternational.org/ “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Summary • Different perspectives allow different interpretations of the term “user-centric” – The perspective of the user is decisive! • Privacy enhancing technologies (e.g. on middleware layer) have to enable developers to design privacy preserving applications • Socio-political environments and legal constraints have to be taken into account • Privacy and data protection needs support from politics and society “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta Contact Mario Hoffmann (Dipl.-Inform.) Head of Department “Secure mobile Systems“ Address Fraunhofer Institute for Secure Information Technology Rheinstrasse 75 64295 Darmstadt Germany Tel Fax e-Mail +49-(0)6151/869-60034 +49-(0)6151/869-224 mario.hoffmann@sit.fraunhofer.de “Supports for Identity Management in Ambient Environments – The HYDRA Approach”, Hasan Akram, Mario Hoffmann I-Centric 26th Oct – 31st Oct, 2008, Sliema, Malta