A Convenient Method for Securely Managing Passwords
advertisement

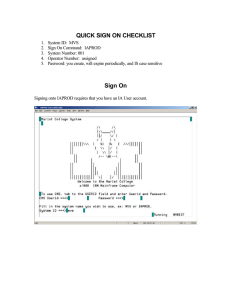
A Convenient Method for Securely Managing Passwords 1 J. Alex Halderman Brent Waters Edward W. Felten Princeton Stanford Princeton J. Alex Halderman ****ing Passwords! • Web site password overload Generating, keeping secret, and recalling passwords for scores of sites • Leads to insecure coping techniques – Writing passwords down – Reusing same passwords • Difficult to enforce better behavior We need to make password security easy 2 J. Alex Halderman In This Talk 1. Approaches to password management 2. Our construction and its security 3. Comparison with other techniques 4. Demonstration of our implementation 5. Future work and conclusions 3 J. Alex Halderman Approaches to Password Mgmt • Local encrypted storage e.g., Password Safe (1998) – Cumbersome to access from multiple locations • Centralized remote authentication e.g., Microsoft Passport (1999) – Needs server-side changes, trusted third party • Cryptographic password generation e.g., LPWA (1997), PwdHash (2004), our scheme (2004) 4 J. Alex Halderman Password Generators Master Password “amazon.com” Hash() “wrbPzdqS” Use as your Amazon password • E.g.: LPWA, PwdHash • Client software derives individual site passwords using deterministic one-way function • Users sets all site passwords to function output • Only need to remember master password to recreate all site passwords—highly transportable! A simple idea, but hard to get right! 5 J. Alex Halderman Stealing the Master Password Password Guess “yahoo.com” “lassie” “rover” “spot” “fido” Hash() “H2VeusSq” “CJPZfAKx” “RWwsYlTi” “LZIniBNd” == =? “LZIniBNd” “LZIniBNd” Adversary learns password from low-security site Dictionary attack to learn master password amazon.com wrbPzdqS gmail.com obIDmogl citibank.com sX4rLlO1 Can access all other password-managed sites Easy to execute because scheme use fast hashes 6 J. Alex Halderman Thwarting Brute Force Attacks attack cost = ½ × dictionary size × cost per guess • Hard to increase dictionary size User habits hard to change, limits on human memory • Increase cost per guess by using slower hash – Used elsewhere to protect password verification routines (UNIX crypt) – Our approach: iterated hash • Security vs. usability tradeoff User has to wait too! — Cache intermediate results 7 J. Alex Halderman Initialization Phase Our Construction Master password User identity “MyD06ReX” “jhalderm@princeton.edu” Hk1() Generation Phase Local Cache Master password (again) Hk2() J. Alex Halderman Target site “amazon.com” Mapping “wrb8zdqS” 8 (k1 >> k2) User’s site password for “amazon.com” Security Analysis Four attack scenarios: 1. No information ? 2. Stolen site password ? 3. Stolen cache data ? 4. Stolen cache + site password Primary concern is offline attacks. 9 J. Alex Halderman Increasing external difficulty Security of Our Scheme Attack scenario Hashes/ Time/ guess guess 1. No information N/A N/A 2. Stolen site password k1+k2 100.1s 3. Stolen cache data k1 100s 4. Stolen cache + site password k2 0.1s 10 J. Alex Halderman Relative Attack Resistance Estimated time to test 100,000 guesses Scheme Stolen password Stolen data Stolen pw and data Password Safe N/A 74.6 secs 74.6 secs LPWA 0.5 secs N/A N/A PwdHash 0.1 secs N/A N/A Our Scheme 116 days 116 days 2.8 hours 11 J. Alex Halderman Equivalent Password Length PwdHash LPWA Our Scheme 12 ********* ******** **** J. Alex Halderman Password Multiplier • Extension for Mozilla Firefox Windows, Mac OS X, and Linux • Tightly integrated with browser Double-click any password field to fill in • Balanced security and convenience – Initialization — 108 iterations, ~100 seconds (Only once per installation) – Password generation — 105 iterations, ~0.1 secs (Before every password operation) 13 J. Alex Halderman Password Multiplier — Demo 14 J. Alex Halderman Future Improvements • Flexible password formatting Cope with sites that require numbers, punctuation, special patterns • Easier password changes Manually and at regular intervals • Improved anti-spoofing Adopt techniques from PwdHash • Port to Internet Explorer, others 15 J. Alex Halderman Require additional “state” Summary — Our scheme: • Provides password access from anywhere our software can be executed • Asks user to remember only one short password • Requires no server-side changes • Does not require trusting a third-party service • Nearly as secure as independent random pwds • Likely much more secure than what you do now • Is practical, available today, and free http://www.cs.princeton.edu/~jhalderm/projects/password/ 16 J. Alex Halderman A Convenient Method for Securely Managing Passwords 17 J. Alex Halderman Brent Waters Edward W. Felten Princeton Stanford Princeton J. Alex Halderman