Midterm2Summer07.doc
advertisement

Grader Use Only:
#1
CMSC132
Summer 2007
Midterm #2
(20)
#2
(10)
#3
(12)
#4
(12)
#5
(10)
#6
(36)
Total
(100)
First Name: _______________________
Last Name: _______________________
Student ID: _______________________
Section time ___________ TA: __________________________
General Rules (Read):
This exam is closed book and closed notes.
If you have a question, please raise your hand.
Total point value is 100 points.
Answer True/False questions by circling the True or False at the end of the question.
Answer essay questions concisely using 1 or 2 sentences. Longer answers are not necessary and
are discouraged.
WRITE NEATLY. If we cannot understand your answer, we will not grade it (i.e., 0 credit).
1
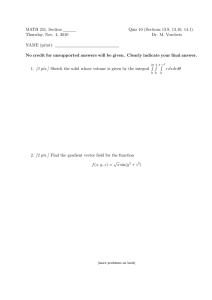
1. (20 pts) Heaps/Trees
Use the following binary tree/heap to answer the questions that follow.
8
9
11
10
13
12
14
a.
What is the big O notation for heapsort?
b.
Heaps are balanced trees. True/False.
c.
A heap is a binary search tree. True/False.
d.
List the order nodes are traversed in an depth-first search traversal of the tree.
e.
List the order nodes are traversed in a breadth-first traversal of the tree.
f.
Draw the heap that would result from inserting 5 in the above heap.
g.
Draw the heap that would result by deleting 8 from the original heap.
2
2. (10 pts) Huffman
A
B
0
1
C
0
1
0
D
0
E
1
1
a.
(3 pts) Use the above Huffman tree to encode the string “BD”. Show the resulting code.
b.
(3 pts) Use the above Huffman tree to decode the code “0111”. Show the resulting string.
c.
(6 pts) Create a Huffman tree for the symbols M, P, R, and T which have the following
frequencies:
M:4
P:5
You don’t need to assign 0’s and 1’s.
3
R:8
T:7
3. (12 pts) Hashing
a.
b.
(2 pts) Using hashing we can achieve a complexity of O(1) during the retrieval of an element.
True/False.
(2 pts) What is the load factor?
i.
ii.
iii.
iv.
Number of entries in the hash table divided by table size
Maximum number of entries that can be placed in the table
The load generated by the multiplicative congruency method
None of the above.
c.
(2 pts) The hashCode method for a class always returns the number 14. Is this a valid
hashCode method for the class? True/False.
d.
(2 pts) Hashing is efficient for a load factor that is less than:
i.
ii.
iii.
iv.
e.
99%
90%
80%
None of the above.
(4 pts) Mention two properties of a good hash function. Notice we are not asking about the
properties of the Java hashCode method.
4
4. (12 pts) Dijkstras’ Algorithm
1
D
2
A
E
2
2
4
B
7
F
5
C
4
Run Dijkstra’s shortest path algorithm on the previous graph using B as the start vertex. Show the
entries in the following table after adding the first 3 nodes (B & 2 other nodes) to the set S of
processed nodes (as defined by Djikstra’s algorithm). Keep in mind that after adding a node to the
set S you must adjust the cost/predecessor of the appropriate successor nodes. You can assume
that initially the cost of all nodes (except the start vertex) is ∞ and the predecessor of every node
is none.
A
B
C
LowestCost
Predecessor
5
D
E
F
5. (10 pts) GUIs
Consider the following Java Swing code that uses a JSlider object. A JSlider object let’s the user
graphically select a value by sliding a knob. The following is a snapshot of a slider:
The stateChanged method is called when we move the knob.
public class JSliderPanel extends JPanel {
private JSlider jSlider;
public JSliderPanel() {
add(jSlider=new JSlider(JSlider.HORIZONTAL));
jSlider.addChangeListener(new Handler());
}
class Handler implements ChangeListener {
public void stateChanged(ChangeEvent e) {
System.out.println("Slider action");
}
}
}
a.
(2 pts) In the above code, which class represents the view?
b.
(2 pts) In the above code, which class represents the controller?
c.
(6 pts) Write a new JSliderPanel constructor that uses an anonymous inner class to implement
the same ChangeListener for the JSlider.
public class JSliderPanel extends JPanel {
private JSlider jSlider;
public JSliderPanel() {
add(jSlider=new JSlider(JSlider.HORIZONTAL));
// YOUR CODE HERE
6
}
}
6. (36 pts) Binary Trees
a.
We generate a balanced binary search tree when elements are inserted in sorted order.
True/False
b.
The following Java class definition for a binary search tree will be used to answer the
questions below. Feel free to add an auxiliary method during the implementation of any
method. Non-recursive solutions will receive no credit.
public class BinarySearchTree <E> {
class Node<T> {
T data;
Node <T> left, right;
public Node(T data) {
this.data = data;
left = right = null;
}
}
Node <E> root; // Tree Root
// YOU MUST IMPLEMENT A DEFAULT CONSTRUCTOR
public boolean isEmpty() {
// YOU MUST IMPLEMENT THIS METHOD
}
public int numberOfLeaves() {
// YOU MUST IMPLEMENT THIS METHOD
}
public ArrayList<E> decreasingOrder() {
// YOU MUST IMPLEMENT THIS METHOD
}
}
i.
ii.
iii.
Constructor – Define a default constructor that creates an empty binary search tree.
isEmpty – Returns true if the tree is empty and false otherwise.
numberOfLeaves – Implement a method named numberOfLeaves . The method
returns the number of leaf nodes present in the tree.
iv. decreasingOrder – Implement a method named decreasingOrder . It returns an
ArrayList object with the data elements of the tree in decreasing order. If the tree is
empty the method will return an empty ArrayList object.
YOU CAN IMPLEMENT THE METHODS ON THE NEXT PAGE
7
8
9
10