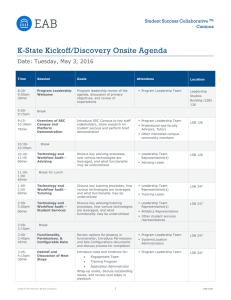
The SIJ Transactions on Computer Science Engineering & its Applications (CSEA), Vol. 2, No. 2, March-April 2014 An Overview of Image Hiding Techniques in Image Processing R. Rathna Krupa* *Department of Information Technology, The Standard Fireworks Rajaratnam College for Women, Sivakasi, Tamilnadu, INDIA. E-Mail: rathnakrupa89@gmail.com Abstract—Image hiding techniques embed a secret image into another image. The fusion of the secret image and the cover image is the resultant stego image. Using the image hiding techniques, existence of the secret image in the final image will be unaware by an unintended observer, so that it can be relocated carefully. One of the common techniques is the LSB (Least Significant Bit) substitution method. It includes the manipulation of the least significant bits in the original image. To enhance the quality of the final image the Optimal Pixel Adjustment Process - OPAP which disarranges the image bits is used. In this paper, different types of LSB schemes and image enhancing schemes are focused. Keywords—Embedding Techniques; Image Embedding; Image Hiding; Least Significant Bits Substitution; Optimal Pixel Adjustment Process. Abbreviations—Least Significant Bit (LSB); Mean Square Error (MSE); Moderately Significant bit (MSB); Optimal Pixel Adjustment Process (OPAP). I. I INTRODUCTION NTERNET has become more popular and common nowa-days. Sending the important data through the net has become a serious threat. Moreover routing the data in an encrypted format is very common and embedding the secret message in an image is a challenge. To safeguard the images from the illegal hindrance or interception, techniques such as watermarking, image hiding is used for the safe transmission of images. This paper focuses on such techniques and ideas. A watermark is a signal or a pattern that is embedded into an image. It is usually done for content authentication. Watermarking methods are divided into: fragile watermarking methods and robust watermarking methods. In robust watermarking methods, the secret information will always be robust against any changes or malfunctions. They are usually used for protecting copyrights. On the other hand, fragile watermarking methods are usually designed so that they can easily get broken. Therefore it is applicable for tamper detection and authentication. Chandramouli & Nasir Memon (2001) has used the watermarking technique with public key verification for watermark insertion and extraction procedure. This can be used for fingerprinting, ownership assertion and for ID-card security purpose. Image authentication against the quantization attack has been proposed by Hongtao Lu et al., (2003). In watermarking, the size of the symbol should be usually small, ranging from one bit to thousands of bits to represent the symbol. The goal of watermarking focuses on the existence of the symbol which is usually small after undergoing certain manipulations and by degrading ISSN: 2321-2381 operations such as filtering, resampling, lossy compression, etc. But in Image Hiding, it is mainly used to transmit important and confidential images, whose size tends to be very large. Many image hiding methods have been proposed by Thien & Lin (2003), Chan & Cheng (2004), Li Zhi & Sui Ai Fen (2004), Wang & Tsai (2007), Wang & Moulin (2007) and many more. Most of these methods does not consider about the compressing of cover image. But Chung et al., (2001) proposed the usage of singular value decomposition and vector quantization for compressing the cover image. The goal of the image hiding technique is to hide the secret image in such a way that it is invisible to the viewers.The Least Significant Bit substitution method and Optimal Pixel Adjustment process are the two image hiding techniques in which the LSB method is used for embedding the secret image and the OPAP method is used for enhancing the final image so that the presence of the secret image is not visible. Wang et al., (2001) proposed a method called the Moderately Significant Bit (MSB) where the fourth bit is taken into account for image hiding. This paper deals with all the facts used for the procedure of hiding the image and making the secret message invisible to the grabbers. This paper is organized as follows. The section II gives the details of how the LSB method works for hiding an image and the other algorithms that is suggested for efficient image hiding mechanism. The section III describes the Optical Pixel Adjustment Process which is used to improve the quality of the resultant image, so that the embedded image is unlikely to be seen by naked eyes. The section IV describes the statistical analysis process to measure the quality of the final image. © 2014 | Published by The Standard International Journals (The SIJ) 30 The SIJ Transactions on Computer Science Engineering & its Applications (CSEA), Vol. 2, No. 2, March-April 2014 The section V explains about the experimental results. In the final section the conclusion of this survey and future work about image hiding is reported. The objective of this study is to know about the image hiding techniques and means to enhance the quality of the image after an image is embedded into it so that protection of the data is maintained. II. LEAST SIGNIFICANT BIT SUBSTITUTION METHOD Every pixel in an image indicates a color and the each image is made up of pixels. The lower values of the pixel in a gray scale image signifies dark areas and the higher values signify light areas. So in order to adjust the shades of the image its values can be adjusted and 8 bits are required to represent these values [Lin-Yu Tseng et al., 2008]. For example consider the following 8-bit binary sequence: 10110011. Summing up all these values where 1 exists, will yield a result of 179. The right-most value is the LSB of this sequence. This value essentially determines whether the total sum is odd or even. If the LSB is a 1, then the total will be an odd number, and if 0, it will be an even number. However, changing the LSB value from a 0 to a 1 does not have a huge impact on the final result. Each 8-bit binary sequence is used for expressing the color of a pixel for an image, so changing the LSB value from a 0 to 1 does not impose a major change and it is unlikely to be noticed by an observer. In fact, the LSBs of each pixel value could be potentially modified, and the changes would still not be visible. This provides an enormous amount of redundancy in the image data, which means that we can effectively substitute the LSBs of the image data, with each bit of the message data until the entire message has been embedded. This is meant by Least Significant Bit Substitution Method. The procedures used in the LSB method are: Get the input cover image and message image. Resize the message image same as that of cover image. Shift the message image pixel values over four bits to right. Make last four bits (LSBs) in the pixel values of the cover image to zero. Finally add the images obtained from step 3 and 4 to get final image. There are other several LSB techniques used for image hiding. They are: LSB array based technique using encryption by RSA algorithm in which four least significant bits are explored by Gandharba Swain & Saroj Kumar Lenka (2012). Transforming LSB Substitution for Image-based Steganography in Matching Algorithms [ChengHsing Yang & Shiuh-Jeng Wang, 2010]. LSB substitution based on image blocks and maximum entropy [Mohamed Radouane et al., 2013]. ISSN: 2321-2381 Dumitrescu et al., (2003) used a technique that is based on a finite state machine whose states are selected multisets of sample pairs, called trace multisets. Some of the trace multisets are equal in their expected cardinalities, if the sample pairs are drawn from a digitized continuous signal. Random LSB flipping causes transitions between these trace multisets with given probabilities, consequently alters the statistical relations between the cardinalities of trace multisets. The method proposed by Puech (2009) combines compression, data hiding and partial encryption of images in a single processing step. This approach can embed data into the image according to the message size and partially encrypt the image and the message without changing the original image content. LSB based techniques pose a difficult challenge to a stego-analyst as it is difficult to differentiate final image and the cover image which is given as input. The differences between them will be very slight. Major advantage of this method is, it is quick and easy. This method works well with gray scale images. It is mainly used for image integrity. The quality of the embedding result cannot be degraded so significantly that the grabbers may notice the existence of the important data [Ran-Zan Wang et al., 2001]. Figure 1: Cover Image Figure 1 is the cover image in which the message image is going to be hidden. It is a grey scale image and this is the image which will be seen clearly by the viewer. Figure 2: Secret Image/Message Image © 2014 | Published by The Standard International Journals (The SIJ) 31 The SIJ Transactions on Computer Science Engineering & its Applications (CSEA), Vol. 2, No. 2, March-April 2014 Figure 2 is the secret image that is going to be embedded in the cover image. This image is also a grey scale image in which the each pixel is shifted right for undergoing the LSB method. 2.3. Pixel Value Differencing In this method the cover image is divided into blocks that consist of two consecutive pixels and the difference between them is also calculated. If the difference is large then it means they are present at the edged areas otherwise they are present at smooth areas. The pixel in the edged area can have larger amount of pixel values. So, more data can be hidden in the edged areas [Rahul Samant & Shrikant Agrawal, 2011]. Before embedding, the difference value is then replaced by the new value. This method is more efficient than the LSB replacement scheme and it is more easy and feasible too. III. Figure 3: Result of LSB Method After applying the LSB method the resultant image is the one that is given in Figure 3.In Figure 3 the secret image is slightly visible when it is seen keenly. This can be tackled by using some image enhancing algorithms such as Optimal Pixel Adjustment Process. 2.1. Optimal LSB When LSB method is used for data hiding, the resultant image which is the stego image has only small differences when compared with the cover image, but the differences can be easily detected using statistical analysis. So Optimal LSB insertion which is an enhanced method is used for getting more accurate stego image. In this method an adjustment process is used to find the correct matching pixel. The closest pixel value when compared with the secret image to that of cover image is selected and then embedding is done in that optimal pixel. This method is more efficient, but finding the closest pixel requires an additional phase. This method first starts by initialising three pixel values and comparison takes place with the cover image pixel which is used to improve the quality and decrease the error in the stego image [Morteza Bashardoost et al., 2013]. OPTIMAL PIXEL ADJUSTMENT PROCESS An optimal pixel adjustment process is proposed to enhance the quality of the final image obtained by the simple LSB substitution method. Moreover, the Optimal Pixel Adjustment Process only requires a checking of the embedding error between the original cover image and the final image obtained by the LSB method to form the final enhanced final image. In-order to improve the quality different techniques has been followed. Zhang and Wang introduced Exploiting Modification Direction (EMD). Furthermore Lee et al., (2007) proposed an improved scheme where it uses two pixels at a time, and gives both pixels a fixed evaluation value. Both these techniques get compromised if encryption techniques become public. So Wen-Chung Kuo (2013) used two kinds of weight-changing evaluation EMD data hiding strategy. One of them uses the table checking and the other uses EMD data hiding. According to the Optimal Pixel Adjustment Process if the error lies between the particular range, then pixels of the image that is retrieved after the LSB method is manipulated accordingly and then the enhanced image pixel is processed. For example if the error lies between 2 k-1 to 2k and if the pixel of the image that is produced from the LSB method is greater than 2k then the pixel present in the final enhanced image is processed with the pixel from the LSB method otherwise the enhanced image pixel will be similar to the input image pixel. In the same way if the error lies between -2k-1 to 2k-1, the pixel in the enhanced image will not be modified [Chi-Kwong Chan & Cheng, 2001]. 2.2. LSB Matching Scheme The LSB Matching scheme also modifies the least significant bits of the pixel for hiding the image but if any one of the bit in the secret image does not match the LSB of the cover image, then random addition or subtraction of the bits from the cover image pixel takes place [Ker, 2004]. In this process if the number of bits in the message image is lesser than the cover image, then pseudo-random permutation is used to deal with it. In the LSB replacement scheme the LSB’s of the cover image is overwritten by the secret bit stream and the other procedures are similar to the LSB Matching Scheme. It has an advantage of being computationally less complex when compared with other schemes. Figure 4: Result of Optimal Pixel Adjustment Process ISSN: 2321-2381 © 2014 | Published by The Standard International Journals (The SIJ) 32 The SIJ Transactions on Computer Science Engineering & its Applications (CSEA), Vol. 2, No. 2, March-April 2014 Figure 4 is the final image where the image that is retrieved after undergoing the LSB method is used in the OPAP process as the input image. This Optimal Pixel Adjustment Process improves the quality of the final image, by reducing the Mean Square Error between the cover image and the final image. So the hackers will not be aware of the secret image hidden in it. The Computational complexities are also reduced considerably. By doing simple adjustment in the pixel values, the enhanced image can easily obtained. Once the image is sent over the internet, the receiver receives it and uses a simple image retrieval algorithm to retrieve the message in it. There will be some degradation of message quality due to loss of least significant bits. So the contrast will be decreased slightly but this will be negligible. Message Image Cover Image Least Significant Bit Substitution Method Stego Image Wei Liu et al., (2010) proposed a resolution progressive compression scheme which compresses an encrypted image progressively in resolution, such that the decoder can observe a low-resolution version of the image, study local statistics based on it, and use the statistics to decode the next resolution level. IV. Then statistical analysis is done in order to study the quality of the images that is obtained from LSB substitution and OPAP process. The Mean Square Error (MSE) and the Peak Signal to Noise Ratio (PSNR) are the two error metrics used to compare image compression quality. Mean Square Error (MSB) is used to estimate the quality difference between the original cover image and the final image. The value of MSE should be as low as possible so that the quality of the resultant image is same as the cover image that was given as input. The value of the MSE will be equal to zero for identical Images. Peak signal-to-noise ratio (PSNR) represents a measure of the peak error. The higher the PSNR value, the better the quality of the final image. The equation for PSNR is, (255 )2 PSNR = 10log 𝑑𝐵. MSE The MSE value is necessary to calculate the value of PSNR [Lin-Yu Tseng et al., 2008]. V. Optimal Pixel Adjustment Process Enhanced Image Figure 5: Overall Process of Image Hiding Figure 5 represents the complete process of the image hiding mechanism in which the enhanced image with minimum Mean Square Error is achieved. The enhanced image which is the final image will have the embedded image hidden in it and it would be unseen by any observer or viewer. To find the difference between the cover image and final image statistical analysis method should be performed. 3.1. Recovery Process In order to recover the secret image at the receiver’s side the pixel of the image that is shifted left at the LSB process should be shifted right. The procedures are: Get the retrieved image as input. Shift the message image pixel values over four bits to the left. Message image is obtained. ISSN: 2321-2381 STATISTICAL ANALYSIS EXPERIMENTAL RESULTS This section presents experimental results obtained from two images. The first image is the cover image and the second one is the secret image. Whenever, according to the procedure done in Section III and Section IV which is the LSB and OPAP process, the Mean Square Error for the stego image is 42.06. The error will be even more higher if the Optical Pixel Adjustment Process is not made and that will be the reason for the slight visibility of the secret image in the cover image. When genetic algorithm is imposed in the final stego image the error will be decreased and the quality will also be enhanced considerably. Therefore, a good image hiding method should be easy to use and at the same time, the presence of the secret image should not be viewable. i.e. the value of Mean Square Error should be lesser and the PSNR value should be greater to get a proper enhanced result. VI. CONCLUSION The main goal of this paper is to show how secret image can be embedded and how it can be sent through the internet by fooling grabbers. Many problems are encountered when transferring important data over the network. A safe and secure procedure is needed to transfer them easily. For this purpose simple image hiding techniques are used and the quality of stego images is also improved by using different mechanisms. So the hackers may not the stego image and will © 2014 | Published by The Standard International Journals (The SIJ) 33 The SIJ Transactions on Computer Science Engineering & its Applications (CSEA), Vol. 2, No. 2, March-April 2014 know nothing about the embedded secret image in it. The experimental results show that the stego image and the cover image remain more or less identical which is the main focus of this paper. This means that a secret message can be sent to the destination without any glitch and this can be used for image integrity protection and in places where important, undisclosed secrets should be sent to the recipient. Research is going on in privacy protection and intellectual property rights protection. In the future, it is expected to find an even better technique and procedure to hide more data in a cover image. The future focus should be made on even more less modification in the cover image and the differences between the cover image and the stego image should be null when statistically analyzed. [10] [11] [12] [13] [14] [15] REFERENCES [1] [2] [3] [4] [5] [6] [7] [8] [9] Ran-Zan Wang, Chi-Fang Lin & Ja-Chen Lin (2001), “Image Hiding by Optimal LSB Substitution and Genetic Algorithm”, International Conference on Pattern Recognition, Vol. 34, Pp. 671–683. R. Chandramouli & Nasir Memon (2001), “Analysis of LSB based Image Steganography Techniques”, Proceedings of International Conference on Image Processing, Vol. 3, Pp. 1019–1022. K.L. Chung, C.H. Shen & L.C. Chang (2001), “A Novel SVDand VQ-based Image Hiding Scheme”, Pattern Recognition Letters, Vol. 22, Pp. 1051–1058. Chi-Kwong Chan & L.M. Cheng (2001), “Improved Hiding Data in Images by Optimal Moderately Significant-Bit Replacement”, IEEE Electronics Letters, Vol. 37, No. 16, Pp.1017–1018. C.C. Thien & J.C. Lin (2003), “A Simple and High-Hiding Capacity Method for Hiding Digit-by-Digit Data in Images based on Modulus Function”, International Conference on Pattern Recognition, Vol. 36, No. 12, Pp. 2875–2881. Hongtao Lu, Ruiming Shen & Fu-lai Chung (2003), “Fragile Watermarking Scheme for Image Authentication”, IEEE Electronics Letters, Vol. 39, No. 12, Pp. 898–900. S. Dumitrescu, Xiaolin Wu & Zhe Wang (2003), “Detection of LSB Steganography via Sample Pair Analysis”, IEEE Transactions on Signal Processing, Vol. 51, No. 7, Pp. 355– 372. C.K. Chan & L.M. Cheng (2004), “Hiding Data in Images by Simple LSB Substitution”, Pattern Recognition, Pp. 469–474. Li Zhi & Sui Ai Fen (2004), “Detection of Random LSB Image Steganography”, Vehicular Technology Conference, Vol. 3, Pp. 2113–2117. ISSN: 2321-2381 [16] [17] [18] [19] [20] A. Ker (2004), “Improved Detection of LSB Steganography in Grayscale Images”, Proceedings of 6th International Workshop, Toronto (Canada), Vol. 3200, Pp. 97–115. Y. Wang & P. Moulin (2007), “Optimized Feature Extraction for Learning-Based Image Steganalysis”, IEEE Transactions Information Forensics Security, Vol. 2, No. 1, Pp. 31–45. C.F Lee, Y.R. Wang & C.C. Chang (2007), “A Steganographic Method with High Embedding Capacity by Improving Exploiting Modification Direction”, IIHMSP, Kaohsiung, Pp. 497–500. R. Wang & Y. Tsai (2007), “An Image-Hiding Method with High Hiding Capacity based on Best-Block Matching and KMeans Clustering”, Pattern Recognition, Vol. 40, No. 2, Pp. 398–409. W. Puech (2009), “Image Encryption and Compression for Medical Image Security”, Proceeding of IEEE Image Processing Theory, Tools & Applications, Pp. 1–2. Wei Liu, Wenjun Zeng, Lina Dong & Qiuming Yao (2010), “Efficient Compression of Encrypted Grayscale Images”, IEEE Transactions on Image Processing, Vol. 19, No. 04, Pp. 1097– 1102. Rahul Samant & Shrikant Agrawal (2011), “Data Hiding in Gray-Scale Images using Pixel Value Differencing”, Technology Systems and Management Communications in Computer and Information Science, Vol. 145, Pp. 27–33. Gandharba Swain & Saroj Kumar Lenka (2012), “A Technique for Secret Communication for New Block Cipher using Dynamic Stegnography”, International Journal of Security and its Applications, Vol. 6, No. 2, Pp. 1–12. Mohamed Radouane, Tarik boujiha, Rochdi messoussi, Nadia Idrissi & Ahmed Roukh (2013), “A Method of LSB Substitution based on Image Blocks and Maximum Entropy”, IJCSI International Journal of Computer Science Issues, Vol. 10, No. 1, Pp. 371–374. Morteza Bashardoost, Ghazali Bin Sulong & Parisa Gerami (2013), “Enhanced LSB Image Steganography Method by using Knight Tour Algorithm Vigenere Encryption and LZW Compression”, IJCSI International Journal of Computer Science Issues, Vol. 10, No. 2, Pp. 221–225. Wen-Chung Kuo (2013), “Data Hiding Schemes based on the Formal Improved Exploiting Modification Direction Method “, Applied Mathematics & Information Sciences Letters, Pp.81– 88. R. Rathna Krupa received the degree in Master of Science for computer science and Information Technology under Madurai Kamarajar University, Madurai. She has worked in open source projects at a private company in Rajapalayam, Virudhunagar. She has some special interests on research fields like image processing, data hiding and embedding. © 2014 | Published by The Standard International Journals (The SIJ) 34
advertisement
Related documents
Download
advertisement
Add this document to collection(s)
You can add this document to your study collection(s)
Sign in Available only to authorized usersAdd this document to saved
You can add this document to your saved list
Sign in Available only to authorized users