MALAYSIA’S NATIONAL CYBER SECURITY POLICY Critical Information Infrastructure Protection (CIIP)
advertisement
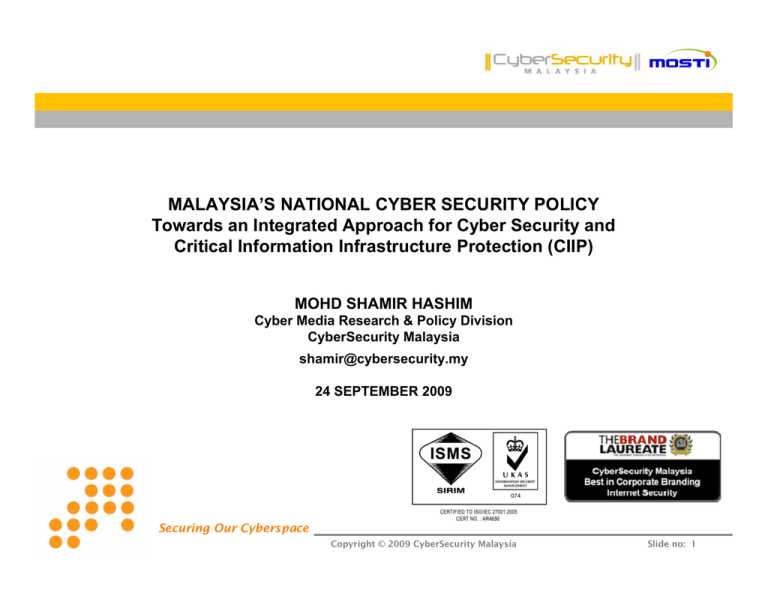
MALAYSIA’S NATIONAL CYBER SECURITY POLICY Towards an Integrated Approach for Cyber Security and Critical Information Infrastructure Protection (CIIP) MOHD SHAMIR HASHIM Cyber Media Research & Policy Division CyberSecurity Malaysia shamir@cybersecurity.my 24 SEPTEMBER 2009 Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 1 CYBER THREATS - Malaysia Technology Technology Related Related Threats Threats Hack Threat Intrusion Fraud Harassment Malicious Code Denial of Service Attack Cyber Cyber Content Content Related Related Threats Threats Threats to National Security Sedition / Defamation Online Porn Hate Speech Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 2 CYBER THREATS CyberSecurity Malaysia’s Analysis High LEVEL Required Knowledge to Attack Sophistication of Attacker’s Tools & Techniques Low 1985 1990 1995 2000 2005 Emerging Threats: large scale, sophisticated and damaging high connectivity creates opportunities to attackers network has everything i.e. financial gain, power, reputation, national secrets conflicts in physical world may lead to 2010 conflicts in cyber world Year Opportunities and capabilities can trigger cyber conflicts Cyber Terrorism / Cyber Warfare most likely to become a future threat Critical National Information Infrastructures (CNII) may become attractive targets Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 3 CYBER SECURITY INCIDENTS - MyCERT • A total of 11,780 security incidents were referred since 1997 (excluding spam) 2500 2000 2123 1942 Type of incidents: •Drones Report •Denial of Service •Fraud & Forgery •Vulnerability Probing •Harassment •Indecent Content •Malicious code •System Intrusion 1500 1372 1000 911 838 527 500 1038 865 625 347 196 81 915 As of August 2009 0 1997 1998 1999 2000 2001 2002 2003 2004 2005 2006 2007 2008 2009 Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 4 CYBER SECURITY INCIDENTS - MyCERT : CNII MALAYSIA • A total of 797 security incidents were referred from Jan-August 2009 441 450 400 Type of incidents: 350 300 •Spam •Drones Report 250 •Denial of Service •Fraud & Forgery 200 •Vulnerability Probing 150 •Harassment •Indecent Content 100 •Malicious code 50 •System Intrusion 274 67 0 8 Banking & Finance Government 2 3 Info & Comm Nat Defence & Sec 2 Energy Food & Agriculture Health Services Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 5 The National Cyber Security Policy formulated by MOSTI 2006 2005 THE NATIONAL CYBER SECURITY POLICY - Objective NCSP Adoption and Implementation The policy recognises the critical and highly interdependent nature of the CNII and aims to develop and establish a comprehensive programme and a series of frameworks that will ensure the effectiveness of cyber security controls over vital assets Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 6 THE NATIONAL CYBER SECURITY POLICY - Vision & CNII Sectors VISION ‘Malaysia's Critical National Information Infrastructure shall be secure, resilient and self-reliant. Infused with a culture of security, it will promote stability, social well being and wealth creation’ CRITICAL NATIONAL INFORMATION INFRASTRUCTURE Assets (real & virtual), systems and functions that are vital to the nation that their incapacity or destruction would have a devastating impact on •National economic strength •National image •National defense & security •Government capability to function •Public health & safety Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 7 THE NATIONAL CYBER SECURITY POLICY - Implementation Approach Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 8 THE NATIONAL CYBER SECURITY POLICY - Policy Thrust 1 8 INTERNATIONAL COOPERATION National Security Council 6 Ministry of Science, Technology & Innovation Ministry of Information, Communication & Culture CYBER SECURITY EMERGENCY READINESS 7 EFFECTIVE GOVERNANCE LEGISLATION & REGULATORY FRAMEWORK 2 Attorney General’s Office ‘Malaysia's Critical National Information Infrastructure shall be secure, resilient and self-reliant. Infused with a culture of security, it will promote stability, social well being and wealth creation CYBER SECURITY TECHNOLOGY FRAMEWORK 3 Ministry of Science, Technology & Innovation COMPLIANCE & ENFORCEMENT CULTURE OF SECURITY & CAPACITY BUILDING Ministry of Information, Communication & Culture Ministry of Science, Technology & Innovation Securing Our Cyberspace R & D TOWARDS SELF RELIANCE Ministry of Science, Technology & Innovation 4 5 Copyright © 2009 CyberSecurity Malaysia Slide no: 9 PT 1: EFFECTIVE GOVERNANCE - Structure Establishment of a national info security coordination center National IT Council Chair: Prime Minister National Cyber Security Advisory Committee (NaCSAC) Chair: Chief Secretary National Cyber Security Coordination Committee (NC3) Chair: Secretary General, Ministry of Science, Technology & Innovation National Cyber Security Policy Working Group | PT1 | PT2 | PT3 | PT4 | PT5 | PT6 | PT7 | PT8 | Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 10 PT 1: EFFECTIVE GOVERNANCE - Members 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. 17. 18. Malaysian Administrative, Modernisation and Management Planning Unit, Prime Minister’s Dept National Security Council, Prime Minister’s Dept Attorney General’s Office. Prime Minister’s Dept Chief Government Security Officer’s Office, Prime Minister’s Dept Ministry of Science, Technology & Innovation Ministry of Defence Ministry of Foreign Affairs Ministry of Energy, Green Technology & Water Ministry of Finance Ministry of Information, Communication & Culture Ministry of Transportation Ministry of Home Affairs Central Bank of Malaysia National Water Services Commission Malaysian Communication & Multimedia Commission Energy Communication Security Commission Malaysia CyberSecurity Malaysia Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 11 PT 2: LEGISLATIVE & REGULATORY FRAMEWORK - Cyber Law Review A Study on the laws of Malaysia to accommodate legal challenges in the Cyber Environment Reduction of & increased in the success in, prosecution in cyber crime Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 12 PT 3: CYBER SECURITY TECHNOLOGY FRAMEWORK - Standards To increase the robustness of the CNII sectors by complying to international standards: MS ISO/IEC 27001:2006 Information Security Management System (ISMS) The International Standards MS ISO/IEC 27001:2006 MS ISO/IEC 17799:2005 Adopted as Malaysian Standards Expansion of national certification scheme for Securing Our Cyberspace infosec mgmt & assuarance Copyright © 2009 CyberSecurity Malaysia Slide no: 13 PT 3: CYBER SECURITY TECHNOLOGY FRAMEWORK - Product Certification MISSION “to increase Malaysia’s competitiveness in quality assurance of information security based on the Common Criteria (CC) standard and to build consumers’ confidence towards Malaysian information security products” Malaysia was accepted as CCRA Certificate Consuming Participant on 28 March 2007 Austria India Czech Republic Turkey Denmark Italy Findand Malaysia Greece Pakistan Hungary Singapore Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 14 PT 4: CULTURE OF CYBER SECURITY & CAPACITY BUILDING – Capacity Building Reduce no of Infosec incidents through Securing Our Cyberspace improved awareness & skill level Copyright © 2009 CyberSecurity Malaysia Slide no: 15 PT 4: CULTURE OF CYBER SECURITY & CAPACITY BUILDING - Awareness Content Developers Content Localisation & Packaging Content Channels Target Audience Children / students Video clips Publications Web Parents / home users International CERT Communities Other industry partners Posters TV & Radio ads KPWKM Competitions MOE MOHE Organisations Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 16 PT 4: CULTURE OF CYBER SECURITY & CAPACITY BUILDING – Awareness Materials WEBSITE NEWS LETTERS www.cnii.cybersecurity.my www.esecurity.org.my www.mycert.org.my ONLINE GAMES Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 17 PT 5: RESEARCH & DEVELOPMENT TOWARDS SELF RELIANCE - R & D Roadmap Development of the National R&D Roadmap for Self Reliance in Cyber Security Technologies is facilitated by MIMOS Acceptance & utilization of local developed info security products Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 18 PT 6: COMPLIANCE & ENFORCEMENT - Risk Assessment Risk Assessment Focus in NCSP : Risk Assessment (in NCSP-PT6 context) looks at the likelihood of threats exploiting vulnerabilities to Cyber Assets disrupting/compromising delivery of Products and Services and the consequence or impact of the disruption/compromises of the Products and Services to the Nation, Commerce, Industry, Government, Consumers and other beneficiaries Strengthen or include infosec enforcement role in all CNII regulators Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 19 PT 7: CYBER SECURITY EMERGENCY READINESS - National Cyber Crisis Management Plan CNII resilience against cyber crime, terrorism, info warfare Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 20 PT 8: INTERNATIONAL COOPERATION - Strategic framework Intl branding on CNII protection with improved awareness & skill level ITU-D ARF Cyber Security Securing Our Cyberspace AP L TE C E APEC SPSG MoU with AusCERT Copyright © 2009 CyberSecurity Malaysia Slide no: 21 PT 8: INTERNATIONAL COOPERATION - OIC –CERT History Organization of the Islamic Conference Computer Emergency Response Team Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 22 PT 8: INTERNATIONAL COOPERATION - OIC –CERT Members Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 23 PT 8: INTERNATIONAL COOPERATION - OIC –CERT Objectives OBJECTIVES • Strengthen relationship amongst CERT/CSIRT in the OIC countries • Information sharing • Prevent/reduce cyber terrorism activitiesTs • Education and Outreach ICT Security Programs • Promote collaborative technology research, development and innovations • Promote Good Practices and / or recommendation to address legal and regulatory issues • Assist member countries to establish National CERTs Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 24 KL Resolution 2009 PT 8: INTERNATIONAL COOPERATION - OIC –CERT Seminar & AGM 2009 Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 25 Securing Our Cyberspace Copyright © 2009 CyberSecurity Malaysia Slide no: 26