Security on Grids The Grid Security Infrastructure Guy Warner NeSC Training Team
advertisement
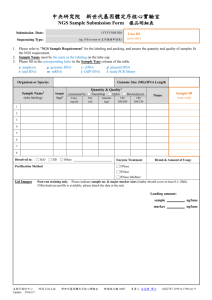
http://www.grid-support.ac.uk http://www.ngs.ac.uk Security on Grids The Grid Security Infrastructure Guy Warner NeSC Training Team http://www.nesc.ac.uk/ http://www.pparc.ac.uk/ http://www.eu-egee.org/ Acknowledgements Some of the slides in this presentation are based on / motivated by: • The presentation given by Carl Kesselman at the GGF Summer School 2004. This presentation may be found at – http://www.dma.unina.it/~murli/GridSummerSchool2004/ curriculum.htm • Lectures given by Richard Sinott and John Watt at the University of Glasgow. These lectures may be found at – http://csperkins.org/teaching/2004-2005/gc5/ • The presentation given by Simone Campana of CERN at First Latinamerican Grid Workshop, Merida, Venezuela. This presentation may be found at – http://agenda.cern.ch/fullAgenda.php?ida=a044965 Installing a UI for the NGS 3 The Problem User Resource • Question: How does a user securely access the Resource without having an account on the machines in between or even on the Resource? • Question: How does the Resource know who a user is and that they are allowed access? Installing a UI for the NGS 4 Overview Security Authentication Grid Security Infrastructure Encryption & Authorization Data Integrity Installing a UI for the NGS 5 Approaches to Security: 1 The Poor Security House Installing a UI for the NGS 6 Approaches to Security: 2 The Paranoid Security House Installing a UI for the NGS 7 Approaches to Security: 3 The Realistic Security House Installing a UI for the NGS 8 Approaches to Grid Security • The Poor Security Approach: – Use unencrypted communications. – No or poor (easily guessed) identification means. – Private identification (key) left in publicly available location. • The Paranoid Security Approach: – Don’t use any communications (no network at all). – Don’t leave computer unattended. • The Realistic Security Approach: – Encrypt all sensitive communications – Use difficult to break identification means. – Keep identification secure at all times (e.g. encrypted on a memory stick). – Only allow access to trusted users. Installing a UI for the NGS 9 The Risks of Poor User Security • Launch attacks to other sites – Large distributed farms of machines, perfect for launching a Distributed Denial of Service attack. • Illegal or inappropriate data distribution and access sensitive information – Massive distributed storage capacity ideal for example, for swapping movies. • Damage caused by viruses, worms etc. – Highly connected infrastructure means worms spread faster than on the internet in general. Installing a UI for the NGS 10 Authentication and Authorization 0598234 John Jane Doe 755 E. Woodlawn Urbana IL 61801 • Authentication – Are you who you claim to be? • Authorisation – Do you have access to the resource you are connecting to? Installing a UI for the NGS 11 The Trust Model No Cross- Domain Trust Certification Authority Certification Authority Policy Authority Policy Authority Sub-Domain B1 Sub-Domain A1 Domain A Domain B Task Federation Service GSI Server X Virtual Organization Domain Server Y slide based on presentation given by Carl Kesselman at GGF Summer School 2004 Installing a UI for the NGS 12 Public Private Key Bob Alice SECURE SECURE INSECURE Life Savings Life Savings Life Savings Private Key Message Public Key Installing a UI for the NGS 13 Certificates • Similar to passport or driver’s license: Identity signed by a trusted party Name Issuer Public Key Signature John Doe 755 E. Woodlawn Urbana IL 61801 State of Illinois Seal BD 08-06-35 Male 6’0” 200lbs GRN Eyes slide based on presentation given by Carl Kesselman at GGF Summer School 2004 Installing a UI for the NGS 15 Certificate Authorities • A small set of trusted entities known as Certificate Authorities (CAs) are established to sign certificates • A Certificate Authority is an entity that exists only to sign user certificates • Users authenticate themselves to CA, for example by use of their Passport or Identity Card. • The CA signs it’s own certificate which is distributed in a secure manner. Name: CA Issuer: CA CA’s Public Key CA’s Signature slide based on presentation given by Carl Kesselman at GGF Summer School 2004 Installing a UI for the NGS 16 Delegation and Certificates Delegation : The act of giving an organization, person or service the right to act on your behalf. • For example: A user delegates their authentication to a service to allow programs to run on remote sites. User CA Proxy Service Signs own Certificate signs Certificate signs Certificate Stage1: Stage2: Stage3: Low Frequency Medium Frequency High Frequency Installing a UI for the NGS 17 User Authorisation to Access Resource slide based on presentation given by Carl Kesselman at GGF Summer School 2004 Installing a UI for the NGS 18 User Responsibilities • Keep your private key secure. • Do not loan your certificate to anyone. • Report to your local/regional contact if your certificate has been compromised. • Do not launch a delegation service for longer than your current task needs. If your certificate or delegated service is used by someone other than you, it cannot be proven that it was not you. Installing a UI for the NGS 19 Summary User via Certificates and Delegated Services delegated to VO. Authentication Authorisation Resource Installing a UI for the NGS 20