International Journal of Application or Innovation in Engineering & Management... Web Site: www.ijaiem.org Email: , Volume 2, Issue 8, August 2013
advertisement

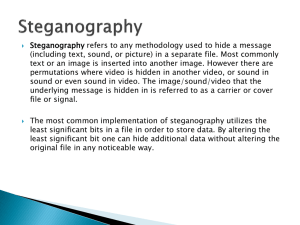
International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 Study and Analysis of Steganography with Pixel Factor Mapping (PFM) Method Indradip Banerjee1, Souvik Bhattacharyya2 and Gautam Sanyal3 1 Department of CSE, National Institute of Technology, Durgapur, West Bengal, India. Department of CSE, University Institute of Technology, Burdwan, West Bengal,India. 3 Department of CSE, National Institute of Technology, Durgapur, West Bengal, India. 2 Abstract Internet expertise’s are now carrying a imperative responsibility in our habitual living. It has the advantages along with the disadvantages; it can generate the requirements of information hiding technology for maintaining the secrecy of the secret information. Steganography is most fashionable information hiding technique in modern day situation, which comes from a Greek word “στεγανό-ς, γραφ-ειν” means “covered or hidden writing”. Extensive capacity of effort has been carried out by different researchers in this ground. In this contribution, a novel special domain image Steganography method has been proposed which has been design based on prime factor calculation on pixel intensity. Keywords: Steganography, Cover Image, Stego Image, Pixel Factor Mapping (PFM) method. 1. INTRODUCTION Security of information is the beautiful aspect of information technology and communication system. Computer, Laptop, Mobile, Internet etc. are most important communication media that join different parts of the world. In contradiction, safety and security of communication system creates an issue. Consequently, the concept of “Information Hiding” [1] has been proposed. Then theory of Cryptography [2] and watermarking [3] has been developed. But in the present days, thanks to the rising computational supremacy, regular cryptographic and watermarking algorithms have been established to be evidence for weak point against mathematical and statistical methods. The word “Security” is not the same like ten years back, because the research in reverse engineering techniques has been increased the processing power, most important race between researches in cryptanalysis [4] and watermarking detection [5]. To solve the problems the concepts of Steganography [6] has been developed by the researchers. Steganography diverge from cryptography. Cryptography is a secure communications which changes the data into a specific form and for that reason an eavesdropper cannot understand it. Steganography techniques attempt to hide the existence of the message itself, so that an observer or eavesdropper does not know that the information is even there or not. Steganography gives the authentication over the data using some tag or labeling on some objects like text, audio, video, image. Hide the presence of a message and create a covert channel is the aim of the Steganography. The message is hidden in another object as a result the transmitted object will be identical looking to every individual’s eye. Steganalysis is the art of detecting any hidden message on the Figure 1: Types of Steganography communication channel. Steganography is crushed when the existence of the hidden message is exposed. The Text Steganography have basic three categories which are as follows [7]: Format-based methods: Hide the steganographic text in the existing cover text by changing formatting like insertion of spaces or non-displayed characters, careful errors tinny throughout the text and resizing of fonts. Random and statistical generation method: Generating the cover text by their own method with the help of known plaintext and make comparison with them. Linguistic methods: With some documented information in society and some linguistic analysis creates the hiding techniques. In audio Steganography[8], messages are embedded into digitized audio signal which result slight alteration of binary sequence of the corresponding audio file. Low-bit Encoding: Binary form of message is used to embed in the LSB (Least Significant Bit) of the cover audio file. Phase Coding: Embed in the phase components of sound which are not audible to the human ear. Several new approaches are studied in video data steganography literature [8]. The approaches are: Application of BPCS Steganography to WAVELET Compressed Video, An Optical Video Cryptosystem with Adaptive Steganography, A Secure Covert Communication Model based on VIDEO Steganography, Lossless Steganography on AVI File using Swapping Algorithm, A New Invertible Data Hiding in Compressed Videos or Images etc. In image Steganography there are various ways have been used by the researchers, which are as follows [9]: Substitution technique in Spatial Domain: In this case the least significant bits of the cover item are replaced in the cover image without modifying. Transform domain technique: Discrete Cosine Transform (DCT), Discrete Wavelet Trans- form (DWT) and Fast Fourier Transform (FFT) are used in this domain to embed information in transform coefficients of the cover images. Spread spectrum Volume 2, Issue 8, August 2013 Page 258 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 technique: Wide frequency bandwidths are used to embed the data bit than the minimum required bandwidth. Statistical technique: Here the information is encoded by changing various numerical properties of cover image and the message bits are hidden in the block of cover image. Distortion technique: Information is stored by signal distortion. Pixel Mapping Method (PMM) [10]: Embedding positions are selected by some function and depends on the pixel intensity value of the seed pixel and its 8 neighbors. The process of embedding is done through mapping of each two or four bits of the secret message in each of the neighbor pixel based on pixel features. In this paper author proposed a novel approach of PFM method for embedding four bits of secret message per pixel. The four bits are combined together and embed using new method i.e. Pixel Factor Mapping (PFM) Method. The pixel selection technique is also a unique mathematical function used here for better security. Another part of the paper has been organized as following sections: Section 2 describes some related works on image steganography. Section 3 deals with proposed method along with the algorithms. In section 4 experimental results are discussed and analyzed. This Section has discussed various attacks applied and their results on the proposed system. Section 5 draws the conclusion. 2. RELATED WORK The image steganography can be possible in two domains, one is Spatial and another is frequency domain. There are various techniques and modules developed by different researchers. Some of them are discussed below: One of the common techniques is to manipulate the least-significant-bit (LSB) [13], [16], [18] and [32] planes by straightforwardly replacing the LSBs of the cover-image with the message bits. LSB methods have high capacity but the LSB insertion is vulnerable in case of cropping and compression of image. The pixel-value differencing (PVD) method proposed by Wu and Tsai [33] can successfully provide both high embedding capacity and outstanding imperceptibility for the stego-image. The pixel-value differencing (PVD) method can segment the cover image into some blocks which are not overlapped. The blocks are containing two connecting pixels and method for embedding is to modify the pixel difference in each pair. Greater modification has the same opinion in case of larger difference in the original pixel values. In the extraction phase, the original range table is necessary. It is used to partition the stego-image by the same method as used to the cover image. Based on PVD method, various approaches have also been proposed. Among them Chang et al. [19] proposes a new method using tri way pixel value differencing which can improve embedding capacity and PSNR value than original PVD method. In 2004, Potdar et al. [20] proposes GLM (Gray level modification) technique can modify Gray level of the image pixels by mapping technique. Gray level modification Steganography is to map data by modifying the pixels Gray level values. The mapping concept of odd and even numbers within an image is used in GLM. It is a one-to-one mapping between the binary data and the selected pixels in an image. Wien Hong and Tung-Shou Chen[11] introduced a new method based on pixel pair matching (PPM). In PPM use the values of pixel pair as a reference coordinate and search a coordinate in the neighborhood set of this pixel pair according to a given message digit. Exploiting modification direction (EMD) and diamond encoding (DE) are two data-hiding methods also proposed based on PPM. Che-Wei Lee and Wen-Hsiang [12] introduced blind an authentication method based on the secret sharing technique. They used the computed values which are mapped into a range of alpha channel values, whose values are near their maximum value of 255. Shunquan Tan and Bin Li [14], identify that the readjusting phase of edge adaptive image steganography based on LSB matching revisited introduces a pulse distortion to the long exponential tail of the histogram of the absolute difference of the pixel pairs. A targeted steganalytic method based on B-Spline fitting is proposed in their method. Sian-Jheng Lin and Wei-Ho Chung [15], initiate the idea of Reversible information-embedding (RIE) in their paper. In this way transform both host signals & message into the stego-signals, and the stego-signals reversed losslessly to the host signals and the message. G.Karthigai Seivi, Leon Mariadhasan, K. L. Shunmuganathan [17], worked on most common and easiest method for embedding messages in an image i.e. least-significant bit (LSB) insertion method which can effectively resist image steganalysis based on statistical analysis. Ching-Nung Yang, Chih-Cheng Wu, Yi-Chin Lin and Cheonshik Kim [21], proposed an efficient matrix based secret image sharing (MSIS) scheme based on simple binary matrix operations. Bhattacharyya and Sanyal‘s Transformation: Bhattacharyya and Sanyal proposed a new image transformation technique in [10] known as Pixel Mapping Method (PMM), this method used for information hiding within the spatial domain of any gray scale image. Embedding pixels are selected by some mathematical function which can depends upon the pixel intensity value of the seed pixel and its 8 neighbors are selected in anti clockwise direction. Data can embed by mapping each two or four bits of the secret message in each of the neighbor pixel based on some features of that pixel. At the receiver side same reverse operations has been used to get back the original information. 3. PROPOSED WORK Author present a novel Pixel Factor Mapping (PFM) method which is based on special domain with the help of Gray scale images (512x512). We have used more than 1000 images in our work, which have been collected from image databases and also those images are used by most of the researchers. The input message can be adopt as digital character format and cope with bit stream. Four bit pair has used for embedding in a separate pixel and the selection of embedding pixel also depends upon mathematical member function. The selection technique is based on pixel intensity value and pixel position on image. Mapping of four bit from the secret message is used for embedding in a pixel, which is based on Volume 2, Issue 8, August 2013 Page 259 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 the maximum prime factor value of image pixel intensity value. In Figure 2 the PFM table shows the mapping of maximum prime factor value. The existing methods can embeds one bit per pixel where as author’s proposed method can embed four bit per pixel. Embedding four bit per pixels can extend the embedding capacity four times than other previous methods and this is the novelty in this contribution. At the receiver side reverse operation has been carried out to get back the original information. Binary Form 10100011011101010… Input Message Divide 4 bit pair 1010 0011 0111 0101 0… Cover Image 198 196 197 187 181 174 180 176 170 182 185 191 192 193 188 181 175 179 172 172 172 182 181 195 197 188 181 179 175 169 166 172 176 174 195 195 186 180 179 175 171 171 172 178 181 192 191 180 183 180 181 176 168 170 172 188 191 191 180 183 182 180 169 162 165 169 Select pixel values 77 65 65 66 74 83 86 92 102 101 87 Calculate Prime Factors 196(2, 2, 7, 7) 188(2, 2, 47) 180(2, 2, 3, 3, 5) Find out correspond ing PFV Calculate expected Number of Nearest matching maximum PVF & Update image pixel intensity Stego Image Calculate Prime Factors of Pixel Intensity & Find out corresponding embedding 4 Bit against PFV Extract 4 bit pair 1010 0011 0111 0101 0… PFM Table Prime Factor Value (PFV) 2 3 5 7 11 13 17 19 23 29 31 37 41 43 47 53 Embedding 4 Bit 0000 0001 0010 0011 0100 0101 0110 0111 1000 1001 1010 1011 1100 1101 1110 1111 Output Message Figure 2: Proposed Work 3.1 Algorithms: 3.1.1 Embedding Algorithm: 1) Select Message four bit pair form. 2) Select the Pixel for embedding by the help of pixel selection algorithm. 3) Pick the intensity value of embedding position. 4) Mapping the PFM Table with message bit. 5) Find out the corresponding PFV (Prime Factor Value) for each 4 Bit message. 6) Calculate the expected nearest number which matched with PFV and the maximum prime factor value of that expected number. Expected nearest number may be greater or less than original intensity. 7) Update the Pixel intensity value with expected nearest number. 8) Generate the Stego Image. 3.1.2 Extracting Algorithm: 1) Select the Pixel with the help of pixel selection algorithm. 2) Pick the intensity value of embedding position. 3) Mapping the PFM Table with pixel intensity. Volume 2, Issue 8, August 2013 Page 260 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 4) Find out the corresponding 4 Bit message for each PFV (Prime Factor Value). 5) Generate the message. 3.1.3 Pixel Selection Algorithm: 1) Select the pixel intensity µ(x,y) value and pixel position x and y. 2) Calculate the membership function for pixel δ(p)=p/63 for 0 ≤ p ≤ 63; δ(p)=(p-64)/63 for 64 ≤ p ≤ 127; δ(p)=(p128)/63 for 128 ≤ p ≤ 191; δ(p)=(p-192)/63 for 192 ≤ p ≤ 255. 3) Put it to a mathematical function a. if (δ(p) > 0 AND δ(p) ≤ 0.4) THEN λ=1 b. if (δ(p) > 0.4 AND δ(p) ≤ 0.7) THEN λ=2 c. if (δ(p) > 0.7) THEN λ = 0 d. ∞ = (x + 1) + λ e. if (∞ ≥ 512) THEN η =1 ; χ = (y + 1) + λ 1. if (χ ≥ 512) THEN χ = 1; f. else η = (x + 1) + λ; χ = y; 4) Get some parameters including η, χ. 5) Using the parameters value generates the row and column position of the next search pixel. 6) Process continues until full message embedding done. 4. RESULTS & ANALYSIS The authors explain the experimental results of the method based on some techniques to evaluate the hiding performance in this section. Capacity of hiding data and Imperceptibility of the stego image, these two techniques is used here for performance metric. Imperceptibility of the image is called the quality of image. The quality of stego image produced by the proposed method and the stego image has been tested thorough some image similarity metrics like MSE, PSNR, Correlations, RMSE, SSIM, KL divergence, Entropy. Figure 3 to 9 shows the graphical representation of calculated value of various similarity metrics for cover and stego images. Various Techniques used to manage the difference between pixels. The techniques are described below: Mean Square Error (MSE) [22]: It is computed by averaging the squared intensity of the cover and stego image pixels. The equation (1) shows the MSE. M 1 N 1 1 NM MSE em, n ..............................(1) 2 m 0 n 0 Where NM is the image size (N x M) and e(m,n) is the reconstructed imag. Peak Signal-to-Noise Ratio (PSNR) [22]: A mathematical measure of image quality is Signal–to-noise ratio (SNR), which is based on the pixel difference between two images [23]. The SNR measure the estimate of Stego image and cover image. PSNR shows in equation (2). PSNR 10 log 10 S 2 MSE .......... .......... .......... (2) Where, S stands for maximum possible pixel value of the image. If the PSNR is greater than 36 DB then the visibility looks same in between cover and stego image, so HVS not identified the changes. Correlations [24]: Pearson’s correlation coefficient is widely used in statistical analysis as well as image processing. Here apply it in Cover and Stego images to see the difference between these two images. The Correlation shows in equation (3). n r i 1 ( xi x ) ( yi y ) n n ..............................(3) ( xi x ) 2 i 1 ( yi y ) 2 i 1 The Xi and Yi are the cover image and bar of X and Y are stego image positions. Root Mean Square Error (RMSE) [25]: RMSE is a frequently used measure of the difference between Cover Image and Stego Image values. These individual differences called residuals and the RMSE aggregate them into a single measure of predictive power. The RMSE shows in equation (4). n RMSE i1 ( X obs,i X mo del,i )2 n ..............................(4) Xobsi and Xmodeli are two image vectors i.e. cover and stego. Structural Similarity Index (SSIM) [22]: Wang et. al[26], proposed Structural Similarity Index concept between original and distorted image. The Stego and Cover images are divided into blocks of 8 x 8 and converted into vectors. Then two means and two standard derivations and one covariance value are computed. After that the luminance, contrast and Volume 2, Issue 8, August 2013 Page 261 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 structure comparisons based on statistical values are computed. Then The SSIM computed between Cover and Stego images. SSIM shows in equation (5). SSIM 2 x 2 x y C1 2 xy C2 2y C1 x2 2y C2 ..............................(5) KL divergence [27]: With the help of probability density function (PDF) for each Image (cover and stego) we estimate the Kullback-Leibler Divergence. KL divergence shows in equation (6) D p || q x pxlog px ..............................(6) qx Entropy [28]: Entropy is a measure of the uncertainty associated with a random variable. Here, a 'message' means a specific realization of the random variable. The equation (7) shows it. S . dQrev .............................(7) T Where, S is the entropy and T is the uniform thermodynamic temperature of a closed system divided into an incremental reversible transfer of heat into that system (dQ) Figure 3: Performance Metrics (MSE) Figure 5: Performance Metrics (Correlation) Figure 7: Performance Metrics (SSIM) Figure 9: Performance Metrics (Entropy) Volume 2, Issue 8, August 2013 Figure 4: Performance Metrics (PSNR) Figure 6: Performance Metrics (RMSE) Figure 8: Performance Metrics (KL divergence) Figure 10: RS Analysis of “Lena.bmp” size 512x512 Page 262 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 Figure 11: Chi Square Probability Distribution of Cover and Stego Images Figure 12: Chi Square Statistics Distribution of Cover and Stego Images Fridrich et al. [30] introduced a powerful steganalytic method which is used for accurately estimate the length of the embedded message from an image, for several LSB steganographic method is RS Analysis. Let I be the image to be analyzed having width W and height H pixels. Each pixel has been denoted as P i.e. for a Gray Scale Image (8 bits per pixel image), value of P = 0, 1,. . . 255. Next step is for divide I into G disjoint groups of n adjacent pixels. For instance n can be 4. Next define a discriminate function f which is responsible to give a real number f(x1 ,….., xn) ε R for each group of pixels G = (x1 ,….., xn). The objective is to capture the smoothness of G using f. Let the discrimination function be n 1 f ( x1 ,..., xn ) xi1 xi .............................(8) i 1 Furthermore, let F1 be a flipping invertible function F1: 0 1, 2 3, . . . , 254 255, and F-1 be a shifting function denoted as F-1 : -1 0, 1 2, . . . , 255 256 over P. For completeness, let F0 be the identity function such as F0(x) = x for all x ε P: Define a mask M that represents which function to apply to each element of a group G. The mask M is an ntuple with values in -1, 0, 1. The value -1 stands for the application of the function F-1, 1 stands for the function F1 and 0 stands for the identity function F0. Similarly, define -M as M’s compliment. Next step is to apply the discriminate function f with the functions F-1,0,1 defined through a mask M over all G groups to classify them into three categories Regular (R), Singular (S) and Unchanged (U) - depending on how the flipping changes the value of the discrimination function. Re gularGroups : G R f (F (G)) f (G).............................(9) E M SingularGroups: GE S M f (F (G)) / f (G).............................(10) UnusableGroups: GEU M f (F (G)) f (G).............................(11) In similar manner R-M, S-M and U-M can be defined for -M such that (RM +SM)/2 ≤ T and (R-M +S-M)/2 ≤ T, where T is the total number of G groups. The conclusion of RS Analysis method describes that, for typical images RM ≈ R-M and SM ≈ SM and no change in R and S value for embedding character of various sizes. Chi-square test[35] is a statistical test. This is used for testing independence and goodness of fit. Testing independence is determines, whether two or more observations across two populations are dependent on each other, i.e. whether one variable helps to estimate the other. Testing for goodness of fit determines if an observed frequency distribution matches a Volume 2, Issue 8, August 2013 Page 263 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 theoretical frequency distribution. In both cases the equation is used for calculate the chi-square statistic. 2 (O E) E 2 .............................(12) O equals the observed frequency and E is the expected frequency. The results of a chi-square test, along with the degrees of freedom, are used with a previously calculated table of chi-square distributions to find a p-value. The p-value can then be used to determine the significance of the test. Here the attack is very necessary in case of Steganography algorithm so we have tested through some steganalysis technique. First exact detector of LSB replacement was the heuristic RS analysis [29] [30] published in 2001. Then Sample Pairs (SP) analysis was analyzed and reformulated by Dumitrescu et al. [31] in 2002. In this work all the stego image has been generated with the help of our algorithm and tested through steganalysis attack algorithm i.e. RS analysis. Figure 10 shows the Analysis of attack of Gray scale image (Lena used here) as cover and stego image after embedding 100-30000 characters. With the help of RS Analysis, we observe that, a typical images RCOVER ≈ RSTEGO and SCOVER ≈ SSTEGO and so no changes found in R and S value for embedding characters of different sizes. The steganalysis tool was developed by Guillermito to implement the chi-square analysis for performing statistical attack and detect any type of hidden messages [34]. In this work Chi Square Probability Distribution and Statistics Distribution graph (Figure 11 and 12) shows no difference in between cover and stego images. Here the entire attack algorithms are working on embedding one bit per LSB where as our technique is embedding four bits per pixel. This technique is not depending upon LSB and for that reason the attack is not performing their profession in this PFM method. The PFM method is compared with LSB [13,16,18,32], PVD [33,19], GLM [20] and PMM [10] method which is shown in tabular form in Figure 13. LSB[13,16,18,32], PVD[33,19], GLM[20] 1. Data can be easily tractable in various image steganography attacks. 2. Evaluating performance only MSE and PSNR has been incorporated. Proposed Pixel Factor Mapping (PFM) Method 1. Tested through some steganography attack like RS analysis, SP analysis and Chi-square analysis etc. 2. Performance measured using various performance metric like MSE, PSNR, SSIM, Correlation, RMSE, KL Divergence, Entropy etc. 3. Security tested and measured high. 3. Security of the hidden data has not tested properly. 4. LSB method directly replacing the LSBs, 4. Use mapping technique with the help of maximum PVD requires range table. GML map prime factor value of pixel intensity and pixel image data by modifying the Gray level. selection method. 5. These methods can embed one bit per 5. This method can embed four bits per pixel. pixel. Figure 13: Comparison between Previous and Proposed Work 5. CONCLUSION This work catch with the techniques for steganography in 4 bit PFM (Pixel Factor Mapping) method related to image Steganography. A well-organized unmarked steganographic method for embedding secret messages into images without producing any key changes has been projected in this paper with the help of various performances metric. This method is a robust method which can also avoid some image attacks after noise addition. From the security aspects the attack technique is very low between the cover image and stego image which surrender a very high security value of the hidden data. The hidden message also stays undetected after application of some well known steganalysis method on it. This method can extract the secret message without the use of cover image. This method can improve and maximize the embedding capacity then previous developed image Steganography systems. In future we have planned to improve the embedding capacity as well as develop the same technique in frequency domain and also check with some other steganalysis attack like WS Analysis etc. References [1] Abbas Cheddad, Joan Condell, Kevin Curran, Paul Mc Kevitt, Digital image steganography: Survey and analysis of current methods Signal Processing 90, 2010,pp. 727– 752. [2] Eskicioglu, A.M. ; Litwin, L."Cryptography", Potentials, IEEE (Volume:20 , Issue: 1 ), Feb/Mar 2001, Page(s): 36 38, ISSN : 0278-6648 [3] Fu-Hau Hsu, Min-Hao Wu, Shiuh-Jeng WANG, "Dual-watermarking by QR-code Applications in Image Processing", 2012 9th International Conference on Ubiquitous Intelligence and Computing and 9th International Conference on Autonomic and Trusted Computing. Volume 2, Issue 8, August 2013 Page 264 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 [4] Kaminsky, A. ; Kurdziel, M. ; Radziszowski, S."An overview of cryptanalysis research for the advanced encryption standard", MILITARY COMMUNICATIONS CONFERENCE, 2010 - MILCOM 2010,San Jose, CA , Oct.31 2010Nov.3 2010, Page(s): 1310 - 1316, ISSN : 2155-7578 [5] Wenjun Zeng ; Liu, B."A statistical watermark detection technique without using original images for resolving rightful ownerships of digital images" Image Processing, IEEE Transactions on (Volume:8 ,Issue: 11 ), Nov 1999, Page(s):1534 - 1548, ISSN : 1057-7149. [6] N.N. EL-Emam, “Hiding a large amount of data with high security using steganography algorithm,” Journal of Computer Science, vol. 3, no. 4, pp. 223-232, April 2007. [7] Krista Bennett (2004). “Linguistic Steganography: Survey, Analysis, and Robustness Concerns for Hiding Information in Text". CERIAS TR 2004-13. [8] V.Sathyal,K.Balasuhramaniyam ,N.Murali, M.Rajakumaran, Vigneswari, "DATA HIDING IN AUDIO SIGNAL, VIDEO SIGNAL TEXT AND JPEG IMAGES", IEEE-International Conference On Advances In Engineering, Science And Management (ICAESM -2012) March 30, 31, 2012. 741-746. [9] Souvik Bhattacharyya, Indradip Banerjee and Gautam Sanyal, "A Survey of Steganography and Steganalysis Technique in Image, Text, Audio and Video as Cover Carrier", Journal of Global Research in Computer Science(JGRCS), Volume 2, No. 4, April 2011 [10] Souvik Bhattacharyya, Lalan Kumar and Gautam Sanyal, "A novel approach of data hiding using pixel mapping method (PMM)" International Journal of Computer Science and Information Security (IJCSIS), 8, 2010 [11] Wien Hong and Tung-Shou Chen, “A Novel Data Embedding Method Using Adaptive Pixel Pair Matching.” IEEE TRANSACTIONS ON INFORMATION FORENSICS AND SECURITY, VOL. 7, NO. 1, FEBRUARY 2012, 176184. [12] Che-Wei Lee and Wen-Hsiang Tsai, "A Secret-Sharing-Based Method for Authentication of Grayscale Document Images via the Use of the PNG Image With a Data Repair Capability" IEEE TRANSACTIONS ON IMAGE PROCESSING, VOL. 21, NO. 1, JANUARY 2012, 207-218 [13] Y. K. Lee. and L. H.Chen. "High capacity image steganographic model".IEE Proc.-Vision, Image and Signal Processing, 147:288–294, 2000. [14] Shunquan Tan, Member, IEEE, and Bin Li, Member, IEEE "Targeted Steganalysis of Edge Adaptive Image Steganography Based on LSB Matching Revisited Using B-Spline Fitting" IEEE SIGNAL PROCESSING LETTERS, VOL. 19, NO. 6, JUNE 2012, 336-339. [15] Sian-Jheng Lin and Wei-Ho Chung, "The Scalar Scheme for Reversible Information-Embedding in Gray-Scale Signals: Capacity Evaluation and Code Constructions", IEEE TRANSACTIONS ON INFORMATION FORENSICS AND SECURITY, VOL. 7, NO. 4, AUGUST 2012, 1155-1167. [16] J.Y. Hsiao. C.C. Chang. and C.-S. Chan. Finding optimal least significant-bit substitution in image hiding by dynamic programming strategy. Pattern Recognition, 36:1583–1595, 2003. [17] G.Karthigai Seivi, Leon Mariadhasan, K. L. Shunmuganathan, "Steganography Using Edge Adaptive Image", IEEE, 2012 International Conference on Computing, Electronics and Electrical Technologies [ICCEET]. [18] C.F. Lin. R.Z. Wang. and J.C. Lin. Image hiding by optimal lsb substitution and genetic algorithm. Pattern Recognition, 34:671–683, 2001. [19] P Huang. K.C. Chang., C.P Chang. and T.M Tu. A novel image steganography method using tri-way pixel value differencing. Journal of Multimedia, 3, 2008. [20] Potdar V.and Chang E. Gray level modification steganography for secret communication. In IEEE International Conference on Industria Informatics., pages 355–368, Berlin, Germany, 2004. [21] Ching-Nung Yang, Chih-Cheng Wu, Yi-Chin Lin and Cheonshik Kim, "Enhanced Matrix-Based Secret Image Sharing Scheme", IEEE SIGNAL PROCESSING LETTERS, VOL. 19, NO. 12, DECEMBER 2012, 789-792. [22] Yusra A. Y. Al-Najjar, Dr. Der Chen Soong, "Comparison of Image Quality Assessment: PSNR, HVS, SSIM, UIQI", International Journal of Scientific & Engineering Research, Volume 3, Issue 8, August-2012 ISSN 2229-5518 [23] a. L. M. Jean-Bernard Martens, "Image dissimilarity", Signal Processing, vol. 70, no. 3, pp. 155-176, 1998. [24] J.L.Rodgers, J.L. and W.A.Nicewander, "Thirteen Ways to Look at the Correlation Coefficient", American Statistician 42, 59-66 (1995). [25] Lehmann, E. L.; Casella, George (1998). Theory of Point Estimation (2nd ed.). New York: Springer. ISBN 0-38798502-6. [26] a. A. C. B. Zhou Wang, "A Universal Image Quality Index," IEEE SIGNAL PROCESSING LETTERS, vol. 9, pp. 81-84, 2002. [27] Pedro J. Moreno, Purdy Ho, Nuno Vasconcelos "A Kullback-Leibler Divergence Based Kernel for SVM Classification in Multimedia Applications" Conference: Neural Information Processing Systems - NIPS , 2003 [28] Claude E. Shannon, "A mathematical theory of communication", The Bell System Technical Journal., 27:379–423. [29] Patricia R. Pereira. Andr R.S. Maral. “A steganographic method for digital images robust to rs steganalysis”. Springer Lecture Notes in Computer Science, Vol. 3656., pages 1192–1199, 2005. Volume 2, Issue 8, August 2013 Page 265 International Journal of Application or Innovation in Engineering & Management (IJAIEM) Web Site: www.ijaiem.org Email: editor@ijaiem.org, editorijaiem@gmail.com Volume 2, Issue 8, August 2013 ISSN 2319 - 4847 [30] J. Fridrich, M. Goljan, and R. Du. “Reliable detection of LSB steganography in grayscale and color images”. In Proceedings of the ACM, Special Session on Multimedia Security and Watermarking, pages 27–30, Ottawa, Canada, October 5, 2001. [31] S. Dumitrescu, X. Wu, and N. D. Memon. “On steganalysis of random LSB embedding in continuous-tone images”. In Proceedings IEEE, International Conference on Image Processing, ICIP 2002, pages 324–339, Rochester, NY, September 22–25, 2002. [32] C.K. Chan. and L. M.Cheng. Hiding data in images by simple lsb substitution. Pattern Recognition, 37:469–474, 2004. [33] D.C. Wu. and W.H. Tsai. A steganographic method for images by pixel value differencing. Pattern Recognition Letters, 24:1613–1626, 2003. [34] Guillermito (2004). Steganography: a few tools to discover hidden data. Retrieved September 29, 2007, from http://www.guillermito2.net/stegano/tools/index.html [35] Bagdonavicius, V., Nikulin, M.S. (2011) "Chi-square goodness-of-fit test for right censored data". The International Journal of Applied Mathematics and Statistics, p. 30-50. AUTHOR Indradip Banerjee is a Research Scholar at National Institute of Technology, Durgapur, West Bengal, India. He received his MCA degree from IGNOU in 2009, PGDCA from IGNOU in 2008, MMM from Annamalai University in 2005 and BCA (Hons.) from The University of Burdwan in 2003. He is registered and pursuing his PhD. in Engineering at Computer Science and Engineering Department, National Institute of Technology, Durgapur, West Bengal, India. His areas of interest are Steganography, Cryptography, Text Steganography, Image Steganography, Quantum Steganography and Steganalysis. He has published 17 research papers in International and National Journals / Conferences. Souvik Bhattacharyya received his B.E. degree in Computer Science and Technology from B.E. College, Shibpur, India and M.Tech degree in Computer Science and Engineering from National Institute of Technology, Durgapur, India. He has received Ph.D (Engg.) from National Institute of Technology, Durgapur, India. Currently he is working as an Assistant Professor and In-Charge in Computer Science and Engineering Department at University Institute of Technology, The University of Burdwan. His areas of interest are Natural Language Processing, Network Security and Image Processing. He has published nearly 65 papers in International and National Journals / Conferences. Gautam Sanyal has received his B.E and M.Tech degree National Institute of Technology (NIT), Durgapur, India. He has received Ph.D (Engg.) from Jadavpur University, Kolkata, India, in the area of Robot Vision. He possesses an experience of more than 25 years in the field of teaching and research. He has published nearly 150 papers in International and National Journals / Conferences. Two Ph.Ds (Engg) have already been awarded under his guidance. At present he is guiding six Ph.Ds scholars in the field of Steganography, Cellular Network, High Performance Computing and Computer Vision. He has guided over 10 PG and 100 UG thesis. His research interests include Natural Language Processing, Stochastic modeling of network traffic, High Performance Computing, Computer Vision. He is presently working as a Professor in the department of Computer Science and Engineering and also holding the post of Dean (Students’ Welfare) at National Institute of Technology, Durgapur, India. Volume 2, Issue 8, August 2013 Page 266