Document 12141096
advertisement
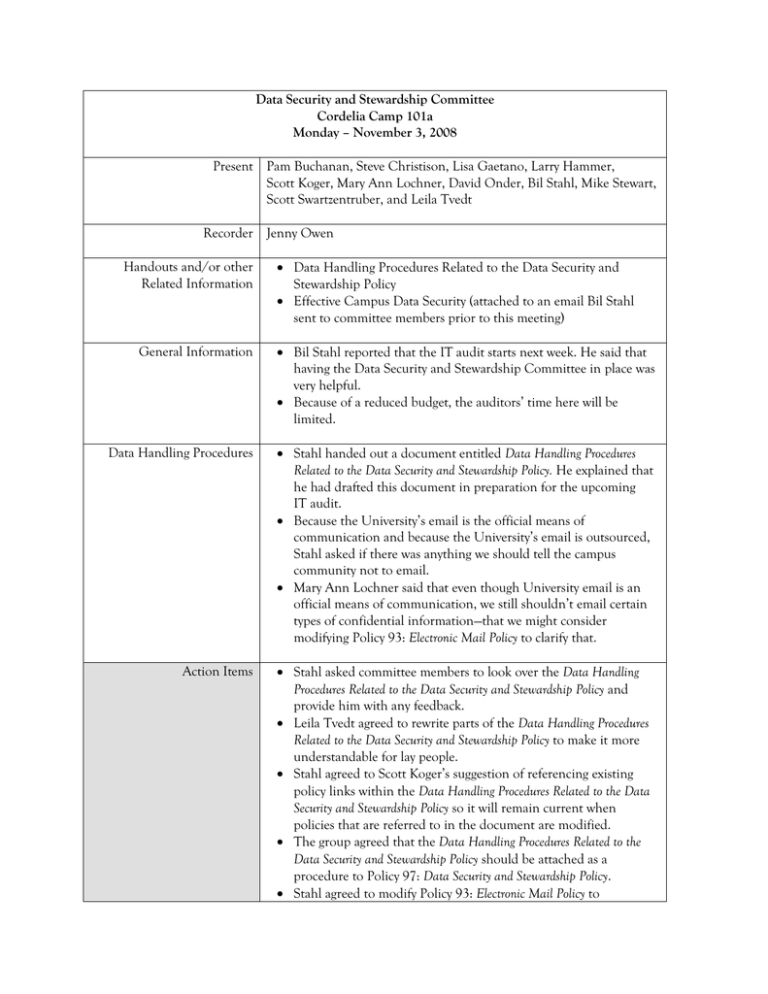
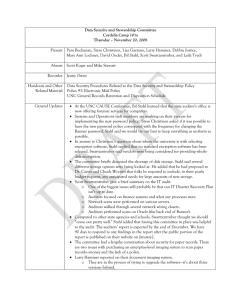
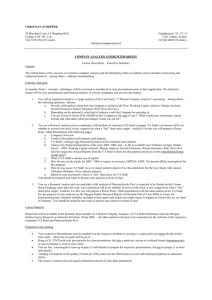
Data Security and Stewardship Committee Cordelia Camp 101a Monday – November 3, 2008 Present Pam Buchanan, Steve Christison, Lisa Gaetano, Larry Hammer, Scott Koger, Mary Ann Lochner, David Onder, Bil Stahl, Mike Stewart, Scott Swartzentruber, and Leila Tvedt Recorder Jenny Owen Handouts and/or other Related Information Data Handling Procedures Related to the Data Security and Stewardship Policy Effective Campus Data Security (attached to an email Bil Stahl sent to committee members prior to this meeting) General Information Bil Stahl reported that the IT audit starts next week. He said that having the Data Security and Stewardship Committee in place was very helpful. Because of a reduced budget, the auditors’ time here will be limited. Data Handling Procedures Stahl handed out a document entitled Data Handling Procedures Related to the Data Security and Stewardship Policy. He explained that he had drafted this document in preparation for the upcoming IT audit. Because the University’s email is the official means of communication and because the University’s email is outsourced, Stahl asked if there was anything we should tell the campus community not to email. Mary Ann Lochner said that even though University email is an official means of communication, we still shouldn’t email certain types of confidential information—that we might consider modifying Policy 93: Electronic Mail Policy to clarify that. Action Items Stahl asked committee members to look over the Data Handling Procedures Related to the Data Security and Stewardship Policy and provide him with any feedback. Leila Tvedt agreed to rewrite parts of the Data Handling Procedures Related to the Data Security and Stewardship Policy to make it more understandable for lay people. Stahl agreed to Scott Koger’s suggestion of referencing existing policy links within the Data Handling Procedures Related to the Data Security and Stewardship Policy so it will remain current when policies that are referred to in the document are modified. The group agreed that the Data Handling Procedures Related to the Data Security and Stewardship Policy should be attached as a procedure to Policy 97: Data Security and Stewardship Policy. Stahl agreed to modify Policy 93: Electronic Mail Policy to incorporate Swartzentruber’s suggestion about pointing to secure portals or links within emails that reference confidential information. Stahl will email a draft of the Policy 93 revision to this committee to review before he presents it to the IT Policy Council. Effective Campus Data Security Stahl bounced the following idea to the committee: “When we look down the road at technology such as cloud computing, it seems that it is becoming much more apparent that we can only control things with policies--that there is very little of what we will be doing that can be controlled with technology.” The committee discussed how to get the campus community started on that level of education. Comments: o Require training as people are hired. o General security awareness training is being required of all university employees. o If we change from technology based to policy based, will it hold up during litigation? o Re-label the H drive to the “secure drive” so people can better understand. o The phrase “train and trust” is becoming more common. o Look at similar institutions to see if there is a general place where you can see what kinds of technology they have. o We have implemented good policies, but we haven’t educated the university community about the policies. Action Items Stahl will ask that the Effective Campus Data Security document be presented for approval to the Executive Council in the very near future. Stahl agreed with Tvedt’s idea of having a consolidated location where overviews of all the IT policies and procedures can be read. He will arrange to have this aggregated onto IT’s website along with frequently asked questions. Koger added that Cornel University had a “slick model for aggregating policies” that Stahl might want to look at.