Prof. Michael P. Harris, - Computer Security Overview Network Security policies:
advertisement
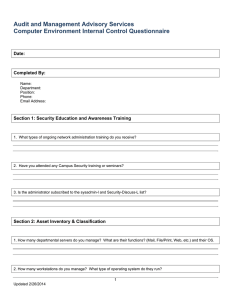
Prof. Michael P. Harris, CCNA, CCAI Director, Cisco Networking Academy Computer Science Department ITSY 1300 - Fundamentals of Information Security (Version 20070911) Lab #02 - Computer Security Overview Network Security policies: An organization's information is one of its most valuable assets. Network security is becoming increasingly important as networks become larger and more complex. Today's mobile and telecommuting users require access locally as well as from outside the network. Threats to an organization's resources can come from internal as well as external sources. Information theft and destruction as well as resource access denial are real concerns for users and system administrators. The overall goal of any information security system is to ensure that information is accurate and available where and when needed. There are a number of components that must interact in a comprehensive network security policy. Physical Access Security - The first line of defense locally to protect network equipment such as servers, switches, and routers is to keep them in a locked, climate controlled, and fire protected environment. If equipment is not physically accessible to unauthorized personnel, there is less chance of accidental or intentional tampering. Login / Password Security - Login and password security policy require that any user accessing a workstation or server have a valid login ID and password. Windows NT, Windows 2000, Windows XP, Novell Netware, and UNIX all have specific requirements for creating and changing passwords. The system administrator can also require that passwords be changed periodically. Setting screen savers that time out and activate your workstation lock are additional measures that enhance login security. File Systems Security - A major component in any comprehensive security policy, file system security determines who can get to what data and what they can do with it. System administrators set up file system security based on users, groups, and permissions. Virus protection - Viruses can do tremendous damage to individual workstations and network servers. Many network operating systems and workstations require antivirus software for adequate protection. UNIX is susceptible to virus attacks like other operating systems, but most viruses are written for Windows based systems because the viruses can affect more systems faster. In addition, most virus creators are not familiar with the UNIX environment enough to know how to create a "UNIX" virus. Remote Access Security - With increases in telecommuting, the network must allow legitimate users to access resources remotely while protecting them from unauthorized access. Access servers and software provide this function. Internet Firewalls - Organizations that maintain Internet web sites need protection from hackers. Various software and hardware solutions are available to help ensure that web servers are available to provide services to legitimate users. Data backups - A comprehensive security policy must include regular backups of important data to minimize downtime in the event of a security breach or disaster such as fire or flood. Backup media such as tapes should be kept offsite in a climate controlled secure environment. Test restores of data should be performed periodically to ensure that data can be recovered from the backups. Disaster Recovery Plan - A written plan is needed that identifies critical data and documents by functional department within an organization. It describes protective measures and steps necessary to ensure that the organization can continue to operate and get back to business quickly with minimum impact to customers. Audits - Security audits should be performed periodically to ensure that the organization and its users are following the security policy and preparing adequately for disaster recovery. Security Audit tools are also available for system administrators to analyze and detect security loopholes such as files with open permissions. Summary: The primary function of system security is to deny access to unauthorized users. Keeping computer information secure is important to the user and the system administrator. By protecting their files and accounts from unauthorized use, users are also protecting their job and reputation. Standard security features include: user passwords that restrict access to the system file and directory protection with permissions files that control remote logins and commands on individual workstations other features that enable system administrators to check for security breaches. On-Line QUIZ: http://www.delmar.edu/Courses/ITSY1300/Labs/SecurityPolicy.html (Drag and drop the correct answers beside the matching descriptions.)