EC310 12-week Review
advertisement

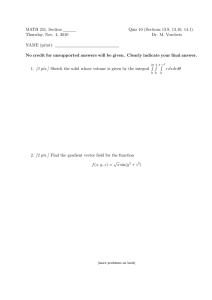
EC310 12-week Review Rules of Engagement Teams selected by instructor Host will read the entire questions. Only after, a team may “buzz” by raise of hand A team must answer the question within 5 seconds after buzzing in (must have answer at hand) If the answer is incorrect, the team will lose its turn and another team may buzz in. No score will be deducted. No negative scores. Maximum score is 100. Once reached, that team will stand down for others to participate. Teams will earn all points scored at the end of game. When selecting a question, Teams must only select questions of different value, unless there are no others, but may be from different categories. All team members will participate and will answer questions Only one round - No Daily Doubles, Double Jeopardy or Final Jeopardy … and no partial credits! Jeopardy! TCP/IP Model Ethernet Internet Protocol ARP Routing / MITM Privileges / Buffer Overflow BGP / BGP Routing 10 pts 10 pts 10 pts 10 pts 10 10 pts 10 pts 10 pts 10 pts 10 pts pts 10 10 pts pts 10 pts 20 pts 20 pts 20 pts 20 pts 20 20 pts 20 pts 20 pts 20 pts 20 pts pts 20 20 pts pts 20 pts 40 pts 40 pts 40 pts 40 pts 40 pts pts 40 40 pts pts 40 pts 40 pts 40 pts 40 pts 40 pts 40 60 pts 60 pts 60 pts 60 pts 60 pts pts 60 60 pts pts 60 pts 60 pts 60 pts 60 pts 60 pts 60 TCP/IP 10 pts Which TCP/IP layer is responsible for processes that provide services to HTTP or FTP? Application Layer Ethernet 10 pts How many bytes are in a physical address? 6 Bytes Example F2 : 45 : 17 : FF : 71 : A2 Internet Protocol 10 pts Which of the following is not a valid IP address? 192.148.2.0 (b) 0.0.0.0 (c) 200.256.32.104 (d) 172.31.22.48 (a) Maximum octet value = 255 ARP 10 pts Which two layers does the Address Resolution Protocol (ARP) involve? Layer 2 (Data Link) & Layer 3 (Network) Routing Tables 10 pts Routing tables are maintained on which of the following: (a) routers (b) host computers (c) both a & b (d) neither Routing/MITM 10 pts TRUE/FALSE: It is best to order the routing table by decreasing mask value. True! This is “longest mask matching” principle Privileges/Buffer Overflow 10 pts What does the Linux command sudo do? Executes a single command as the root user! TCP/IP 20 pts The Transport layer is encapsulated by which layer? Network Layer (Layer 3) Ethernet 20 pts What is the purpose of the CRC field in an Ethernet frame? Used for Error Detection Internet Protocol 20 pts What is the network address for the IP address 200.32.33.234 / 23 ? (mask) (Network bits) (Host bits) (Mask) 200. 32.00100001.11101010 255.255.11111110.00000000 (Network ID) 200. 32.00100000.00000000 (IP address) 200.32.32.0 Zero out the host bits to get… ARP 20 pts An evil attacker launching an ARP-spoof hardware attempts to associate his ___________ IP address with the victim’s ___________ address. Answer choices: hardware or IP Routing/MITM 20 pts If a router receives a packet with a destination IP address that does not match any of the networks on the routing table, what does the router do with it? The router sends it to the default router. This is often indicated in the routing table by: Mask Network Any Any or /0 0.0.0.0 Privileges/Buffer Overflow 20 pts What does setting the setuid permission on an executable program do? Whenever the program is executed it will behave as though it were being executed by the owner! TCP/IP 40 pts What is the name of the collection of 1’s and 0’s at layers 5 through 2? Layer 5 – “Message” Layer 4 – “Segment” Layer 3 – “Packet or Datagram” Layer 2 – “Frame” Ethernet 40 pts Calculate the bandwidth seen by user 3 if each network is connected via 10 Mbps Ethernet. 4 1 B1 B2 5 2 3 6 10Mbps ÷ 3 = 3.33Mbps Internet Protocol 40 pts How many addresses can be assigned to hosts on the network 138.43.29.128 / 26 ? 32 total bits – 26 network bits = 6 host bits 26-2=62 addresses assignable to hosts. Account for the broadcast and network addresses. ARP 40 pts What two types of ARP messages exist? ARP Request & ARP Reply What is the fundamental problem with ARP that allows an ARP-spoof to be possible? An ARP reply can be sent (and be accepted!) without an ARP request Routing/MITM 40 pts Fill in the missing information in the routing table for R1. Privileges/Buffer Overflow 40 pts What is the correct order for arranging the payload in a buffer overflow attack, and what are their purposes? Choices are given below: The exploit (shellcode) Repeated return addresses NOP sled NOP Sled – It is a series of “no operation” commands that lets the hacker be a bit off with the return address, so that the return address just has to point anywhere within the NOP sled. Otherwise, the return address would need to be the precise first address of the exploit. The exploit – This is the executable program. Repeated return addresses – The return address points towards the exploit as the next instruction (however, see the note regarding the NOP sled). It is repeated so that the hacker would have a number of chances to get the address correctly positioned in the Return Address field in the stack. TCP/IP 60 pts Suppose an application entity wants to send a 100 byte message to a peer entity. If each layer from 4-2 appends a 15 byte header, what percentage of the total frame size is actual application entity data? [100 / (100+15+15+15) ] x100 = 69% Ethernet 60 pts Assume the Network layer passes the Data Link layer 6030 bytes of information to transmit. How many Ethernet frames will be required? 6030÷1500 = 4.02 thus 5 Frames Internet Protocol 60 pts What is the block of addresses assigned to the network 56.45.100.0 / 23 ? (mask) (Network bits) (Host bits) 56.45.01100100.00000000 56.45.01100100.00000000 = 56.45.100.0 (First Address) ... 56.45.01100101.11111111 = 56.45.101.255 (Last Address) ARP 60 pts You are user C in the network below. Design an ARP Spoofing attack on User D. What changes would you make to the ARP cache? N1 : L1 N2 : L2 N3 : L3 N4 : L3 L4 N5 : L5 Routing/MITM 60 pts Design an MITM attack to divert traffic from the server Target’s Network 40.230.45.161 Target’s IP Address Attacker’s Lie 40 .230 .45 00101000 11100110 00101101 40 .230 .45 00101000 11100110 00101101 40 .230 .45 00101000 11100110 00101101 Ans: 40.230.45.160 / 27 Other possible Answers: 40.230.45.160 / 28 40.230.45.160 / 29 40.230.45.160 / 30 40.230.45.160 / 31 .128 1 0 0 0 0 0 0 0 0 0 1 0 0 0 .161 1 0 1 0 0 .160 1 0 1 0 0 Privileges/Buffer Overflow 60 pts Name and describe two technical solutions to prevent a buffer overflow attack. The non-executable stack: The CPU will not execute any machine instructions located in the portion of main memory reserved for the stack. The stack canary: The CPU checks a known value in memory just prior to the location of the return address (to make sure it was not changed) before resetting the EIP. Address space layout randomization: The stack and the heap are placed in random memory locations, preventing the hacker from easily predicting return addresses’ location. BGP/BGP Routing 10 pts Briefly describe each of the following Autonomous Systems Categories: (a) Stub AS (b) Multihomed AS (c) Transit AS Has only one connection to another AS Has more than one connection to other ASes, but doesn’t allow data to pass through it Connects to more than one AS and allows traffic to pass through it BGP/BGP Routing 20 pts Describe the steps followed in BGP routing when selecting a route. 1) a BGP router first attempts to find all paths from the router to a given destination 2) it then judges these paths against the policies of the AS administrator 3) it then selects a “good enough” path to the destination that satisfies the policy constraints BGP/BGP Routing 40 pts Consider the network diagram and BGP route announcement from Router 3 below, assuming no local preferences are set. What AS path would an IP packet from 12.12.12.1 take to reach 17.17.200.2? 40 – 2003 – 2005 What AS path would an IP packet from 13.13.13.3 take reach 17.17.200.2? 40 – 2003 – 2005 What AS path would an IP packet from 20.20.20.1 take to reach 17.17.200.2? 60 – 40 – 2003 – 2005 BGP/BGP Routing 60 pts Name and describe (include negative and positive consequences) one technical solution that an AS network operator can use to combat prefix hijacking an MITM attack on BGP networks? Filtering – Best current practices for AS network operators dictate the use of filters at AS borders to reject suspicious route announcements or alter malicious route attributes. Filters are manually established based on the routing policies of an organization. Filtering has both a business cost and computational cost associated with it. Internet Routing Registries – These are repositories of the IP prefixes, ASNs, routing policy, network topology, and human points of contact for those ASes which choose to register their information. While this method may be effective, the downside is that these registries are only effective if the registry data is secure, complete, and accurate, which is currently not guaranteed. Resource Public Key Infrastructure (RPKI) – Similar to the IRRs, RPKI is a repository of Internet routing information. The key difference is that it uses the X.509 certificate system to provide cryptographic assurance of (1) the association between an ASN and the IP prefixes it has been allocated, and (2) the association between an ASN and the IP prefixes it is authorized to originate. There is nothing in RPKI which validates the route attributes, including the AS path, associated with a BGP route announcement from an AS. Nor does it provide certainty that the AS which has registered their information used the correct ASN or set of prefixes. Nor does it provide network topology information or human points of contact as with IRRs. Lastly, it does not mandate that network operators use this information when constructing their filters. How RPKI is applied is entirely dependent on what AS network operators choose to do with the information available.