EC310: Applications of Cyber Engineering Alpha: ____________________ Exam #2
advertisement

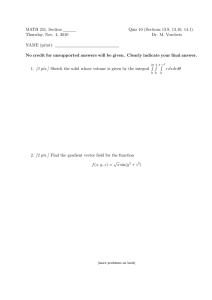
EC310: Applications of Cyber Engineering Exam #2 Alpha: ____________________ Section: ____________________ 12 WEEK EXAM NAME: 1. 2. 3. 4. ______________________ This is individual work. SHOW ALL WORK! Write legibly to receive credit. Turn in your equation sheet. SCORE: ___________/100 1 SCALE >89.5%: 31337 79.5 – 89.5%: H@XX0R 69.5 – 79.5%: G33K 59.5 – 69.5%: $€RiPt K1DD13 <59.5%: n00b EC310: Applications of Cyber Engineering Exam #2 Lesson 11/12 – TCP/IP model/Ethernet Alpha: ____________________ Section: ____________________ 1. [7.5] List the layers of the TCP/IP model and select the letter that best describes the main function of each. (0.5 pts for each table item, 1 pt for each letter) ____ ____ ____ ____ ____ a. b. c. d. e. Transfers frames across a single link connecting two nodes Responsible for end-to-end flow, error, and congestion control Sends bits over a channel Processes that provide services to users such as HTTP and FTP Responsible for routing packets and internetworking 2. [7] Two standard (10 Mbps) Ethernet topologies are illustrated in Figure 1 and Figure 2 for a network consisting of six computers. Study the figures and answer the questions below. (Show your work for maximum credit) Figure 1 Figure 2 a. How much bandwidth does each user get for the network topology depicted in Figure 1? (2 pts) b. How much bandwidth does each user get for the network topology depicted in Figure 2? (2 pts) c. How much bandwidth would each user get if a switch was used to connect together the six computers in my network? (3 pts) 2 EC310: Applications of Cyber Engineering Exam #2 Lesson 13 – Internet Protocol Alpha: ____________________ Section: ____________________ 3. [4] Answer True or False to each of the following statements: (1 pt each) a. An IP address is a software address. T/F b. IP addresses are used at the network layer. T/F c. There are 6 bytes in an IP address. T/F d. Once set, the IP address of a computer never changes. T / F 4. [3] Select from the following those that are valid IPv4 network mask? (There maybe more than 1 correct answer) a. /45 b. 255.255.128.0 c. 128.255.255.0 d. 255.255.240.0 e. /16 5. [9] You are a network administrator and given the following block of addresses from your ISP 137.18.129.128/27 a. How many hosts can you support on this network? (Show your work for maximum credit) (2 pts) b. What is the first possible host ID? (Show your work for maximum credit) (2 pts) c. What is the last possible host ID? (Show your work for maximum credit) (3 pts) d. What is the broadcast address for your network? (Show your work for maximum credit) (2 pts) 3 EC310: Applications of Cyber Engineering Exam #2 Alpha: ____________________ Section: ____________________ Lesson 14/15 – Routing Part I/II 6. [4] What feature of the Address Resolution Protocol makes it particularly vulnerable to a spoofing attack? 7. [4] Fill in the blanks for the below statements that describe the two major categories of routing protocols. (2 pts each) a. In ___________ routing, a router will tell its immediate neighbors what it knows about the entire network. b. In ___________ routing, a router will tell the entire network what it knows about its immediate neighbor (controlled flooding). 8. [8] Complete the partial routing table for Router C for the destinations listed below. (1 pt each) Destination Next element Total cost --- 0 A B C D E 4 EC310: Applications of Cyber Engineering Exam #2 Lesson 16 – MITM Attack Alpha: ____________________ Section: ____________________ 9. [4] What does a router assume by default when another router sends it information about the state of its links or the distance between it and other routers? 10. [20] An attacker is located on the 3.4.5.0/25 network and wants to prevent midshipmen from reaching a website at 8.9.7.96. He turns his computer into a router using Loki and advertises a false network of 8.9.7.80/28 to Router A. EC310 MID c. There are 3 parts to complete this question. i. Fill in the blanks to complete Router A’s routing table. (0.5 pts each) ii. In the line provided below Router A’s routing table, fill in the false route the attacker would inject. (4 pts) iii. Draw a line from the false route pointing to the location in which it would be injected into Router A’s routing table. (2 pts) 5 EC310: Applications of Cyber Engineering Exam #2 Alpha: ____________________ Section: ____________________ d. Will the attacker be successful in redirecting the midshipmen’s traffic? Justify your answer. (5 pts) e. List and briefly describe two technical solutions that could be implemented on Router A to prevent the attacker from injecting false routing information. (2 pts each) Solution #1 Solution #2 Solution #3 f. Who is responsible for configuring these security measures on Router A (check one)? (1 pt) _________ : The Network User _________ : The Network Administrator _________ : The Network Hardware Manufacturer _________ : The Network Programmer 6 EC310: Applications of Cyber Engineering Exam #2 Lesson 17/18 – Border Gateway Protocol I/II Alpha: ____________________ Section: ____________________ 11. [6] State and briefly describe the two problems solved by partitioning the Internet into a number of separate Autonomous Systems vice using a single routing protocol. (3 pts each) 12. [7.5] Which (if any) of the two flavors of BGP would routers in the picture below need to be running. 7 EC310: Applications of Cyber Engineering Exam #2 Alpha: ____________________ Section: ____________________ 13. [9] Given the below figure, fill in the BGP Path Table for R4. Note: R1 is preferred over R3. R4 BGP Path Table Networks Next AS 14. [7] AS8 wants to transmit packets of data to AS3. Due to a peering conflict, AS8 will not allow packets to traverse through AS7. Circle each link in the path you will take to route packets to AS3 and calculate the total cost. Total Cost: TURN IN YOUR HAND-WRITTEN EQUATION SHEET WITH YOUR EXAM _____________________________________________________________________________________________