Document 10409632
advertisement

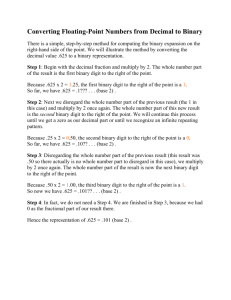
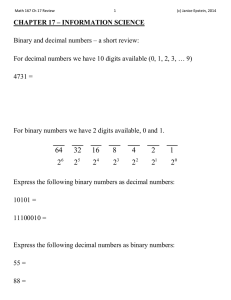
(c) Epstein, Carter & Bollinger 2016 Exam 3 Review P a g e |1 Exam 3 Topics Chapter 16 – Identification Numbers Know what 𝑎 mod 𝑚 ≡ 𝑏 means (section 17.1 in the book). Be able to calculate 𝑥 𝑚𝑜𝑑 𝑦 (section 17.1 in the book). Understand the purpose of a check digit. Know the most common types of errors (single-digit errors, adjacent transpositions, jump transpositions) that can occur when dealing with identification numbers. When given the scheme to determine a check digit, be able to o Find the check digit. o Determine if a code is valid. o Find a missing value in the code if the check digit is given. o Determine which errors are and are not caught by the check digit scheme. Know which digits of a zip code signify the geographic region, section facility, and local delivery areas. Recognize a bar code. Given a chart of symbols, write or decode a bar code. Given an identification number and the scheme, use it to code or decipher the information such as birth date and gender. Chapter 17 – Information Science Know what a binary code is. Know how to convert from binary numbers (base two) to decimal numbers (base ten) and decimal numbers to binary numbers. Use error checking to determine or verify a code word, given the message and the error checking method. Be able to compute check digits for code words using the Venn Diagram that symbolized the parity-check sum scheme used in the notes. When there is a single error, be able to correct code words using the Venn Diagram that symbolized the paritycheck sum scheme used in the notes. Be able to compute check digits for code words given the parity-check sums for the code. Be able to determine the distance between two strings. Be able to determine the weight of a binary code and use the weight to determine the error detecting/correcting abilities of the code. Know what nearest-neighbor decoding is and be able to use it for decoding messages. Be able to encode and decode messages that have symbols (such as letters of the alphabet) expressed in binary form when the coding scheme is provided. Use delta encoding to compress or expand data. Be able to create a Huffman code given a table of probabilities and use it to encode a message. Be able to decode using a Huffman code. Be able to encrypt and decrypt messages using the Caesar, decimation, and Vigenère ciphers. Be able to add binary strings.