Experiment 2_1433_1434_term2
advertisement

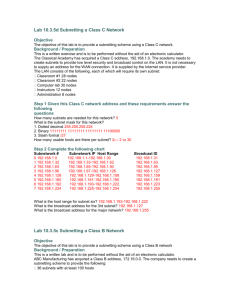
Experiment 2 Designing the network, IP addressing and Subnets, designing using Variable Length Subnet Mask Dr. Mohamed Abd-Eldayem References: • CCNA Curriculum • CCNA Command Quick Reference by Scott Epson 1 2.1 Ethernet Switching 2.1 Layer 2 bridging 2 2.1 Layer 2 bridging The bridge has just been started so the bridge table is empty. The bridge just waits for traffic on the segment. When traffic is detected, it is processed by the bridge. Host A is pinging Host B. Since the data is transmitted on the entire collision domain segment, both the bridge and Host B process the packet. The bridge adds the source address of the frame (Host A) to its bridge table. Since the address was in the source address field and the frame was received on port 1, the frame must be associated with port 1 in the table. The destination address of the frame is checked against the bridge table. Since the address is not in the table, the frame is forwarded to the other segment. Host B processes the ping request and transmits a ping reply back to Host A. The data is transmitted over the whole collision domain. Both Host A and the bridge receive the frame and process it. The bridge adds the source address of the frame to its bridge table (Host B). Since the source address was not in the bridge table and was received on port 1, the source address of the frame must be associated with port 1in the table. The destination address of the frame is checked against the bridge table. Since the address is in the table, the port assignment is checked. The address of Host A is associated with the port the frame came in on, so the frame is not forwarded. 3 2.1 Layer 2 bridging: Controls traffic between two collision domains Host A ping Host C. Since the data is transmitted on the entire collision domain 4 segment, both the bridge and Host B process the frame. Host B discards the frame as it was not the intended destination. The bridge adds the source address of the frame to its bridge table. Since the address is already entered into the bridge table the entry is just renewed. The destination address of the frame (Host C) is checked against the bridge. Since the address is not in the table, the frame is forwarded to the other segment. Host C processes the ping request and transmits a ping reply back to Host A. The data is transmitted over the whole collision domain. Host D discards the frame, as it was not the intended destination. The bridge adds the source address of the frame (Host C) to its bridge table. The frame must be associated with port 2 in the table. The destination address of the frame (Host A) is checked against the bridge. The address is in the table but it is associated with port 1, so the frame is forwarded to the other segment. •A bridge has only two ports and divides a collision domain into two parts, but it do not affect the logical or Layer 3 addressing. Thus, a bridge will divide a collision domain but has no effect on a logical or broadcast domain. 5 2.2 Switch operation 6 •A switch is simply a bridge with many ports. When only one node is connected to a switch port, the collision domain on the shared media contains only two nodes. •Most switches are capable of supporting full duplex 2.3 Class A, B, C, D, and E IP addresses IP addresses are divided into: Class A addresses are assigned to larger networks. Class B addresses are used for medium-sized networks, and Class C for small networks. The first step in determining which part of the address identifies the network and which part identifies the host is identifying the class of an IP address. Default Subnet Mask 255 . 0 . 0 . 0 11111111.00000000.00000000.00000000 255 . 255 . 0 . 0 11111111.11111111.00000000.00000000 255 . 255 . 255 . 0 11111111.11111111.11111111.00000000 255 . 255 . 255 . 255 11111111.11111111.11111111.11111111 1: indicates Network Portion 0: indicates Host Portion 7 2.3 Class A, B, C, D, and E IP addresses 8 2.4 Reserved IP addresses: Network address – Used to identify the network itself An IP address that has binary 0s in all host bit positions is reserved for the network address. Ex.:The 198.150.11.0 network. Data that is sent to any host on that network (198.150.11.1- 198.150.11.254) will be seen outside of the local area network as 198.159.11.0. The only time that the host numbers matter is when the data is on the local area network. Broadcast address – Used for broadcasting packets to all the devices on a network The 198.150.11.255 broadcast address. Data that is sent to the broadcast address will be read by all hosts on that network (198.150.11.1- 198.150.11.254). 9 2.5 Public and private IP addresses Public IP addresses are unique and it must be obtained from an Internet 10 service provider (ISP) RFC 1918 sets aside three blocks of IP addresses for private, internal use. These three blocks consist of one Class A, a range of Class B addresses, and a range of Class C addresses. Addresses that fall within these ranges are not routed on the Internet backbone. Internet routers immediately discard private addresses. If addressing a nonpublic intranet, a test lab, or a home network, private addresses can be used instead of globally unique addresses. Also Private IP addresses can be intermixed with public IP addresses. This will conserve the number of addresses used for internal connections. Connecting a network using private addresses to the Internet requires translation of the private addresses to public addresses. This translation process is referred to as Network Address Translation (NAT). 11 2.6 The Mechanics of Subnetting 2.6.1 Introduction Subnetting is to devid a large network into smaller subnetworks To create the subnetwork structure, host bits must be reassigned as network bits. The 12 starting point for this process is always the leftmost host bit. Subnet addresses include the Class A, Class B, and Class C network portion, plus a subnet field and a host field. The subnet field and the host field are created by assigning bits from the host portion (Network Part portion never changes) to the original network portion of the address. Subnetting provides addressing flexibility for the network administrator, and enable him to provide broadcast containment and low-level security on the LAN. Subnetting provides some security since access to other subnets is only available through the services of a router. Further, access security may be provided through the use of access lists. A LAN is seen as a single network with no knowledge of the internal network structure. This view of the network keeps the routing tables small and efficient. Given a local node address of 192.168.10.14, the world outside the LAN sees only the advertised major network number of 192.168.10.0. The reason for this is that the local address of 192.168.10.14 is only valid within the LAN 192.168.10.0 and cannot function anywhere else. 13 •For any IP address, if the subnet mask is the default IP address of that class then there is no subnetting 2.6.2 Establishing the subnet mask address Selecting the number of bits to use in the subnet process will depend on the maximum number of hosts required per subnet. Most Significant Bit (MSB) List Significant Bit (LSB) The last two bits in the last octet, regardless of the IP address class, may never be assigned to the subnetwork. The subnet mask gives the router the information required to determine in which network and subnet a particular host resides. The subnet octet or octets are determined by adding the position value of the bits that were borrowed. The subnet octet or octets are determined by adding the position value of the bits that were borrowed. If three bits were borrowed, the mask for a Class C address would be 255.255.255.224. This mask may also be represented, in the slash format, as /27. The number following the slash is the total number of bits that were used for the network and subnetwork portion To determine the number of bits to be used, the network designer needs to calculate how many hosts 14 the largest subnetwork requires and the number of subnetworks needed. Subnetting chart 15 Ex1.: A network requires 30 hosts and five subnetworks. IP = 192.168.10.0, Class C Using the subnetting chart, by consulting the row titled ”Usable hosts”, the chart indicates that for 30 usable hosts three bits are required. This creates, six usable subnetworks. Number of usable subnets= two to the power of the assigned subnet bits or borrowed bits, minus two (reserved addresses for subnetwork id and subnetwork broadcast) usable subnets =(2 borrowed bits) – 2 = (23) – 2 = 6 Number of usable hosts= two to the power of the bits remaining, minus two (reserved addresses for subnet id and subnet broadcast) usable hosts= (2 remaining host bits) – 2 = (25) – 2 = 30 16 Ex1.: Applying the subnet mask Start with zero (0) when numbering subnets. The first subnet is always referenced as the 17 zero subnet (the same as the major network number), in this case 192.168.10.0. The broadcast ID for the whole network is the largest number possible, in this case 192.168.10.255. The subnetwork ID for subnet number seven. This number is the three network octets with the subnet mask number inserted in the fourth octet position. Three bits were assigned to the subnet field with a cumulative value of 224. When consulting the subnetting chart or using the formula, the three bits assigned to the subnet field will result in 32 total hosts assigned to each subnet. This information provides the step count for each subnetwork ID. Adding 32 to each preceding number, starting with subnet zero, the ID for each subnet is established. Notice that the subnet ID has all binary 0s in the host portion. The broadcast field is the last number in each subnetwork, and has all binary ones in the host portion. This address has the ability to broadcast only to the members of a single subnet Since the subnetwork ID for subnet zero is 192.168.10.0 and there are 32 total hosts the broadcast ID would be 192.168.10.31. Starting at zero the 32nd sequential number is 31. 2.6.3 Subnetting Class A and B networks The available bits for assignment to the subnet field in a Class A address is 22 bits while a Class B address has 14 bits. Assigning 12 bits of a Class B address to the subnet field creates a subnet mask of 255.255.255.240 or /28. Assigning 20 bits of a Class A address to the subnet field creates a subnet mask of 255.255.255.240 or /28. class of address needs to be subnetted: Total subnets = 2 the bits borrowed Total hosts= 2 the bits remaining Usable subnets = 2 the bits borrowed - 2 Usable hosts= 2 the bits remaining - 2 18 19 Steps to Solve Subnetting Questions 1) Look at the MSB of the IP, Identify the Class(A, B or C), then determine the number of bits assigned to the Network Portion (8 for class A, 16 for Class B and 24 for Class C) Ex.: IP=182.250.200.3, Class = B, N =16 bits 2) Look at Subnet Mask (SM), the number of zeros identify the Host portion Ex. SM = 11111111.11111111.11111111.00000000, H=8 bits 3) Look at IP and SM together, The portion Between the Network and Host portions is the Sub Network portion. Ex. IP= 182 . 250 . 200 . 3 10110110. 11111010.11001000.00000011 SM = 11111111.11111111.11111111.00000000 = 255.255.255.0 N = 16 SN = 8 H= 8 4) Identify the Subnet ID: By doing (IP address ) AND (Mask) Subnet ID = 10110110. 11111010.11001000.00000000 5) Identify Broadcast address: By changing all bits of host portion in Subnet ID to 1’s. Broadcast address = 10110110. 11111010.11001000.11111111 6) Identify the First IP address: Change the LSB of host portion in Subnet ID to 1. First IP address = 10110110. 11111010.11001000.00000001 7) Identify the Last IP address: Subtract 1 from host portion of Broadcast address. Last IP address = 10110110. 11111010.11001000.11111110 20 Example: IP=182.250.200.250, SM= 255.255.255.128 IP SM = 10110110. 11111010.11001000.11111010 = 11111111.11111111.11111111.10000000 N = 16 21 Subnet ID Broadcast address First IP address Last IP address SN = 9 H= 7 = 10110110. 11111010.11001000.10000000 = 10110110. 11111010.11001000.11111111 = 10110110. 11111010.11001000.10000001 = 10110110. 11111010.11001000.11111110 Variable Length Subnet Mask (VLSM) 22 Variable-Length Subnet Masking (VLSM) is the more realistic way of subnetting a network to make for the most efficient use of all of the bits. Classful (classical) subnetting are inefficient because all subnets have the same number of hosts because they all use the same subnet mask. For example, if you borrow 4 bits on a Class C network, you end up with 14 valid subnets of 14 valid hosts. A serial link to another router only needs 2 hosts, but with classical subnetting, you end up wasting 12 of those hosts. VLSM is the process of “subnetting a subnet” and using different subnet masks for different networks in your IP plan. IP Subnet Zero With classical subnetting, you always have to eliminate the subnets that contain either all zeros or all ones in the subnet portion. Hence, number of valid subnets =2N– 2 Cisco devices can use those subnets, as long as the command ip subnet-zero is in the configuration. (Router(config)#ip subnet-zero). Hence, number of valid subnets =2N 23 Example: Create an IP plan using VLSM for a Class C network—192.168.100.0/24 1) 2) 3) 4) 5) 24 Determine how many H bits will be needed to satisfy the largest network. Pick a subnet for the largest network to use. Pick the next largest network to work with. Pick the third largest network to work with. Determine network numbers for serial links. 1) Determine how many H bits will be needed to satisfy the largest network. 2H – 2 ≥ 50, Therefore H = 6 for Network A You need 6 H bits, 2 N bits (8 – 6 ) to create subnets Now have: NNHHHHHH (The 8 bits in the fourth octet) All subnetting will now have to start at this reference point. 2) Pick a subnet for the largest network to use. We have 2N or 22 or 4 subnets: NN = 00HHHHHH 01HHHHHH 10HHHHHH 11HHHHHH 25 If you add all zeros to the H bits, you are left with the network numbers for the four subnets: 00000000 = .0 Network A 01000000 = .64 10000000 = .128 11000000 = .192 All of these subnets will have the same subnet mask: 11111111.11111111.11111111.11000000 Or 255.255.255.192 or /26 , The /x notation represents how to show different subnet masks when using VLSM. /26 means that the first 26 bits of the address are network; the remaining 6 bits are H bits. 3) Pick the next largest network to work with. 2H – 2 ≥ 27, H = 5, You need 5 H bits for Network B. Pick one of the remaining /26 networks to work with Network B. Select 128/26 network: 10000000 But you need only 5 H bits, not 6. Therefore, you are left with 10N00000 Where 10 represents the original pattern of subnetting. N represents the extra bit. 00000 represents the 5 H bits you need for Network B. Because you have extra bit, you can create two smaller subnets from the original subnet: 10000000 =.128 and 10100000 =.160 You have now subnetted a subnet! This is the basis of VLSM. The mask now equals: 11111111.11111111.11111111.11100000 or 255.255.255.224 or /27 Pick one of these new sub-subnets for Network B: 10000000 /27 = Network B Use the remaining sub-subnet for future growth, You want to make sure the addresses are not overlapping with each other. So go back to the original table. 26 3) Pick the next largest network to work with. 27 (Continue) 4) Pick the third largest network to work with. 2H – 2 ≥ 12, H = 4, Networks C and Network D = 12 hosts each. You can chose .192/26 network, or .160/27 network. (select 160/27): 10100000 But you only need 4 H bits, not 5. Therefore, you are left with 101N0000 Because you have this extra bit, you can create two smaller subnets from the original subnet: 10100000 = .160 and 10110000 = .176, Masks will be 11111111.11111111.11111111.11110000 or 255.255.255.240 or /28 Pick one of these new sub-subnets for Network C and one for Network D. 28 5) Determine network numbers for serial links. All serial links between routers have the same property in that they only need two addresses in a network—one for each router interface. Determine the number of H bits needed for these networks: 2H – 2 ≥ 2, H = 2 You need 2 H bits to satisfy the requirements of Networks E, F, G, and H. You have two of the original subnets left to work with. Select the .0/26 network: 00000000 But you need only 2 H bits, not 6. Therefore, you are left with 00NNNN00 where 00 represents the original pattern of subnetting. NNNN represents the extra bits you have. 00 represents the 2 H bits you need for the serial links. Because you have 4 N bits, you can create 16 sub-subnets from the original subnet: 00000000 = .0/30 00000100 = .4/30 00001000 = .8/30 00001100 = .12/30 00010000 = .16/30 ........................... ........................... 00111000 = .56/30 00111100 = .60/30 29 •You need only four of them. You can hold the rest for future expansion •Going back to the original table •No number is used twice. •You have now created an IP plan for the network and have made the plan as efficient as possible, • wasting no addresses in the serial links and leaving room for future growth. •This is the power of VLSM! 30