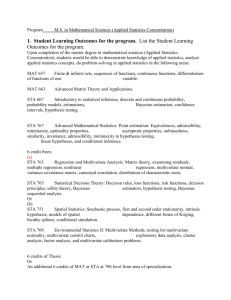
Capwap Overview
advertisement
CAPWAP Overview SAAG Presentation 65th IETF 23 March 2006 Scott G. Kelly scott@hyperthought.com T. Charles Clancy clancy@cs.umd.edu Agenda • Introduction • Some background and current scope • Security-related protocols, relationships, considerations, requirements • Current state of things • Conclusion 23 March 2006 CAPWAP Overview 2 Introduction • CAPWAP working group is defining a protocol to control and provision wireless access points • Things carried over the protocol include – – – – Access Point configuration/control Network access control decisions Cryptographic session keys User data • Security is obviously a significant concern • Working group wants to invite security area participation • Requesting appointment of a security advisor – Provide designated point of contact with security directorate – Help to avoid delays, surprises in document advancement process due to unforeseen security concerns 23 March 2006 CAPWAP Overview 3 Background Early Architecture WLAN ELEMENTS Mgmt AS/AAA AS: Authentication Server, typically RADIUS AP AP: wireless access point AP STA: wireless station (typically a laptop) STA 23 March 2006 CAPWAP Overview STA STA STA 4 Background • Early WLAN deployments rely on “fat” access points – Standalone, individually managed network elements – mgmt scaling issues • Limited RF range implies many APs required for significant coverage area – User roaming implies other infrastructure issues • Relatively simple trust chain – STA-AP • EAPoL • WEP – AP-AS • EAP over RADIUS 23 March 2006 CAPWAP Overview 5 Current Architecture (Security Protocol Hierarchy and Interactions) Mgmt AAA SNMP HTTP TLS SSH RADIUS Optional IPsec AC AC CAPWAP CAPWAP WTP WTP WTP 802.1X, 802.11i, WPA 802.1X, 802.11i, WPA STA STA STA STA WTP STA STA STA STA Each layer in hierarchy depends on layers above for security 23 March 2006 CAPWAP Overview 6 Background, cont. • Current generation moving to centralized control model, “thin” access points – AC: access controller, centralized point of control – WTP: wireless termination point (new name for access points) • Complex interactions – AC-AAA • EAP over RADIUS (optional IPsec) – WTP-STA • WEP, WPA, WPA2, 802.11i – AC-WTP • Intermediate communications impacting all aspects of operations • This presents a number of challenges that merit IETF attention 23 March 2006 CAPWAP Overview 7 Complex Trust Relationships Color Coding Mgmt • short-term keys • long-term keys AAA RADIUS PSK Admin Credential MK AC MSK/PMK Long-Term EAP Credential AC PSK/Cert WTP WTP WTP WTP PTK STA 23 March 2006 STA STA STA STA CAPWAP Overview STA STA STA 8 CAPWAP Interdependencies Protocols, trust relationships, etc • Many interdependent security protocols between STA and network • CAPWAP is used to bootstrap trust between the STA and WTP using a series of pre-established trust relationships – – – – AAA credential between AC and AS CAPWAP credential between AC and WTP EAP credentials between STA and AS 802.11i security context (PTK) between WTP and STA • CAPWAP must not degrade security of surrounding components 23 March 2006 CAPWAP Overview 9 CAPWAP Threats • Multiple deployment models – Direct L2 connection – Routed L3 connection, one administrative domain – Routed L3 connection, over potentially hostile hops • Direct L2 connection – Largely a physical security problem – Post a guard, lock the doors, etc. • Routed L3 connection, same administrative domain – Seems similar to L2 at first glance, but… – Mobile systems invalidate many assumptions regarding security of local LAN (soft and chewy inside is now exposed) – Can mitigate with network admission control, VLANs, etc, but CAPWAP cannot assume or mandate these things 23 March 2006 CAPWAP Overview 10 CAPWAP Threats, cont. • Routed L3 connection, over potentially hostile hops – Examples • Remote WTP scenarios – – – – Employees take WTPs home, connect back to central AC Branch office WTP, central office AC Hotspots some hops may be over wireless • Mesh (e.g. metro wifi) – Threat mitigation requires strong crypto • Mutual authentication • Data integrity verification • Confidentiality in many cases 23 March 2006 CAPWAP Overview 11 Additional CAPWAP Security Considerations • “Splitting the MAC” introduces security complexity, subtleties • Functionality previously handled by AP is now divided between WTP and AC • Examples – If 802.11 crypto is terminated at the WTP, security context must arrive there securely (via AC), and WTP must implement 802.11 data security functions • Otherwise, AC implements 802.11 data security functions – Since user/station authentication is mediated by the AC, it must securely interact with AS • WTP forwards 802.1X frames to AC • AC-WTP communications must not be weak link in chain 23 March 2006 CAPWAP Overview 12 CAPWAP Protocol Security Requirements IN SCOPE • AC ↔ WTP – Authentication is unique, strong, mutual, and explicit – Communications protected by strong ciphersuite NOT CURRENTLY IN SCOPE (but important to be aware of) • • • • AC ↔ AAA STA ↔ AAA STA ↔ WTP Management ↔ AC 23 March 2006 CAPWAP Overview 13 Current State of CAPWAP • 4 competing protocol proposals were evaluated – WG created independent eval team – Protocols: LWAPP,SLAPP,WiCoP,CTP • WG chose LWAPP as basis for new CAPWAP protocol • LWAPP provides its own proprietary security mechanisms • Eval team (and others) recommended replacing this with DTLS 23 March 2006 CAPWAP Overview 14 LWAPP Security Protocol, cont. • T. Charles Clancy (UMD) conducted security review, proposed improvements • Protocol subsequently modified to meet wg objectives draft requirements and Clancy suggestions • LWAPP/DTLS draft submitted by Kelly & Rescorla • DTLS added to capwap-00 draft as proposed security mechanism • Numerous operational details yet to be specified, but no show-stoppers uncovered or anticipated • WG still discussing, hopefully to reach closure soon 23 March 2006 CAPWAP Overview 15 Compare/Contrast DTLS vs LWAPP DTLS LWAPP • Standards-based protocol • Home-grown protocol • TLS is well reviewed (DTLS is equivalent from security perspective) • Latest incarnation has only one public review • Widely deployed on the Internet (TLS) • Little deployment experience • Negotiation capability provides for algorithm agility • No algorithm negotiation – crypto change requires protocol forklift • Several freely available implementations • No known open source implementations • Built-in DoS protection • No DoS protection • Employs security best practices • A few questionable security practices – – – • – – – Unidirectional crypto keys Each side contributes to IVs Security parameter verification via message hash Continued benefit from broad deployment and scrutiny 23 March 2006 • Same key used for transmit/receive One side controls IV generation No verification of negotiable parameters (psk vs cert) One-off (capwap-only) deployment severely limits exposure to scrutiny CAPWAP Overview 16 SUMMARY • • • • Security is clearly an integral concern for CAPWAP IEEE efforts primarily focused on STA+WTP+AS ACWTP interactions introduce various subtleties It’s easy to get security wrong, even when clueful people are involved – more skilled reviewers mitigates the risk • CAPWAP would clearly benefit from additional security community participation • Group is requesting a security advisor – Designated point of contact with security directorate – Avoid delays in document advancement due to security concerns • Questions? 23 March 2006 CAPWAP Overview 17