Chapter 11
advertisement
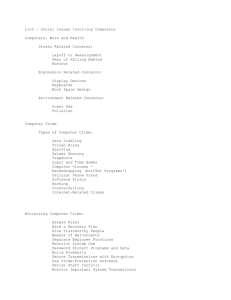
Chapter 11-1 Chapter 11: Computer Crime, Fraud, Ethics, and Privacy Introduction Computer Crime, Abuse, and Fraud Three Examples of Computer Crimes Preventing Computer Crime and Fraud Ethical Issues, Privacy, and Identity Theft Chapter 11-2 Computer Crime, Abuse, and Fraud High level of public interest Data on incidents is limited Sources of information Computer Security Institute (CSI) annual survey KPMG surveys Association of Certified Fraud Examiners (ACFE) survey Chapter 11-3 Computer Crime, Abuse, and Fraud Computer Crime Manipulation of a computer or computer data Dishonestly obtain money, acquire property, or something of value, or cause a loss Computer Abuse Unauthorized use of, or access to, a computer Against the wishes of the owner Chapter 11-4 Computer Crime Examples Chapter 11-5 Computer Crime, Abuse, and Fraud Fraudulent Financial Reporting Intentional falsification of accounting records Intend to mislead analysts, creditors, investors Misappropriation of Assets Misuse of company assets Committed by employees within an organization Chapter 11-6 Asset Misappropriation Examples Chapter 11-7 Federal Legislation of Computer Crimes Computer Fraud and Abuse Act of 1986 (CFAA) Amended in 1994 and 1996 Computer Fraud Definition An illegal act Computer technology essential for perpetration, investigation, or prosecution Chapter 11-8 CFAA Fraudulent Acts Unauthorized theft, use, access, modification, copying, or destruction of software or data Theft of money by altering computer records or the theft of computer time Intent to illegally obtain information or tangible property through the use of computers Chapter 11-9 CFAA Fraudulent Acts Use, or the conspiracy to use, computer resources to commit a felony Theft, vandalism, destruction of computer hardware Trafficking in passwords or other login information for accessing a computer Extortion that uses a computer system as a target Chapter 11-10 Federal Legislation Affecting the Use of Computers Chapter 11-11 Federal Legislation Affecting the Use of Computers Chapter 11-12 State Legislation Every state has a computer crime law State law provisions Define computer terms Define some acts as misdemeanors Declare other acts as felonies Chapter 11-13 Computer-Crime Statistics Limited availability of data Private companies handle abuse internally Most computer abuse is probably not discovered Growth of computer crime Exponential growth in use of computer resources Continuing lax security Availability of information about how to perpetrate computer crimes Chapter 11-14 Importance of Computer Crime and Abuse to AISs Impact on AISs Favored target due to control of financial resources Prized target for disgruntled employees Responsible for designing, selecting, and implementing controls that protect AISs Reliance on auditors to verify financial statement Additional Items Ability to mislead public if information is incomplete or inaccurate Difficulty in detecting fraudulent activities Large amount of losses Chapter 11-15 Compromising Valuable Information: The TRW Credit Data Case Summary Credit rating company Altered company credit ratings for a fee Clients relied on inaccurate information Analysis diddling – proprietary data Fair Credit Reporting Act – protection of consumer Data Chapter 11-16 Wire Fraud and Computer Hacking: Edwin Pena and Robert Moore Summary Voice over Internet Protocol (VoIP) Hacked into other provider’s network Billed those companies Analysis Growth of hacking Importance of education and prevention Utilize ethical hackers for instrusion testing Chapter 11-17 Denial of Service: The 2003 Internet Crash Summary Slammer worm Identified weakness in Microsoft SQL Server 2000 software Analysis Denial of Service (DOS) attacks Computer Viruses Computer Worms and Worm Programs Boot-sector Viruses and Trojan Horse Programs Chapter 11-18 Protecting Systems Preventing Viruses Firewalls Antivirus software Antivirus control procedures Organizational Control Procedures Discourage free exchange of computer disks or external programs Require strong passwords to limit unauthorized access Use antivirus filters Chapter 11-19 Common Types of Computer Crime and Abuse Chapter 11-20 Preventing Computer Crime and Fraud Enlist Top-Management Support Increase Employee Awareness and Education Assess Security Policies and Protect Passwords Strong passwords Social engineering Lock-out systems Dialback systems Chapter 11-21 10 Simple Steps to Safer PCs Chapter 11-22 10 Simple Steps to Safer PCs Chapter 11-23 Preventing Computer Crime and Fraud Implement Controls Identify Computer Criminals Nontechnical Backgrounds Noncriminal Backgrounds Education, Gender, and Age Don’t Forget Physical Security Employ Forensic Accountants Chapter 11-24 Occupations of Computer Abuse Offenders Chapter 11-25 Fraud Losses and Education Level of Perpetrator Chapter 11-26 Recognizing Symptoms of Employee Fraud Accounting Irregularities Internal Control Weaknesses Unreasonable Anomalies Lifestyle Changes Behavioral Changes Chapter 11-27 Study Break #4 Most computer criminals: A. B. C. D. E. Have nontechnical backgrounds Have noncriminal backgrounds Have little college education Are young and bright Have probably not been caught, so we don’t know much about them Chapter 11-28 Study Break #4 - Answer Most computer criminals: A. B. C. D. E. Have nontechnical backgrounds Have noncriminal backgrounds Have little college education Are young and bright Have probably not been caught, so we don’t know much about them Chapter 11-29 Ethical Issues, Privacy, and Identity Theft Ethics A set of moral principles or values Governs organizations and individuals Ethical behavior Making choices and judgments that are morally proper Acting accordingly Chapter 11-30 Ethical Issues, Privacy, and Identity Theft Ethical Issues and Professional Associations Codes of Ethics/Professional Conduct Certification programs and Ethics committees Meeting the Ethical Challenges Inform employees of importance of ethics Ethics training Lead by example Utilize reward system Chapter 11-31 Ethical Issues in Computer Usage Chapter 11-32 Ethical Issues, Privacy, and Identity Theft Company Policies with Respect to Privacy Who owns the computer and data stored on it? What purposes the computer may be used? What uses are authorized or prohibited? Identity Theft Dumpster diving Phishing Smishing Chapter 11-33 Identity Theft Methods Chapter 11-34