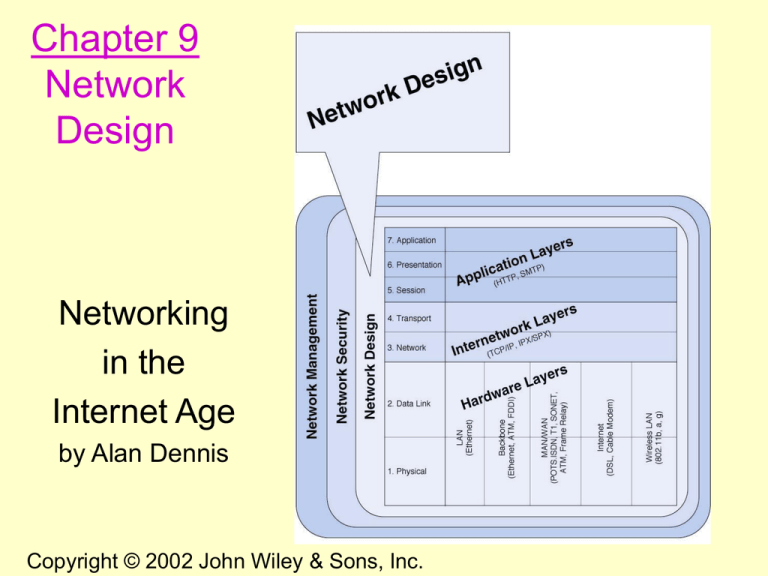
Chapter 9
Network
Design
Networking
in the
Internet Age
by Alan Dennis
1
Copyright © 2002 John Wiley & Sons, Inc.
Copyright John Wiley & Sons, Inc. All rights reserved.
Reproduction or translation of this work beyond that named in
Section 117 of the United States Copyright Act without the
express written consent of the copyright owner is unlawful.
Requests for further information should be addressed to the
Permissions Department, John Wiley & Sons, Inc. Adopters of
the textbook are granted permission to make back-up copies for
their own use only, to make copies for distribution to students of
the course the textbook is used in, and to modify this material to
best suit their instructional needs. Under no circumstances can
copies be made for resale. The Publisher assumes no
responsibility for errors, omissions, or damages, caused by the
use of these programs or from the use of the information
contained herein.
2
Chapter 9. Learning Objectives
• Be familiar with the overall process of design
and implementing a network
• Be familiar with techniques for developing a
logical network design
• Be familiar with techniques for developing a
physical network design
• Be familiar with network design principles
3
Chapter 9. Outline
• Introduction
– Traditional Network Design, Building Block Network
Design
• Needs Analysis
– Geographic Scope, Application Systems, Network Users,
Categorizing Network Needs, Deliverables
• Technology Design
– Designing Clients and Servers, Designing Circuits and
Devices, Network Design Tools, Deliverables
• Cost Assessment
– Request for Proposal, Selling the Proposal to Management,
Deliverables
• Designing for Network Performance
– Managed Networks, Network Circuits, Network Devices,
Minimizing Network Traffic
4
Introduction
5
Traditional Network Design
• The traditional network design approach
follows a structured systems analysis
and design process similar to that used to
build application systems.
– The network analyst meets with users to determine
the needs and applications.
– The analyst estimates data traffic on each part of
the network.
– The analyst designs circuits needed to support this
traffic and obtains cost estimates.
– Finally, a year or two later, the network is
implemented.
6
Traditional Network Design
• Three forces are making the traditional
design approach less appropriate for many
of today’s networks:
– 1. The underlying technologies used in
computers, networking devices and network
circuits are rapidly changing.
– 2. Network traffic is growing rapidly.
– 3. The balance of costs has changed
dramatically over the last 10 years.
7
Building Block Network Design
(Figure 9-1)
• While some organizations still use the traditional
approach, many others use a simpler approach to
network design, the building block approach.
• This approach involves three phases: needs
analysis, technology design, and cost assessment.
• When the cost assessment is initially completed,
the design process returns to the needs analysis
phase and cycles through all three phases again,
refining the outcome of each phase.
• The process of cycling through all three design
phases is repeated until a final design is decided
on (Figure 9-2).
8
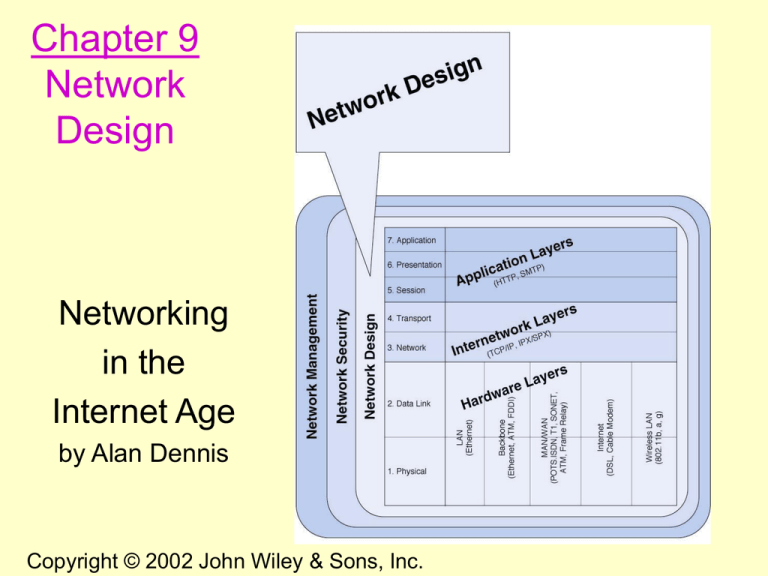
Figure 9-1 Network Design
9
Fig. 9-2 The cyclical nature of network design 10
Needs Analysis
11
Needs Analysis
• The first step is to analyze the needs of network users
along with the requirements of network applications.
• Most efforts today involve upgrades and not new network
designs, so most needs may already be understood.
• LAN and BN design issues include improving
performance, upgrading or replacing unreliable or aging
equipment, or standardizing network components to
simplify network management.
• At the MAN/WAN level, circuits are leased and upgrades
involve determining if capacity increases are needed.
• The object of needs analysis is to produce a logical
network design, which describes what network elements
will be needed to meet the organization’s needs.
12
Geographic Scope (Figure 9-3)
• Needs analysis begins by breaking the
network into three layers based on their
geographic and logical scope:
– The access layer which lies closest to the user
– The distribution layer which connects the
access layer to the rest of the network
– The core layer which connects the different
parts of the distribution layer together.
13
Figure 9-3 Geographic Scope
14
Application Systems
• The designers must review the applications
currently used on the network and identify
their location so they can be connected to
the planned network (baselining).
• Next, applications expected to be added to
the network are included.
• It is also helpful to identify the hardware
and software requirements and protocol
type for each application.
15
Network Users
• In the past, application systems accounted for the
majority of network traffic. Today, much network
traffic comes from Internet use (i.e., e-mail and
WWW).
• The number and type of users that will generate
network traffic may thus need to be reassessed.
• Future network upgrades will require
understanding how the use of new applications,
such as video, will effect network traffic.
16
Categorizing Network Needs
• The next step is to assess the traffic generated in
each segment, based on an estimate of the relative
magnitude of network needs (i.e. typical vs. high
volume). This can be problematic, but the goal is a
relative understanding of network needs.
• Once identified, network requirements should be
organized into mandatory requirements, desirable
requirements, and wish list requirements.
17
Deliverables
• The key deliverable for the needs
assessment stage is a set of network maps,
showing the applications and the circuits,
clients, and severs in the proposed network,
categorized as “typical” or “high volume”.
18
Figure 9-4 Sample needs assessment
19
Technology Design
20
Technology Design
• After needs assessment has been completed,
the next design phase is to develop a
technology design (or set of possible
designs) for the network.
21
Designing Clients and Servers
• In the building block approach, the technology
design is specified by using “standard” computer
units:
– “Typical” users are allocated “base level” client
computers, as are servers supporting “typical”
applications.
– “High volume” users and servers are assigned
“advanced” computers.
– The definition for a standard unit, however,
keeps changing as hardware costs continue to
fall.
22
Designing Circuits and Devices
• Two interrelated decisions in designing network
circuits and devices are: 1) deciding on the
fundamental technology and protocols and 2)
choosing the capacity each circuit will operate at.
• Capacity planning means estimating the size and
type of the “standard” and “advanced” network
circuits for each type of network.
• This requires some assessment of the current and
future circuit loading in terms of average vs. peak
circuit traffic.
23
Estimating Circuit Traffic
• The designer often starts with the total
characters transmitted per day per circuit, or
if possible, the maximum number of
characters transmitted per two second
interval if peak demand must be met.
• While no organization wants to overbuild its
network and pay for unneeded capacity,
going back and upgrading a network often
significantly increases costs.
24
Network Design Tools
• Network modeling and design tools can perform a
number of functions to help in the technology design
process.
• Some modeling tools require the user to create the
network map from scratch. Other tools can “discover”
the existing network.
• Once the map is complete, the next step is to add
information about the expected network traffic and see
if the network can support the level of traffic that is
expected. This may be accomplished through
simulation models.
• Once simulation is complete, the user can examine the
results to see the estimated response times and
throughput.
25
Deliverables
• The key deliverables at this point are a
revised set of network maps that
include general specifications for the
hardware and software required.
• In most cases the crucial issue is the
design of the network circuits.
26
Figure 9-5 Physical Network Design
27
Cost Assessment
28
Cost Assessment
• Cost assessment’s goal is to assess the costs of
various network alternatives produced as part of
technology design. Costs to consider include:
Circuit costs for both leased circuits and cabling.
Internetworking devices such as switches and routers.
Hardware costs including servers, memory, NICs & UPSs.
Software costs for operating systems, application software
and middleware.
Network management costs including special hardware,
software, and training.
Test and maintenance costs for monitoring equipment and
supporting onsite repairs.
Operations costs to run the network.
29
Request for Proposal (RFP)
• While some components can be purchased “offthe-shelf”, most organizations develop an RFP
before making large network purchases.
• The RFP creates a competitive environment for
providing network equipment and services (see
Figure 9-6).
• Once vendors have submitted network proposals,
the organization evaluates them against specific
criteria and selects the winner(s).
• Multi-vendor selections have the advantage of
maintaining alternative equipment and services
sources, but are also more difficult to manage.
30
Figure 9-6. Request for Proposal
• Background Information
– Organizational profile; Overview of current network; Overview of new
network; Goals of the new network
• Network Requirements
– Choice sets of possible network designs (hardware, software, circuits);
Mandatory, desirable, and wish list items, Security and control requirements;
Response time requirements; Guidelines for proposing new network designs
• Service Requirements
– Implementation time plan; Training courses and materials; Support services
(e.g., spare parts on site); Reliability and performance guarantees
• Bidding Process
– Time schedule for the bidding process; Ground rules; Bid evaluation criteria;
Availability of additional information
• Information Required from Vendor
– Vendor corporate profile; Experience with similar networks; Hardware and
software benchmarks; Reference list
31
Selling the Proposal to Management
• An important hurdle to clear in network design is
obtaining the support of senior management.
• Gaining acceptance from senior management lies
in speaking their language and presenting the
design in terms of easily understandable issues.
• Rather than focusing on technical issues such as
upgrading to gigabit Ethernet, it is better to make a
business case by focusing on organizational needs
and goals such as comparing the growth in
network use with the growth in the network
budget.
32
Deliverables
• There are three key deliverables for this step:
1. An RFP issued to potential vendors.
2. After the vendor has been selected, the revised
set of network maps including the final
technology design, complete with selected
components.
3. The business case written to support the
network design, expressed in terms of business
objectives.
33
Designing for Network
Performance
34
Network Management Software
• Network management software is designed
to provide automated support for some or
all of the network management functions
(Figure 9-8 shows an example).
• There are three fundamentally different
types of network management software:
– Device management software
– System management software
– Application management software
35
Figure 9-8 Network management software (Source: HP OpenView)
36
Network Management Software
• One major problem is ensuring that hardware
devices from different vendors can understand and
respond to the messages sent by the network
management software of other vendors.
• The two most commonly used network
management protocols are:
– Simple Network Management Protocol (SNMP, part of
the TCP/IP protocol suite)
– Common Management Interface Protocol (CMIP,
developed by ISO)
37
Simple Network Management Protocol
(See Figure 9-9)
• SNMP: TCP/IP suite protocol for network
management that allows agents to communicate
with each other and other network devices
• Agents: programs residing on network devices
that gather and share network status information
• Management Information Bases (MIBs):
databases of network status statistics such as
traffic levels, error rates & data rates
• Network Management Console: when requested,
data from the MIBs is sent to a Network
Management Console.
38
Fig. 9-9 Network management with SNMP
39
Policy-based Management
• In policy-based management, the network
manager uses special software to set priority
policies for network traffic.
• These take effect when the network
becomes busy.
• For example, videoconferencing might be
given a high priority since delays will have
the highest impact on the performance of
that application.
40
Traffic Analysis
• The easy way to manage network traffic growth is
simply to upgrade heavily used circuits.
• A more sophisticated approach is to do traffic
analysis. Consider the network in Figure 9-10:
– The Toronto-Dallas network segment is
heavily used (thick line), but the traffic is
mostly moving between LA and NY.
– The solution is to create a new LA to NY
segment (dashed line).
41
Figure 9-10 Simple WAN
42
Service Level Agreements
• More organizations establish service level
agreements (SLAs) with common carriers.
• SLAs specify the type of performance and
fault conditions for their leased circuits.
• For example, a 99.9% availability means
the circuit will be down for 8.76 hours/year.
• The SLA also often includes the maximum
allowable response time.
43
Network Devices
• Since network devices vary in their
characteristics, a network’s performance
will be influenced by the devices selected to
operate on it.
• Three important factors to network
performance that are related to network
device characteristics are:
– Device latency
– Device memory
– Load balancing
44
Device Latency
• Latency is the delay (waiting time) that occurs
when a device processes a message.
• Slow speed devices have high latency, while high
speed devices have low latency.
• The fastest devices run at wire speed.
• Latency becomes a critical issue under high traffic
conditions since high latency devices can create
traffic congestion.
• This is similar to the way that long lines of traffic
form at tollbooths on highways during rush hour.
45
Device Memory
• Memory and latency are related, since any device
that operates at less than wire speed may need to
store newly arrived packets.
• Otherwise packets will need to be retransmitted,
making the traffic situation worse.
• Memory is also important for servers since
memory access speeds are many times faster than
hard disk access times.
• The larger the memory a server has, the more
likely it is able to process a request quickly, so
Web and file servers should have the greatest
amount of memory practical.
46
Load Balancing
• Load balancing means sharing the
processing load between servers.
• A separate load balancing server is usually
needed to allocate the work between
processors.
• The load-balancing server then allocates
tasks to the other processors, using an
algorithm such as a round robin formula.
• An example of this is shown in Figure 9-11.
47
Figure 9-11 Network with load balancer
48
Minimizing Network Traffic
• An alternative way of improving network
performance is to minimize network traffic.
• This can be done by shifting some of the
data so it resides closer to the users (for
example, a mirrored web site).
• Two current approaches to minimize traffic
flow are content caching and content
delivery.
49
Content Caching (Figure 9-12)
• Content caching means storing frequently used
web pages locally, using a cache engine.
• Web requests do not go out directly, they are first
shunted by the router to the cache engine to see if
they are available locally.
• Traffic volume is lowered since many frequently
requested web sites, such as yahoo.com, can be
retrieved from the cache and don’t need to go out
on the Internet.
50
Figure 9-12 Network with cache engine
51
Content Delivery (see Figure 9-13)
• Another way to minimize network traffic is for
web site operators to move content closer to users,
called content delivery, is done by operating web
servers near NAPs, MAEs and other exchanges to
minimize network traffic.
• If a web page of one of the content deliverers
client’s is accessed, it checks if any web page
components are located on a server near the
requesting computer and sends those.
• This benefits both the Web provider by lessening
demand on its Web servers, the ISP by lowering
demand on its Internet circuits, as well as
decreasing Internet traffic overall.
52
Figure 9-13 Network with content delivery
53
End of Chapter 9
54