EC Technologies and the Internet
Steve McVey
Director of Web Commerce
Sterling Commerce, Inc.
steve_mcvey@stercomm.com
614-791-6408
Federation of Tax Administrators
March 18, 2016
1
EC Technologies and the Internet
• Web EDI
• XML
• Internet EDI
2
Web EDI
• Extend Trading Communities
• Low Cost of Entry
• Browser and Forms-Based
• Back-End is EDI or flat file
Traditional EDI (15%)
File transfers (25%)
Forms-based (60%)
3
Web EDI
Important Considerations:
• Security
• Audits and Controls
• Recovery
• Performance
4
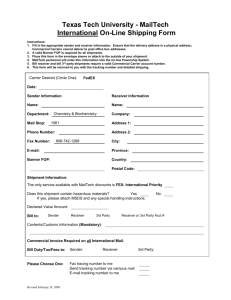
Web Forms Example
5
XML
• XML - eXtensible Markup Language
– A markup language for documents
containing structured information
– Contains both content and context
• Compelling Reasons for Use
– Relatively easy to implement
– Suitable for business process integration
and visual rendering
– Rapid acceptance by the market
6
XML
SGML
Standard Generalized
Markup Language
XML
eXtensible
Markup Language
HTML
HyperText Markup
Language
•Complex
•Powerful and extensible
•Used for formatting of complex technical documents
•Easy to use
•Extensible
•Separates content from presentation
•Used for web integration
•Easy to use
•Defines data presentation, not the content
•Does not facilitate application integration
•Used for presentation of simple information
7
XML
DTD
App
Systems
DTD
XML
Document
DTD
XSL
Browser
View
KEY
DTD - Document Type Definition
XSL - eXtensible Style Language
8
XML
XML and EDI
• Similar goals: inter-enterprise business process
integration
• EDI
– Well-established, mature
– Limited audience
– Highly structured
– Semantics agreed upon
• XML
– Emerging
– Easy to understand
– Largely unstructured
– Semantics under development
9
XML -- Sample XML Purchase Order
<order>
<order-no>654321</order-no>
<order-date>19980322</order-date>
<ship-to>
<DUNS=”5551122222">
<address>
<address:name>Dave Wilkinson</address:name>
<address:address1>123 W Main St
</address:address1>
<address:city>Columbus</address:city>
<address:state>OH</address:state>
</address>
</ship-to>
<bill-to>
<DUNS="8580828442">
<address>
<address:name>Sterling Commerce</address:name>
<address:address1>4600 Lakehurst Ct.
</address:address1>
<address:city>Columbus</address:city>
<address:state>OH</address:state>
<address:zipcode>43019</address:zipcode>
</address>
</bill-to>
<item>
<item:identifier>
<item:SKU>123456789</item:SKU>
<item:UPC>987654321</item:UPC>
<item:name>A Real Big Fast Computer</item:name>
</item:identifier>
<item:quantity>1</item:quantity>
<item:unit>EA</item:unit>
<item:price>3299.99</item:price>
</item>
</order>
10
XML -- Sample EDI Purchase Order
BEG*00*NE*654321**19980322~
N1*ST*DAVE WILKINSON*1*5551122222~
N3*123 W MAIN ST~
N4*DUBLIN*OH*43228~
N1*BT*STERLING COMMERCE*1*8580828442~
N3*4600 LAKEHURST CT~
N4*DUBLIN*OH*43019~
PO1**1*EA*3299.99**UP*987654321*VC*123456789~
PID***A REAL BIG FAST COMPUTER~
CTT*1~
11
XML
• XML Challenges
– Multiple implementations
• Vendor - Ariba (cXML), Commerce One (CBL)
• Industry - RosettaNet
• Enterprise
– Hybrid world
• Not everyone will adopt XML at the same pace
– Evolving technology
• More information:
– Sterling Commerce White Paper: “XML and Electronic
Commerce”
– www.xmledi.org
– www.xml.com
12
Internet EDI — EDIINT
• Electronic Data Interchange - Interoperability
(EDIINT)
• Working Group of the Internet Engineering Task
force (IETF) to provide for multi-vendor, interoperable exchange of business documents
among organizations over the Internet
• EDIINT AS1 - SMTP
– CommerceNet certified interoperability testing
– http://www.ietf.org/internet-drafts/draft-ietf-ediint-as1-09.txt
• EDIINT AS2 - HTTP
– Slated for completion in 10/99
– http://www.ietf.org/internet-drafts/draft-ietf-ediint-as2-04.txt
13
Background
• EDIINT Standard addresses:
– Privacy
– Authentication
– Integrity
– Non-Repudiation
• CommerceNet certified interoperability testing
– www.commerce.net
14
Internet EDI — EDIINT
Convergence of Standards
• UCC
– Using AS1 (SMTP)
– Pilot Project Complete October 1998
• Automotive/ANX
– Adopting AS2 (HTTP)
– Includes “E5” Standard
• Gas/Energy
– Adopting AS2 (HTTP)
– Includes GISB Standard
15
Security Overview
Symmetric Key Encryption
Key
Plaintext
Key
Encryption
Decryption
Plaintext
Ciphertext
SENDER
RECEIVER
16
Security Overview
Asymmetric Key Encryption
Plaintext
Public Key
Private Key
Encryption
Decryption
Plaintext
Ciphertext
SENDER
RECEIVER
17
Comparison of Encryption Techniques
Symmetric Keys
Public-Private Keys
• Advantages
• Advantages
– Fast
– Simple
• Disadvantages
– Multiple parties have keys
– Smaller key lengths
– Less vulnerable to
compromise
– Longer key lengths
• Disadvantages
– More difficult to manage
– Slower
18
Encryption Algorithms
Algorithm
Symmetric
(Secret)
Asymmetric
Key Length
RC2
RC4
RC5
40*, 64, 128
DES
56
Triple
DES
168
RSA
512*, 1024, 2048
(Public/Private)
*Defaults for EDIINT
19
Security Overview
SENDER
One-time
Symmetric Key
Plaintext
Create
Hash
Cyphertext
Encrypted
File
Sender’s
Private Key
Encryption
Encrypted
Digital
Signature
20
Security Overview
SENDER
One-time
Symmetric Key
Plaintext
Create
Hash
Digital Envelope
Cyphertext
Encrypted
File
Sender’s
Private Key
Receiver’s
Public Key
Encryption
Encrypted
Digital
Signature
Encrypted
One-time
key
21
Security Overview
SENDER
One-time
Symmetric Key
Plaintext
Create
Hash
Digital Envelope
Cyphertext
RECEIVER
One-time
Symmetric Key
Plaintext
Encrypted
File
Sender’s
Private Key
Receiver’s
Public Key
Encryption
Encrypted
Digital
Signature
Encrypted
One-time
key
Receiver’s
Private Key
Decryption
22
Security Overview
SENDER
One-time
Symmetric Key
Plaintext
Create
Hash
Digital Envelope
Cyphertext
RECEIVER
One-time
Symmetric Key
Plaintext
Encrypted
File
Sender’s
Private Key
Receiver’s
Public Key
Encrypted
Digital
Signature
Encrypted
One-time
key
Create
Rehash
Sender’s
Public Key
Sender’s
Hash
Receiver’s
Hash
Receiver’s
Private Key
Compare
Hash
Encryption
Decryption
23
Security Overview
SENDER
One-time
Symmetric Key
Plaintext
Create
Hash
Digital Envelope
Cyphertext
RECEIVER
One-time
Symmetric Key
Plaintext
Encrypted
File
Sender’s
Private Key
Compare
Hash
Receiver’s
Public Key
Encrypted
Digital
Signature
Encrypted
One-time
key
Signed Receipt
Encryption
(MDN)
Create
Rehash
Sender’s
Public Key
Sender’s
Hash
Receiver’s
Hash
Receiver’s
Private Key
Compare
Hash
Decryption
24
 0
0