RMON - World Colleges Information
advertisement
SNMP
Simple network management protocol
Group: Techno
Presented by:
Karthik Gottiparthy
Gautami Parulkar
Neeraj Sharma
Jigar Patel
Hariharan Venkataraman
1
Agenda
•
•
•
•
•
Introduction
Basic Concepts
MIB
RMON
SNMPv3
2
SNMP
• SNMP is a tool (protocol) that allows for remote and
local management of items on the network including
servers, workstations, routers, switches and other
managed devices.
• It operates over the UDP
UDP Port 161 - SNMP Message
UDP Port 162 - SNMP Trap Messages
3
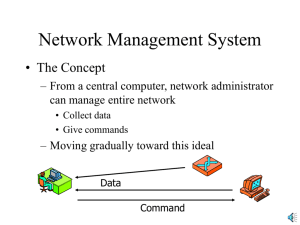
Basic Components
The network management contains four key elements
• Management station(NMS)
It is an interface by which the network manager may monitor
and control the network
• Management Agent
It responds to requests for information and actions from
management station( hosts, bridges, routers and hubs)
• Management information base
It functions as a collection of access points at the agent for the
management station
• Network Management protocol(SNMP)
The management station and agents are linked by this
4
5
SNMP Commands
• SNMP has 5 different functions referred to as Protocol Data Units (PDU’s), which
are:
• GetRequest(Get) - Retrieves the value of a MIB variable stored on the agent
machine(integer, string, or address of another MIB variable)
•
GetNextRequest(GetNext) - Retrieves the next value in MIB table
(continued till the end of the MIB table)
• GetResponse(Response) - Response from a SNMP agent to Get, GetNext and Set
commands
•
SetRequest(Set) - Changes the value of a MIB variable
•
Trap
- Asynchronous notification.
-SNMP agents can be programmed to send a trap
6
7
SNMP communities
•
An SNMP community is the group of agents and
management stations using SNMP protocol.
• A community name is used to identify a group.
• It will not respond to requests from management stations
that do not belong to one of its communities. SNMP
default communities are:
• Write = private
• Read = public
8
9
SNMP
• Management Information Base (MIB)
• Structure of Management Information.
• MIB Object Definition.
10
MIB(Management Information Base)
•Each resource to be managed is represented by an
object.Collections of these objects is MIB.
•Each object is a data variable that represents one aspect
of the managed agent.e.g.: these aspects may be the
TCP,IP,UDP connections done .
•MIB is a text file that describes the managed object
using syntax of ASN.1(Abstract Syntax Notation).
11
STRUCTURE OF MANAGEMENT
INFORMATION
• SMI generates a framework within which
a MIB can be defined and constructed.
• SMI identifies the data types used in MIB and
specifies how resources within the MIB can be
represented and named.
• Defines individual object including the syntax and
the value of the object.
12
STRUCTURE OF MANAGEMENT
INFORMATION
Data Types:
1.SIMPLE TYPES:
2.APPLICATION-WIDE TYPES:
• INTEGER
• OBJECT STRING
• OBJECT IDENTIFIER
•
•
•
•
•
•
Gauge
Counter
Time Ticks
IP Address
Opaque
Network Address
13
MIB Structure
• Each Type of object is associated with an
identifier called Object Identifier(OID).
• Identifier serves to name the object and also a
value is associated with the type of the object.
• An OID is represented by a sequence of integers
separated by decimal points.
• Set of defined objects has a Tree Structure.
14
MIB Object Group
iso(1)
org(3)
dod(6)
internet(1)
directory(1)
mgmt(2)
experimental(3)
private(4)
15
MIB Object Group Cond’t
system (1)
interface (2)
at (3)
mgmt (2)
mib-2(1)
ip (40)
icmp (50)
tcp (6)
udp (7)
egp (8)
transmission(10)
snmp(11)
16
Organization of Managed objects
Example: When a SNMP manager requests for the object, it
will send first an OID to the SNMP agent requesting the
information about the object.
The OID : 1.3.6.1.2.1.6.4
iso.org.dod.internet.mgmt.mib-2.tcp.tcpMaxConn
1 3 6
1
2
1
6
4
17
Example of an Object Definition
tcpMaxConn
OBJECT-TYPE
SYNTAX INTEGER
ACCESS read-only
STATUS mandatory
DESCRIPTION
“The limit on the total
number of TCP
connections the
entity can support.
In entities where the
tcp(mib-2 6)
maximum number of
connection is dynamic,
this object should
contain the value –1.”
::= {tcp 4}
tcpRtoAlgorithm(1)
tcpRtoMin(2)
tcpRtoMax(3)
tcpMaxConn(4)
18
Object Definition
• Object-Type:
- String that describes the MIB object.
• SYNTAX:
- Defines what kind of info is stored in the MIB object.
• ACCESS:
-read-only,read-write,write-only,not accessible.
• STATUS:
-state of the object in regards the SNMP .
i.e. mandatory,optional,obsolete,deprecated.
• DESCRIPTION:
- Reason why the MIB object exists.
19
SNMP-MIB Browser
20
SNMP – MIB Browser (3)
Navigation…
- MIB Tree
System
sysUpTime
-Notice Lower LHS
- Notice OID
21
SNMP – MIB Browser (4)
SNMP PDU’s…
(1) Get
- Select ‘Go’
‘Get’
- RHS has values.
- OID – Value
22
SNMP – MIB Browser (5)
SNMP PDU’s…
(2) GetNext
-Selected OID is:
.1.3.6.1.2.1.1.5
-Returned value:
(.1.3.6.1.2.1.1.6)
or
“DSG, O’Reilly Institute,
F.35”
23
SNMP – MIB Browser (6)
SNMP…
(3) Get SubTree
-Position of MIB:
.1.3.6.1.2.1.1
(a.k.a. system)
-RHS values:
Returns all values
below system.
24
SNMP – MIB Browser (7)
SNMP…
(4) Walk
-MIB Location:
.1.3.6.1.2.1
(a.k.a. mib-2)
- Returns *ALL* values
under mib-2
25
SNMP – MIB Browser (8)
Tables…
- MIB Location:
.1.3.6.1.2.1.2.2
(or interfaces)
- Select ifTable,
Go, then Table View.
- Refresh/Poll
26
SNMP – MIB Browser (9)
SNMP…
- Graph
-
Select a
value from
the RHS,
say
sysUpTime
-
Highlight
and select
‘Go’, then
‘Graph’.
-
Interval = 1s
set.
27
RMON – Remote Network Monitoring
What is RMON?
• specification of MIB
• provides vital information
• It defines a set of functions to support remote monitoring
Why RMON?
• problem with MIB II
•
purely local
How is RMON differs from MIB II?
•
Whole network
28
RMON Components
NMS
RMON
MIB
Ethernet
RMON
probe
29
RMON MIB Groups
• Statistics (1) – Ethernet stats
• History (2) – snapshots based on stats(1)
• Alarm (3) – ability to set threshold, generate
alarm on interesting event
• Host (4) – per i/f host stats
• HostTopN (5) – store/sort by top N hosts
• Matrix (6) – X talks to Y
• Filter (7) – filter pkts and capture/or cause event
• Capture (8) – traditional pkt analyzer
• Event (9) – table of events generated by probe
• TokenRing (10) – maintains statistics and
configuration information for token ring subnets
30
RMON version
RMON v1:
• Defines 10 MIB groups
• Physical and Data link (MAC layer) layers of the OSI
model.
RMON v2:
• An extension of RMON 1
• RMON2 has an emphasis on IP traffic and applicationlevel traffic.
• monitor packets on all network layers.
31
Central Management
Console with RMON
A
Ethernet
Router
Router
B
Local Management
Console with RMON
Router
Ethernet
Router
1
FDDI
backbone
Router
2
Router
PC with
RMON probe
Router with
RMON probe
Token ring
LAN
Ethernet
3
32
SNMP v1,v2
•SNMP is a simple request/response protocol. This behavior is
implemented by using one of four protocol operations: Get, GetNext,
Set, and Trap.
•SNMPv1 operates over protocols such as User Datagram Protocol
(UDP), Internet Protocol (IP), OSI Connectionless Network Service
(CLNS), AppleTalk Datagram-Delivery Protocol (DDP), and Novell
Internet Packet Exchange (IPX).
•SNMPv1 is widely used and is the de facto network-management
protocol in the Internet community.
•SNMP version 2 (SNMPv2) is an evolution of the initial version
Both versions contain lack of security.
33
SNMP v3
•The SNMPv3 architecture introduces the User-based Security
Model (USM) for message security and the View-based Access
Control Model (VACM) for access control.
•The architecture supports the concurrent use of different security,
access control and message processing models.
•The security features:
•Message integrity - Ensuring that a packet has not been
tampered with in-transit.
•Authentication - Determining the message is from a valid
source.
•Encryption - Scrambling the contents of a packet prevent it
34
from being seen by an unauthorized source.
SNMP v3
•SNMPv3 also introduces the ability to dynamically configure the SNMP
agent.
•This dynamic configuration support enables addition, deletion, and
modification of configuration entries either locally or remotely.
•SNMP lacks any authentication capabilities, which results in vulnerability
to a variety of security threats.
•It include masquerading occurrences, modification of information,
message sequence and timing modifications, and disclosure.
•SNMPv3 Applications
* Command Generators
* Command Responders
* Notification Originators
* Notification Receivers
* Proxy Forwarders.
35
?
36