IP address - DePaul University
advertisement
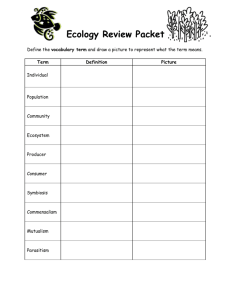
TDC 461 Basic Communications Systems Session 6 15 Mai 2001 • T1 Framing • Packet Switching – Packet Headers Agenda • The Internet – – – – Structure Applications IP Addresses The World Wide Web • Universal Resource Locators (URLs) • HTML – The Domain Name System (DNS) • Intranets – Applications – Security T1 Details • Bipolar Representation – T1 uses Bipolar Coding to represent 1 and 0 bits – ‘1’ bit represented by alternating +3 volt, -3 volt pulses – ‘0’ bits represented by no voltage • Framed Format Bipolar Representation Data +3V Voltage -3V 0 0 1 1 0 1 0 0 0 1 T1 Frame Format 1 bit 8 bits 8 bits 8 bits F DS0 #1 DS0 #2 DS0 #3 8 bits . . . DS0 #24 Each DS0 called a time slot 8000 frames/sec * 8 bits/slot = 64 Kbps 24 * 8 + 1 = 193 bits/frame 8000 frames/sec * 193 bits/frame = 1.544 Mbps 8000 Framing bits sent per second T1 Framing Bits • Framing Bits used for – Allow receiver to find the start-of-frame (frame synchronization). – Group sets of 12 frames into superframes – Indicate which frames contain signaling bits – Provide error checking (CRC) (ESF T1) – Provide Facilities Data Link channel to transmit network management messages (ESF T1) T1 Framing Bits (D4 Frame) • D4 Framing - Superframe T1 (1970) – F-bit pattern marks 12-frame superframes – F-bit pattern: 100011011100 • Odd frames: 101010 (Basic framing pattern) • Even frames: 001110 (marks 6th, 12th frames) – One Signaling Bit “robbed” in 6th & 12th frames for each Time Slot • Each signaling bit indicates whether that Time Slot is currently IDLE (1) or IN-USE (0) D4 Frame Format Frames 1-5, 7-11: 1 bit 8 bits 8 bits 8 bits F DS0 #1 DS0 #2 DS0 #3 8 bits . . . DS0 #24 Frames 6, 12: 1 bit F 7 bits 1 S DS0 #1 I G 7 bits 1 S DS0 #2 I G 7 bits 1 DS0 #3 S I G . . . 7 bits 1 DS0 #24 S I G T1 Framing Bits (ESF Frame) • D5 Framing - Extended Superframe T1 (1983) – F-bit pattern marks 24-frame extended superframes – F-bit pattern: • Odd frames: Facilities Data Link • Every 4th frame: 001011 (Framing pattern) • Every 4th frame: CRC for previous ESF ESF Frame Advantages • Facilities Data Link – • Cyclic Redundancy Check (CRC) – – Packet Data Services • • • • Customer pays – Packet Data Services Access Line Access Line Router New York Chicago Router Router Router Router Customer Network Router Carrier Network LAN Hub Client Customer Network LAN Hub Server Packet Switching • Concepts: – – – – Packetizing • Example: – I want to send a 50 Mbyte file – Max. packet length is 5000 bytes Packet Switch Operations • Packet switch (router) is a storeand-forward device • • • • Packet Switching = Statistical Time Division Multiplexing • A Packet Switch acts as a multiplexer, allowing multiple devices to share a single physical line. Packet Switching = Statistical Time Division Multiplexing Access Line: Shared by Multiple devices at Customer site Customer Packet Switch CSU Carrier Packet Switch Carrier Packet Switch Carrier Data Trunk: Shared by Multiple customers of this carrier network Packet Switching = Statistical Time Division Multiplexing • • Packet Switching and OSI • Packet switching functions performed by Network Layer (Layer 3) software • Layer 3 protocol determines: – max. packet length – packet header format – address format Example: X.25 • X.25 protocol: – Max packet length = 1024 bytes – Header format: • 4-bit General Format Identifier • 4-bit Logical Group Number • 8-bit Logical Channel Number • 8-bit Packet Type Identifier – Address: Logical Group/Channel Example: Internet Protocol • IP protocol: – Max packet length = 65,536 bytes – Header format: • 4-bit Version Number • 4-bit Header Type • 8-bit Service Type • 16-bit Length • 16-bit Identifier Example: Internet Protocol • IP protocol header format(cnt’d): • 16-bit Offset • 8-bit Time-to-Live • 8-bit Protocol • 16-bit Checksum • 32-bit Source Address • 32-bit Destination Address – Address: 4-byte IP address Packets inside Frames • Layer 3 packets can be carried inside any type of Layer 2 frame – Layer 3 protocol determines end-toend delivery – Layer 2 protocol just used on one physical transmission link Packets inside Frames • Example: IP packet carried inside Ethernet frame Ethernet Header IP Header Data Internet Protocol (IP) packet Ethernet Frame Ethernet Trailer Packets and Frames • Routers modify frame headers & trailers so packet can travel end-toend over many links T1 Token Ring IP packets / TR frames C.O. Router Router modifies frame CSU T1 CSU IP packets / PPP frames Router Router modifies frame Token Ring IP packets / TR frames X.25 Details • • • X.25 Details • Virtual Channel Communications – To send data, you must • • • X.25 Details • Cost of X.25 service – Carrier monthly charges based on: • • • X.25 Details • Network Error Control – Each Packet Switch in the network buffers customer data and handles ACKs and retransmission • • X.25 Details • Packet Assembler / Disassemblers (PADs) – – Terminal Terminal PC without X.25 Software Terminal Modem Modem Customer PAD PC with X.25 Software PAD CSU Dial-Up (POTS) Access Line Modem Carrier PAD Leased Access Line PAD Modem X.25 Switch LEC X.25 Network X.25 Switch LEC X.25 Network Mainframe CSU X.25 Switch Leased Access Line X.25 Switch X.25 Switch X.25 Switch National X.25 Backbone X.25 Switch IP Comparison to X.25 • • • PCs with LAN card and TCP/IP Software LAN PC without TCP/IP Software Customer Site IP Router IP Router Dial-Up (POTS) Access Line: Host Access Modem PC with TCP/IP Software and SLIP/PPP Software Dial-Up (POTS) Access Line: SLIP/PPP Access CSU Modem Modem Leased Access Line UNIX Host IP Router Regional ISP Network IP Router Modem Regional ISP Network IP Router IP Router IP Router IP Router National ISP Backbone IP Router What is the Internet? • A “Network of Networks” • Multiple networks of many types are all interconnected • The single common element: Internet Protocol (IP) – – The Key Players • End Users are businesses and individuals who wish to use the Internet • Internet Service Providers (ISPs) are carriers that maintain networks of IP routers to provide IP packet service – – • ISPs interconnect with each other at Metropolitan Area Exchanges (MAEs) PCs with LAN card and TCP/IP Software LAN PC without TCP/IP Software Customer Site IP Router IP Router Dial-Up (POTS) Access Line: Host Access Modem PC with TCP/IP Software and SLIP/PPP Software Dial-Up (POTS) Access Line: SLIP/PPP Access CSU Modem Modem Leased Access Line UNIX Host IP Router Regional ISP Network IP Router Modem Regional ISP Network IP Router IP Router IP Router IP Router National ISP Backbone IP Router Access to Internet • Access lines to ISP routers can be: – – – – • See http://www.thelist.com for list of ISPs and pricing information Who Makes Money? • End Users and Businesses • Regional ISPs pay National ISPs • ISPs pay telecommunications carriers Application Layer Protocols • Telnet – Allows remote login to another computer • File Transfer Protocol (FTP) – Transfers files between computers • Simple Mail Transport Protocol (SMTP) – Sends e-mail to another computer • Post Office Protocol (POP) – Downloads e-mail from e-mail server • Hypertext Transfer Protocol (HTTP) – Transfers files between Web servers and Web clients running browser software IP Addresses • Each IP address is 4 bytes long • Format: each byte written in decimal separated by dots - “dotted decimal” – – IP Addresses • How does every device on the Internet get a different IP address? • IP Address Prefixes assigned to organizations by the Internet Assigned Numbers Authority (IANA)--now Network Solutions – – • These organizations then control all IP addresses starting with that prefix IP Address Classes • Class A Address: – First byte value between 1 and 127 – IANA specifies value of 1st byte – Organization chooses IP address for each device by assigning value in last 3 bytes. – Organization has (256 * 256 * 256) = 16 million different IP addresses!! – Example: IP addresses 36.x.x.x are all controlled by Stanford University IP Address Classes • Class B Address: – First byte has value between 128 and 191 – IANA specifies value of 1st and 2nd bytes – Organization chooses IP address for each device by assigning value in last 2 bytes. – Organization has (256 * 256) = 65,536 different IP addresses!! – Example: IP addresses 140.192.x.x are all controlled by DePaul University IP Address Classes • Class C Address: – First byte has value between 192 and 223 – IANA specifies value of 1st, 2nd and 3rd bytes – Organization chooses particular IP address for each device by assigning value in last byte. – Organization gets 256 different IP addresses – Example: IP addresses 207.36.140.x are all controlled by Microsoft Corporation IP Address Classes A B C D E Range of host addresses 32 Bits Class 0 Network 10 Network 110 1110 11110 1.0.0.0 to 127.255.255.255 Host 128.0.0.0 to 191.255.255.255 Host Network Host 192.0.0.0 to 223.255.255.255 Multicast address 224.0.0.0 to 239.255.255.255 Reserved for future use 240.0.0.0 to 247.255.255.255 Other Ways to get IP Addresses • Small businesses and individuals usually don’t go through the IANA – – The Web • The World Wide Web is a collection of computers on the Internet that use – HTTP protocol to transfer files (web pages) – Hypertext Markup Language (HTML) to represent • Formatting information for display • Clickable Hyperlinks to go to other pages • Web browsers access HTML and other files from servers using HTTP • Web Servers store files and make them available to browsers Web Sites • To publish a Web Site, a user must – Find a Web server, that is • Connected to the Internet at all times (not dial-up access) • Running web server software • Has disk space that can be used for storing files. – Preferably, get good software to help in creating graphics and HTML pages. • Cost: – Many ISPs provide disk space and web page building tools to their clients for a small fee. URLs • Universal Resource Locator (URL) is the format used to specify a particular resource on the Web. <protocol>://<host>/<directory>/<file> • Protocol – HTTP:, TELNET:, FTP:, etc. • Host – Either DNS name or IP address of device on the Internet HTML • Hypertext Markup Language allows a text file to be augmented with tags that specify – Formatting information (font size, bold, italics, table formats, etc) – Locations to include image files (using GIF, JPEG or other graphics formats) – Hyperlinks (highlighted text and an associated URL to go to if clicked) – Associated executable applets (written in Java, Javascript, ??) Browser Operations <protocol>://<host>/<directory>/<file> • Given this URL, a browser will – – – – Domain Name System • The Internet utilizes a system of Domain Name System (DNS) servers. – brewster.cs.depaul.edu Host subdomain domain top-level domain Domain Name System • Top-Level Domains: – 2-letter top-level domains for each country - .fr for France, .de for Germany, etc. – .edu - Educational Institutions – .com - Commercial – .gov - Government – .mil - Military – .org - Organizations – .net - Network providers – .int - Internet organizations Domain Name System • Top-Level DNS Servers • Domain DNS Servers Domain Name System • Example: You type “http://www.ibm.com” in browser: – Your PC sends DNS request packet to DePaul DNS server – DePaul DNS server forwards packet to “.com” toplevel DNS server – Top-level DNS server forwards packet to “ibm.com” Domain DNS Server at IBM Corp. – IBM DNS server looks up IP address and sends result back to your PC at DePaul. Intranets • Intranets are internal business networks that use Internet Web technologies to improve business processes. • Employees use standard Web Browsers to accomplish many business applications Intranet Applications • Collaborative Software – Share and modify documents simultaneously – In-house video and audio conferencing • Information Sharing – Company Newsletters – Employee Handbooks – Help Desk • “Paperless Office” – All paper-based processes can be moved onto web-based forms on-line. Intranet Advantages • Increased Access to Information – Easy to look up answers on-line • Reduced Costs – Reduced management cost – Reduced cost of disseminating information – Increased productivity • Increased Flexbility • New Applications Intranet Disadvantages • Increased Network Usage and Costs – May be difficult to predict data traffic loads – New applications may increase overall management costs • Increased Security Risks – Risks from within organization – Risks from outside organization (if connected to the public Internet). Intranet Security • Firewalls – Filtering application gateways placed between internal networks and public Internet – Watches all data packets going in both directions • IP Address Translation – Can be used to hide internal IP addresses from outside world Corporate Network Dial-Up Communications Server FIREWALL External (Dirty) Network Router Packet Filtering Router The Internet (Untrusted) Public Web Server