Security and Privacy in Computer Forensics Applications
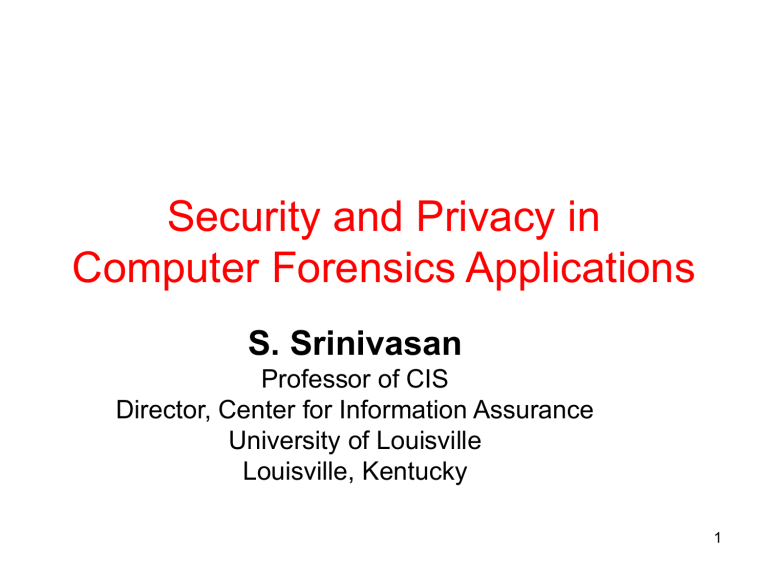
Security and Privacy in
Computer Forensics Applications
S. Srinivasan
Professor of CIS
Director, Center for Information Assurance
University of Louisville
Louisville, Kentucky
1
Outline
• Computer Forensics in academia
– History
– Emerging curricula
– Technology
– Collaboration
• Applications
• Security issues
• Privacy concerns
2
Computer Forensics
• Computer Forensics
– process involves:
• Collection
• Preservation
• Analysis
• Presentation of evidence from digital sources
• Historically a law enforcement responsibility
3
Computer Forensics
• 1984 – FBI forms the Computer Analysis and
Response Team (CART)
• 1993 - first international Computer Evidence conference held
• 1995 – International Organization for
Computer Evidence formed
• 1997 – G-8 Summit in Moscow calls for training law enforcement personnel for solving high tech crimes
4
Computer Forensics
• 2000 – first Regional Computer Forensics
Lab formed in Dallas
• 2006 – latest (14 th ) RCFL opened in
Louisville, KY
5
FBI’s Regional Computer
Forensics Labs (RCFLs)
Source: www.rcfl.gov
6
Computer Forensics in Academia
• Many programs housed in Criminal Justice departments
• Main focus on evidence preservation and presentation
• Analysis done by forensic examiners well versed in computing
• Over 100 CF programs exist today in US
7
Computer Forensics in Academia
• Important programs to review:
– Purdue University, West Lafayette, IN
– University of Tulsa, Tulsa, OK
– University of Central Florida, Orlando, FL
– Mississippi State Univ., Mississippi State, MS
– Champlain College, Burlington, VT
8
Emerging Curricula
• Typical courses in Computer Forensics program:
– Networking
– Operating Systems
– Data Communications
– Computer Evidence
– Criminal Law
– Basic Computer Forensics
– Advanced Computer Forensics
– Ethics
– Algebra and Statistics
9
Emerging Curricula
• Emphasis on both technology and policy
• Exposure to forensic tools
– EnCase
– FTK
• Significance of chain of evidence
10
Technology
• Understanding of
– storage technology
– operating system features
• Windows
• Linux
• Unix
• Mac OS
– file systems
11
Technology
• Knowledge of
– Slack space
– Host Protected Area (HPA)
– Device Configuration Overlay (DCO)
• Disk imaging
• Data recovery
• Total data deletion
• Handling encryption
12
Collaboration
• Computer Forensics investigation requires collaboration of
– Law enforcement
– Attorneys
– Computer specialists
• In academia, collaborating units could be:
– Computer Science
– Criminal Justice
– Law
– Accounting & Finance
13
Applications
– Lasts longer than people believe
– Businesses monitor employee emails
– Admissible in legal proceedings
– Protect using PGP
• E-commerce
– Exchange of confidential data
– Impersonation
14
Applications
• Data backup
– Encrypt
– Secure transfer of backup media
– Periodic recovery
15
Security Issues
• Data hiding
• Image hiding
• Improper destruction of sensitive data
• Weak authentication tools
– Created, Accessed, Modified date
– Boot password
– Password cracking
16
Privacy Concerns
• Computer Forensic investigation reveals:
– Passwords
– Encryption keys
– Images
• Scope of investigation
• Use of knowledge beyond goal of investigation
• Legal requirements
17
Privacy Protection
• Ten guidelines:
1. Remove personally identifiable data from storage media
2. Store an identical copy of any evidentiary media given to law enforcement
3. Limit search to goal of investigation
4. Handle time stamped events in strictest confidence
5. On networks, packet acknowledgement be via the use of tokens than IP addresses
18
Privacy Protection
6. Safe storage of all internal logs
7. Preservation of event logs in external nodes
8. Put policies in place for actionable items related to attacks
9. Put policies in place for safeguarding backed up data related to an investigation
10. Handle disposal of sensitive data in a secure manner
19
Summary
• Computer Forensics provides plenty of trace back capabilities
• Forensic investigators should get periodic training in ethical handling of data
• Policies should be in place to protect privacy of subjects in an investigation
20
References
• Computer Evidence: Collection and
Preservation by Christopher Brown, Thomson
Publishers, MA 2006, ISBN: 1-58450-405-6
• Guide to Computer Forensics and
Investigations , 2nd edition by Bill Nelson et al,
Thomson Publishers, MA 2006, ISBN: 0-619-
21706-5
• Computer Forensics – Hacking Exposed:
Secrets and Solutions by Chris Davis et al,
Osborne-McGraw Hill Publishers, NY 2005,
ISBN: 0-070225675-3
21
References
• File System Forensic Analysis by Brian
Carrier, Addison-Wesley, MA, 2005, ISBN:
0321268172
• Alec Yasinsac, Robert Earbacher, Donald
G. Marks, Mark Pollitt, Peter M. Sommer,
"Computer Forensics Education", IEEE
Computer Security and Privacy Magazine ,
July-Aug 2003, Vol. 1, No. 4, pp. 15-23
22
References
• EnCase http://www.guidancesoftware.com
• FTK http://www.accessdata.com
• FileHound http://www.filehound.org
• SATA http://www.serialata.org/
• Creating disk image http://darkdust.net/marc/diskimagehowto.php
• National Institute of Justice document on dd command http://www.ncjrs.gov/pdffiles1/nij/203095.pdf
23
References
• Computer Forensics programs http://www.e-evidence.info/education.html
• Brian Carrier http://dftt.sourceforge.net/
24
Thank you!
srini@louisville.edu
www.louisville.edu/infosec
25