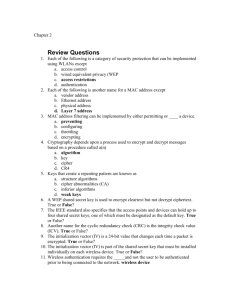
Wireless Security

COEN 350
Mobile Security
Wireless Security
Wireless offers additional challenges:
Physical media can easily be sniffed.
War Driving
Legal?
U.S. federal computer crime statute, Title 18 U.S.C. 1030,
Crime to knowingly access a computer used in interstate or foreign communication "without authorization" and obtain any information from the computer.
Crime to access a computer without authorization with
"intent to defraud" to obtain "anything of value."
But not if "the object of the fraud and the thing obtained consists only of the use of the computer and the value of such use is not more than $ 5,000 in any 1-year period."
Wireless Security
Wireless offers additional challenges:
Physical media can easily be sniffed.
Mobile computing needs to preserve battery power.
Calculations cost more on a mobile platform.
Especially important for sensor networks
Wireless Security:
Attackers Perspective
Knowing the Threat
Targets of opportunity
Goal is
Internet access.
Easy pickings.
Targeted attacks
Targets assets valuable enough.
Internal attackers
Most Dangerous
Can open an unintentional security hole
IEEE 802.11
Wired Equivalent Privacy (WEP)
Protocol
Based on a shared secret k .
Distributed out of band.
Uses CRC for internal integrity protection.
Uses RC4 to encrypt network traffic.
WEP Protocol
WEP Protocol
Confidentiality
Original packet is first check-summed.
Checksum and data form the payload.
Transmitting device creates a 24-bit random initialization vector IV.
IV and shared key are used to encrypt with
RC4
WEP Protocol
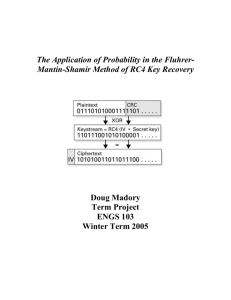
RC4
Generates a pseudo-random stream of bytes (keystream)
Based on a secret internal state
Permutation S of all 256 possible bytes
Two index pointers
Plaintext is XORed with keystream
WEP Protocol
RC4
Key Scheduling Algorithm (KSA)
Initializes S based on a key for i from 0 to 255
S[i] := i j := 0 for i from 0 to 255 j := (j + S[i] + key[i mod keylength]) mod 256 swap(S[i],S[j])
WEP Protocol
RC4
Pseudo-Random Generation Algorithm
(PRGA)
Generates pseudo-random byte stream i := 0 j := 0 while GeneratingOutput: i := (i + 1) mod 256 j := (j + S[i]) mod 256 swap(S[i],S[j]) output S[(S[i] + S[j]) mod 256]
WEP Protocol
RC4
Known weaknesses
Keystream slightly biased
Fluhrer & McGrew attack can distinguish keystream from random stream given a GB of input.
Fluhrer, Mantin, Shamir: statistics for output of the first few bytes of output keystream are non-random, leaking information about key.
WEP Protocol
Authentication
Station associating with access point needs to authenticate itself.
Both exchange the type of authentication that is accepted.
Open: Just identification between station and
AP
Shared Secret: Participants send nonces to each other, encrypt the nonce using WEP (and the shared secret key), and verify the other’s response.
WEP has no key management
Everyone allowed to have access to a wireless network has the same key.
Anyone with the key can read ALL traffic.
WEP: RC4
RC4 uses the key and the IV to produce a stream of pseudo-random bytes.
Calculates cipher text from plaintext by
XORing the pseudo-random stream with the plain-text.
WEP: RC4
WEP: Attacks on RC4
Dictionary Attack
Build database:
2 24 different IVs
Build a database of 2 24 streams of MTU bytes
(2,312 B) for each different IV.
Takes < 40 GB storage.
XOR two entries with the same IV.
Result are the two plaintexts XORed.
Natural language text has enough redundancy to decrypt the XOR of two text streams.
WEP: Attacks on RC4
Dictionary Attack
Many packages can be completely or partially guessed.
XORing guessed plaintext and captured cipher gives pseudo-random byte stream for a given IV.
Some implementations reset IVs poorly.
This simplifies dictionary attacks.
WEP: Attacks on RC4
Injection Attack
Attacker creates packets on the wireless connection.
Attacker XORs plaintext and cipher.
Builds Pseudo-Random Stream database indexed by IV.
RC4
Fluhrer, Mantin, Shamir Attack
First few bits of several thousand messages reveals key.
Based on an analysis of the RC4 code.
Originally kept secret, but later leaked on the internet.
RC4
Fluhrer, Mantin, Shamir Attack
Key Scheduling Algorithm
Sets up RC4 state array S
S is a permutation of 0, 1, … 255
Output generator uses S to create a pseudo-random sequence.
First byte of output is given by
S[S[1]+S[S[1]]].
First byte depends on
{S[1], S[S[1], S[S[1]+S[S[1]]}
RC4
Fluhrer, Mantin, Shamir Attack
Key Scheduling Algorithm
First byte of plain text package is part of the SNAP header
0xAA for IP and ARP packages
0xFF or 0xE0 for IPX
Guessing the first byte is trivial
Some IVs are vulnerable: “resolved”
(KeyByte+3, 0xFF, *)
Plus some more
Easy to test whether an IV is vulnerable.
Search for vulnerable IVs.
They leak key bytes probabilistically.
Large number of packets does it.
RC4
Fluhrer, Mantin, Shamir Attack
Optimization needs about 5,000,000 to
1,000,000 packages.
Counter-measures:
Change key frequently.
Change IV counters to avoid bad IVs.
WEP Message Modification
WEP uses CRC code to ascertain integrity of messages.
CRC code is linear:
CRC(x y) = CRC(x) CRC(y).
Attacker knows plaintext M and desired modification
for target plaintext M’ = M .
Attacker want to substitute X = P (M,CRC(M)) for
P (M’,CRC(M’)).
Attacker sends
X ( ,CRC( )) = P (M,CRC(M)) ( ,CRC( ))
= P (M’,CRC(M’))
Wireless Insecurity Problems
WiFi card software allows users to change the MAC address.
Wireless Security
Casual user, low yield traffic
WEP is good enough.
Enterprise, Commercial
Combine WEP with higher order security
SSH
VPN
IPSec
WPA
Created by WiFi Alliance
Certification started April 2003
Uses 802.1X authentication server
Distributed different keys to each user.
Can also be used in “pre-shared key” (PSK) mode
Every user uses the same passphrase.
Called WPA Personal
IEEE 802.1X
Standard for portbased authentication.
Uses a third-party authentication server such as Radius http://www.linux.com/howtos/8021X-HOWTO/index.shtml
WPA
Protocol changes over WEP
CRC is replaced by “Michael” MIC.
MIC now includes a frame counter, preventing replay attacks.
Payload bit flipping is now impossible.
Data encryption still uses RC4, but now
Prevents key recovery attacks on WEP by using
128b Key
48b Initialization vector
Temporal Key Integrity Protocol (TKIP) changes key dynamically.
TKIP
Temporal Key Integrity Protocol
Ensures that every data packet has its own encryption key.
802.11i
Uses AES instead of RC4.
Subset published as WPA2
Uses 802.1X authentication
Protocol Layers
WEP
Privacy only.
Very elementary security.
WPA
Temporal Key Exchange Protocol
Fixes WEP that scrambles keys between packages and adds a secure message check.
AES: Advanced Encryption Standard
802.11i
Military grade encryption, replaces DES
802.1X
General purpose and extensible framework for authentication users and generating / distributing keys.
Simple Secure Network (SSN)
Recipe for authentication based on 802.1X