Setting Up a Virtual Private Network
advertisement
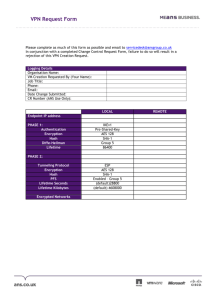
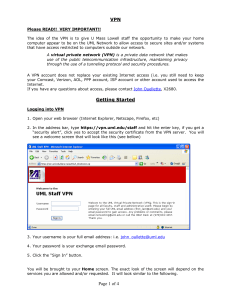
Chapter 11 Setting Up a Virtual Private Network Objectives After reading this chapter and completing the exercises, you will be able to: Explain the components and essential operations of virtual private networks (VPNs) Describe the different types of VPNs Create VPN setups, such as mesh or hub-and-spoke configurations Choose the right tunneling protocol for your VPN Enable secure remote access for individual users via a VPN Recommend best practices for effective configuration and maintenance of VPNs VPN Components and Operations 1. The goal of VPNs is to provide a cost-effective and secure way to connect businesses to one another and remote workers to office networks. If remote branch offices were to connect to one another using a LANbased file-sharing protocol, such as NetBIOS or AppleTalk, the results could be disastrous; the company’s sensitive personnel information, job data, and accounting department records could all become accessible to intruders who are able to either guess or obtain valid usernames and passwords. Because multinational corporations may well need to connect branch offices in various countries, VPNs provide an ideal means of communication. VPN Components 1. In terms of hardware, the following statements are true: A VPN can have two endpoints or terminators. Endpoints are hardware or software devices that perform encryption to secure data, authentication to make sure the host requesting the data is an approved user of the VPN, and encapsulation to protect the integrity of the information being sent. A VPN can have a tunnel. A tunnel is a secure channel used by the VPN and runs through the Internet from one endpoint to another. 2. The devices that form the endpoints of the VPN (these are often said to “terminate” the VPN) can be one of the following: Endpoints of VPN A server running a tunneling protocol A VPN appliance, which is a special hardware device devoted to setting up VPN communications A firewall/VPN combination; many high-end firewall programs support VPN setups as part of their built-in features A router-based VPN; routers that support IPSec can be set up at the perimeter of the LANs to be connected Essential Activities of VPNs 1. Because the VPN uses the Internet to transfer information from one computer or LAN to another, the data needs to be well protected. IP Encapsulation 1. VPNs protect packets by performing IP encapsulation, the process of enclosing a packet within another one that has a different IP source and destination information in order to provide a high degree of protection. 2. The benefit of encapsulating IP packets within other packets is that the source and destination information of the actual data packets (the ones being encapsulated) are completely hidden. The VPN encapsulates the actual data packets within packets that use the source and destination addresses of the VPN gateway. Data Payload Encryption 1. One of the big benefits of using VPNs is the fact that they encrypt the data portion of the packets that pass through them. They do not encrypt the header information within packets—only the data payload that the packets carry. The encryption can be performed in one of two ways: transport method and tunnel method. Encrypted Authentication 1. Two types of keys can be exchanged in an encrypted transaction: Symmetric keys: The keys are exactly the same. The two hosts exchange the same secret key to verify their identities to one another. Asymmetric keys: Each participant has a different secret key called a private key. The private key is used to generate a public key. The participants in the transaction exchange their public keys. Each can then use the other’s public key to encrypt information, such as the body of an e-mail message. When the recipient receives the encrypted message, he or she can decrypt it using the private key. Benefits and Drawbacks of VPNs 1. The advantages and disadvantages of VPNs are summarized in the following table: Advantages Less expensive than leased lines Disadvantages VPNs can still be expensive, especially if you use multiple VPN appliances Scalability and flexibility; allows many different computers to communicate over many different networks Uses the unregulated and often unreliable Internet All traffic that passes through the VPN is encrypted You can control how the VPN is configured Complexity VPN client software may not be compatible with all desktops; testing needs to be done, which can be time consuming VPNs Extend a Network's Boundaries 1. Each VPN connection extends your network to a new location that is out of your control, and each such connection can open up your network to intrusions, viruses, or other problems. You need to take extra care with users who connect to the VPN through always-on connections. Here are some suggestions for how to deal with the increased risk. Dealing with Increased Risk Use of two or more authentication tools to identify remote users Integrate virus protection Set usage limits Quick Quiz 1. A VPN can have two _____ or terminators. Answer: endpoints 2. When using the _____ method of data encryption, the host encrypts traffic when it is generated; the data part of packets is encrypted, but not the headers. Answer: transport 3. If your VPN's _____ is not configured properly, you can easily expose your corporate network. Answer: authorization 4. _____ authentication adds something the user possesses, such as a token or smart card, and something physically associated with the user, such as fingerprints or retinal scans. Answer: Multifactor Types of VPNs 1. In general, you can set up two different types of VPNs. The first type links two or more networks and is called a site-to-site VPN. The second type makes a network accessible to remote users who need dial-in access and is called a client-to-site VPN. The two types of VPNs are not mutually exclusive; many large corporations link the central office to one or more branch locations using site-to-site VPNs, and they also provide dial-in access to the central office by means of a client-to-site VPN. VPN Appliances 1. One way to set up a VPN is to use a hardware device such as a router that has been configured to use IPSec or another VPN protocol. Another option is to obtain a VPN appliance, a hardware device specially designed to terminate VPNs and join multiple LANs. VPN appliances can permit connections between large numbers of users or multiple networks, but they don’t provide other services such as file sharing and printing. 2. One VPN appliance that has a strong reputation is the SonicWALL series of VPN hardware devices. This series is comprised of nine different VPN products. 3. Another widely used VPN appliance is the Symantec Firewall/VPN appliance. Similar to the SonicWALL, the Symantec Firewall/VPN appliance is a series of different models. Each model is an integrated security VPN networking device that provides secure and cost-effective Internet connectivity between locations. Software VPN Systems 1. Software VPNs are generally less expensive than hardware systems, and they tend to scale better for fastgrowing networks. One of the popular software VPN products is F-Secure VPN+. This product supports traveling employees who need private access to a corporate LAN or intranet from any dial-up location, IT staff who need the ability to secure internal networks and partition parts of the network, and corporate partners who require secure connections to a company’s data network for business collaboration. F-Secure VPN+ supports Windows, Linux, and Solaris Sparc clients and servers as well as gateways. 2. Another widely used software VPN is Novell BorderManager VPN services. This software-based VPN supports both the TCP/IP protocol as well as IPX/SPX (another LAN protocol), which is found on older Novell networks. BorderManager can support up to 256 sites per tunnel and can handle up to 1,000 dial-in users per server. Novell BorderManager VPN clients run on Windows 95, 98, NT 4.0, 2000, Me, and XP. VPN Combinations of Hardware and Software 1. You may also use VPN systems that implement both VPN appliances and client software. The Cisco 3000 Series VPN Concentrator is another family of five different models of products. Supporting from 100 to over 10,000 simultaneous VPN users, the Cisco 3000 Series VPNs provide solutions for the smallest office or branch location to the largest enterprise setting. Access levels can be set either by the individual user or by groups, which allows for easy configuration and maintenance of company security policies. Combination VPNs 1. You may also be forced to operate a VPN system that is “mixed” not only in terms of using both hardware and software, but also by different vendors. You might have one company that issues certificates, another that handles the client software, another that handles the VPN termination, and so on. The challenge is to get all of these pieces to talk to one another and communicate with one another successfully. Quick Quiz 1. A VPN that links two or more networks is a(n) ____ VPN. Answer: site-to-site 2. A hardware device specially designed to terminate VPNs and join multiple LANs is known as a VPN _____. Answer: appliance 3. _____ VPN+ is a popular software package for VPN. Answer: F-Secure VPN Setups 1. If you have only two participants in a VPN, the configuration is relatively straightforward in terms of expense, technical difficulty, and the time involved. However, when three or more networks or individuals need to be connected, several options arise. Mesh Configuration 1. In a mesh configuration, each participant (that is, network, router, or computer) in the VPN has an approved relationship, called a security association (SA), with every other participant. In configuring the VPN, you need to specifically identify each of these participants to every other participant that uses the VPN. Before initiating a connection, each VPN hardware or software terminator checks its routing table or SA table to see if the other participant has an SA with it. Hub-and-Spoke Configuration 1. In a hub-and-spoke configuration, a single VPN router contains records of all SAs in the VPN. Any LANs or computers that want to participate in the VPN need only connect to the central server, not to any other machines in the VPN. This setup makes it easy to increase the size of the VPN as more branch offices or computers are added. 2. The problem with hub-and-spoke VPNs is that the requirement that all communications flow into and out of the central router slows down communications, especially if branch offices are located on different continents around the world. In addition, the central router must have double the bandwidth of other connections in the VPN because it must handle both inbound and outbound traffic at the same time. The high-bandwidth charge for such a router can easily amount to several thousand dollars per month. Hybrid Configuration 1. Any critical communications with branch offices that need to be especially fast should be part of the mesh configuration. However, far-flung offices such as overseas branches can be part of a hub-and-spoke configuration. A hybrid setup that combines the two configurations benefits from the strengths of each one—the scalability of the hub-and spoke option and the speed of the mesh option. Configurations and Extranet and Intranet Access 1. Each end of the VPN represents an extension of your corporate network to a new location; you are, in effect, creating an extranet. The same security measures you take to protect your own network should be applied to the endpoints of the VPN. Each remote user or business partner should have firewalls and anti-virus software enabled, for instance. Quick Quiz 1. In a mesh configuration, each participant (that is, network, router, or computer) in the VPN has an approved relationship, called a(n) _____, with every other participant. Answer: security association 2. A(n) _____VPN is ideally suited for communications within an organization that has a central main office and a number of branch offices. Answer: hub-and-spoke 3. VPNs can also be used to give parts of your own organization access to other areas through a corporate _____. Answer: intranet Tunneling Protocols Used with VPNs 1. In the past, firewalls that provided for the establishment of VPNs used proprietary protocols. Such firewalls would only be able to establish connections with remote LANs that used the same brand of firewall. Today, the widespread acceptance of the IPSec protocol with the Internet Key Exchange (IKE) system means that proprietary protocols are used far less often. IPSec/IKE 1. IPSec is a standard for secure encrypted communications developed by the Internet Engineering Task Force (IETF). IPSec provides two security methods: Authenticated Headers (AH) and Encapsulating Security Payload (ESP). AH is used to authenticate packets, whereas ESP encrypts the data portion of packets. 2. IPSec can work in two different modes: transport mode and tunnel mode. Transport mode is used to provide secure communications between hosts over any range of IP addresses. Tunnel mode is used to create secure links between two private networks. Tunnel mode is the obvious choice for VPNs; however, there are some concerns about using tunnel mode in a client-to-site VPN because the IPSec protocol by itself does not provide for user authentication. However, when combined with an authentication system like Kerberos, IPSec can authenticate users. 3. IPSec is commonly combined with IKE as a means of using public key cryptography to encrypt data between LANs or between a client and a LAN. IKE provides for the exchange of public and private keys. PPTP 1. Point-to-Point Tunneling Protocol (PPTP) is commonly used by remote users who need to connect to a network using a dial-in modem connection. PPTP uses Microsoft Point-to-Point Encryption (MPPE) to encrypt data that passes between the remote computer and the remote access server. L2TP 1. Layer 2 Tunneling Protocol (L2TP) is an extension of the protocol long used to establish dial-up connections on the Internet, Point-to-Point Protocol (PPP). L2TP uses IPSec rather than MPPE to encrypt data sent over PPP. PPP Over SSL/PPP Over SSH 1. Point-to-Point Protocol (PPP) over Secure Sockets Layer (SSL) and Point-to-Point Protocol (PPP) Over Secure Shell (SSH) are two UNIX-based methods for creating VPNs. Both combine an existing tunnel system (PPP) with a way of encrypting data in transport (SSL or SSH). 2. SSL is a public key encryption system used to provide secure communications over the World Wide Web. SSH is the UNIX secure shell, which was developed when serious security flaws were identified in Telnet. SSH enables users to perform secure authenticated logons and encrypted communications between a client and host. SSH requires that both client and host have a secret key in advance (a pre-shared key) in order to establish a connection. Quick Quiz 1. _____ is a standard for secure encrypted communications developed by the Internet Engineering Task Force (IETF). Answer: IPSec 2. ____ uses Microsoft Point-to-Point Encryption (MPPE) to encrypt data that passes between the remote computer and the remote access server. Answer: PPTP 3. ____ is an extension of the protocol long used to establish dial-up connections on the Internet, Point-toPoint Protocol (PPP). Answer: L2TP 4. _____ is a public key encryption system used to provide secure communications over the World Wide Web. Answer: SSL Enabling Remote Access Connections within VPNs 1. If users in disparate locations need to connect to the home office via a VPN, you need to set up a remote access connection. A VPN is a good way to secure communications with users who need to connect remotely by both dialing into their ISP and establishing a connection to the corporate network or by using their existing cable modem or DSL connection to the Internet to initiate the VPN connection to the corporate network. To enable a remote user to connect with a VPN, you need to issue that user VPN client software. You should also make sure the user’s computer is equipped with anti-virus software and a firewall. Configuring the Server 1. One step in setting up a client-to-server VPN is configuring the server to accept incoming connections. If you use a firewall-based VPN, you need to identify the client computer. Check Point FireWall-1, for instance, calls this process defining a network object. 2. The major operating systems include their own ways of providing secure remote access. In Linux, you use the IP Masquerade feature built into the Linux kernel to share a remote access connection. A part of IP Masquerade, called VPN Masquerade, enables remote users to connect to the Linux-based firewall using either PPTP or IPSec. 3. Windows XP and 2000 include a Network Connections Wizard that makes it particularly easy to set up a workstation to accept incoming VPN connections, with one limitation: the Remote Access Server that is used to provide the connection has the ability to permit only one incoming connection at a time. Configuring Clients 1. After you set up the server, you then need to configure each client that wants to use the VPN. This either involves installing and configuring VPN client software or, in the case of a Windows-to-Windows network, using the Network Connection Wizard. FireWall-1 uses client software called SecuRemote that, when installed on a client computer, enables connections to another host or network via a VPN. VPN Best Practices 1. The successful operation of a VPN depends not only on its hardware and software components and overall configuration, but also on a number of other best practices. These include security policy rules that specifically apply to the VPN, the integration of firewall packet filtering with VPN traffic, and auditing the VPN to make sure it is performing acceptably. The Need for a VPN Policy 1. In a corporate setting, the VPN is likely to be used by many different workers in many different locations. A VPN policy is essential for identifying who can use the VPN and for ensuring that all users know what constitutes proper use of the VPN. This can be a separate stand-alone policy, or it may be a clause within a larger security policy. Packet Filtering and VPNs 1. When configuring a VPN, you must decide early on where encryption and decryption of data will be performed in relation to packet filtering. You can either decide to do encryption and decryption outside the packet-filtering perimeter or inside it. Auditing and Testing the VPN 1. After the VPN is installed, you need to test the VPN client on each computer that might use the VPN. In an organization with many different workstations, this can be a time-consuming prospect. There is no easy way around this, but you can choose client software (which is installed as part of the test) that is easy for end users to install on their own to save you time and effort. 2. To give you an idea of how testing of a VPN client might work, consider the following step-by-step scenario: You issue VPN client software and a certificate to the remote user. You call the remote user on the phone and lead him or her through the process of installing the software and storing the certificate. If you are using IPSec, you verify with the remote user that the IPSec policies are the same on both the remote user’s machine and on your VPN gateway. You tell the user to start up the VPN software and connect to your gateway. (Hopefully, you’ll be able to remain on the phone while the end user connects, but, if the remote user has only one telephone line and a dial-up connection to the Internet, you may have to communicate by e-mail.) If there are any problems connecting to the gateway, tell the remote user to write down or report the error message exactly to help you correctly diagnose the problem. After the connection is established, the remote user should authenticate by entering his or her username and password when prompted to do so. Quick Quiz 1. Having two connections on the same line is known as _____. Answer: split tunneling 2. What is the type of encryption that is used when packets are encrypted at the host as soon as they are generated? Answer: Transport 3. Incoming PPTP connections arrive on TCP port ____. Answer: 1723 4. One step in setting up a client-to-server VPN is configuring the _____ to accept incoming connections. Answer: server 5. In Linux, you use the IP _____ feature built into the Linux kernel to share a remote access connection. Answer: Masquerade Class Discussion Topics 1. Discuss the benefits and risks of using VPN. 2. Discuss the considerations that affect the choice of using hardware or software to provide a VPN. 3. Discuss the elements of a VPN policy and how it fits into an overall security policy. Additional Case Projects 1. You have been asked to write up a guide to be used when testing new client installations. What steps would you include in this guide? How would you handle different client hardware and software configurations? 2. You have been asked to set up a VPN for a medium-size company that wishes to have office workers telecommute. The company asks for recommendations regarding using hardware or software to support the VPN, what type of configuration is required, and what the requirements of client machines should be. Make some recommendations and explain why you chose those options. 3. You are writing a VPN policy for a large company with offices overseas. What elements will you include in the policy? Further Readings or Resources There’s a Web site devoted solely to the subject of finding VPN hardware and software and providing reviews of different products. Visit Find VPN at http://findvpn.com/providers/vpnware.cfm. SANS provides a sample VPN Policy in PDF format at www.sans.org/newlook/resources/policies/Virtual_Private_Network.pdf.