ViPNet EDI
drive your collaboration secure
What is ViPNet EDI?
Electronic data interchange (EDI) systems are used for
standardized electronic data exchange. They include exchange
standards, electronic facilities for users and providers, data
transmission media, etc.
Legally significant EDI
Legally significant electronic docflow provides
electronic documents as effective in court as paper
documents. This generally implies the following:
■■
■■
■■
The document must have an electronic signature
of the sender, which can then be verified by the
receiver. In ViPNet EDI, the sending party signs
documents with private key, which corresponds to
its public key certificate.
Parties must be notified about the delivery stages
of each document. In ViPNet EDI, the parties and
the system’s automatic components exchange
notifications and are always aware of documents’
delivery state. For example, the sender is notified
about the receiver having accepted the data.
After the exchange, documents and their
notifications are stored in a safe depository of an
independent third party. This party can provide
the data as evidence in investigations.
ViPNet EDI is a flexible system for secure, convenient,
and legally binding data / document exchange
between parties, which can be commercial companies,
official authorities, or any other organizations.
2
ViPNet EDI is a flexible system for secure,
convenient, and legally binding data / document exchange between parties, which can
be commercial companies, official authorities,
or any other organizations.
Endpoints
Parties send and receive data with their endpoint
client software. The parties at the endpoints may
be persons, companies, automatic data processing
systems (applications or appliances), depending on
your business needs.
Transport media
With ViPNet EDI, the data is safely transferred
between endpoints over public or trusted channels
(a dedicated physical channel or a VPN). In public
channels, the data is protected with asymmetric
encryption.
Components
ViPNet EDI system provides endpoint and transport
components for EDI solutions:
■■
■■
Ready-to-use and custom ViPNet EDI endpoint
software.
ViPNet EDI data transport channel infrastructure.
If you already have pre-existing endpoint software
for data exchange or transportation channels of other
vendors, ViPNet EDI components can be integrated
with them.
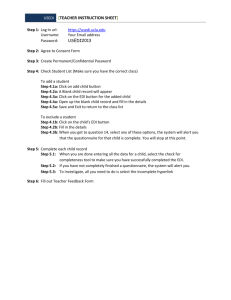
How it works?
Endpoint: Flexible architecture
DATA
Sender’s endpoint
integration with data
processing applications,
web portals
use a trusted
dedicated channel
API
company:
■■ persons
■■ applications
■■ appliances
PARTIES
Receiver’s
endpoint
your trusted channel
EDI
client
EDI
client
CHOOSE THE
TRANSPORTATION MEDIA
use the Internet, outsource delivery to a
trusted third party
PROCESSING RULES
■■ sender signature verification
■■ document structure verification: documents
that you are sending are in correct format
re
trusted a
a
public are
Internet
a
Service provider: trusted third party
EDI customers can outsource secure and prompt data
transmission to a specialized provider.
WHY CUSTOMERS OUTSOURCE
■■ They save on maintenance of the docflow infrastructure.
■■ They are not worried about your provider reading your data;
it is inaccessible to anyone but you.
■■ The provider is not bound with either of the parties, is therefore
independent and legislatively capable of providing evidence in
investigations and trials.
DATA PROTECTION IN PUBLIC CHANNELS
■■ encrypted at the application layer with
your asymmetric key
■■ inaccessible to any other parties
(including the EDI provider)
EDI
server
Encrypted backup
DATA STORAGE
Encrypted backups of transmitted data can be
stored in a safe depository. They cannot be
decrypted by any malicious parties trying to
access customers’ data in the storage.
Transmission proof data any time past (e.g.
delivery time) can also be stored and extracted
from the EDI provider, whenever its customers
need to prove the delivery.
ViPNet EDI
3
Why ViPNet EDI?
ViPNet EDI has unique features that make your data exchange genuinely safe and convenient.
The variety of implementation options allows you to select the most suitable and cost-saving
solution for your business.
Document exchange
is truly confidential
Choosing
the transmission media
Strong cryptography
Option 1: Internet + EDI provider
The data that users exchange can be encrypted
with asymmetric keys. An asymmetrically encrypted
document can be decrypted only by the receiver.
In other words, the sender encrypts a document
individually for the receiver. This encrypted document
is inaccessible to any other parties, including the EDI
provider.
Digital certificates
Each document is signed with a private key, which
corresponds to its public key certificate.
The encryption makes it safe to exchange data
over the Internet, so EDI customers can save on
maintaining a secure dedicated network.
This also means that customers can safely outsource
data delivery to a third party, their EDI provider:
with asymmetric key encryption, they can be
confident that even their provider will not access
their data. Outsourcing the delivery, they save on
maintaining the delivery infrastructure.
Option 2: Trusted channel
If customers trust a delivery channel (e.g. they are
using a dedicated channel that they control), they
may exchange without encryption and maintain
the infrastructure themselves. This is especially
useful when they already have a trusted channel (a
dedicated physical channel or a VPN); this allows them
to save on computational resources for processing
the encrypted data at the endpoints.
If customers don’t have a dedicated physical channel
or a VPN, but they need one, we can help them to
deploy it from scratch.
Option 3: Fuse the two
If customers face the challenge of extreme
data security requirements, they can exchange
asymmetrically encrypted data over a trusted
channel.
4
Optional cloud storage
and safe depository
Web and on-premise
endpoint clients
Local document storage at the endpoints is
vulnerable to occasional loss of data due to disk
corruption.However, you can safely store your
transmission data in the cloud, as long as it is
encrypted and inaccessible even to the cloud storage
provider. ViPNet EDI allows you to store your data in
the cloud.
The cloud storage allows for the usage of web
endpoint clients for web access. With a web client,
users have access to their accounts and sent /
received documents from any location, directly from
their mobile devices or from available desktops with
Internet access.
It is useful to store the data and the notifications that
travel along the communication channel. The delivery
data can be extracted from the storage and used as
evidence for auditing, dispute resolutions or any other
kind of investigations. ViPNet EDI provides means
for storing your data in a safe depository. You can
access transmission data from any time in the past
and verify the legal status of the transmission as of its
actual date.
However, if your users frequently go offline, let them
have local copies of their transmission data on their
desktops with on-premise endpoint clients. This
won’t prevent them from using web client access; they
will work with the same set of documents with both
web and on-premise clients.
Both the cloud storage and the safe depository can
be owned by the EDI provider.
ViPNet EDI
5
Document exchange
formalization
Intense docflow is complicated by the need for
manual processing (sending, verifying, receiving etc.)
When you have many similar documents, you can
formalize them and enjoy the benefits:
■■
■■
■■
■■
Formalized documents are easier to fill. You don’t
think of wording, but select from the available set
of variants. Moreover, you can implement a data
consistency check of filled forms. For example, in
the personal data form, the system may be tuned
to verify whether a person’s age suggests having
a passport and may then check that the passport
data has been entered.
Formalized documents are easier to read. When
you get used to a certain form, you just scan
through it and find the data you need.
It is much easier to perform data search and
filtering in formalized documents, as long as all the
data is in a similar format.
A formalized document exchange allows for
automatization, saving your staff’s time. For
example, a formalized item requirement will be
machine-readable even when filled by a person.
ViPNet EDI system provides special means for
formalizing a company’s docflow of any complexity.
This is simple and does not require any experience in
coding. A customer can start exchanging formalized
documents as soon as they are prepared.
6
Flexible endpoint
interface for human
and machine access
The ViPNet EDI system has implemented client
interfaces for users to create, send, and receive
documents.
For integration with automatic systems (e.g. CRM
systems), we have developed API. Among other
things, this allows you to integrate the ViPNet EDI
system into an existing dataflow infrastructure for
protecting communication channels. For example,
if your IT components communicate over media
that has been threatened or compromised, you can
implement ViPNet EDI to encrypt the communications
and establish logging.
We can also implement an endpoint client specially
customized for your business.
How do we make it
Take a look at the variety of dataflow topologies,
which you can implement with ViPNet EDI (see below).
EDI dataflow topologies
The ViPNet EDI system supports various models of dataflow direction between endpoints.
For the models given below, we have developed solutions that implement the unique ViPNet
EDI features.
Mesh
(social networklike topology)
Many business cases require
point-to-point communication
in a mesh. For example,
commercial companies interact
with each other just like
users of social networks: they
need to be free to make new
connections.
IMPLEMENTATION CASE
Commercial docflow (EDI B2B, box product)
CHALLENGE
Secure and legally significant EDI for commercial entities.
REQUIREMENTS
Delivery
■■ Data transportation outsourced to a trusted service provider.
■■ Internet used for data exchange.
Other
■■ Endpoint compatibility with various CRM systems.
■■ Legislative requirements for the EDI met (document format, parties’ and
controlling entities’ notification upon document delivery).
■■ Easy setup and usage (basic-level user qualification).
SOLUTION
■■ Fully packaged, can be purchased and launched in a company as is.
■■ Asymmetrically encrypted EDI.
■■ Components:
■■ The service customer’s client. Web client supported.
■■ Routing / processing server with cloud document storage.
■■ Formalized documents exchange supported.
IMPLEMENTATION PREREQUISITES
■■ Internet access.
CASES
The solution is implemented in small and large companies, including
banks and governmental entities. Has substantially reduced the cost of
docflow.
■■ A large company has integrated ViPNet EDI into a pre-existing CRM
system. Users sense no change in the interface and have no need to
learn new techniques, but their docflow is now protected.
■■
ViPNet EDI
7
Hub-spokes
topology
Some interactions are based
on endpoints submitting data
to a hub, a data collector.
For example, commercial
companies submit their
accounts and reports to tax
collectors.
IMPLEMENTATION CASE
Electronic filing (EDI B2G)
CHALLENGE
Secure reports submission to controlling government agencies.
REQUIREMENTS
Delivery
■■ Data transportation outsourced to a trusted service provider.
■■ Internet used for data exchange.
Other
■■ Compatibility with pre-existing electronic report receiving interfaces at
control agencies (adherence to required inbound document format).
■■ Legislative requirements for the EDI met (document format, parties’
notification upon document delivery).
■■ Easy setup and usage (basic-level user qualification).
HUB
SOLUTION
■■ Asymmetrically encrypted EDI.
■■ Components:
■■ Data submitter’s client.
■■ Routing / processing server with cloud document storage.
■■ Each report status traced.
IMPLEMENTATION PREREQUISITES
Internet access.
■■ Routing / processing server customized for interaction with report
receiving interfaces*.
■■
* For control agencies that do not
have report receiving interfaces
implemented, we can develop
custom interfaces.
8
CASES
■■ Several government control agencies have switched from paperwork to
collecting reports from commercial companies with ViPNet EDI. Now,
the docflow is prompt and safe.
■■ Some providers specialize on submitting reports for other companies.
With ViPNet EDI, they make it a successful business.
Pass gate
topology
When a pool of technical
requests is processed by
several specialists, they need
to know which requests are
not being processed yet.
They don’t want to take on a
request that is already being
processed by another person.
?
?
?
?
OK
CHALLENGE
Distributing requests for public services (e.g. issuing passports) among
executives.
REQUIREMENTS
Delivery
■■ Data delivery provided by the owner (a pre-existing dedicated channel).
Other
■■ Compatibility with pre-existing dedicated data delivery channels.
■■ Easy setup and usage (basic-level user qualification).
?
?
OK
OK
OK
IMPLEMENTATION CASE
Collaboration for requests processing (EDI G2G)
OK
SOLUTION
Components:
■■ Executive’s client.
■■ Routing / processing server with data storage.
■■ Formalized requests processing supported.
■■ Each request status traced.
■■
IMPLEMENTATION PREREQUISITES
■■ Dedicated channel.
■■ Routing / processing server customized as a gateway to the dedicated
channel.
CASES
■■ Several governmental departments, dozens of banks, and hundreds of
local governments use the solution for request processing without data
loss or delay.
ViPNet EDI
9
Notes
10
© 1991–2014 Infotecs. All rights reserved.
No part of this publication may be reproduced, published, stored in an electronic database, or transmitted, in
any form or by any means — electronic, mechanical, recording, or otherwise — for any purpose, without the
prior written consent of Infotecs.
ViPNet is a registered trademark of Infotecs.
All brands and product names that are trademarks or registered trademarks are the property of their owners.
ViPNet EDI
11
00083-01 101 01 ENU
Infotecs Americas Inc.,
41 Madison Avenue,
New York, NY, 10010
Tel:
+1 (646) 589-8571 (sales)
+1 (646) 589-8570 (support)
Email: support@infotecs.us
Web: http://www.infotecs.us