Configuring the Cisco VPN 3000 Concentrator to the PIX Firewall

Configuring the Cisco VPN 3000
Concentrator to the PIX Firewall
Introduction
The goal of this sample configuration is to connect a private network behind a Cisco PIX
Firewall to a private network behind the Cisco VPN 3000 Concentrator. The devices on the networks know each other by their private addresses.
Hardware and Software Versions
This configuration was developed and tested using the software and hardware versions below.
PIX Software 5.1.2
VPN 3000 Concentrator with 2.5.2.F
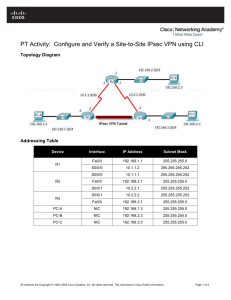
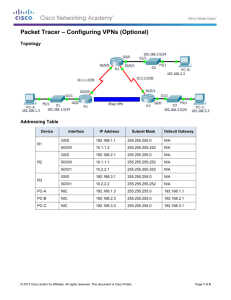
Network Diagram
Configurations
PIX Firewall Configuration
PIX Version 5.1(2) nameif ethernet0 outside security0 nameif ethernet1 inside security100 enable password 8Ry2YjIyt7RRXU24 encrypted passwd 2KFQnbNIdI.2KYOU encrypted hostname pix515b fixup protocol ftp 21 fixup protocol http 80 fixup protocol h323 1720 fixup protocol rsh 514
fixup protocol smtp 25 fixup protocol sqlnet 1521 names access-list 101 permit ip 10.13.1.0 255.255.255.0
10.31.1.0 255.255.255.0 pager lines 24 logging on no logging timestamp no logging standby logging console debugging no logging monitor no logging buffered logging trap debugging no logging history logging facility 20 logging queue 512 logging host outside 172.18.124.99 interface ethernet0 auto interface ethernet1 auto mtu outside 1500 mtu inside 1500 ip address outside 172.18.124.157 255.255.255.0 ip address inside 10.13.1.48 255.255.255.0
no failover failover timeout 0:00:00 failover ip address outside 0.0.0.0 failover ip address inside 0.0.0.0 arp timeout 14400 global (outside) 1 172.18.124.156 nat (inside) 0 access-list 101 nat (inside) 1 10.13.1.0 0.0.0.0 0 0 conduit permit icmp any any route outside 0.0.0.0 0.0.0.0 172.18.124.132 1 timeout xlate 3:00:00 conn 1:00:00 half-closed
0:10:00 udp 0:02:00 timeout rpc 0:10:00 h323 0:05:00 timeout uauth 0:05:00 absolute aaa-server TACACS+ protocol tacacs+ aaa-server RADIUS protocol radius no snmp-server location no snmp-server contact snmp-server community public no snmp-server enable traps floodguard enable sysopt connection permit-ipsec crypto ipsec transform-set myset esp-des esp-md5hmac crypto map newmap 10 ipsec-isakmp crypto map newmap 10 match address 101 crypto map newmap 10 set peer 172.18.124.132 crypto map newmap 10 set transform-set myset crypto map newmap interface outside isakmp enable outside isakmp key cisco address 172.18.124.132 netmask
255.255.255.255 isakmp identity address
isakmp policy 10 authentication pre-share isakmp policy 10 encryption des isakmp policy 10 hash md5 isakmp policy 10 group 1 isakmp policy 10 lifetime 28800 telnet timeout 5 terminal width 80
Cryptochecksum:fe99619c07301293d6dc9e5a8404cc55
: end
VPN Concentrator Configuration
As this was a lab setting, we first accessed the VPN Concentrator through the console port and added a minimal configuration so that the further configuration could be done through the graphical user interface (GUI). To assume no configuration in the concentrator, we went through:
Administration > System Reboot > Schedule reboot > Reboot with Factory/Default
Configuration
After rebooting, the VPN Concentrator came up in Quick Configuration, and the following items were configured:
Time/Date
Interfaces/Masks in Configuration > Interfaces (public=172.18.124.132/24, private=10.31.1.80/24)
Default Gateway in Configuration > System > IP routing > Default_Gateway
> 172.18.124.157
At this point, the VPN Concentrator was accessible through html from the inside network.
Note: Because we were managing our Concentrator from outside , we also had to go into:
Configuration > Interfaces > 2-public > Select IP Filter > 1. Private (Default)
Administration > Access Rights > Access Control List > Add Manager
Workstation to add the IP address of the external manager.
This is not necessary unless you are managing the the VPN Concentrator from outside .
After bringing up the GUI, we rechecked the interfaces at Configuration > Interfaces :
Then we went to Configuration > System > Tunneling Protocols > IPSec LAN-to-
LAN > Modify to configure the IPSec LAN-to-LAN tunnel:
We went to Configuration > System > Tunneling Protocols > IPSec > IKE Proposals to configure the IKE Proposals :
We checked the Security Associations settings by going to Configuration > Policy
Management > Traffic Management > Security Associations > Modify :
At this point, there should be connectivity between devices on either side of the VPN
Concentrator and the PIX. debug
and
show
Commands
On the PIX
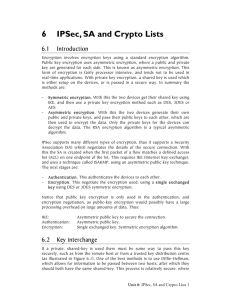
debug crypto engine - Shows the traffic that is encrypted.
debug crypto ipsec - To see the IPSec negotiations of phase 2.
debug crypto isakmp - To see the ISAKMP negotiations of phase 1.
Before attempting any of the above debug commands, please see Important Information on Debug Commands .
On the VPN Concentrator
The following debug options are individually available if you go to Configuration >
System > Events > Classes > Add (shown below):
IKE
IKEDBG
IKEDECODE
IPSEC
IPSECDBG
IPSECDECODE
The actual debug can be seen by by going to Monitoring > Event Log and clicking Get
Log :
IPSec status can be seen by going to Monitoring > Statistics > IPSec :