DOC - SCONCE
advertisement

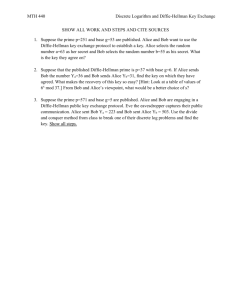
ICS 134 – Spring 2011: Homework 2 Name: Q1 Student ID: Q2 /20 Q3 /20 Q4 /20 Q5 /20 TOTAL /20 /100 Due: Wednesday, May 18, 2011 @noon Turning it in: Email your homework as a single-file PDF attachment to edecrist@uci.edu. Use subject line: “ICS134 HW2”. Warning: Homework submissions not following above guidelines will not be graded. 1 Problem 1: Recall the man-in-the-middle (MiTM) attack discussed in class. Suppose that Alice and Bob, instead of using plain Diffie-Hellman, run the following key agreement protocol: 1. 2. 3. Alice Bob: Alice, PKAlice Bob generates random value y Bob Alice: Bob, PKBob, E ( PKAlice, g y mod p ) Alice generates random value x Alice Bob: E ( PKBob, g x mod p ) Where PKAlice is Alice’s public key and PKBob is Bob’s public key. E(PK,X) denotes public key encryption of X under public key PK. At the end of the protocol, both Alice and Bob compute the same key: K = g xy mod p. Is this protocol susceptible to man-in-the-middle attack? Explain why or why not? 2 Problem 2: Recall the zero-knowledge “cave” example (discussed in class) that illustrates the utility of zero knowledge in real life. What is the importance of this step in the protocol? What would happen if it were skipped? 3) V looks into the cave (while standing at point A) 3 Problem 3: What would happen if we replace squaring in Fiat-Shamir with cubing? In other words, on the Prover side, we have: I=S3 mod n and x=R3 mod n. And, on the Verifier side, we check that, either R3 mod n = x and (RS)3 mod n = X*I mod n 4 Problem 4: Alice and Bob have never communicated and have no shared secrets. But, they want to establish a secure communication channel (i.e., somehow compute a common secret key). They don’t like difficult math like Diffie-Hellman . So, instead, they do the following: 1. Alice composes N different “puzzles” of the form Xi = E(ki, Pi || Ki) for 0<i<=N, where ki is a unique key, per puzzle, Ki is another unique per-puzzle key and Pi is a (also unique) puzzle number/counter. E(ki, “Alice”||Pi || Ki) denotes the encryption, under key ki, of string “Alice” together with Pi and Ki. 2. Alice stores copies of all unencrypted puzzles in her local table (see step 4 below). 3. Alice shuffles all puzzles (so their order is random) and sends all of them to Bob. 4. After receiving all puzzles, Bob picks one of them at random and breaks it by brute force. Doing so takes O(2M) work where M is the size (in bits) of each ki. Let’s say, he breaks the puzzle Xj (by computing kj) and obtains Pj and Kj. 5. Now, Bob sends a message to Alice: Pj, E(Kj,”Bob”). NOTE: Keep in mind that Pj is the puzzle number! 6. Alice receives this message and, using Pj, looks up the correct puzzle Xj in her table, gets Kj and decrypts Bob’s message. 7. From here on, Alice and Bob have a common secret key – Kj. Eve is a strictly PASSIVE adversary. She eavesdrops on ALL messages between Alice and Bob. Her goal, is to determine the key Kj. How much work would she need to do in order to compute Kj? 5 Problem 5 Suppose that Alice sees Bob’s RSA signatures on two distinct messages m 1 and m2: S1 = m1d mod n and S2= m2d mod n where d is Bob’s private key and (e, n) are his public exponent and modulus, respectively. a) How can Alice compute/fake Bob’s signatures on: m1j , m2-1 and m1j m2k for any arbitrary positive integers j and k? b) How can these attacks be avoided? 6