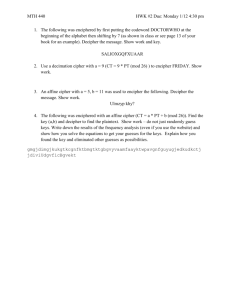
Section 2.2
advertisement

1
Section 2.2: Affine Ciphers; More Modular Arithmetic
Practice HW (not to hand in)
From Barr Textbook
p. 80 # 2a, 3e, 3f, 4, 5a, 7, 8
9, 10 (Use affinecipherbreaker Maplet to solve)
Extra Problems
Find the following gcd’s
a. gcd(30, 40)
b. gcd(150, 500)
c. gcd(187, 455)
Answers
10
50
1
In shift ciphers, messages are encrypted by using an additive key. To increase security,
we can, in addition to an additive parameter, encipher messages using a multiplicative
parameter. In affine ciphers, the key used for encipherment involves using both a
multiplicative and additive parameter. Before describing affine ciphers, we give some
necessary mathematics background.
Mathematics Background for Affine Ciphers
All natural numbers (numbers in the set {1, 2, 3, 4, 5, } can be expressed as the
product of two or more numbers. For example,
6 2 3 , 20 4 5 2 2 5 , and 7 1 7 .
Two numbers that can be multiplied together to get another number are called the factors
or divisors of that number. For example,
6 2 3 (2 and 3 are the divisors or factors of 6)
20 4 5 2 2 5 (2 and 5 are factors or divisors of 20).
7 1 7 (1 and 7 are the divisors or factors of 7).
Note that the only factors of 7 are 1 and itself. A number with this special type of
property is said to be prime, which we formally define next.
Definition: A natural number p is said to be prime if p 1 and its only divisors are 1
and p . A natural number that is not prime is said to be composite.
It can be shown that there are an infinite number of primes. The following set lists the
first ten primes:
{2, 3, 5, 7, 11, 13, 17, 19, 23, 29, }
The prime numbers provide the building blocks of all numbers. The next theorem
illustrates this fundamental fact.
2
Theorem: The Fundamental Theorem of Arithmetic. Every natural number larger than 1
is a product of primes. This factorization can be done in only one way if order is
disregarded.
For example, to factor 30, we can compute
30 6 5
2
3
5
3
2
5
5
2
3
.
same prime factorizat ion disregarding order
An elementary way to obtain prime factorizations with small prime factors involves the
use of a calculator and a factor tree. The next two examples illustrate this technique.
Example 1: Factor 90
Solution:
█
Example 2: Factor 935
Solution:
█
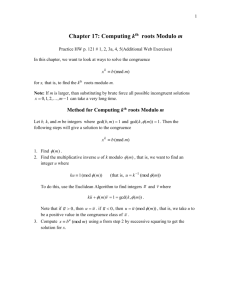
3
Greatest Common Divisor
The common prime factors of two numbers can be used to find the greatest common
divisor of two numbers, which we define next.
Definition: The greatest common divisor of two natural numbers a and b , denoted as
gcd( a, b) , is the largest natural number that divides a and b with no remainder.
Elementary Method for Computing the gcd of Two Numbers
Decompose each number into its prime factors. The gcd is obtained by multiplying the
prime factors the two numbers have in common. If the two numbers have no common
prime factors, then the gcd = 1.
Example 3: Find the gcd(20, 30).
Solution:
█
Example 4: Find the gcd(1190, 935).
Solution:
█
4
Example 5: Find the gcd(15, 26).
Solution:
█
Note: Two numbers a and b where the gcd( a, b) 1 are said to be relatively prime.
Multiplicative Inverses
In the real number system, every non-zero number has a multiplicative inverse – the
number you must multiply to a given number to get 1.
Example 6: Fill in the ( ) for (2) 1 , (10) 1 , and (a) 1 if we are working in
the real number system.
Solution:
█
5
Note: In some number systems, multiplicative inverses in most cases do not exist.
Example 7: Solve (2) 1 and (10) 1 using the integers
{, 4, 3, 2, 1, 0, 1, 2, 3, 4, }
Solution:
█
Note: In the modular arithmetic system, a multiplicative inverse may or may not exist,
depending on the following fact involving the gcd:
*Fact: If the gcd( b, m) 1 , then b has an inverse with respect to the modulus m , that
is, b 1 exists.
Example 8: Does 8 have an inverse with respect to the modulus 26?
Solution:
█
Example 9: Does 9 have and inverse with respect to the modulus 26?
Solution:
█
6
Later in the course, we will see a general mathematical method for computing
multiplicative inverses. For now, since we will work with a MOD 26 system, we will
display a table showing the numbers in a MOD 26 with their multiplicative inverses:
a
1
a MOD 26
1
1
3
9
5
21
7
15
9
3
11
19
15
7
17
23
19
11
21
5
23
17
25
25
Table 1: Multiplicative Inverses MOD 26
Example 10: Use Table 1 to find 7 1 MOD 26.
Solution:
█
Multiplicative inverses expand our ability to solve equations and congruences in modular
arithmetic. This is made possible using the multiplicative property of modular arithmetic,
which we state next.
Multiplicative Property for Modular Arithmetic
If a b mod m ,
then for any number k ,
ka kb mod m
We illustrate how this property can be used in the following example.
7
Example 11: Solve 11x 1 5 mod 26 for x .
Solution:
█
Multiplicative inverses in modular arithmetic can be useful in solving systems of linear
equations, which are useful for cryptanalysis. This next example illustrates this fact.
8
Example 12: Solve the system of equations (congruences)
8a b 18 mod 26
17a b 11 mod 26
Solution:
█
9
Mathematical Description of Affine Ciphers
Given a and b in Z 26 {0, 1, 2, , 24, 25} where gcd( a, 26) 1 . We encipher a
plaintext letter x to obtain a ciphertext letter y by computing
y (ax b) MOD 26.
Here, the key is made up of a multiplicative parameter a and an additive parameter b .
The next example illustrates how a message is enciphered.
Example 13: Encipher “RADFORD” using the affine cipher y (5 x 4) MOD 26.
Solution:
█
Note: Recall that for an affine cipher y (ax b) MOD 26 to be defined properly,
gcd( a, 26) 1 . Besides allowing a recipient to decipher a message, the next example
illustrates another reason why this requirement is essential.
10
Example 14 Use the affine cipher y (2 x 1) MOD 26 to encipher “AN”.
Solution:
█
Deciphering an Affine Cipher
For an affine cipher y (ax b) mod 26 where gcd( a, 26) 1 , decipherment can be
done uniquely. Given the numerical representation of the plaintext message x and
ciphertext message y , we take
y (ax b) mod 26
Hence, x a 1 ( y b) MOD 26 is the decipherment formula for affine ciphers. We
illustrate this formula with an example.
11
Example 15: Decipher the message “ARMMVKARER” that was encrypted using the
affine cipher
y (3x 5) MOD 26
(*)
Solution
█
12
Cryptanalysis of Affine Ciphers
For an affine cipher y (ax b) MOD 26, an enemy must know the multiplicative
parameter a and additive parameter b in order to decipher and break a message. Once a
and b are known, x a 1 ( y b) MOD 26 can be computed and the message broken.
Two methods of attack can be used to attempt to break an affine cipher.
Methods for Breaking and Affine Cipher
1. Exhaustion. Note there are 12 possible multiplicative parameters a where
gcd( a, 26) 1 and 26 possible additive parameters b . This gives 12 26 312 total
(a, b) pairs to test.
2. Frequency analysis. Quicker way which involves matching to highly frequently
occurring ciphertext letters with two highly frequently occurring plaintext letters.
Involves solving a system of equations MOD 26.
The next example illustrates method 2.
13
Example 16: Suppose we receive a ciphertext that was enciphered using an affine cipher.
After running a frequency analysis on the ciphertext, we find out that the most highly
frequently occurring letters in the ciphertext are W and H. Assuming that these letters
correspond to E and T respectively, find the parameters a and b that were used in the
affine cipher.
Solution: Recall that for an affine cipher y (ax b) mod 26 , x is the numerical
representation of the plaintext letter and y is the numerical representation of the
ciphertext letter. Hence, using the MOD 26 alphabet assignment and the equation
y (ax b) mod 26 , we see that
Plaintext E x 4 corresponds to the ciphertext W y 22 which gives the
equation (1) 22 (a 4 b) mod 26
Plaintext T x 19 corresponds to the ciphertext H y 7 which gives the equation
(2) 7 (a 19 b) mod 26
Rearranging and putting these equations together gives
4a b
22 mod 26
(1)
19a b
7 mod 26
(2)
To find a , we must solve this system of equations.
To eliminate the parameter b, we subtract equation (2) from equation (1):
4a b 22 mod 26
19a b 7 mod 26
15a
15 mod 26
Since 15 MOD 26 11 , we can write the resulting equation from the subtraction as:
11a 15 mod 26 .
We next solve this result by multiplying both sides by 111 :
111 11 a 111 15 mod 26 .
Noting from the MOD 26 multiplicative inverse table that 111 mod 26 19 , we obtain
a 19 15 mod 26 285 mod 26 25
(continued on next page)
14
Hence a 25 . We can substitute a 25 into either equation (1) or (2) to find b.
Choosing equation (1) 4a b 22 mod 26 , we obtain:
4(25) b 22 mod 26
or
100 b 22 mod 26 .
Subtracting 100 from both sides gives
b (22 100) mod 26
or
b 78 mod 26 0 .
Hence a 25 and b 0 solves the above system of equations. Hence, the affine cipher
y = (25x + 0) mod 26 = 25x mod 26 was used to encrypt the message.
█