6320Mid2Review1.Ans
advertisement
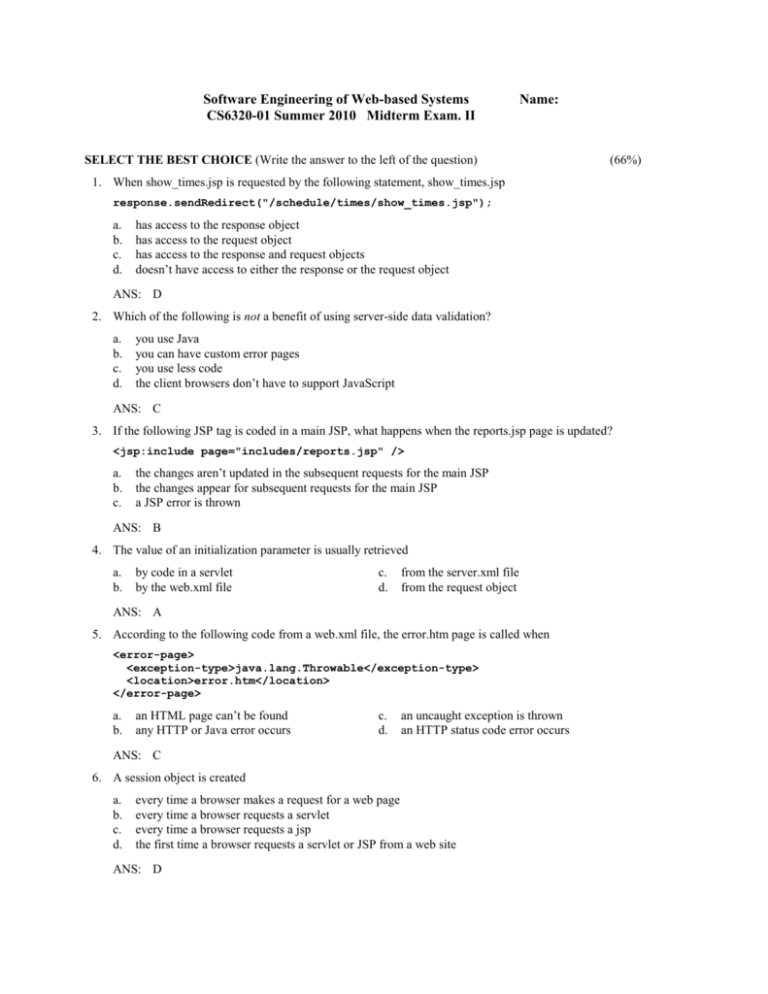
Software Engineering of Web-based Systems CS6320-01 Summer 2010 Midterm Exam. II Name: SELECT THE BEST CHOICE (Write the answer to the left of the question) (66%) 1. When show_times.jsp is requested by the following statement, show_times.jsp response.sendRedirect("/schedule/times/show_times.jsp"); a. b. c. d. has access to the response object has access to the request object has access to the response and request objects doesn’t have access to either the response or the request object ANS: D 2. Which of the following is not a benefit of using server-side data validation? a. b. c. d. you use Java you can have custom error pages you use less code the client browsers don’t have to support JavaScript ANS: C 3. If the following JSP tag is coded in a main JSP, what happens when the reports.jsp page is updated? <jsp:include page="includes/reports.jsp" /> a. b. c. the changes aren’t updated in the subsequent requests for the main JSP the changes appear for subsequent requests for the main JSP a JSP error is thrown ANS: B 4. The value of an initialization parameter is usually retrieved a. b. by code in a servlet by the web.xml file c. d. from the server.xml file from the request object ANS: A 5. According to the following code from a web.xml file, the error.htm page is called when <error-page> <exception-type>java.lang.Throwable</exception-type> <location>error.htm</location> </error-page> a. b. an HTML page can’t be found any HTTP or Java error occurs c. d. an uncaught exception is thrown an HTTP status code error occurs ANS: C 6. A session object is created a. b. c. d. every time a browser makes a request for a web page every time a browser requests a servlet every time a browser requests a jsp the first time a browser requests a servlet or JSP from a web site ANS: D 7. The current session object is available a. b. only to JSPs only to servlets c. to both servlets and JSPs ANS: C 8. Which of the following statements is invalid? a. b. c. d. String name = session.getAttribute("fullName"); Book book = (Book) session.getAttribute("bookObj"); session.setAttribute("fullName", "Ted Andrews"); session.removeAttribute("fullName"); ANS: A 9. When you use URL encoding for session tracking, you must a. b. c. d. e. convert all HTML pages in the application to JSPs use the encodeURL method to encode all URLs in the JSPs use the encodeURL method to encode all URLs in the servlets a and b above a, b, and c above ANS: D 10. The following Anchor tag demonstrates how to use <a href="/WorkServlet?shift=<%= shiftCode %>" > View your schedule </a> a. b. URL rewriting URL encoding c. d. hidden fields cookies ANS: A 11. When you use hidden fields to pass parameters to a servlet or JSP, all but one of the following is true. Which one is it? a. b. c. d. the parameters aren’t shown in the URL the user can see the parameters by using the browser to look at the page’s source code you don’t have to store the parameters in the session object you can’t use URL encoding ANS: D 12. If you use the MVC pattern with EL, a. b. c. d. the servlets create the JavaBeans and set the bean properties the servlets create the JavaBeans and the JSPs set the bean properties the JSPs create the JavaBeans and set the bean properties the JSPs create the JavaBeans and the servlets set the bean properties ANS: A 13. Before a server uses SSL to transmit data to a client, it a. b. c. d. provides a digital secure certificate to the client decrypts all data confirms the identity of the client authorizes the client ANS: A 14. A digital secure certificate is provided a. b. for a fee from a certificate authority free from a certificate authority c. d. for a fee from a registration authority free from a registration authority ANS: A 15. The maximum SSL strength for an application’s connections is determined by a. b. c. d. the SSL methods that you use the certification authority the registration authority the digital secure certificate ANS: D 16. Once you establish a secure connection, the application a. b. c. d. returns to a non-secure connection for subsequent requests uses absolute URLs to continue using the secure connection continues to use a secure connection until an absolute URL specifies a non-secure connection continues to use a secure connection until until a relative URL specifies a non-secure connection ANS: C 17. In Tomcat, a security constraint is coded in a. b. the web.xml file the server.xml file c. d. the context.xml file the application ANS: A 18. Which of the following is not included in a security constraint? a. b. c. the URL pattern for the restricted resources the authorized roles for accessing the restricted resources the authorized usernames for accessing the restricted resources ANS: C 19. The security realm provides the authorized a. b. usernames and passwords usernames and roles c. d. usernames, passwords, and roles passwords and roles ANS: C 20 . By default, Tomcat uses a security realm that stores the user data in a. b. the web.xml file the server.xml file c. d. a database the tomcat-users.xml file ANS: D 21. When an application uses basic authentication, a. b. c. d. the username and password are encrypted before being sent to the server a dialog box automatically prompts the user for a username and password the usernames and passwords are stored in the tomcat-users.xml file the web.xml file provides the path for the login page ANS: B 22. When an application uses form-based authentication, a. b. c. d. the username and password are encrypted before being sent to the server a dialog box automatically prompts the user for a username and password the usernames and passwords are stored in the tomcat-users.xml file the web.xml file provides the path for the login page ANS: D FILL IN THE MISSING BLANKS (27%) Select the best fit from the following word, or words: request, response, request parameters, WEB-INF, META-INF, tomcat, doPost, doGet, JSP, servlet, JSTL, JDBC, JavaBeans, AJAX, web.xml, ServletContext, init, attributes, cookie, URL rewriting, set, get, self-signed, context.xml, Context . 1. When you use the MVC pattern, you often add ________________________ to the request object before you forward it to a JSP or another servlet. ANS: attributes 2. By default, the servlet API uses a _______________________________ to store a session ID. ANS: cookie 3. To automatically append the session ID to a URL, you can use the encodeURL method of the _______________________________ object. ANS: response 4. Cookies are retrieved from the __________________________ object. ANS: request 5. Instead of storing data that’s used for a single request in the session object, you can use hidden fields or __________________________________. ANS: URL rewriting 6. One of the advantages that EL has over standard JSP tags is that you can not only use EL with ___________________ but also with maps, arrays, and lists. ANS: JavaBeans 7. One of the disadvantages of using EL is that it doesn’t provide a way to _______________ properties. ANS: set 8. A _________________________ digital secure certificate is enables you to test SSL connections in a local environment without purchasing a secure certificate. ANS: self-signed 9. You use the auth-method element in the ____________________ file to specify the type of authentication that’s going to be used by the application. ANS: web.xml ANSWER THE FOLLOWING QUESTION: (7%) In Exercise 16-1 Test a secure connection, the step 1 says that you need to create a self-signed certificate. (a) How do you create this certificate? (b) How can you be sure this is created before the testing ? Then step 1 says that you need to remove the comments in Tomcat’s server.xml file from the Connector element. (c) What is the purpose of doing so?