CNS ANSWER KEY FOR IV CSE
advertisement

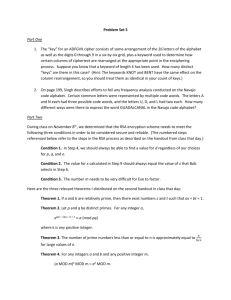
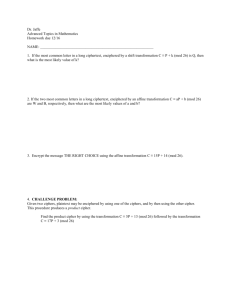
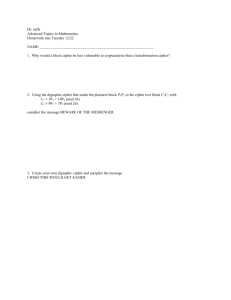
SNS COLLEGE OF ENGINEERING Kurumbapalayam(Po), Coimbatore – 641 107 Accredited by NAAC-UGC with ‘A’ Grade Approved by AICTE & Affiliated to Anna University, Chennai INTERNAL ASSESMENT EXAMINATIONS - I COURSE: B.E – CSE IT2352 – CRYPTOGRAPHY AND NETWORK SECURITY ANSWER KEY PART A 1. Cryptography is defined as the art or science encompassing the principles and methods of transforming an intelligible message into one that is unintelligible and then retransforming that message back to its original form. 2. Masquerade, Replay, Modification of messages, Denial of Service (DoS) 3. Cipher text= ANUIESTNANVRIY 4. gcd(1970, 1066)=2 5. XY mod n, if n is prime use Fermat little theorem, if n is not prime, check the value of X. If X is small use modular exponentiation and if x is big use Euler’s theorem 6. The S-boxes are the nonlinear part of DES that makes it difficult to break the algorithm and secure against linear and differential cryptanalysis. the s-boxes provide the "confusion" of data and key values, whilst the permutation P then spreads this as widely as possible, so each S-box output affects as many S-box inputs in the next round as possible, giving "diffusion". 7. Differential cryptanalysis is a general form of cryptanalysis applicable primarily to block ciphers, but also to stream ciphers and cryptographic hash functions. In the broadest sense, it is the study of how differences in information input can affect the resultant difference at the output. PART B 8. A) (i) Classical Cryptosystem Substitution Cipher- Mono alphabetic Cipher Caesar Cipher Affine Cipher Polyalphabetic Cipher Playfair Cipher Vigenere Cipher Hill Cipher 1 Transposition Cipher- Rail fence Technique Simple Columnar Transposition Technique Simple Columnar Transposition Technique with multiple rounds (ii) LFSR Sequence: In computing, a linear-feedback shift register (LFSR) is a shift register whose input bit is a linear function of its previous state. The most commonly used linear function of single bits is exclusive-or (XOR). Thus, an LFSR is most often a shift register whose input bit is driven by the XOR of some bits of the overall shift register value. B) (i) TYPES OF SECURITY SERVICES: The classification of security services are as follows: Confidentiality: Ensures that the information in a computer system and transmitted information are accessible only for reading by authorized parties. Eg., printing, displaying and other forms of disclosure. Authentication: Ensures that the origin of a message or electronic document is correctly identified, with an assurance that the identity is not false. Integrity: Ensures that only authorized parties are able to modify computer system assets and transmitted information. Modification includes writing, changing status, deleting, creating and delaying or replaying of transmitted messages. Non repudiation: Requires that neither the sender nor the receiver of a message be able to deny the transmission. Access control: Requires that access to information resources may be controlled by or the target system. Availability: Requires that computer system assets be available to authorized parties when needed. 9. A) (i) CHINESE REMAINDER THEOREM: Define pk = m1 …cmk …mn. That is, pk is the product of the m’s with mk omitted. By Lemma 1, (pk,mk) = 1. Hence, there are numbers sk, tk such that skpk + tkmk = 1. In terms of congruences, skpk = 1 (mod mk) . Now let x = a1p1s1 + a2s2p2 + ・ ・ ・ + anpnsn. If j 6= k, then mk | pj , so mod mk all the terms but the k-th term are 0 mod mk: x = akpksk = ak .. 1 = ak (mod mk) . 2 This proves that x is a solution to the system of congruences (and incidentally, gives a formula for x). Now suppose that x and y are two solutions to the system of congruences. x = a1 (mod m1) and y = a1 (mod m1) x = a2 (mod m2) and y = a2 (mod m2) ... x = an (mod mn) and y = an (mod mn) Then x = ak = y (mod mk) so x − y = 0 (mod mk) or mk | x − y. Thus, x − y is a multiple of all the m’s, so [m1, . . . ,mn] | x − y. But the m’s are pairwise relatively prime, so m1 …mn | x − y, or x = y (mod m1…mn) . That is, the solution to the congruences is unique mod m1… mn. (ii) The value of x=13 B) (i) GENERAL FORM FOR MODULAR EXPONENTIATION, FERMAT’S THEOREM AND EULER’S THEOREM WITH ITS THEOREM: Modular exponentiation is a type of exponentiation performed over a modulus. It is useful in computer science, especially in the field of public-key cryptography. The operation of modular exponentiation calculates the remainder when an integer b (the base) raised to the eth power (the exponent), be, is divided by a positive integer m (the modulus). In symbols, given base b, exponent e, and modulus m, the modular exponentiation c is: c ≡ be (mod m). Fermat's little theorem states that if p is a prime number, then for any integer a, the number a p − a is an integer multiple of p. In the notation of modular arithmetic, this is expressed as If a is not divisible by p, Fermat's little theorem is equivalent to the statement that a p − 1 − 1 is an integer multiple of p, or in symbols Euler’s function (n) denotes the number of positive integers not exceeding n and relatively prime to it. (We count 1 as relatively prime to all numbers). (ii) a) By fermat’s little theorem 321 mod 11= 20 10. A) (i) LEGENDRE SYMBOL: Let p be an odd prime number. An integer a is a quadratic residue modulo p if it is congruent to a perfect square modulo p and is a quadratic nonresidue modulo p otherwise. The Legendre symbol is a function of a and p defined as JACOBI SYMBOL: For any integer and any positive odd integer the Jacobi symbol is defined as the product of the Legendre symbols corresponding to the prime factors of : 3 (ii) a)1411/ 317 = +1 b) 1735/507 = -1 B) (i) DES algorithm : The Data Encryption Standard (DES) is a secret key encryption scheme adopted as standard. It uses a 56-bit key, which is today considered by many to be insufficient as it can with moderate effort be cracked by brute force. A variant called Triple-DES (TDES or 3DES) uses a longer key and is more secure, but has never become popular. The Advanced Encryption Standard (AES) is expected to supersede DES (and 3DES) as the standard encryption algorithm. Encryption of a block of the message takes place in 16 stages or rounds. From the input key, sixteen 48 bit keys are generated, one for each round. In each round, eight so-called S-boxes are used. These S-boxes are fixed in the specification of the standard. Using the S-boxes, groups of six bits are mapped to groups of four bits. The S-boxes appear to be randomly filled, but this is not the case. The block of the message is divided into two halves. The right half is expanded from 32 to 48 bits using another fixed table. The result is combined with the subkey for that round using the XOR operation. Using the S-boxes the 48 resulting bits are then transformed again to 32 bits, which are subsequently permutated again using yet another fixed table. This by now thoroughly shuffled right half is now combined with the left half using the XOR operation. In the next round, this combination is used as the new left half. 4