Question 1
advertisement
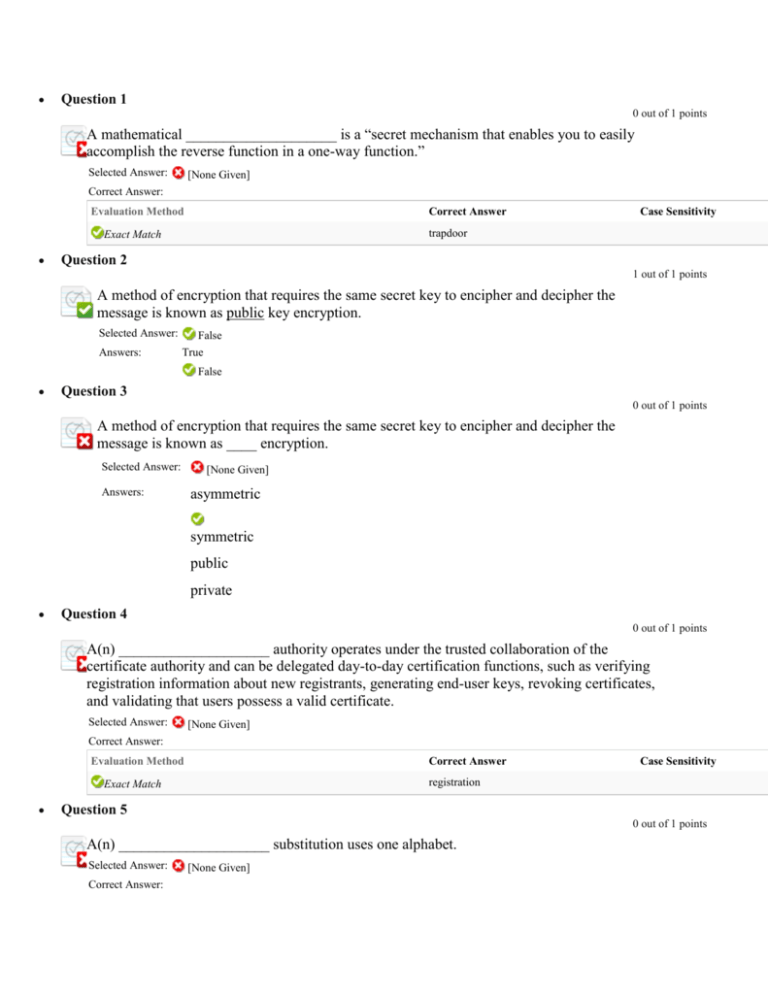
Question 1 0 out of 1 points A mathematical ____________________ is a “secret mechanism that enables you to easily accomplish the reverse function in a one-way function.” Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer trapdoor Exact Match Case Sensitivity Question 2 1 out of 1 points A method of encryption that requires the same secret key to encipher and decipher the message is known as public key encryption. Selected Answer: Answers: False True False Question 3 0 out of 1 points A method of encryption that requires the same secret key to encipher and decipher the message is known as ____ encryption. Selected Answer: Answers: [None Given] asymmetric symmetric public private Question 4 0 out of 1 points A(n) ____________________ authority operates under the trusted collaboration of the certificate authority and can be delegated day-to-day certification functions, such as verifying registration information about new registrants, generating end-user keys, revoking certificates, and validating that users possess a valid certificate. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer registration Exact Match Case Sensitivity Question 5 0 out of 1 points A(n) ____________________ substitution uses one alphabet. Selected Answer: Correct Answer: [None Given] Evaluation Method Correct Answer monoalphabetic Exact Match Case Sensitivity Question 6 0 out of 1 points A(n) distinguished name uniquely identifies a certificate entity, to a user’s public key. Selected Answer: Answers: [None Given] True False Question 7 0 out of 1 points A(n) key is the programmatic steps used to convert an unencrypted message into an encrypted sequence of bits that represent the message. Selected Answer: Answers: [None Given] True False Question 8 0 out of 1 points A(n) man-in-the-middle attack attempts to intercept a public key or even to insert a known key structure in place of the requested public key. Selected Answer: Answers: [None Given] True False Question 9 0 out of 1 points A(n) registration authority issues, manages, authenticates, signs, and revokes users’ digital certificates, which typically contain the user’s name, public key, and other identifying information. Selected Answer: Answers: [None Given] True False Question 10 0 out of 1 points A(n) response attack is an attempt to resubmit a recording of the deciphered authentication to gain entry into a secure source. Selected Answer: Answers: [None Given] True False Question 11 0 out of 1 points Also known as the one-time pad, the ____________________ cipher, which was developed at AT&T, uses a set of characters only one time for each encryption process. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Vernam Exact Match Case Sensitivity Question 12 0 out of 1 points An X.509 v3 certificate binds a(n) _____, which uniquely identifies a certificate entity, to a user’s public key. Selected Answer: Answers: [None Given] message digest fingerprint distinguished name digital signature Question 13 0 out of 1 points An attacker may obtain duplicate texts, one in ciphertext and one in plaintext, which enable the individual to reverse-engineer the encryption algorithm in a(n) knownplaintext attack scheme. Selected Answer: Answers: [None Given] True False Question 14 0 out of 1 points As DES became known as being too weak for highly classified communications, Double DES was created to provide a level of security far beyond that of DES. Selected Answer: Answers: [None Given] True False Question 15 0 out of 1 points Attackers may conduct an encrypted-plaintext attack by sending potential victims a specific text that they are sure the victims will forward on to others. Selected Answer: Answers: [None Given] True False Question 16 0 out of 1 points Bit stream methods most commonly use functions like the exclusive OR operation (_____). Selected Answer: [None Given] Answers: XOR EOR NOR OR Question 17 0 out of 1 points Common implementations of RA include: systems to issue digital certificates to users and servers; directory enrollment; key issuing systems; tools for managing the key issuance; and verification and return of certificates. Selected Answer: Answers: [None Given] True False Question 18 0 out of 1 points DES uses a 64-bit key. Selected Answer: Answers: [None Given] True False Question 19 0 out of 1 points DES uses a(n) _____-bit block size. Selected Answer: Answers: [None Given] 32 64 128 256 Question 20 Needs Grading Describe digital certificates. Selected Answer: Correct Answer: [None Given] Digital certificates are public-key container files that allow computer programs to validate the key and identify to whom it belongs. The certificate is often issued by a third party that certifies the authenticity of the information it contains. A digital signature attached to the certificate’s container file certifies the file’s origin and integrity. A certificate authority (CA) issues, manages, authenticates, signs, and revokes users’ digital certificates, which typically contain the user name, public key, and other identifying information. Response Feedback: [None Given] Question 21 Needs Grading Describe how hash functions work and what they are used for. Selected Answer: Correct Answer: [None Given] Response Feedback: [None Given] Hash functions are mathematical algorithms that generate a message summary or digest to confirm the identity of a specific message and to confirm that there have not been any changes to the content. While they do not create a ciphertext, hash functions confirm message identity and integrity, both of which are critical functions in e-commerce. Hashing functions do not require the use of keys, but it is possible to attach a message authentication code (MAC)—a key-dependent, one-way hash function—that allows only specific recipients (symmetric key holders) to access the message digest. Question 22 Needs Grading Describe symmetric and asymmetric encryptions. Selected Answer: Correct Answer: [None Given] Symmetric Encryption. Encryption methodologies that require the same secret key to encipher and decipher the message are using what is called private key encryption or symmetric encryption. Symmetric encryption methods use mathematical operations that can be programmed into extremely fast computing algorithms so that the encryption and decryption processes are executed quickly by even small computers. The primary challenge of symmetric key encryption is getting the key to the receiver, a process that must be conducted out of band (meaning through a channel or band other than the one carrying the ciphertext) to avoid interception. Asymmetric Encryption. Another category of encryption techniques is asymmetric encryption. Whereas the symmetric encryption systems are based on using a single key to both encrypt and decrypt a message, asymmetric encryption uses two different but related keys, and either key can be used to encrypt or decrypt the message. Asymmetric encryption can be used to provide elegant solutions to problems of secrecy and verification. This technique has its highest value when one key is used as a private key, which means that it is kept secret (much like the key of symmetric encryption), known only to the owner of the key pair, and the other key serves as a public key, which means that it is stored in a public location where anyone can use it. Response Feedback: [None Given] Question 23 0 out of 1 points Dictionary attacks are a collection of brute-force methods that attempt to deduce statistical relationships between the structure of the unknown key and the ciphertext that is the output of the cryptosystem. Selected Answer: Answers: [None Given] True False Question 24 0 out of 1 points Digital ____________________ are electronic documents that can be part of a process of identification associated with the presentation of a public key. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer certificates Exact Match Case Sensitivity Question 25 0 out of 1 points Digital ____________________ are encrypted messages that can be mathematically proven to be authentic. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer signatures Exact Match Case Sensitivity Question 26 0 out of 1 points Digital ____________________ are public key container files that allow computer programs to validate the key and identify to whom it belongs. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer certificates Exact Match Case Sensitivity Question 27 0 out of 1 points Digital signatures should be created using processes and products that are based on the ____. Selected Answer: [None Given] Answers: DSS NIST SSL HTTPS Question 28 0 out of 1 points ESP in transport mode can be used to establish a virtual private network, assuring encryption and authentication between networks communicating across the Internet. Selected Answer: Answers: [None Given] True False Question 29 0 out of 1 points Encryption is a process of hiding information and has been in use for a long time. Selected Answer: Answers: [None Given] True False Question 30 0 out of 1 points Encryption is the process of converting the ciphertext into a message that conveys readily understood meaning. Selected Answer: Answers: [None Given] True False Question 31 0 out of 1 points Hash algorithms are publicly known functions that create a value by converting variablelength messages into a single fixed-length value. Selected Answer: Answers: [None Given] True False Question 32 0 out of 1 points Hashing functions do not require the use of keys, but it is possible to attach a message ____________________ code. Selected Answer: [None Given] Correct Answer: Evaluation Method Exact Match Correct Answer Case Sensitivity authentication Question 33 0 out of 1 points Hashing functions require the use of keys. Selected Answer: Answers: [None Given] True False Question 34 0 out of 1 points In 1917, Gilbert S.Vernam, an AT&T employee, invented a polyalphabetic cipher machine that used a non-repeating random key. Selected Answer: Answers: [None Given] True False Question 35 0 out of 1 points In 1953, Giovan Batista Belaso introduced the idea of the passphrase (password) as a key for encryption. Selected Answer: Answers: [None Given] True False Question 36 0 out of 1 points In IPSEC ____________________ mode, only the IP data is encrypted, not the IP headers. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer transport Exact Match Case Sensitivity Question 37 0 out of 1 points In a(n) ____ attack, the attacker eavesdrops during the victim’s session and uses statistical analysis of the user’s typing patterns and inter-keystroke timings to discern sensitive session information. Selected Answer: Answers: [None Given] replay timing correlation dictionary Question 38 0 out of 1 points In a(n) ____________________ attack, the attacker eavesdrops during the victim’s session and uses statistical analysis of the user’s typing patterns and inter-keystroke timings to discern sensitive session information. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer timing Exact Match Case Sensitivity Question 39 0 out of 1 points In a(n) word attack, the attacker encrypts every word in a dictionary using the same cryptosystem as used by the target. Selected Answer: Answers: [None Given] True False Question 40 0 out of 1 points In transport mode the entire IP packet is encrypted and is then placed as the content portion of another IP packet. Selected Answer: Answers: [None Given] True False Question 41 0 out of 1 points Internet Protocol Security is designed to protect data integrity, user confidentiality, and authenticity at the IP packet level. Selected Answer: Answers: [None Given] True False Question 42 0 out of 1 points Julius Caesar was associated with an early version of the transposition cipher. Selected Answer: Answers: [None Given] True False Question 43 0 out of 1 points Netscape developed the ____________________ Layer protocol to use public key encryption to secure a channel over the public Internet, thus enabling secure communications. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Exact Match Secure Socket Exact Match Secure Sockets Case Sensitivity Question 44 0 out of 1 points Nonrepudiation means that customers or partners can be held accountable for transactions, such as online purchases, which they cannot later deny. Selected Answer: Answers: [None Given] True False Question 45 0 out of 1 points Once the attacker has successfully broken an encryption, he or she may launch a replay attack, which is an attempt to resubmit a recording of the deciphered authentication to gain entry into a secure source. Selected Answer: Answers: [None Given] True False Question 46 0 out of 1 points One encryption method made popular by spy movies involves using the text in a book as the key to decrypt a message. Selected Answer: Answers: [None Given] True False Question 47 0 out of 1 points One of the most widely known cryptographic algorithms is the Data ____________________ Standard, which was developed by IBM and is based on the company’s Lucifer algorithm. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Encryption Exact Match Case Sensitivity Question 48 0 out of 1 points PGP uses the freeware ZIP algorithm to compress the message after it has been digitally signed but before it is encrypted. Selected Answer: Answers: [None Given] True False Question 49 0 out of 1 points PKI systems are based on public key cryptosystems and include digital certificates and certificate authorities. Selected Answer: Answers: [None Given] True False Question 50 0 out of 1 points Plaintext or cleartext is the original unencrypted message that is encrypted; also the name given to the results of a message that has been successfully decrypted. Selected Answer: Answers: [None Given] True False Question 51 0 out of 1 points Popular cryptosystems use a hybrid combination of symmetric and asymmetric algorithms. Selected Answer: Answers: [None Given] True False Question 52 0 out of 1 points Privacy Enhanced Mail was proposed by the Internet Engineering Task Force as a standard to function with the public key cryptosystems. Selected Answer: Answers: [None Given] True False Question 53 0 out of 1 points SHA-1 produces a(n) _____-bit message digest, which can then be used as an input to a digital signature algorithm. Selected Answer: Answers: [None Given] 48 56 160 256 Question 54 0 out of 1 points SSL builds on the encoding format of the Multipurpose Internet Mail Extensions protocol by adding encryption and authentication through the use of digital signatures based on public key cryptosystems. Selected Answer: Answers: [None Given] True False Question 55 0 out of 1 points Secure Electronic Transactions was developed by MasterCard and VISA in 1997 to provide protection from electronic payment fraud. Selected Answer: Answers: [None Given] True False Question 56 0 out of 1 points Secure HTTP provides the Internet communication services between client and host without consideration for encryption of the data that is communicated over the connection between client and server. Selected Answer: Answers: [None Given] True False Question 57 0 out of 1 points Secure Multipurpose Internet Mail Extensions builds on the encoding format of the Multipurpose Internet Mail Extensions protocol by adding encryption and authentication through the use of digital signatures based on public key cryptosystems. Selected Answer: Answers: [None Given] True False Question 58 0 out of 1 points Sequence encryption is a series of encryptions and decryptions between a number of systems, wherein each system in a network decrypts the message sent to it and then reencrypts it using different keys and sends it to the next neighbor, and this process continues until the message reaches the final destination. Selected Answer: Answers: [None Given] True False Question 59 0 out of 1 points Standard-HTTP (S-HTTP) is an extended version of the Hypertext Transfer Protocol that provides for the encryption of individual messages between a client and server across the Internet. Selected Answer: Answers: [None Given] True False Question 60 0 out of 1 points Substitution ciphers that use two or more alphabets, and are referred to as ____ substitutions. Selected Answer: [None Given] Answers: multialphabetic monoalphabetic polyalphabetic polynomic Question 61 0 out of 1 points Symmetric encryption uses two different but related keys, and either key can be used to encrypt or decrypt the message. Selected Answer: Answers: [None Given] True False Question 62 0 out of 1 points The 3DES implements a block cipher with a variable block length and a key length of 128, 192, or 256 bits. Selected Answer: Answers: [None Given] True False Question 63 0 out of 1 points The AES algorithm was the first public key encryption algorithm. Selected Answer: Answers: [None Given] True False Question 64 0 out of 1 points The AES implements a block cipher called the Rijndael Block Cipher. Selected Answer: Answers: [None Given] True False Question 65 0 out of 1 points The CA periodically distributes a(n) ____ to all users that identifies all revoked certificates. Selected Answer: [None Given] Answers: CRL RA MAC AES Question 66 0 out of 1 points The SHTTP security solution provides six services: authentication by digital signatures, message encryption, compression, e-mail compatibility, segmentation, and key management. Selected Answer: Answers: [None Given] True False Question 67 0 out of 1 points The Secure ____________________ Standard is a standard issued by the National Institute of Standards and Technology. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Hash Exact Match Case Sensitivity Question 68 0 out of 1 points The ____ algorithm was the first public key encryption algorithm developed (in 1977) and published for commercial use. Selected Answer: Answers: [None Given] DES RSA MAC AES Question 69 0 out of 1 points The ____ is essentially a one-way hash value that is encrypted with a symmetric key. Selected Answer: Answers: [None Given] signature MAC fingerprint digest Question 70 0 out of 1 points The ____ is responsible for the fragmentation, compression, encryption, and attachment of an SSL header to the cleartext prior to transmission. Selected Answer: Answers: [None Given] Standard HTTP SFTP S-HTTP SSL Record Protocol Question 71 0 out of 1 points The ____ protocol provides system to system authentication and data integrity verification, but does not provide secrecy for the content of a network communication. Selected Answer: Answers: [None Given] ESP AH HA SEP Question 72 0 out of 1 points The ____________________ OR operation is a function of Boolean algebra in which two bits are compared, and if the two bits are identical, the result is a binary 0. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer exclusive Exact Match Case Sensitivity Question 73 0 out of 1 points The ____________________ cipher simply rearranges the values within a block to create the ciphertext. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Exact Match transposition Exact Match permutation Case Sensitivity Question 74 0 out of 1 points The application header protocol provides secrecy for the content of a network communication. Selected Answer: Answers: [None Given] True False Question 75 0 out of 1 points The asymmetric encryption systems are based on using a single key to both encrypt and decrypt a message. Selected Answer: Answers: [None Given] True False Question 76 0 out of 1 points The encapsulating security ____________________ protocol provides secrecy for the contents of network communications as well as system to system authentication and data integrity verification. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer payload Exact Match Case Sensitivity Question 77 0 out of 1 points The encapsulating security payload protocol provides confidentiality services for IP packets across insecure networks. Selected Answer: Answers: [None Given] True False Question 78 0 out of 1 points The message ____________________ is a fingerprint of the author’s message that is to be compared with the receiver’s locally calculated hash of the same message. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer digest Exact Match Case Sensitivity Question 79 0 out of 1 points The more common name for asymmetric encryption is ____________________ key encryption. Selected Answer: Correct Answer: [None Given] Evaluation Method Correct Answer public Exact Match Case Sensitivity Question 80 0 out of 1 points The most common hybrid system is based on the Diffie-Hellman Key Exchange method, which is a method for exchanging private keys using public key encryption. Selected Answer: Answers: [None Given] True False Question 81 0 out of 1 points The most popular modern version of steganography involves hiding information within files that appear to contain digital pictures or other images. Selected Answer: Answers: [None Given] True False Question 82 0 out of 1 points The number of horizontal and vertical pixels captured and recorded is known as the image’s depth. Selected Answer: Answers: [None Given] True False Question 83 0 out of 1 points The permutation cipher simply rearranges the values within a block to create the ciphertext. Selected Answer: Answers: [None Given] True False Question 84 0 out of 1 points The process of hiding messages is called ____________________. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer steganography Exact Match Case Sensitivity Question 85 0 out of 1 points The science of encryption is known as ____________________. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer cryptology Exact Match Case Sensitivity Question 86 0 out of 1 points The successor to 3DES is the ____________________ Encryption Standard. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Advanced Exact Match Case Sensitivity Question 87 0 out of 1 points To ____________________ means to encrypt or convert plaintext into the equivalent ciphertext. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer encipher Exact Match Case Sensitivity Question 88 0 out of 1 points To encipher means to decrypt or convert ciphertext into the equivalent plaintext. Selected Answer: Answers: [None Given] True False Question 89 0 out of 1 points To perform the Caesar cipher encryption operation, pad values are added to numeric values that represent the plaintext that needs to be encrypted. Selected Answer: Answers: [None Given] True False Question 90 0 out of 1 points Two hundred and eighty five computers can crack a 56-bit key in one year, ten times as many would do it in a little over a month. Selected Answer: Answers: [None Given] True False Question 91 0 out of 1 points When an asymmetric cryptographic process uses the sender’s private key to encrypt a message, the sender’s public key must be used to decrypt the message. Selected Answer: Answers: [None Given] True False Question 92 0 out of 1 points When using a(n) ____________________ cipher, you replace one value with another. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer substitution Exact Match Case Sensitivity Question 93 0 out of 1 points With Diffie-Hellman, asymmetric encryption is used to exchange session keys. Selected Answer: Answers: [None Given] True False Question 94 0 out of 1 points You cannot combine the XOR operation with a block cipher operation. Selected Answer: Answers: [None Given] True False Question 95 0 out of 1 points ____ are encrypted messages that can be mathematically proven to be authentic. Selected Answer: [None Given] Answers: Digital signatures MAC Message certificates Message digests Question 96 0 out of 1 points ____ attacks are a collection of brute-force methods that attempt to deduce statistical relationships between the structure of the unknown key and the ciphertext that is the output of the cryptosystem. Selected Answer: Answers: [None Given] Timing Dictionary Correlation Man-in-the-middle Question 97 0 out of 1 points ____ functions are mathematical algorithms that generate a message summary or digest to confirm the identity of a specific message and to confirm that there have not been any changes to the content. Selected Answer: [None Given] Answers: Hash Map Key Encryption Question 98 0 out of 1 points ____ is a Federal Information Processing Standard that specifies a cryptographic algorithm that is used within the U.S. government to protect information at federal agencies that are not a part of the national defense infrastructure. Selected Answer: Answers: [None Given] DES 2DES AES 3DES Question 99 0 out of 1 points ____ is a hybrid cryptosystem originally designed in 1991 by Phil Zimmermann. Selected Answer: [None Given] Answers: PGP DES AH ESP Question 100 0 out of 1 points ____ is an integrated system of software, encryption methodologies, protocols, legal agreements, and third-party services that enables users to communicate securely. Selected Answer: Answers: [None Given] MAC PKI DES AES Question 101 0 out of 1 points ____ is an open source protocol to secure communications across any IP-based network such as LANs, WANs, and the Internet. Selected Answer: Answers: [None Given] PEM SSH IPSec SET Question 102 0 out of 1 points ____ is the amount of effort (usually in hours) required to perform cryptanalysis on an encoded message so that it may be decrypted when the key or algorithm (or both) are unknown. Selected Answer: Answers: [None Given] Code Algorithm Key Work factor Question 103 0 out of 1 points ____ is the entire range of values that can possibly be used to construct an individual key. Selected Answer: Answers: [None Given] Code Keyspace Algorithm Cryptogram Question 104 0 out of 1 points ____ is the information used in conjunction with an algorithm to create the ciphertext from the plaintext or derive the plaintext from the ciphertext. Selected Answer: Answers: [None Given] Password Cipher Key Passphrase Question 105 0 out of 1 points ____ is the process of converting an original message into a form that is unreadable to unauthorized individuals. Selected Answer: [None Given] Answers: Encryption Decryption Cryptology Cryptography Question 106 0 out of 1 points ____ was developed by Phil Zimmermann and uses the IDEA Cipher for message encoding. Selected Answer: Answers: [None Given] PEM PGP S/MIME SSL Question 107 0 out of 1 points ____________________ is the process of making and using codes to secure the transmission of information. Selected Answer: [None Given] Correct Answer: Evaluation Method Correct Answer Cryptography Exact Match Case Sensitivity Question 108 0 out of 1 points ____________________ or cryptosystem is an encryption method or process encompassing the algorithm, key(s) or cryptovariable(s), and procedures used to perform encryption and decryption. Selected Answer: [None Given] Correct Answer: Evaluation Method Exact Match Correct Answer Cipher Case Sensitivity