Security
Grenoble University
History / Organization / Calendar
Objective
Content : 2 possible « tracks »:
« M2 P » SCCI :
« M2R SCCI »
Yet:
• « SAFE » : cursus en apprentissage, enseigné en Français
Some examples of Master thesis
Context - Objective
Context : expansion of networks and distributed applications
Confidentiality, Authentication, Integrity, Non-repudiation
Various applications and professional skills:
Enterprise specialised in security: solutions providers (hardware, software, smartcard, …); security audit, …
Specialized department of a company : bank, e-business, telecom, video, tv, …
Information system within a company: network/system administration
Formation spécialisée en 1 an conjointe UJF – INP (Grenoble Univ.)
Institut Fourier et Ensimag
Objective : formation of experts in security and coding technologies
Cryptology : mathematical protocols (RSA, AES, ECC…)
Security : software/hardware (network, system, integraton)
Applications : watermarking, multimedia, smartcard, …
Directed to profession (M2P) or to research (M2R)
Brief history & Organization
Master UJFIPG Cryptologie, Sécurité, Codage de l’Information (2001…)
Sept 2003 : first promotion:17 graduate students
Up to Sept 2010: 198 graduated students (99 IPG, 99 UJF); 230 expected in 2011.
From Sept 2007: international M2P – program taught in English
M2 Security, Cryptology and Coding of Information Systems
Gathers French and English speaking students (2 groups of students)
From Sept 2008: part of MOSIG International Master
Director UJF/IF : Philippe.Elbaz-Vincent@ujf-grenoble.fr
Co-director INP/ENSIMAG: Jean-Louis.Roch@imag.fr
From Sept 2011: 2 academic programs: M2R and M2P SCCI
http://www-ufrima.imag.fr/ue_filiere.php3?filiere=M2RCRYPTO&id=739&lang=en
http://www-ufrima.imag.fr/spip.php?article49
http://www-fourier.ujf-grenoble.fr/enseignement/spip.php?rubrique19
From Sept 2011: can be attended as a standard track for ENSIMAG students
« Grenoble-INP » semestre à choix
Academic calendar:
M2R : sept-january : courses / Feb-june: Master thesis
M2P : sept-march: courses / April-sept: Master thesis r thesis)
mid-June: mid-term presentation and mid-September: Master thesis defense
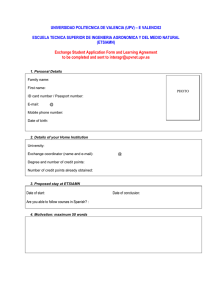
M2- P Mosig SCCI (M2-P)
Organization / Credits
27 ECTS Thèse de Master
3 ECTS UE Transversal
( Anglais /Français/Histoire des sciences, ….)
30 ECTS “scientifique/technique”
15 ECTS Tronc commun
12 ECTS Spécialisation au choix: “info” ou “math”
3 ECTS = UE au choix (2 proposés, ouvert Master)
General schedule for a 6 ECTS scientific module
36h lectures (in English)
+ 24h “training” in ½ group: TP/ Exercises/ Complements
1 group taight in English + 1 group taught in French
of Information Systems
Content / Credits for the Master degree
Non-elective Core Courses 18 ECTS
Security models: proofs, protocols and politics
Symmetric and asymmetric cryptology – PKI
System administration and network security
English or French
Choose one of the two following elective 12 ECTS
Elective A. Security of systems and infrastructures
Advanced security of system and networks
Hardware and embedded secure architectectures
Distributed algorithms and fault-tolerance
Deployment of a secure grid infrastructure
Elective B. Cryptology, coding and multimedia appl.
Advanced cryptology: elliptic curves and cryptanalysis
Multimedia applications and watermarking
Error correcting codes and fault-tolerance
Choose one of the two following elective 3 ECTS
Elective 1. Smart card security, certification and norms
Elective 2 . Quantum cryptography, biometrics, pairings
ECTS Teaching teams
3
3
6
6
Autreau, Lafourcade, Roch
Dumas, Elbaz-Vincent
Denneulin, Wagner, Marchand
Pool Langues
3
3
3
3
6
3
3
3
3
Wagner, Castellucia
Leveugle
Quéma, Anghel
Denneulin, Wagner
Elbaz-Vincent , Leprévost, Gillard
Cayre, Ebrahimi, Bas
Roch, Patchichkine, Brossier
Autreau, Canovas, Potet
Arrighi, Elbaz-Vincent
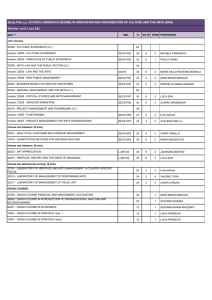
Formation à la recherche en SECR
Travail individuel (lectures, no “training”, assignments)
1 ECTS = 24 H work = 6h lectures + 18h individual homework
Aspects fondamentaux, aussi bien math que info
Common core: 24 ECTS
Security models: proofs, protocols and politics
Symmetric and asymmetric cryptology
– PKI
System and Network Security
• System administration and network security
• Advanced security of system and networks
Advanced cryptology:elliptic curves and cryptanalysis
Elective. 6 ECTS
Either: [6 ECTS]
•
Smart card security, certification and norms
• Quantum cryptography, biometrics, pairings
Or elective course in the M2 MI [6 ECTS]
•
Requires validation by the program director
[3 ECTS]
[3 ECTS]
[6 ECTS]
[6 ECTS]
[6 ECTS]
[6 ECTS]
Examples of Master thesis
Integration of zero-knowledge authentication on smart card [C-S]
Secure server for SIP telecommunications [INRIA]
Integration of strong authentication in an information system [British Telecom]
Management of identity for printer access [Helwett-Packard, Germany]
Reconfiguraton of a secure infrastructure [France-Telecom, Grenoble]
Conception et réalisation d’un composant de sécurité [Ministère Défense, Paris]
Analysis and deployment of a confidential data service [Solucom, Nantes]
Integration of biometrics in crypto protocols [SAGEM, Paris]
Hidden channel attacks [SAGEM, Paris]
Windows CardSpace components in a smart card [Gemalto, La Ciotat]
Secure loading of jar in JavaCard3.0 [Gemalto, La Ciotat]
Lightweight electronic signature [Dictao, Paris]
Wireless infrastructure for emergency comm. [Wisecomm, Germany]
Secure and anonymous communication on internet [UL, Luxembourg]
Test of crypto-secure random generators [LTSI, Lyon]
Security analysis of a medical data protection scheme [Philips, Eindhoven]
Supervision of the CEA computer infrastructure [CEA, Grenoble]
Security analysis of images watermarking [GIPSA, Grenoble]
Security audit of the SCADA platform [Atos Origin, Grenoble]
….