RPISEC-Crypto
advertisement
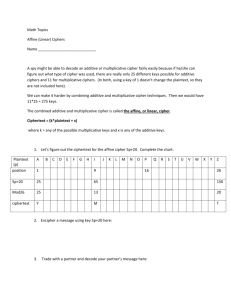
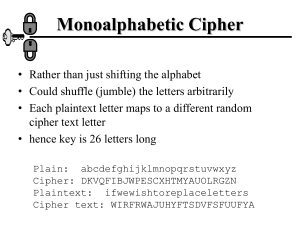
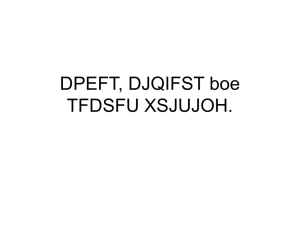
Crypto for CTFs RPISEC 2013 Ben Kaiser Terminology • • • • • • • • plaintext - the original message ciphertext - the coded message cipher - algorithm for transforming plaintext to ciphertext key - info used in cipher known only to sender/receiver encipher (encrypt) - converting plaintext to ciphertext decipher (decrypt) - recovering ciphertext from plaintext cryptography - study of encryption principles/methods cryptanalysis (codebreaking) - the study of principles/methods of deciphering ciphertext without knowing key Classification • Characterize by: • Type of encryption operations used • substitution • transposition • product • Number of keys used • single-key (private) • two-key (public) • Way in which plaintext is processed • Block – processes a block of element at a time • Stream – processes continuous stream of elements Classical Ciphers - Substitution • Letters of plaintext are replaced by other letters or by numbers or symbols. • Monoalphabetic ciphers: For every letter, one and only one letter (or symbol) is substituted. • Polyalphabetic ciphers: Throughout the cipher text, different symbols can stand for the same letter, and the same symbols can stand for different letters Monoalphabetic Ciphers The “key” for substitution ciphers is a mapping from plaintext alphabet to ciphertext alphabet. It must be known to both parties. • Caesar cipher: • Each character is converted to a numeric value (0-25), then summed with a constant value (the key) and modded by 25. • rpisecisfun becomes uslvhflvixq if the key is 3. Monoalphabetic Ciphers • The Caesar Cipher is easy to break by brute force since there are only 25 possible keys. Let’s look at a more complex monoalphabetic cipher. • What if we had a 26-character key that maps each plaintext character to a ciphertext character at random? That gives 26! = 403 septillion possible keys. Frequency Analysis • You’d think this would be incredibly difficult to break, but it’s not thanks to frequency analysis • In English, “E” is the most common letter, followed by T,R,N,I,O,A, and S. Z,J,K,Q, and X are quite rare. Frequency Analysis • Calculate the letter frequencies for your ciphertext, then compare counts against known values. • Use known tricks: • • • • • • • • The most common letter at the end of a word is E The most common beginning letter of a word is T A single-letter word is A or I, and on rare occasions, O. The most frequent two-letter word is OF, followed by TO and IN The most used three-letter word is THE, next common is AND The most frequent four-letter word is THAT Q is always followed by U The most common double letters are: LL, EE, SS, OO, TT, FF, RR, NN, PP and CC Practice: Cracking a Monoalphabetic Cipher UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZV UEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSXEPYEPOPD ZSZUFPOMBZWPFUPZHMDJUDTMOHMQ • Hints: Practice: Cracking a Monoalphabetic Cipher UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZV UEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSXEPYEPOPD ZSZUFPOMBZWPFUPZHMDJUDTMOHMQ • Hints: • Count the letter frequencies and compare to the chart. Make educated guesses and work from there (guess & check). Practice: Cracking a Monoalphabetic Cipher UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZV UEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSXEPYEPOPD ZSZUFPOMBZWPFUPZHMDJUDTMOHMQ • Hints: • Count the letter frequencies and compare to the chart. Make educated guesses and work from there (guess & check). • P & Z are very frequent in the ciphertext – let’s guess those are E and T, the two most common letters in English. Practice: Cracking a Monoalphabetic Cipher UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZV UEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSXEPYEPOPD ZSZUFPOMBZWPFUPZHMDJUDTMOHMQ • Hints: • Count the letter frequencies and compare to the chart. Make educated guesses and work from there (guess & check). • P & Z are very frequent in the ciphertext – let’s guess those are E and T, the two most common letters in English. • ZW is a common letter combination. If Z = T then maybe TH? What does that make ZWP likely to be? Practice: Cracking a Monoalphabetic Cipher UZQSOVUOHXMOPVGPOZPEVSGZWSZOPFPESXUDBMETSXAIZV UEPHZHMDZSHZOWSFPAPPDTSVPQUZWYMXUZUHSXEPYEPOPD ZSZUFPOMBZWPFUPZHMDJUDTMOHMQ • Hints: • Count the letter frequencies and compare to the chart. Make educated guesses and work from there (guess & check). • P & Z are very frequent in the ciphertext – let’s guess those are E and T, the two most common letters in English. • ZW is a common letter combination. If Z = T then maybe TH? What does that make ZWP likely to be? • “It was disclosed yesterday that several informal but direct contacts have been made with political representatives of the vietcong in moscow.” CSAW 2011 Crypto5: 200 Pts JR UNIR QVFPBIRERQ GUNG BHE YNFG GUERR GENAFZVFFVBAF JR'ER RNFVYL QRPVCURERQ. JR UNIR GNXRA PNER BS GUR CNEGL ERFCBAFVOYR SBE GURVE RAPBQVAT NAQ NER ABJ HFVAT N ARJ ZRGUBQ. HFR GUR VASBEZNGVBA CEBIVQRQ NG YNFG JRRX.F ZRRGVAT GB QRPVCURE NYY ARJ ZRFFNTRF. NAQ ERZRZORE, GUVF JRRX.F XRL VF BOSHFPNGRQ. No hint was provided, but I’ve only showed you one cipher so far so connect the dots. CSAW 2011 Crypto5: 200 Pts JR UNIR QVFPBIRERQ GUNG BHE YNFG GUERR GENAFZVFFVBAF JR'ER RNFVYL QRPVCURERQ. JR UNIR GNXRA PNER BS GUR CNEGL ERFCBAFVOYR SBE GURVE RAPBQVAT NAQ NER ABJ HFVAT N ARJ ZRGUBQ. HFR GUR VASBEZNGVBA CEBIVQRQ NG YNFG JRRX.F ZRRGVAT GB QRPVCURE NYY ARJ ZRFFNTRF. NAQ ERZRZORE, GUVF JRRX.F XRL VF BOSHFPNGRQ. Answer: The key is 13. WE HAVE DISCOVERED THAT OUR LAST THREE TRANSMISSIONS WERE EASILY DECIPHERED. … PHDays CTF 2013: Crypto 100 Decrypt the message: 7y9rr177sluqv1r4pw Hint: at $ PHDays CTF 2013: Crypto 100 Decrypt the message: 7y9rr177sluqv1r4pw Hint: at $ The cipher used is the Atbash Cipher. Each letter is assigned to the letter at the opposite end of the alphabet – A=Z, B=Y, C=X, etc. In this case, the numbers 0-9 were added onto the end of the key so A=9, B=8, … J=1, K=Z, L=Y, etc. PHDays CTF 2013: Crypto 100 Decrypt the message: 7y9rr177sluqv1r4pw Hint: at $ The cipher used is the Atbash Cipher. Each letter is assigned to the letter at the opposite end of the alphabet – A=Z, B=Y, C=X, etc. In this case, the numbers 0-9 were added onto the end of the key so A=9, B=8, … J=1, K=Z, L=Y, etc. classiccryptoisfun CSAW 2011 Crypto1 – 100 pts 87 101 108 99 111 109 101 32 116 111 32 116 104 101 32 50 48 49 49 32 78 89 85 32 80 111 108 121 32 67 83 65 87 32 67 84 70 32 101 118 101 110 116 46 32 87 101 32 104 97 118 101 32 112 108 97 110 110 101 100 32 109 97 110 121 32 99 104 97 108 108 101 110 103 101 115 32 102 111 114 32 121 111 117 32 97 110 100 32 119 101 32 104 111 112 101 32 121 111 117 32 104 97 118 101 32 102 117 110 32 115 111 108 118 105 110 103 32 116 104 101 109 32 97 108 108 46 32 84 104 101 32 107 101 121 32 102 111 114 32 116 104 105 115 32 99 104 97 108 108 101 110 103 101 32 105 115 32 99 114 121 112 116 111 103 114 97 112 104 121 46 This is a simple monoalphabetic cipher. Do these numbers look like anything you recognize? If not, try frequency analysis. More Advanced Monoalphabetic Ciphers • The Playfair Cipher is a famous advanced Monoalphabetic Cipher that uses single word as a key. That word is used to generate a 5x5 character matrix: • If “MONARCHY” is the key, our matrix looks like this: MONAR CHYBD EFGIK LPQST UVWXZ Playfair Cipher • plaintext encrypted two letters at a time: • if a pair is a repeated letter, insert a filler like 'X', eg. "balloon" encrypts as "ba lx lo on" • if both letters fall in the same row, replace each with letter to right (wrapping back to start from end), eg. “ar" encrypts as "RM" • if both letters fall in the same column, replace each with the letter below it (again wrapping to top from bottom), eg. “mu" encrypts to "CM" • otherwise each letter is replaced by the one in its row in the column of the other letter of the pair, eg. “hs" encrypts to "BP", and “ea" to "IM" or "JM" (as desired) • Decrypt ONANMSVFBIKLEBUBFSCFAT using “MONARCHY” as a key. Polyalphabetic Ciphers • In a polyalphabetic ciphers, each letter of a ciphertext does not always decrypt to the same plaintext letter. • The Vigenère Cipher is essentially multiple Caesar Ciphers: • • • • key is multiple letters long K = k1 k2 ... kd ith letter specifies ith alphabet to use use each alphabet in turn repeat from start after d letters in message Vigenère Cipher • • • • • write the plaintext out write the keyword repeated above it use each key letter as a caesar cipher key encrypt the corresponding plaintext letter eg using keyword deceptive • key: • plaintext: • ciphertext: deceptivedeceptivedeceptive wearediscoveredsaveyourself ZICVTWQNGRZGVTWAVZHCQYGLMGJ Kasiski Method of Breaking Vigenère • Guess the key length • • • • • • • • • Find a number of duplicated sequences Collect all their distances apart Look for common factors Thus obtain a set of monoalphabetic ciphers (each is subject to letter fq. Char.) repetitions in ciphertext give clues to period so find same plaintext an exact period apart which results in the same ciphertext of course, could also be random fluke eg repeated “VTW” in previous example • suggests size of 3 or 9 • then attack each monoalphabetic cipher individually using same techniques as before Transposition Ciphers • Transposition (or permutation) ciphers hide the message by rearranging the letter order in the message without altering the actual letters used. • The classic example is the Rail Fence cipher, in which you write message letters out diagonally over a number of rows, then read off the cipher row by row. • Plain Text: Meet me tonight + padding(qxz) M E M T N G T X E T E O I H Q Z • Cipher Text: MEMTNGTXETEOIHQZ